Crypto World
Betterment Confirms Data Breach After Crypto Phishing Attack

Betterment has confirmed a security incident in which attackers exploited social engineering to access third-party tools used by the company, exposing customer contact data and enabling a targeted crypto-themed phishing attempt. The breach, detected on January 9, did not involve compromised passwords or customer accounts, according to the firm. Still, the episode highlights how marketing and operations platforms can become a weak link, especially when attackers leverage trusted communication channels to deceive users.
Key takeaways
- Unauthorized access occurred on January 9 through social engineering targeting third-party platforms used for marketing and operations.
- Exposed data included names and email addresses, and in some cases postal addresses, phone numbers, and dates of birth.
- Attackers sent a fraudulent crypto-related message to a subset of customers, attempting to solicit funds.
- No customer accounts, passwords, or login credentials were accessed, according to the company’s investigation.
- Betterment engaged CrowdStrike for forensics and plans a post-incident review within 60 days.
Market context: Social engineering and phishing remain among the most common attack vectors in fintech, with third-party SaaS tools increasingly targeted as firms expand digital communications and customer outreach.
Why it matters
The incident underscores the risks associated with outsourced platforms that handle customer communications. Even when core infrastructure remains secure, attackers can exploit peripheral systems to reach users at scale.
For customers, the breach serves as a reminder that legitimate-looking messages can be deceptive, particularly when they reference popular investment themes like crypto. For fintech firms, it reinforces the need to secure not only internal systems but also the broader vendor ecosystem.
What to watch next
- Publication of Betterment’s post-incident review within the next 60 days.
- Results from the independent data analytics review assessing potential privacy risks.
- Any regulatory or customer notifications that follow the final investigation.
- Changes to Betterment’s controls and training aimed at preventing social engineering.
Sources & verification
- Betterment customer updates published between January 9 and February 3, 2026.
- Company statements confirming forensic findings and remediation steps.
- Details of the phishing message and affected data categories described in official updates.
How the breach unfolded and what it revealed
Betterment disclosed that an unauthorized individual gained access to certain company systems on January 9 by impersonating legitimate users and exploiting trust-based workflows. Rather than breaching core technical infrastructure, the attacker leveraged social engineering tactics against third-party software platforms that support marketing and operational functions.
This access allowed the attacker to view and extract customer contact information. According to the company, the data exposure primarily involved names and email addresses, though in a subset of cases it also included physical addresses, phone numbers, and birthdates. The total number of affected customers has not been disclosed.
Using the compromised access, the attacker distributed a fraudulent message that appeared to originate from Betterment. The notification promoted a fake crypto-related opportunity, claiming that users could triple the value of their holdings by sending $10,000 to a wallet controlled by the attacker. The message was sent to a limited group of customers whose contact details were accessible through the breached systems.
Betterment said it identified the unauthorized activity on the same day and immediately revoked access to the affected platforms. An internal investigation was launched, supported by the cybersecurity firm CrowdStrike, to determine the scope of the intrusion and verify whether customer accounts or credentials were at risk.
Subsequent forensic analysis found no evidence that the attacker accessed Betterment customer accounts, passwords, or login credentials. The company emphasized that multiple layers of security protected account-level systems and that the breach was confined to contact data and communications tooling.
In the days following the incident, Betterment contacted customers who received the fraudulent message and advised them to disregard it. The firm reiterated that it would never request passwords or sensitive personal information via email, text, or phone calls.
The security incident coincided with additional disruptions in mid-January. On January 13, Betterment experienced intermittent outages to its website and mobile app caused by a distributed denial-of-service attack. The company restored partial service within about an hour and full access later that afternoon, stating that the DDoS event did not compromise account security.
By early February, Betterment provided further updates on its investigation. The company confirmed that while some customer data had been accessed, the privacy impact appeared limited to contact information. An independent data analytics firm was engaged to review all accessed data, including information that a group claiming responsibility for the breach alleged it had posted online.
Betterment also noted that it plans to publish a comprehensive post-incident review within 60 days. In parallel, the company said it is strengthening controls and training programs to better defend against social engineering attempts, which rely on deception rather than technical exploits.
One aspect of the disclosure drew scrutiny from security observers. As of publication, Betterment’s security incident webpage included a “noindex” directive in its source code, instructing search engines not to index the page. While such tags are sometimes used during active investigations, they can make it harder for customers and the public to discover information about breaches through web searches.
The incident reflects a broader pattern across the fintech and crypto-adjacent sectors, where attackers increasingly target trusted communication channels instead of core systems. As companies integrate more third-party tools to manage customer relationships, marketing campaigns, and operational workflows, the attack surface expands beyond traditional network defenses.
For Betterment, the episode has so far not resulted in confirmed financial losses or account takeovers. Still, it highlights how quickly trust can be tested when attackers successfully impersonate a well-known financial platform. The company’s forthcoming post-incident review will likely provide further insight into how the breach occurred and what safeguards will be implemented to reduce the risk of similar attacks in the future.
Crypto World
Crypto giant debuts WTI trading, but it’s a different model to Hyperliquid’s perps


The Iran war has set oil on fire and crypto exchanges are racing to offer 24/7 trading to fill tradfi gaps, with most copying decentralized giant Hyperliquid’s perpetual-futures play.
Crypto market-making giant Wintermute is taking a different approach. On Tuesday, its derivatives unit, Wintermute Asia, launched over-the-counter (OTC) trading in WTI crude oil contracts for difference (CFDs).
CFD is type of derivative that allows traders to speculate on the price movement of an asset without owning it. Similar to futures, CFDs track the asset’s price, but the key difference is that only the difference between the opening and closing prices is exchanged between the trader and the broker when the contract is closed.
These are typically traded over-the-counter and can be tailored in term sof size, duration and margin requirements. This bespoke flexibility allows professional traders and institutions to design strategies that match specific risk-return objectives, rather than conforming to one-size-fits-all derivatives such as Hyperliquid’s oil perpetual futures.
Wintermute’s CFD launch comes amid weeks of intense geopolitical volatility in the Middle East. Escalating tensions between Iran and the U.S.–Israel coalition have left traders in a bind over weekends when traditional finance markets are closed, limiting their ability to adjust positions or manage risk effectively. This led to outsized trading activity on Hyperliquid’s energy market perpetuals and prompted WIntermute to offer CFDs.
“We are seeing strong demand from counterparties looking to use digital asset infrastructure to trade traditional products like oil. The recent price action made that need much more immediate, as many investors were unable to act until traditional venues reopened,” said Evgeny Gaevoy, CEO of Wintermute.
“A Wintermute counterparty could have traded the weekend move before the Monday gap or responded immediately to the reversal,” Gaevoy added.
Note that Wintermute is a counterparty in the CFD. Traders aren’t matched with each other; they are trading directly against Wintermute, which is taking on the market risk. The firm is, therefore, leveraging its risk management systems and deep liquidity to monetize demand for 24/7 crude than simply supplying liquidity to perpetual futures.
Traders can access WTI CFDs with zero trading fees, using a variety of fiat and crypto assets as margin, the official announcement said. Contracts can be executed via chat, Wintermute’s electronic OTC platform, or API. The rollout builds on the recent introduction of tokenized gold, further broadening Wintermute Asia’s suite of offerings beyond purely digital assets.
Crypto World
Enlivex Raises Funds for Rain Prediction Market Token Buys

Immunotherapy company Enlivex has raised $21 million via a debt financing agreement to purchase another 3 billion tokens tied to the prediction market platform Rain.
Enlivex said on Tuesday it exercised an option to acquire another 3 billion Rain (RAIN) tokens at a 62% discount for $10 million on Sunday while extending its option to purchase another 272.1 billion RAIN tokens at the same price to December 2027. The debt financing came from The Lind Partners, a New York-based asset manager.
“We are continuing to execute our prediction markets treasury strategy, and we are pleased that Lind provided us with substantial capital, allowing us to continue the execution of our operating plan, as well as to acquire approximately three billion additional RAIN tokens,” said Enlivex executive chair Shai Novik.
Enlivex develops cell therapy solutions for knee osteoarthritis, but is one of several non-crypto companies that have purchased cryptocurrencies in the hopes that it will strengthen their balance sheets and attract a wider base of investors.
The company also said it approved a $20 million share buyback program, aimed at enhancing shareholder value.

The value of Enlivex’s RAIN treasury is directly tied to Rain’s decentralized prediction market platform, which has a built-in 2.5% fee that automatically buys back and burns RAIN tokens in a bid to boost the token’s supply-demand dynamics.
RAIN token, Envilex shares trade mostly flat
The Rain token rose 7% to $0.009 after Enlivex’s announcement before falling slightly to $0.0088, trading flat over the last 24 hours with a 0.3% gain, according to CoinGecko.
Shares in Enlivex (ENVL) also traded mostly flat on Tuesday and closed the trading day down 0.9% to $1.10, but gained 4.5% in after-hours trading, rising to $1.15.
Related: Kalshi, Polymarket eye $20B valuations in potential fundraising: WSJ
Rain runs on the Ethereum Layer-2 Arbitrum network and ranks among the top 10 prediction market platforms by total value locked and fees over the past seven days, DeFiLlama data shows.
Prediction markets have become one of the hottest use cases in crypto, with trading volumes increasing more than 1,200% to $23.3 billion between February 2025 and February 2026.
The market continues to be dominated by Kalshi and Polymarket, however, which account for more than 80% of trading volumes.
Magazine: IronClaw rivals OpenClaw, Olas launches bots for Polymarket — AI Eye
Crypto World
The Illusion of Decentralization – Smart Liquidity Research

Whales Control More of DeFi Than You Think
(And they’re better at the game.)
DeFi sells a powerful narrative: open, permissionless, and fair. Anyone with a wallet can participate. No gatekeepers. No middlemen. Just code.
But beneath that ideal lies a quieter reality—one where a relatively small group of high-capital players, known as whales, exert outsized influence over markets, governance, and even protocol design.
It’s not exactly a conspiracy. It’s just math… and a lot of money.
Who Are the Whales?
In traditional finance, they’d be hedge funds, market makers, or ultra-high-net-worth individuals. In DeFi, they’re wallet addresses holding massive amounts of capital—often early adopters, crypto-native funds, or insiders who got in before things were cool.
While retail users are debating APRs on Twitter, whales are moving liquidity across protocols like chess pieces—strategically, quietly, and with a level of coordination that’s hard to track in real time.
Liquidity Is Power
In DeFi, liquidity isn’t just participation—it’s control.
Protocols rely on liquidity pools to function. The deeper the pool, the better the trading experience. But here’s the catch: whales provide a significant chunk of that liquidity.
That gives them leverage:
- They can move markets by adding or removing liquidity.
- They can farm incentives efficiently, capturing the majority of rewards.
- They can influence token price stability just by repositioning funds.
When a whale exits a pool, it’s not just a withdrawal—it’s a shockwave.
Governance: One Token, One Vote… Sort Of
On paper, DeFi governance is democratic. In reality, it’s closer to shareholder capitalism.
Voting power is typically proportional to token holdings. So when whales hold a large percentage of governance tokens, they effectively steer protocol decisions.
That includes:
- Emissions schedules
- Treasury allocations
- Protocol upgrades
- Incentive structures
Retail users can vote—but whales decide.
And if you’ve ever wondered why some proposals seem oddly favorable to large holders… well, now you know.
The Strategy Gap
It’s not just about capital. Whales are better at the game.
They have:
- Access to private deal flow (early token allocations, OTC trades)
- Custom tools and bots for execution and monitoring
- Teams and analysts tracking opportunities across chains
- Risk management frameworks that go beyond “ape and pray.”
While retail users chase yield, whales engineer it.
They hedge positions, loop strategies, and optimize gas like it’s a competitive sport. By the time a “hot opportunity” hits Crypto Twitter, whales have already extracted most of the value.
Incentives Are Designed Around Them
Here’s the uncomfortable truth: many DeFi protocols need whales.
High TVL looks good. Deep liquidity attracts users. Large holders stabilize ecosystems—until they don’t.
So protocols often design incentives that naturally favor bigger players:
- Tiered rewards
- Volume-based perks
- Early access programs
- Governance influence
It’s not malicious—it’s survival. But it does tilt the playing field.
So, Where Does That Leave Retail?
At a disadvantage? Yes. Completely powerless? Not quite.
Retail users still have advantages:
- Agility – You can enter and exit positions faster without moving markets.
- Narrative awareness – You’re often closer to emerging trends and communities.
- Lower expectations – You don’t need to deploy millions to win.
The key is understanding the game you’re in.
Stop assuming DeFi is a level playing field. It isn’t. But that doesn’t mean you can’t play smart.
Playing Smarter in a Whale’s Ocean
If whales dominate through capital and strategy, retail wins through awareness and timing.
A few mindset shifts:
- Follow liquidity, not hype
- Watch wallet movements, not influencer threads
- Prioritize sustainability over short-term APY
- Assume you’re late—and act accordingly
And most importantly: don’t confuse accessibility with equality.
Final Reflections
DeFi didn’t eliminate power dynamics—it just made them more transparent (if you know where to look).
Whales aren’t villains. They’re just better-equipped players operating in a system that rewards scale, speed, and strategy.
The real edge isn’t pretending they don’t exist.
It’s learning how they move—and positioning yourself before the splash hits.
REQUEST AN ARTICLE
Crypto World
Retail traders fare worse on prediction markets than sportsbooks


Prediction markets are exciting, but they’re not reliable wealth builders for retail users.
Research by Citizens shows that retail prediction market users are losing more money than legal sports bettors, with the sharpest traders and market makers capturing returns on the other side of their flow which. The research note also reveals the platforms are drawing a younger demographic than traditional sportsbooks.
The median return for a prediction market user was -8% from July 2025 through mid-March, compared with -5% for sports book users over the same period, Citizens JMP Securities analyst Jordan Bender wrote, citing transaction data from analytics company Juice Reel.
Individuals trading more than $500,000 on prediction markets generated a median ROI of +2.6%, consistent with sharp-bettor benchmarks validated by professional players. Every cohort below that level was negative, sliding to -26.8% for users trading less than $100.
No cohort within legal sports betting was profitable either, but the decay is less severe: the $500,000-plus sports betting cohort posted -0.6%, and the smallest accounts came in at -29.3%.
One of the major differences between the two platforms is who is on the other side of the trade.
Prediction markets do not limit or ban profitable users the way regulated sportsbooks do, concentrating informed flow on the platforms. That flips the traditional model. In sportsbooks, the house manages risk and filters out winning players. In prediction markets, retail traders are directly exposed to professionals, market makers, and high-volume participants who consistently take the other side of less informed flow.
Two professional bettors on a Citizens JMP call last week said prediction markets offer a more attractive path to positive returns precisely because retail users provide the liquidity, the note reads.
Are prediction markets a threat to online gambling?
Gaming CEOs have dismissed the threat of prediction markets, according to the Citizens JMP report, which compiled executive commentary from 4Q25 earnings calls.
DraftKings’ Jason Robins said prediction markets are not materially incremental to existing customers. Flutter’s Peter Jackson said the company found no evidence of material cannibalization. BetMGM’s Adam Greenblat estimated a low-to-mid-single-digit percentage impact on betting revenue. Citizens JMP’s own estimate is around 5%.
The bigger issue may not be cannibalization but acquisition. About 24% of Kalshi users are under 25, with a median age of 31, compared with just 7% for DraftKings and FanDuel, where the median age is closer to 35, according to Sensor Tower data cited in the report. Roughly 90% of DraftKings revenue comes from users over 30, the report said.
FanDuel and DraftKings downloads fell 18% and 13% year-over-year from September 2025 through February 2026, per Sensor Tower data cited by Citizens JMP. Over the same stretch, Kalshi logged 6.3 million downloads.
Prediction markets may not be pulling existing sportsbook users away. They may be intercepting the next generation before they ever download DraftKings.
Crypto World
The Illusion of Decentralization – Smart Liquidity Research
Whales Control More of DeFi Than You Think
(And they’re better at the game.)
DeFi sells a powerful narrative: open, permissionless, and fair. Anyone with a wallet can participate. No gatekeepers. No middlemen. Just code.
But beneath that ideal lies a quieter reality—one where a relatively small group of high-capital players, known as whales, exert outsized influence over markets, governance, and even protocol design.
It’s not exactly a conspiracy. It’s just math… and a lot of money.
Who Are the Whales?
In traditional finance, they’d be hedge funds, market makers, or ultra-high-net-worth individuals. In DeFi, they’re wallet addresses holding massive amounts of capital—often early adopters, crypto-native funds, or insiders who got in before things were cool.
While retail users are debating APRs on Twitter, whales are moving liquidity across protocols like chess pieces—strategically, quietly, and with a level of coordination that’s hard to track in real time.
Liquidity Is Power
In DeFi, liquidity isn’t just participation—it’s control.
Protocols rely on liquidity pools to function. The deeper the pool, the better the trading experience. But here’s the catch: whales provide a significant chunk of that liquidity.
That gives them leverage:
- They can move markets by adding or removing liquidity.
- They can farm incentives efficiently, capturing the majority of rewards.
- They can influence token price stability just by repositioning funds.
When a whale exits a pool, it’s not just a withdrawal—it’s a shockwave.
Governance: One Token, One Vote… Sort Of
On paper, DeFi governance is democratic. In reality, it’s closer to shareholder capitalism.
Voting power is typically proportional to token holdings. So when whales hold a large percentage of governance tokens, they effectively steer protocol decisions.
That includes:
- Emissions schedules
- Treasury allocations
- Protocol upgrades
- Incentive structures
Retail users can vote—but whales decide.
And if you’ve ever wondered why some proposals seem oddly favorable to large holders… well, now you know.
The Strategy Gap
It’s not just about capital. Whales are better at the game.
They have:
- Access to private deal flow (early token allocations, OTC trades)
- Custom tools and bots for execution and monitoring
- Teams and analysts tracking opportunities across chains
- Risk management frameworks that go beyond “ape and pray.”
While retail users chase yield, whales engineer it.
They hedge positions, loop strategies, and optimize gas like it’s a competitive sport. By the time a “hot opportunity” hits Crypto Twitter, whales have already extracted most of the value.
Incentives Are Designed Around Them
Here’s the uncomfortable truth: many DeFi protocols need whales.
High TVL looks good. Deep liquidity attracts users. Large holders stabilize ecosystems—until they don’t.
So protocols often design incentives that naturally favor bigger players:
- Tiered rewards
- Volume-based perks
- Early access programs
- Governance influence
It’s not malicious—it’s survival. But it does tilt the playing field.
So, Where Does That Leave Retail?
At a disadvantage? Yes. Completely powerless? Not quite.
Retail users still have advantages:
- Agility – You can enter and exit positions faster without moving markets.
- Narrative awareness – You’re often closer to emerging trends and communities.
- Lower expectations – You don’t need to deploy millions to win.
The key is understanding the game you’re in.
Stop assuming DeFi is a level playing field. It isn’t. But that doesn’t mean you can’t play smart.
Playing Smarter in a Whale’s Ocean
If whales dominate through capital and strategy, retail wins through awareness and timing.
A few mindset shifts:
- Follow liquidity, not hype
- Watch wallet movements, not influencer threads
- Prioritize sustainability over short-term APY
- Assume you’re late—and act accordingly
And most importantly: don’t confuse accessibility with equality.
Final Reflections
DeFi didn’t eliminate power dynamics—it just made them more transparent (if you know where to look).
Whales aren’t villains. They’re just better-equipped players operating in a system that rewards scale, speed, and strategy.
The real edge isn’t pretending they don’t exist.
It’s learning how they move—and positioning yourself before the splash hits.
REQUEST AN ARTICLE
Crypto World
Ripple taps Singapore sandbox to test stablecoin-powered trade finance with RLUSD


Ripple is testing whether its stablecoin can replace the manual payment processes that have slowed cross-border trade for decades, and Singapore’s central bank is giving it a sandbox to prove it.
The company said in a note shared with CoinDesk on Wednesday that it is participating in BLOOM, a Monetary Authority of Singapore initiative designed to extend settlement capabilities for tokenized bank liabilities and regulated stablecoins.
As part of the plan, Ripple is partnering with Unloq, a supply chain finance technology provider, to pilot a system where cross-border trade payments using RLUSD are released automatically when predefined conditions are met, such as shipment verification.
Traditional trade finance is built on layers of manual verification, documentary credits, and correspondent banking relationships that can take days or weeks to settle. The Ripple-Unloq pilot uses Unloq’s SC+ platform to bundle trade obligations, settlement conditions, and financing workflows into a single execution layer, with RLUSD on the XRP Ledger handling the actual money movement.
Singapore has positioned itself as the regulatory testing ground for institutional digital asset use cases, and BLOOM specifically targets the infrastructure layer rather than speculative products.
Getting into the program signals that MAS considers the RLUSD-on-XRPL stack credible enough for regulated experimentation, which matters more for Ripple’s enterprise pipeline than another exchange listing or payments corridor ever could.
This is the third significant Ripple announcement in three weeks.
The company expanded Ripple Payments into a full-stack stablecoin infrastructure platform, secured an Australian financial services license through acquisition, and now has a central bank-backed pilot for trade finance.
Ripple is building the regulatory and institutional credibility layer that turns RLUSD from a stablecoin with modest adoption into the settlement asset for enterprise use cases that require compliance and programmability.
Crypto World
Cardano (ADA) price signal that once preceded a 300% rally is back
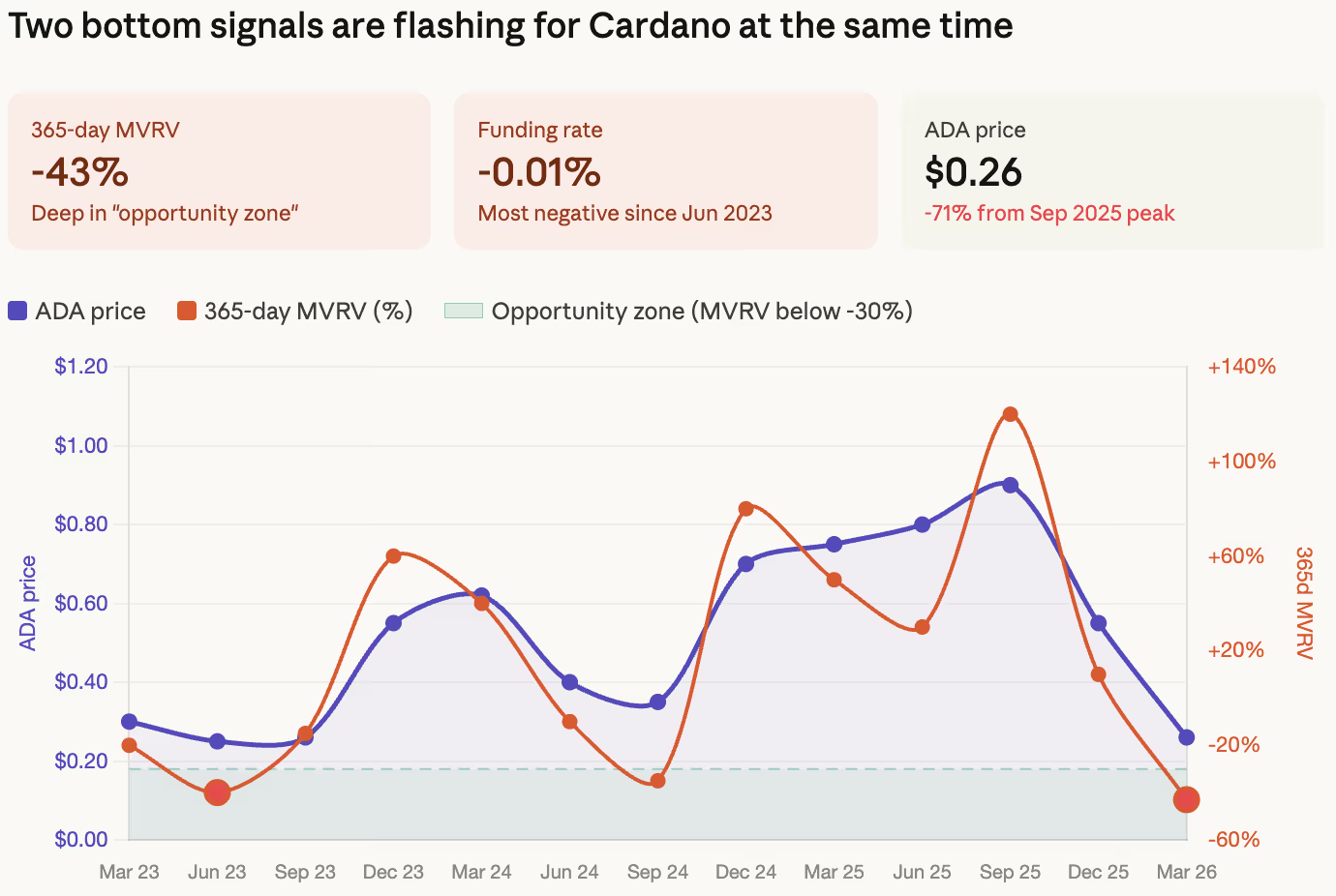
The average Cardano holder who bought in the past year is down 43%. The derivatives market is betting it gets worse. But both of those things happening at once have historically meant the opposite.
Santiment data shows ADA’s 365-day Market Value to Realized Value (MVRV) ratio has fallen to -43%, meaning wallets that have been active on the Cardano network over the past year are sitting on an average loss of 43% on their positions.
The metric is deep in what Santiment labels the “opportunity zone,” a band that previous instances in 2023 and late 2024 preceded recoveries as the MVRV mean-reverts toward zero.

MVRV measures average trading returns across a given timeframe, and it always gravitates back toward zero over time. When it’s extremely negative, the holders most likely to panic-sell have already sold. The remaining supply sits in hands that are either committed to holding or have already accepted the loss. That’s the kind of positioning that reduces further selling pressure and sets up the conditions for a bounce when any catalyst arrives.
At the same time, Binance’s weekly average funding rate for ADA has turned to its most negative reading since June 2023. Funding rates reflect the balance between long and short positioning in perpetual futures. A deeply negative rate means shorts are dominant and paying longs to keep their positions open. In simpler terms, the derivatives market is crowded on the bearish side.
That crowding is what makes it a contrarian signal. When shorts are this concentrated, any positive price movement triggers liquidations that force short sellers to buy back their positions, which pushes the price higher, which triggers more liquidations.
The cascade works in reverse too, but the historical pattern on ADA shows that funding rate extremes of this magnitude have preceded short squeezes more often than they’ve preceded further declines.
The last time both signals aligned this clearly was mid-2023, when ADA was trading around $0.25 before rallying roughly 300% over the following 18 months. That doesn’t mean the same outcome is guaranteed, however, as ADA is down 71% since its September peak, the broader market is dealing with a war, sticky inflation, and no rate cuts in sight, and Cardano’s ecosystem metrics haven’t produced the kind of usage growth that would justify a fundamental repricing.
But bottom signals aren’t about fundamentals. They’re about positioning. And the positioning on Cardano right now, with average holders at -43% returns and shorts at a three-year high, is the kind of setup where the next move catches the majority off guard.
ADA was trading at $0.26 on Tuesday, down roughly 7% on the week.
Crypto World
holds near $1.41 as range tightens, breakout setup builds


XRP is holding near $1.41 after a steady session, but price is stuck in a tight range, with neither buyers nor sellers taking control. The longer it stays compressed between support and resistance, the more likely a sharper move becomes.
News Background
- XRP traded in line with the broader crypto market, with no major token-specific catalyst driving price action.
- Whale wallets added roughly 40 million XRP over the past week, suggesting accumulation during consolidation.
- Market sentiment remains tied to macro conditions, with crypto reacting cautiously to interest rate expectations.
Price Action Summary
- XRP gained about 0.6%, moving from roughly $1.38 to $1.41
- Price traded within a tight $1.38–$1.43 range
- Repeated rejection near $1.42 capped upside
- Buyers defended dips near $1.38, forming higher lows
Technical Analysis
- XRP is trading in a tightening range, with support near $1.38 and resistance around $1.42.
- Higher lows suggest buyers are slowly stepping in, but lack of strong follow-through keeps momentum muted.
- The structure resembles a compression setup, where price coils before a larger move.
- Volume is slightly elevated but not strong enough yet to confirm a breakout.
What traders say is next?
- Traders are watching a break above $1.42 for a move toward $1.45–$1.50.
- If $1.38 support fails, downside could extend toward $1.30.
- For now, XRP remains range-bound, with the next move likely driven by a break on either side of this tightening range.
Crypto World
Robinhood Approves $1.5B Share Buyback
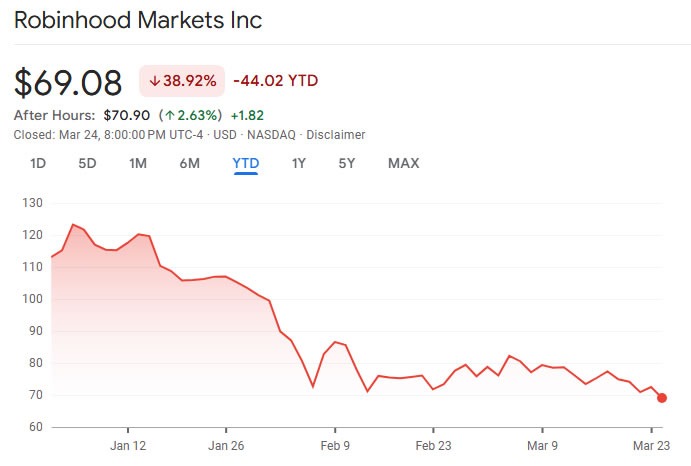
Stock and crypto trading platform Robinhood has approved to buy back $1.5 billion worth of its shares.
Robinhood said in a Securities and Exchange Commission filing on Tuesday that the company’s board of directors approved the $1.5 billion share repurchase program, which it will carry out over the next three years.
The program includes $1.1 billion in new incremental capacity, with the remainder rolled over from an older repurchase program.
“Robinhood is a generational company with a massive long-term opportunity,” Robinhood financial chief Shiv Verma said in a statement. “This authorization reflects the confidence of our management team and board in our ability to continue delivering innovative products for customers and creating value for shareholders while returning capital over time.”
The stock buyback, typically seen as signaling that a company believes its stock is undervalued, comes as shares in Robinhood (HOOD) have struggled so far this year amid a broad downturn in stocks and crypto.
Robinhood also said that its subsidiary, Robinhood Securities, entered a $3.25 billion revolving credit facility with JPMorgan Chase, replacing the prior $2.65 billion facility. It can expand by up to $1.62 billion, bringing the maximum credit to $4.87 billion.
Robinhood stock tanks nearly 5%
Shares in Robinhood ended trading on Tuesday, down 4.7% to $69.08, closing at the lowest level this year. The stock slightly recovered to $70.90 after hours.
Robinhood’s stock is down almost 39% so far this year and has lost 54.7% since its October all-time high of $152.46, as broader macroeconomic concerns and the Iran war impact stocks.

However, Robinhood’s share price over the past 12 months has seen it gain nearly 43% as its expanded into other products such as prediction markets and banking.
Analyst sentiment aggregator TipRanks puts the 12-month average Robinhood stock price forecast at $123.85 and agrees that the stock is a “strong buy” based on 16 Wall Street analysts.
Related: SEC gives go-ahead to Nasdaq for tokenized trading trial
Robinhood Chain to launch this year
Despite its share price woes, Robinhood remains committed to crypto and real-world asset tokenization, launching its own Ethereum layer-2 network to testnet in February.
CEO Vlad Tenev said that the network processed 4 million transactions in its first week of public testnet activity.
Robinhood Chain is designed to support tokenized equities, exchange-traded funds (ETFs) and other traditional financial instruments, and the mainnet launch is planned for later this year.
Magazine: Banks want to run Vietnam’s crypto exchanges, Boyaa’s $70M BTC plan: Asia Express
Crypto World
ECB Says Stablecoins and Tokenized Deposits Need Central Bank Money
Tokenized deposits and stablecoins need tokenized central bank money as a public settlement anchor if Europe’s tokenized financial markets are to scale, Piero Cipollone, a member of the European Central Bank’s Executive Board, said on Monday.
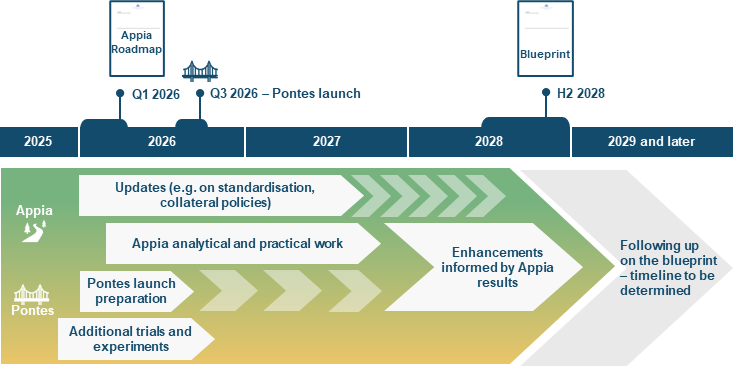
Cipollone pointed to Pontes, the Eurosystem’s distributed ledger technology (DLT) settlement initiative, which is designed to connect market DLT platforms with the Eurosystem’s TARGET Services and provide settlement in central bank money.
“Without tokenised central bank money, a seller of a tokenised security may receive payment in an asset they are not comfortable holding – one exposed to price volatility or credit risk – which limits the market’s ability to scale,” Cipollone said in a speech at the House of the Euro in Brussels on Monday.
The ECB said Pontes is due for an initial launch in the third quarter of 2026, allowing market participants to settle DLT-based transactions in central bank money. The comments build on the ECB’s broader Appia initiative, published on March 11, which is intended to produce a blueprint for a future European tokenized financial ecosystem by 2028.
Related: ECB opens digital euro work on ATMs and payment terminals
Europe’s tokenized markets need legal clarity
Beyond settlement in central bank money, Cipollone said Europe also needs closer public-private cooperation and a legal framework that matches the technology.
One of Appia’s building blocks serves as an interoperability standard for assets, ensuring that tokenized assets can be transferred across different DLT platforms via a compatible data format and smart contract standards.

Cipollone urged market infrastructure operators, banks, custodians and technology providers to explore and submit feedback related to the Appia roadmap, seeking to foster more public-private partnerships.
Related: Sweden’s H100 eyes Europe’s No. 2 Bitcoin treasury with 3,500 BTC deal
Cipollone also said Europe may ultimately need a dedicated legal framework to support the seamless issuance and transfer of tokenized assets across the bloc.
He called the European Commission’s proposal to extend the DLT Pilot Regime an “important development,” but cautioned that the absence of a holistic tokenization framework introduces the risk of “building advanced settlement infrastructure on a patchwork of regulations, leaving us unable to fully reap the benefits.”
The comments come days after stablecoin issuer Circle submitted feedback to the European Commission’s Market Integration Package on March 20, urging lawmakers to expand the existing DLT Pilot Regime and provide e-money token (EMT) cash account services to authorized crypto-asset service providers.
Magazine: How crypto laws changed in 2025 — and how they’ll change in 2026
-
Crypto World4 days ago
NIO (NIO) Stock Plunges 6.5% as Shelf Registration Sparks Dilution Worries
-

 Fashion5 days ago
Fashion5 days agoWeekend Open Thread: Adidas – Corporette.com
-

 Politics4 days ago
Politics4 days agoJenni Murray, Long-Serving Woman’s Hour Presenter, Dies Aged 75
-
 Crypto World3 days ago
Crypto World3 days agoBest Crypto to Buy Now: Strategy Just Spent $1.57 Billion on Bitcoin During Fear While Early Investors Quietly Enter Pepeto for 150x Potential
-

 News Videos7 days ago
News Videos7 days agoRBA board divided on rate cut, unusually buoyant share market | Finance Report | ABC NEWS
-
 Crypto World3 days ago
Crypto World3 days agoBitcoin Price News: Bhutan Sells $72 Million in BTC Under Fiscal Pressure, but the Smart Money Entering Pepeto Sees What the Market Does Not
-
 Politics7 days ago
Politics7 days agoThe House | The new register to protect children from their abusers shows Parliament at its best
-

 Tech5 days ago
Tech5 days agoinKONBINI Lets You Spend Summer Days Behind the Register
-

 Crypto World7 days ago
Crypto World7 days agoCanada’s FINTRAC revokes registrations of 23 crypto MSBs in AML crackdown
-

 Sports2 days ago
Sports2 days agoRemo Stars and Kano Pillars Strengthen Survival Hopes in NPFL
-
 NewsBeat6 days ago
NewsBeat6 days agoResidents in North Lanarkshire reminded to register to vote in Scottish Parliament Election
-

 News Videos7 days ago
News Videos7 days agoPARLIAMENT OF MALAWI – PAC MEETING WITH REGISTRAR OF FINANCIAL ON AMARYLLIS HOTEL – INQUIRY LIVE
-

 Politics5 days ago
Politics5 days agoGender equality discussions at UN face pushbacks and US resistance
-

 Business3 days ago
Business3 days agoNo Winner in March 21 Drawing as Prize Rolls to $133 Million for Next
-

 Business6 days ago
Business6 days agoWho Was Alex Pretti? 5 Key Facts About the ICU Nurse Killed by Federal Agents in Minneapolis
-
 Sports2 days ago
Sports2 days agoGary Kirsten Accuses Pakistan Cricket Board Of ‘Interference’, Mohsin Naqvi Responds
-
 Tech2 days ago
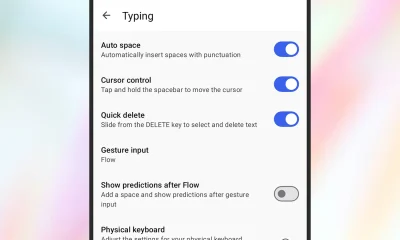
Tech2 days agoGive Your Phone a Huge (and Free) Upgrade by Switching to Another Keyboard
-

 Tech6 days ago
Tech6 days agoInventec’s bizarre VeilBook laptop hides its touchpad under a sliding keyboard just to give cooling fans a little breathing room
-
Sports6 days ago
Vikings Free Agency Enters Phase 2 with Key Questions
-

 Sports5 days ago
Sports5 days ago2026 Kentucky Derby horses, odds, futures, preview, date: Expert who nailed 12 Derby-Oaks Doubles enters picks










You must be logged in to post a comment Login