Tech
Critical flaw in Protobuf library enables JavaScript code execution


Proof-of-concept exploit code has been published for a critical remote code execution flaw in protobuf.js, a widely used JavaScript implementation of Google’s Protocol Buffers.
The tool is highly popular in the Node Package Manager (npm) registry, with an average of nearly 50 million weekly downloads. It is used for inter-service communication, in real-time applications, and for efficient storage of structured data in databases and cloud environments.
In a report on Friday, application security company Endor Labs says that the remote code execution vulnerability (RCE) in protobuf.js is caused by unsafe dynamic code generation.
The security issue has not received an official CVE number and is currently being tracked as GHSA-xq3m-2v4x-88gg, the identifier assigned by GitHub.
Endor Labs explains that the library builds JavaScript functions from protobuf schemas by concatenating strings and executing them via the Function() constructor, but it fails to validate schema-derived identifiers, such as message names.
This lets an attacker supply a malicious schema that injects arbitrary code into the generated function, which is then executed when the application processes a message using that schema.
This opens the path to RCE on servers or applications that load attacker-influenced schemas, granting access to environment variables, credentials, databases, and internal systems, and even allowing lateral movement within the infrastructure.
The attack could also affect developer machines if those load and decode untrusted schemas locally.
The flaw impacts protobuf.js versions 8.0.0/7.5.4 and lower. Endor Labs recommends upgrading to 8.0.1 and 7.5.5, which address the issue.
The patch sanitizes type names by stripping non-alphanumeric characters, preventing the attacker from closing the synthetic function. However, Endor comments that a longer-term fix would be to stop round-tripping attacker-reachable identifiers through Function at all.
Endor Labs is warning that “exploitation is straightforward,” and that the minimal proof-of-concept (PoC) included in the security advisory reflects this. However, no active exploitation in the wild has been observed to date.
The vulnerability was reported by Endor Labs researcher and security bug bounty hunter Cristian Staicu on March 2, and the protobuf.js maintainers released a patch on GitHub on March 11. Fixes to the npm packages were made available on April 4 for the 8.x branch and on April 15 for the 7.x branch.
Apart from upgrading to patched versions, Endor Labs also recommends that system administrators audit transitive dependencies, treat schema-loading as untrusted input, and prefer precompiled/static schemas in production.
Tech
A comet gets destroyed by the sun, data centers endanger the Potomac River, and more science news
The Artemis II astronauts are settling back into life on Earth, but we’re not quite tired yet of hearing about their amazing journey. There’s a new PBS documentary now streaming on YouTube that dives into the Artemis program and the latest efforts to send humans to the moon again. Also this week, NASA shared some awesome images of a comet flying into the sun, the nonprofit American Rivers released its annual report on the most endangered rivers in the US and ESA posted a throwback image of Mars to highlight some interesting changes down on the surface. Here are the science stories that caught our attention this week.
A comet grazes too close to the sun
Earlier this month, a recently discovered comet made a close approach to the sun — but it couldn’t handle the heat. NASA has shared incredible images of the encounter that took place on April 4, showing the comet exploding into dust as it swings around our star. As NASA notes in a social media post, this was “its first and last observed flyby of the Sun.”
The comet, C/2026 A1 (also known as MAPS) was first spotted on January 13 of this year. As it neared the sun, it was observed by a slew of instruments: NASA and ESA’s SOHO (Solar and Heliospheric Observatory) spacecraft, NASA’s STEREO (Solar Terrestrial Relations Observatory) and NASA’s PUNCH (Polarimeter to Unify the Corona and Heliosphere). This allowed for views of its passage from multiple angles. Seen in a narrow-field coronagraph view captured by SOHO, the comet appears to plunge directly into the sun. But, the wide view from NASA’s STEREO shows it actually swinging closely around the sun before breaking apart.
MAPS was one of a family of comets aptly called Kreutz sungrazing comets, and according to Karl Battams, the principal investigator for SOHO’s coronagraph, its destruction occurred likely several hours before what would have been its closest approach.
Potomac named most endangered river in the US
The nonprofit conservation organization American Rivers has released its 2026 report on the most endangered rivers in the country, and data centers play a major role in the status of its top pick. According to American Rivers, the Potomac River is the most endangered in the US due both to the threat of sewage pollution from aging pipe systems and the “unprecedented surge in data center development” in its vicinity.
The Potomac River basin spans parts of Pennsylvania, Maryland, Virginia, West Virginia and Washington, DC. In January, the catastrophic failure of the Potomac Interceptor wastewater pipe in Montgomery County, Maryland dumped hundreds of millions of gallons of untreated sewage into the Potomac River and the Chesapeake and Ohio (C&O) Canal, causing bacteria levels to hit over 4,000 times the safe recreational limit at sites closest to the incident, according to the report. The Potomac Interceptor is over 60 years old, and is just one of many in the region that is at or past the 50-year service life, American Rivers notes.
On top of that, data center development in places like Virginia and Maryland has skyrocketed, which could put a strain on local water and energy sources. Data centers also have potential to cause further pollution to the river.
“The region currently has over 300 data centers and is on track to have a total of about 1,000 centers occupying roughly 200 million square feet of buildings — enough to cover 3,472 football fields — on an estimated 20,000 acres of land,” the report explains. “These facilities pose a significant and growing threat to both water quality and water quantity, yet are being approved without meaningful transparency, regulatory review, and assessment of cumulative impacts.”
The organization is calling for Congress to reauthorize infrastructure funding bills so aging systems can be upgraded, and for regulators in these states to require transparency about data centers’ resource use, along with comprehensive environmental assessments before development plans are approved.
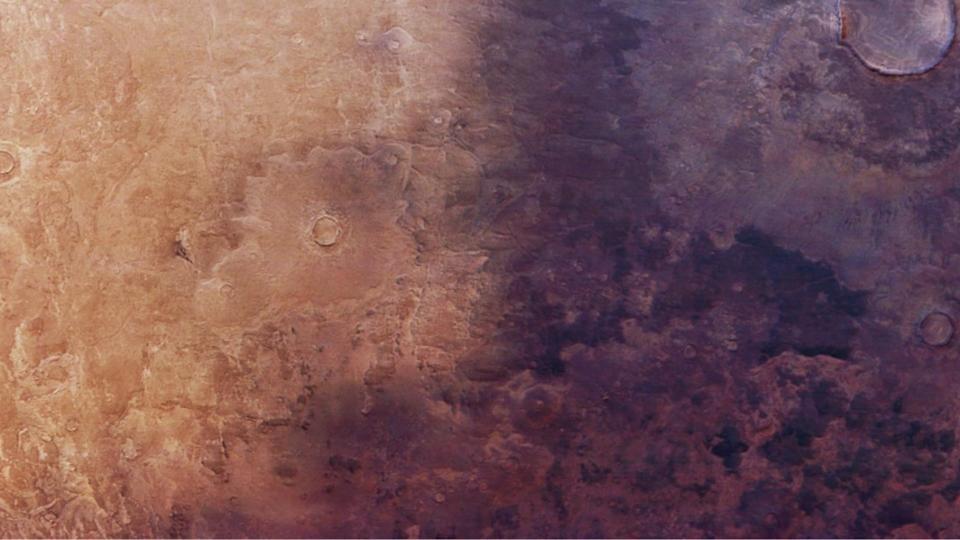
Mars ash: then vs now

ESA/DLR/FU Berlin
The European Space Agency this week shared a look at how a region on Mars has changed since it was observed by NASA’s Viking orbiters way back in 1976. New images captured by ESA’s Mars Express spacecraft show how dark volcanic ash has encroached upon a swath of land in an area known as the Utopia Planitia basin. If you visit the blog post, you’ll find a side by side comparison of images from the two time periods.
It’s a rare example of an observable change on the surface of the red planet that’s occurred over such a short period of time, ESA notes. The agency explains, “The spread of the ash over the last 50 years has two possible explanations: either it has been picked up and moved about by martian winds, or the ochre dust that previously covered the dark ash has been blown away.”
Before you go, be sure to check these stories out too:
Tech
Rockstar On Latest Potential Hack & Information Leak: Meh, We Don’t Care

from the this-is-the-way dept
Several years ago, Rockstar Games suffered an intrusion into its corporate network. During that intrusion, a trove of data, files, and information about the in-development and unfinished Grand Theft Auto 6 game was exfiltrated. Under monetary threat of that data leaking, Rockstar completely lost its mind and went on a DMCA takedown campaign to try to remove any leaked content or footage that was being teased by the hacker in circulation. Readers here will already know that this kind of DMCA whac-a-mole never works and instead served only to Streisand the whole story into wider consciousness, working directly against Rockstar’s purposes in the first place.
Today, Rockstar is under threat of a similar leak. The company has acknowledged that hacking group ShinyHunters gained access to Rockstar information through a third-party data breach, namely that of Anodot, and has threatened to leak all that data if it isn’t paid by Rockstar.
ShinyHunters claim to have breached Rockstar’s outsourced Snowflake cloud storage system by way of a third-party analytics tool, Anodot, which reportedly suffered its own breach recently. With authentication tokens from Anodot, ShinyHunters would not have needed to crack Snowflake’s security directly. They would have just been recognized as an authorized party and let in through the front door, like Agent 47 in a security guard outfit. ShinyHunters claims to have had access to Rockstar’s database for a significant amount of time before it was realized anything was amiss.
“Your Snowflake instances were compromised thanks to Anodot.com. Pay or leak,” ShinyHunters wrote in a post on their site. “This is a final warning to reach out by 14 Apr 2026 before we leak along with several annoying (digital) problems that’ll come your way. Make the right decision, don’t be the next headline.”
Unlike the previous hack and threat of a leak, however, Rockstar appears to be taking a completely different tactic. In addition to once again refusing to pay any ransom, which is absolutely the correct course of action, the company has also basically shrugged its shoulders over this entire situation.
Rockstar quickly responded to Kotaku saying that while “a limited amount of non-material company information was accessed,” the incursion would have “no impact on our organization or our players.”
There’s still no clear idea of what data has been taken, but Rockstar is certainly playing it very cool. ShinyHunters, should it go through with plans to publish the information, will likely post it to its dark web pages from which it’ll eventually filter to the wider public.
Now, I want to be careful to not give Rockstar any undue credit here. As discussed below, the type of data that was gained in this particular breach is far more banal than the previous one, which included actual unfinished game footage, and perhaps it’s that which explains this change in stance.
But I would argue that this is mostly the right course even if that weren’t the case. You can’t bottle up the genie once the leak is out there, so you might as well put your PR hat on and engage with the public in a way that puts the company and the product in the best light, while also acknowledging the thirst for more information on the unreleased game.
This is something we’ve advocated for for years now. It’s a simple as putting out a statement roughly like:
Hey, everyone! We know there might be a leak about our company and the upcoming Grand Theft Auto title coming out soon and we know you’re interested in anything you can get your hands on about the game. We are too! We want you to see the game, but we do prefer you see it in its finished state. But if you can’t wait that long, we understand. Please just also understand that we are something of a victim in all of this. It kind of hurts and is frustrating to have our plans for this release get derailed by this kind of criminal activity, but all we ultimately care about is making sure you know just how awesome the next GTA is going to be!
Good will would abound, the hackers wouldn’t get the payout that wished for, and the company could appear awesome, and, more importantly, human. I very much hope that this response from Rockstar thus far is an indication that that’s where the company is headed with all of this.
In this case, ShinyHunters did eventually release the leaked info, and you can see why Rockstar didn’t care:
Looking at the structure of the data, it does appear to come from automated exports generated by analytics pipelines. The files are compressed CSV outputs, commonly used for batch reporting in cloud data platforms like Snowflake. This supports earlier reporting that the access point was not Rockstar’s core network but a third-party analytics integration, believed to involve Anodot.
Some of the files also reference internal monitoring and testing. For example, dataset names linked to cheat detection models and platform-level revenue mismatches suggest the data includes operational insights used by Rockstar teams to manage gameplay balance and detect abuse. There are also references to Zendesk ticket metrics and customer support reporting, indicating visibility into service operations rather than individual player accounts.
What is not present in the leaked material is just as important. There are no player credentials, account data, or unreleased game assets such as GTA VI content. That aligns with Rockstar’s earlier statement that the breach involved limited company information and did not impact players.
So perhaps Rockstar’s reaction is more explained by the lack of any really problematic content in the leak. But, still, it is a reminder that you don’t have to completely freak out over every leak.
Filed Under: breach, grand theft auto, hack, leak, shinyhunters
Companies: rockstar games
Tech
Daily Deal: Python Crash Course

from the good-deals-on-cool-stuff dept
The Python Crash Course is a guide on how to get started in Python, why you should learn it, and how you can learn it. The syntax of the language is clean and the length of the code is relatively short. In this comprehensive course, you will get in-depth knowledge in data types, loops, python command lines, docstrings, and much more. It’s fun to work in Python because it allows you to think about the problem rather than focusing on the syntax. If all this excites you, then join this python coding course today! It’s on sale for $11.
Note: The Techdirt Deals Store is powered and curated by StackCommerce. A portion of all sales from Techdirt Deals helps support Techdirt. The products featured do not reflect endorsements by our editorial team.
Filed Under: daily deal
Tech
Game Jam Winner Spotlight: Lilac Song
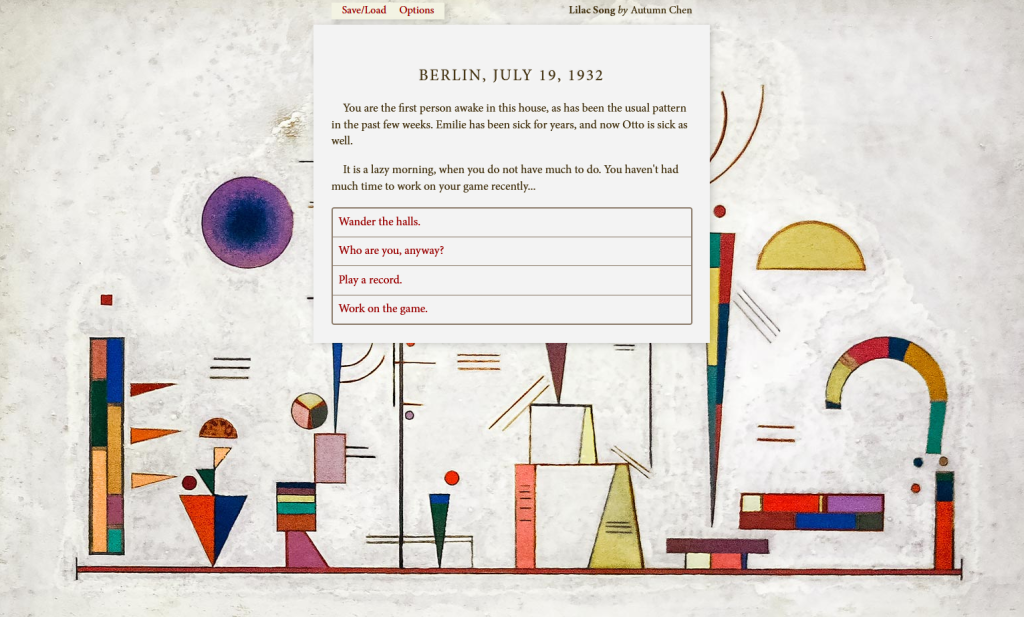
from the gaming-like-it’s-1930 dept
We’re past the halfway point in our series of spotlight posts looking at the winners of our eighth annual public domain game jam, Gaming Like It’s 1930! We’ve already covered the Best Adaptation, Best Deep Cut, and Best Visuals winners, and this week we’re looking at the winner of Best Remix: Lilac Song by Autumn Chen.
There were fewer interactive fiction submissions in this year’s jam than there often have been in past editions, but even if the field had been more crowded, Lilac Song would have undoubtedly stood out. It’s a somber, thoughtful story that casts the player as a servant to Prussian Minister-President Otto Braun during the last few years of the Weimar Republic. It revolves around and intriguing and fitting premise: the servant has been designing a simulation game about power and politics in Germany, from which she aims to draw insights that could preserve democracy and prevent the rise of Hitler and the Nazi Party.

The story is far more than a cursory look at these events: it’s clearly rooted in robust historical knowledge about this critical time and place, with myriad details about the specifics of the political situation as well as an additional exploration of gender politics and transgenderism in the era. But what’s especially notable for this jam is the way it weaves in a wide variety of artistic and musical works from 1930, which form the backdrop of its setting and the game itself. Amidst the story unfolding (and careening towards its inevitable ending) the player wanders the halls of Braun’s house and chooses paintings to admire and music to listen to. These works (by Paul Klee, Wassily Kandinsky, Felix Mendelssohn, and more) become the wallpaper and soundtrack of the game.

Though the story takes center stage, the careful selection and use of these public domain works lend verisimilitude to the story and polish to the game design, resulting in more immersion than the text alone could achieve. For employing a curated combination of newly-public-domain works that elevates the interactive fiction without overtaking it, Lilac Song is this year’s Best Remix.
Congratulations to Autumn Chen for the win! You can play Lilac Song in your browser on Itch. We’ll be back next week with another winner spotlight, and don’t forget to check out the many great entries that didn’t quite make the cut. And stay tuned for next year, when we’ll be back for Gaming Like It’s 1931!
Filed Under: copyright, game jam, games, gaming, gaming like it’s 1930, public domain, winner spotlight
Tech
Auto Enthusiast Scores Running Tesla Model 3 for Two Grand and Turns It Into Bare-Bones Go-Kart


Remmy Evans learned via a friend that a Tesla Model 3 was sitting in some guy’s driveway in Idaho. The owner had bought it cheaply with the intention of removing the drivetrain and installing it in an old car from the 1970s, but he abandoned the plan after realizing how much time the body work would take. Evans was able to negotiate a price of exactly $2k and walk away with a rolling chassis that was still capable of moving on its own.
The seats and steering wheel remained in place, as did the motors, battery pack, and center screen. Everything else had been stripped out. There were no body panels remaining, including the windshield. The tires were so worn down that you could see the wires through the rubber in a couple locations, and this car had been lying unregistered for at least two years. Nonetheless, the electric motors started immediately away, and the readout displayed a full battery charge.
Sale
Segway Ninebot S2 Electric Self-Balancing Scooter – Master Your Commute w/t 11.2 mph Max. Speed, 21.7 Mi…
- Speed & Range: Experience exhilarating rides with the Ninebot S2’s impressive top speed of 11.2 mph and range of 21.7 miles.
- Beginner-Friendly: Perfect for riders aged 16-50, the Segway S2 features a user-friendly learning mode, providing a smooth and gradual introduction.
- Adjustable & Supportive: Enjoy a customized fit tailored to your needs, as the Segway S2 accommodates heights ranging from 4’3″ to 6’6″ and supports…

Evans fitted it with bright red wheels and new tires so that it could really grip the road rather than destroying the tires every time he turned the wheel. As a safety measure, he looped a heavy-duty ratchet strap across his lap, similar to a makeshift harness. He also disabled the car’s road-sensing safety measures, allowing it to run freely in track mode.

However, charging was a potential disaster. The first attempt at a fast charger was unsuccessful since the adapter just would not fit the port. Evans went to a hardware store, got a cutting tool, and fixed the problem by cutting the top of the adaptor on the spot so it could slide in. Once connected, the battery charged to full capacity and the LCD displayed 212 miles of range remaining. Home charging took roughly 7 or 8 hours on a Level 2 unit, or closer to 14 hours on a standard wall plug.

So, with the car all fixed up, Evans took it for a test drive, and unexpectedly, it passed the test without drawing any unwelcome notice from the cops. Later practices included donuts in a parking lot, burnouts, and a few of open-road runs that exceeded 60 mph. Because there was no top, the wind blew directly into the automobile, but it handled perfectly. At a friend’s home, the stripped-down Tesla ripped over dirt berms, jumped off a tabletop jump, and just kept going. One of his buddies rode along and claimed it was similar to the three-wheeled roadster that some people enjoy, but more faster.

Heavy drifting around the lot had a toll on the battery, which depleted far faster than it would on a regular drive. After a long afternoon of zooming around, the range had dropped to just 18 miles remaining, yet the car still made it home with a mile to spare. There was only one evident drawback: the onboard computer was logging an alarming 78 error codes because all of the cameras and sensors were missing.
[Source]
Tech
As if the plate wasn’t already full, AI is about to worsen the global e-waste crisis
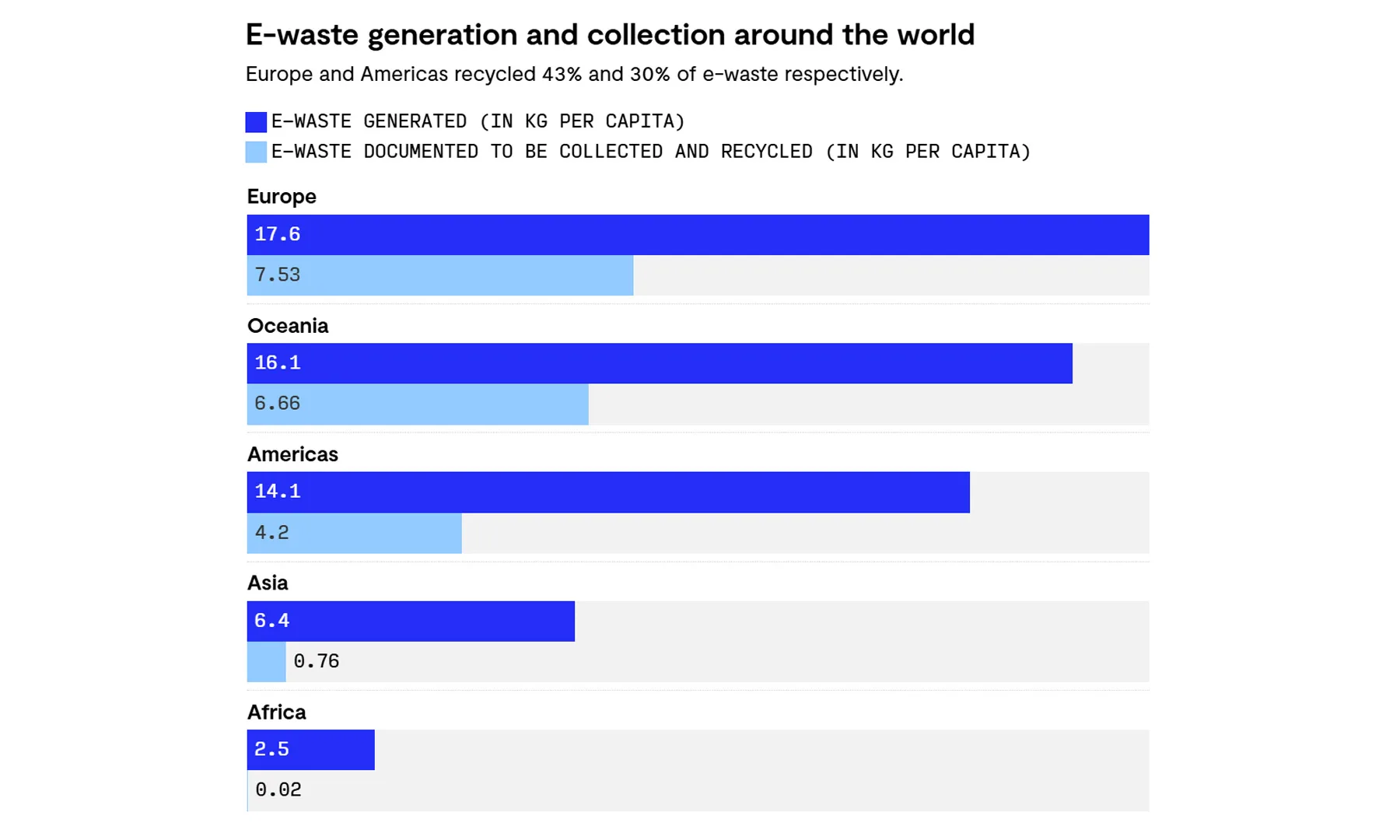
AI is already changing how the world works, but it’s also quietly making one of our biggest environmental problems even worse. And no, this isn’t about energy consumption this time. It’s about the hardware. Because every smarter AI model comes with a physical cost.
AI is about to supercharge the e-waste problem
According to a study published in Nature Computational Science (via Rest of World), the rapid rise of AI could add between 1.2 to 5 million metric tons of e-waste by 2030. The reason is pretty simple. AI relies on high-performance hardware like GPUs and specialized servers, and these don’t last very long. Most of this equipment gets replaced every 2 to 5 years, which means older hardware is quickly discarded as newer, faster systems take over.

And this is happening at scale. As companies race to build bigger data centers and train more powerful models, the demand for hardware keeps rising, along with the pile of obsolete machines left behind.
This isn’t just a tech problem but a global one
E-waste is already one of the fastest-growing waste streams in the world, with tens of millions of tonnes generated every year. And the worst part? A large chunk of it isn’t properly recycled. Improper handling can release toxic materials like lead and mercury into the environment, posing serious risks to both ecosystems and human health. And here’s the uncomfortable truth: most of this waste ends up in lower-income countries, where recycling often happens under unsafe conditions. That means that while the benefits of AI are global, the environmental cost is not equally shared.

At the end of the day, AI might feel like a purely digital revolution. But behind the scenes, it’s building a very real, very physical footprint. And if things don’t change, that footprint is only going to keep growing.
Tech
Where to Shop for Vinyl Records Online (2026): Discogs, Bandcamp, Ebay
For smaller releases, including LPs from midsize indie labels (Drag City, Kranky, Superior Viaduct), check out Midheaven Mailorder. This site is run by the San Francisco distributor Revolver USA, which sells to record stores around the US but also sells direct to consumers. Here you’ll find a ton of independent music, including choice reissues from bigger names like Devo, Sonic Youth, and The Fall.
Another great independent record store is Amoeba Music, made famous for its amazing selection at numerous California stores, and its What’s in Your Bag YouTube series. If you want to support a good brick-and-mortar record store and know what you want, we always recommend buying from Amoeba instead of Amazon.
Independent Labels
Screenshot courtesy of Parker Hall
Record labels like Stones Throw, Sub Pop, Secretly Group, Fat Possum, Rough Trade, Daptone, Blue Note, International Anthem, and hundreds more all have websites and sell records directly. If you notice that there is an artist you like signed to a given smaller label, there is a good chance that other artists on the label have a similar vibe.
Start by checking out the liner notes on the back of all your albums to see who made them, then chase down those labels on the web. You’ll likely find some cool new tunes on vinyl along the way.
Directly From the Artists
We’ve saved the best for last. Pay the artists for their work by putting cash—or a Venmo transaction—directly in their hands. Buying a record at the merch table when an artist plays in your town is not only convenient for you (there’s no shipping, and you typically won’t be charged tax), but it’s one of the biggest income streams for bands that tour. You can often find special editions, special colored vinyl variants, and even records that haven’t yet been released just by stopping at the merch table. And if you’re lucky enough to meet the artist at the venue, they will usually sign the record jacket for you.
If you don’t get out much (we know, concerts are expensive), just find their website, social media page, or record label and place an order. I have at least a few records with personal thank-yous and signatures from small artists, which feels really special every time I listen to them!
Tech
Tinder wants to check your humanity by gazing into an orb. Yes, you read that right

Online dating is already a trust minefield, and now Tinder wants to add an eyeball scan to the mix. The popular dating app has announced a global partnership with World, the biometric identity company founded by OpenAI’s Sam Altman. To prove you are a real human on Tinder, you will soon have the option to get your eyes scanned by a physical orb device.
What is World ID and how does Tinder’s human verification work?

World is a company built around the idea that proving your humanity online will become increasingly important as AI bots multiply and outnumber real people on the internet. Its solution is a proprietary scanning device called the Orb, which scans your irises at its physical outlets to verify that you are a real person.
Once verified, you receive a World ID linked to that scan. World already ran a pilot of this verification process with Tinder in Japan earlier this year, and that trial was apparently successful enough to warrant a worldwide rollout.

On Tinder, users who go through the World ID verification process will receive a badge on their profile indicating they are a verified human. To sweeten the deal, Tinder is also offering five free Boosts to anyone who completes the verification. The company hopes that this incentive is meaningful enough for people to hand over their biometric data.
Is this just about dating apps, or is the World orb coming for everything?

Tinder is just the beginning. Zoom is now integrating World ID so that meeting hosts can verify participants’ identity before joining a call. DocuSign is also adopting the technology, letting users require World verification on contracts. Meanwhile, Reddit might adopt World ID as a bot detection tool.
On top of that, World has launched Concert Kit, a tool that lets artists reserve concert tickets for verified humans only, taking direct aim at scalper bots. Concert Kit will soon be tested at a Bruno Mars World Tour show in San Francisco.
Even though World is pushing hard for mainstream adoption, governments in Brazil and several other countries have banned it over privacy concerns. Whether handing your biometric data to a third party becomes the new normal is a question that is only going to get louder from here.
Tech
Xbox expansion cards are now cheaper than SSDs, and PC users are repurposing them


The storage pricing situation is so bad right now that in some cases using an older expansion card designed for a gaming console can be a better option than purchasing a new SSD. A Reddit user recently shared an experiment with Xbox expansion cards, adapting the seemingly proprietary format for…
Read Entire Article
Source link
Tech
DOJ refuses to help French authorities in criminal probe of X

The US Department of Justice is siding with X, as the social media platform owned by Elon Musk navigates a criminal investigation unfolding in France. As first reported by The Wall Street Journal, the Justice Department characterized the French probe as “an effort to entangle the United States in a politically charged criminal proceeding aimed at wrongfully regulating through prosecution the business activities of a social media platform.”
France launched its investigation into X in July, accusing the platform of manipulating its algorithm and “fraudulent data extraction.” Months later, French authorities raided X’s office in Paris and issued summonses to Musk and Linda Yaccarino, the former CEO of X, to appear for interviews on April 20 as part of the probe. According to WSJ, French officials are also investigating X for other charges, including disseminating CSAM and Holocaust denial. However, France’s latest move to ask the Department of Justice for assistance has been stonewalled.
“This investigation seeks to use the criminal legal system in France to regulate a public square for the free expression of ideas and opinions in a manner contrary to the First Amendment of the United States Constitution,” the DOJ wrote in letter, as seen by WSJ.
An xAI official told WSJ that it’s “grateful to the Justice Department for rejecting this effort by a prosecutor in Paris to compel our CEO and several employees to sit for interviews.” The company spokesperson also said there was “no wrongdoing” and that it was a “baseless investigation.”
-

 NewsBeat6 days ago
NewsBeat6 days agoPep Guardiola and Gary Neville agree over Arsenal title problem that benefits Man City
-

 Crypto World5 days ago
Crypto World5 days agoThe SEC Conditionalises DeFi Platforms to Be Avoided for Broker Registration
-

 Politics6 days ago
Politics6 days agoWorld Cup exit makes Italy enter crisis mode
-

 Fashion1 day ago
Fashion1 day agoWeekend Open Thread: Theodora Dress
-

 Crypto World5 days ago
Crypto World5 days agoSEC Signals Exemption for Crypto Interfaces From Broker Registration
-

 News Videos4 days ago
News Videos4 days agoSecure crypto trading starts with an FIU-registered
-

 Sports2 days ago
Sports2 days agoNWFL Suspends Two Players Over Post-Match Clash in Ado-Ekiti
-
 Crypto World5 days ago
Crypto World5 days agoSEC Proposes Certain Crypto Interfaces Don’t Need to Register as Brokers
-

 NewsBeat5 days ago
NewsBeat5 days agoTrump and Pope Leo: Behind their disagreement over Iran war
-

 NewsBeat7 days ago
NewsBeat7 days agoJD Vance announces ‘no agreement’ with Iran over nuclear weapons fear
-

 Politics1 day ago
Politics1 day agoPalestine barred from entering Canada for FIFA Congress
-

 Crypto World1 day ago
Crypto World1 day agoRussia Pushes Bill to Criminalize Unregistered Crypto Services
-

 Sports6 days ago
Sports6 days agoNWFL opens Pathway for new Clubs ahead of 2026 Season
-

 Business2 days ago
Business2 days agoCreo Medical agree sale of its manufacturing operation
-
Sports7 days ago
Dexter Lawrence, Stefon Diggs, Trading for De’Von Achane
-
Business6 days ago
Kering slides after Morgan Stanley downgrade, Gucci woes loom
-

 Crypto World6 days ago
Crypto World6 days agoTrump whales load up ahead of Mar-a-Lago luncheon.
-

 Crypto World6 days ago
Crypto World6 days agoSei Network Enters Quiet Reset Phase as On-Chain Metrics Signal a Slowdown in 2026
-

 Tech6 days ago
Tech6 days agoGoogle adds E2E encryption to Gmail for iOS and Android enterprise users
-

 Tech6 days ago
Tech6 days agoApple glasses won’t go brand shopping like Meta did with Ray-Ban and Oakley






-SOURCE-Parker-Hall.jpg)








You must be logged in to post a comment Login