


The Dutch Ministry of Finance confirmed on Monday that some of its systems were breached in a cyberattack detected last week. Officials said the ministry was...
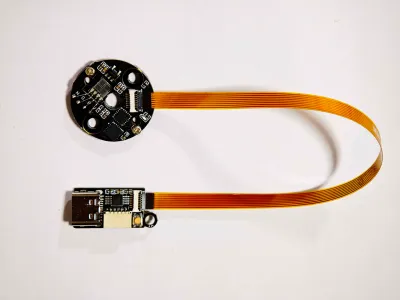
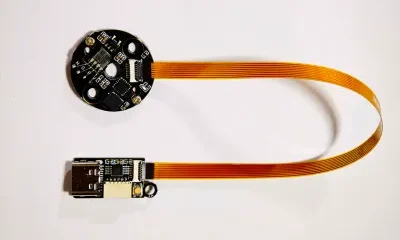

Some people love fiddling with their 3D printers, others love printing. Some fiddle so they can spend more time printing, which is probably where this latest...



BrianFagioli writes: Canonical has joined the Rust Foundation as a Gold Member, signaling a deeper investment in the Rust programming language and its role in modern...



In a CNN interview in which he was asked about Apple’s upcoming 50th anniversary and how the company has shaped the tech industry, Wozniak was asked...



from the because-i-got-section-230 dept The internet has been rightfully enjoying videos from the defamation trial against Afroman, a musician known for his humorous songs including “Because...
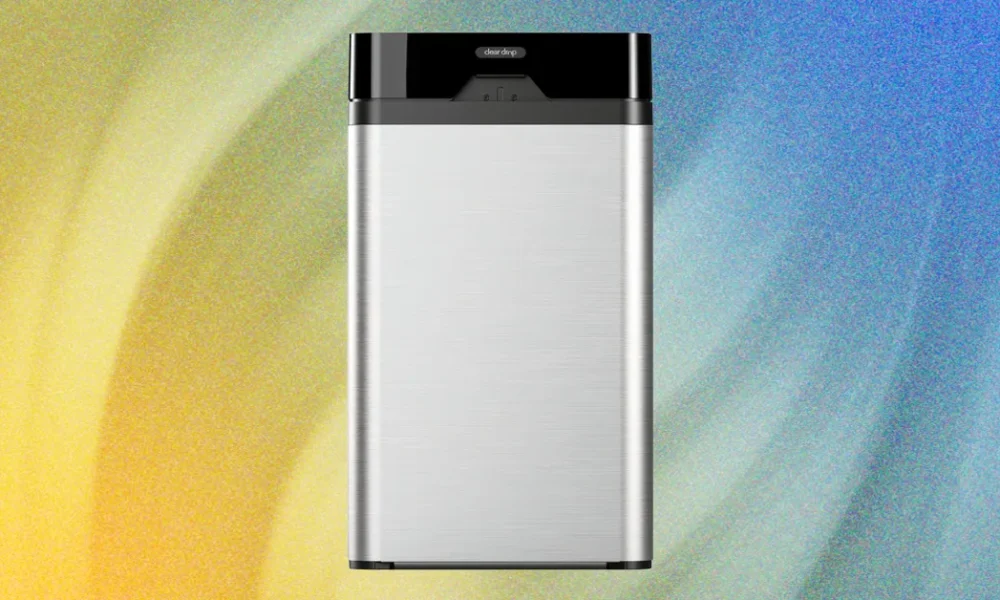


Soft plastics are notorious for jamming sorting machines, slipping through processing lines, and wreaking havoc on the environment. They’re also not accepted in most municipal curbside...



Plenty of old handhelds spend their retirement gathering dust in a box somewhere, and this Game Boy Advance was no exception. Abandoned, completely dead, and sporting...



The Tycoon2FA phishing-as-a-service (PhaaS) platform that Europol and partners disrupted on March 4 has already returned to previously observed activity levels. Microsoft led the technical disruption,...
The Kubernetes community retired Ingress NGINX this month after years of under-resourcing. The migration scramble it triggered is now consolidating around one open source beneficiary, and...



Jay Leno climbed into the cab of a Tesla Semi, settled into the center seat, and eased the truck forward with a fully loaded trailer in...