Crypto World
Vitalik Buterin Unveils Human-Centered Crypto Security Strategy


Ethereum co-founder Vitalik Buterin has outlined a new framework for crypto security, offering practical strategies rooted in redundancy, multi-angle verification, and human-centric design.
He argues that the best way to protect users is to close the gap between their intent and system behavior.
Vitalik Buterin Explains Closing the Gap Between User Intent and System Security
Buterin’s insights, dismantling the idea of perfect security, arrive at a time when crypto platforms continue to face wallet hacks, smart contract exploits, and complex privacy risks.
By merging security with user experience, Buterin provides developers with a roadmap for balancing protection with usability.
Buterin reframes security as an effort to minimize the divergence between what users want and what systems do.
While user experience broadly addresses this gap, security specifically targets tail-risk scenarios in which adversarial behavior could lead to severe consequences.
“Perfect security is impossible—not because machines are flawed, or because humans designing them are flawed, but because the user’s intent is fundamentally an extremely complex object,” Buterin wrote.
He points out that even a seemingly simple action, like sending 1 ETH to a recipient, involves assumptions about identity, blockchain forks, and common-sense knowledge that cannot be fully encoded.
More intricate objectives, such as preserving privacy, add layers of complexity: metadata patterns, message timing, and behavioral signals can all leak sensitive information. This makes it difficult to distinguish between “trivial” and “catastrophic” losses.
The challenge mirrors early debates in AI safety, where specifying goals strongly proved notoriously difficult. In crypto, translating human intent into code faces a similar barrier.
Redundancy and Multi-Angle Verification
To compensate for these limitations, Buterin advocates redundancy: users specify intent through multiple overlapping methods. Systems act only when all specifications align.
This approach applies across Ethereum wallets, operating systems, formal verification, and hardware security.
For instance, programming type systems require developers to specify both program logic and expected data structures; mismatches prevent compilation.
Formal verification adds mathematical property checks to ensure code behaves as intended. Transaction simulations allow users to preview on-chain consequences before confirming actions.
Post-assertions require both action and expected outcomes to match. Multisig wallets and social recovery mechanisms distribute authority across multiple keys. This ensures that single-point failures do not compromise security.
The Role of AI in Security
Buterin also envisions large language models (LLMs) as a complementary tool, describing them as “a simulation of intent.”
Generic LLMs mirror human common sense, while user-fine-tuned models can detect what is normal or unusual for an individual.
“LLMs should under no circumstances be relied on as a sole determiner of intent. But they are one ‘angle’ from which a user’s intent can be approximated,” he noted.
Integrating LLMs with traditional redundancy methods could enhance mismatch detection without creating single points of failure.
Balancing Security and Usability
Critically, Buterin emphasizes that security should not translate into unnecessary friction for routine actions.
Low-risk tasks should be easy or even automated, while risky actions, such as transfers to new addresses or unusually large sums, require additional verification.
This calibrated approach ensures protection without frustrating users.
By blending redundancy, multi-angle verification, and AI-assisted insights, Buterin offers a roadmap for crypto platforms to reduce risk while maintaining usability.
Perfect security may be unattainable, but a layered, human-centered approach can safeguard users and strengthen trust in decentralized systems.
Crypto World
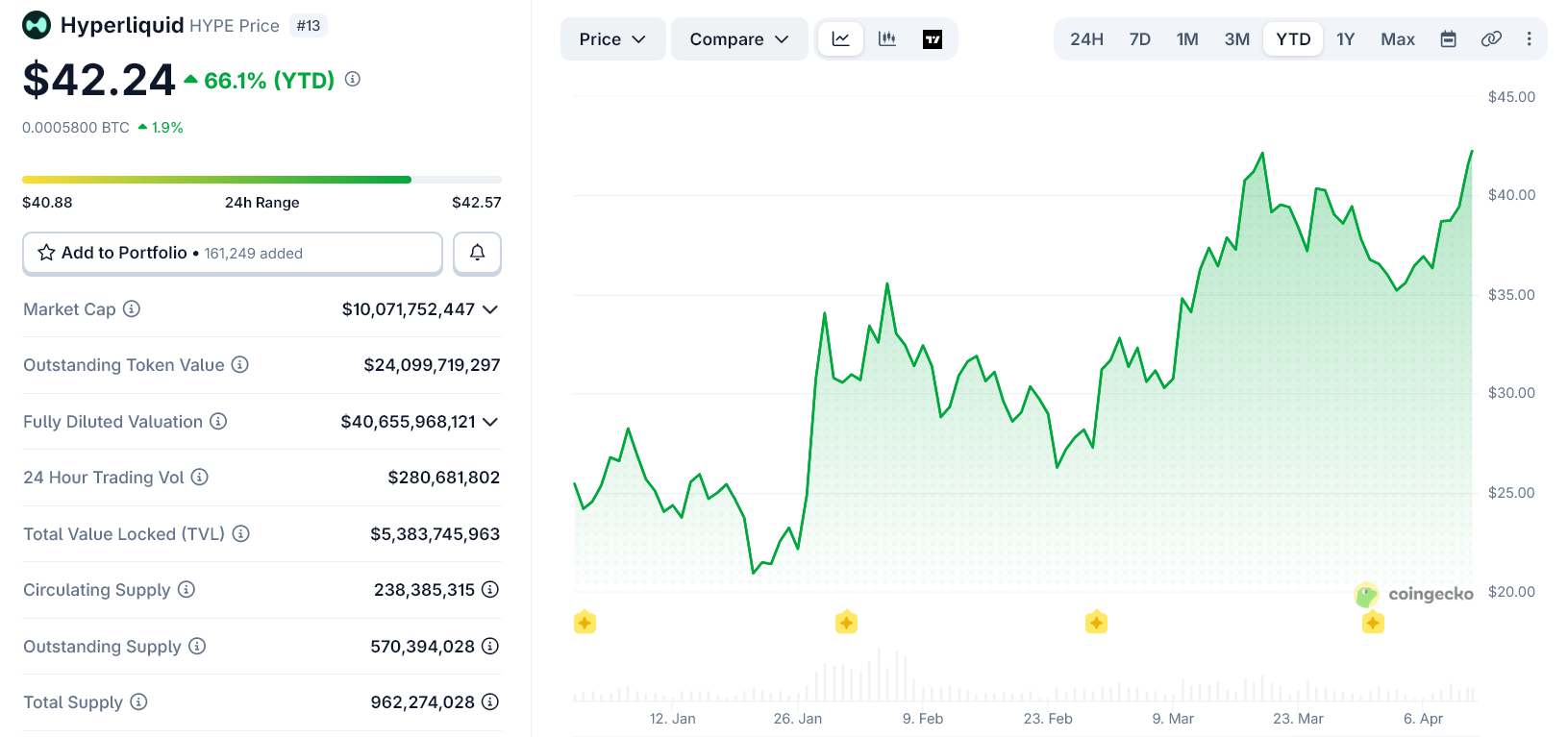
Bitwise Is Launching Its Hyperliquid ETF Soon
Bitwise is signaling the imminent launch of a US exchange-traded fund (ETF) tied to the decentralized trading network Hyperliquid.
In an amended registration statement filed with the SEC, the digital asset index fund manager disclosed critical operational details for the proposed product.
BHYP Ticker For Bitwise’s Hyperliquid ETF
Bitwise’s filing says the trust’s primary objective is to provide exposure to the value of Hyperliquid held by the vehicle. The fund’s secondary objective is to earn staking rewards.
“In connection with its investment objective of seeking to derive additional Hyperliquid through staking, the Trust will stake some or all of the Hyperliquid held in the Trust Hyperliquid Accounts,” the filing stated.
Meanwhile, the new filing introduces the ticker symbol BHYP and establishes a sponsor fee of 67 basis points.
Industry experts noted that these inclusions represent one of the final procedural hurdles before a fund goes live on national exchanges.
If approved by securities regulators, the Hyperliquid fund will integrate into a rapidly expanding suite of Bitwise investment vehicles.
Over the past year, the asset manager has aggressively expanded its product lineup beyond legacy assets such as Bitcoin and Ethereum. The firm has been providing regulated exposure for alternative layer-one networks and protocols, including Solana, Chainlink, and XRP.
Meanwhile, the push for a US spot product follows closely on the heels of Bitwise’s international expansion.
On April 9, the firm listed the Bitwise Hyperliquid Staking physically backed product on the Deutsche Börse Xetra. That instrument tracks the Kaiko HYPE Reference Rate LDNLF index.
The fund automatically captures on-chain staking yields, sparing institutional allocators the operational friction of managing private keys and self-custody infrastructure.
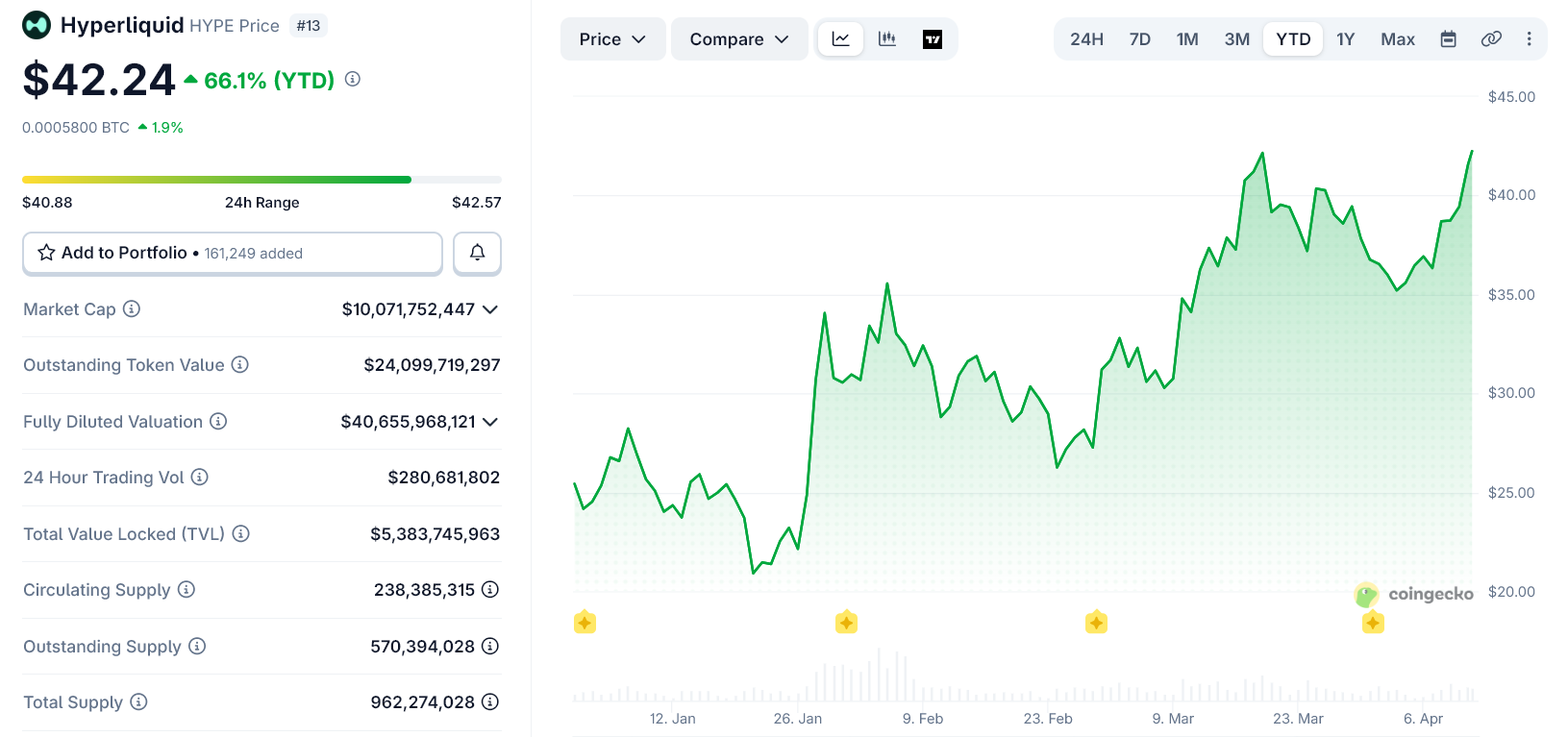
HYPE Outperforms Crypto Bear Market
Since the beginning of the year, Hyperliquid’s HYPE has emerged as one of the best-performing digital assets.
The altcoin has surged 66% since the beginning of 2026. This demonstrates distinct relative strength against a broader digital asset market that has struggled to find its footing early in the year.
A significant catalyst for Hyperliquid’s recent outperformance is its underlying utility during periods of acute macroeconomic stress. As military hostilities flared in the Middle East involving the US, Israel, and Iran, traditional financial markets were shuttered for the weekend.
During that liquidity gap, institutional and retail participants aggressively rotated into Hyperliquid’s blockchain-based infrastructure.
The decentralized platform became a critical venue for traders seeking to hedge geopolitical risks. They used synthetic perpetual futures contracts to gain exposure to global benchmarks such as Brent crude and gold before the recent Pakistan-brokered ceasefire took effect.
The post Bitwise Is Launching Its Hyperliquid ETF Soon appeared first on BeInCrypto.
Crypto World
Monad Crypto Whales Just Hit a 90-Day Accumulation Peak: Is MON About to Break Its All-Time High?

Monad Crypto (MON) is trading near $0.035 after a 18% surge in 24 hours, with large holder netflow on-chain data registering its highest reading in 90 days – a level not seen since the token’s initial post-launch run.
Exchange outflows have spiked alongside that number, indicating cold storage accumulation rather than positioning for a near-term exit.
The complicating factor is immediate: MON price is pressing into the $0.035–$0.040 resistance block that capped its last local peak, and the all-time high of $0.049 sits another 15% above that ceiling. Is this whale accumulation the real setup, or is the market running ahead of confirmation?
The Accumulation/Distribution indicator is trending higher in tandem with price, a structurally bullish read.
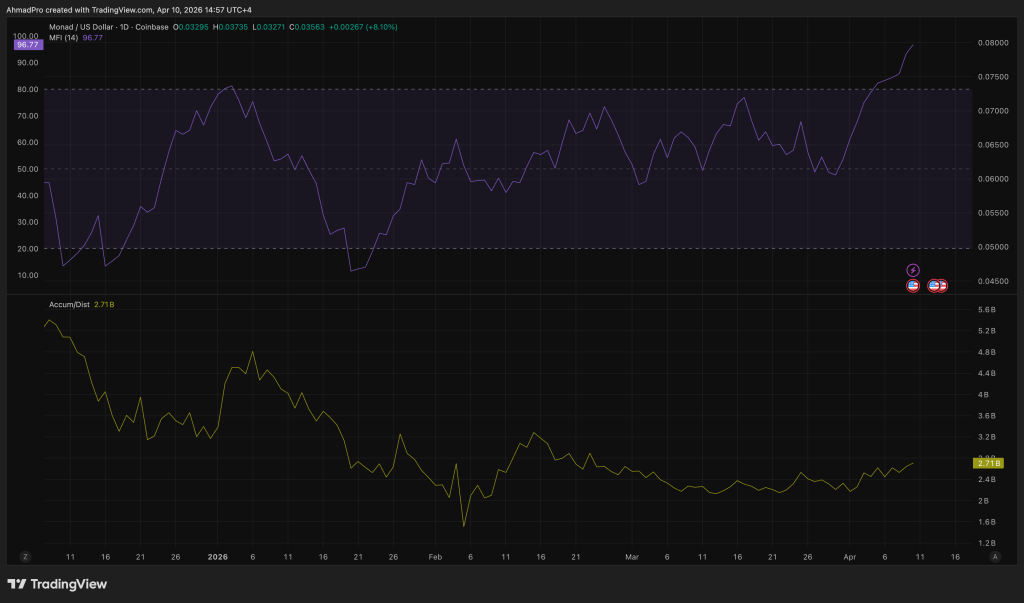
Trading volume exceeded $2.69 billion in the past day, and the Money Flow Index is holding slightly above 80, suggesting capital is still entering rather than rotating out. What the on-chain data doesn’t yet confirm is whether this print translates into a clean breakout or a high-volume rejection at resistance.
Discover: The best pre-launch token sales
Can Monad Crypto Clear $0.040 Resistance or Does the Overbought Signal Force a Reset for MON Crypto?
The price analysis starts at the 200-day EMA, currently clustered near $0.0345. MON is trading just above that level, which means the immediate battle is confirming it as support rather than ceiling.
A hold here with successive closes above $0.035 starts building the structure needed for a run at $0.040.
If MON clears $0.040 on volume comparable to today’s session, the path to the all-time high near $0.049 opens without a major structural obstacle in between.
If $0.035 fails to hold as support after the current push, the $0.0293 liquidity cluster becomes the next relevant floor, and below that the $0.023–$0.025 zone enters the picture.

The Bollinger Bands are the counterweight here. MON has entered the overbought region – price is pressing the upper band – which historically signals either a short consolidation or an outright pullback before the next leg.
The band position doesn’t invalidate the bull case; it narrows the path. For us, the invalidation is a daily close back below $0.0293 on elevated volume. That would suggest distribution, not accumulation, is driving the flows.
The Monad crypto ecosystem is adding weight to the technical setup. Neverland, the flagship DeFi protocol on the network, is approaching $40 million in Total Value Locked, and TVL across integrated protocols has grown roughly 15% this week.
That’s utility keeping pace with speculation – a healthier signal than price momentum running on narrative alone.
Discover: The best crypto to diversify your portfolio with
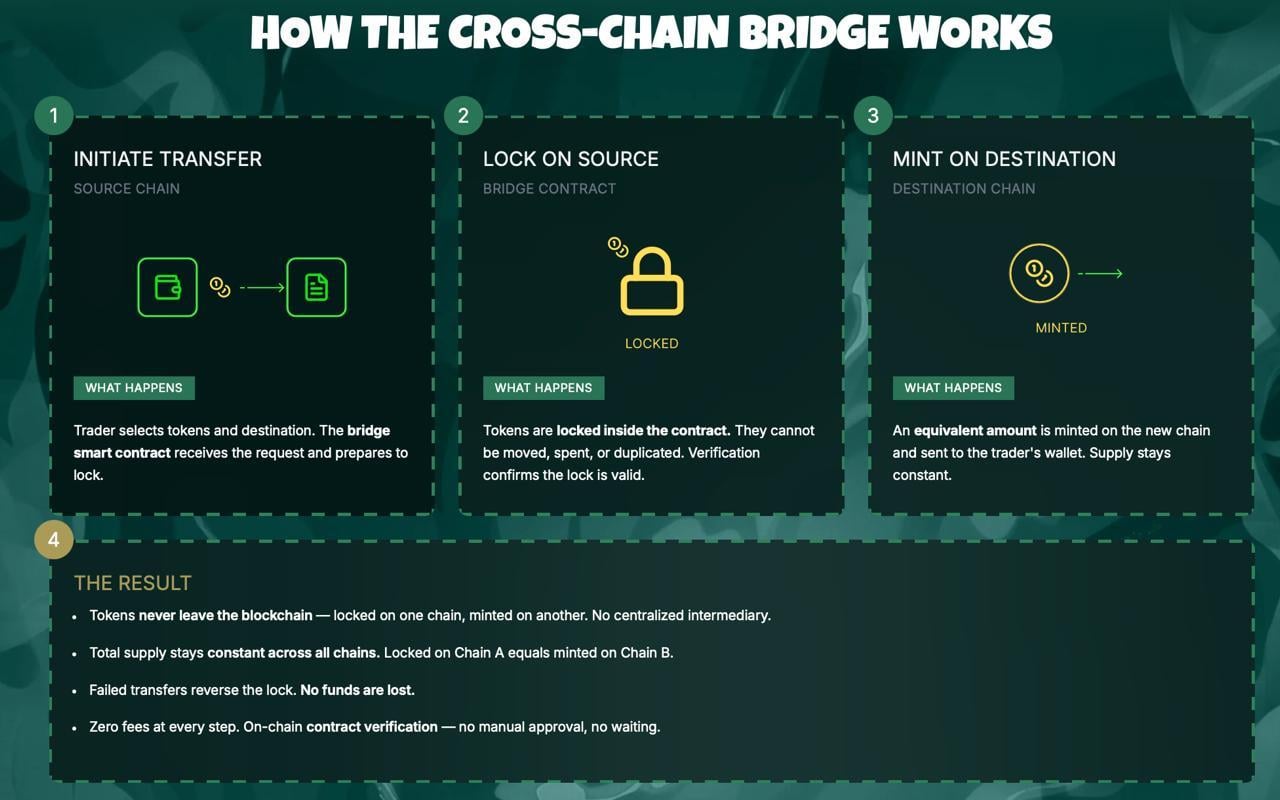
Missed Monad Crypto? Liquid Chain Raises $700,000 Heading Into The First Week
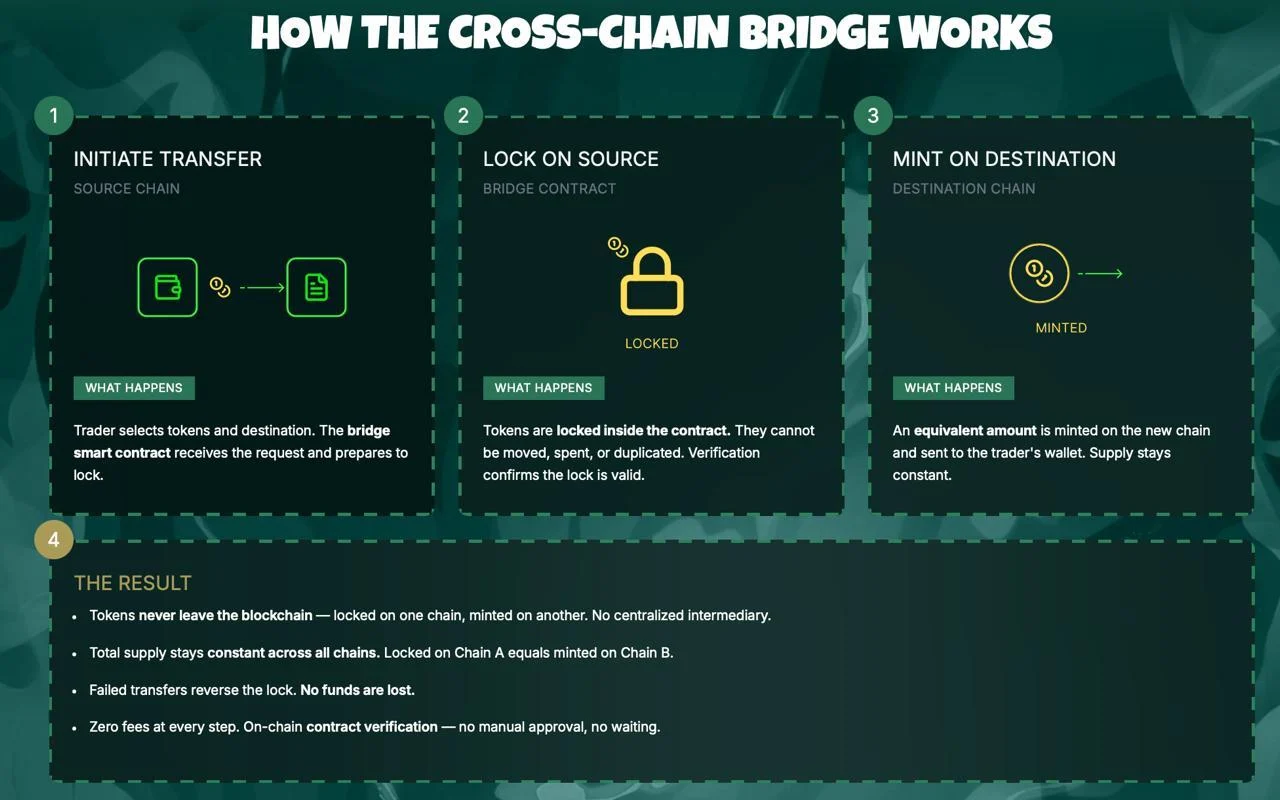
Liquid Chain built a Unified Liquidity Layer that aggregates capital across multiple Layer-2 networks using Chainlink’s Cross-Chain Interoperability Protocol (CCIP) as the messaging backbone.
The core problem it solves is real and expensive – assets stranded on individual L2s require manual bridging, creating slippage, delay, and trust assumptions that institutional allocators won’t accept.
Liquid Chain’s architecture lets users move assets seamlessly across chains without manual bridge interactions, with CCIP handling the verification and message-passing layer beneath the surface.
The project has been pitching its Layer-3 DeFi buildout as a credible answer to the fragmentation problem, and the Convergence judges agreed.
Other notable hackathon submissions concentrated on Real-World Asset tokenization and DeFi automation – a consistent signal that Chainlink’s developer community is orienting toward institutional-grade infrastructure rather than consumer speculation. The CCIP adoption rate implied by the hackathon submissions validates Chainlink’s cross-chain positioning at exactly the moment demand for tamper-proof oracle settlement is breaking records on Polymarket.
Explore the LiquidChain presale and current allocation terms here.
The post Monad Crypto Whales Just Hit a 90-Day Accumulation Peak: Is MON About to Break Its All-Time High? appeared first on Cryptonews.
Crypto World
Steakhouse Financial Confirms DNS Hijack, Says No User Funds Were Lost

TLDR:
- Attackers socially engineered OVHcloud support to remove hardware 2FA, enabling full account access within an hour.
- The phishing site used an Inferno Drainer kit and ran live for roughly four hours on March 30, 2026.
- ICANN’s five-day domain transfer lock gave Steakhouse Financial time to cancel an outbound transfer filed by the attacker.
- Steakhouse vaults on Morpho operated independently throughout; no depositor funds were at risk at any point.
A social engineering attack briefly redirected Steakhouse Financial’s website to a phishing page on March 30, 2026.
Attackers manipulated the domain registrar’s support team to strip account security protections. The phishing site ran for roughly four hours before the team reclaimed control. No user funds were lost, and no onchain contracts were touched.
How Attackers Broke Into Steakhouse Financial’s Domain Registrar
The attacker called OVHcloud, the domain registrar used by Steakhouse Financial, and posed as the account owner. They provided enough personal information to pass OVH’s phone-based identity check.
An OVH support agent then removed the hardware-based two-factor authentication on the account.
Within seconds of logging in, the attacker ran automated scripts. These deleted every second-factor device on the account and enrolled their own. The speed pointed to a pre-planned operation.
The attacker then redirected the domain’s nameservers to servers under their control.
They pointed the site’s A records to a cloned version of the Steakhouse website hosted on Hostinger. That cloned site carried a wallet drainer linked to Inferno Drainer, a known drainer-as-a-service operation.
Let’s Encrypt TLS certificates were obtained within minutes. This made the phishing site appear legitimate to standard browsers. Wallet extensions from Phantom, MetaMask, and Rabby flagged the site as malicious independently and quickly.
Steakhouse Financial Regained Control Within Hours, Funds Remained Safe
Steakhouse Financial’s team spotted the unauthorized email-change notification at 08:47 UTC and contacted OVH immediately. The phishing site went live around 09:59 UTC.
The team posted a public warning on X at 10:34 UTC, under 30 minutes after the site became operational.
The Security Alliance (SEAL) was brought in at 11:25 UTC while the attack was still active. The team worked across multiple parallel tracks. These included account recovery, DNS forensics, and transfer cancellation.
The attacker had filed an outbound domain transfer. ICANN’s five-day transfer timelock gave the team time to cancel it.
The team contacted Hostinger directly to reject the transfer on the receiving end. Hostinger later confirmed the offending account was frozen and closed.
By 12:56 UTC, the team had reclaimed the OVH account. DNS was fully restored by approximately 13:55 UTC. Steakhouse Financial confirmed all domains were safe to use by April 1.
The company has since migrated to a registrar supporting hardware-key MFA and registrar-level locks. A continuous DNS monitoring system now watches all Steakhouse domains in real time. According to the post-mortem published by Steakhouse Financial on X, a full vendor security review process is now being established across all supply-chain vendors.
Adrian Cachinero Vasiljevic, the partner responsible for operations at Steakhouse Financial, issued a personal apology. He stated that identifying this attack vector was his responsibility and committed to driving the security hardening work going forward.
Crypto World
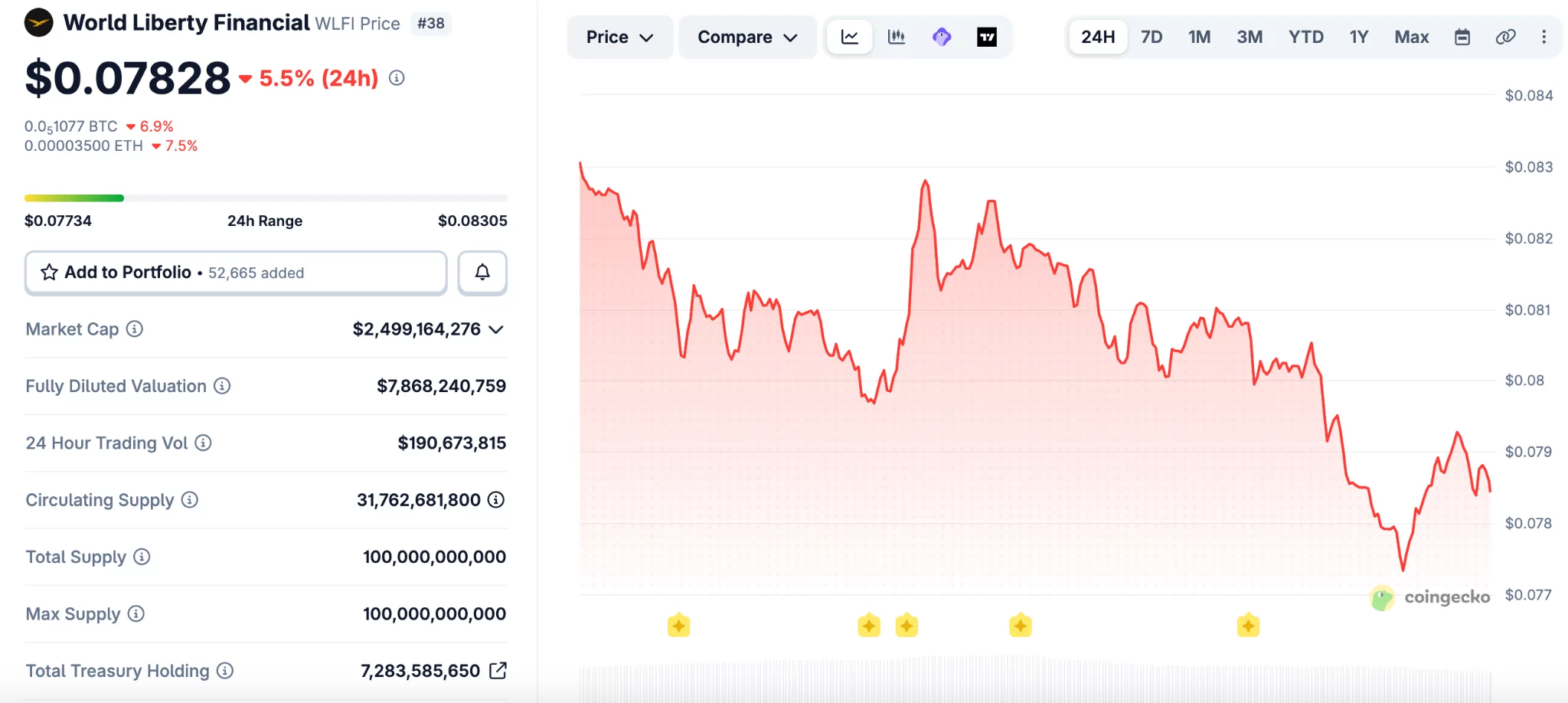
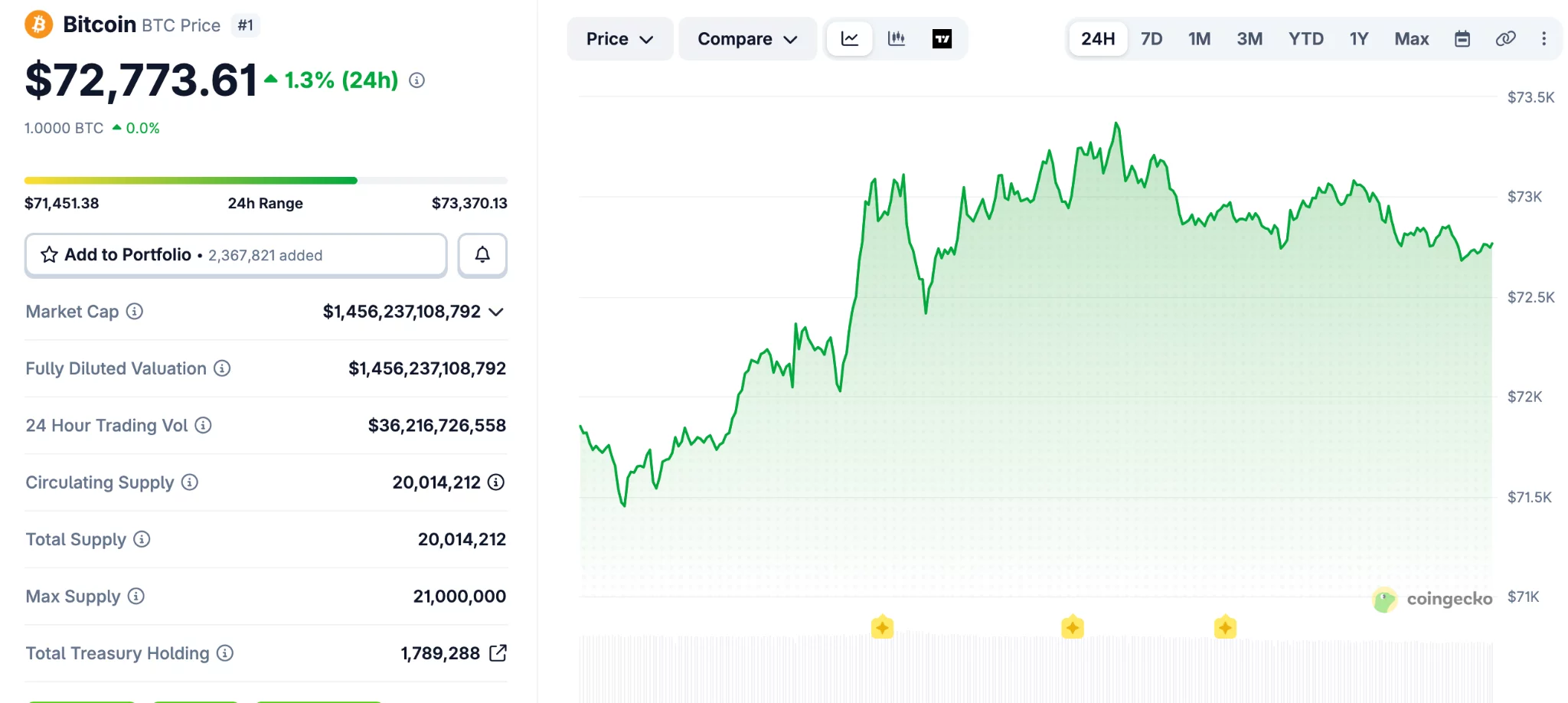
WLFI drops to record low after token-backed loan draws scrutiny
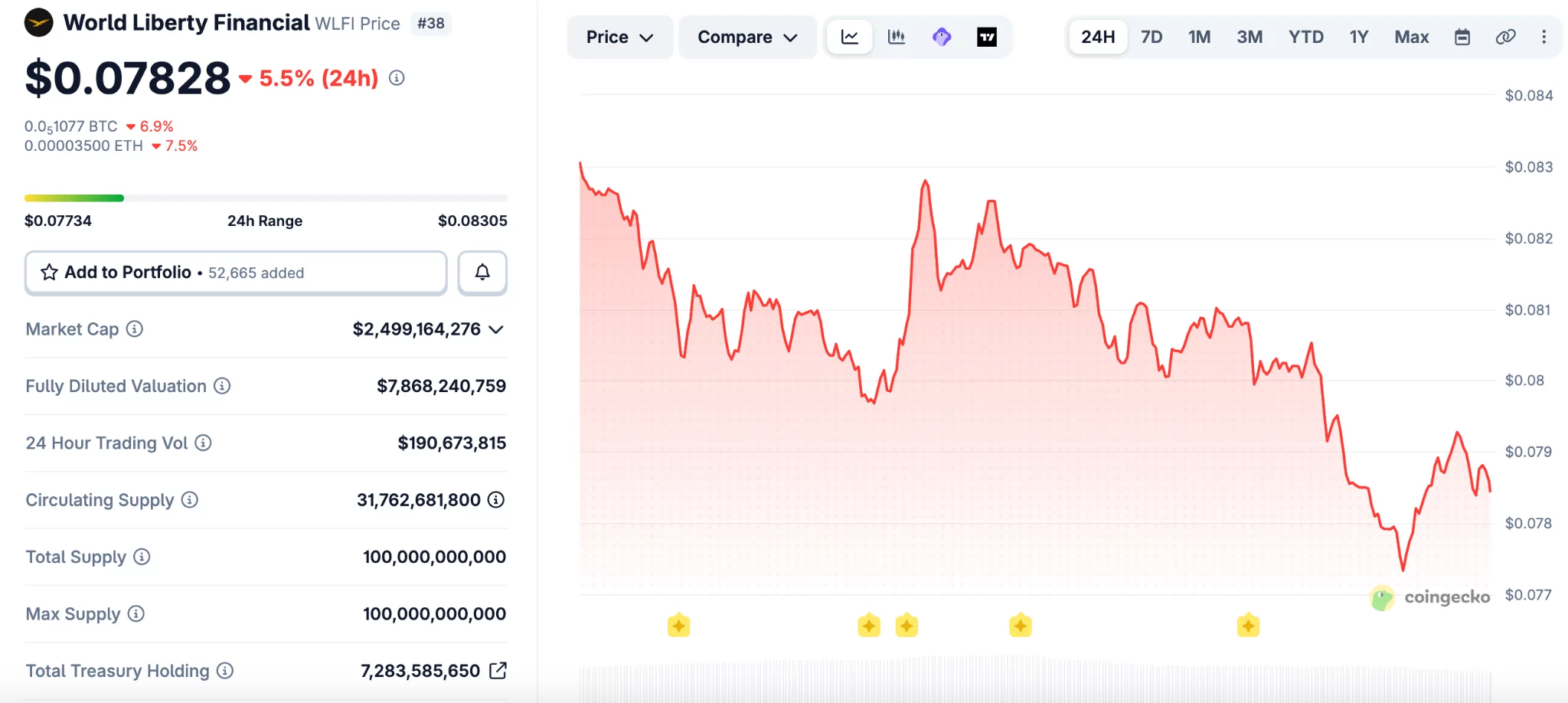
WLFI (WLFI) fell to a new all-time low on Saturday after onchain data showed wallets linked to World Liberty Financial used large token holdings to borrow stablecoins.
Summary
- WLFI fell to a record low after a self-backed loan raised fresh market risk questions.
- Onchain data showed linked wallets used 5 billion WLFI tokens to borrow stablecoins on Dolomite.
- World Liberty said its positions remain safe and framed the lending move as yield strategy.
The move added pressure to the Trump-linked project as traders weighed the risk tied to using its own token as collateral.
WLFI dropped to about $0.077, its lowest level on record, before trading near $0.079. The token is now down 76% from its peak of $0.33 reached in September, based on CoinGecko data.
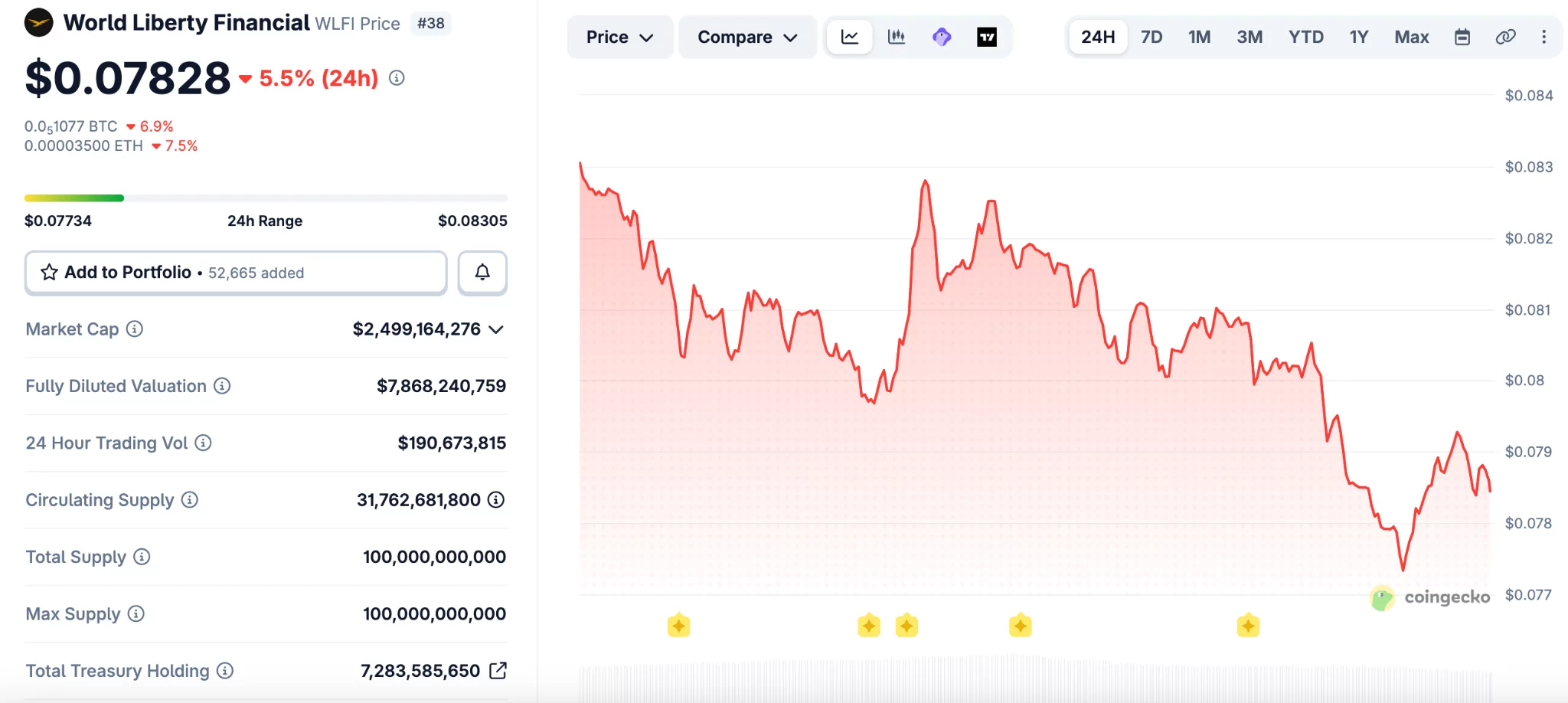
The decline followed reports that wallets tied to World Liberty Financial deposited about 5 billion WLFI tokens on Dolomite. The same position was then used to borrow $75 million in USD1 and USDC.\
Arkham data showed that more than $40 million of the borrowed funds later moved to Coinbase Prime. That transfer drew more attention to the project’s financing activity and the size of its exposure.
The market reaction was swift because WLFI is not viewed as a deeply liquid asset. A large collateral position tied to price swings can increase pressure if the token falls further.
DeFi users on X said the structure could create risk for lenders if WLFI moves closer to liquidation levels. Some pointed to the token’s high fully diluted valuation and limited trading depth as a weak point.
“WLFI has almost a $10 billion FDV, but it is not an extremely liquid asset,” wrote one user. “So imagine what would happen if 5% of WLFI’s total supply would suddenly need to be sold to liquidate the position.”
Another user compared the setup to borrowing cash against self-created value. The user said,
“It’s the financial equivalent of printing casino chips, borrowing cash against them, and telling everyone else not to panic because the house still believes in the chips.”
Dolomite remains a smaller player in DeFi lending. DefiLlama ranks it 19th among lending platforms by total value locked, which added more focus to the size of the WLFI-linked position.
World Liberty defends the strategy
World Liberty Financial responded on social media and said its positions remain well above liquidation thresholds. The project described itself as an “anchor borrower” and said the strategy supports yield generation.
The team wrote,
“Everyday users are earning outsized stablecoin yields right now — at a time when traditional markets are offering very little.” It added, “That’s the whole point.”
The project also said it plans to introduce a governance proposal for early retail holders. The proposal would replace immediate token access with a phased vesting schedule, subject to a community vote.
Disclosure: This article does not represent investment advice. The content and materials featured on this page are for educational purposes only.
Crypto World
WLFI drops to record low after token-backed loan draws ccrutiny
WLFI (WLFI) fell to a new all-time low on Saturday after onchain data showed wallets linked to World Liberty Financial used large token holdings to borrow stablecoins.
Summary
- WLFI fell to a record low after a self-backed loan raised fresh market risk questions.
- Onchain data showed linked wallets used 5 billion WLFI tokens to borrow stablecoins on Dolomite.
- World Liberty said its positions remain safe and framed the lending move as yield strategy.
The move added pressure to the Trump-linked project as traders weighed the risk tied to using its own token as collateral.
WLFI dropped to about $0.077, its lowest level on record, before trading near $0.079. The token is now down 76% from its peak of $0.33 reached in September, based on CoinGecko data.
The decline followed reports that wallets tied to World Liberty Financial deposited about 5 billion WLFI tokens on Dolomite. The same position was then used to borrow $75 million in USD1 and USDC.\
Arkham data showed that more than $40 million of the borrowed funds later moved to Coinbase Prime. That transfer drew more attention to the project’s financing activity and the size of its exposure.
The market reaction was swift because WLFI is not viewed as a deeply liquid asset. A large collateral position tied to price swings can increase pressure if the token falls further.
DeFi users on X said the structure could create risk for lenders if WLFI moves closer to liquidation levels. Some pointed to the token’s high fully diluted valuation and limited trading depth as a weak point.
“WLFI has almost a $10 billion FDV, but it is not an extremely liquid asset,” wrote one user. “So imagine what would happen if 5% of WLFI’s total supply would suddenly need to be sold to liquidate the position.”
Another user compared the setup to borrowing cash against self-created value. The user said,
“It’s the financial equivalent of printing casino chips, borrowing cash against them, and telling everyone else not to panic because the house still believes in the chips.”
Dolomite remains a smaller player in DeFi lending. DefiLlama ranks it 19th among lending platforms by total value locked, which added more focus to the size of the WLFI-linked position.
World Liberty defends the strategy
World Liberty Financial responded on social media and said its positions remain well above liquidation thresholds. The project described itself as an “anchor borrower” and said the strategy supports yield generation.
The team wrote,
“Everyday users are earning outsized stablecoin yields right now — at a time when traditional markets are offering very little.” It added, “That’s the whole point.”
The project also said it plans to introduce a governance proposal for early retail holders. The proposal would replace immediate token access with a phased vesting schedule, subject to a community vote.
Disclosure: This article does not represent investment advice. The content and materials featured on this page are for educational purposes only.
Crypto World
Aethir Contains Bridge Hack While Losses Stay Below $90K


Aethir said it remains fully operational after containing an attack on its ATH bridge contracts.
Summary
- Aethir said it contained the ATH bridge exploit quickly and kept total user losses below $90,000.
- The company said Ethereum ATH supply stayed intact while affected contracts were disconnected to stop losses.
- PeckShield first estimated higher losses, while Aethir said compensation details will arrive next week soon.
The company said the exploit did not affect the main ATH supply on Ethereum, while user losses stayed below $90,000.
Aethir said it detected a malicious attack targeting ATH bridge contracts that connect Ethereum with other chains. The company said it disconnected all affected contracts soon after finding the issue and stopped further damage.
The team added that the ETH-ARB bridge on Squid was not affected during the incident. It also said the main ATH supply on Ethereum remains intact, which helped prevent wider disruption across the network.
Aethir said it will share a full compensation plan next week. The company also said it is working with authorities and exchange partners to trace the attacker and block related funds.
“A full attacker wallet list will be posted in Discord as we monitor the funds,” Aethir said, in its update.
It added that a detailed memo will explain what happened, which users were affected, and how compensation will work.
Aethir credited several exchanges for acting quickly after the exploit. The company named Binance, Upbit, Bithumb, and HTX among the platforms that blacklisted identified wallets tied to the incident.
The project also thanked ZeroShadow for helping with analysis during the response. Aethir said that early action from partners helped limit the scope of the losses and support the ongoing investigation.
PeckShield had flagged the exploit a day earlier and initially estimated losses at about $400,000. The blockchain security firm also said the attacker moved funds from BNB Chain to Tron through several addresses.
That early estimate differed from Aethir’s latest figure of under $90,000 in user losses. The gap places more attention on fund tracing and the final accounting of the incident.
Crypto attacks continue to pressure the market
The Aethir case comes as crypto security breaches keep hitting the market. PeckShield recently said losses from 20 security incidents reached about $52 million in March, nearly double the February total.
The firm also pointed to a growing pattern where one exploit can spread stress across linked DeFi platforms. Those events can weaken liquidity, create bad debt, and strain lending markets beyond the first target.
PeckShield cited ResolvLabs and Venus Protocol as recent examples of wider fallout after exploits. It also noted targeted attacks on individuals, including a multimillion-dollar theft tied to social engineering on Kraken. The trend has carried into April as other platforms deal with new attacks.
Crypto World
Binance New Listing Calendar Heats Up as Strategy Holds 766,970 BTC and One Presale Fills Fast
Strategy now holds 766,970 BTC worth over $54 billion after buying roughly 45,000 BTC in the past 30 days, proving the largest corporate holder is not slowing down even with BTC above $71,000.
The binance new listing calendar is where the next round of returns gets decided, and the presale filling fastest right now is the one with a confirmed spot on that calendar.
Pepeto is approaching its listing date with more than $8.87 million raised and the cofounder who built the original Pepe coin, and wallets are rushing to lock in the presale entry before stages close.
Strategy bought roughly 45,000 BTC over the past month, pushing its total to 766,970 BTC per CoinDesk. The company launched its STRC offering to fund more purchases, and the position now tops $54 billion.
BTC cleared $72,700 after the ceasefire rally that wiped $600 million in shorts per Bloomberg, and the next confirmed binance new listing is where presale holders turn floor entries into returns that BTC at current prices cannot match.
How BNB, SOL, and the Next Binance New Listing Compare for Returns
Pepeto: What Happens When a Working Exchange Hits the Binance New Listing Calendar
Most tokens land on Binance with a whitepaper and a promise. Pepeto lands with a finished exchange that already runs live trades, and that difference is why the binance new listing for this token is getting more attention than any other presale this cycle.
Zero fee swaps keep positions whole. The bridge moves tokens across chains without charging a cent. The contract scanner catches rug pulls before a dollar goes in. All three tools are live, not coming soon, live.
The presale hit $8.87 million during extreme fear while the rest of the market froze, and the Pepe cofounder who took 420 trillion tokens to $11 billion with nothing behind it is building a real exchange this time. Every contract cleared a SolidProof audit, 186% APY staking grows every position, and analysts model 100x to 300x starting at the $0.0000001863 entry.
The presale fills faster each round because the wallets inside know what listing day does, it replaces this price permanently and the return belongs only to the wallets that got in while the number still existed. The binance new listing date is the clock, and every hour closer is one hour less before the entry is gone.
BNB: Exchange Token Holds $605 but Upside Stays Measured
BNB holds near $605 with quarterly token burns and Binance volume keeping demand steady per CoinMarketCap.
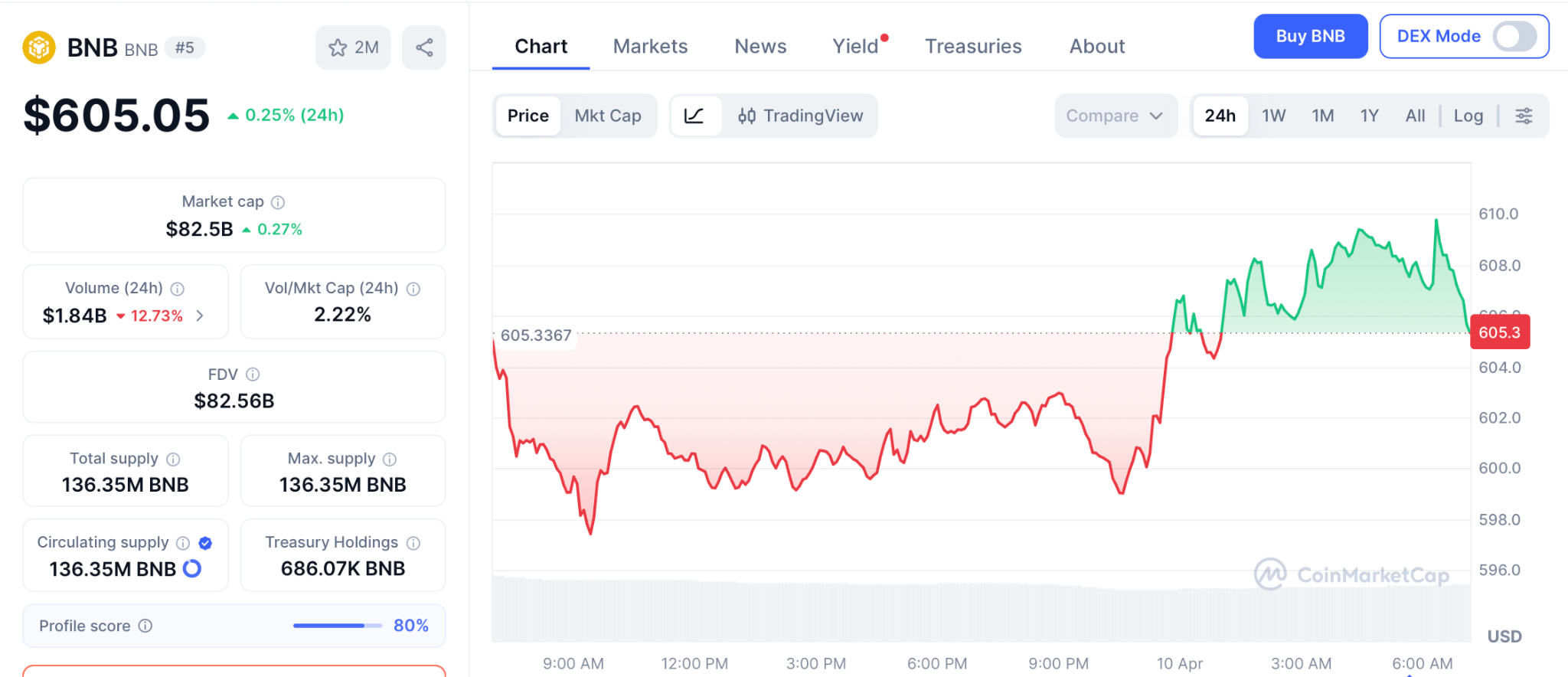
New listings on Binance historically lift BNB as traders move capital onto the platform, and the upcoming Pepeto listing adds another event to the calendar.
BNB offers stability, but from $605 the path to $900 is roughly 50%, far from the kind of return a presale floor delivers when the binance new listing opens the gap between entry and market price.
Solana: SOL Sits at $84 With Strong Fundamentals but Limited Ceiling
SOL trades near $84 after commodity classification cleared regulatory clouds per CoinGecko. Nine ETF filings and the Alpenglow upgrade add long term weight, and institutional ownership of SOL products sits at 48.8%, the highest of any crypto fund.
CME Group also plans SUI and AVAX futures for May, showing derivatives markets are expanding beyond BTC and ETH. SOL is strong, but from $84 even a move to $300 delivers 3.5x over months while presale entries hold the spread between presale and listing where the widest returns get built.
Conclusion
Strategy’s 766,970 BTC proves long term confidence in digital assets, but the wallets watching the binance new listing calendar are looking past large caps toward presale entries with real weight. Pepeto has the live exchange, the capital, and the confirmed listing to back it.
The last stage sold out ahead of schedule, and this one fills while these words load. The presale price stops existing the moment the binance new listing date arrives, and the returns belong only to the wallets that got in while the door was still open.
Click To Visit Pepeto Website To Enter The Presale
FAQs
What is the most expected binance new listing in 2026?
Pepeto leads with $8.87 million raised, a live exchange with zero fee trading, and a confirmed listing date. The Pepe cofounder and SolidProof audit give it the strongest profile this cycle.
Can a binance new listing deliver bigger returns than holding BNB or SOL?
BNB at $605 offers 50% to $900 and SOL at $84 targets 3.5x to $300. Presale entries at floor price carry the listing gap where the widest returns in every cycle get built.
Disclaimer: This is a Press Release provided by a third party who is responsible for the content. Please conduct your own research before taking any action based on the content.
Crypto World
Bitcoin nears $73K again as ETH and HYPE push higher
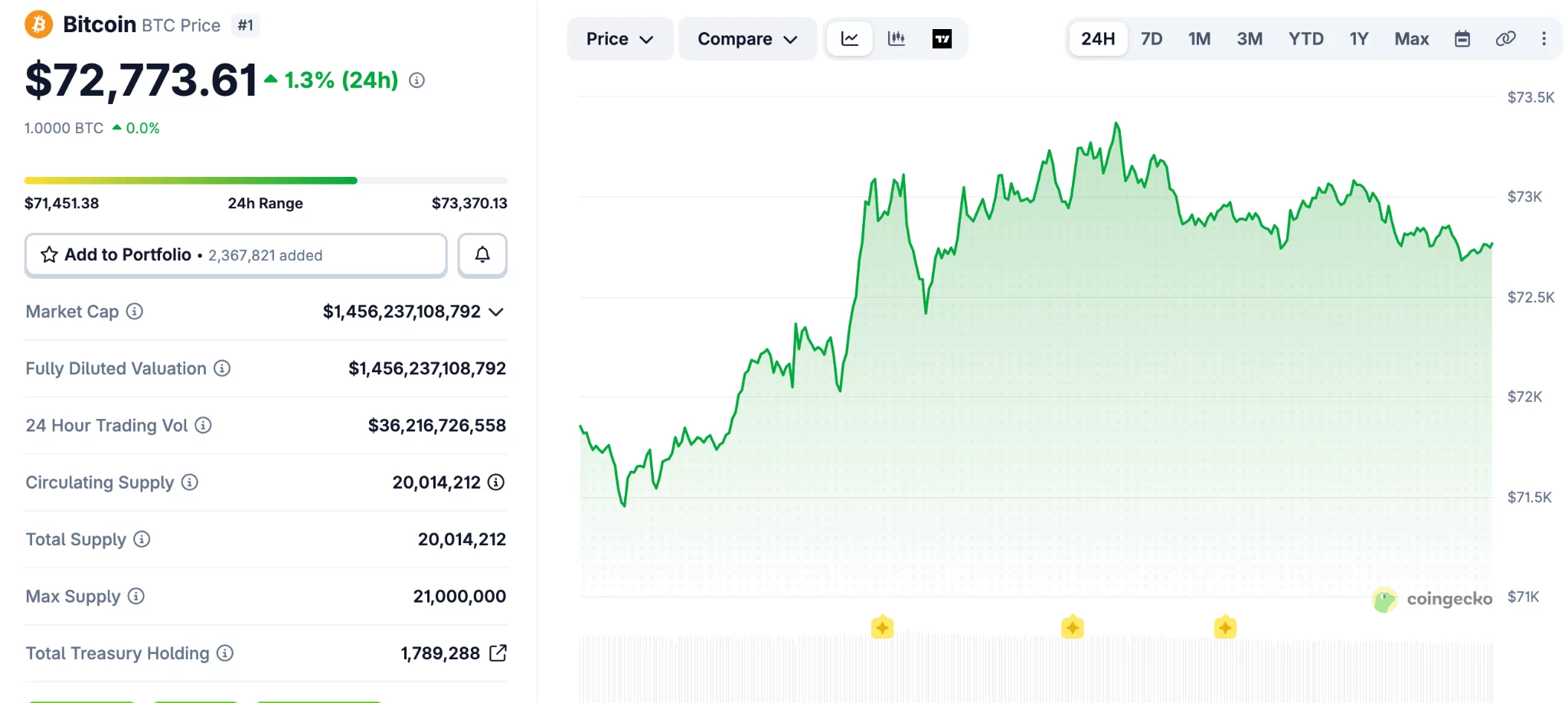
Bitcoin (BTC) extended its upward move over the past 24 hours and reached its highest level in three weeks.
Summary
- Bitcoin climbed above $73,000 as traders weighed cease-fire updates and stronger March CPI data yesterday.
- Ethereum moved back above $2,200, while HYPE and DASH posted gains across the altcoin market.
- RAVE surged 100% in one day and entered the top 100 tokens.
The broader crypto market also moved higher, with Ethereum (ETH), HYPE (HYPE), and RAVE among the tokens posting gains.
Bitcoin traded in a tight range between $66,000 and $67,000 over the weekend. That changed on Monday when the asset moved above $70,000 after reports said the United States and Iran had started talks.
The price later slipped below $68,000 after follow-up reports challenged that claim. Bitcoin then turned higher again on Tuesday after both sides announced a “two-week cease-fire,” which supported market sentiment.
The asset kept climbing even after March CPI data showed stronger inflation. It reached $73,500 earlier today, its highest level since March 18, before easing slightly below $73,000.
Bitcoin’s market value rose to $1.455 trillion, according to CoinGecko data. Its share of the total crypto market also increased over the past week and now stands above 57%.
Ethereum, HYPE, and RAVE lead altcoin gains
Ethereum moved back above the $2,200 mark after a 2.3% daily rise. BNB also traded higher and moved past $600, while HYPE climbed more than 5% and reclaimed $40.
Most large-cap altcoins followed the same direction, though gains remained moderate. A few tokens, including WLFI, XMR, and CC, posted small losses during the session.
RAVE recorded the strongest move among the top gainers. The token jumped 100% in one day and extended its weekly gain to about 700%, which pushed it into the top 100 assets by market value.
DASH also posted a sharp advance and moved above $45 after a 13% gain. SIREN added 10% and returned to the $0.80 level.
The total crypto market value increased by more than $100 billion from last week. It stood at $2.530 trillion at press time, showing broader strength across the sector.
Disclosure: This article does not represent investment advice. The content and materials featured on this page are for educational purposes only.
Crypto World
Iran Bitcoin toll report raises questions over oil ship payments


Reports that Iran may accept crypto for oil tanker tolls in the Strait of Hormuz have sparked debate across the digital asset market.
Summary
- Reports on Iran’s possible crypto tolls for oil tankers have split opinion across Bitcoin and stablecoin circles.
- Analysts said stablecoins face freeze risks, while Bitcoin supporters called BTC harder to block or control.
- Galaxy’s Alex Thorn said tanker payments may use Bitcoin addresses, not Lightning, due to size limits.
The discussion followed a Financial Times report that linked the proposal to Iran’s efforts to reduce exposure to US sanctions.
Market participants have focused on one question: whether Bitcoin would play a real role in such payments. Conflicting claims have since pointed to stablecoins or Chinese yuan as other possible options.
The latest debate started after reports said Iran was considering Bitcoin payments for ships crossing the Strait of Hormuz. The waterway remains one of the world’s busiest energy routes, which has pushed the topic beyond crypto circles and into wider market discussions.
Alex Thorn, head of firmwide research at Galaxy, said later reports did not fully support the original Bitcoin claim. He said some accounts suggested the tolls could instead be settled in stablecoins or Chinese yuan, which left the payment method unclear.
That uncertainty has driven much of the reaction from Bitcoin supporters and market analysts. With no confirmed payment framework in place, traders and industry figures have treated the story as a developing issue rather than a settled policy.
The lack of an official and detailed public plan from Iranian authorities has also kept room for doubt. For now, the crypto market is responding more to reports and commentary than to a final rule.
Bitcoin and stablecoins draw different arguments
Bitcoin supporters argued that BTC would be harder for outside parties to freeze or block. Justin Bechler said, “USDT and USDC include built-in blacklist functions at the smart contract level,” adding that issuers can freeze funds when addresses are flagged.
He also said, “Bitcoin has no issuer, no compliance officer to pressure, and no freeze function.” That argument has pushed some market participants to present Bitcoin as a more resilient option for cross-border settlement under sanctions pressure.
Still, that view has not settled the debate. Stablecoins remain widely used in global crypto payments because they reduce price swings, and that may still matter for any large commercial transaction tied to oil shipping.
The discussion also reflects the difference between theory and practice. A payment method may look strong on paper, but large state-linked payments depend on speed, scale, compliance risk, and operational ease.
Payment size and logistics remain key issues
Thorn estimated that tanker tolls could range from $200,000 to $2 million per ship. That size has raised doubts about whether the Lightning Network would be the main rail, even though some early reporting suggested a payment could be completed within seconds.
He said the more likely setup would involve Iran providing a QR code or a Bitcoin address after approving a ship’s passage. That method would avoid the limits that can affect very large Lightning payments.
Thorn also noted that the largest known Lightning transaction to date was about $1 million. That figure matters because some tanker tolls may sit above that level, which could make direct onchain settlement or pre-arranged transfers more practical.
Crypto World
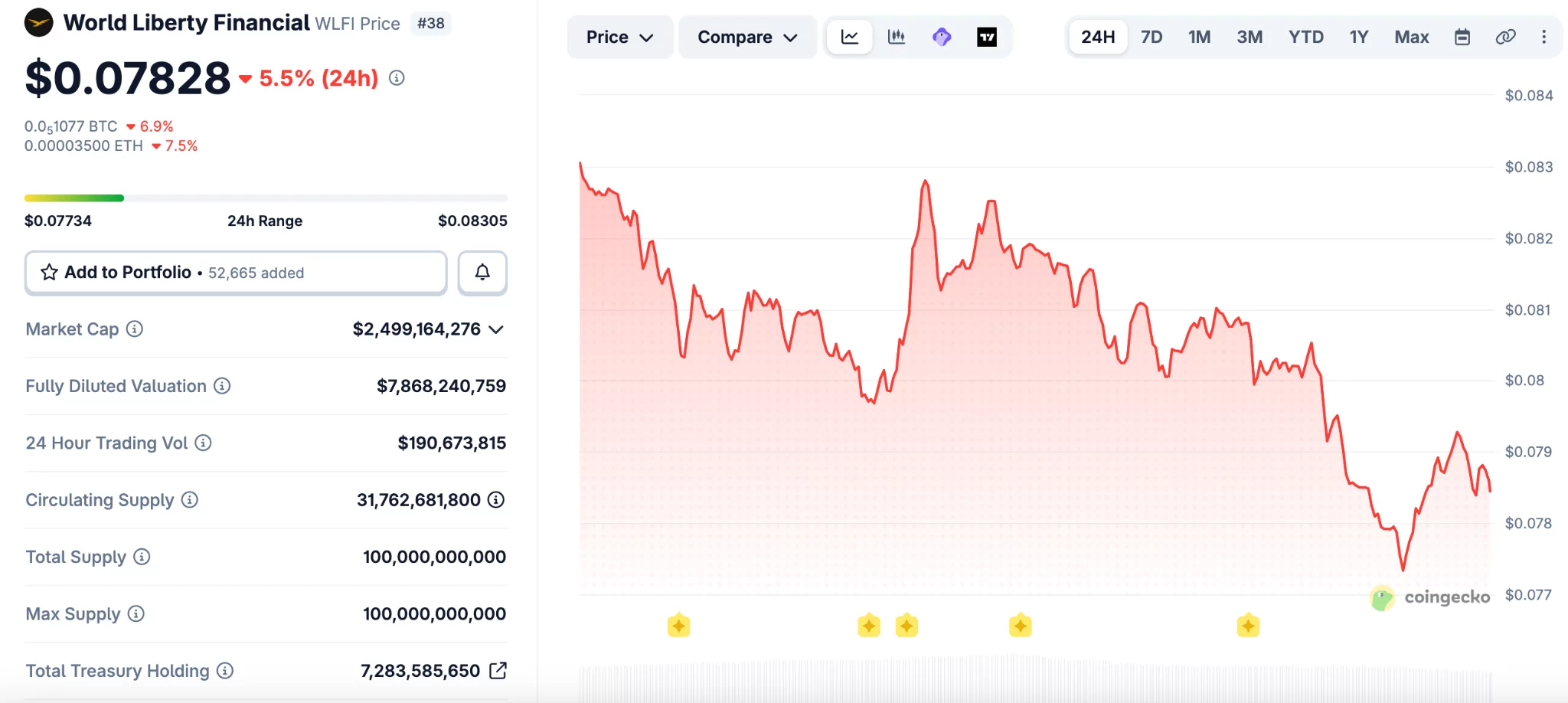
WLFI Drops to Record Low After Token-Backed Borrowing Raises Risk Concerns
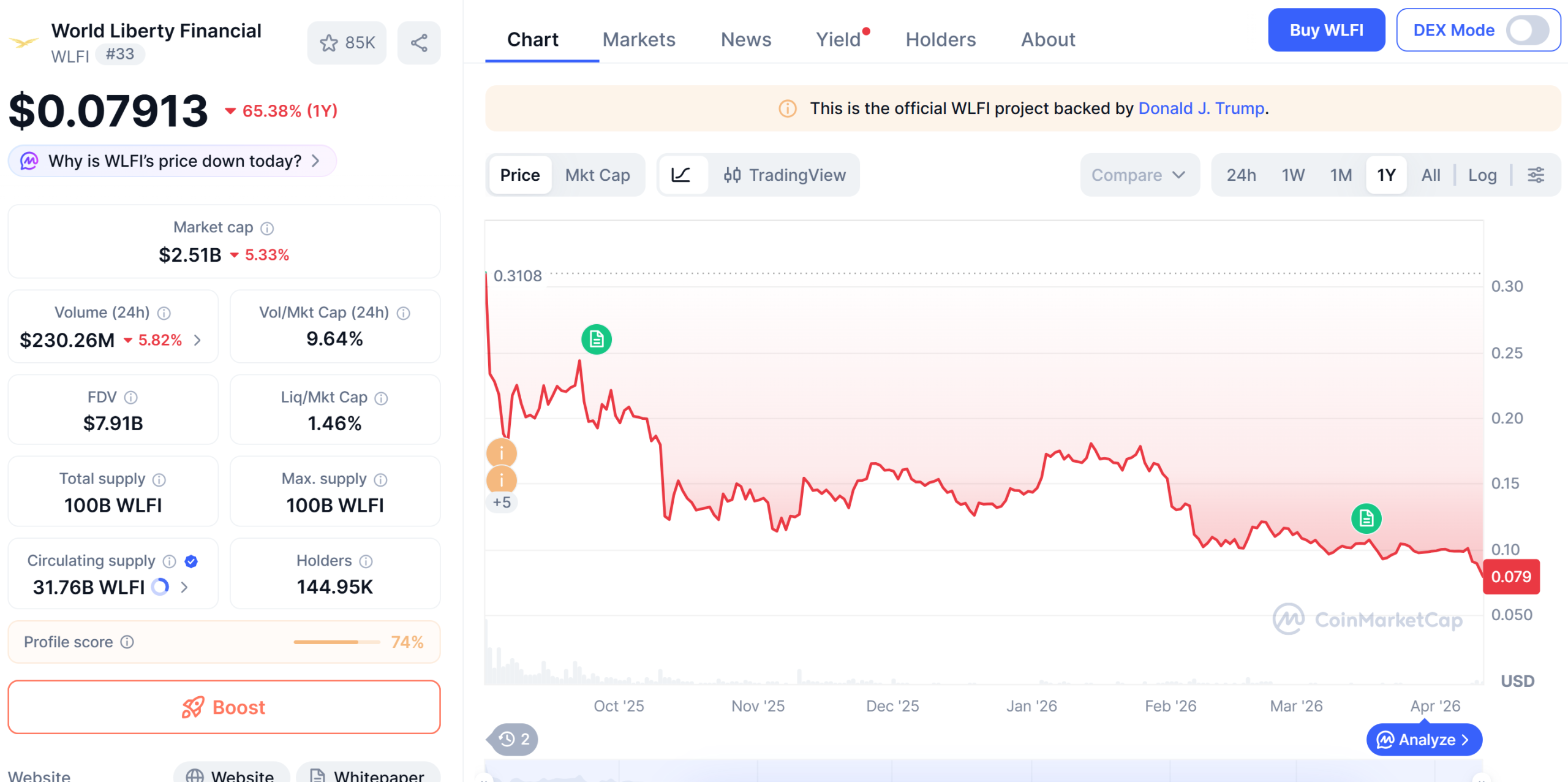
WLFI, the native token of the Donald Trump–backed World Liberty Financial platform, sank to an all-time low on Saturday as crypto users expressed concerns after revelations that the project used a large amount of its own tokens to take out loans.
The token hit a new low of around $0.07714 on Saturday, down 83% from its peak of $0.46 reached last September, according to data from CoinMarketCap. WLFI is currently at $0.07879, down by 4.66% over the past day.
The downturn came after it was revealed that wallets linked to World Liberty Financial deployed substantial WLFI holdings as collateral on Dolomite, a decentralized lending platform co-founded by the project’s chief technology officer, Corey Caplan.
Onchain data from Arkham shows that a wallet linked to World Liberty Financial deposited around 5 billion WLFI tokens on Dolomite. The wallet then used the tokens as collateral to borrow $75 million in USD1 and USDC (USDC) stablecoins, later transferring more than $40 million to Coinbase Prime.
Related: CFTC unveils innovation task force members in crypto clarity push
WLFI-backed loan position sparks concerns
The large collateral position has raised concerns among DeFi analysts, who warn it could create risks for lenders on Dolomite if WLFI’s price falls and approaches liquidation levels.
“WLFI has almost a $10 billion FDV, but it is not an extremely liquid asset,” one user wrote on X. “So imagine what would happen if 5% of WLFI’s total supply would suddenly need to be sold to liquidate the position,” he added.
Another X user argued that the setup resembles creating artificial “chips” and borrowing against them. “It’s the financial equivalent of printing casino chips, borrowing cash against them, and telling everyone else not to panic because the house still believes in the chips,” they claimed.
Dolomite has a relatively small footprint in decentralized finance, ranking 19th among lending platforms by total value locked, according to DefiLlama.
Related: White House warns staff as Iran bets add to growing insider trading concerns
World Liberty defends WLFI lending
World Liberty Financial acknowledged the lending activity on social media, but sought to calm markets, stating that its positions remain well above liquidation thresholds. The project described itself as an “anchor borrower” for WLFI and argued that the strategy helps generate yield.
“Everyday users are earning outsized stablecoin yields right now — at a time when traditional markets are offering very little. That’s the whole point,” the project wrote on X.
On Friday, World Liberty said it will soon introduce a governance proposal to create a phased unlock schedule for WLFI tokens held by early retail buyers, replacing immediate access with a long-term vesting plan subject to community vote.
Magazine: Bitcoin may take 7 years to upgrade to post-quantum — BIP-360 co-author
-

 Business5 days ago
Business5 days agoThree Gulf funds agree to back Paramount’s $81 billion takeover of Warner, WSJ reports
-

 Sports7 days ago
Sports7 days agoIndia men’s 4x400m and mixed 4x100m relay teams register big progress | Other Sports News
-

 Politics17 hours ago
Politics17 hours agoUS brings back mandatory military draft registration
-

 Fashion17 hours ago
Fashion17 hours agoWeekend Open Thread: Veronica Beard
-

 Tech4 days ago
Tech4 days agoHow Long Can You Drive With Expired Registration? What Florida Law Says
-

 Business6 days ago
Business6 days agoNo Jackpot Winner, Prize to Climb to $231 Million
-

 Fashion5 days ago
Fashion5 days agoMassimo Dutti Offers Inspiration for Your Summer Mood Board
-

 Sports18 hours ago
Sports18 hours agoMan United discover Nico Schlotterbeck transfer fee as defender reaches Dortmund agreement
-

 Fashion4 days ago
Fashion4 days agoLet’s Discuss: DEI in 2026
-

 Crypto World3 days ago
Crypto World3 days agoBitcoin recovers as US and Iran Agree a Ceasefire Deal
-

 Crypto World2 days ago
Crypto World2 days agoCanary Capital Files SEC Registration for PEPE ETF
-

 Business14 hours ago
Business14 hours agoTesla Model Y Tops China Auto Sales in March 2026 With 39,827 Registrations, Beating Cheaper EVs and Gas Cars
-

 Business6 days ago
Business6 days agoAkebia Therapeutics, Inc. (AKBA) Discusses Pipeline Progress and Strategic Focus on Kidney Disease Treatments at R&D Day – Slideshow
-

 Business23 hours ago
Business23 hours agoOpenAI Halts Stargate UK Data Centre Project Over Energy Costs and Copyright Row
-

 Tech5 days ago
Tech5 days agoGamer Restores the Original PlayStation Portal From Two Decades Ago
-

 Tech5 days ago
Tech5 days agoHaier is betting big that your next TV purchase will be one of these
-
 Tech5 days ago
Tech5 days agoThe Xiaomi 17 Ultra has some impressive add-ons that make snapping photos really fun
-
 Tech5 days ago
Tech5 days agoSamsung just gave up on its own Messages app
-

 Tech5 days ago
Tech5 days agoSave $130 on the Samsung Galaxy Watch 8 Classic: rotating bezel, sleep coaching, and running coach for $369
-

 Tech5 days ago
Tech5 days agoItalian court says Netflix must refund customers up to $576 over price hikes













You must be logged in to post a comment Login