Tech
Analysis of one billion CISA KEV remediation records exposes limits of human-scale security


Author: Saeed Abbasi, Senior Manager, Threat Research Unit, Qualys
With Time-to-Exploit now at negative seven days and autonomous AI agents accelerating threats, the data no longer supports incremental improvement. The architecture of defense must change.
What Leaders Need to Know
Analysis of CISA’s Known Exploited Vulnerabilities over the past four years shows critical vulnerabilities still open at Day 7 worsened from 56% to 63% despite teams closing 6.5x more tickets. Staffing cannot solve this.
Of the 52 tracked weaponized vulnerabilities in our study, 88% were patched more slowly than they were exploited — half were weaponized before any patch existed.
The problem is not speed. It is the operational model itself.
Cumulative exposure, not CVE counts, is the true risk metric that security teams now need to measure. While dashboards reward the sprint to get patches implemented, breaches exploit the tail. AI is not another attack surface — instead, the transition period where AI-powered attackers face human defenders is the industry’s most dangerous window.
In response, defenders have to implement their own autonomous, closed-loop risk operations.
The Broken Physics
New research from the Qualys Threat Research Unit, analyzing more than one billion CISA KEV remediation records from across 10,000 organizations over four years, quantifies what the industry has long suspected but never proved at scale. The operational model underpinning enterprise security is broken.
Vulnerability volumes have grown 6.5 times since 2022. According to Google M-Trends 2026, the average Time-to-Exploit has collapsed to negative seven days; in other words, adversaries are weaponizing the most serious vulnerabilities before patches exist. The percentage of critical vulnerabilities still open at seven days has climbed from 56 percent to 63 percent.
Yet this is not for lack of effort. Organizations closed 400 million more vulnerability events annually now than they did at baseline. Teams work harder, but it fails to make the difference where it counts. Our researchers call this the “human ceiling” — a structural limit no amount of staffing or process maturity can overcome. The constraint is not effort. It is the model itself.
Of 52 high-profile weaponized vulnerabilities tracked with complete exploitation timelines, 88 percent were remediated slower than they were exploited. As an example, Spring4Shell was exploited two days before disclosure, yet the average enterprise needed 266 days to remediate.
Similarly, the flaw in Cisco IOS XE was weaponized a month early; average close was 263 days.
The attacker’s advantage was measured in days. The defender’s response was measured in seasons. This is not an intelligence failure. It is an operationalization failure.
To understand the future around risk operations, AI and managing remediation at scale, come to ROCON EMEA, the Risk Operations Center Conference.
Join your peers and learn more about automated remediation.
The Manual Tax and Risk Mass
The report identifies a “Manual Tax” — the multiplier effect where long-tail assets that human processes cannot reach drag exposure from weeks into months. For Spring4Shell, average remediation was 5.4 times the median.
The median tells a manageable story. The average tells the truth. Infrastructure systems face a harsher reality: for Cisco IOS XE, even the median was 232 days — compared to endpoint medians consistently under 14. When the best-case outcome is eight months, the Manual Tax is no longer a multiplier. It is the baseline.
Looking at average figures is no longer helpful for decision-making. Instead, looking at Risk Mass — vulnerable assets multiplied by days exposed — captures what CVE counts obscure around cumulative exposure. A companion metric, Average Window of Exposure (AWE), measures the full duration from weaponization to remediation across the environment.
As an example, Follina was weaponized 30 days before disclosure with an average close at Day 55.
However, the AWE stretched to 85 days. While the blind spot before disclosure accounted for 36 percent of that 85 days, the long tail of patching accounted for a further 44 percent. In total, pre-disclosure and long tail together represent 80 percent. The sprint that gets measured makes up less than 20.
At the same time, of 48,172 vulnerabilities disclosed in 2025, only 357 were remotely exploitable and actively weaponized. Organizations are burning remediation cycles on theoretical exposure while genuinely exploitable gaps persist.
Why the Gap Will Widen
Cybersecurity has long operated as a derivative of technology shifts — Windows security followed Windows, cloud security followed cloud. Leading practitioners and investors now argue AI breaks that pattern. It is not merely a new surface to defend; it is a fundamental transformation of the adversary itself.
Offensive agents can already discover, weaponize, and execute faster than any human-staffed operation can respond. The remediation data proves humans cannot keep pace today. Autonomous AI ensures the gap will accelerate tomorrow.
The transition period — where AI-powered attackers face human-speed defenders — represents the industry’s most dangerous window, compounded by the structural vulnerabilities that dominate the near term: attack surfaces expanded beyond what teams can govern, identity sprawl that outpaces policy, and remediation workflows still built on manual execution.
The traditional scan-and-report model was built for lower volumes of CVEs and longer exploit timelines. What replaces it is an end-to-end Risk Operations Center: embedded intelligence arriving as machine-readable decision logic, active confirmation validating whether a vulnerability is actually exploitable in a specific environment, and autonomous action compressing response to the timescale the threat demands.
The objective is not to eliminate human judgment but to elevate it, shifting practitioners from tactical execution to governing the policies that direct their own autonomous systems.
The organizations already winning the physics gap are not winning with larger teams. They are winning because they have removed human latency from the critical path.
How Security Teams can close the Risk Gap
The scan-and-report model — discover, score, ticket, manually route — was built for lower volumes and longer exploit timelines.
What replaces it is an end-to-end Risk Operations Center: embedded intelligence arriving as machine-readable decision logic, active confirmation validating whether a vulnerability is actually exploitable in a specific environment, and autonomous action compressing response to the timescale the threat demands.
The objective is not to eliminate human judgment but to elevate it — shifting practitioners from tactical execution to governing the policies that direct autonomous systems. The organizations already winning the physics gap are not winning with larger teams. They are winning because they have removed human latency from the critical path.
Time-to-Exploit will not return to positive numbers. Vulnerability volume will not plateau. The reactive model has hit a hard mathematical ceiling.
The only remaining question is whether organizations will use the architecture to match the mathematics — before the window between human-scale defense and autonomous-scale offense closes for good.
Contact Qualys for insights into how companies manage remediation at scale with automation and AI, and how you can make that difference right now.
Sponsored and written by Qualys.
Tech
The Beats Studio Buds+ drop to $99, and they’re the wireless earbuds I’d recommend for iPhone and Android users alike


The Beats Studio Buds+ are down to $99.95, a $70 saving off their $169.95 list price, and that gets you true wireless noise canceling, spatial audio, and sweat resistance at a price that most competing earbuds with this feature set can’t touch. For anyone using an iPhone or an Android device, these cover the bases better than most things at this price.
What you’re getting
The Studio Buds+ improved on the original Studio Buds in two meaningful ways: better ANC performance and the addition of spatial audio, which delivers a more immersive, three-dimensional listening experience on compatible content. The noise-canceling handles commuting and office environments well, and transparency mode is responsive enough to actually use when you need to stay aware of your surroundings.
What sets the Studio Buds+ apart from most earbuds at this price is the cross-platform compatibility. They pair seamlessly with iPhone through the Apple ecosystem while offering full Android integration through the Beats app, one-touch Google Assistant access, and Find My Device support. Most earbuds at this price favor one platform at the expense of the other; the Studio Buds+ don’t make that compromise.
The built-in microphone handles calls clearly, the IPX4 sweat resistance makes them a practical gym companion, and the compact charging case keeps the overall package travel-friendly.
Why it’s worth it
Spatial audio and ANC together in a wireless earbud typically push the price well above $100. The Beats Studio Buds+ at $99.95 bring both to a price point where the decision becomes considerably easier, particularly for anyone who switches regularly between Apple and Android devices and doesn’t want to sacrifice features to do so.
The bottom line
The Beats Studio Buds+ at $99.95 are a well-rounded wireless earbud at a price that makes the feature set look considerably more expensive than it is. The ANC, spatial audio, and genuine dual-platform compatibility add up to an earbud that’s difficult to beat at this price, and the $70 saving makes it the right time to pick them up.
Tech
South Korea moves to curb the meteoritic rise of DRAM and PC hardware prices
Conditions in the hardware market remain strained, with prices for nearly all components rising sharply as AI companies place unprecedented pressure on supply chains for future demand. In this environment, stricter market regulation may be warranted, but there appears to be little appetite in Washington for increased government intervention.
Read Entire Article
Source link
Tech
Garmin may be working on a Whoop competitor

Whoop, the makers of a screen-free fitness tracker of the same name, could soon have some competition. Fitbit teased its take on a Whoop-style band with the help of Steph Curry at the end of March, and based on a trademark filing spotted by Gadgets & Wearables, Garmin appears to be working on its own band that tracks similar health metrics.
This new Garmin wearable, called “CIRQA” in the trademark filing submitted in February, is designed to measure “the body’s physical parameters and other physiological data, bio-signals, and bodily behavior.” That could broadly describe the smartwatches and fitness trackers Garmin already sells. But the CIRQA apparently goes further, by also measuring “recovery from physical and emotional stress, human alertness level, and performance,” a set of more granular, wellness-focused features that could bring the unreleased wearable into the same ballpark as a Whoop.
Garmin accidentally leaked that it was working on a new wearable via a hastily removed store page in January, Android Authority reports. While some phantom web pages and a trademark do not guarantee Garmin is working on a new device, or that the band will be screen-free in the same way the Whoop is. If the company is preparing a competitor, though, the timing makes sense. Where other devices try to split the difference between tracking biometrics and offering real-time information or other smartwatch features, Whoop is decidedly data-first. Its wearables monitor as much information as possible through a nondescript band, and then analyze and display what it learned via a smartphone app. The approach is attractive to anyone tired of dealing with screens, and the growing number of people obsessed with optimizing their health. In fact, Whoop just raised $575 million on the back of its current success. It would make sense that Garmin and Google (via its Fitbit brand) would want a piece of the company’s audience, too.
Whoop-style bands are also a perfect fit for future uses of AI in health and fitness tracking. Google is interested in having users turn to Fitbit’s AI-powered health coach for everything from workout tracking to nutrition advice. If health data processing is going to happen in the cloud, and you’re going to have to pull out your smartphone to view that data anyway, it makes sense to sell a tracker without a screen.
Tech
The FAA is encouraging gamers to get jobs in air traffic control

Sick! The Federal Aviation Administration is targeting gamers in its most recent job advertisement for air traffic controllers. The administration’s annual hiring window opens at 12AM ET on April 17, and considering the ongoing shortage of air traffic controllers, it’s calling this a period of “supercharged hiring.” Rad! The FAA’s YouTube video draws parallels between gaming and directing air traffic, and notes that the average salary for the role after three years is $155,000. Hella!
The FAA is clearly seeking players who are at least old enough to remember the Xbox One and Bjergsen in the LCS, which puts would-be candidates around their early 20s at least. It’s either that, or the ad editors really just picked videos at random from the pile of stock footage marked gamerz. But I won’t lie, it made me smile to see that Xbox One logo appear out of nowhere. Nostalgia is a hell of a thing.
“To reach the next generation of air traffic controllers, we need to adapt,” US Transportation Secretary Sean P. Duffy said. “This campaign’s innovative communication style and focus on gaming taps into a growing demographic of young adults who have many of the hard skills it takes to be a successful controller.”
The FAA has been losing more air traffic controllers than it can hire and retain since the 2010s, and this trend only worsened during the pandemic in the 2020s, according to a report released in December by the US Government Accountability Office. The administration increased hiring every year since 2021, but at the end of 2025 it employed 13,164 air traffic controllers, 6 percent fewer than in 2015, the report said. At the same time, the number of flights in the air traffic control system increased by about 10 percent, to 30.8 million.
Or, as the FAA put it on the ATC hiring page: “Join the BEST AND BRIGHTEST, the elite squad of 14,000 controllers protecting 2.9 million daily passengers.” Applicants must be a US citizen, under 31 (maybe those video editors do know what they’re doing), and be able to speak fluent English. An aptitude test, medical screening and academy training follows, among other steps.
Tech
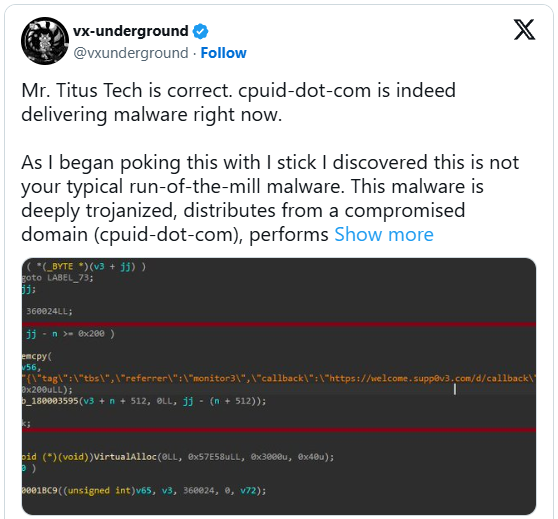
CPUID Site Hijacked To Serve Malware Instead of HWMonitor Downloads

Attackers briefly hijacked part of CPUID’s backend and swapped legitimate download links on its site with malware-laced ones. “The issue hit tools like HWMonitor and CPU-Z, with users on Reddit and elsewhere starting to notice something wasn’t right when installers tripped antivirus alerts or showed up under odd names,” reports The Register. From the report: CPUID has since confirmed the breach, pinning it on a compromised backend component rather than tampering with its software builds. “Investigations are still ongoing, but it appears that a secondary feature (basically a side API) was compromised for approximately six hours between April 9 and April 10, causing the main website to randomly display malicious links (our signed original files were not compromised),” one of the site’s owners said in a post on X. “The breach was found and has since been fixed.”
The files themselves appear to have been left alone and remain properly signed, so it doesn’t seem like anyone got into the build process. Instead, the problem sat in front of that, in how downloads were being served. For anyone who hit the site during that stretch, though, that distinction offers little comfort. If the link you clicked had been swapped out, you were pulling whatever it pointed to, whether you realized it or not.
Tech
CPUID hacked to deliver malware via CPU-Z, HWMonitor downloads
Hackers gained access to an API for the CPUID project and changed the download links on the official website to serve malicious executables for the popular CPU-Z and HWMonitor tools.
The two utilities have millions of users who rely on them for tracking the physical health of internal computer hardware and for comprehensive specifications of a system.
Users who downloaded either tool reported on Reddit recently that the official download portal points to the Cloudflare R2 storage service and fetches a trojanized version of HWiNFO, another diagnostic and monitoring tool from a different developer.
The name of the malicious file is HWiNFO_Monitor_Setup, and running it launches a Russian installer with an Inno Setup wrapper, which is atypical and highly suspicious.
Users reported that downloading the clean hwmonitor_1.63.exe from the direct URL was still possible, indicating that the original binaries were intact, but the distribution links appear to have been poisoned.
The externalized download chain was also confirmed by Igor’s Labs and @vxunderground, who reported that a fairly advanced loader using known techniques, tactics, and procedures (TTPs) is involved.
“As I began poking this with a stick, I discovered this is not your typical run-of-the-mill malware,” stated vxunderground.
“This malware is deeply trojanized, distributes from a compromised domain (cpuid-dot-com), performs file masquerading, is multi-staged, operates (almost) entirely in-memory, and uses some interesting methods to evade EDRs and/or AVs such as proxying NTDLL functionality from a .NET assembly.”
The researcher claims that the same threat group targeted users of the FileZilla FTP solution last month, suggesting that the attacker is focusing on widely used utilities.
The downloaded ZIP is flagged by 20 antivirus engines on VirusTotal, although not clearly identified. Some classify it as Tedy Trojan, and others as Artemis Trojan.
Some researchers on Virustotal say that the fake HWiNFO variant is an infostealer malware.
BleepingComputer has contacted CPUID to learn more about what happened, the date of the compromise, the affected versions, and what impacted users should do. A spokesperson has provided the following statement.
“Investigations are still ongoing, but it appears that a secondary feature (basically a side API) was compromised for approximately six hours between April 9 and April 10, causing the main website to randomly display malicious links (our signed original files were not compromised). The breach was found and has since been fixed.” – CPUID
The same person told us that the hackers hit them at a time when the main developer was away on holiday.
Currently, it appears that CPUID has fixed the problem and now serves clean versions for both CPU-Z and HWMonitor.
Tech
The Artemis II astronauts are back after a 10-day journey around the moon

The Orion capsule carrying the Artemis II astronauts has successfully splashed down off the coast of San Diego at 8:07PM Eastern time on April 10. It signals the conclusion of Artemis II’s 10-day journey around the moon, which is meant to be a test flight for a future mission that would bring humanity back to the lunar surface. The Orion crew module carrying the mission’s astronauts separated from the service module at 7:33 PM. While the service module was designed to burn up in the Earth’s atmosphere, the crew capsule was built to bring the astronauts back home safely.
By 7:53 PM, Orion reached our planet’s upper atmosphere, where a six-minute communication blackout occurred due to the capsule heating up as it started its guided descent. The capsule has 11 parachutes, with its drogue parachutes being deployed at 23,400 feet to stabilize and slow it down. When Orion reached 5,400 feet above the ground, the drogue parachutes were cut off so that the three main parachutes could be deployed. That decreased the capsule’s velocity to 200 feet per second, enabling a safe splashdown.
NASA’s engineers conducted several tests while the capsule was in the water before the recovery team headed to the capsule on inflatable boats to extract the crew from Orion. By 9:34 PM, all four crew members were out of the capsule. They were then hoisted into helicopters and flown to the USS John P. Murtha dock ship, where doctors will assess their health.
Artemis II launched on April 1 with four astronauts on board: NASA’s Reid Wiseman, Victor Glover and Christina Koch, as well as Canadian Space Agency’s Jeremy Hansen. They traveled around the moon for almost 10 days, reaching distances no other crewed mission has before it. The astronauts took photos of the far side of the moon, the side we don’t see from our planet, including amazing closeups of the lunar surface using their smartphones. That makes them the first humans to directly and personally view the lunar far side.
During NASA’s post-splashdown news conference, the agency said it will announce the Artemis III crew soon. Artemis III will rendezvous with one or both commercial landers being developed by SpaceX and Blue Origin in low Earth orbit, which will take humans to the lunar surface. It will test the lander’s ability to dock with Orion before NASA lands humans on the moon again.
Tech
Artemis II Astronauts Are Home Safe

Here’s the astronauts’ out-of-this-world menu.
Astronaut eats: they’re not just Tang and Space Food Sticks these days. NASA shared a look at the menu for the Artemis II astronauts, and it doesn’t sound half bad.
The Artemis II crew will enjoy more than 10 types of beverages, including coffee, mango-peach smoothies, green tea, apple cider, lemonade, a pineapple drink, cocoa and breakfast drinks flavored in their choice of chocolate, vanilla or strawberry.
The most common food items they’ll eat include tortillas, wheat flat bread, vegetable quiche, barbecued beef brisket, mango salad, granola with blueberries, macaroni and cheese, tropical fruit salad, couscous with nuts, broccoli au gratin, spicy green beans, almonds, cashews, and butternut squash cauliflower.
NASA also reports that the astronauts can choose to spice up their meals — there are five different hot sauces available to the crew. And culinary flavorings available include maple syrup, chocolate spread, peanut butter, spicy mustard, strawberry jam, honey, cinnamon and almond butter. Sweet treats include cookies, chocolate, pudding, cake, candy-coated almonds and cobbler.
And, no, they’re not popping a flavor pill or sucking a sandwich out of a tube, like old sci-fi shows told us.
“Food aboard Orion is ready-to-eat, rehydratable, thermostabilized or irradiated,” NASA says. “The crew uses Orion’s potable water dispenser to rehydrate foods and beverages and a compact, briefcase-style food warmer to heat meals as needed.”
Tech
Today’s NYT Mini Crossword Answers for April 11
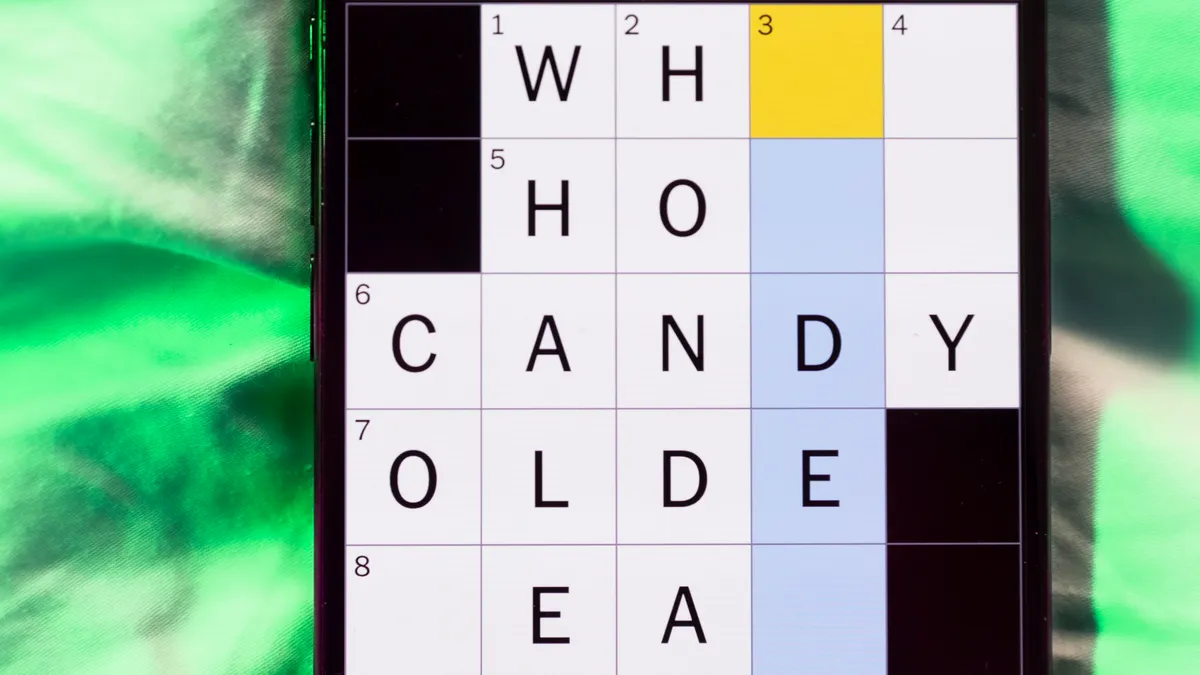
Looking for the most recent Mini Crossword answer? Click here for today’s Mini Crossword hints, as well as our daily answers and hints for The New York Times Wordle, Strands, Connections and Connections: Sports Edition puzzles.
Need some help with today’s Mini Crossword? It’s the longest of the week, the Saturday edition. Read on for all the answers. And if you could use some hints and guidance for daily solving, check out our Mini Crossword tips.
If you’re looking for today’s Wordle, Connections, Connections: Sports Edition and Strands answers, you can visit CNET’s NYT puzzle hints page.
Read more: Tips and Tricks for Solving The New York Times Mini Crossword
Let’s get to those Mini Crossword clues and answers.
The completed NYT Mini Crossword puzzle for April 11, 2026.
Mini across clues and answers
1A clue: N.B.A. team that plays at M.S.G.
Answer: KNICKS
7A clue: Guy with a nerdy, passionate interest
Answer: FANBOY
8A clue: Rudely merges
Answer: CUTSIN
9A clue: Standard number of bowling pins
Answer: TEN
10A clue: Inflated sense of one’s own importance
Answer: BIGEGO
13A clue: Arrived via airplane
Answer: FLEWIN
14A clue: History-making achievements, perhaps
Answer: FIRSTS
Mini down clues and answers
1D clue: Colonel Sanders’s fast-food chain
Answer: KFC
2D clue: Spiral-shelled mollusks
Answer: NAUTILI
3D clue: 1, 2 or 3, but not 1.23
Answer: INTEGER
4D clue: “60 Minutes” producer
Answer: CBSNEWS
5D clue: Colorful pond fish
Answer: KOI
6D clue: Thesaurus listing: Abbr.
Answer: SYN
10D clue: Closest pal, for short
Answer: BFF
11D clue: “Go on, ___!” (“Scram!”)
Answer: GIT
12D clue: Opposite of offs
Answer: ONS
Tech
iPhone Fold, MacBook Neo, and iPhones in Space, on the AppleInsider Podcast

There is a huge amount to say about the latest iPhone Fold rumors, and a lesson for Apple in how the MacBook Neo could even be too successful, on the AppleInsider Podcast.

Even on Earth, iPhones are so light they feel as if they could float
After months or even really years of rumors and expectations over the iPhone Fold, it really does look as if one is coming. There’s still the issue of when, as conflicting reports are arguing over a range of dates, but they all agree it’s coming.
Not all of them can agree on why, though. If only to save you unnecessarily buying the single most expensive iPhone ever conceived, we’ve got reasons why you should and shouldn’t buy it. And we’ve got reasons why it will probably be worth waiting.
Continue Reading on AppleInsider | Discuss on our Forums
-

 Business5 days ago
Business5 days agoThree Gulf funds agree to back Paramount’s $81 billion takeover of Warner, WSJ reports
-

 Sports6 days ago
Sports6 days agoIndia men’s 4x400m and mixed 4x100m relay teams register big progress | Other Sports News
-

 Politics14 hours ago
Politics14 hours agoUS brings back mandatory military draft registration
-

 Fashion14 hours ago
Fashion14 hours agoWeekend Open Thread: Veronica Beard
-

 Tech3 days ago
Tech3 days agoHow Long Can You Drive With Expired Registration? What Florida Law Says
-

 Business6 days ago
Business6 days agoNo Jackpot Winner, Prize to Climb to $231 Million
-

 Fashion5 days ago
Fashion5 days agoMassimo Dutti Offers Inspiration for Your Summer Mood Board
-

 Sports15 hours ago
Sports15 hours agoMan United discover Nico Schlotterbeck transfer fee as defender reaches Dortmund agreement
-

 Fashion4 days ago
Fashion4 days agoLet’s Discuss: DEI in 2026
-

 Crypto World3 days ago
Crypto World3 days agoBitcoin recovers as US and Iran Agree a Ceasefire Deal
-

 Business11 hours ago
Business11 hours agoTesla Model Y Tops China Auto Sales in March 2026 With 39,827 Registrations, Beating Cheaper EVs and Gas Cars
-

 Business6 days ago
Business6 days agoAkebia Therapeutics, Inc. (AKBA) Discusses Pipeline Progress and Strategic Focus on Kidney Disease Treatments at R&D Day – Slideshow
-

 Crypto World2 days ago
Crypto World2 days agoCanary Capital Files SEC Registration for PEPE ETF
-

 Business20 hours ago
Business20 hours agoOpenAI Halts Stargate UK Data Centre Project Over Energy Costs and Copyright Row
-

 Tech5 days ago
Tech5 days agoHaier is betting big that your next TV purchase will be one of these
-

 Tech5 days ago
Tech5 days agoGamer Restores the Original PlayStation Portal From Two Decades Ago
-
 Tech5 days ago
Tech5 days agoThe Xiaomi 17 Ultra has some impressive add-ons that make snapping photos really fun
-
 Tech5 days ago
Tech5 days agoSamsung just gave up on its own Messages app
-

 Tech5 days ago
Tech5 days agoSave $130 on the Samsung Galaxy Watch 8 Classic: rotating bezel, sleep coaching, and running coach for $369
-

 Tech5 days ago
Tech5 days agoItalian court says Netflix must refund customers up to $576 over price hikes













You must be logged in to post a comment Login