- Criminals are adding hundreds of malicious packages to npm
- The packages try to fetch a stage-two payload to infect the machines
- The crooks went to lengths to hide where they host the malware
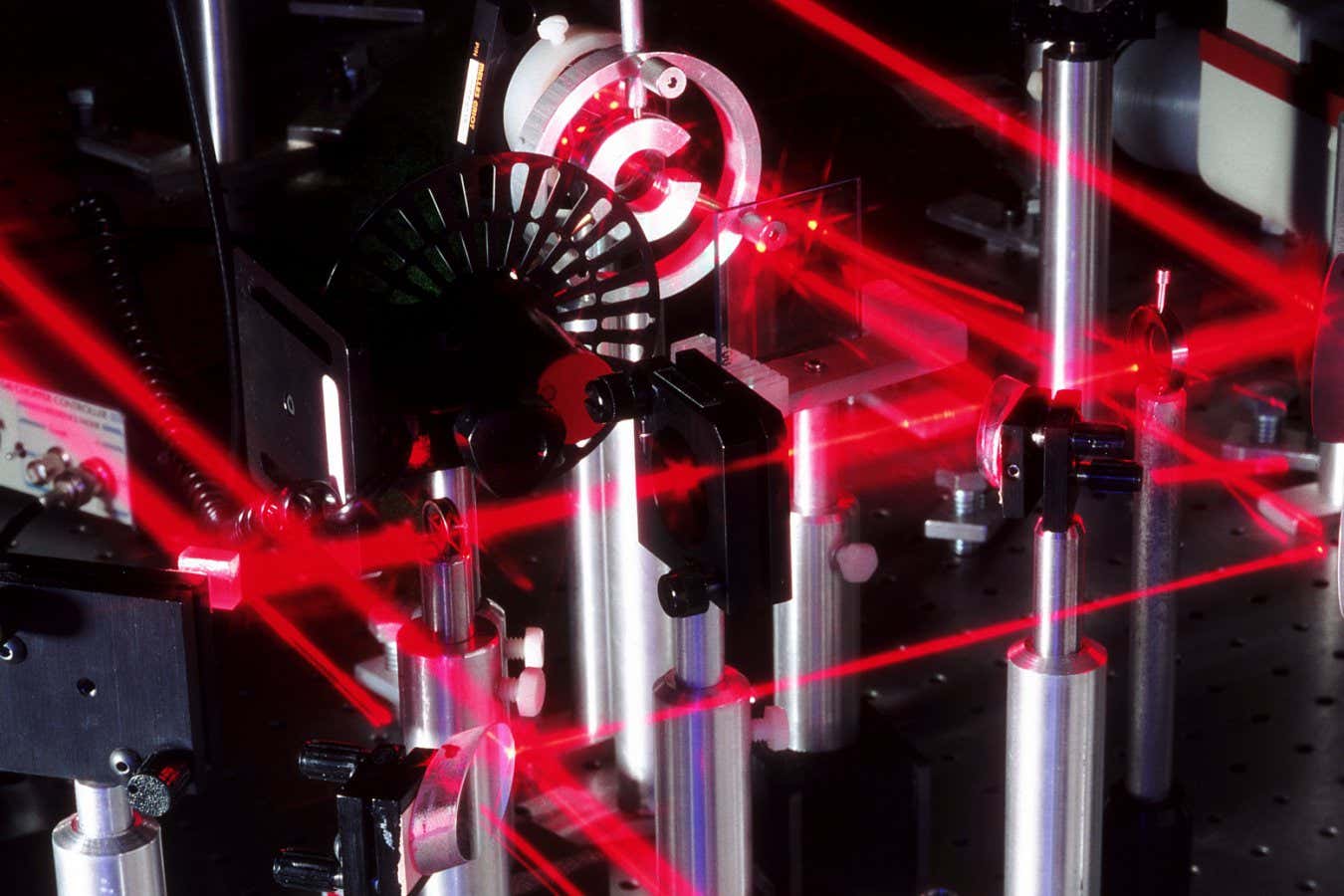
Software developers, especially those working with cryptocurrencies, are once again facing a supply chain attack via open source code repositories.
Cybersecurity researchers from Phylum have warned a threat actor has uploaded hundreds of malicious packages to the open source package repository npm. The packages are typosquatted versions of Puppeteer and Bignum.js. Developers who are in need of these packages for their products, might end up downloading the wrong version by mistake, since they all come with similar names.
If used, the package will connect to a hidden server, fetch the malicious second-stage payload, and infect the developers’ computers. “The binary shipped to the machine is a packed Vercel package,” the researchers explained.
Hiding the IP address
Furthermore, the attackers wanted to execute something else during package installation, but since the file wasn’t included in the package, the researchers couldn’t analyze it. “An apparent oversight by the malicious package author,” they say.
What makes this campaign stand out from other similar typosquatting supply chain campaigns is the lengths the crooks went to hide the servers they controlled.
“Out of necessity, malware authors have had to endeavor to find more novel ways to hide intent and to obfuscate remote servers under their control,” the researchers said. “This is, once again, a persistent reminder that supply chain attacks are alive and well.”
The IP cannot be seen in the first-stage code. Instead, the code will first access an Ethereum smart contract, where the IP is stored. This ended up being a double-edged sword, since the blockchain is permanent and immutable, and thus allowed the researchers to observe all of the IP addresses the crooks ever used.
Since the targets are developers working with cryptocurrency, the goal was most likely to steal their seed phrases, and gain access to their wallets.
Software developers, particularly those working in the Web3 space, are often targets of such attacks. Therefore, double-checking the names of all downloaded packages is a must.
Via Ars Technica




























































































































































You must be logged in to post a comment Login