Crypto World
Dmail to shut down its decentralized email service on May 15

Decentralized email platform Dmail Network has announced it will shut down after five years of operation, citing escalating infrastructure costs, weak monetization, failed fundraising efforts, and limited token utility. The company said it will gradually cease all services starting May 15, and urged users to export their data before then, as all nodes will be shut down afterward, rendering emails and accounts inaccessible.
Positioning itself as a Web3 communication tool built around wallet-based email, encrypted messaging, and on-chain notifications, Dmail had aimed to demonstrate that decentralized infrastructure could scale with user demand. In January 2025, Dmail’s profile among AI DApps surged; DappRadar ranked the project second in that category for the month, reporting 4.9 million unique active wallets. Despite the early momentum, Dmail’s founders say expanding operational costs outpaced monetization and investment, ultimately undermining the project’s sustainability.
Key takeaways
- In its shutdown notice, Dmail Network says it will begin winding down services on May 15, with all nodes going offline thereafter, effectively ending access to emails and accounts on the platform.
- Infrastructure costs—covering bandwidth, storage, and compute—consumed a growing share of the budget as the user base expanded, while the project failed to identify a scalable paid model or monetization path.
- Funding rounds failed to materialize, acquisitions fell through, and staff departures left the team unable to maintain critical infrastructure or push a viable economic model.
- The project’s token never achieved a clear, scalable use case, and its economic design did not establish a self-sustaining loop; the token price subsequently hit an all-time low.
- Tonight’s news sits within a broader pattern of Web3 project closures, reflecting a challenging environment for infrastructure-heavy, user-reliant services.
Escalating costs vs. decentralized promises
At the heart of Dmail’s exit lie the economics of running a decentralized communication platform at scale. The shutdown notice emphasizes that bandwidth, storage, and computing resources form the majority of operating expenses, costs that grow as more users come online. While decentralization can reduce reliance on centralized servers, it does not eliminate the physical requirements of delivering reliable, globally accessible services. The company notes that despite exploring various monetization avenues, it could not secure a business model that users were willing to support at scale.
The experience underscores a recurring tension in the space: the ambition to offer censorship-resistant, privacy-preserving communications often collides with the costs of maintaining robust infrastructure and a sustainable economic engine. Even with strong early user engagement, especially for crypto-native applications that rely on on-chain primitives or specialized services, the path to profitability remains uncertain without durable monetization or external capital cycles.
Funding headwinds and the token narrative
Dmail’s leadership pinpoints financing challenges as a critical contributor to the shutdown. Multiple fundraising rounds did not close, and strategic acquisitions that might have bolstered the platform’s capital runway did not come to fruition. When coupled with ongoing staff churn and the resulting strain on maintenance capabilities, the project’s ability to keep its infrastructure online deteriorated over time.
Compounding the financial strain was the token’s performance, which failed to translate into a compelling, large-scale use case. The project’s native token did not establish a durable economic design that could support a self-sustaining ecosystem, according to the shutdown note. After the announcement, the token price retraced to all-time lows, with data from CoinGecko showing a slide to about $0.0002067 per token. This dynamic mirrors a broader market pattern where tokenomics and real utility struggle to align with high operational costs and user expectations.
Context within a challenging Web3 landscape
Dmail’s exit comes amid a wave of closures that illustrates the current fragility of some Web3 native services, particularly those that depend on sustained infrastructure beyond simple software deployments. Earlier in March, DAO tooling platform Tally announced a wind-down, citing a lack of a viable market for its products. A week later, Balancer Labs reported shutting down parts of its protocol four months after a major exploit drained more than $100 million. While each case has its own specifics, the trend underscores a critical point for builders in this space: without a durable path to revenue and resilience against funding cycles and security incidents, even technically innovative projects can struggle to endure.
For users, developers, and investors, Dmail’s experience reinforces the importance of aligning decentralization promises with practical, scalable economics. It also highlights the need for clear exit strategies and data portability when services decide to wind down, ensuring users can preserve important communications and records before shutdowns take effect.
In sharing its decision, Dmail urged users to export data ahead of May 15, and suggested that anyone relying on the service prepare for discontinuation of access as the network’s nodes go offline. For observers, the episode serves as a reminder that the most ambitious technical visions must be matched by disciplined business models and sustainable funding paths if they are to endure in a competitive crypto ecosystem.
Looking ahead, readers will want to monitor how remaining Web3 communication projects address the dual pressures of infrastructure costs and monetization. Will new models emerge that better balance decentralization with long-term sustainability? And how will the broader market’s appetite for funding, partnerships, and user growth shape the next generation of crypto-enabled communication tools?
Crypto World
Execution Risk In Crypto Is The New Custody Risk


Opinion by: Ido Sofer, founder and CEO at Sodot.
The crypto industry is normally well ahead of its game when it comes to pure innovation and functionality, but security is a different matter.
For years, custody risk in crypto was defined by a single fear: the theft of private keys. The industry responded by hardening storage with cold storage, air-gapped systems, MPC and other methods. It then recognized that protecting only the keys is not enough, introducing transaction security and policies to prevent malicious transactions that steal funds, although the keys remain safe. Both of these remain a serious threat, but focusing solely on private keys obscures a deeper shift.
Custody itself has expanded far beyond private keys.
“Custody” once meant protecting private keys. That definition no longer reflects reality. Custody has evolved into a complex, automated system that operates different kinds of transactions, across multiple venues, custodians, vendors and internal systems. Modern trading firms operate across exchanges, staking platforms, liquidity venues and infrastructure providers, each with API keys, validator keys, deployment credentials and system-level secrets that can move capital directly or indirectly.
Many of these credentials are stored in secret managers that, by design, return the full key to any authenticated process. Convenient, yes, but structurally fragile. If the execution environment is compromised, either by an external attacker, an employee that was threatened or a malicious dependency, the full key is compromised. Custody risk has expanded beyond dormant on-chain keys into a live execution layer, where capital moves in milliseconds and exposure happens in real time.
The evolution of custody security
Custody security evolved in stages. First, the industry secured private keys in storage. It then moved beyond storage, embedding policy and multi-party controls to govern how those keys were used in execution. The next step is inevitable: apply the same zero-exposure and policy-driven discipline to every key and credential. In modern crypto operations, API keys, deployment credentials and execution secrets carry significant risk. Extending private key best practices across this broader surface is no longer optional; it is the defining challenge of execution risk.
In recent years, the execution risk has emerged as the single biggest vector for large-scale exploits. Cybercriminals are bypassing onchain security mechanisms in favor of the soft underbelly, namely the API keys, server credentials and other off-chain secrets needed to facilitate trading, code deployment, staking and custodial actions. Recent major breaches, including the Bybit hack, started with an off-chain hack and compromised credentials, which later led to on-chain loss of funds.
How big is the execution risk?
It’s big and structural. Asset managers, trading firms, custodians and payment companies connect to dozens of CEXs, DEXs, liquidity providers and other vendors simultaneously. Each integration introduces its own credentials, access controls and operational dependencies. Managing these spans across development, ops, trading, risk and security teams, which creates complexity that compounds over time.
Securing these operations is a never-ending struggle. Maintaining consistent security policies and multi-vendor access is a massive headache that’s largely manual, resulting in inevitable security gaps and configuration drift.
Related: Bitcoin is infrastructure, not digital gold
Execution risk is not inherent toautomation. It is a byproduct of how trading systems have historically been designed. In many centralized exchange environments, API keys and operational credentials are placed directly inside trading infrastructure to eliminate latency. For market makers and trading firms, speed is not a feature, it is the business model. Even marginal delay affects revenue.
Over time, full-key availability inside live systems became normalized as the simplest way to achieve high-performance execution. Credentials sit in a constant state of readiness so transactions can be authorized instantly. The issue is not that capital moves quickly. It is that unilateral authority is embedded inside operational infrastructure. And when authority is concentrated where execution happens, it becomes the most predictable attack vector.
Existing controls fall short
Existing tools fall far short of what’s required, considering the complexity of modern execution environments.
While crypto exchanges, custodians and over-the-counter trading desks certainly employ robust security policies for specific operations, it’s incredibly difficult for them to synchronize those controls across such a fragmented ecosystem. In fact, it’s almost impossible to maintain consistent governance across forty-odd exchanges for any length of time. Since it’s done manually, in silo, errors are inevitable, and a single mistake can put millions of dollars in value at risk.
There’s also the counterparty risk to consider. Exchanges and custodians may have their own vulnerabilities in the shape of bugs, misconfigured infrastructure and inconsistent policy enforcement mechanisms. If a trading firm’s internal security code requires geofencing, but one of the exchanges it’s connected to has a buggy implementation of that control, it creates a risk at the point of execution.
The risk is intolerable
The lesson the industry learned from private key security is clear: eliminate full key exposure and enforce strict policy controls around usage. Those principles must now extend beyond on-chain private keys to every credential capable of authorizing value movement.
The solution is not simply better secret storage. Secret managers were built for convenience; they return the full key to any authenticated process. In live execution environments, that model distributes authority to multiple components of the system at the very moment capital is in motion.
What is required is zero key exposure architecture systems where no single machine or employee ever holds unilateral control, combined with enforceable, context-aware policies governing how credentials are used. Multi-party computation (MPC) is one way to implement this model, but the principle is broader — expand private-key security best practices across the entire crypto execution layer.
Opinion by: Ido Sofer, founder and CEO at Sodot.
This opinion article presents the author’s expert view, and it may not reflect the views of Cointelegraph.com. This content has undergone editorial review to ensure clarity and relevance. Cointelegraph remains committed to transparent reporting and upholding the highest standards of journalism. Readers are encouraged to conduct their own research before taking any actions related to the company.
Crypto World
Ripple CEO Reveals the Secret Behind Its Crypto and Fiat Treasury System

What does it take to get corporations into digital assets? According to Brad Garlinghouse, the formula is surprisingly simple.
The Ripple CEO just broke down the “secret sauce” behind Ripple Treasury. It’s an enterprise treasury management platform that lets businesses view and manage both fiat and digital assets (including XRP and RLUSD stablecoins) in a single, unified dashboard.
The Two-Ingredient Formula
Garlinghouse laid it out clearly. No complicated onboarding, no new systems to learn, and no juggling between separate platforms for fiat and crypto. Just one unified solution.
Fun Fact: Ripple Treasury facilitated $13 trillion in payments last year. That’s roughly half of the entire US GDP processed through a single treasury platform!
What Changed
Ripple Treasury just launched as the first Treasury Management System (TMS) with native digital asset capabilities. For CFOs, this means a single place to hold and manage both digital and fiat assets.
Renaat Ver Eecke, who leads Ripple Treasury (formerly GTreasury), explained the vision:
“From the moment GTreasury became Ripple Treasury, we’ve been building to this, giving Corporates a clear, trusted entry point into digital assets.”
The new features include Digital Asset Accounts and Unified Treasury. Corporate treasurers no longer need separate systems, separate logins, separate workflows. Everything lives in one place.
Ver Eecke outlined the roadmap: connecting to Ripple’s regulated payments network and prime brokerage. This will allow corporates to use digital assets and stablecoins for cross-border intercompany payments, earn yield on idle cash around the clock, and much more.
The key insight: Corporations don’t want to become crypto companies. They want to use crypto rails without changing their operations. Ripple Treasury meets them exactly where they are.
Ver Eecke summarized it bluntly: “Corporate treasury has never had a solution like this before.”
Ripple Has a Unique Value in the Enterprise Segment
Traditional treasury management is fragmented. Fiat accounts here, digital assets there, cross-border payments somewhere else. Every system requires its own processes, its own compliance checks, its own headaches.
Ripple Treasury collapses all of that into a single platform. Trusted. Regulated. Embedded in existing workflows.
For CFOs who have been watching crypto from the sidelines, waiting for an entry point that doesn’t require rebuilding their entire infrastructure, this is it. The friction is gone.
Garlinghouse called it the secret sauce. Looking at $13 trillion in volume and native digital asset capabilities, the recipe seems to be working.
The post Ripple CEO Reveals the Secret Behind Its Crypto and Fiat Treasury System appeared first on BeInCrypto.
Crypto World
Why the RWA Market Is Slowing Down: Is the Boom Over?
After months of continuous growth, the RWA sector is showing its first signs of a slowdown.
Distributed asset value sits at $27.49 billion with only 1.74% growth over the past 30 days. Stablecoins even recorded a slight decline.
RWA Growth is Dying Out
Current data from RWA.xyz shows the following picture:
- Distributed Asset Value: $27.49 billion, up 1.74% in a month.
- Represented Asset Value: $403.28 billion, up 3.33%.
- Total Asset Holders: 707,564, up 5.7%.
- Total Stablecoin Value: $299.88 billion, down 0.07%.
- Total Stablecoin Holders: 241.80 million, up 4.35%.
The number of holders continues to grow, but the value is not keeping pace. New market participants are entering, but bringing less fresh capital than in previous months.
Fun Fact: Despite the slowdown, RWA distributed value has grown from under $5 billion in early 2024 to nearly $28 billion today. The long-term trend remains intact!

Which RWA Segments Are Cooling
Several asset categories are contributing to the slowdown:
- Commodities: Gold prices have stagnated, and tokenized gold follows the underlying asset.
- US Treasuries: Still the largest segment in the RWA market, but momentum has flattened. Initial demand for tokenized T-bills appears to be stabilizing.
- Stocks and Asset-Backed Credit: Both categories are also showing reduced growth.
The chart from RWA.xyz displays a clear pattern: explosive growth through 2024 and into early 2025, followed by a gradual flattening in recent months.
A monthly growth rate of 1.74% does not constitute a crash. Annualized, that still represents over 20% growth.
However, compared to the triple-digit percentage gains the RWA sector recorded in 2024, the deceleration is clearly visible.
The slight 0.07% decline in stablecoins deserves particular attention. Stablecoins often serve as an entry point into tokenized assets. A shrinking pool may indicate reduced on-chain activity.
On the positive side: asset holders grew by 5.71%. New participants continue to enter the market, though with more cautious capital allocation.
The RWA sector appears to be entering a phase of normalization following a period of strong growth. Whether this represents a temporary consolidation or the beginning of a longer trend remains to be seen in the coming months.
The post Why the RWA Market Is Slowing Down: Is the Boom Over? appeared first on BeInCrypto.
Crypto World
Corporate Bitcoin Split: Strategy Holds, Nakamoto Sells
Corporate Bitcoin (BTC) holders are diverging into two distinct paths amid continued market pressure. While Strategy held steady on its massive BTC reserves, Nakamoto Holdings moved in the opposite direction, selling at a loss and trimming exposure as it reworks its balance sheet.
The contrast highlights a growing divide in the corporate Bitcoin treasury model. Some holders have refused to sell, treating BTC as a long-term reserve asset and doubling down through volatility, while others are being forced to unlock liquidity, book losses or rethink capital allocation.
With Bitcoin down 46% from its peak, the risks behind debt-fueled or aggressive buying strategies are becoming harder to ignore.
Elsewhere, a proposed Bitcoin-backed municipal bond in New Hampshire is moving closer to issuance. It has now received a speculative-grade rating from Moody’s, underscoring both the appeal and the risks of tying public financing to digital assets.
Nakamoto realizes losses as Bitcoin treasury model comes under pressure
Bitcoin treasury company Nakamoto Holdings sold roughly $20 million worth of Bitcoin in March, executing the sale at prices well below its prior acquisition costs. The transaction reduced its holdings to just over 5,000 BTC and marked a shift from unrealized to realized losses.
The company sold approximately 284 BTC at around $70,400 per coin, significantly less than its average purchase price. The proceeds were earmarked for working capital and business investments tied to recent mergers.
Alongside the crypto sale, Nakamoto also cut its equity exposure to Japanese company Metaplanet, selling millions of shares at a loss. The moves point to a broader balance-sheet reset as digital asset treasury companies come under pressure.

Strategy pauses Bitcoin buys, keeps its treasury intact
Michael Saylor’s Strategy broke a months-long pattern of steady Bitcoin accumulation, reporting no purchases during the latest weekly disclosure period.
The pause stands out because Strategy has maintained consistent buying as a core part of its corporate identity and capital strategy, especially during the recent market downtrend that has seen Bitcoin fall from $120,000 to below $70,000.
Weekly disclosures have become a signal for institutional demand, and even a temporary halt could suggest squeamishness over market conditions, capital availability or the pace of buying. Strategy still holds roughly 762,000 BTC, maintaining its position as the largest corporate holder of the asset.

New Hampshire Bitcoin-backed bond inches toward reality after Moody’s rating
A proposed Bitcoin-backed municipal bond in New Hampshire has moved a step closer to issuance after receiving a Ba2 rating, below investment grade, from Moody’s. The structure would give investors exposure to Bitcoin-linked returns within a public finance framework, with proceeds expected to support public infrastructure and development projects.
The planned issuance, reportedly around $100 million, would be backed by Bitcoin collateral rather than traditional tax revenues. Repayments would depend on returns from that collateral, introducing a new approach that ties crypto markets to municipal borrowing.

CoinShares debuts on Nasdaq following SPAC deal
Digital asset manager CoinShares launched on the Nasdaq on Wednesday following a merger with special purpose acquisition company Vine Hill Capital, marking another step in bringing crypto-native companies to US public markets.
The deal gives CoinShares access to a broader investor base and deeper capital markets, while offering public market investors exposure to a company focused on digital asset products and infrastructure. SPAC structures have remained a viable route for crypto companies seeking listings despite shifting market conditions.
As Cointelegraph previously reported, the SPAC merger valued CoinShares at roughly $1.2 billion.
Crypto Biz is your weekly pulse on the business behind blockchain and crypto, delivered directly to your inbox every Thursday.
Crypto World
Coinbase Joins Crypto Bank Trust Wave, Landing Conditional Approval From the OCC


Coinbase got conditional approval from the OCC for its trust, a step toward federal oversight for its offerings to replace the current state by state licensing approach.
Coinbase announced on Thursday that it has received conditional approval from the Office of the Comptroller of the Currency (OCC) to establish Coinbase National Trust Company, a non-insured national trust bank to be headquartered in New York.
The approval marks a step toward Coinbase operating as a federally regulated digital asset custodian — and the latest milestone in a sweeping regulatory shift reshaping how crypto firms interact with the U.S. banking system.
The preliminary green light requires Coinbase to build out compliance systems, hire key staff, pass regulatory reviews, and demonstrate strong risk management and anti-money-laundering controls before it can secure a full charter.
A national trust bank charter gives Coinbase a single federal regulator — the OCC — in place of the patchwork of state money transmitter licenses it currently holds, allowing it to offer custody, safekeeping, and related digital asset services in a fiduciary capacity as a qualified custodian under SEC regulations.
In yesterday’s blog post, the largest U.S. centralized exchange noted that it does not plan to become a commercial bank:
“Coinbase is not becoming a commercial bank. We will not be taking retail deposits. We will not be engaging in fractional reserve banking.”
Looking ahead, Coinbase’s chief legal officer told CNBC that the company plans to explore payment infrastructure products alongside its custody business, with an eye on expanding stablecoin use — particularly USDC — as a mainstream global payment method.
Coinbase joins a crowded field of crypto firms racing to secure federal charters under the OCC’s current leadership.
Circle applied for its own national trust bank license — to be called First National Digital Currency Bank — and received conditional approval in December 2025. Crypto.com similarly secured conditional OCC approval for its Foris Dax National Trust Bank in February.
The trend has not gone uncontested: the Bank Policy Institute, whose members include JPMorgan, Goldman Sachs, and Bank of America, is reportedly weighing a lawsuit against the OCC over what it sees as an uneven regulatory playing field.
This article was written with the assistance of AI workflows. All our stories are curated, edited and fact-checked by a human.
Crypto World
SBI Ripple Asia Partners with DSRV to Research XRP Payments

XRP Ledger Chosen to Be the Research Framework
XRP Ledger will be used as the fundamental blockchain platform in the study. In addition, it will discuss how the network assists in payment processing in various markets. In this way, the firms would assess the technical performance under actual conditions. The companies explained that the project does not imply the immediate product rollout, but it will seek to collect technical and regulatory experience to be used in the future. Therefore, the research will guide long-term infrastructure planning.
Japan and South Korea are still working on creating stablecoin and blockchain laws. As a result, there are differences between two systems that should be analyzed in detail. The paper will examine compliance standards in the two jurisdictions. In the study, the researchers will evaluate what blockchain is doing with existing payment infrastructure. It will also compare compatibility with current banking and remittance systems. This will help to ensure that the solutions that will be developed in the future can work within the set frameworks.
The two companies will consider transaction flows and operating models. Therefore, the work will touch upon the stability and performance of the system under real conditions. In addition, it will also analyze some of the risks that may be associated with blockchain-based payments. The project identifies a number of areas of focus on which to analyze. It will look at the issues in the business environment and institutional differences between the two nations. Also, it will determine technical and operational obstacles that influence adoption.
Payments Under Evaluation Use Cases
The companies will consider the real-life uses of blockchain in payments. Therefore, they seek to find feasible applications of cross-border remittances. This will assist in laying down the future implementation directions. This research follows Ripple as it keeps on expanding partnerships with the global payment networks. Furthermore, South Korea has seen more currency being traded on local exchanges, indicating a growth of the stablecoin activity in the country. Such developments give a background to current research. The collaborative research creates a framework for analysing blockchain payments in two regulated markets. In addition, it assists in the planning of cross-border financial infrastructure in the future.
Crypto World
South Korean ‘drug lord’ extradited as authorities target Bitcoin trail


South Korea extradites alleged drug boss Park Wang‑yeol and prepares a blockchain forensics push to trace at least 6.8b won in Bitcoin‑linked drug proceeds.
Summary
- South Korea has extradited alleged drug kingpin Park Wang-yeol from the Philippines and placed him under a joint drug crime task force.
- Investigators will scrutinize Bitcoin wallet activity to trace at least 6.8 billion won (about $5 million) in confirmed proceeds and search for far larger hidden assets.
- The case showcases how Korean law enforcement now leans on blockchain forensics to unwind complex, cross-border narcotics networks.
South Korean authorities have taken custody of alleged “drug lord” Park Wang‑yeol, extradited from a Philippine prison where he was serving a 60‑year sentence for the 2016 “sugarcane field” triple homicide, to face new narcotics and money‑laundering charges at home. Reuters reported that Park, believed to be 47, is suspected of running a drug trafficking ring from inside his Philippine cell, coordinating shipments of “large quantities” of methamphetamine and other narcotics into South Korea via encrypted apps. According to Korean media summaries cited by outlets including the Dong‑A Ilbo, officials estimate he oversaw a monthly drug business worth roughly 30 billion won (around $22 million), turning prison into a command center rather than a constraint.
The Korean Drug Crime Joint Investigation Headquarters — a consolidated task force of prosecutors and police — has made clear that tracing Park’s financial footprint will rely heavily on on‑chain analysis of Bitcoin wallets believed to have received drug proceeds. While confirmed criminal takings in the current indictment stand at roughly 6.8 billion won (just over $5 million), investigators told domestic media they suspect the true scale of assets moved through crypto wallets between November 2019 and July 2024 is “several times larger.
Reporting from Chosun Ilbo details how Park allegedly directed accomplices in Korea to sell drugs sourced from abroad — including at least 4.9 kilograms of methamphetamine and thousands of ecstasy and ketamine doses — then funneled profits through digital channels rather than traditional banking rails. The task force has identified more than 200 accomplices across roles such as suppliers, smugglers and street dealers, underlining the networked nature of the operation and the need for tools that can map complex flows of funds.
South Korea has quietly built one of the more aggressive crypto‑crime enforcement programs in Asia, deploying specialist units that routinely use blockchain analytics platforms to deanonymize wallets and claw back illicit proceeds. A 2024 briefing from Blockchain Intelligence Group noted that Seoul’s joint investigation division recovered roughly 163.87 billion won (about $121 million) in crypto‑linked criminal proceeds in a single year, relying on tools that “identify clusters of wallets,” “track the flow of funds” and link addresses to real‑world entities.
Recent cases underscore both the potential and pitfalls of this approach: DL News reported in February that prosecutors managed to recover $22 million worth of Bitcoin that had effectively gone “missing” in an earlier phishing investigation, even as separate lapses saw police mismanage and temporarily lose more than $1.4 million in seized BTC. In that context, the Park Wang‑yeol probe is emerging as a showcase for how far Korean authorities can push on‑chain forensics to pierce one of the country’s most notorious narcotics empires — and whether they can do so while tightening their own controls over seized digital assets.
Crypto World
Hyperliquid Price Rallied 13% but the Money Underneath Tells Another Story
Hyperliquid (HYPE) price trades near $35.60 on April 3, carrying a 13% monthly gain that masks an 8% decline over the past seven days.
On the surface, the monthly performance looks strong for a market under pressure. However, the 8-hour chart is forming a bearish reversal pattern, institutional money flow is diverging from price, and the platform’s own financial metrics show a sharp deterioration in capital commitment. The bounce currently underway may extend further before the structure breaks, but the weight of evidence points toward eventual weakness.
An Inverse Cup Forms as Big Money Quietly Exits
Since March 10, Hyperliquid price has been tracing an inverse cup and handle pattern on the 8-hour chart, a bearish reversal structure. The current bounce is forming what closely resembles the handle, a smaller upward drift within a narrowing channel before a potential breakdown.
The handle remains intact as long as HYPE stays below $40.30. A confirmed break below the neckline would activate the pattern’s measured move, projecting approximately 22% downside from the neckline.
Chaikin Money Flow (CMF), a proxy for institutional buying and selling pressure, confirms the weakness behind the pattern. Since late February, while HYPE price trended higher, CMF trended lower, deepening into negative territory at -0.06. That bearish divergence indicates that large participants have been reducing exposure throughout the rally.
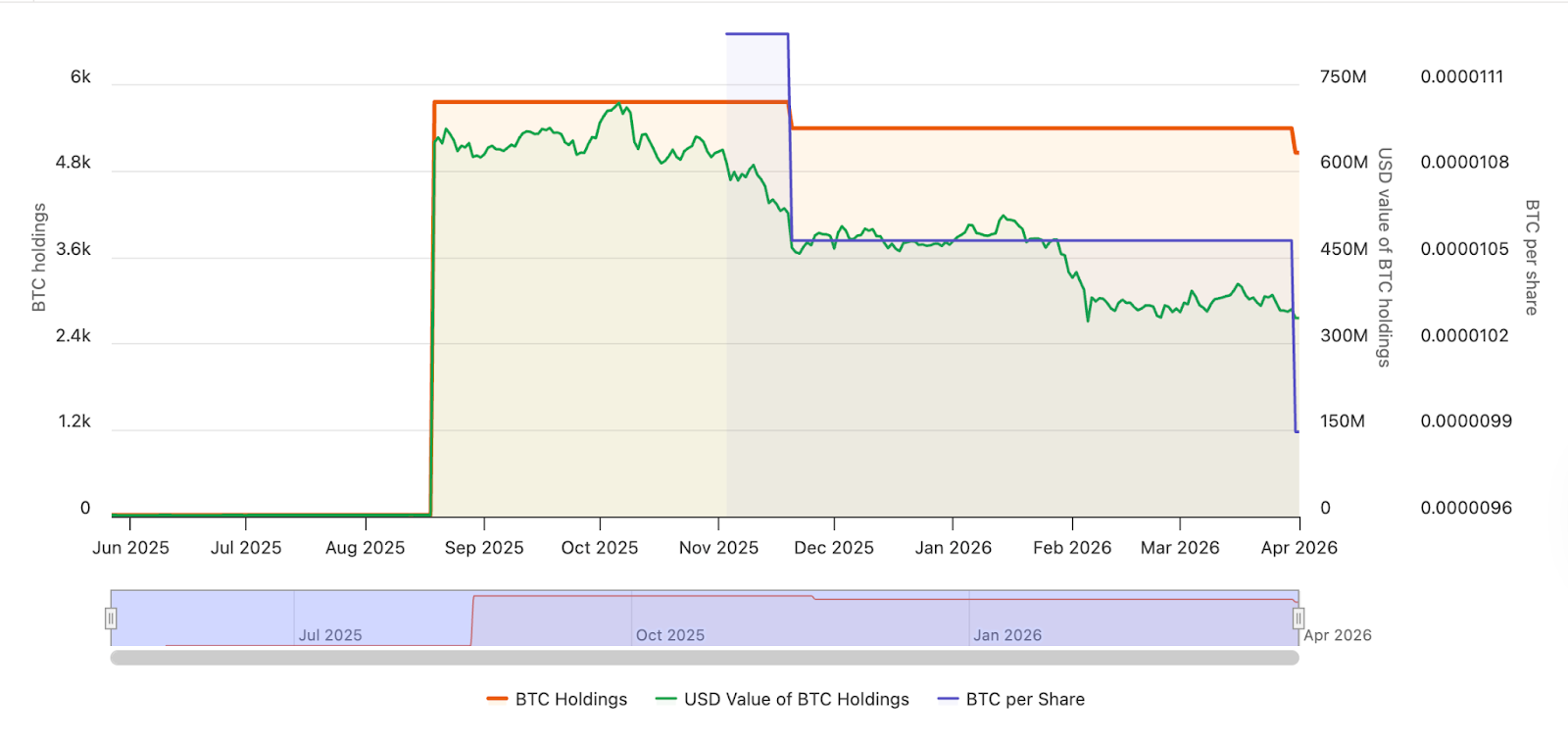
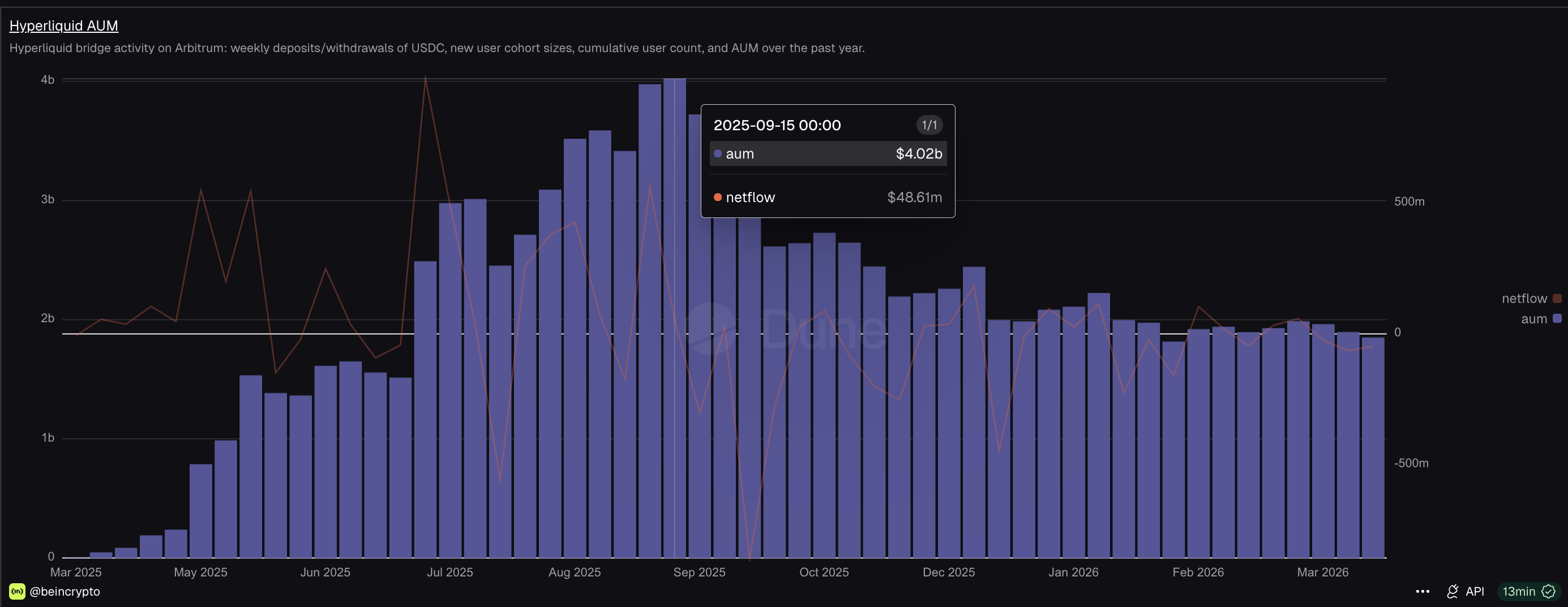
The on-chain data from Dune Analytics possibly explains why. Hyperliquid’s USDC-based assets under management (AUM) on Arbitrum peaked at $4.02 billion around mid-September 2025. By March 30, 2026, that figure had dropped to $1.85 billion, a 54% decline. USDC net flow, which measures the difference between deposits and withdrawals, remains in negative territory, meaning more stablecoins are leaving the platform than entering.
The AUM decline reflects a broader DeFi capital contraction. Total DEX spot volume across all platforms fell to $155 billion in March 2026, its lowest level since September 2024.
As a derivatives-focused platform with spot offering too, Hyperliquid allows traders to generate outsized volume through leverage with relatively small USDC deposits.
When capital commitment shrinks at the platform level while price rises, the rally lacks the financial foundation to sustain itself. The liquidation map now determines whether the bounce extends before the pattern resolves.
Liquidation Imbalance Could Fuel a Bounce Before the Break
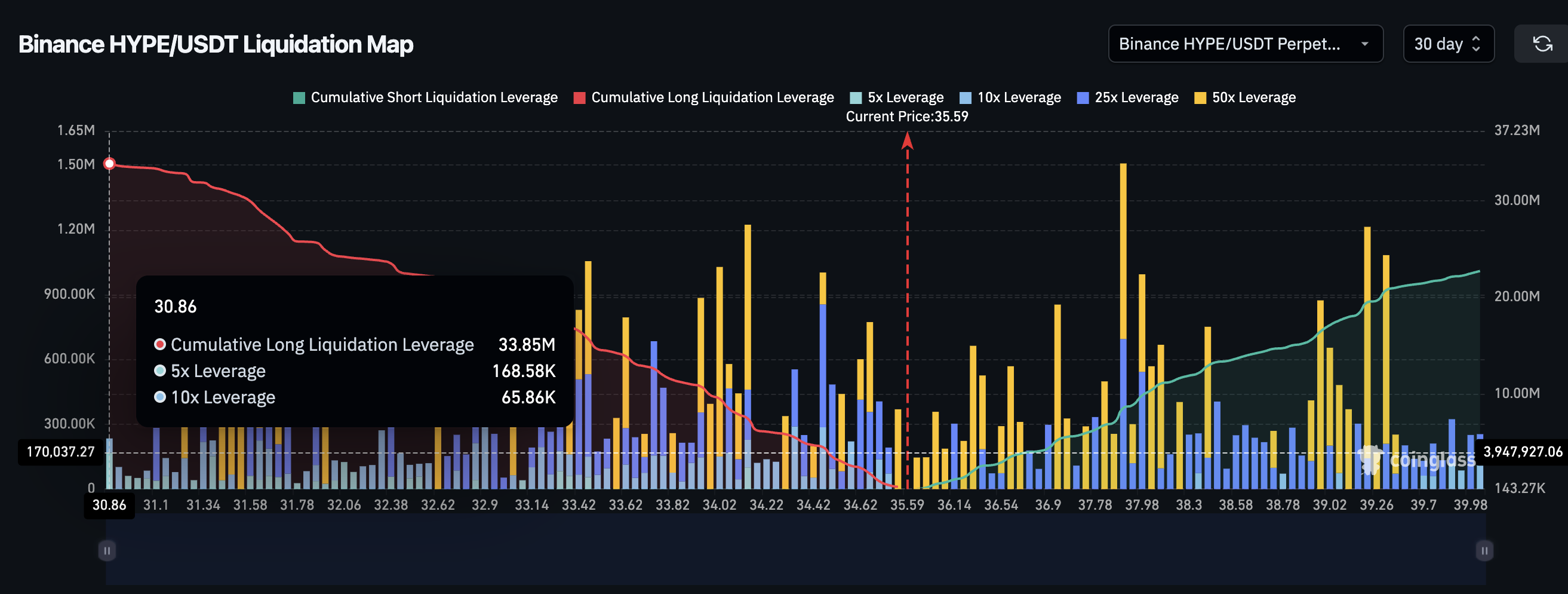
The Binance HYPE/USDT liquidation map adds an important layer that complicates the bearish timeline. Over the past seven days, the HYPE liquidation picture is heavily skewed toward shorts. Cumulative short liquidation leverage stands at $23.92 million, while long liquidation leverage sits at just $7.92 million. That roughly 75% tilt toward shorts means even a modest upward price move could trigger a cascade of forced short closures, temporarily pushing Hyperliquid price higher.
This short-heavy 7-day positioning likely exists because the past week’s 8% decline already flushed most of the recent long positions through liquidations. What remains are new shorts betting on continued weakness.
Want more token insights like this? Sign up for Editor Harsh Notariya’s Daily Crypto Newsletter here.
However, the 30-day liquidation map flips the picture. Over that timeframe, cumulative long leverage is $33.85 million against $22.73 million in shorts.
The roughly 30% tilt toward longs means the broader positioning still favors upside bets. If the bounce driven by 7-day short squeezes fails to reclaim key levels and price resumes its decline, those 30-day long positions become vulnerable. A move toward the neckline at $34.13 could trigger both the pattern breakdown and a fresh wave of long liquidations, accelerating the sell-off.
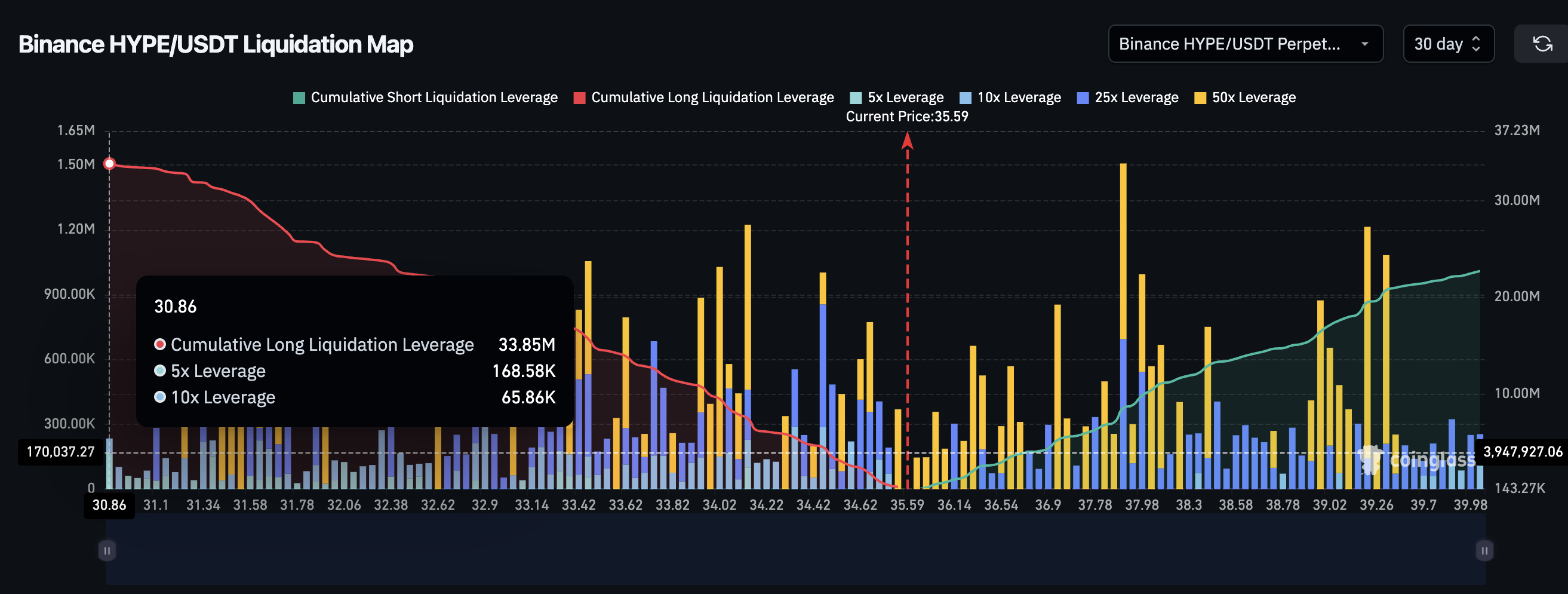
The liquidation data therefore supports a scenario where the handle extends higher on short-term short squeezes before the broader structure breaks down under the weight of long-biased leverage and declining capital flows.
Hyperliquid Price Levels That Decide the Pattern
The 8-hour chart with Fibonacci levels frames the path for Hyperliquid price from here. HYPE currently trades at $35.60, sitting between the 0.382 Fib at $35.53 and the 0.236 Fib at $36.39.
For the bounce to gain meaningful traction, HYPE needs to clear $36.39 first, followed by $37.79. A move above $40.30 would weaken the inverse cup and handle structure, and reclaiming $43.78 would invalidate the pattern entirely.
On the downside, $34.83 acts as the immediate floor. A close below $34.13 confirms the neckline break and activates the measured move, projecting a 22% decline that could take HYPE price toward $26.81.
Between $34.13 and $26.81, interim support sits at $33.14, $31.87 and $28.22.

Inverse cup and handle patterns do not always complete. The short-heavy 7-day liquidation setup could produce a squeeze that pushes price above the handle, delaying or invalidating the breakdown. However, the combination of falling CMF, shrinking AUM, negative USDC flows, and a long-biased 30-day leverage structure all suggest the bounce is more likely a pause than a reversal.
A close below $34.13 separates a temporary squeeze-driven bounce from a pattern-confirmed decline toward $26.81. But reclaiming $40.30 would be the first evidence of near-term strength.
The post Hyperliquid Price Rallied 13% but the Money Underneath Tells Another Story appeared first on BeInCrypto.
Crypto World
Riot Platforms Sells 3,778 BTC in Q1 2026 for $289.5M


Nasdaq-listed Bitcoin miner Riot Platforms sold 3,778 BTC in the first quarter of 2026, generating roughly $289.5 million in net proceeds.
Riot Platforms, a major publicly traded Bitcoin mining company listed on Nasdaq, sold 3,778 BTC during Q1 2026, netting approximately $289.5 million in proceeds. The sale represents a significant reduction in the miner’s Bitcoin holdings and marks a notable shift in the company’s position management strategy.
The move aligns with broader selling activity across the Bitcoin mining sector. Multiple publicly traded miners have collectively sold more than 15,000 BTC in recent months, signaling increased liquidation pressure within the industry.
Sources: Riot Platforms
This article was generated automatically by The Defiant’s AI news system from publicly available sources.
Crypto World
The revolving door for lawyers between Kalshi and DOJ


A lawyer who helped Kalshi win a key court fight against the federal government now helps the federal government protect Kalshi from state attorneys general.
Yaakov Roth, a former Jones Day white shoe lawyer who represented Kalshi in the landmark KalshiEX v. Commodity Futures Trading Commission (CFTC) case, appeared by name on federal complaints filed yesterday against Illinois, Arizona, and Connecticut.
His current title is now Principal Deputy Assistant Attorney General, Department of Justice (DOJ) Civil Division. These federal lawsuits argue that state gambling laws should have little jurisdiction over prediction markets due to the CFTC’s oversight.
In essence, the suits are attempts by the CFTC to protect Kalshi from state-level actions.
Roth joined the DOJ in February 2025. He had already secured a pivotal victory in late 2024 when the DC Circuit denied the CFTC’s emergency stay against Kalshi’s event contracts contingent on US elections. In January 2025, Roth argued the full appeal, then joined DOJ. The CFTC later dropped its appeal against Kalshi in May 2025 in a victory for Roth.
The Biden-era CFTC disapproved of Kalshi’s proposed congressional control election contracts in 2023. Kalshi then sued the CFTC, challenging that decision. By May 2025, the Trump-era CFTC voluntarily dropped the commissioners’ appeal.
Now at the US government’s DOJ instead of Kalshi’s law firm Jones Day, Roth has been found on a team on the other side of the “v.” (versus) separator in lawsuit titles involving Kalshi.
The Kalshi-government lawyer pipeline
Roth is not the only former Kalshi lawyer to land a government job.
Eliezer Mishory, Kalshi’s former General Counsel lawyer, stepped down in March 2025 to take a DOGE-linked role at the SEC, where his title is Senior Advisor to the Chairman.
Mishory previously worked at the CFTC under Brian Quintenz.
Read more: Are Polymarket and Kalshi decentralized?
Quintenz, a former CFTC commissioner, has sat on Kalshi’s board since 2021.
Trump nominated Quintenz as Chairman of the CFTC in February 2025. However, his nomination was withdrawn in September 2025 amid mounting concerns, such as documents obtained by Freedom of Information Act (FOIA) requests revealing his incoming staff seeking CFTC information about Kalshi’s competitors or the Winklevoss twins lobbying Trump directly against his candidacy.
Kalshi also has another strong connection to the White House via Donald Trump’s son, Donald Trump Jr. He has served as an advisor to Kalshi and as an advisory board member of Polymarket; additionally, he is an investor in Polymarket through a venture capital firm, 1789 Capital.
The federal government that sued Kalshi now cushions it from states
Kalshi CEO Tarek Mansour celebrated Roth’s DOJ appointment on LinkedIn. “Without Yaakov Roth’s legal guidance and leadership, prediction markets in America wouldn’t be where they are today,” Mansour wrote. He called Roth “arguably one of the best appellate litigators in the country” and added, “We couldn’t be more excited for him and his next journey at the DOJ.”
Indeed.
The three state-level lawsuits involve cease-and-desist letters to Kalshi, Polymarket, and other prediction market operators.
Arizona went furthest. It filed 20 criminal charges against Kalshi in March 2026, including four counts of election wagering.
CFTC Chairman Michael Selig, a Trump appointee, declared in February that the agency would “no longer sit idly by” while states challenged its authority. His Innovation Advisory Committee includes executives from Kalshi, Polymarket, FanDuel, and DraftKings. Its 35 members are almost entirely industry executives.
Sports betting accounted for the majority of Kalshi’s trading volume in recent months. The company reported over $1 billion in Super Bowl trading volume alone. States call those trading contracts gambling. The Trump administration calls them non-gambling derivatives or prediction markets; specifically, it considers them commodity event contracts.
The question is probably not whether the revolving door between Kalshi and federal agencies spins. It is whether any lawyer, or anyone, plans to stop it.
Got a tip? Send us an email securely via Protos Leaks. For more informed news, follow us on X, Bluesky, and Google News, or subscribe to our YouTube channel.
-

 NewsBeat7 days ago
NewsBeat7 days agoThe Story hosts event on Durham’s historic registers
-

 NewsBeat21 hours ago
NewsBeat21 hours agoSteven Gerrard disagrees with Gary Neville over ‘shock’ Chelsea and Arsenal claim | Football
-

 Sports7 days ago
Sports7 days agoSweet Sixteen Game Thread: Tide vs Michigan
-
Entertainment4 days ago
Fans slam 'heartbreaking' Barbie Dream Fest convention debacle with 'cardboard cutout' experience
-

 Business16 hours ago
Business16 hours agoNo Jackpot Winner and $194 Million Prize Rolls Over
-

 Crypto World2 days ago
Crypto World2 days agoGold Price Prediction: Worst Month in 17 Years fo Save Haven Rock
-

 Entertainment6 days ago
Entertainment6 days agoLana Del Rey Celebrates Her Husband’s 51st Birthday In New Post
-

 Tech5 days ago
Tech5 days agoThe Pixel 10a doesn’t have a camera bump, and it’s great
-
Crypto World3 days ago
Dems press CFTC, ethics board on prediction-market insider trades
-

 Sports3 days ago
Sports3 days agoTallest college basketball player ever, standing at 7-foot-9, entering transfer portal
-

 Tech5 days ago
Tech5 days agoAvatar Legends: The Fighting Game comes out in July and it looks pretty slick
-

 Tech3 days ago
Tech3 days agoEE TV is using AI to help you find something to watch
-

 Fashion6 days ago
Fashion6 days agoAmazon Sundays: Soft Spring Layers
-

 Business2 days ago
Business2 days agoLogin and Checkout Issues Spark Merchant Frustration
-

 Fashion7 days ago
Fashion7 days agoWhen Evening Dressing Gets Colorful for Spring
-

 Tech5 days ago
Tech5 days agoElon Musk’s last co-founder reportedly leaves xAI
-

 Tech3 days ago
Tech3 days agoHow to back up your iPhone & iPad to your Mac before something goes wrong
-

 Tech4 days ago
Tech4 days agoApple will hide your email address from apps and websites, but not cops
-

 Crypto World4 days ago
Crypto World4 days agoU.S. rule change may open trillions in 401(k) funds to crypto
-

 Politics4 days ago
Politics4 days agoShould Trump Be Scared Strait?










You must be logged in to post a comment Login