Crypto World
Cross-Chain Governance Attacks – Smart Liquidity Research

The Governance Exploit Nobody Is Pricing In. Bridges get hacked. That’s old news. We’ve seen the carnage: nine-figure exploits, drained liquidity, emergency shutdowns, Twitter threads filled with “funds are safu” copium.
From Ronin Network to Wormhole, bridge exploits have become a recurring tax on innovation. But here’s the uncomfortable truth. The next systemic risk in crypto probably won’t be a bridge exploit. It’ll be a governance exploit enabled by cross-chain voting power. And almost nobody is pricing it in.
The Shift: From Asset Bridges to Power Bridges
Cross-chain infrastructure has evolved.
We’re no longer just bridging tokens for yield. We’re bridging:
Protocols increasingly allow governance tokens to exist on multiple chains simultaneously — often via wrapped representations or omnichain token standards (like those enabled by LayerZero Labs).
This improves capital efficiency and participation.
But it also introduces a new attack surface:
The separation of voting power from finality.
The Core Problem: Governance Is Local. Voting Power Is Not.
Governance contracts typically live on a single “home” chain.
But voting power can be represented across multiple chains.
This creates a dangerous gap:
-
Tokens are locked on Chain A
-
Voting power is mirrored on Chain B
-
Governance decisions are executed on Chain A
If the system relies on cross-chain messaging to sync voting balances, any delay, exploit, or manipulation in that messaging layer becomes a governance vector.
You don’t need to drain liquidity.
You just need to distort voting power long enough.
And governance proposals often pass with shockingly low turnout.
The Attack Path Nobody Talks About
Let’s walk through a hypothetical.
Step 1: Acquire or Manipulate Voting Power Cross-Chain
An attacker:
-
Borrows governance tokens
-
Bridges them to a secondary chain
-
Exploits a delay in balance updates
-
Or abuses inconsistencies in wrapped token accounting
In poorly designed systems, the same underlying tokens may temporarily influence voting in multiple domains.
Even if briefly.
Even if “just a bug.”
Governance doesn’t need hours. It needs one block.
Step 2: Flash Governance
We’ve already seen governance flash-loan exploits in DeFi.
The most infamous example? The attack on Beanstalk in 2022.
The attacker used flash loans to acquire massive voting power, passed a malicious proposal, and drained ~$182M.
Now imagine that dynamic — but across chains.
Flash-loaned tokens → bridged representation → governance vote → malicious proposal executed → unwind.
All before the watchers even understand what happened.
Step 3: Proposal Payloads as Weapons
Governance proposals can:
If cross-chain voting power is compromised, the proposal payload becomes the exploit.
No bridge drain required.
Just governance “working as designed.”
Why Markets Aren’t Pricing This Risk
Three reasons.
1. Everyone Is Still Fighting the Last War
After major bridge hacks, teams hardened signature validation and multisig thresholds.
But governance-layer risk is subtler.
It doesn’t show up as “TVL at risk” on dashboards.
It shows up as “who controls protocol direction.”
That’s harder to quantify.
2. Voting Participation Is Low
Many DAOs struggle to get 10–20% participation.
Which means:
You don’t need 51%.
You need slightly more than apathy.
Cross-chain voting power distortions don’t need to be massive. They just need to be decisive.
3. Composability Multiplies Complexity
Modern governance stacks combine:
-
Delegation contracts
-
Token wrappers
-
Cross-chain messaging
-
Snapshot systems
-
Execution timelocks
Each layer introduces potential inconsistencies.
And composability means failures cascade.
Where the Real Risk Lives
This isn’t about one protocol.
It’s systemic.
The more governance tokens become:
The more fragile governance assumptions become.
If a governance token is:
You’ve built a multi-dimensional voting derivative.
And derivatives break under stress.
Ask TradFi. They have scars.
The Governance Exploit Nobody Is Pricing In
Markets price:
-
Smart contract risk
-
Bridge exploit risk
-
Oracle manipulation risk
But they do not price:
Cross-domain voting synchronization risk.
No dashboards are tracking:
-
Governance message latency
-
Cross-chain vote desync windows
-
Wrapped-token vote inflation
-
Double-counted delegation
Yet these variables may determine who controls billion-dollar treasuries.
What Builders Should Be Doing (Now)
If you’re designing cross-chain governance:
1. Separate Voting Power from Bridged Liquidity
Avoid naïve 1:1 mirroring without strict finality checks.
2. Introduce Vote Finality Windows
Require:
-
Cross-chain state verification
-
Message settlement delays
-
Proof-of-lock confirmations
Before votes are counted.
3. Use Decay or Cooldowns on Newly Bridged Tokens
Voting power shouldn’t activate instantly after bridging.
If tokens just moved chains 5 seconds ago, maybe they shouldn’t decide protocol destiny.
4. Simulate Governance Stress Scenarios
Run adversarial simulations:
If your governance model breaks under simulation, it will break in production.
What Investors Should Be Asking
Before allocating to a multi-chain DAO:
-
Where does governance live?
-
How is voting power mirrored?
-
Can voting power be double-counted during bridge latency?
-
What happens if the messaging layer stalls?
-
Is there a time lock between the vote and execution?
If the answers are vague, the risk is real.
And it’s not priced in.
The Inevitable Wake-Up Call
Crypto learns through catastrophe.
-
Smart contract exploits → audits became standard.
-
Oracle exploits → TWAP and redundancy
-
Bridge hacks → validator hardening
Governance-layer cross-chain exploits are likely next.
And when it happens, it won’t look like a hack.
It’ll look like a proposal that “passed.”
That’s the scary part.
Final Thought
Cross-chain infrastructure is powerful. It enables capital mobility, global participation, and modular design.
But it also decouples authority from location.
And when authority becomes fluid across chains, attackers don’t need to steal funds.
They just need to win a vote.
That’s the governance exploit nobody is pricing in.
And by the time the market does, it’ll already be too late.
REQUEST AN ARTICLE
Crypto World
Anchorage Digital Buys Strategy STRC as Stock Becomes Most-Shorted
Crypto bank Anchorage Digital said it now holds Strategy’s perpetual preferred security STRC on its balance sheet, adding an institutional backer to Michael Saylor’s Bitcoin treasury company at a time when Wall Street traders are increasingly betting against it.
In a Wednesday post on X, Anchorage co-founder and CEO Nathan McCauley said the purchase shows alignment between two companies built around Bitcoin (BTC) infrastructure and corporate treasury adoption. “Conviction compounds. Institutions don’t just talk about Bitcoin, they structure around it,” McCauley wrote.
“When the company that operationalizes Bitcoin infrastructure puts capital alongside the company that operationalized the Bitcoin treasury strategy…that’s a signal,” he added. Anchorage did not reveal the size or timing of the position.
According to Strategy’s website, STRC is a Nasdaq-listed perpetual preferred security marketed as a short-duration, high-yield instrument. The shares pay an 11.25% annual dividend distributed monthly in cash. Capital raised through the instrument has historically financed the firm’s continued Bitcoin accumulation.
Related: Michael Saylor says quantum threat to Bitcoin is more than 10 years away
Strategy becomes Wall Street’s most-shorted stock
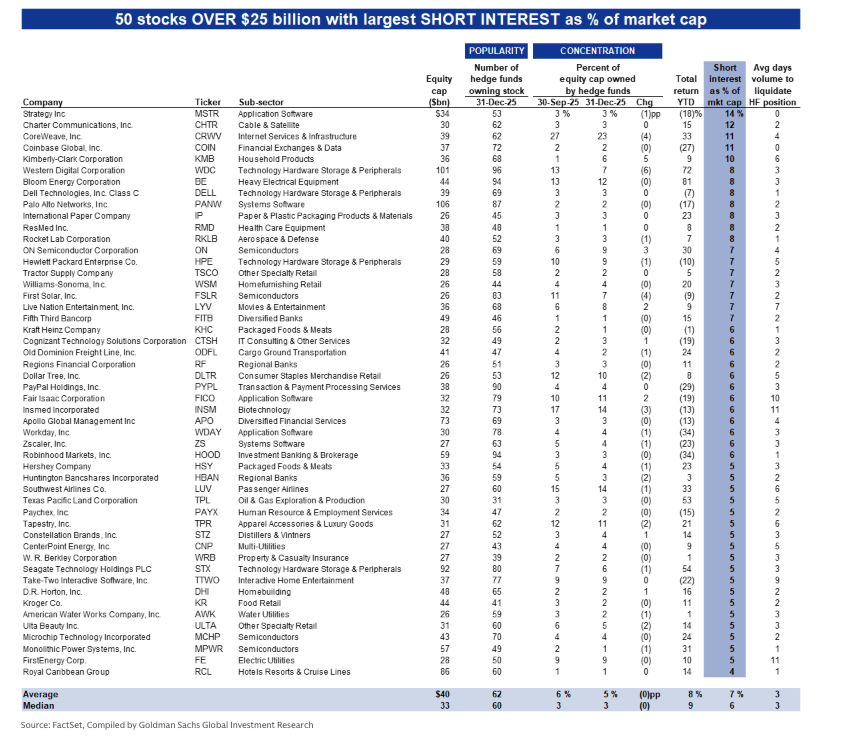
Anchorage’s purchase comes as Strategy has climbed to the top of Goldman Sachs’ list of most-shorted large-cap US equities by short interest as a percentage of market capitalization. A year ago, it did not rank among the top 50. The company began rising on the list in late 2025 as its share price weakened even before Bitcoin peaked in October.

Short selling involves borrowing shares and selling them with the expectation of repurchasing later at a lower price. Losses can grow if the stock rises.
Strategy functions as a leveraged public-equity proxy for Bitcoin. It issues securities and deploys the proceeds into BTC. Gains can amplify during rallies, while downturns magnify pressure on the share price.
The company currently holds 717,722 Bitcoin worth about $46.68 billion at current market prices. On Monday, it announced another purchase, acquiring 592 BTC for $39.8 million. The coins were acquired at an average cost of roughly $76,020, leaving the company sitting on an estimated $7 billion unrealized loss with Bitcoin trading near $66,000.
Related: Michael Saylor hints at Strategy’s 100th Bitcoin buy
Strategy plans debt-to-equity shift
Last week, Strategy founder Michael Saylor said the company intends to convert roughly $6 billion in convertible bond debt into equity, replacing repayment obligations with newly issued shares. The change would lower leverage on the balance sheet by turning bondholders into shareholders, though it could dilute existing investors.
The firm added that its Bitcoin treasury would still cover its liabilities even in an extreme downturn. According to the company, Bitcoin would need to fall close to $8,000, an estimated 88% drop, before its holdings and debt reached parity.
Magazine: Bitcoin may take 7 years to upgrade to post-quantum — BIP-360 co-author
Crypto World
Solana (SOL) Jumps 7% Daily, Bitcoin (BTC) Rebounds to $65K: Market Watch

KITE has entered the top 100 alts after a massive 20% surge daily, and a 135% pump monthly.
After a few consecutive days of charting new local lows to $62,500, bitcoin’s price has finally rebounded, and the asset even neared $66,500 earlier today, where it was stopped.
Most altcoins are in the green as well today, with ETH nearing $1,900, and XRP reclaiming the $1.36 support. SOL and XMR have surged the most from the larger caps.
BTC Bounces to $65K
Bitcoin was violently rejected on both occasions at the beginning of the previous business week to reclaim the $70,000 level, and the subsequent corrections pushed it south to $66,000 by Wednesday. It rebounded in the following days and went above $68,000 during the weekend.
However, more macro uncertainty ensued after the latest tariff developments, including another global taxation of 10% to 15% from Trump. BTC remained still at first, but nosedived on Sunday evening/Monday morning when the futures markets opened. In just over an hour, the cryptocurrency plummeted to under $64,500.
After a dead-cat bounce, the bears were back in control on Tuesday and initiated another leg down – this time, bitcoin slumped to a new three-week low of $62,500. The bulls finally woke up at this point and drove the asset north by roughly $4,000. It was stopped there and now sits above $65,000, but it’s still 3% up on the day.
Its market cap has reclaimed the $1.3 trillion level, while its dominance over the alts has climbed above 56%.
Alts Try to Rebound
Most altcoins were hit hard over the past few days as well. Ethereum dipped to $1,800, but now stands $100 higher at $1,900. XRP is back at a crucial support at $1.36, while BNB has neared $600. TRX, DOGE, BCH, ADA, and HYPE are also in the green daily.
SOL and XMR have surged the most from the larger caps. 7% gains have pushed the former to $82, while the latter is above $335.
KITE has entered the top 100 alts with a massive 20% daily surge. MORPHO follows suit, while LEO and WLFI are next.
The total crypto market cap has recovered around $80 billion daily and is up to $2.330 trillion on CG.
Binance Free $600 (CryptoPotato Exclusive): Use this link to register a new account and receive $600 exclusive welcome offer on Binance (full details).
LIMITED OFFER for CryptoPotato readers at Bybit: Use this link to register and open a $500 FREE position on any coin!
Disclaimer: Information found on CryptoPotato is those of writers quoted. It does not represent the opinions of CryptoPotato on whether to buy, sell, or hold any investments. You are advised to conduct your own research before making any investment decisions. Use provided information at your own risk. See Disclaimer for more information.
Crypto World
Trump makes little mention of China in the longest State of the Union speech

U.S. President Donald Trump shakes hands with members of Congress as he departs following his State of the Union address in the House Chamber of the US Capitol in Washington, DC, on Feb. 24, 2026.
Andrew Caballero-Reynolds | AFP | Getty Images
BEIJING — U.S. President Donald Trump avoided directly naming China in his State of the Union address Tuesday, just weeks before his scheduled trip to Beijing.
In what was the longest State of the Union (SOTU) speech by any U.S. president, Trump covered a range of topics from inflation and tariffs to stock market records.
But notably, he did not directly mention China, other than a reference to “Russian and Chinese military technology” that guarded Venezuelan President Nicolas Maduro during the operation that led to the capture of the foreign leader.
During Trump’s first term from 2017 to 2021, he made direct references to the Chinese nation in all three of his State of the Union addresses. The remarks had largely highlighted the threat from Beijing to the U.S.
“Trump doesn’t want to pick a fight with China in an election year,” said Gabriel Wildau, managing director, Teneo, referring to the coming U.S. midterm elections in November.
“Stability in U.S.-China relations is a priority for the president at least this year and potentially for the rest of his term,” Wildau said.
In order to maintain that relationship, Trump plans to visit Beijing from March 31 to April 2, the first trip by a U.S. president since 2017.
But China’s foreign ministry has yet to confirm exact dates for the visit, pointed out George Chen, partner at The Asia Group. “That makes Trump look more desperate to visit China more than how much [Chinese president Xi Jinping] wants to host him.”
“The lack of mentions about China in Trump’s speech is another example to show how Trump stays cautious now about U.S.-China relations,” Chen said.

China and the U.S. ratcheted up tariffs on each others’ goods last spring to well over 100%, before reaching a trade truce in October to bring tariffs below 50% for the next year. Beijing also tightened its restrictions on rare earths exports worldwide. The Asian country dominates the global supply chain for rare earths, critical minerals used in a swath of technologies.
“The state of the union showed Trump thinks glorifying U.S. military triumphs over weak states like Venezuela makes better election year politics than fighting with China over rare earths,” Wildau said.
Uncertainty around tariffs picked up over the weekend after the U.S. Supreme Court last week struck down tariffs that Trump had imposed on a swath of countries last year. Trump then quickly pointed to an alternative basis for raising the global tariff rate.
In social media posts on Weibo, two Chinese state media outlets highlighted opposition within Congress to Trump’s speech. Local attention in China to Trump’s address was otherwise muted.
Trump’s limited mention of China also reflects how unpredictable his policy on Beijing can be, said Yue Su, principal economist at the Economist Intelligence Unit (EIU).
“By contrast, [Democrat U.S. President Joe] Biden consistently referred to China in his speeches, which underscored a degree of continuity and predictability in his China policy,” she said, referring to Trump’s predecessor.
The Democratic Party’s rebuttal to Trump’s State of the Union Tuesday focused directly on Beijing.
“But as the president spoke of his perceived successes tonight, he continues to cede economic power and technological strength to Russia, bow down to China, bow down to a Russian dictator and make plans for war with Iran,” said Virginia Governor Abigail Spanberger, who gave the rebuttal.
A big deal coming?
For a U.S. president who has called out Xi by name in public speeches, the absence of mentioning the world’s second-largest economy in the SOTU speech marks a strategic move.
If Trump seals a deal during his Beijing trip, “he could easily frame it as a major achievement for his base,” said EIU’s Su. “And if negotiations do not go well, a retaliatory or hardline approach could be presented in a similarly positive light domestically.”
Steven Okun, founder and CEO of Singapore-based APAC Advisors, said that this year, the speech was understandably more focused on topics that impact the midterm elections, which don’t include China.
But he pointed out that if Trump really wanted to address U.S. consumer affordability, lowering tariffs on China would “show up much quicker in people’s pocketbooks.”
“So, we may see a deal on tariffs with China end of March or early April,” Okun said Wednesday on CNBC’s “Access Middle East.”
Many U.S. company executives are expected to accompany Trump on his trip to China in a few weeks. Meetings with Chinese counterparts can be an opportunity to support deals, including Chinese purchases of U.S. agricultural products.
When asked about Trump’s limited discussion of China, Marko Papic, a chief strategist at global investment research firm BCA Research, simply said: “A big deal is coming!”
—CNBC’s Sydney Goh contributed to this report.
Crypto World
$61M in stolen crypto seized in North Carolina fraud crackdown
Federal prosecutors in the Eastern District of North Carolina announced the seizure of more than $61 million worth of Tether (USDT) in one of the largest cryptocurrency asset forfeiture actions tied to a romance-style investment fraud known as a “pig butchering” scheme.
Summary
- Over $61 million in USDT was seized by federal agents in North Carolina, linked to wallets used in a “pig butchering” romance investment scam.
- Homeland Security Investigations traced victims’ stolen funds through a chain of crypto wallets, leading to forfeiture of the remaining balances.
- U.S. authorities, with assistance from Tether, highlighted the operation as part of an ongoing crackdown on cryptocurrency fraud and money-laundering schemes.
North Carolina Feds seize $61M in crypto
The operation shows growing U.S. efforts to trace and reclaim digital assets used in complex fraud and money-laundering networks.
The U.S. Department of Justice said the seized funds were traced to multiple cryptocurrency wallets controlled by criminal actors who lured victims into fraudulent crypto trading platforms after building trust through purported romantic relationships.
Once victims deposited money into these fake platforms, operators allegedly prevented withdrawals or demanded bogus “fees” and “taxes” to extract more funds. Investigators from Homeland Security Investigations in Raleigh, North Carolina, followed the flow of the stolen proceeds through a network of wallets and identified accounts still holding significant balances subject to seizure and forfeiture.
“The seizure of a staggering $61 million … shows that, in the Eastern District of North Carolina, cheaters never win,” said U.S. Attorney Ellis Boyle, highlighting the district’s asset forfeiture team’s work with HSI to disrupt the fraud network.
The DOJ also acknowledged assistance from Tether in facilitating the transfer of the assets once targeted wallets were identified.
Pig butchering scams, a hybrid of romance fraud and investment deception, have become an escalating threat globally, with victims often recruited on social media or dating apps before being directed to professional-looking, yet fake, cryptocurrency investment portals. Once funds are sent, victims find themselves unable to withdraw, leaving law enforcement to trace and recover the proceeds.
The $61 million seizure adds to a broader trend of high-profile crypto forfeitures by U.S. authorities in recent years.
Crypto World
AI, Institutions & the Era of Real Value


As the calendar turned to 2026, the cryptocurrency industry found itself standing on a peculiar threshold. The adrenaline-fueled institutional waves of 2024 and 2025 have receded, leaving behind a landscape that is irrevocably changed. We are no longer in the Wild West of digital finance, but neither have we arrived at a global consensus of stability.
Instead, 2026 presents itself as a year of paradoxes, record-breaking infrastructure growth clashing with geopolitical uncertainty, and the rise of autonomous AI agents trading against a backdrop of traditional regulatory fatigue.
To decipher the complex signals of this new year, BeInCrypto reached out to a roundtable of industry heavyweights who are shaping the ecosystem from the inside. We are privileged to share insights from Fernando Lillo Aranda (Marketing Director at Zoomex), Vivien Lin (Chief Product Officer at BingX), Griffin Ardern (Head of BloFin Research & Options Desk), Dorian Vincileoni (Head of Regional Growth at Kraken), Federico Variola (CEO of Phemex), Mike Williams (Chief Communication Officer at Toobit), and Michael Ivanov (CEO of Arcanum Foundation).
Their consensus? The era of easy money based on hype is over. Welcome to the era of systems, convergence, and rigorous reality checks.
The Pulse of 2026: Mature Growth or Structural Uncertainty?
The opening months of 2026 have felt different. The manic euphoria that characterized previous bull cycles has been replaced by something heavier, more calculated. The question on every investor’s mind is whether we are poised for a breakout year or bracing for a storm.
Fernando Lillo Aranda, Marketing Director at Zoomex, suggests that while the narrative of a 2026 Bull Run was heavily pushed last year, the reality on the ground requires a sharper eye. He points out that the market is no longer driven solely by retail sentiment but by invisible hands, complex institutional strategies that operate beneath the surface.
Lillo Aranda observes:
“There was a strong narrative last year positioning 2026 as the start of a new bull run.
However, those of us who have been in the market for a long time understand that the reality is more nuanced… Overall, the sentiment at the start of 2026 feels like a blend of mature growth and renewed volatility.”
Lillo Aranda notes that while December was typically sluggish, the start of the year has shown constructive patterns. “The market is more structurally robust than in previous cycles, yet still dynamic and opportunity-driven,” he adds, emphasizing that 2026 is a year to “stay engaged and active, there is momentum, liquidity, and volatility to be embraced.”
However, not everyone views the horizon with unblemished optimism. Mike Williams, Chief Communication Officer at Toobit, injects a note of geopolitical realism. In his view, the market cannot be decoupled from the chaotic state of global affairs. Williams warns:
“Uncertainty in the world, politics, and economics will rule the market sentiment and cause big waves that are very unpredictable. It is the time to stay calm and put everything in perspective.”
This tug-of-war between structural robustness (Zoomex) and macro-uncertainty (Toobit) sets the stage for what Griffin Ardern of BloFin describes as the “Matthew Effect”, a biblical reference to the rich getting richer. Ardern argues that we are in a phase of mature growth, but it is a growth that disproportionately benefits the giants.
“The crypto market is already in a mature growth phase, but it may become further dominated by the ‘Matthew effect,’” Ardern explains.
“As mainstream assets like BTC and ETH are more widely accepted by traditional markets, they will have better liquidity and be favoured by both institutional and retail investors.”
Ardern paints a stark picture for altcoins in 2026. With regulatory relaxation, high quality projects are bypassing token launches in favor of listing on US stock markets. This leaves the token market with “higher potential risks and lower appeal,” driving a wedge between the blue chips and the rest of the field.
Beyond Hype: The Narratives That Matter
If 2021 was about NFTs and 2024 was about ETFs, what is the defining story of 2026? The answers from our guests suggest a massive pivot away from speculation and toward functional integration, specifically regarding Artificial Intelligence.
Vivien Lin, Chief Product Officer at BingX, delivers perhaps the most futuristic yet tangible prediction for the year. She believes the narrative has shifted from humans trading crypto to AI using crypto.
“Crypto is moving beyond being a financial experiment into becoming the trust and settlement layer for AI-driven systems,” Lin asserts.
“As AI agents begin to trade, allocate capital, manage risk, and interact with users autonomously, blockchain provides the transparency, auditability, and incentive alignment that AI alone cannot offer.”
For Lin, the killer app of 2026 isn’t a new memecoin, it’s the infrastructure that allows AI to function safely. “In 2026, the most important crypto products will not be about speculation, but about using AI to simplify complexity… The convergence of AI and crypto will define how the next generation of financial and digital services is built.”
Michael Ivanov, CEO of Arcanum Foundation, agrees that AI is central, but he refuses to pin 2026 on a single storyline. He sees a trifecta of innovation driving the sector.
“We don’t see a single narrative this year,” Ivanov says.
“Too much interesting things going out there: AI-integrated blockchains, RWA (Real World Asset) adoption, and new interesting web3 gaming projects coming this year.”
While the tech-focused narratives of AI and Gaming are compelling, Federico Variola, CEO of Phemex, argues that the overarching theme is actually a return to economic sanity. After years of vaporware, 2026 is the year the bills come due, and only profitable protocols will survive.
Variola states firmly:
“We expect a return to fundamentals after a period dominated by hype cycles, memecoins, narratives, and short-term speculation. In 2026, value will accrue to projects showing real revenue, real growth, and sustainable economics.”
This sentiment echoes across the board, the market has grown up. Whether it’s Toobit’s Mike Williams calling for “mass adoption driven by understanding” rather than hype, or Phemex’s call for real revenue,”the message is clear. The era of the whitepaper millionaire is over. The era of the profitable product has begun.
The Heartbeat of the Market: Who is Driving the Price?
For over a decade, retail investors, the degens, the believers, the forum dwellers, were the undisputed kings of crypto. But after the massive institutional inflows of the mid-2020s, has the retail investor become obsolete?
The consensus is “No,” but their role has changed dramatically.
BloFin’s Griffin Ardern offers a critical distinction. While retail is still present, the “Main Street” listing of projects on traditional stock exchanges is draining talent and capital away from the on-chain token economy. This reinforces the dominance of Bitcoin and Ethereum, which are now institutional darlings.
However, Mike Williams from Toobit highlights a geographical divergence. While the United States market has become heavily institutionalized, Europe remains a stronghold for the individual investor.
Williams notes:
“Depends on the markets. In the US definitely (institutions rule), but in Europe, the market consists of more individuals, and institutions are still adopting and adjusting according to all the legislation.”
Michael Ivanov of Arcanum Foundation remains bullish on the retail sector, predicting a resurgence of individual participation in 2026, provided the industry solves its User Experience (UX) problem.
“We see interest from retail investors and this will be a good trend for this year to simplify their path,” Ivanov says.
The implication is that retail hasn’t left; they are waiting for tools that make participation as easy as using a banking app, a sentiment that aligns perfectly with Vivien Lin’s prediction of AI simplifying complexity.
The Survival Guide: Strategic Advice for 2026
Given this landscape, institutional dominance, AI convergence, and lingering geopolitical volatility, how should the savvy investor rebalance their portfolio this January? Our guests offered advice that deviates significantly from the buy low, sell high mantras of the past.
The most profound shift in thinking comes from Kraken’s Dorian Vincileoni, Head of Regional Growth. His advice is to stop looking at tickers and start looking at infrastructure.
“Think in terms of systems, not assets,” Vincileoni advises.
“In a market now dominated by institutional capital, the strongest positions are those aligned with infrastructure that benefits from scale, liquidity and long-term usage.”
Vincileoni challenges investors to ignore the noise of short-term narratives.
“Short-term narratives matter less than exposure to neutral rails that others are forced to use over time. The goal is not to predict every move, but to position yourself where capital, utility and inevitability intersect.”
Griffin Ardern from BloFin takes a more defensive, macro-economic stance. In a world where currencies are increasingly politicized, he advocates for what he calls “rigorous diversification.”
“Due to current geopolitical risks, ‘cross-border assets’ or ‘offshore assets’ unaffected by fiscal or monetary policies… will be favoured,” Ardern says.
He suggests looking beyond crypto and stocks to precious metals, commodities, and even foreign exchange.
“When fiat currencies themselves can be weaponised, holding a basket of fiat currencies (rather than a single fiat currency) becomes more important.”
Michael Ivanov (Arcanum) and Mike Williams (Toobit) both emphasize the psychological aspect of trading in 2026. With the market moving faster than human reaction times, relying on emotion is a death sentence. Ivanov suggests:
“The more diversity you have, the better for your portfolio. Look for new automatic instruments in the crypto investment segment that can make the long play with no emotion.”
Williams echoes this, reminding us that strategy must trump volatility. “Differentiate between long and short term goals… Don’t shift your strategies based on the market movements, but on these.”
Conclusion: The Industrial Age of Crypto
As we look ahead at the remainder of 2026, the insights from Zoomex, BingX, BloFin, Kraken, Phemex, Toobit, and Arcanum paint a cohesive picture. The crypto industry has not just grown, it has evolved into a complex layer of the global financial fabric.
We are entering a period of “Industrial Crypto.” It is a time defined by the Matthew Effect, where the biggest assets solidify their dominance. It is a time where AI agents will likely conduct more transactions than human traders. And it is a time where value is measured not by community hype, but by revenue, utility, and systemic inevitability.
For the investor, the message is clear: the easy games are finished. Success in 2026 requires thinking in systems, diversifying against geopolitical chaos, and embracing the boring reality of fundamental growth. The volatility remains, but the game has changed.
Special thanks to Fernando Lillo Aranda, Vivien Lin, Griffin Ardern, Dorian Vincileoni, Federico Variola, Mike Williams, and Michael Ivanov for their contributions to this report.
Crypto World
Trump’s State of the Union Signals No Relief on Rates, Ignores Crypto


The US President Donald Trump delivered a nearly two-hour State of the Union address on Tuesday — the longest in US history — touting economic gains, warning Iran against pursuing nuclear weapons, and defending his tariff agenda after a Supreme Court setback.
Yet in a speech that touched on taxes, AI, housing, and healthcare, digital assets were entirely absent.
All the Trumps Were There, but Not Crypto
The omission is striking. All of Trump’s children were in attendance, including sons Donald Jr. and Eric, who have been deeply involved in crypto ventures such as World Liberty Financial and various token launches.
The president himself has repeatedly pledged to make the US “the crypto capital of the planet.” None of that made it into the address.
Tariff Chaos and Sticky Inflation Keep the Fed on Hold
For crypto markets, the most consequential signals were macro, not legislative.
Trump called the Supreme Court’s ruling striking down his emergency tariffs “very unfortunate” and vowed to maintain them under alternative legal authorities, insisting “congressional action will not be necessary.”
But the rollout quickly turned chaotic. Trump first announced a 10% replacement rate, then revised it to 15% days later. Yet official documents show the lower rate took effect Tuesday with no directive to raise it. The EU suspended ratification of its summer trade deal on Monday; India deferred scheduled talks.
Trump repeated his claim that tariffs could “substantially replace” income taxes. Economists call this implausible. The federal government collected $2.4 trillion in income taxes in 2024 but took in only about $300 billion from tariffs — and must now refund roughly half of that under the court ruling. Also, US importers pay the tariffs, not foreign governments.
On inflation, Trump claimed core inflation fell to 1.7% in late 2025. The reality is more complicated. The Fed’s preferred gauge — core PCE — accelerated to 3% in December, well above the 2% target.
With inflation sticky and tariff policy unresolved, the Fed is widely expected to hold rates steady for the foreseeable future. The three-quarter-point cuts delivered late last year appear to be the last for some time. For risk assets, including crypto, the higher-rate environment persists.
AI Gets Attention, Crypto Does Not
While crypto went unmentioned, AI earned a dedicated segment. Trump announced a “ratepayer protection pledge” requiring tech companies to build their own power plants for data centers, acknowledging the grid “could never handle” surging demand.
First Lady Melania Trump‘s AI legislation work was also highlighted — a sign that AI policy occupies a far more prominent place in the administration’s agenda than digital asset regulation.
The Bottom Line
Trump’s record-length address was a midterm election pitch built on economic optimism. But for crypto participants, the takeaways are clear: no legislative momentum for digital assets despite the president’s family being neck-deep in the industry, unresolved tariff turmoil injecting macro uncertainty, and a Fed locked in place by sticky inflation. The conditions weighing on risk assets aren’t likely to change anytime soon.
Crypto World
BTC close to a bottom in price, but bulls will have to be patient


Bitcoin is exhibiting textbook bottom formation characteristics across multiple indicators, trading at levels that historically precede significant recoveries, according to onchain analyst James Check. Time — not price — is, however, likely to be the bigger test for bitcoin bulls.
“Every mean reversion model, from technical to onchain, is trading within bottom formation levels, typically seen after the price capitulation event (which December 2018 and June 2022 were examples of),” wrote Check on Tuesday morning as bitcoin plunged through $63,000, seemingly on its way to testing the Feb. 5 panic low of $60,000.
“Either Bitcoin is dead, will no longer mean revert, and all your models are broken,” Check continued. “Or you should be ignoring the bears … and quietly [be] dollar cost averaging [and] stacking sats from here on.”
Check — who correctly urged caution in 2025 about investing in any of BTC treasury companies formed to try and replicate the success of Michael Saylor’s Strategy — acknowledged today that it’s possible or even likely that the price of bitcoin could fall even further from here. Time, though, will be the more important factor. He reminded of the brutal 2022 bear market. Folks remember the price low around $15,600 in December of that year, but bitcoin essentially bottomed six months earlier at about $17,600. The rest was just waiting, and then a final liquidity flush (surrounding the FTX collapse).
“This is literally what a de-risked setup looks like for bitcoin,” concluded Check. “If you’re not actively accumulating bitcoin at this stage, then when?”
Crypto World
Anthropic Accuses Three Firms of Using Sophisticated Distillation Attacks

Artificial intelligence firm Anthropic has accused three AI firms of illicitly using its large language model Claude to improve their own models in a technique known as a “distillation” attack.
In a blog post on Sunday, Anthropic said that it had identified these “attacks” by DeepSeek, Moonshot, and MiniMax, which involve training a less capable model on the outputs of a stronger one.
Anthropic accused the trio of generating “over 16 million exchanges” combined with the firm’s Claude AI across “approximately 24,000 fraudulent accounts.”
“Distillation is a widely used and legitimate training method. For example, frontier AI labs routinely distill their own models to create smaller, cheaper versions for their customers,” Anthropic wrote, adding:
“But distillation can also be used for illicit purposes: competitors can use it to acquire powerful capabilities from other labs in a fraction of the time, and at a fraction of the cost, that it would take to develop them independently.”
Anthropic said that the attacks focused on scraping Claude for a wide range of purposes, including agentic reasoning, coding and data analysis, rubric-based grading tasks, and computer vision.
“Each campaign targeted Claude’s most differentiated capabilities: agentic reasoning, tool use, and coding,” the multi-billion-dollar AI firm said.

Anthropic says it was able to identify the trio via an “IP address correlation, request metadata, infrastructure indicators, and in some cases corroboration from industry partners who observed the same actors and behaviors on their platforms.”
DeepSeek, Moonshot, and Minimax are all AI companies based in China. All three have estimated valuations in the multi-billion dollar range, with DeepSeek being the most widely internationally recognized out of the three.
Beyond the intellectual property implications, Anthropic argued that distillation campaigns from foreign competitors present genuine geopolitical risks.
“Foreign labs that distill American models can then feed these unprotected capabilities into military, intelligence, and surveillance systems—enabling authoritarian governments to deploy frontier AI for offensive cyber operations, disinformation campaigns, and mass surveillance,” the firm said.
Moving forward, Anthropic said it would protect itself by enhancing detection systems to help spot dubious traffic, sharing threat intelligence, and tightening access controls, among other things.
Related: Citrini’s AI doom report sees software, payment stocks tumble
The firm also called for more collaboration from domestic industry participants and lawmakers to help stop foreign AI companies from attacking US firms.
“No company can solve this alone. As we noted above, distillation attacks at this scale require a coordinated response across the AI industry, cloud providers, and policymakers. We are publishing this to make the evidence available to everyone with a stake in the outcome.”
Magazine: Crypto loves Clawdbot/Moltbot, Uber ratings for AI agents: AI Eye
Crypto World
Blockchain Association Pitches Crypto Tax Plan to Congress

The Blockchain Association urged Congress to exempt low-dollar crypto transactions and tax mining and staking rewards upon sale.
A US crypto lobby group has shared with Congress its tax proposals for crypto and has met with House lawmakers working on a crypto tax bill to shape one of the industry’s top policy priorities.
The Blockchain Association released its crypto tax policy positions on Tuesday, which called for stablecoins to be treated as cash for ordinary purchases and for a de minimis tax exemption on “low-dollar” crypto transactions.
It argued that tax reporting for “negligible gains or losses from routine transactions imposes disproportionate costs on individuals and overwhelms tax administration without meaningful revenue upside.”
The group also said it supports extending wash-sale rules to digital assets, which would limit investors’ ability to claim losses if they repurchase the same asset within a specified period.
The Blockchain Association’s efforts come as lawmakers debate how to tax crypto.
Republican Senator Cynthia Lummis introduced a bill in July to tax-exempt some crypto transactions, which was met with opposition from Democratic Senator Elizabeth Warren.

The Blockchain Association argued that tax reporting for digital assets should safeguard taxpayer privacy while still enabling effective enforcement against illicit crypto activities.
It also argued that mining and staking rewards should be treated as self-created property and taxed when sold or otherwise disposed of, rather than when they are received.
Related: Dutch House of Representatives advances controversial 36% tax law
The organization met with White House officials earlier this month to advance market structure legislation that includes favorable stablecoin rewards provisions.
Warren opposes proposed crypto tax laws
Lummis’ crypto tax bill included several provisions that the Blockchain Association advocated for, but that faced strong opposition from Warren in October.
Warren argued that the de minimis exception proposal would cost the US $5.8 billion and slammed a proposal that would allow crypto investors to avoid reporting income from crypto transactions under $300.
“If someone bought $300 worth of gold, or $300 worth of Apple stock, would they be required to report any income they made from those transactions?” she argued.
Magazine: DAT panic dumps 73,000 ETH, India’s crypto tax stays: Asia Express
Crypto World
Bitcoin Rebound To $65K Holds As US Stocks Recover From AI Meltdown

Bitcoin’s (BTC) bleed slowed on Tuesday as US markets recovered from Monday’s AI and software-stocks-driven selloff. At the US market closing bell, the Dow locked in a 370-point gain, while the S&P 500 held on to a 0.77% rally. The swift recovery of US equity markets appears to have played a role in easing negative pressure on crypto investors looking to cut risk asset exposure.
Bitcoin analysts continue to stress the importance of the former $65,000 support being reclaimed and the $60,000 level holding, with many suggesting that a dip below the latter figure would swiftly usher in new lows in the low $50,000 range.
While Bitcoin now trades 49% away from its all-time high, BTC market resource Material Indicators flagged a $4.5 million spot purchase by “mega whales” on Tuesday morning. In the post, Material Indicators noted that while the figure is insignificant, “it’s significantly larger than the typical $1M – $2M market order we see from that order class.”

They added:
“We typically see them do this when they are buying directly into liquidity to help break walls.”
Time for a Bitcoin turnaround?
Currently, few signals point to a reversal of the prolonged bear trend, but analysts are quick to note how deeply oversold Bitcoin is, citing several data points that marked turning points in sentiment and positioning when extreme thresholds were breached.
As reported by Cointelegraph, Bitcoin’s weekly RSI has fallen to 25.71, lows not seen since July, 2022. As shown in the chart below, RSI readings below 28 have previously been a discounted buying opportunity and an early signal that the market is finding a bottom.

Galaxy head of firmwide research Alex Thorn said Bitcoin is “nearing all-time oversold territory,” explaining that the:
“Weekly RSI is lower than any time except the darkest of bears.”
Related: Bitcoin ‘fair value’ gap sets $45K target as AI woes haunt stocks, gold
Bitcoin is also within 9% of its 200-week exponential moving average at $58,855, a level some traders have pointed to as the start of the bottoming process in previous market cycles. Crypto analyst Rekt Capital, on the other hand, painted a less optimistic picture.
According to the analyst, the now confirmed daily close below the 200-EMA “could turn it into resistance on any upcoming recovery.” Rekt Capital suggested that future retests of the moving average would instead “prompt additional bearish acceleration to the downside.”

Even if Bitcoin is on its way to a bottom, the process could take many months. According to Bitcoin analyst Brian Brookshire, “grinding out a bottom” could take time, but some steps in the right direction would be equalization of the BTC supply in the profit-loss metric and “Bitcoin bouncing off mining cost.”
Brookshire also alluded to future US Federal Reserve rate cuts, either by Chairman Jerome Powell or the potential future chair, Kevin Warsh, as having an impact on BTC price.

This article does not contain investment advice or recommendations. Every investment and trading move involves risk, and readers should conduct their own research when making a decision. While we strive to provide accurate and timely information, Cointelegraph does not guarantee the accuracy, completeness, or reliability of any information in this article. This article may contain forward-looking statements that are subject to risks and uncertainties. Cointelegraph will not be liable for any loss or damage arising from your reliance on this information.
-

 Video5 days ago
Video5 days agoXRP News: XRP Just Entered a New Phase (Almost Nobody Noticed)
-

 Fashion5 days ago
Fashion5 days agoWeekend Open Thread: Boden – Corporette.com
-
 Politics3 days ago
Politics3 days agoBaftas 2026: Awards Nominations, Presenters And Performers
-

 Entertainment7 days ago
Entertainment7 days agoKunal Nayyar’s Secret Acts Of Kindness Sparks Online Discussion
-

 Sports2 days ago
Sports2 days agoWomen’s college basketball rankings: Iowa reenters top 10, Auriemma makes history
-

 Politics2 days ago
Politics2 days agoNick Reiner Enters Plea In Deaths Of Parents Rob And Michele
-

 Sports6 days ago
Sports6 days agoClearing the boundary, crossing into history: J&K end 67-year wait, enter maiden Ranji Trophy final | Cricket News
-

 Business3 days ago
Business3 days agoMattel’s American Girl brand turns 40, dolls enter a new era
-

 Crypto World1 day ago
Crypto World1 day agoXRP price enters “dead zone” as Binance leverage hits lows
-

 Business3 days ago
Business3 days agoLaw enforcement kills armed man seeking to enter Trump’s Mar-a-Lago resort, officials say
-

 Entertainment6 days ago
Entertainment6 days agoDolores Catania Blasts Rob Rausch For Turning On ‘Housewives’ On ‘Traitors’
-

 Tech3 days ago
Tech3 days agoAnthropic-Backed Group Enters NY-12 AI PAC Fight
-

 NewsBeat2 days ago
NewsBeat2 days ago‘Hourly’ method from gastroenterologist ‘helps reduce air travel bloating’
-

 NewsBeat3 days ago
NewsBeat3 days agoArmed man killed after entering secure perimeter of Mar-a-Lago, Secret Service says
-

 Politics3 days ago
Politics3 days agoMaine has a long track record of electing moderates. Enter Graham Platner.
-
 Crypto World7 days ago
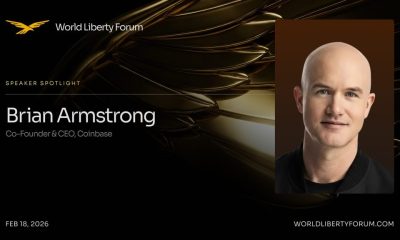
Crypto World7 days agoWLFI Crypto Surges Toward $0.12 as Whale Buys $2.75M Before Trump-Linked Forum
-

 Tech15 hours ago
Tech15 hours agoUnsurprisingly, Apple's board gets what it wants in 2026 shareholder meeting
-

 NewsBeat11 hours ago
NewsBeat11 hours agoPolice latest as search for missing woman enters day nine
-

 Crypto World5 days ago
Crypto World5 days ago83% of Altcoins Enter Bear Trend as Liquidity Crunch Tightens Grip on Crypto Market
-
Sports2 days ago
2026 NFL mock draft: WRs fly off the board in first round entering combine week











