Crypto World
FBI Issues Urgent Warning as Russian Hackers Target Signal Users and Compromise Thousands of American Accounts

TLDR:
- Russian intelligence-linked hackers have compromised thousands of Signal accounts through targeted phishing campaigns globally.
- High-value targets include current and former U.S. government officials, military personnel, journalists, and political figures.
- Signal’s encryption remains unbroken — Russian hackers bypass it by stealing user credentials through social engineering.
- The FBI urges Americans to never share PINs or 2FA codes and to report suspicious activity to IC3.gov immediately.
The FBI has issued a stark warning about Russian hackers actively targeting Americans who use Signal and other commercial messaging apps.
Working alongside the Cybersecurity and Infrastructure Security Agency, the bureau confirmed that thousands of individual accounts have already been compromised.
The campaign focuses on high-value targets, including current and former U.S. government officials, military personnel, political figures, and journalists. Authorities stress that Signal’s encryption is not at fault — end users are the primary vulnerability.
FBI Confirms Russian Hackers Are Actively Compromising Signal Accounts Across the Globe
Russian hackers linked to the country’s intelligence services have been running a coordinated phishing campaign against Signal users.
The operation involves sending messages disguised as official CMA support communications to unsuspecting targets. Once a user interacts with the message, the attacker gains full access to their account.
FBI Director Kash Patel publicly confirmed the threat, warning Americans through an official statement on X.
After gaining access, Russian hackers can read private messages and browse full contact lists. They can also send messages while posing as the account owner. This creates a chain of trust-based attacks that are difficult for recipients to detect.
The phishing messages are carefully tailored to each target, making them appear legitimate and urgent. Victims are typically asked to click a link, provide a verification code, or submit an account PIN. Any of these actions immediately hands control of the account to the attacker.
Authorities noted that the campaign continues to evolve. Russian hackers may expand their methods to include malware designed to infect victim devices directly. This development moves the threat beyond social engineering into more technically advanced territory.
Signal’s end-to-end encryption remains fully operational and has not been breached. However, the FBI warned that phishing renders encryption irrelevant when attackers access accounts directly. No level of encryption can protect a user who unknowingly hands over their credentials.
What Americans Can Do Right Now to Protect Their Signal Accounts
The FBI and CISA released joint guidance to help Americans defend against the ongoing Russian hacker campaign.
The first step is straightforward: stop all interaction the moment a message feels suspicious. Users should never share PINs or two-factor authentication codes for actions they did not personally initiate.
Any unsolicited message requesting account information should be treated as a potential phishing attempt. Even messages appearing to come from known contacts warrant caution if they contain unusual requests.
When uncertain, users should contact the sender through a completely separate channel before responding.
Group chats also need to be monitored carefully for unauthorized participants. Users should scan participant lists regularly for duplicate or unfamiliar accounts.
Any anomaly should be verified through secure communication outside of the app before further messages are shared.
The FBI reminded Americans that legitimate Signal support never sends verification links through direct messages.
Real support teams communicate exclusively through official email channels and never request codes or PINs inside the app. Any message claiming otherwise is almost certainly a phishing attempt by Russian hackers.
Americans who suspect they have been targeted should report the activity to the Internet Crime Complaint Center at IC3.gov or contact their nearest FBI field office.
Organizational IT and security teams should also be notified immediately. Fast reporting strengthens the FBI’s ability to track the campaign and protect additional accounts from being compromised.
Crypto World
Bitcoin Mining Difficulty Drops 7.7% in Biggest Cut Since February
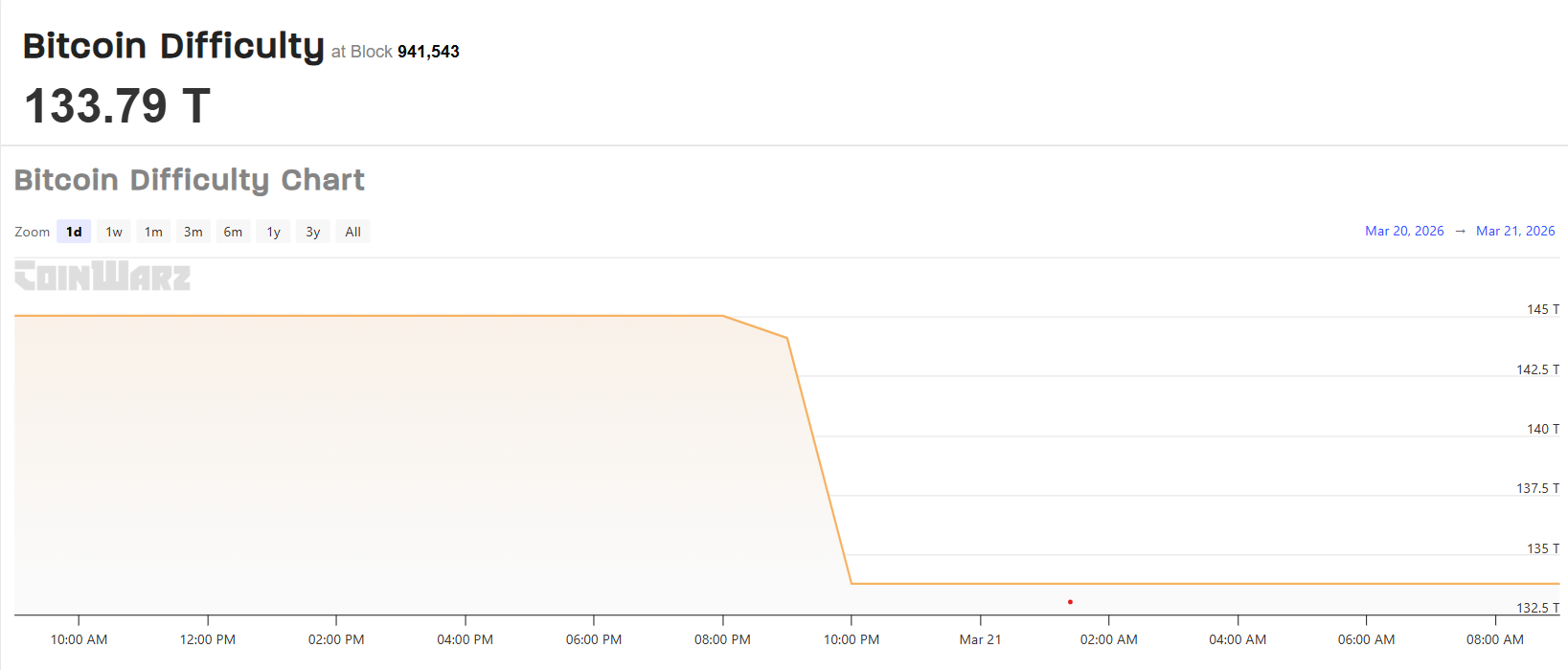
Bitcoin’s mining difficulty fell by around 7.7% at the latest adjustment on March 20 to 133.79 trillion at block 941,472, the sharpest drop since February, according to CoinWarz data.
The latest move takes difficulty down from around 145 trillion in mid-March and roughly 148 trillion at the start of the year. A lower difficulty means it takes less computational work to earn the same block reward, slightly improving revenue per unit of hashrate for firms that stay online.
The adjustment followed slower-than-target block production over the prior 2,016 blocks. CloverPool data showed average block times at about 12 minutes 36 seconds, well above Bitcoin’s 10-minute target, forcing the network to recalibrate lower.
In February, difficulty dropped sharply after weather-related disruptions in the United States temporarily knocked large American mining facilities offline, and it later rebounded by about 15% as hashrate returned to the network once power conditions normalized.
Bitcoin (BTC) difficulty measures how hard it is for miners to find a valid hash for the next block and is automatically adjusted to keep issuance steady at one block every 10 minutes.
When more computing power, or hashrate, joins the network, difficulty rises to prevent blocks from being mined too quickly, while a decline in hashrate triggers a lower difficulty, making it easier for remaining miners to earn rewards.

Related: Cango reports $285M Q4 loss as Bitcoin mining costs surge in 2025
The next difficulty adjustment is currently estimated for April 3, though that projection changes with each new block.
Miners pivot to AI as power costs bite
The difficulty reset also comes as several listed miners push further into AI and high-performance computing infrastructure in search of steadier returns on power and data-center capacity.
Last week, crypto trader Ran Neuner argued AI had become Bitcoin mining’s biggest competitor as both industries compete for electricity, even going as far as to say that “AI has killed Bitcoin forever.”
Bitcoin miners such as Core Scientific, MARA Holdings, Hut 8 and Cipher Mining have begun reallocating capacity or pivoting toward AI workloads, while some operators have reduced hashrate or shut down less efficient rigs as profitability tightens.
On Feb 21, Bitdeer liquidated 943 BTC from reserves and sold newly mined coins, cutting corporate holdings to zero. In its latest weekly update on March 21, it confirmed that its BTC holdings remained at zero.
Big questions: Would Bitcoin survive a 10-year power outage?
Crypto World
SBF angles for presidential pardon with tweets praising Donald Trump


Former FTX CEO Sam Bankman-Fried, who is currently serving a 25-year sentence for fraud, has renewed public praise of U.S. President Donald Trump, adding to speculation that he hopes to secure a pardon.
In a recent post on X, written through a proxy using prison-approved communications, Bankman-Fried backed Trump’s decision to launch strikes against Iran. He framed the move as necessary to counter nuclear risk and claimed the operation had sharply reduced Iran’s military capacity.
The comments mark his latest in a string of statements supportive of the U.S. president. In earlier posts, he pointed to lower gas prices under Trump than in the Biden era and in other countries. He also credited Trump with “saving” the SEC by replacing former chair Gary Gensler with Paul Atkins, arguing the shift eased pressure on crypto firms and reduced inter-agency conflict.
The tone has drawn attention, given Bankman-Fried’s legal position. Presidential pardons have historically extended to financial crimes, and Trump has shown a willingness to grant clemency in high-profile cases. Ross Ulbricht, who operated a digital black market platform called Silk Road, was sentenced to life in prison without the possibility of parole in 2015 before Trump freed him shortly after being sworn in in 2025. For Bankman-Fried, whose conviction stemmed from one of the largest financial collapses in crypto history, public alignment with the president may serve a clear purpose.
His outreach comes as the remnants of his former empire continue to unwind. Earlier this week, the FTX Recovery Trust said it will distribute about $2.2 billion to creditors as part of an ongoing Chapter 11 process, pushing recovery rates close to full repayment for many claim classes.
Still, the damage from FTX’s collapse runs deep. Millions of customers lost access to funds in 2022, and the event shook trust in crypto markets. Prices fell, firms failed, and regulators stepped in with tighter scrutiny. The case remains a reference point for risk in the industry.
Bankman-Fried’s praise of Trump’s Iran policy lands as that decision faces growing criticism, with some warning the conflict could strain public finances and disrupt global oil supply, as well as concerns about inflation and higher costs for households and businesses.
For now, Bankman-Fried remains behind bars, communicating through intermediaries while his former company repays creditors. His lawyers filed a motion for a new trial in February, which the government opposed. His public messaging, however, suggests he is trying to shape an outcome beyond the courtroom.
Crypto World
66-Year-Old Retired Man Scammed in 3 Cryptocurrency Fraud Cases


The Hong Kong Police Cyber Crime Bureau has issued a warning after a 66-year-old retired man fell victim to three separate cryptocurrency scams.
Summary
- A Hong Kong senior loses HK$6.6M in three separate cryptocurrency scams.
- Police warn against transferring money or crypto to strangers to avoid fraud.
- Fraudsters impersonating experts tricked the victim into losing all his savings.
In total, the elderly victim lost HK$6.6 million after being misled by fraudsters posing as cryptocurrency experts, according to local reports.
In September 2025, the victim received a WhatsApp message from a fraudster claiming to be a cryptocurrency investment expert. The scammer promised guaranteed profits and offered to teach the victim how to invest in cryptocurrencies.
Trusting the individual, the elderly man handed over HK$1.4 million. After the cryptocurrency was deposited into the fraudster’s account, the scammer vanished. Realizing he had been deceived, the victim reported the incident to the police.
Not willing to give up, the victim went online to seek help from another “cryptocurrency expert” to recover his losses. The new fraudster reassured the victim that recovery was possible, but demanded 600,000 yuan as a deposit. Once the victim transferred the money, the so-called expert disappeared as well, and the victim realized he had been scammed a second time.
In January of this year, the victim was contacted by another fraudster claiming to be able to recover his previous losses. This time, the fraudster insisted that the victim purchase 4.6 million yuan worth of cryptocurrency and deposit it into a designated account. As with the previous scams, the fraudster disappeared after the victim complied. At this point, the elderly man had lost his entire life savings to scammers.
Police Warning and Advice
The police are urging citizens to be cautious and avoid transferring money or cryptocurrency to strangers. They emphasize that no one can guarantee to recover losses, and any offer that promises guaranteed returns or insider information is likely a scam. If someone offers to help recover funds after a previous scam, it is likely part of a serial fraud scheme.
Additionally, the FBI has issued a warning about fake tokens on the Tron blockchain impersonating the agency. Scammers are using these fake tokens to trick users into providing personal information under the false pretense that their wallets are under investigation.
Crypto World
Early Ethereum Whale Rebuilds Position with $19.5M ETH Purchases

Key takeaways
On-chain activity and the ETH exposure narrative
ETF flows, price backdrop, and what they signal
Bitmine’s conviction, DeMark signals, and the long arc of ETH
Crypto World
Ripple Burns 9M RLUSD, Slowing Push Toward $2B Supply Target Pace Now

RLUSD Supply Adjustments and Treasury Activity
Ripple executed the latest burn through its treasury wallet, permanently removing nine million RLUSD tokens from circulation. Consequently, the move reduced the available supply and followed earlier large-scale burns during the same month. The action forms part of routine supply management tied to redemptions and liquidity balancing.
Earlier in March, Ripple eliminated twenty-five million RLUSD on the Ethereum blockchain through a similar treasury operation. Moreover, the firm conducted another ten million token burn on the XRP Ledger before this latest adjustment. These consecutive reductions indicate active oversight of the circulating supply across multiple blockchain networks.
🔥🔥🔥🔥🔥🔥 9,000,000 #RLUSD burned at RLUSD Treasury.https://t.co/3K4NW7GKCE
— Ripple Stablecoin Tracker (@RL_Tracker) March 20, 2026
Stablecoin issuers typically burn tokens when users redeem assets or when reserves require rebalancing. Therefore, Ripple maintains a one-to-one backing model by aligning supply with underlying reserves. This approach supports transparency and ensures compliance with audit expectations tied to regulated stablecoins.
RLUSD Market Growth and Slowing Momentum
RLUSD has recorded steady adoption since its launch in December 2024, supported by rising transaction volumes and integrations. Currently, the stablecoin holds a market capitalization of nearly 1.5 billion dollars with notable daily trading activity. However, continued burns have slowed the pace of net supply expansion despite earlier rapid growth.
Market participants had anticipated a quicker move toward the two billion supply level based on early adoption trends. Additionally, integrations with major financial institutions contributed to expectations of accelerated issuance and broader usage. Yet, the recent sequence of burns has offset minting activity and tempered that trajectory.
Despite slower growth, RLUSD maintains consistent demand across payment channels and institutional use cases. Moreover, transaction data shows ongoing utility rather than speculative accumulation driving activity. This pattern reflects stable adoption dynamics even as total supply growth stabilizes.
XRP Ledger Role and Institutional Context
The XRP Ledger continues to support RLUSD issuance and settlement alongside Ethereum-based operations. Consequently, Ripple uses multiple networks to distribute supply and manage cross-chain liquidity efficiently. This structure allows flexibility while maintaining consistent reserve backing across platforms.
Institutional integrations have played a key role in RLUSD adoption, especially within cross-border payment systems. Furthermore, partnerships with financial entities have increased transaction throughput and strengthened real-world usage. These developments contribute to steady demand, even as treasury burns adjust the circulating supply.
Ripple’s approach shows controlled supply management rather than unchecked expansion of its stablecoin ecosystem. Therefore, the firm balances minting and burning to reflect actual usage patterns and reserve requirements. This method supports long-term stability and aligns RLUSD growth with measurable demand conditions.
Crypto World
Crypto Market Rebounds as Bitcoin Hits $71K After Volatility

The crypto market recovered today as Bitcoin climbed back above $71,000 after recent losses. The broader market cap rose to $2.42 trillion, supported by derivatives activity. However, macro pressure and weak sentiment continue to shape short-term direction.
Key Highlights
- Bitcoin rebounds to $71K after major options expiry boosts momentum
- Ethereum struggles near $2.1K despite short-term institutional support
- XRP holds firm as retail demand offsets weaker institutional flows
- Crypto market cap climbs to $2.42T amid volatile macro backdrop
- Analysts warn of short-term rallies but highlight ongoing downside risks
⚡️ Bitcoin back above $71K.
Ethereum reclaims $2K — strength returning across the market.Momentum is building again. 🚀$BTC $ETH pic.twitter.com/vhMtAGvElD
— Nehal (@nehalzzzz1) March 20, 2026
Bitcoin Holds Above $71K as Options Expiry Drives Momentum
Bitcoin price trades near $71,000 after rebounding from post-FOMC lows earlier this week. The recovery follows the expiry of $1.7 billion in BTC options. This expiry event aligned with a max pain level near $70,000, supporting upward movement.
Moreover, implied volatility has increased, which signals rising short-term bullish sentiment. At the same time, traders reduced demand for downside protection, which reflects improved confidence. However, positioning remains tactical as the next quarterly expiry approaches.
Meanwhile, macro conditions continue to influence price action, as delayed rate cuts weigh on sentiment. ETF outflows have also added pressure in recent sessions. Still, strong support from institutional and derivatives traders has helped stabilize Bitcoin.
Ethereum Struggles Near $2,100 Despite Institutional Activity
Ethereum price trades around $2,150 after holding a key support zone near $2,100. The asset rebounded slightly after options worth nearly $380 million expired. However, the put-to-call ratio near 1.02 indicates balanced sentiment.
At the same time, implied volatility continues to rise, which suggests expectations of near-term price swings. Institutional accumulation has supported Ethereum, yet momentum remains weak compared to Bitcoin. This reflects ongoing uncertainty in broader market conditions.
In addition, macro risks and lower institutional demand continue to limit upside potential. Analysts expect Ethereum could retest levels below $2,100 if pressure builds again. Therefore, the current rebound appears fragile despite temporary support.
XRP Maintains Strength as Retail Demand Supports Price
XRP price holds near $1.40 as steady retail demand supports its recent performance. The asset shows resilience despite weaker institutional participation. Expanding utility also contributes to its relative stability in the current market cycle.
Furthermore, analysts expect XRP could rise toward $1.50 in the short term. This outlook depends on continued demand and stable market conditions. However, broader uncertainty could still limit sustained upward movement.
At the same time, market dynamics continue to shift as traders adjust positions. Altcoins, including XRP, may benefit from declining Bitcoin dominance. Yet, analysts warn that sudden reversals could trigger repeated stop-outs for short-term traders.
Macro Trends and Oil Markets Shape Crypto Sentiment
Global macro developments continue to influence crypto market direction. Oil prices have declined after signals of increased supply and reduced geopolitical escalation. This has improved risk sentiment across financial markets.
Additionally, policy discussions around Iranian oil sanctions have contributed to price declines. However, supply risks remain, as disruptions could push oil prices significantly higher. This uncertainty continues to affect broader market stability.
As a result, crypto assets remain sensitive to external economic signals. While the current rebound reflects short-term relief, underlying risks persist. Therefore, market participants continue to adjust strategies based on evolving conditions.
Crypto World
Bitcoin price flattens at $70K, altcoins show indecision amid global tensions


The cryptocurrency market has experienced a slowdown in the past 24 hours, with Bitcoin’s price showing little movement. As of now, Bitcoin (BTC) trades within a narrow range, oscillating between $69,500 and $70,600.
Summary
- Bitcoin stabilizes around $70K after volatility, with a minor correction from earlier highs.
- Altcoins show minimal price changes, with most trading within a narrow range.
- Market uncertainty persists amid rising geopolitical tensions, with Bitcoin driving altcoin performance.
Meanwhile, this is after a week of high volatility and substantial liquidations in the derivatives market. The altcoin market also reflects a similar lack of significant price action, suggesting a calm period before potential price shifts.
Bitcoin’s price has been relatively stable around $70,000 following a week of intense volatility. At the time of writing, Bitcoin is closer to $71,000, but the market volume has slowed down as expected for the weekend. Earlier in the week, BTC surged past $76,000 but has since corrected by nearly 10%.
This price drop is partly attributed to ongoing geopolitical tensions, particularly the conflict between the US, Israel, and Iran. Rising oil prices and inflation fears have added to the uncertainty, leading to a broader market correction. The risk-on markets, including crypto, have experienced a downturn, and the future direction of Bitcoin’s price may depend heavily on the resolution of these global issues.
Altcoin market shows minimal movement
The altcoin market has shown minimal price changes over the past 24 hours. Most cryptocurrencies have remained within a narrow range, with price fluctuations generally between -1% and +1%.
Some altcoins, such as WLFI, have shown modest gains of over 4%, but these are exceptions and do not suggest sustained upward momentum. The broader market remains cautious, with little to suggest that a breakout in altcoins is imminent. In the current market conditions, the altcoins’ performance is largely influenced by Bitcoin’s price movements.
Disclosure: This article does not represent investment advice. The content and materials featured on this page are for educational purposes only.
Crypto World
BlackRock Moves $140M in Bitcoin and Ethereum ETF Flows Turn Negative

BlackRock has moved a fresh batch of Bitcoin and Ethereum to Coinbase Prime, totaling over $140 million in value. The transfers follow recent ETF outflows and weaker price momentum across major crypto assets. The activity adds pressure to a market that has already shown signs of slowing institutional demand.
Bitcoin Transfers Reflect ETF Pressure
BlackRock transferred 544 Bitcoin to Coinbase Prime as ETF outflows increased across the sector. The transaction aligns with recent declines in ETF inflows and softer price action. Additionally, Bitcoin has struggled to maintain upward momentum after its recent rally.
BlackRock just deposited 47,728 $ETH($102.13M) and 544 $BTC($38.3M) to Coinbase Prime.https://t.co/qmuDIrPHc6 pic.twitter.com/kmqXk3XzEx
— Lookonchain (@lookonchain) March 20, 2026
Data shows that the transferred Bitcoin is worth about $38.3 million at current market prices. The movement links directly to wallets associated with BlackRock’s IBIT Bitcoin ETF. Consequently, the transfer suggests a response to redemption activity within the fund.
Bitcoin ETFs recorded continued outflows over two consecutive sessions, with total withdrawals exceeding $90 million. This trend follows a period of strong inflows earlier in the quarter. However, the current slowdown reflects reduced demand at higher price levels.
Ethereum Movement Signals Liquidity Shift
BlackRock also transferred 47,728 Ethereum tokens to Coinbase Prime during the same transaction window. The Ethereum portion accounted for approximately $102.13 million of the total transfer. Moreover, the scale of the movement highlights significant liquidity repositioning.
The transferred Ethereum originates from wallets tied to BlackRock’s ETHA Ethereum ETF. This connection indicates that ETF-related flows continue to influence on-chain activity. Hence, the movement may reflect adjustments to meet redemption or trading requirements.
Ethereum has faced uneven performance despite broader market recovery attempts in recent weeks. Price action remains sensitive to both ETF flows and macro sentiment. Additionally, large transfers often increase short-term volatility expectations in the market.
Market Context and Institutional Positioning
BlackRock continues to dominate both Bitcoin and Ethereum ETF markets despite recent outflows. The firm relies on Coinbase Prime for custody and execution of its crypto transactions. Therefore, transfers to the platform often signal preparation for trading activity.
Market participants interpret the latest deposits in different ways, depending on broader sentiment. Some view the transfers as preparation for asset sales following ETF withdrawals. However, others consider the possibility of liquidity setup for future positioning.
The broader crypto market has shown reduced momentum as Bitcoin trades near the $70,000 level. This price range has acted as a resistance zone after the recent rally phase. Consequently, large institutional flows now play a more visible role in shaping direction.
Crypto World
Institutions Buy Crypto Now, Not Waiting for Market Bottom

Institutional demand for digital assets remains resilient even as markets endure ongoing turbulence. New data show that large investors are preparing to increase allocations despite a sharp sell-off since October, signaling that institutions see crypto as part of a diversified, regulated portfolio rather than a short-term trade. In parallel, stablecoins are expanding their footprint beyond trading floors into regulated financial channels, with Japan moving forward on regulated USDC lending products and new models tying digital assets to real-world assets taking shape. At the same time, traditional capital markets are increasingly a venue for crypto enterprises, as Abra pursues Nasdaq listing plans via a SPAC merger. Taken together, these developments suggest a crypto market that continues to mature through regulated, compliant pathways even as volatility and policy questions persist.
On the investor side, sentiment remains constructive. A January survey of 351 investors conducted with Coinbase and EY-Parthenon found that a majority plan to increase their digital asset exposure this year, with 73% indicating they would buy more and 74% expecting price Appreciation over the next 12 months. Bitcoin and Ether continue to anchor entry points for many, but interest is widening into stablecoins and tokenized assets. Notably, roughly two-thirds of respondents expressed a preference for gaining exposure via regulated vehicles, such as exchange-traded products, underscoring a demand for structures that blend crypto access with traditional oversight.
Key takeaways
- Institutional appetite for crypto persists despite volatility: a January survey found 73% of respondents plan to buy more digital assets this year, with 74% anticipating higher prices over the next 12 months.
- Regulated access remains central: two-thirds favor exposure through regulated vehicles like exchange-traded products, signaling a continued shift toward compliant crypto investment avenues.
- Japan expands regulated USDC use: SBI’s USDC lending efforts illustrate a move beyond trading into retail-friendly, regulated stablecoin products in a mature market.
- Crypto firms press for public-market access: Abra is pursuing Nasdaq listing via a SPAC merger, reflecting a broader interest in traditional capital markets amid uneven IPO activity.
- Real-world assets enter yield-enabled crypto models: Theo launches a $100 million gold-linked yield stablecoin vault, a sign that asset-backed and yield-bearing structures are becoming more mainstream.
Institutional demand endures amid volatility
Despite a broad crypto market trough since October, institutional investors appear undeterred about the medium-term trajectory. The Coinbase–EY-Parthenon survey paints a picture of continued capital deployment into digital assets, with participants signaling readiness to scale exposure even as price volatility remains a defining feature of the current cycle. While BTC and ETH remain the core entry points, institutions are increasingly exploring stablecoins and tokenized collateral as part of diversified portfolios. A notable share also indicates a preference for regulated vehicles—such as exchange-traded products—as a preferred channel for gaining crypto exposure—an indicator that risk controls and governance frameworks are expected to accompany future inflows.
The persistence of institutional demand matters for several reasons. First, it helps sustain liquidity and depth in established markets, even when spot prices swing. Second, it accelerates the adoption curve for regulated products and custodial solutions that can meet more conservative risk profiles. Finally, it supports longer-term price discovery that is anchored in institutional participation rather than speculative retail flows alone. As this dynamic unfolds, market participants will be watching how custody, compliance, and reporting standards evolve to accommodate an increasingly diversified investor base.
Japan advances regulated USDC lending and stablecoin use
In Japan, the regulated pathway for stablecoins is expanding beyond trading desks. SBI’s Vic Trade arm has moved forward with a retail USDC lending service, a development that aligns with regulatory clarity already established for Circle’s USDC in the country. The platform will let users lend USDC in exchange for yield, marking one of the first retail-facing products of its kind in Japan and signaling broader institutional confidence in dollar-backed tokens within a controlled framework. The move comes as licensed players gain greater scope to offer regulated stablecoin services, illustrating how formal regulatory acceptance can catalyze new onramps and product segments for both individuals and institutions.
Japan’s approach reinforces a broader pattern: stablecoins are moving from pure trading tools toward regulated financial products that can fit into everyday financial activity. This transition could influence global standards, as other jurisdictions consider how to balance innovation with consumer protection, tax treatment, and cross-border settlement efficiency. For investors, the development widens the menu of regulated entry points into crypto, potentially improving risk parity for diversified portfolios that include stablecoin yield strategies alongside traditional equities and bonds.
Abra eyes Nasdaq through SPAC amid IPO market ebbs and flows
Abra, a long-running crypto wealth manager, is pursuing a public listing via a merger with New Providence Acquisition Corp., a move that would place the combined company on Nasdaq under the ticker ABRX. The deal values the merged entity at approximately $750 million, reflecting a shift in Abra’s focus toward wealth management services—trading, custody, and yield products—after regulatory constraints constrained its earlier lending operations. The SPAC route provides a faster path to public markets in an environment where traditional IPO activity remains tepid, underscoring a continuing willingness among crypto firms to access public capital through alternative routes when regulatory and market conditions are uncertain.
The Abra strategy highlights a broader trend: crypto firms are increasingly pursuing traditional capital markets access as a means to scale and signal legitimacy, even as scrutiny from regulators remains intense. While SPACs can offer speed, they also bring ongoing governance and disclosure expectations that could shape Abra’s strategy in the coming years. Investors will be watching how the company harmonizes its wealth-management-centric model with the transparency and investor protections demanded by public markets, as well as how it navigates evolving digital-asset custody and compliance benchmarks.
Theo introduces gold-backed yield innovation
Theo, a tokenization platform, unveiled a new $100 million vault tied to a gold-backed, yield-bearing stablecoin. The product combines traditional commodity backing with on-chain financial mechanics to deliver price stability alongside yield opportunities. In this hybrid model, gold serves as the collateral underpinning the token’s value, offering an alternative to fiat-backed stablecoins while expanding the range of on-chain income strategies for users. The vault represents a growing wave of experimentation with yield-bearing stablecoins that move beyond simple price stability, exploring how real-world assets and yield-generation can coexist within a regulated, on-chain framework.
Such innovations underscore a broader industry push to bring real-world collateral and cash-flow mechanics into the crypto ecosystem. As platforms experiment with different collateral mixes and automated yield strategies, investors gain access to a wider set of risk-and-reward profiles. Observers will want to monitor how gold-backed models perform in practice, how liquidity and valuation are maintained across stressed market scenarios, and how regulators respond to asset-backed stablecoins that blur the lines between traditional financial products and crypto innovations.
Looking ahead, the momentum across institutions, regulated stablecoins, public-market access, and yield-focused innovations suggests a crypto landscape that is maturing through structured, compliant channels. Market participants should keep a close eye on regulatory developments in key jurisdictions, the rollout of retail products in regulated markets, and the continued evolution of asset-backed and tokenized yield vehicles as potential catalysts for broader adoption and more diverse investment strategies.
Crypto World
BTC Price Holds $70K as Analysts Spot Cycle Reset Signs


Bitcoin (BTC) stayed near the $70,000 level after a volatile week shaped by geopolitical tensions and the latest Federal Reserve meeting. BTC price traded at $70,672.50 at the time of writing, down slightly over 24 hours and up 0.11% over the past seven days.
Summary
- BTC price stayed above $70,000 after sharp swings tied to macro pressure and Fed remarks.
- Analysts said bitcoin’s valuation and realized price levels now resemble past cycle bottom formations.
- Binance outflows averaged $55 million daily, pointing to steady demand behind bitcoin’s recent resilience.
Bitcoin pushed toward $74,000 twice in recent days before failing to hold that level. Over the weekend, BTC price dropped toward $70,000 after market pressure followed U.S. military action on Iranian infrastructure.
The asset then recovered early in the week and climbed to $76,000 on Tuesday, its highest level in almost six weeks. That rally faded quickly. Bitcoin slipped back to $74,000 on Wednesday and then fell from about $74,400 to $71,200 before the FOMC decision.
The Federal Reserve kept interest rates unchanged, which matched market expectations. Bitcoin briefly rebounded to $72,000 after the decision, but later comments from Fed Chair Jerome Powell on inflation and the economy added pressure and pushed BTC down to $68,800 on Thursday.
Even with those losses, bitcoin avoided a deeper breakdown and moved back above $70,000. That recovery has kept attention on current support levels and near-term trader positioning.
Analysts point to cycle and valuation signals
Crypto analyst Michaël van de Poppe said the valuation of BTC against gold is showing a monthly engulfing signal. He wrote, “It doesn’t mean that we immediately go up from here,” while adding that similar setups in 2015, 2018 and 2020 marked bear market lows.
Another market watcher, CryptosRus, said bitcoin is trading near its realized price, a level that has previously aligned with major cycle lows. He said,
“Every time $BTC reaches this zone, it doesn’t stay here for long.”
Moreover, CryptoQuant analyst burakkesmeci said Binance netflow data suggests steady buying demand behind bitcoin’s recent strength. According to his reading, the Binance BTC Netflow SMA30 has stayed below zero, showing sustained exchange outflows.
He said about $55 million worth of BTC has been leaving Binance daily on average. That trend, he said, helped support bitcoin’s rise from $65,000 to $74,000 and may explain why BTC price has remained firm even as broader markets faced pressure.
Disclosure: This article does not represent investment advice. The content and materials featured on this page are for educational purposes only.
-

 Tech6 days ago
Tech6 days agoYour Legally Registered ‘Motorcycle’ Might Not Count Under Proposed US Law
-

 Politics17 hours ago
Politics17 hours agoJenni Murray, Long-Serving Woman’s Hour Presenter, Dies Aged 75
-

 Tech4 days ago
Tech4 days agoAre Split Spacebars the Next Big Gaming Keyboard Trend?
-

 Fashion18 hours ago
Fashion18 hours agoWeekend Open Thread: Adidas – Corporette.com
-
Sports7 days ago
Why Duke and Michigan Are Dead Even Entering Selection Sunday
-

 Business6 days ago
Business6 days agoSearch for Savannah Guthrie’s Mother Enters Seventh Week with No Arrests
-

 Business7 days ago
Business7 days agoUS Airports Launch Donation Drives for Unpaid TSA Workers as Partial Government Shutdown Enters Fifth Week
-

 Crypto World7 days ago
Crypto World7 days agoCoinbase and Bybit in Investment Talks: Could Bybit Finally Enter the US Crypto Market?
-
Crypto World13 hours ago
NIO (NIO) Stock Plunges 6.5% as Shelf Registration Sparks Dilution Worries
-

 News Videos3 days ago
News Videos3 days agoRBA board divided on rate cut, unusually buoyant share market | Finance Report | ABC NEWS
-

 Business5 days ago
Business5 days agoAustralian shares drop as Iran war enters third week
-

 Crypto World5 days ago
Crypto World5 days agoCrypto Lender BlockFills Enters Chapter 11 with Up to $500M in Liabilities
-
 Politics3 days ago
Politics3 days agoThe House | The new register to protect children from their abusers shows Parliament at its best
-

 Fashion5 days ago
Fashion5 days ago25 Celebrities with Curly Hair That Are Naturally Beautiful
-

 Tech1 day ago
Tech1 day agoinKONBINI Lets You Spend Summer Days Behind the Register
-

 Crypto World3 days ago
Crypto World3 days agoCanada’s FINTRAC revokes registrations of 23 crypto MSBs in AML crackdown
-

 Politics4 days ago
Politics4 days agoReal-time pollution monitoring calls after boy nearly dies
-

 Crypto World7 days ago
Crypto World7 days agoCrypto Losses Drop 87% in February, But Hackers Are Now Targeting People, Not Code
-
 NewsBeat3 days ago
NewsBeat3 days agoResidents in North Lanarkshire reminded to register to vote in Scottish Parliament Election
-

 Business5 days ago
Business5 days agoMeta planning major layoffs as AI spending and automation reshape workforce










You must be logged in to post a comment Login