Tech
Nvidia’s agentic AI stack is the first major platform to ship with security at launch, but governance gaps remain


For the first time on a major AI platform release, security shipped at launch — not bolted on 18 months later. At Nvidia GTC this week, five security vendors announced protection for Nvidia’s agentic AI stack, four with active deployments, one with validated early integration.
The timing reflects how fast the threat has moved: 48% of cybersecurity professionals rank agentic AI as the top attack vector heading into 2026. Only 29% of organizations feel fully ready to deploy these technologies securely. Machine identities outnumber human employees 82 to 1 in the average enterprise. And IBM’s 2026 X-Force Threat Intelligence Index documented a 44% surge in attacks exploiting public-facing applications, accelerated by AI-enabled vulnerability scanning.
Nvidia CEO Jensen Huang made the case from the GTC keynote stage on Monday: “Agentic systems in the corporate network can access sensitive information, execute code, and communicate externally. Obviously, this can’t possibly be allowed.”
Nvidia defined a unified threat model designed to flex and adapt for the unique strengths of five different vendors. Nvidia also names Google, Microsoft Security and TrendAI as Nvidia OpenShell security collaborators. This article maps the five vendors with embargoed GTC announcements and verifiable deployment commitments on record, an analyst-synthesized reference architecture, not Nvidia’s official canonical stack.
No single vendor covers all five governance layers. Security leaders can evaluate CrowdStrike for agent decisions and identity, Palo Alto Networks for cloud runtime, JFrog for supply chain provenance, Cisco for prompt-layer inspection, and WWT for pre-production validation. The audit matrix below maps who covers what. Three or more unanswered vendor questions mean ungoverned agents in production.
The five-layer governance framework
This framework draws from the five vendor announcements and the OWASP Agentic Top 10. The left column is the governance layer. The right column is the question every security leader’s vendor should answer. If they can’t answer it, that layer is ungoverned.
|
Governance Layer |
What To Deploy |
Risk If Not |
Vendor Question |
Who Maps Here |
|
Agent Decisions |
Real-time guardrails on every prompt, response, and action |
Poisoned input triggers privileged action |
Detect state drift across sessions? |
CrowdStrike Falcon AIDR, Cisco AI Defense [runtime enforcement] |
|
Local Execution |
Behavioral monitoring for on-device agents |
Local agent runs unprotected |
Agent baselines beyond process monitoring? |
CrowdStrike Falcon Endpoint [runtime enforcement]; WWT ARMOR [pre-prod validation] |
|
Cloud Ops |
Runtime enforcement across cloud deployments |
Agent-to-agent privilege escalation |
Trust policies between agents? |
CrowdStrike Falcon Cloud Security [runtime enforcement]; Palo Alto Prisma AIRS [AI Factory validated design] |
|
Identity |
Scoped privileges per agent identity |
Inherited creds; delegation compounds |
Privilege inheritance in delegation? |
CrowdStrike Falcon Identity [runtime enforcement]; Palo Alto Networks/CyberArk [identity governance platform] |
|
Supply Chain |
Model scanning + provenance before deploy |
Compromised model hits production |
Provenance from registry to runtime? |
JFrog Agent Skills Registry [pre-deployment]; CrowdStrike Falcon |
Five-layer governance audit matrix. Three or more unanswered vendor questions indicate ungoverned agents in production. [runtime enforcement] = inline controls active during agent execution. [pre-deployment] = controls applied before artifacts reach runtime. [pre-prod validation] = proving-ground testing before production rollout. [AI Factory validated design] = Nvidia reference architecture integration, not OpenShell-launch coupling.
CrowdStrike’s Falcon platform embeds at four distinct enforcement points in the Nvidia OpenShell runtime: AIDR at the prompt-response-action layer, Falcon Endpoint on DGX Spark and DGX Station hosts, Falcon Cloud Security across AI-Q Blueprint deployments, and Falcon Identity for agent privilege boundaries. Palo Alto Networks enforces at the BlueField DPU hardware layer within Nvidia’s AI Factory validated design. JFrog governs the artifact supply chain from the registry through signing. WWT validates the full stack pre-production in a live environment. Cisco runs an independent guardrail at the prompt layer.
CrowdStrike and Nvidia are also building what they call intent-aware controls. That phrase matters. An agent constrained to certain data is access-controlled. An agent whose planning loop is monitored for behavioral drift is governed. Those are different security postures, and the gap between them is where the 4% error rate at 5x speed becomes dangerous.
Why the blast radius math changed
Daniel Bernard, CrowdStrike’s chief business officer, told VentureBeat in an exclusive interview what the blast radius of a compromised AI agent looks like compared to a compromised human credential.
“Anything we could think about from a blast radius before is unbounded,” Bernard said. “The human attacker needs to sleep a couple of hours a day. In the agentic world, there’s no such thing as a workday. It’s work-always.”
That framing tracks with architectural reality. A human insider with stolen credentials works within biological limits: typing speed, attention span, a schedule. An AI agent with inherited credentials operates at compute speed across every API, database, and downstream agent it can reach. No fatigue. No shift change. CrowdStrike’s 2026 Global Threat Report puts the fastest observed eCrime breakout at 27 seconds and average breakout times at 29 minutes. An agentic adversary doesn’t have an average. It runs until you stop it.
When VentureBeat asked Bernard about the 96% accuracy number and what happens in the 4%, his answer was operational, not promotional: “Having the right kill switches and fail-safes so that if the wrong thing is decided, you’re able to quickly get to the right thing.” The implication is worth sitting on. 96% accuracy at 5x speed means the errors that get through arrive five times faster than they used to. The oversight architecture has to match the detection speed. Most SOCs are not designed for that.
Bernard’s broader prescription: “The opportunity for customers is to transform their SOCs from history museums into autonomous fighting machines.” Walk into the average enterprise SOC and inventory what’s running there. He’s not wrong.
On analyst oversight when agents get it wrong, Bernard drew the governance line: “We want to keep not only agents in the loop, but also humans in the loop of the actions that the SOC is taking when that variance in what normal is realized. We’re on the same team.”
The full vendor stack
Each of the five vendors occupies a different enforcement point the other four do not. CrowdStrike’s architectural depth in the matrix reflects four announced OpenShell integration points; security leaders should weigh all five based on their existing tooling and threat model.
Cisco shipped Secure AI Factory with AI Defense, extending Hybrid Mesh Firewall enforcement to Nvidia BlueField DPUs and adding AI Defense guardrails to the OpenShell runtime. In multi-vendor deployments, Cisco AI Defense and Falcon AIDR run as parallel guardrails: AIDR enforcing inside the OpenShell sandbox, AI Defense enforcing at the network perimeter. A poisoned prompt that evades one still hits the other.
Palo Alto Networks runs Prisma AIRS on Nvidia BlueField DPUs as part of the Nvidia AI Factory validated design, offloading inspection to the data processing unit at the network hardware layer, below the hypervisor and outside the host OS kernel. This integration is best understood as a validated reference architecture pairing rather than a tight OpenShell runtime coupling. Palo Alto intercepts east-west agent traffic on the wire; CrowdStrike monitors agent process behavior inside the runtime. Same cloud runtime row, different integration model and maturity stage.
JFrog announced the Agent Skills Registry, a system of record for MCP servers, models, agent skills, and agentic binary assets within Nvidia’s AI-Q architecture. Early integration with Nvidia has been validated, with full OpenShell support in active development. JFrog Artifactory will serve as a governed registry for AI skills, scanning, verifying, and signing every skill before agents can adopt it. This is the only pre-deployment enforcement point in the stack. As Chief Strategy Officer Gal Marder put it: “Just as a malicious software package can compromise an application, an unvetted skill can guide an agent to perform harmful actions.”
Worldwide Technology launched a Securing AI Lab inside its Advanced Technology Center, built on Nvidia AI factories and the Falcon platform. WWT’s vendor-agnostic ARMOR framework is a pre-production validation and proving-ground capability, not an inline runtime control. It validates how the integrated stack behaves in a live AI factory environment before any agent touches production data, surfacing control interactions, failure modes, and policy conflicts before they become incidents.
Three MDR numbers: what they actually measure
On the MDR side, CrowdStrike fine-tuned Nvidia Nemotron models on first-party threat data and operational SOC data from Falcon Complete engagements. Internal benchmarks show 5x faster investigations, 3x higher triage accuracy in high-confidence benign classification, and 96% accuracy in generating investigation queries within Falcon LogScale. Kroll, a global risk advisory and managed security firm that runs Falcon Complete as its MDR backbone, confirmed the results in production.
Because Kroll operates Falcon Complete as its core MDR platform rather than as a neutral third-party evaluator, their validation is operationally meaningful but not independent in the audit sense. Industry-wide third-party benchmarks for agentic SOC accuracy do not yet exist. Treat reported numbers as indicative, not audited.
The 5x investigation speed compares average agentic investigation time (8.5 minutes) against the longest observed human investigation in CrowdStrike’s internal testing: a ceiling, not a mean. The 3x triage accuracy measures one internal model against another. The 96% accuracy applies specifically to generating Falcon LogScale investigation queries via natural language, not to overall threat detection or alert classification.
JFrog’s Agent Skills Registry operates beneath all four CrowdStrike enforcement layers, scanning, signing, and governing every model and skill before any agent can adopt it — with early Nvidia integration validated and full OpenShell support in active development.
Six enterprises are already in deployment
EY selected the CrowdStrike-Nvidia stack to power Agentic SOC services for global enterprises. Nebius ships with Falcon integrated into its AI cloud from day one. CoreWeave CISO Jim Higgins signed off on the Blueprint. Mondelēz North America Regional CISO Emmett Koen said the capability lets his team “focus on higher-value response and decision-making.”
MGM Resorts International CISO Bryan Green endorsed WWT’s validated testing environments, saying enterprises need “validated environments that embed protection from the start.” These range from vendor selection and platform validation to production integration. The signal is converging across buyer types, not uniform at-scale deployment.
What the five-vendor stack does not cover
The governance framework above represents real progress. It also has three holes that every security leader deploying agentic AI will eventually hit. No vendor at GTC closed any of them. Knowing where they are is as important as knowing what shipped.
-
Agent-to-agent trust. When agents delegate to other agents, credentials compound. The OWASP Top 10 for Agentic Applications lists tool call hijacking and orchestrator manipulation as top-tier risks. Independent research from BlueRock Security scanning over 7,000 MCP servers found 36.7% contain vulnerabilities. An arXiv preprint study across 847 scenarios found a 23 to 41% increase in attack success rates in MCP integrations versus non-MCP. No vendor at GTC demonstrated a complete trust policy framework for agent-to-agent delegation. This is the layer where the 82:1 identity ratio becomes a governance crisis, not just an inventory problem.
-
Memory integrity. Agents with persistent memory create an attack surface that stateless LLM deployments do not have. Poison an agent’s long-term memory once. Influence its decisions weeks later. The OWASP Agentic Top 10 flags this explicitly. CrowdStrike’s intent-aware controls are the closest architectural response announced at GTC. Implementation details remain forward-looking.
-
Registry-to-runtime provenance. JFrog’s Agent Skills Registry addresses the registry side of this problem. The gap that remains is the last mile: end-to-end provenance requires proving the model executing in production is the exact artifact scanned and signed in the registry. That cryptographic continuity from registry to runtime is still an engineering problem, not a solved capability.
What running five vendors actually costs
The governance matrix is a coverage map, not an implementation plan. Running five vendors across five enforcement layers introduces real operational overhead that the GTC announcements did not address. Someone has to own policy orchestration: deciding which vendor’s guardrail wins when AIDR and AI Defense return conflicting verdicts on the same prompt. Someone has to normalize telemetry across Falcon LogScale, Prisma AIRS, and JFrog Artifactory into a single incident workflow. And someone has to manage change control when one vendor ships a runtime update that shifts how another vendor’s enforcement layer behaves.
A realistic phased rollout looks like this: start with the supply chain layer (JFrog), because it operates pre-deployment and has no runtime dependencies on the other four. Add identity governance (Falcon Identity) second, because scoped agent credentials limit blast radius before you instrument the runtime. Then instrument the agent decision layer (Falcon AIDR or Cisco AI Defense, depending on your existing vendor footprint), then cloud runtime, then local execution. Running all five simultaneously from day one is an integration project, not a configuration task. Budget for it accordingly.
What to do before your next board meeting
Here is what every CISO should be able to say after running the framework above: “We have audited every autonomous agent against five governance layers. Here is what’s in place, and here are the five questions we are holding vendors to.” If you cannot say that today, the issue is not that you are behind schedule. The issue is that no schedule existed. Five vendors just shipped the architectural scaffolding for one.
Do four things before your next board meeting:
-
Run the five-layer audit. Pull every autonomous agent your organization has in production or staging. Map each one against the five governance rows above. Mark which vendor questions you can answer and which you cannot.
-
Count the unanswered questions. Three or more means ungoverned agents in production. That is your board number, not a backlog item.
-
Pressure-test the three open gaps. Ask your vendors, explicitly: How do you handle agent-to-agent trust across MCP delegation chains? How do you detect memory poisoning in persistent agent stores? Can you show a cryptographic binding between the registry scan and the runtime load? None of the five vendors at GTC has a complete answer. That is not an accusation. It is where the next year of agentic security gets built.
-
Establish the oversight model before you scale. Bernard put it plainly: keep agents and humans in the loop. 96% accuracy at 5x speed means errors arrive faster than any SOC designed for human-speed detection can catch them. The kill switches and fail-safes have to be in place before the agents run at scale, not after the first missed breach.
The scaffolding is necessary. It is not sufficient. Whether it changes your posture depends on whether you treat the five-layer framework as a working instrument or skip past it in the vendor deck.
Tech
Mistral bets on ‘build-your-own AI’ as it takes on OpenAI, Anthropic in the enterprise

Most enterprise AI projects fail not because companies lack the technology, but because the models they’re using don’t understand their business. The models are often trained on the internet, rather than decades of internal documents, workflows, and institutional knowledge.
That gap is where Mistral, the French AI startup, sees opportunity. On Tuesday, the company announced Mistral Forge, a platform that lets enterprises build custom models trained on their own data. Mistral announced the platform at Nvidia GTC, Nvidia’s annual technology conference, which this year is focused heavily on AI and agentic models for enterprise.
It’s a pointed move for Mistral, a company that has built its business on corporate clients while rivals OpenAI and Anthropic have soared ahead in terms of consumer adoption. CEO Arthur Mensch says Mistral’s laser focus on the enterprise is working: the company is on track to surpass $1 billion in annual recurring revenue this year.
A big part of doubling down on enterprise is giving companies more control over their data and their AI systems, Mistral says.
“What Forge does is it lets enterprises and governments customize AI models for their specific needs,” Elisa Salamanca, Mistral’s head of product, told TechCrunch.
Several companies in the enterprise AI space already claim to offer similar capabilities, but most focus on fine-tuning existing models or layering proprietary data on top through techniques like retrieval augmented generation (RAG). These approaches don’t fundamentally retrain models; instead, they adapt or query them at runtime using company data.
Mistral, by contrast, says it is enabling companies to train models from scratch. In theory, this could address some of the limitations of more common approaches — for example, better handling of non-English or highly domain-specific data, and greater control over model behavior. It could also allow companies to train agentic systems using reinforcement learning and reduce reliance on third-party model providers, avoiding risks like model changes or deprecation.
Techcrunch event
San Francisco, CA
|
October 13-15, 2026
Forge customers can build their custom models using Mistral’s wide library of open-weight AI models, which includes small models such as the recently introduced Mistral Small 4. According to Mistral co-founder and chief technologist, Timothée Lacroix, Forge can help unlock more value out of its existing models.
“The trade-offs that we make when we build smaller models is that they just cannot be as good on every topic as their larger counterparts, and so the ability to customize them lets us pick what we emphasize and what we drop,” Lacroix said.
Mistral advises on which models and infrastructure to use, but both decisions stay with the customer, Lacroix said. And for teams that need more than guidance, Forge comes with Mistral’s team of forward-deployed engineers who embed directly with customers to surface the right data and adapt to their needs — a model borrowed from the likes of IBM and Palantir.
“As a product, Forge already comes with all the tooling and infrastructure so you can generate synthetic data pipelines,” Salamanca said. “But understanding how to build the right evals and making sure that you have the right amount of data is something that enterprises usually don’t have the right expertise for, and that’s what the FDEs bring to the table.”
Mistral has already made Forge available to partners including Ericsson, the European Space Agency, Italian consulting company Reply, and Singapore’s DSO and HTX. Early adopters also include ASML, the Dutch chipmaker that led Mistral’s Series C round last September at a €11.7 billion valuation (approximately $13.8 billion at the time).
These partnerships are emblematic of what Mistral expects Forge’s main use cases to be. According to Mistral’s chief revenue officer Marjorie Janiewicz, these include governments who need to tailor models for their language and culture; financial players with high compliance requirements; manufacturers with customization needs; and tech companies that need to tune models to their code base.
Tech
Kit Becomes Firefox’s First Mascot and Ready Companion
Kit, Firefox’s first mascot, has just made his debut, thanks to Mozilla, who combined fox and red panda features with some searing flame elements to create a one-of-a-kind creature that sticks out. Kit’s tail constantly seems like it’s on the move, even when he’s just relaxing, since his body language, posture, and eyes all appear to be working together to nail the mood.
Illustrator Marco Palmieri created the final design, starting with some pencil drawings to get a feel for the ideas and ensure they were strong before going on to other tools. Design agency JKR then stepped in and collaborated with Mozilla to take the project to the next level by delving into what makes Firefox tick, including the logo colors and the fox itself.
Apple 2026 MacBook Neo 13-inch Laptop with A18 Pro chip: Built for AI and Apple Intelligence, Liquid…
- HELLO, MACBOOK NEO — Ready for whatever your day brings, MacBook Neo flies through everyday tasks and apps. Choose from four stunning colors in a…
- THE MOST COLORFUL MACBOOK LINEUP EVER — Choose from Silver, Blush, Citrus, or Indigo — each with a color-coordinated keyboard to complete the…
- POWER FOR EVERYDAY TASKS — Ready the moment you open it, MacBook Neo with the A18 Pro chip delivers the performance and AI capabilities you need to…
According to Amy Bebbington of Mozilla, Kit is the browser’s BFF for the internet era, as it serves as a gentle reminder to users that Firefox has their back. This comes at a time when the web is undergoing significant changes and people are becoming increasingly concerned about what is happening with their data and trust. Firefox is responding by not disclosing users’ personal information and allowing them to opt in or out of artificial intelligence.
Kit is also present in quiet moments, such as when you first log in, try something new, or do something nice while browsing, and you can even use him as a wallpaper for new browser tabs under the customization menu. You may also see him on the official website, social media, and during meetups. Overall, these subtle touches make the sign-in process feel like reconnecting with an old friend. Kit is quite understated, but he provides just the right amount of personality to remind you that the browser is only there to help (not get in the way).
Tech
Anker’s Upcoming Liberty 5 Pro Max Buds Will Have an AI Voice Recorder in Their Charging Case

Anker earbuds and headphones may not have the premium status of Apple, Bose and Sony, but the brand’s value-priced products have a loyal following. Anker aficionados have been waiting for the company to release the Pro version of its $100 Soundcore Liberty 5 earbuds.
According to NotebookCheck, via leaker AnkerInsider, whose X account appears suspended, the release is near. Two versions of Anker’s new flagship earbuds are due to arrive in the coming months: The Liberty 5 Pro and Liberty 5 Pro Max. Both will feature a new AI chip called the Anker Thus to power the buds.
Read more: Best wireless earbuds of 2026
The new models don’t look anything like the current Liberty 5 buds, which have a traditional stem design. Both new Pro models will feature upgraded noise canceling (Anker’s new Adaptive ANC 4.0), Bluetooth 6.1, an IP55 dust- and water-resistant rating, Dolby Atmos spatial audio, Bluetooth multipoint and an AI-powered audio upscaling feature.
While both the Liberty 5 Pro and Liberty Pro Max have a touchscreen built into their cases, the Max’s case also doubles as a voice recorder with built-in microphones. The recorder will reportedly be able to recognize your voice thanks to voiceprint recognition.
Anker has apparently developed its own AI chip for its flagship earbuds.
The upcoming buds are expected to be officially announced in late May, with the Liberty 5 Pro to be priced at $170, and the Liberty 5 Pro Max retailing for $230 (the Max already have a shell of listing on Best Buy that notes the voice recorder). Both have a battery life of around 6.5 hours with noise cancellation turned on.
AI voice recorders have been proliferating in recent months (you might have seen an ad for one on Facebook or Instagram). Anker is shipping its Soundcore Work coin-sized wearable Al note take/voice recorder for $129 with a $39-off coupon code. Presumably, some of the same technology found in the wearable recorder will make its way over to the Liberty 5 Pro Max.
The Liberty 5 Pro Max won’t be the first pair of earbuds to have a microphone in their case. Nothing’s Ear (3) flagship earbuds have a Super Mic in their case, which had me talking to my hand when making calls. It’s a clear sign that as earbud performance plateaus, brands are getting creative with extra features to help their products stand out from the pack.
Talking to the Nothing Ear (3) case while making a call in the streets of New York. More earbuds cases appear set to have built-in microphones.
Tech
Apple's latest Background Security Improvement targets a WebKit flaw
A Background Security Improvement in iOS 26.3.1 fixes a WebKit issue in Safari that could break one of the web’s most important safety rules.
Apple has fixed a WebKit bug for Safari and other browsers
Apple released a Background Security Improvement on March 17 for iOS 26.3.1, iPadOS 26.3.1, macOS 26.3.1, and macOS 26.3.2. The update fixes a WebKit flaw that could let a malicious website bypass a key browser security rule.
The company said the issue was caused by a cross-origin problem in the Navigation API and assigned it CVE-2026-20643. Apple addressed the flaw by improving input validation to stop harmful web content from breaking the browser’s protections.
Continue Reading on AppleInsider | Discuss on our Forums
Tech
Australian tea brand T2 Tea to shutter all Singapore stores
Tech
Part Three trailer introduces Robert Pattinson’s villainous new character

It’s only been two years since Dune: Part Two but we already have a trailer for the third installment. The appropriately-named Dune: Part Three is an adaptation of Frank Herbert’s Dune Messiah book from 1969.
Just like the book, the latest film takes place a number of years after Dune: Part Two. “If the first movie was contemplation, a boy exploring a new world, and the second one is a war movie, this one is a thriller,” . “It is action-packed and tense. More muscular.”
Despite the time jump, most primary actors are returning. This includes Timothée Chalamet, Zendaya and Javier Bardem. Anya Taylor-Joy, who briefly appeared in the second film, is also coming back. The same goes for Jason Momoa, despite his Duncan Idaho character dying in the first film. Book readers will likely understand what that means.
The trailer also highlights the antagonist Scytale, as portrayed by Robert Pattinson. He should be a more nuanced villain than Baron Harkonnen, though that’s not exactly a high bar.
The release date is coming up fast. Dune: Part Three hits theaters on December 18. That’s this year. Villeneuve had intended to take a break after making the second one to focus on a smaller and more personal film, but said that he kept “waking in the middle of the night” with potential images from the third installment.
Tech
Startup proposes USB drives as a modern replacement for DVDs and Blu-rays


Video StoreAge is a new company focused on creating physical releases of indie films. The startup aims to take a more authorial approach to distribution, using a patented encrypted USB drive to share its curated titles. Its ultimate goal is to disrupt algorithm-driven distribution in favor of communities and grassroots…
Read Entire Article
Source link
Tech
NVIDIA’s NemoClaw Gives Personal AI Agents the Safety Companies Need
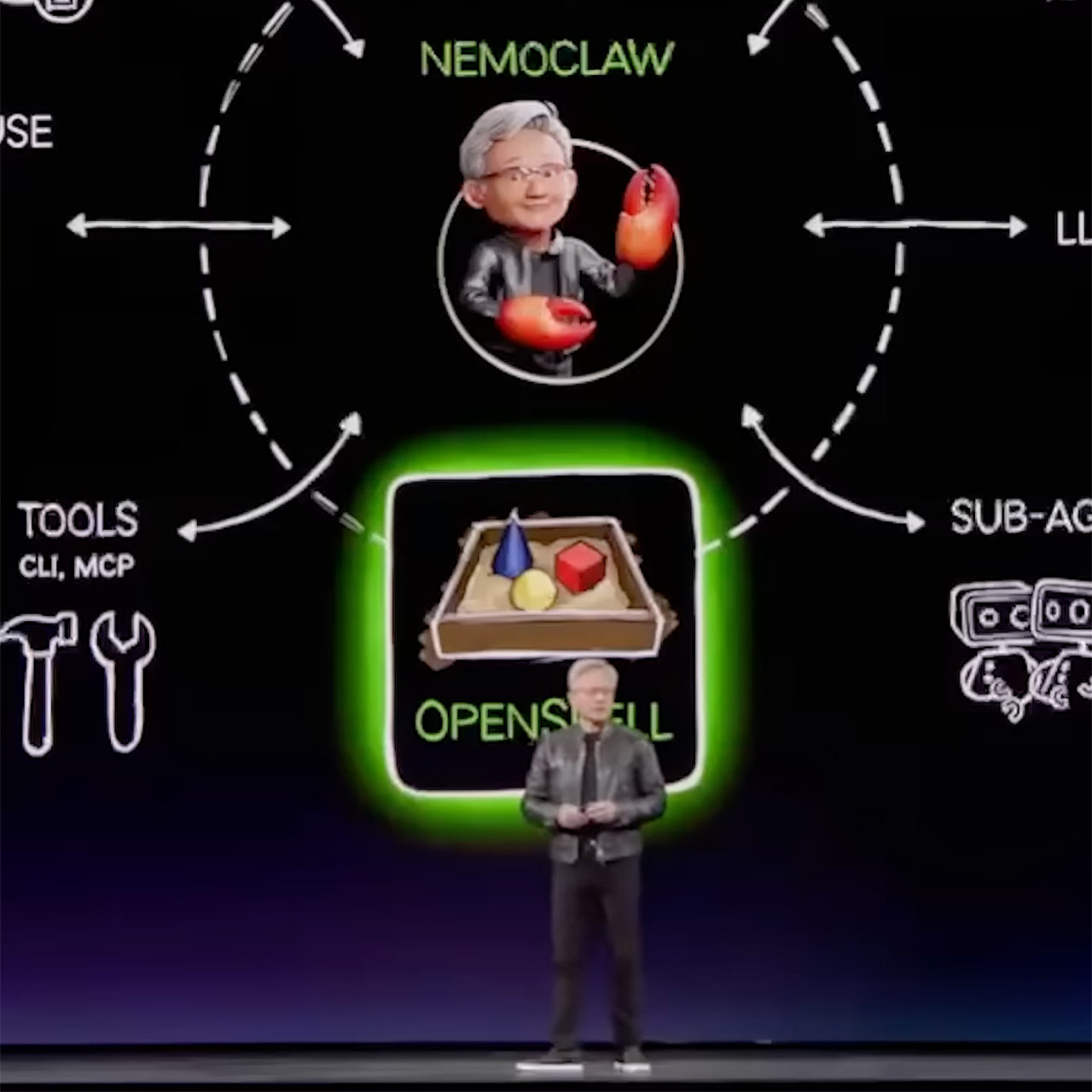
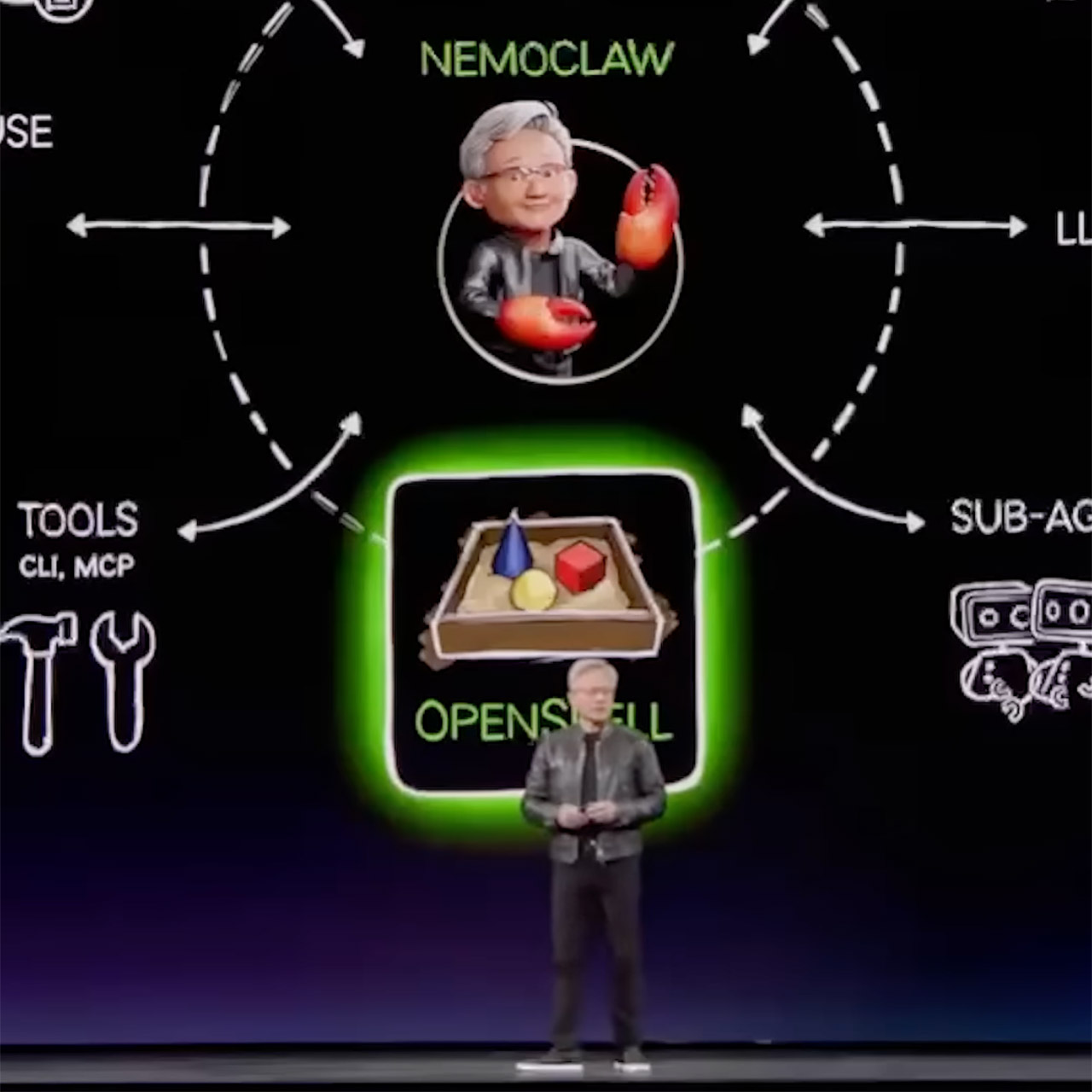
OpenClaw took the tech industry by surprise earlier this year when an Austrian engineer created the first version in roughly an hour. This small project swept through the community like wildfire as the most open-source endeavor on record, allowing anyone to set up a personal AI agent to operate directly on their own PC and accomplish tasks like organizing files or pounding out code without sending any data off to who knows where. At GTC, NVIDIA introduced NemoClaw, a software add-on for OpenClaw that can be installed with a single command. This new layer includes the security features and privacy controls that transform these agents from fun little experiments to useful business solutions.
NemoClaw is simple to integrate into your existing setup since it introduces OpenShell, a runtime that isolates each agent in its own small bubble. Then you can create rules in plain text files that specify which folders the agent may browse, which networks it can connect to, and which external services it can access. Everything else, and we mean everything, is off limits, and every step they make leaves a clear paper trail for you to follow.
Plaud Note Pro AI Voice Recorder, Transcribe & Summarize with AI, App Control, Note Taker for Meetings…
- AI-POWERED TRANSCRIPTION & MULTI-DIMENSIONAL SUMMARIES: Plaud Note Pro is your professional voice transcriber, delivering high-accuracy transcription…
- ENHANCED CONTEXT WITH MULTIMODAL INPUT: Capture audio, type notes, add images, and press to highlight key moments for richer context. During…
- CHAT WITH YOUR RECORDINGS USING “ASK Plaud”: Unlock deeper insights with this interactive AI. Ask questions, extract key points, draft emails, and get…
NVIDIA is marrying this with some of their own open models known as Nemotron, which run locally on whatever hardware is available. You’re talking everything from RTX-powered laptops to entire workstations and dedicated AI systems. When you need a little more horsepower, you can utilize a privacy router to connect to more powerful cloud models while keeping all of your sensitive information in-house. The end result is a framework that allows your agents to work in a mix of local and remote resources while maintaining tight boundaries.
Companies are already putting these components to use in real-world situations. Cisco runs agents that detect security flaws, verify databases, map affected devices, and create a thorough remediation plan, all of which must be checked against the rules in real time. Box uses the same framework to handle invoices and contracts, using abilities that work well with existing access levels. NVIDIA has also partnered with Salesforce, CrowdStrike, and a few more large brands to achieve the same level of control across all of their technologies. OpenClaw agents run 24 hours a day, seven days a week on personal computers, professional workstations, and servers without interfering with anything else. If you have dedicated hardware, you can keep them up and running for hours, if not days, while they work.
It is currently available as an early preview through official sources, such as on Github. Users can begin testing right away, although NVIDIA says some rough edges must be ironed out before they are formally put into production. Developers have complete access to the toolkit, which includes sample models, runtimes, and guidance for creating their own agents. Jensen Huang referred to OpenClaw as the operating system for personal AI, indicating a trend toward software that can be instructed to do things. Peter Steinberger, the original creator of OpenClaw, sees this combination as a method for users to design and run their own secure assistants.
Tech
Polymer Blend Capacitor Packs Four Times More Energy


As electronics demand higher energy density, one component has proved challenging to shrink: the capacitor. Making a smaller capacitor usually requires thinning the dielectric layer or electrode surface area, which has often resulted in a reduction of power. A new polymer material could help change that.
In a study published 18 February in Nature, a Pennsylvania State University-led team reported a capacitor crafted from a polymer blend that can operate at temperatures up to 250 °C while storing roughly four times as much energy as conventional polymer capacitors. Today’s advanced polymer capacitors typically function only up to about 100 °C, meaning engineers often rely on bulky cooling systems in high-power electronics. The research team has filed a patent for the polymer capacitors and plans to bring them to market.
Capacitors deliver rapid bursts of energy and stabilize voltage in circuits, making them essential in applications ranging from electric vehicles and aerospace electronics to power-grid infrastructure and AI data centers. Yet while transistors have steadily shrunk with advances in semiconductor manufacturing, passive components such as capacitors and inductors have not scaled at the same pace.
“Capacitors can account for 30 to 40 percent of the volume in some power electronics systems,” says Qiming Zhang, an electrical engineering researcher at Penn State and study author, explaining why it’s important to make smaller capacitors.
A plastics blend more powerful than its parts
The research team combined two commercially available engineered plastics: polyetherimide (PEI), originally developed by General Electric and widely used in industrial equipment, and PBPDA, known for strong heat resistance and electrical insulation. When processed together under controlled conditions, the polymers self-assemble into nanoscale structures that form thin dielectric films inside capacitors. Those structures help suppress electrical leakage while allowing the material to polarize strongly in an electric field, allowing greater energy storage.
The resulting material exhibits an unusually high dielectric constant—a measure of how much electrical energy a material can store. Most polymer dielectrics have values around four, but the blended polymer dielectric in the new work had a value of 13.5.
“If you look at the literature up to now, no one has reached this level of dielectric constant in this type of polymer system,” Zhang says. “Putting two commonly used polymers together and seeing this kind of performance was a surprise to many people.”
Because the material can remain operational even at elevated temperatures—such as those from extreme environmental heat or hot spots in densely built components—capacitors built from this polymer could potentially store the same amount of energy in a smaller package.
“With this material, you can make the same device using about [one-fourth as much] material,” Zhang says. “Because the polymers themselves are inexpensive, the cost does not increase. At the same time, the component can become smaller and lighter.”
How the polymer mix improves capacitors
The researchers’ finding is “a big advancement,” says Alamgir Karim, a polymer research director at the University of Houston who was not involved in the Penn State development. “Normally when you mix polymers, you don’t expect the dielectric constant to increase.”
Karim says the effect likely arises from nanoscale interfaces created when the polymers partially separate. “At about a 50–50 mixture, the polymers don’t fully mix and instead create a very large interfacial area,” he says. “Those interfaces may be where the unusual electrical behavior comes from.”
If the material can be produced at scale, it could help address a key bottleneck in high-power electronics. Higher-temperature capacitors could reduce cooling requirements and allow engineers to pack more power into smaller systems—an advantage for aerospace platforms, electric vehicles, the electric grid, and other high-temperature environments.
But translating the concept from laboratory methods to commercial manufacturing may present challenges, says Zongliang Xie, a postdoctoral researcher at the Lawrence Berkeley National Laboratory. The Penn State team is now producing small dielectric films, but industrial capacitor manufacturing typically requires continuous rolls of material that can extend for kilometers.
“Industry generally prefers extrusion-based processing because it’s easier and cheaper to control,” Xie says. “Scaling to produce great lengths of film while maintaining the same structure and performance could complicate matters. There’s potential, but it’s also challenging.”
Still, researchers say the discovery demonstrates that new performance limits may still be unlocked using familiar materials. “Developing the material is only the first step,” Zhang says. “But it shows people that this barrier can be broken.”
From Your Site Articles
Related Articles Around the Web
Tech
Dune Part Three Trailer Reveals the Weight Paul Atreides Carries After Victory


Crowds flocked to the AMC Century City theater in Los Angeles this morning for a special IMAX event featuring the first look at the concluding chapter in Denis Villeneuve’s “Dune” saga. Zendaya, Robert Pattinson, Javier Bardem, and Anya Taylor-Joy came out to meet the fans in person, while Timothée Chalamet sent in a video greeting via his phone. The energy in the room altered suddenly, as this plot picks up 17 years after the previous film finished and revolves around what happens when someone gains too much power.
The footage starts with Paul and Chani having a private conversation about what they could name their future child. Ghanima for a girl and Leto for a male, but even it felt tight, a result of how they’d begun to drift apart in the last film. Within seconds, the screen was filled with broader pictures of Paul and Stilgar exploring the cosmos on new planets, as their reach for the Atreides empire grew rapidly. Large sights of fleets of ships slicing across alien sky, as well as soldiers moving across rocky terrain far from Arrakis.
Sale
LEGO Icons Dune Atreides Royal Ornithopter 10327, Collectible Dune Inspired Model for Build and Display…
- Dune building set for adults – Collectible LEGO Icons Dune Atreides Royal Ornithopter building project for fans of the Dune 2021 movie
- What’s in the box? – Everything you need to craft a LEGO replica of the Dune Atreides Royal Ornithopter aircraft with foldout, flappable wings and…
- Minifigure character lineup – Includes Paul Atreides, Lady Jessica, Gurney Halleck, Chani, Leto Atreides, Liet Kynes, Duncan Idaho and Baron…

Chani showed up shortly, this time fighting her way through a violent battle scene. A sandworm can be spotted in the midst of it all, balancing on its back before diving into the melee. Just as Chani was in the middle of it, Alia, now all grown up and played by Anya Taylor-Joy, stepped into several critical frames of her own.

Paul himself provides some of the low, echoing vocals that run under the music throughout, while Robert Pattinson appears as Scytale, the shape-shifter who is as slick as ever and whose loyalties are impossible to read. Jason Momoa has also returned, and Duncan Idaho was seen briefly. Returning cast members include Rebecca Ferguson (Lady Jessica), Florence Pugh (Princess Irulan), and Javier Bardem (Stilgar), who join an already impressive group.

Villeneuve described this installment as a fast-paced thriller centered on action and pressure. Note how, even in the midst of all that upheaval, Paul and Chani’s link remains strong, as he describes it as a steady pulse that runs through everything, with a focus primarily on the two of them. He also emphasizes how the large jump in time allows Alia to become much more vital to the tale, which the previous films just hinted at. Also, it appears that Hans Zimmer has returned to the soundtrack. Fans who left the theater today are already counting down the days until December 18, 2026, when the film is released.
-

 Tech7 days ago
Tech7 days agoA 1,300-Pound NASA Spacecraft To Re-Enter Earth’s Atmosphere
-

 Crypto World4 days ago
Crypto World4 days agoHYPE Token Enters Net Deflation as HyperCore Buybacks Outpace Staking Rewards
-

 Fashion4 days ago
Fashion4 days agoWeekend Open Thread: Addict Lip Glow
-

 Tech2 days ago
Tech2 days agoYour Legally Registered ‘Motorcycle’ Might Not Count Under Proposed US Law
-
Sports3 days ago
Why Duke and Michigan Are Dead Even Entering Selection Sunday
-

 NewsBeat6 days ago
NewsBeat6 days agoResidents reaction as Shildon murder probe enters second day
-

 Business2 days ago
Business2 days agoSearch for Savannah Guthrie’s Mother Enters Seventh Week with No Arrests
-

 Business7 days ago
Business7 days agoSearch Enters Sixth Week With New Leads in Tucson Abduction Case
-
 Sports6 days ago
Sports6 days agoPWHL, Senators discussing plan to keep Charge in Ottawa
-

 Business3 days ago
Business3 days agoUS Airports Launch Donation Drives for Unpaid TSA Workers as Partial Government Shutdown Enters Fifth Week
-

 Crypto World3 days ago
Crypto World3 days agoCoinbase and Bybit in Investment Talks: Could Bybit Finally Enter the US Crypto Market?
-

 Tech4 hours ago
Tech4 hours agoAre Split Spacebars the Next Big Gaming Keyboard Trend?
-

 NewsBeat6 days ago
NewsBeat6 days agoI Entered The Manosphere. Nothing Could Prepare Me For What I Found.
-

 Business3 days ago
Business3 days agoCountry star Brantley Gilbert enters growing non-alcoholic beer market
-

 Business1 day ago
Business1 day agoAustralian shares drop as Iran war enters third week
-

 Sports4 days ago
Sports4 days agoCollege Basketball Best Bets: Conference Tournament Semifinal Picks
-

 Crypto World1 day ago
Crypto World1 day agoCrypto Lender BlockFills Enters Chapter 11 with Up to $500M in Liabilities
-

 Tech7 days ago
Tech7 days agoClarity as strategy
-

 Politics7 days ago
Politics7 days agoTrump Says Middle East Is ‘Very Lucky’ That He’s President
-
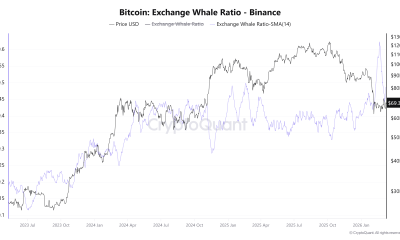
 Crypto World6 days ago
Crypto World6 days agoThree Binance Charts May Be Hinting at Bitcoin’s Next Move
















You must be logged in to post a comment Login