Crypto World
Bybit Crosses a Line in Rwanda That Binance Has Walked for Years Without Consequence

The National Bank of Rwanda (BNR) publicly warned citizens against using the Rwandan Franc (FRW) for crypto transactions, two days after global exchange Bybit listed FRW on its peer-to-peer (P2P) platform without regulatory clearance.
The BNR highlighted Bybit’s promotional announcement, stating that crypto-assets remain unauthorized for payments, FRW conversion, or P2P trading under current law.
Why Bybit’s Timing Could Not Have Been Worse
Rwanda has maintained a restrictive stance on private crypto since 2018, when the BNR first declared cryptocurrencies illegal for domestic use.
That position has shifted gradually. In March 2025, the BNR and the Capital Markets Authority (CMA) released a draft framework to regulate Virtual Asset Service Providers (VASPs).
The bill explicitly prohibits crypto as legal tender, bans crypto mining and mixers, and bars tokens pegged to the FRW.
On March 4, 2026, Rwanda’s Cabinet approved a comprehensive version of that bill. The Chamber of Deputies passed its general principles on March 31. Committee review continues.
Bybit launched its FRW P2P feature on April 2, just two days later, offering new-user rewards and bi-weekly merchant commissions.
Its announcement made no mention of local regulatory approval. Community members also flagged that promotional materials featured an outdated Rwandan national emblem.
A Direct Challenge to Rwanda’s CBDC Plans
The BNR is piloting its own Central Bank Digital Currency (CBDC), the e-FRW, following a proof-of-concept completed in February 2026. A 12-month domestic pilot is underway before international cross-border testing begins.
Unregulated foreign platforms attaching the FRW to crypto markets risk undermining that effort and eroding public trust in the currency.
The CMA has also cited pressure from the Financial Action Task Force (FATF) over crypto-linked money laundering as a core reason for formal regulation.
What Comes Next
Under the draft law, unlicensed VASP operators in Rwanda face fines up to 30 million FRW, roughly $21,000, and up to five years in prison.
Bybit has not publicly responded to the BNR’s warning. Binance and Remitano have offered FRW P2P pairs for years without triggering comparable pushback, suggesting Bybit’s loud promotional approach crossed a regulatory threshold.
Whether Bybit removes FRW voluntarily or waits for formal enforcement may set a precedent for every foreign exchange eyeing East Africa.
The post Bybit Crosses a Line in Rwanda That Binance Has Walked for Years Without Consequence appeared first on BeInCrypto.
Crypto World
Attorney Says Drift Protocol May Be Liable for Damages After Attack
The hack of the Solana-based decentralized finance (DeFi) platform Drift Protocol could have been prevented if standard operational security procedures were followed by the Drift team, and may constitute “civil negligence,” according to attorney Ariel Givner.
“In plain terms, civil negligence means they failed their basic duty to protect the money they were managing,” Givner said in response to the post-mortem update provided by the Drift team and how it handled Wednesday’s $280 million exploit.
The Drift team failed to follow “basic” security procedures, including keeping signing keys on separate, “air-gapped” systems that are never used for developer work, and conducting due diligence on blockchain developers met through industry conferences.

“Every serious project knows this. Drift didn’t follow it,” she said, adding, “They knew crypto is full of hackers, especially North Korean state teams.” Givner continued:
“Yet their team spent months chatting on Telegram, meeting strangers at conferences, opening sketchy code repos, and downloading fake apps on devices tied to multisignature controls.”
Advertisements for class action lawsuits against Drift Protocol are already circulating, she said. Cointelegraph reached out to the Drift Team but did not receive a response by the time of publication.

The incident is a reminder that social engineering and project infiltration by malicious actors are major attack vectors for cryptocurrency developers that could drain user funds and permanently erode customer trust in compromised platforms.
Related: Drift explains $280M exploit as critics question Circle over USDC freeze
Drift Protocol says attack took “months” of planning
The Drift Protocol team published an update on Saturday outlining how the exploit occurred and claimed that the attackers planned the attack for six months before execution.
Threat actors first approached the Drift team at a “major” crypto industry conference in October 2025, expressing interest in protocol integrations and collaboration.
The malicious actors continued to build rapport with the Drift development team in the ensuing six months, and once enough trust was built, they began sending the Drift team malicious links and embedding malware that compromised developer machines.
These individuals, who are suspected of working for North Korea state-affiliated hackers and physically approached the Drift developers, were not North Korean nationals, according to the Drift team.
Drift said, with “medium-high confidence,” that the exploit was carried out by the same actors behind the October 2024 Radiant Capital hack.
In December 2024, Radiant Capital said the exploit was carried out through malware sent via Telegram from a North Korea-aligned hacker posing as an ex-contractor.
Magazine: Meet the hackers who can help get your crypto life savings back
Crypto World
Bitcoin Liquidation Map Signals $6B Short Squeeze Risk Near Key $72.5K Level

TLDR:
- Over $6 billion in short positions face liquidation if the Bitcoin price rises toward the $72.5K level
- Nearly $2 billion in long positions are exposed to liquidation risk if Bitcoin drops below $65K
- Dense liquidation clusters between $68K and $74K may drive rapid upside price movement
- Lower zones around $60K to $66K show strong long liquidation pressure during downside moves
Bitcoin is approaching a critical price range where large leveraged positions face liquidation pressure. Data from a recent liquidation map shows billions in potential forced trades, with both upside and downside zones tightly packed around current levels.
Liquidation Map Reveals Tight Market Positioning
A recent post by Crypto Rover on X points to a sharp imbalance in Bitcoin’s liquidation landscape. The data shows over $6 billion in short positions at risk if Bitcoin climbs toward $72,500. Meanwhile, nearly $2 billion in long positions sit vulnerable near the $65,000 level.
The visualization tracks liquidation activity over a 30-day window. Bitcoin’s current price stands near $67,314, marked clearly on the chart. Price levels stretch from roughly $58,000 to $74,000, offering a clear view of where leverage is concentrated.
Above the current price, the cumulative short liquidation curve rises steeply. This indicates that many traders have opened short positions expecting a decline. As price moves higher, these positions face forced closure, which requires buying Bitcoin back.
Below the current level, the long liquidation curve grows steadily. This shows that many traders are positioned for upside but risk liquidation if prices fall. When these positions close, they trigger selling pressure.
Exchange-specific data adds more detail. Clusters from Binance, OKX, and Bybit show where liquidation activity is most concentrated. These zones often attract price movement due to the liquidity they provide.
Key Price Zones Define Market Direction
The liquidation map points to several high-activity zones that traders are watching closely. Around $65,000, there is a dense cluster of long liquidations. This area has already seen recent activity, making it a sensitive level.
Further down, the $60,000 to $62,000 range holds another concentration of long positions. If Bitcoin drops into this zone, forced selling could accelerate quickly. This type of movement often leads to sharp and rapid declines.
On the upside, liquidity builds strongly between $68,000 and $74,000. The most notable concentration appears between $72,000 and $74,000. This range holds the largest pool of short liquidations identified in the data.
If Bitcoin moves into this upper band, short sellers may be forced to exit positions. That process requires buying, which can push prices even higher. This chain reaction is often referred to as a short squeeze.
The current structure places Bitcoin between two pressure zones. Below the market, long positions risk liquidation and potential cascading sell-offs. Above the market, short positions create conditions for upward acceleration.
Crypto Rover’s tweet frames this setup as a market caught between competing forces. The larger liquidity pool sits above the current price, suggesting a strong area of interest. However, downside zones remain active and closely packed.
The map does not predict direction but shows where leverage is concentrated. Traders use this data to understand where forced activity may occur. These zones often act as magnets, drawing price toward areas with the most liquidity.
Crypto World
Michael Saylor Signals New Bitcoin Move as Strategy Holdings Face Short-Term Loss

TLDR:
- Strategy holds 762,099 BTC valued near $50.9B, maintaining one of the largest corporate Bitcoin positions globally.
- The firm reports an average entry price of $75,694 per BTC, with a current unrealized loss nearing $6.9B.
- Over 100 purchase events show a consistent accumulation strategy across multiple Bitcoin market cycles.
- Saylor’s recent post signals continued buying interest as market prices fluctuate within the $80K–$90K range.
Michael Saylor signaled renewed Bitcoin activity through a brief social media post and updated portfolio data from his firm.
The update presents a clear view of holdings, purchase history, and current performance during ongoing market fluctuations.
Bitcoin Holdings Show Ongoing Accumulation Strategy
Michael Saylor posted on X stating, “Back to Work,” alongside a dashboard tracking his firm’s Bitcoin reserves. He shared the update less than an hour before it gained rapid traction among market participants.
The dashboard shows total holdings of 762,099 BTC, valued at about $50.90 billion at current market prices. The firm holds an average acquisition cost of $75,694 per Bitcoin. Based on current pricing, the position shows an unrealized loss of nearly $6.9 billion, or about 12%.
The data also shows that the firm executed 104 separate purchase events over several years. It spread these acquisitions across different market cycles, including periods of volatility and recovery. The visual chart plots Bitcoin’s price movements alongside each purchase point.
A white line tracks Bitcoin’s price trend from 2020 through 2025. Orange markers show purchase entries, while a green dashed line marks the average cost basis. This layered view presents a structured accumulation approach instead of sporadic buying.
Crypto Patel stated that the firm could execute another Bitcoin purchase soon. The post referenced the firm’s 13th strategy tracker update in 2026.
Market Response and Current Performance
Saylor’s post drew strong engagement and sustained attention from market participants. Within the first hour, users posted hundreds of comments and reposts, while likes crossed several thousand. Views also exceeded 100,000, showing strong visibility.
At the same time, the dashboard shows that the portfolio remains below its total cost basis. The current valuation stands lower than the total investment of $57.69 billion. This gap reflects recent price movement within the $80,000 to $90,000 range.
The chart also captures earlier phases of Bitcoin’s market cycle. Prices moved sharply between 2020 and 2022, then climbed steadily into 2024 and 2025. Recent data points show a pullback from higher levels.
Despite the current gap, the firm continues its steady accumulation pattern. It placed purchase markers across both market highs and lows. This pattern aligns with a structured buying method instead of reactive trading.
Saylor paired his brief caption with a detailed dashboard to present a clear message of continued activity. The timing of the update, along with mentions of a possible new purchase, keeps attention on the firm’s next move.
The dataset reflects a long-term positioning strategy focused on Bitcoin. While current figures show a temporary shortfall, the firm continues its consistent purchase record. Market participants now watch closely for further updates.
Crypto World
Dogecoin Sits on Critical Support as Breakout Pressure Builds Toward Next Big Move

TLDR:
- Dogecoin trades near $0.09 support, with price action showing tight consolidation and reduced volatility
- A break above $0.12–$0.15 could signal renewed bullish momentum if supported by strong volume
- Continued weakness below $0.09 may push DOGE toward lower targets near $0.07 or even $0.05
- Historical data shows DOGE remains below prior yearly levels, reflecting a prolonged cooling phase
Dogecoin continues to trade near a critical support level, with recent market activity showing a balance between weakening bearish pressure and early signs of potential recovery. Price action remains compressed, keeping traders focused on the next decisive move.
Price Structure Signals Ongoing Consolidation
Recent chart data shared by Bitcoinsensus shows that Dogecoin has maintained a broad logarithmic uptrend channel since 2023.
The asset previously recorded strong upward moves of nearly 290% and 440% within this structure. However, the current price has returned to the lower boundary, where support is being tested again.
From late 2024, Dogecoin entered a clear downtrend after peaking near $0.45. The rally phase, which began around October 2024, saw rapid gains driven by strong speculative activity. Large bullish candles dominated this period, reflecting high volatility and increased market participation.
As momentum faded, the market shifted into a distribution phase between December 2024 and early 2025. During this period, price struggled to maintain higher levels and formed repeated rejection points. This eventually led to a breakdown, confirming the end of the prior bullish cycle.
Throughout 2025, the asset continued forming lower highs and lower lows. Temporary recoveries occurred, yet each rally failed to break above previous resistance levels. A sharp drop around October 2025 added further pressure, likely triggered by rapid liquidations or external market factors.
Since late 2025, price action has tightened within a narrow range between $0.09 and $0.10. Smaller candles now reflect reduced volatility and a lack of strong directional momentum. This phase suggests either accumulation or a pause before another move lower.
Market Awaits Breakout Confirmation
Another market perspective shared by Jonathan Carter points to a potential breakout from a descending channel pattern. According to his analysis, bullish pressure has been gradually increasing, which may lead to a move above current resistance levels.
Key resistance zones remain at $0.12 to $0.15, followed by higher targets extending toward $0.20. A sustained move above these levels would require stronger volume and consistent demand. Without that, the broader structure remains weak.
On the downside, the $0.09 level continues to act as immediate support. A breakdown below this range may expose lower targets near $0.07 and potentially $0.05. These levels are viewed as psychological zones where buyers may attempt to re-enter the market.
Additional context from KrissPax shows how current price levels compare historically during easter. Dogecoin trades significantly below its levels from the past two years, including $0.1614 in 2025 and $0.1823 in 2024. This comparison reflects the broader cooling phase following earlier market enthusiasm.
For now, Dogecoin remains in a neutral-to-bearish position. Price stability at support offers some balance, yet the absence of higher highs keeps upside expectations limited. Traders continue to monitor volume and structure for confirmation of the next trend direction.
Crypto World
Tesla Inc. Stock Stumbles After Delivery Miss as Bearish Momentum Tightens Grip

TLDR:
- Tesla delivered 358,023 vehicles in Q1 2026, missing expectations and adding pressure on stock performance.
- Rising inventory above 50,000 units signals demand concerns amid continued high production levels.
- RSI below 50 and weak MACD confirm bearish momentum with no clear reversal signal yet forming.
- Price remains below key resistance levels, keeping the broader downtrend intact in the near term.
Tesla Inc. shares declined after first-quarter delivery data fell short of expectations, adding pressure to an already weakening chart structure. The latest figures showed rising inventory levels, while analysts adjusted price targets amid ongoing market caution.
Delivery Miss and Analyst Reactions Weigh on Sentiment
A recent tweet from Coin Bureau reported that Tesla delivered 358,023 vehicles in Q1 2026. This figure came in below expectations by 7,600 units. Meanwhile, production reached 408,386 vehicles, leaving inventory elevated by more than 50,000 units.
As a result, sentiment weakened across the market. Goldman Sachs and Truist Financial both reduced their price targets on TSLA. However, they maintained Hold ratings, signaling a cautious stance rather than a fully negative outlook.
The delivery miss added pressure to an already fragile technical setup. Market participants have been closely watching Tesla’s ability to sustain demand levels. The inventory build raised concerns about near-term balance between production and sales.
At the same time, the broader structure of the stock has shifted. Price action no longer reflects the strong momentum seen in late 2025. Instead, it shows a gradual transition into a weaker phase.
Technical Indicators Show Ongoing Downtrend
The daily chart for Tesla reflects a clear directional shift. The stock peaked near the $480–500 range before entering a consistent decline. Since January 2026, the pattern of lower highs and lower lows has remained intact.
Currently trading around $360, the price sits close to recent lows. There is no clear bounce formation, which suggests sellers remain in control. For any structural change, the price would need to break above the $400–420 range.
Momentum indicators also point to weakness. The Relative Strength Index is near 39, staying below the neutral 50 level. This position reflects bearish momentum without entering deeply oversold territory.
Repeated attempts to push above 50 have failed. This pattern indicates limited buying pressure. As a result, downside movement may continue without a strong reversal signal.
The Moving Average Convergence Divergence indicator also supports the trend. Both MACD lines remain below zero, confirming bearish conditions. The histogram has stayed mostly negative, although recent bars show slight flattening.
This flattening suggests selling pressure may be slowing. However, it does not confirm a reversal. A bullish crossover has not yet appeared, leaving the broader trend unchanged.
Key levels remain critical for short-term direction. Support is seen near $350, where recent reactions have occurred. A break below this level could open the path for further declines.
Resistance stands between $380 and $400, marking a recent consolidation zone. A move above this range would be needed to test the larger resistance near $420.
For now, the structure reflects stabilization within a downtrend rather than a confirmed bottom. Price behavior, combined with weak momentum, continues to favor cautious positioning.
Crypto World
Xrp Price Prediction: XRP Hits Record Usage While Price Drops but Pepeto Crosses $8.68M and the Early Wallets Know Why
The XRP Ledger just processed a record 4.49 million transactions in a single day while active addresses topped 200,000 and total wallets crossed 7.7 million, all-time highs for the network. Yet XRP still sits at $1.29, down 30% this year.
That gap between what the chain does and what your portfolio shows makes you question where the actual gains are hiding.
Pepeto finished its exchange build with $8.68 million raised at the fastest clip any meme project has posted in 2026, and the xrp price prediction numbers make clear why capital keeps flowing into this presale instead.
The XRP Ledger hit 4.49 million daily transactions this week, a first in over two years, while total wallets crossed 7.7 million for an all-time high, per CoinMarketCap. The network is busier than ever, but the price has not followed.
XRP ETFs pulled over $1 billion in inflows since launching in November, yet weekly flows have dried up and the token trades 64% below its $3.65 cycle high, per CoinDesk. The institutions bought the utility. The chart has not caught up.
Where the XRP Outlook and the Pepeto Presale Tell Opposite Stories
Pepeto: The Play XRP’s Market Cap Can No Longer Offer
The xrp price prediction conversation keeps holders focused on whether $1.30 holds or cracks, but Pepeto is where the wallets hunting real multiples are placing their money right now, and the tools behind this presale show why.
What would XRP look like if zero-fee trading lived inside the token itself instead of relying on outside partners to set every cost? Pepeto fills that space. PepetoSwap runs every swap at zero cost so your cost stays clean from the start, and the contract scanner reads each token before you commit so the danger shows on your screen instead of in your balance.
Think about holding XRP before the SEC case ended in 2025, when it traded under $0.50 and most people had given up on the case. The wallets that loaded positions during that fear turned modest bets into a 7x within five months, and every holder who caught that wave says the same thing: they nearly missed it and they wish they had gone bigger.
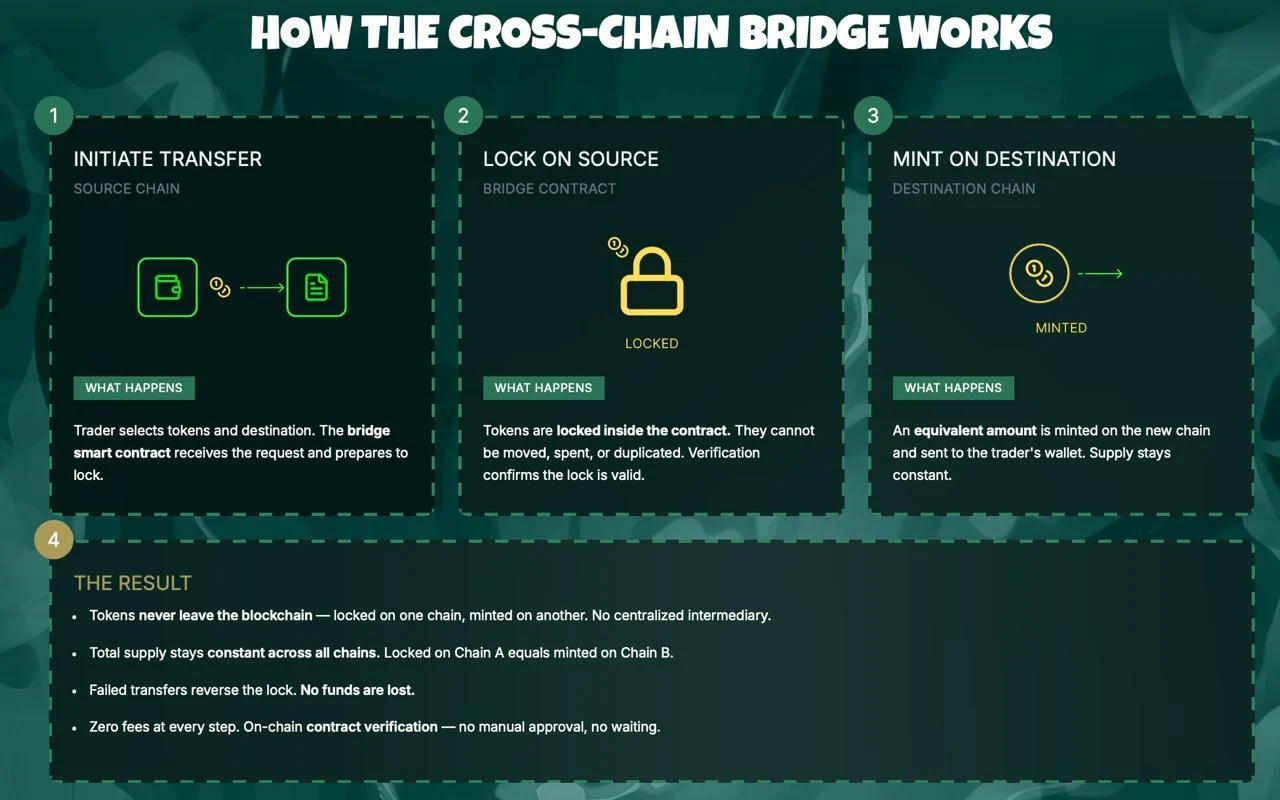
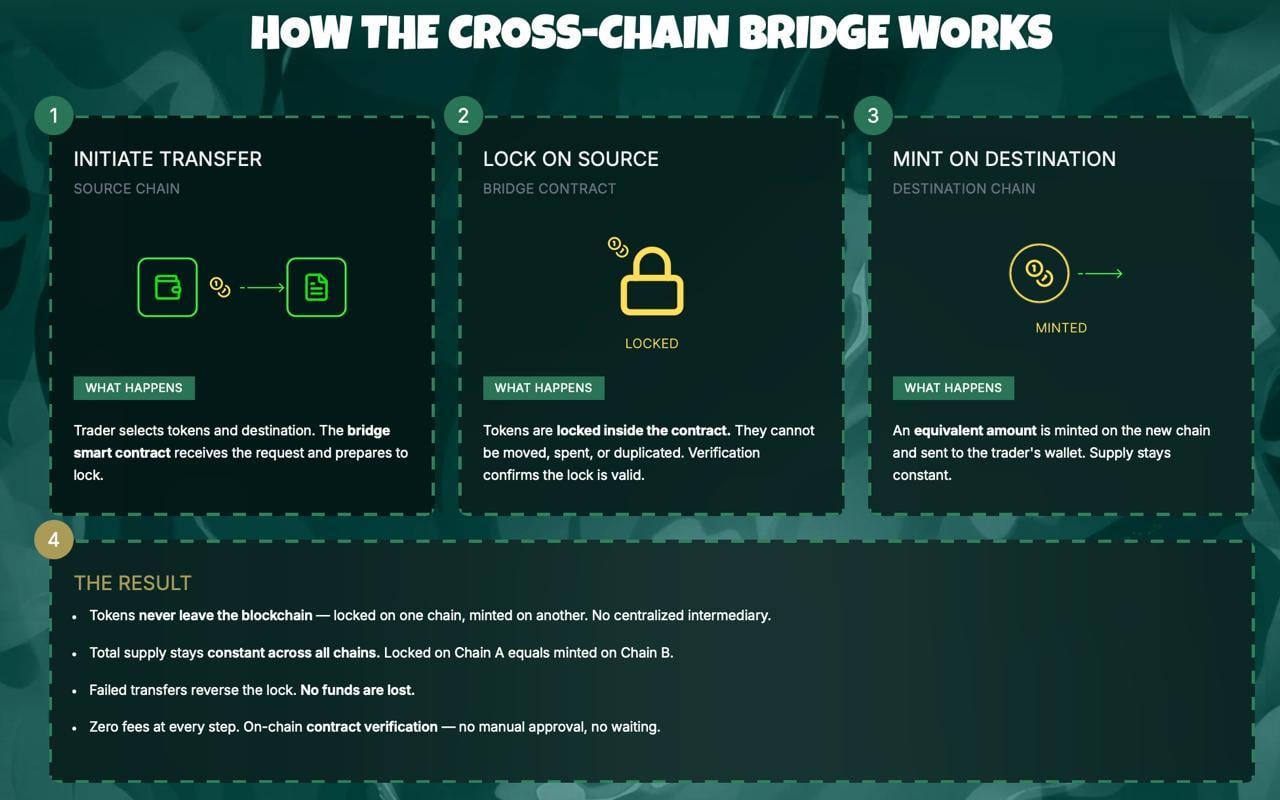
Pepeto sits in that same type of window today. More than $8.68 million raised at $0.0000001862 during a Fear Index of 9, built by the founder behind the original Pepe token together with a former Binance executive who designed the platform, and verified clean by SolidProof before a single dollar came in. Staking at 188% APY adds to positions while the listing gets closer. The cross-chain bridge moves tokens between ETH, BNB, and Solana at zero gas.
The presale entries that created millionaires in past cycles all shared one pattern: a working product, extreme fear, and a crowd too scared to move, and Pepeto checks every box at $0.0000001862 before the Binance listing shuts the window.
Xrp Price Prediction: Where Does XRP Go From $1.29?
XRP trades at $1.29 on April 5, down 64% from its $3.65 cycle high despite record network usage, according to CoinMarketCap.
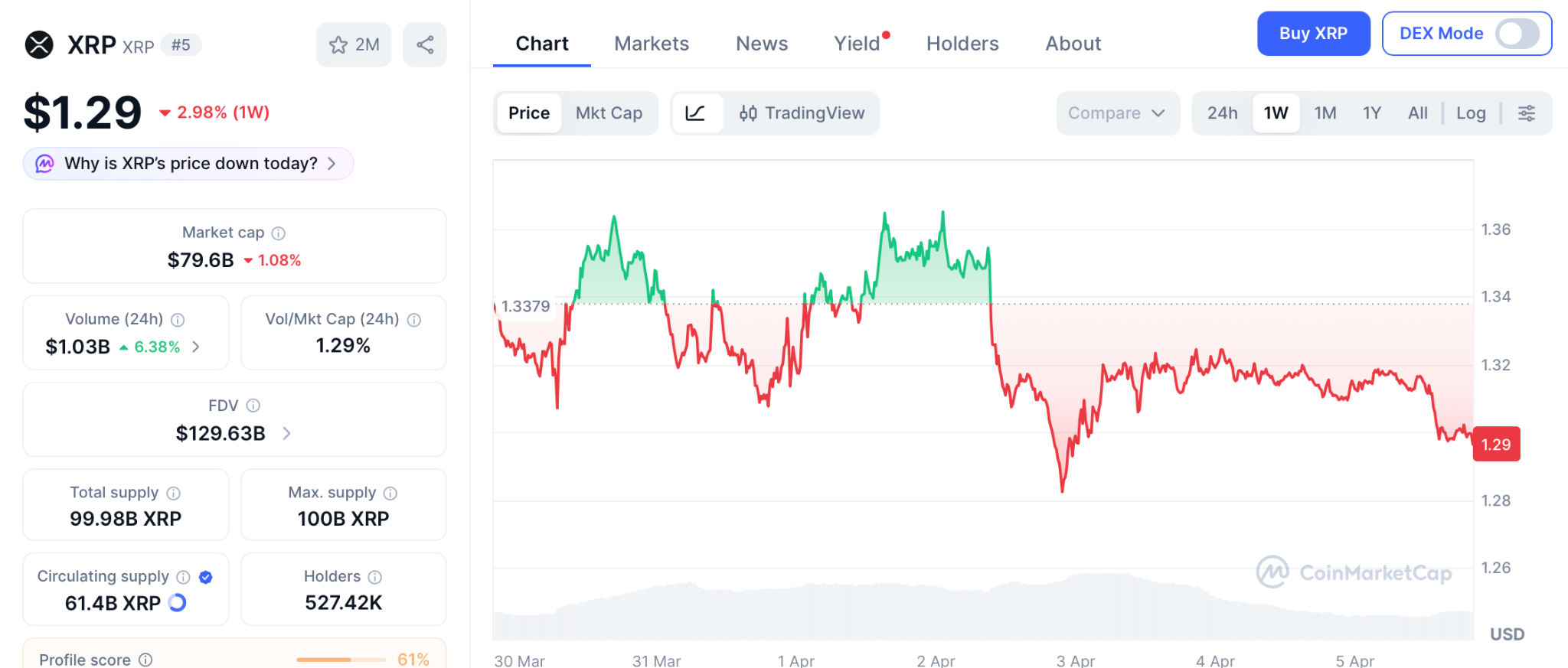
Standard Chartered holds a $2.80 target under current conditions, with the number jumping to $8 if the CLARITY Act clears the Senate after April 13. Support at $1.30 has held every test, and the 50-day moving average at $1.42 acts as the first ceiling. Above that opens $1.60 and then $2.80.
The xrp price prediction math from an $81 billion cap means even a 3x needs the kind of fresh capital that arrives over quarters, and that cap is why wallets keep moving into presale plays where a single listing produces what XRP needs a full year to reach.
Conclusion
Record network activity and falling prices both confirm the same truth: an $81 billion token where every bounce meets selling will not produce returns that reshape your future, and Pepeto is where that math still works.
The XRP holders who loaded below $0.50 before the SEC ruling all say the same thing: they nearly skipped it and wish they had gone all in. That same signal now points toward Pepeto with $8.68 million committed during a Fear Index of 9 and a Binance listing confirmed.
The Pepeto official website still shows presale pricing, and entering while fear keeps others frozen is how those early XRP wallets built everything they have. Missing this entry could be the one call you carry for the rest of this cycle.
Click To Visit Pepeto Website To Enter The Presale
FAQs
What xrp price prediction levels matter with record network activity?
Support holds at $1.30, resistance at $1.42 and $1.60 above. Pepeto’s presale with Binance listing targets 100x at Pepeto.
Can XRP match the returns Pepeto presale holders target?
XRP needs years for a 3x from its $81 billion cap. Pepeto targets those multiples from a single listing event.
Is now the right time to enter while the xrp price prediction stays bearish?
$8.68 million raised during extreme fear proves smart money already moved. Presale stages fill faster each week before the Binance listing.
Disclaimer: This is a Press Release provided by a third party who is responsible for the content. Please conduct your own research before taking any action based on the content.
Crypto World
Pump.fun $350 Million PUMP Buybacks Fail To Lift Token Price
Pump.fun (PUMP) has spent $350 million buying back its own token since July 2025, yet the price sits 81% below its September all-time high and recently hit record lows.
The Solana-based meme coin launchpad now faces growing community backlash over what critics call a tokenomics structure designed for extraction rather than growth.
Why $350 Million in Buybacks Haven’t Moved the Needle
Pump.fun’s official dashboard confirms cumulative purchases of $350 million in PUMP, removing roughly 116 billion tokens from circulation.
That equals about 32.9% of the circulating supply. The protocol directs nearly all daily revenue toward repurchases, averaging around $1 million per day.
Despite this aggressive strategy, PUMP trades near $0.00165, well below its $0.004 ICO price and far from its $0.0088 peak.

Users argue that insiders hold roughly half the supply and sell into each buyback for exit liquidity.
“They own 50% of the $PUMP supply they could have easily sold into every buyback as exit liquidity… Probably one of the worst tokenomic structures in the industry,” wrote 0xSweep.
Supply Pressure and the July Cliff
Only 59% of the one trillion PUMP supply currently circulates. A major unlock scheduled for July 12, 2026, will make 41% of the locked supply tradable. Founders and early investors acquired tokens at negligible cost.
On-chain data from March showed a team-linked wallet transferring 1.75 billion PUMP to Bitget, reinforcing sell-off concerns.
Meanwhile, cumulative protocol revenue has surpassed $1 billion according to DefiLlama, yet none of it has translated into sustained token appreciation.
Whether the buyback program represents genuine value return or a liquidity exit ramp for insiders will depend on what happens when those locked tokens hit the open market this summer.
The post Pump.fun $350 Million PUMP Buybacks Fail To Lift Token Price appeared first on BeInCrypto.
Crypto World
Aave V4 Explained: How Hubs, Spokes, and Credit Lines Redefine DeFi Liquidity Management

TLDR:
- Aave V4 uses immutable Liquidity Hubs to hold assets and track supplied and borrowed balances across markets.
- Spokes handle all user-facing functions like supplying and borrowing, and can be upgraded without changing Hub code.
- Credit lines connect each Spoke to a Hub on a per-asset basis, with draw caps enforced on every transaction.
- Governance controls liquidity access by adjusting draw caps per asset, giving the Aave DAO precise risk management tools.
Aave V4 brings a restructured liquidity model built around three core components: Hubs, Spokes, and credit lines. Understanding how these three parts connect explains how liquidity moves across the protocol.
It also shows how risk is managed across different markets. This architecture marks a clear shift from previous Aave versions.
For anyone following DeFi closely, the design choices behind V4 reflect a more deliberate approach to building modular, upgradeable lending infrastructure.
What Liquidity Hubs and Spokes Are Designed to Do
A Liquidity Hub in Aave V4 is a smart contract that holds deposited assets. When a user supplies USDC, those tokens are stored directly inside a Hub.
Each Hub tracks how much of every asset has been supplied and how much has been borrowed across all connected markets.
As crypto researcher @0xKolten explained, Hubs are intentionally immutable, meaning their underlying code cannot be modified after deployment.
This keeps the liquidity layer stable over time, reducing the risk of bugs introduced through upgrades. New assets can still be registered through governance, since adding an asset is treated as a state change, not a code change.
A single blockchain network can support multiple Hubs, each running its own independent balance sheet. The current Ethereum deployment launched with three: Core Hub, Prime Hub, and Plus Hub. None of these Hubs share accounting with one another.
Spokes are the contracts users interact with directly. Supplying, borrowing, repaying, and withdrawing all happen through a Spoke.
Each Spoke carries its own market logic, including collateral factors, price feeds, and liquidation rules. Because Spokes are upgradeable, governance can adjust risk parameters without affecting the Hub layer.
How Credit Lines Tie the Entire System Together
Every connection between a Spoke and a Hub is a credit line, and each one is defined per asset. A Spoke borrowing USDC from a Hub and that same Spoke borrowing USDT from the same Hub are two entirely separate credit lines. Each carries its own draw cap, which the Hub enforces before any transaction is processed.
The draw cap works similarly to a borrow cap in Aave V3. Governance can raise it to open more access or lower it to reduce the Spoke’s exposure. Setting a cap to zero stops new borrowing entirely while keeping all existing positions intact.
A Spoke can hold credit lines to more than one Hub simultaneously. The Bluechip Spoke on Prime Hub demonstrates this.
Users supply WETH, wstETH, WBTC, and cbBTC as collateral into Prime Hub, while that same Spoke holds separate credit lines to Core Hub for stablecoins like USDC, USDT, and EURC.
When a borrower draws stablecoins through the Bluechip Spoke, the liquidity comes from Core Hub up to each asset’s authorized cap.
The tokens received are the actual underlying assets, not synthetic versions. This structure gives Aave governance a direct, asset-level tool to control how much of any Hub’s liquidity a Spoke can access at any given time.
Crypto World
Polymarket puts US-Iran invasion odds at 63% after Trump post

The odds of a potential U.S. invasion of Iran spiked on the Polymarket prediction market to 63% on Sunday, driven by recent remarks from President Donald Trump and ongoing regional tensions. Polymarket data show the odds rising to this level as volume on the contract reached roughly $3.74 million at the time of publication. The market had previously touched a high near 68% on March 29, a level that reflected elevated risk in the region amid a U.S. troop buildup and chatter about potential moves against Kharg Island, a key Iranian oil shipping hub.
Markets also reacted to political signals in the shorter term. On Tuesday, after Trump suggested the U.S. might withdraw from Iran within two to three weeks, Bitcoin climbed about 2.6% and the S&P 500 index gained around 2.9%. Yet the latest tweet from Trump on Sunday presented a sharper and more aggressive stance, which some traders and analysts described as a reversal that injected renewed uncertainty into risk assets. Bitcoin, by the time of observation, hovered near the $67,500 area, with price action showing little sustained upside beyond that initial knee-jerk move.
“There will be nothing like it! Open the fuckin’ strait, you crazy bastards, or you’ll be living in hell,”
That was Trump’s late-week post on Truth Social, which the market quickly digested alongside the broader geopolitical backdrop. The exchange between flaring rhetoric and cautious downside risk has left traders trying to parse what comes next for a market that remains highly sensitive to geopolitical headlines and policy signals. Brent crude oil, a closely watched barometer of energy risk and sanction dynamics, remained elevated, closing the week above $109 per barrel as markets prepared to resume trading after the Easter break.
The episode also drew a chorus of commentary from economists and market observers about the risks of escalating conflict. Economist Peter Schiff criticized the tone of the rhetoric, arguing that threatening civilian infrastructure is counterproductive and risks undermining credibility in negotiations. “I wish Trump would stop threatening Iranian civilian infrastructure. It’s a lose-lose for us: backing down hurts his negotiating credibility,” Schiff said, noting that escalation could intensify regional tensions and complicate U.S. relations. Peter McCormack, a Bitcoin-focused podcaster, echoed the sense of alarm, calling the development “wild” in response to the latest exchange.
The broader market backdrop remains fragile as investors weigh the odds of conflict against potential economic backlash, including energy flows and sanctions dynamics. On the price front, Bitcoin’s response to political headlines has become a focal point for risk assets, with traders tracking both reactionary moves and longer-term narrative shifts around crypto as a hedging or speculative instrument in times of geopolitical stress. Data from TradingView indicated BTC’s price hovered around the $67,500 level in the immediate aftermath of the latest developments, signaling a cautious stance rather than a decisive breakout.
Key takeaways
- The Polymarket odds of a U.S. invasion of Iran before 2027 rose to 63% on Sunday, with roughly $3.74 million in volume, reflecting elevated political risk pricing in crypto markets.
- Bitcoin briefly surged about 2.6% in reaction to a possible withdrawal timeline for Iran, while the S&P 500 climbed around 2.9% on the same backdrop before later stabilizing.
- The latest Trump post on Truth Social injected renewed uncertainty, illustrating how mixed signals from political leadership can keep risk assets tethered to headlines rather than fundamentals.
- Oil markets remain tense, with Brent crude trading above $109 per barrel as markets digest the potential for sanctions, supply disruptions, and broader geopolitical spillovers.
- Market commentary from economists and crypto voices underscores the risk: rhetoric can move prices in the near term, but the sustainability of moves depends on policy actions and actual conflict dynamics.
Polymarket, risk pricing and the geopolitical lens
At the heart of the episode is how prediction markets like Polymarket are used as a barometer for risk appetite. The 63% odds figure, while not a forecast of certainty, signals that a non-trivial share of participants assign a meaningful probability to a U.S. military scenario in the coming years. The volume around $3.7 million demonstrates substantial speculative activity tied to a geopolitical event with potentially outsized macro consequences. Historically, such markets can swing in response to rapid-fire news, but they also tend to reflect the evolving balance sheets of risk: the more uncertain the horizon, the higher the premium on hedges and bets that mirror that probability spectrum.
Crucially, the odds move alongside the broader narrative around U.S. policy toward Iran, including troop positioning and statements about potential targets. The March 29 peak around 68% is a reminder that even among risk-averse investors, spikes can occur when the threat of escalation appears tangible. For traders in crypto markets, these predictions are less about a direct exposure to geopolitical conflict and more about the spillover effects on risk sentiment, liquidity, and demand for assets perceived as hedges or risk-on plays depending on the narrative driving headlines.
Markets in motion: crypto, equities and energy under the same stress test
The immediate price response in Bitcoin and equities underscored a familiar pattern: time-sensitive headlines can trigger quick moves in risk assets, followed by a reversion as events unfold or as clarity improves. The Tuesday move—BTC up around 2.6% and the S&P 500 rising roughly 2.9%—illustrates how a potential de-escalation signal can momentarily ease risk concerns. But the subsequent Sunday post, with a more aggressive stance, reintroduced volatility into the system, highlighting the fragility of market positioning in periods of mixed signals.
On the energy front, Brent crude’s endurance above $109 per barrel points to a global energy backdrop that could compound macro risk if the Iran situation intensifies. In a market where oil, sanctions policy, and military postures are intertwining factors, investors are left weighing how any disruption to Iranian oil flows could ripple through inflation expectations, central-bank policy assumptions, and risk asset valuations.
Beyond headlines, observers have underscored a broader narrative: geopolitical risk remains a dominant variable in crypto market discourse. While Bitcoin has shown resilience as a non-sovereign asset with a potential appeal as a hedge in turbulent times, the asset’s price dynamics in relation to conflict-related risk are far from straightforward. The current episode reinforces the need for readers to monitor not just the price channel of BTC, but the evolving policy environment, sanctions posture, and the timing of any real military or diplomatic moves that could alter the market’s risk calculus.
Related reading: Polymarket backlash and market adjustments, and earlier coverage of Trump signals on withdrawal. For readers interested in the energy angle, a look at the Iranian mining sector’s regulatory climate provides additional context to how policy shifts can ripple through both crypto and traditional markets.
As the situation unfolds, investors should watch how the administration frames its next steps and how markets price in both the probability of conflict and the likelihood of de-escalation. The coming days will be telling for whether risk appetite recovers on any signs of restraint or remains subdued on the prospect of renewed tensions.
What remains uncertain is how much of the current price action reflects genuine strategic shifts versus the amplification of narratives on social and prediction markets. Readers should stay tuned to official policy updates, macro data releases, and ongoing market commentary to gauge whether the current episode marks a temporary disturbance or the beginning of a longer, more consequential cycle for crypto, equities, and energy markets.
Crypto World
ETH Futures Volumes Hit Seven Times Spot Trading as Open Interest Nears All-Time High

TLDR:
- ETH open interest has recovered to 6.4 million ETH, approaching the all-time high of 7.8 million ETH set in July 2025.
- Binance controls roughly 36% of the ETH derivatives market, holding 2.3 million ETH in total open interest alone.
- The spot-to-futures ratio on Binance dropped to 0.13, the lowest annual level ever recorded for Ethereum trading activity.
- Heavy leverage across ETH futures markets raises volatility risks, as large position unwinds can trigger rapid liquidation cascades.
ETH futures volumes are running roughly seven times higher than spot trading on Binance. Open interest on Ethereum derivatives has climbed to 6.4 million ETH, approaching the all-time high of 7.8 million ETH set in July 2025.
The spot-to-futures volume ratio has now dropped to 0.13, marking the lowest annual level ever recorded for the asset.
Broader market uncertainty continues to push many investors toward caution, drawing a visible divide between conservative holders and more speculative participants.
Open Interest Nears Previous All-Time High After October Decline
Ethereum’s derivatives market has shown a steady and gradual recovery following a notable dip recorded in October 2024.
Open interest on ETH futures fell as low as 5 million ETH before turning higher once again. Since then, it has climbed steadily back toward levels approaching the prior peak of 7.8 million ETH reached in July 2025.
Crypto analyst Darkfost flagged this trend, noting that speculative traders remain unusually active despite broader market uncertainty.
His observations point to a growing divergence between more cautious mainstream investors and those drawn to derivatives. That divide is becoming clearer as open interest continues to build.
Binance remains the dominant force within the ETH derivatives market. The exchange currently holds 2.3 million ETH in open interest, representing around 36% of the total market share.
That concentration gives Binance considerable influence over Ethereum’s price movements on any given trading day.
Such dominance from a single platform also adds a layer of risk to the overall market structure. Any sharp shift in activity on Binance could quickly spread to the broader Ethereum ecosystem. Analysts and traders tracking ETH futures flows should, therefore, watch Binance’s figures closely.
Record Low Spot-to-Futures Ratio Reflects Heavy Leverage Across ETH Market
The spot-to-futures volume ratio on Binance has reached its lowest annual level ever recorded for ETH. At 0.13, this means that for every $1 traded on the spot market, roughly $7 moves through futures contracts. This figure illustrates the extent to which derivatives now dominate ETH trading activity entirely.
As Darkfost noted, this pattern suggests that speculation is currently the primary driver behind Ethereum’s price action.
When futures volume outpaces spot by this margin, price movements are more likely to reflect trader positioning than actual demand. That makes market direction more difficult to interpret with confidence.
Heavy reliance on leverage also makes the broader market more vulnerable to sudden swings. When large leveraged positions begin to unwind, a chain of liquidations can follow quickly. These events tend to sharpen volatility in both directions and within a short time frame.
For those actively participating in the ETH market, this setup warrants careful attention to risk management. Monitoring open interest levels and funding rates alongside price action can help traders gauge how stretched positions have become.
Markets driven primarily by futures activity tend to shift direction more sharply and suddenly than those grounded in steady spot demand.
-

 NewsBeat3 days ago
NewsBeat3 days agoSteven Gerrard disagrees with Gary Neville over ‘shock’ Chelsea and Arsenal claim | Football
-

 Business3 days ago
Business3 days agoNo Jackpot Winner and $194 Million Prize Rolls Over
-

 Fashion2 days ago
Fashion2 days agoWeekend Open Thread: Spanx – Corporette.com
-
Entertainment6 days ago
Fans slam 'heartbreaking' Barbie Dream Fest convention debacle with 'cardboard cutout' experience
-

 Crypto World4 days ago
Crypto World4 days agoGold Price Prediction: Worst Month in 17 Years fo Save Haven Rock
-

 Tech7 days ago
Tech7 days agoThe Pixel 10a doesn’t have a camera bump, and it’s great
-

 Tech7 days ago
Tech7 days agoAvatar Legends: The Fighting Game comes out in July and it looks pretty slick
-
Crypto World5 days ago
Dems press CFTC, ethics board on prediction-market insider trades
-

 Sports1 day ago
Sports1 day agoIndia men’s 4x400m and mixed 4x100m relay teams register big progress | Other Sports News
-

 Business4 days ago
Business4 days agoLogin and Checkout Issues Spark Merchant Frustration
-

 Tech6 days ago
Tech6 days agoApple will hide your email address from apps and websites, but not cops
-

 Tech6 days ago
Tech6 days agoEE TV is using AI to help you find something to watch
-

 Sports5 days ago
Sports5 days agoTallest college basketball player ever, standing at 7-foot-9, entering transfer portal
-

 Politics6 days ago
Politics6 days agoShould Trump Be Scared Strait?
-

 Tech6 days ago
Tech6 days agoFlipsnack and the shift toward motion-first business content with living visuals
-
Tech6 days ago
Daily Deal: StackSkills Premium Annual Pass
-

 Fashion6 days ago
Fashion6 days agoThe Best Spring Trends of 2026
-

 Sports6 days ago
Sports6 days agoWomen’s hockey camp eyes fitness boost, tactics ahead of WC 2026 campaign | Other Sports News
-

 Crypto World6 days ago
Crypto World6 days agoU.S. rule change may open trillions in 401(k) funds to crypto
-

 Tech6 days ago
Tech6 days agoHow to back up your iPhone & iPad to your Mac before something goes wrong














You must be logged in to post a comment Login