from the a-failure-at-any-level dept
Look, I get it. Government waste is real. Bureaucratic bloat is real. The desire to have a federal government that spends taxpayer money wisely and operates without unnecessary friction? That’s a pretty standard and quite reasonable desire in American politics. So when Elon Musk showed up promising he could cut $2 trillion in federal spending by bringing the vaunted “efficiency” of the tech world to the government, a lot of people — not just MAGA diehards, but regular people who’d spent time cursing at a federal website built in 2003 or waiting on hold with the DMV — thought: sure, maybe give it a shot. A decade of fawning tech press coverage about Elon Musk will do that to your priors.
We now have the receipts on how that went. And they’re absolutely damning.
Between a comprehensive forensic accounting from the New York Times published in December and a detailed report from House Oversight Committee Ranking Member Robert Garcia released in February, we can now do a proper post-mortem on DOGE. The diagnosis: the patient was dead on arrival, the surgery was performed by people who lied about their credentials, and the bill for the operation far exceeded anything that was supposedly “saved.”
Let’s start with the most basic question: did DOGE save the government money? Because that was, you know, apparently the whole point (or so we were told).
The answer, as the Times bluntly puts it:
But the group did not do what Mr. Musk said it would: reduce federal spending by $1 trillion before October. On DOGE’s watch, federal spending did not go down at all. It went up.
Spending went up. Musk promised $2 trillion in cuts during the campaign, started walking that back almost immediately after the election, and the actual result was that the government spent more money. The entire exercise was supposed to pay for itself many times over. Instead, the taxpayer funded an $81 million operation that produced negative returns.
But DOGE had that website — the “Wall of Receipts” — proudly tallying up all those billions in savings, right? About that. The Times went through the 40 largest items on DOGE’s claimed savings list:
In DOGE’s published list of canceled contracts and grants, for instance, the 13 largest were all incorrect.
At the top were two Defense Department contracts, one for information technology, one for aircraft maintenance. Mr. Musk’s group listed them as “terminations,” and said their demise had saved taxpayers $7.9 billion. That was not true. The contracts are still alive and well, and those savings were an accounting mirage.
Together, those two false entries were bigger than 25,000 of DOGE’s other claims combined.
Of the 40 biggest claims on DOGE’s list, The Times found only 12 that appeared accurate — reflecting real reductions in what the government had committed to spend.
Two fake line items on a spreadsheet claimed more “savings” than 25,000 other entries combined. Of the 40 biggest claims, 28 were wrong. The 13 biggest were all wrong. The very first day the “Wall of Receipts” went live, its largest claim was an $8 billion Department of Homeland Security contract that was off by a factor of 1,000 — the contract was actually worth $8 million, as many folks reported at the time. That’s the kind of error that would get you fired from an introductory accounting course, and these were the people supposedly bringing precision and transparency to the federal government.
The accounting trick DOGE relied on most heavily is worth understanding, because it reveals whether this was mere incompetence or something more deliberate. The Times explains that in many cases, DOGE simply lowered the “ceiling value” of contracts — the theoretical maximum the government could spend, not what it was actually spending — and then claimed the full difference as “savings.” A defense contractor CEO explained this perfectly to stock analysts:
This summer, CACI’s chief executive, John Mengucci, told stock analysts that the change was meaningless.
“It doesn’t change a thing for this company,” he said. His company had always expected to be paid about $2 billion over the contract’s life span. And even if the contract ever did reach the ceiling, he said, the Pentagon could just raise it again.
“There’s no reduction of revenue,” Mr. Mengucci said.
Or to put it in even more understandable terms:
“Does lowering the maximum limit on your credit card save you any money?” said Travis Sharp, a senior fellow at the Center for Strategic and Budgetary Assessments, which studies federal spending. “No, it does not.”
The core of DOGE’s operations was to manufacture pretend statistics so that Musk and friends could claim savings that weren’t real. It was how DOGE manufactured the appearance of progress while delivering essentially nothing. After DOGE initially claimed $55 billion in savings, the website’s own documentation only supported $16.5 billion. Media analysis then showed half of that was a single data entry error (that $8 billion instead of $8 million). A Politico analysis found DOGE had cut only $1.4 billion in actual spending — and even that money couldn’t reduce the deficit because it would be returned to agencies that were legally obligated to spend it. More than one-third of DOGE’s contract cancellations yielded no monetary savings at all.
The Garcia report traces a trajectory that any honest observer should find embarrassing:
During the 2024 presidential campaign, Elon Musk claimed he could reduce the federal deficit by eliminating “at least $2 trillion” in federal spending, promising the destruction of the American social safety net. He began walking back these goals after President Trump’s election victory. In early 2025, Mr. Musk appeared on a variety of conservative-leaning podcasts and media outlets baselessly claiming that fake or stolen Social Security numbers led to more than $500 billion in fraud. Media analysis classified Mr. Musk’s claims about waste and fraud in the federal government as lacking evidence or misleading, saying that he misconstrued Government Accountability Office (GAO) reports or lacked basic understanding of the contracts in question.
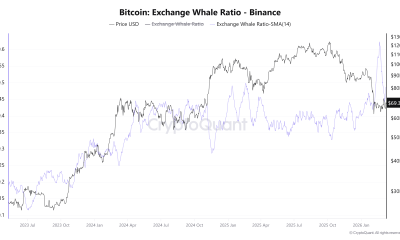
So: $2 trillion, then $1 trillion, then $55 billion claimed, then $16.5 billion documented, then $1.4 billion confirmed, then spending went up anyway. That’s quite a trajectory for something that was sold as bringing Silicon Valley precision and efficiency to government.
Okay, fine — DOGE didn’t save much money. But did it at least make the government run better? Did it cut red tape, speed things up, make services less awful?
No. It did the opposite. And this is the part that should really bother anyone who genuinely wanted government reform.
The Garcia report documents in excruciating detail how DOGE’s “efficiency” measures actually added bureaucratic layers:
In one example, a State Department employee described a new requirement for a 250-word essay, extra forms, and days of work and approvals needed to hire a vendor for an embassy event, which previously would have taken a single day. In another, a NASA employee was required to write several detailed paragraphs justifying a purchase of fastening bolts. FDA employees have stated that DOGE requirements have caused significant delays in routine food monitoring tests for items like exposure to heavy metals because spending for every step—from purchasing lab supplies to paying to ship samples between labs—now requires separate department-level approval.
Much efficient. Very savings.
As one federal employee stated:
“It is becoming increasingly difficult to continue to work, which I fear is the point.”
Meanwhile, the services Americans actually rely on got measurably worse:
At the Social Security Administration (SSA), wait times for a callback ballooned to as high as two and a half hours for assistance between January and March 2025. Americans attempting to access the SSA website for assistance frequently found the webpage down or unresponsive as DOGE recklessly implemented changes while cutting information technology (IT) staff. SSA eventually discarded several of the supposed fraud checks implemented by DOGE because they significantly delayed claim processing without meaningfully combatting fraud. Career employees reportedly knew that DOGE’s anti-fraud measures would make little difference but were intimidated into silence for fear of losing their jobs. DOGE also implemented a new requirement for Social Security applicants to verify their identity in person instead of over the phone if they aren’t able to do so online, while at the same time closing regional and local offices and reducing the workforce at those offices that remained. More than six million seniors have to drive nearly 50 miles round trip to reach their nearest Social Security office, more than twice the average distance an elderly person expects to drive in a day.
This was a heist dressed up as a reform — and the damage to everyday Americans wasn’t a bug.
Layoffs at the Food and Drug Administration (FDA) led to delays in clinical trials and getting new drugs to sick patients. Remaining FDA workers reported struggling to meet statutorily mandated schedules for approving both tobacco products and medical products after the Trump Administration announced 3,500 job cuts across the agency. At one point, FDA drug center leadership resorted to asking drug review staff to volunteer to work on contracting and acquisition tasks because the layoffs had eliminated the entire contracting office.
The Times talked to people on the receiving end of the small-dollar cuts that were DOGE’s actual handiwork. An organization providing counseling and rehabilitation services to torture survivors had to close its centers and stop paying 75% of its staff. A program that sent museum staff into low-income Baltimore schools to teach parents about child development was terminated by form letter because it “no longer serves the interest of the United States.” Research projects were killed at the stage where data had been collected but results hadn’t been published, rendering the government’s entire prior investment wasted. And the impact on American people was real.
Mr. Roehm said he was particularly concerned about possible suicides — around a quarter of the torture victims the group served had recently experienced suicidal ideation.
“We know for sure that survivors we are no longer able to serve are suffering,” he said.
Those dollar amounts were small, compared with DOGE’s largest claims. That is, in effect, how DOGE ultimately saved so little but still caused so much disruption. For small business and local communities, relatively modest sums had major effects.
“It’s the small numbers that hurt people,” said Lisa Shea Mundt, whose company, the Pulse of GovCon, tracks government contracts.
This is how DOGE managed to simultaneously save almost nothing and cause enormous disruption: the big-dollar claims were fake, and the real cuts targeted things that were individually small but collectively devastating to the people who depended on them.
And then there’s the corruption angle, which is where this moves from incompetence into something much uglier.
DOGE staff were embedded at nearly every executive branch agency, and many of them were associates or employees of Musk’s own companies. The conflicts of interest were staggering and barely concealed. The Garcia report details how DOGE staff were involved in firing FDA investigators responsible for oversight of Musk’s biotech company Neuralink. DOGE took aim at the Consumer Financial Protection Bureau — which just happened to be the agency that would directly oversee a mobile payments function Musk wanted to add to X. The DOGE staffer who oversaw firings at the CFPB owned approximately $365,000 in shares of companies regulated by the Bureau. Executive branch employees are generally prohibited from working on matters in which they hold a personal stake, but there’s no indication this person took any such precautions.
Elon Musk and DOGE’s active involvement in knee-capping agencies with which he has a direct conflict makes clear that Musk, DOGE, and the broader Trump Administration are focused on weakening accountability for the American people while advancing their own interests.
DOGE staff at the IRS initiated mass firing of skilled specialists responsible for auditing the complex tax filings of large corporations and the ultra-wealthy. The Congressional Budget Office has found that reductions in funding for IRS tax enforcement reduce federal revenues. So DOGE’s “efficiency” move at the IRS will likely cost the government more in uncollected taxes than it could ever have saved.
The same pattern held at the CFPB, which since 2011 had received $7.3 billion in funding but returned over $21 billion to consumers through enforcement actions — a three-fold return on investment. DOGE gutted it anyway. The IRS Direct File program — a free electronic tax filing service that 86% of users said increased their trust in the IRS and was projected to save taxpayers $11 billion once fully operational — was killed after lobbying by for-profit tax preparation companies.
And perhaps most alarming were the data security violations that I’ve written about multiple times. A whistleblower from SSA reported that DOGE operatives had accessed a database containing “the entire country’s Social Security information,” copied it to a high-risk external system, and violated a court order barring them from continued access. The DOJ later had to file “corrections” to prior testimony from senior SSA staff, admitting that DOGE employees had in fact accessed SSA’s most sensitive data and covertly signed a “Voter Data Agreement” with a political advocacy group that sought to overturn election results. And here’s one I had missed:
DOGE’s forced access to Treasury data was particularly noteworthy as a Treasury threat intelligence analysis recommended that DOGE staff “be placed under insider threat monitoring and alerting after their access to payment systems is revoked. Continued access to any payment systems by DOGE members, even ‘read only,’ may have posed the single greatest insider threat risk the Bureau of the Fiscal Service has ever faced.”
At the NLRB, a whistleblower reported that DOGE operatives sent enormous amounts of sensitive case information outside the government to unknown recipients — information that companies like Musk’s SpaceX could use to “get insights into damaging testimony, union leadership, legal strategies and internal data.” OPM’s own Inspector General found that DOGE employees flouted cybersecurity and privacy laws, and that Trump appointees at OPM overrode career civil servants’ warnings about security to force implementation of DOGE’s systems, which may have resulted in a massive national security threat:
Experts have shown evidence raising concerns of potential Russian and Chinese access to OPM servers shortly after DOGE created the government-wide email infrastructure. Separately, information received by Committee Democratic staff indicated that DOGE employees lowered all firewall protections at OPM to enable the exfiltration of data for use outside of a government environment.
Yikes.
And while they were gutting agencies that protect Americans, they also gutted the agencies actually responsible for catching waste, fraud, and abuse. Offices of Inspectors General — the very watchdogs whose mission aligns with what DOGE claimed to be doing — were starved of resources. One OIG lost 20% of its staff and was operating with “the fewest number of auditors in decades.” The DOJ’s Public Integrity Section, which oversees prosecutions of politicians accused of corruption, was purged of all but a fraction of its former employees.
The Garcia report’s conclusion is perhaps the most honest assessment of the whole debacle:
Many analyses have referred to the DOGE disaster as a failure, and DOGE did indeed fail at its stated mission of meaningfully reducing spending and increasing government efficiency. But in the Trump Administration’s vindictive, ideologically motivated, and pointless quest to break the federal government, drive out talented and committed public servants, and make flashy promises of cutting fraud while enriching themselves and their wealthy donors, DOGE was a resounding success.
Now, the Garcia report is a Democratic minority report, and the most committed DOGE defenders will dismiss it on those grounds alone. But the most devastating evidence comes from DOGE’s own website — which kept quietly deleting incorrect entries — from the Times’ independent analysis, from a defense contractor’s CEO telling his shareholders the “savings” were meaningless, from the GAO finding multiple violations of the Impoundment Control Act, from OPM’s own Inspector General, and from the DOJ having to file corrections to its own court filings.
You don’t need to trust a single Democratic politician to see what happened here. You just need to look at the numbers.
Oh, and yes: Musk himself admitted in a podcast interview with MAGA influencer and former DOGE employee Katie Miller (wife of Stephen) in December that DOGE had fallen short and said that if he could go back in time, he wouldn’t do it again, preferring instead to have “worked on my companies.” The man who was going to supposedly save the republic from government bloat decided his actual companies were more worth his time. Musk’s public admission probably shouldn’t carry too much weight either way — he knows DOGE was publicly perceived as a failure and he’s distancing himself — but it is a fitting coda.
This whole thing was billed not just by MAGA faithful, but also by many in the media, as an expected triumph of private sector brilliance over government incompetence. What it actually demonstrated is that when you hand the keys to people who don’t understand how government works, don’t respect the people who do, and have massive personal financial conflicts of interest, you get chaos, corruption, and a bigger bill for taxpayers. The people who were making government work better — the original U.S. Digital Service employees who were building more efficient systems and better websites — got fired and replaced with Musk acolytes who couldn’t tell the difference between a contract ceiling and actual spending.
The MAGA world continues to pretend DOGE was a ruthless cost-cutting machine. The receipts say otherwise: it failed in every direction except enriching corporations connected to the administration. It was a looting operation dressed up as reform.
Filed Under: abuse, doge, efficiency, elon musk, fraud, government spending, waste






















































You must be logged in to post a comment Login