Crypto World
Hacker Drains $5.9M From Ethereum Liquidity Provider TrustedVolumes

TrustedVolumes, a liquidity provider on the Ethereum blockchain, lost about $5.9 million in funds to a hacker on Thursday.
The attacker was able to exploit a vulnerability within the custom trading system used by the platform and managed to withdraw the funds, which included ETH, WBTC, as well as USDT and USDC stablecoins.
What Happened
According to blockchain security firm Blockaid, which caught the exploit as it was happening, the stolen funds included 1,291 WETH, around 16.9 WBTC, roughly 206,000 USDT, and just under 1.27 million USDC.
The attack worked by abusing a design flaw in TrustedVolumes’ custom order-settlement system, known as a Request for Quote (RFQ) proxy.
GoPlus Security posted a breakdown showing that the attacker registered themselves as an authorized “order signer” using a function called “registerAllowedOrderSigner()” that was publicly accessible.
The function allows anyone to designate their own address as a valid signer for trades they controlled, and while normally that would be harmless enough, the settlement function had a separate problem: it checked authorization against one address while actually pulling funds from a different one.
As detailed in a technical report posted by security researcher Defi Nerd, the attacker used that gap to execute four drain transactions against the TrustedVolumes resolver contract, which had previously given the proxy permission to move its tokens.
According to them, each time, the proxy pulled assets from the resolver and sent only a single raw USDC unit back. Then the attacker converted the stolen WETH back into ETH and forwarded everything to their own wallet.
TrustedVolumes confirmed the exploit and publicly posted three wallet addresses holding the stolen funds, asking the hacker to get in touch about a “bug bounty and a mutually acceptable resolution.”
1inch Distances Itself as DeFi Hacks Continue
Because TrustedVolumes functions as a liquidity provider and market maker on 1inch, some early reports framed the incident as a 1inch exploit.
However, that is not accurate, and both 1inch and Blockaid put out statements clarifying that the protocol itself was not compromised and no user funds on 1inch were affected. TrustedVolumes operates independently across multiple platforms, not exclusively on 1inch.
The attack occurred during an especially difficult period for the DeFi ecosystem since it followed a catastrophic month of April, where more than $650 million worth of crypto was stolen from different projects.
KelpDAO and Drift Protocol were the most affected, having $292 million and $285.2 million taken away from them.
So at $5.9 million, this latest exploit is smaller in scale. But the technical sophistication of the approach, deploying a helper contract, abusing self-service signer registration, and exploiting a maker/funding-source mismatch in a single transaction, puts it in a different category from a simple bug or misconfiguration.
The post Hacker Drains $5.9M From Ethereum Liquidity Provider TrustedVolumes appeared first on CryptoPotato.
Crypto World
Iran’s Largest Exchange Stays Off OFAC Blacklist

Estimates of Nobitex’s scale vary, but multiple firms place its activity in the billions of dollars. TRM Labs, for instance, reported approximately $5 billion in observed volume on Nobitex between 2025 and March 2026. Chainalysis has previously noted that inflows to Nobitex addresses exceeded the combined inflows of Iran’s next ten largest exchanges, underscoring the platform’s outsized role in the domestic crypto economy. Nobitex’s own disclosures say it serves around 11 million Iranians, about 12% of the population, with a broad suite of services that extends beyond spot trading to margins, yield products, liquidity pools, gift cards, and crypto-collateralized lending. The platform also provides differentiated terms for professional and institutional participants.
Key takeaways
- Nobitex processes billions in value and claims a retail footprint of roughly 11 million users, making it a linchpin of Iran’s crypto activity despite a broader online isolation.
- Regulators have not sanctioned Nobitex on the U.S. Treasury’s Specially Designated Nationals (SDN) List, but authorities have long treated Iranian crypto exchanges as blocked financial institutions, complicating enforcement and international participation.
- Investigations and disclosures link Nobitex to state-driven usage, including central-bank activity in stablecoins and ties to elite networks, prompting questions about where sanctions pressure is most effective.
- Analysts warn that the Nobitex case highlights a larger tension: sanctions aim at deterring regime finance, but may also entangle millions of ordinary users who rely on crypto for access to foreign liquidity and inflation resilience.
Nobis footprint: retail gateway and strategic asset channel
Beyond its consumer-facing services, Nobitex has developed an architecture that some observers describe as purpose-built to operate under sanctions. Its platform accommodates a broad retail audience, while its API and service tiers cater to high-volume traders and institutions seeking faster settlement and higher limits. This combination makes Nobitex more than a passive conduit; it acts as a central node where ordinary users and sanctioned-related flows intersect.
In parallel, broader market research situates Nobitex as a critical domestic hub. The exchange’s scale aligns with a larger pattern identified by researchers: Iran’s crypto environment has matured from experimental use into a structured ecosystem that blends retail adoption with state-driven financial choreography. As Chainalysis has emphasized, Iran’s crypto model—mass retail, external-facing gateways, and offshore intermediaries—has evolved into infrastructure that regulators must increasingly reckon with.
Sanctions architecture and the state’s use of Nobitex
Several investigations have sketched out how Nobitex intersects with sanctions policy and external finance. In January 2026, Elliptic published a report detailing systematic purchases of the U.S. dollar-pegged stablecoin USDT by Iran’s central bank. The firm documented at least $507 million in such purchases conducted through a UAE broker, with assets reportedly routed to Nobitex and converted into Iranian rial liquidity. The arrangement suggests an end-run around conventional foreign-exchange channels, leveraging stablecoins to inject dollars into the domestic economy through a sanctioned intermediary.
Separately, Reuters traced Nobitex back to influential Iranian families, including the Kharrazi clan, and noted that one of the early Nobitex investors was Mohammad Baqer Nahvi, a former official tied to Safiran Airport Services and placed on the OFAC SDN List in 2022 for facilitating drone-related shipments. These connections fuel scrutiny of Nobitex as more than a market operator; for some observers, the platform sits at the intersection of political power and financial access.
The platform has also attracted attention for its technical and compliance footprint. Leaked materials in 2025 suggested Nobitex’s internal code contained modules intended to bolster stealth transactions, endpoint switching, and compliance evasion. A document titled “Nobitex Privacy” outlined strategies aimed at evading U.S. FinCEN and Western blockchain-analytics tools. Such material reinforces perceptions that Nobitex was engineered—at least in some respects—to function under sanctions-era constraints.
And the public record of sanctions enforcement adds nuance to Nobitex’s status. The U.S. Treasury has sanctioned Iran-linked exchanges in the past, including instances where platforms operated from overseas. Yet Nobitex is incorporated in Iran, and its core user base resides there, complicating the enforcement calculus. OFAC has clarified that Iranian digital asset exchanges are treated as blocked financial institutions irrespective of individual SDN designation, a stance that carries significant implications for any foreign counterparties seeking to transact or list Iranian-driven assets.
The broader enforcement framework is not limited to named entities. OFAC’s published FAQs note that sanctions goals can be achieved through targeting specific addresses, designating exchange houses, or naming individuals and OTC brokers. The result is a multidimensional approach where a domestic exchange can be affected not only by direct restrictions but also by the risk posture of foreign banks, stablecoin issuers, and other transactional intermediaries. In Nobitex’s case, some observers argue that a formal SDN listing may offer limited incremental leverage beyond existing restrictions, given that U.S. persons are already prohibited from transacting with Iranian exchanges.
Analysts also consider the human element in sanctions design. Crystal Intelligence’s Nick Smart argues that Nobitex’s user base is heavily concentrated among ordinary Iranians, complicating the decision to isolate the regime from its citizens. This “human shield” concern mirrors broader debates about the social impact of asset freezes, and it contrasts with cases like Garantex—another exchange with a different operational profile that allowed authorities to seize servers with less collateral impact on retail users.
What this means for policy, markets, and the road ahead
The Nobitex narrative sits at a nexus of three ongoing dynamics in crypto regulation and geopolitics. First, sanctions policy is moving from targeting isolated entities to shaping entire market structures. The industry’s experience in Iran, Russia, North Korea, and other jurisdictions shows that what began as experimental financial maneuvers have matured into state-aligned economic strategies. Chainalysis has described this shift as a pattern of institutionalization, not just episodic enforcement.
Second, the question of how best to apply pressure remains unsettled. Isolating a local platform through a targeted SDN listing the most effective means to choke off “exits” like stablecoins and cross-border flows, or would broader action against offshore intermediaries be more impactful? The answer may depend on the ability of regulators to coordinate with foreign entities and on whether a platform like Nobitex is treated as a domestic utility or as a strategic choke point for external finance.
Finally, the Nobitex case underscores a practical tension for investors and builders in crypto markets: sanctions-driven adoption, resilience, and risk. For users inside Iran, crypto provides a degree of inflation protection and external liquidity, but the same infrastructure can be repurposed for currency interventions and regional proxy transfers. For international participants, the case highlights the importance of robust due diligence, counterparty risk assessment, and compliance frameworks when engaging with platforms tied to politically sensitive jurisdictions.
Looking ahead, observers will watch how U.S. policymakers recalibrate their approach to Iranian crypto markets. Will the authorities move to extend SDN designations to newly prominent platforms, or will they sharpen enforcement around exits and stablecoin flows to minimize collateral damage to ordinary users? The answer could shape not only Nobitex’s trajectory but the broader balance between sanctions efficacy and the unintended consequences for millions of ordinary Iranians who rely on crypto for access to global liquidity.
As regulators and market participants digest these developments, the central question remains: where does the line lie between pressuring regime finance and preserving the financial agency of everyday users? The answer will unfold in the next rounds of sanctions policy, enforcement actions, and the evolving architecture of Iran’s crypto economy.
Crypto World
How Iran’s biggest crypto exchange stays off the OFAC blacklist
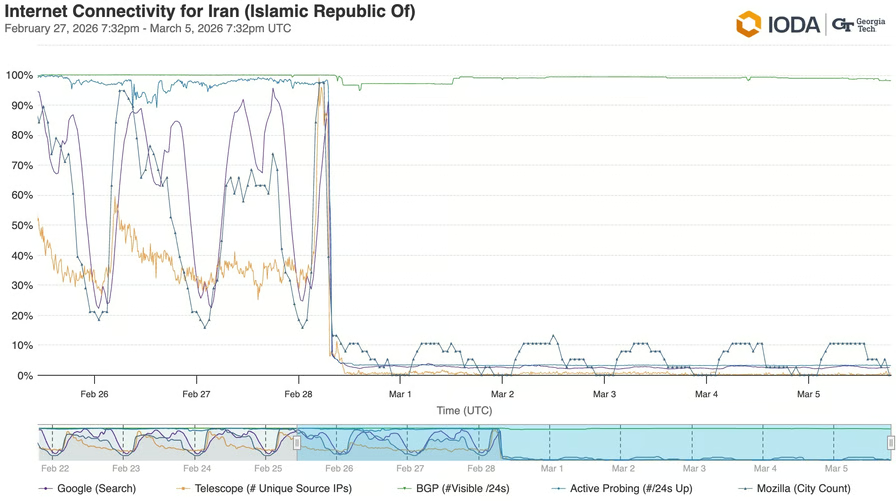

Iran’s internet formally remained part of global routing, but user activity fell almost to zero. That points to a managed restriction on citizens’ access to the external network. Source: IODA.
But in that digital darkness, one vital financial service continued to operate without interruption: Nobitex, a cryptocurrency exchange linked to Iran’s ruling elite.
We compiled the available information about the platform and tried to understand how Iranian authorities use it, what investigations by analytics firms have revealed, and why, despite all these findings, the exchange is still not on OFAC’s SDN List.
The scale and scope of Iran’s crypto giant
Nobitex is far from a niche platform. While estimates vary, analysts agree that the asset flows moving through the exchange are measured in the billions of dollars. For instance, TRM Labs recorded an observed volume of approximately $5 billion between 2025 and March 2026.

Earlier, Chainalysis noted that asset inflows to Nobitex addresses exceeded the combined figure for Iran’s 10 other largest exchanges. Source: Chainalysis.
Nobitex has an extensive retail user base. According to the platform’s own figures, it serves about 11 million Iranians — almost 12% of the country’s population.
The exchange offers a suite of services typical for the industry: spot and margin trading, yield-bearing products, liquidity pools, digital gift cards, and even crypto-collateralized lending.
Nobitex also caters to professional market participants and institutional players. These entities are provided with specialized terms, such as increased limits and high-speed APIs.
What drew attention to the platform, however, wasn’t its retail operations. It was information suggesting Nobitex functions as a national currency gateway for a country cut off from SWIFT.
Shadow banking network
A series of investigations available online focus on how Nobitex helps the Iranian leadership evade economic sanctions.
In January 2026, Elliptic published a report detailing systematic purchases of the USDT stablecoin by Iran’s central bank. According to the company, transactions totaling at least $507 million were carried out through a broker in the UAE, with the assets sent “primarily” to Nobitex.
Since the stablecoins could be sold for rials, the regulator was effectively carrying out a foreign exchange intervention outside the international banking system.
This is far from the only use case for the exchange by the state. A recent Reuters investigation linked the platform’s founders — brothers Ali and Mohammad Kharrazi — to one of the country’s most influential political and clerical families.
The agency also established that one of the largest early investors in the exchange was Mohammad Baqer Nahvi, vice president of Safiran Airport Services — a company placed on the OFAC SDN List in September 2022 for organizing flights to supply Iranian drones to Russia.
Separately, Elliptic and Chainalysis have documented Nobitex’s links to wallets associated with Hamas, the Houthi Ansar Allah movement, the propaganda outlet Gaza Now and the sanctioned Russian exchange Garantex.
The exchange itself appears to have built its infrastructure from the outset for operating under sanctions.
In June 2025, the platform’s source code and portions of its internal documentation were leaked online. According to this data, the code contained modules for generating stealth addresses, transaction batching and splitting, endpoint switching, and specific logic designed to bypass compliance checks. A document titled “Nobitex Privacy” was also made public, explicitly describing a strategy to evade FinCEN tools and Western blockchain analytics.
Half measures or strategic restraint?
In April 2026, reports surfaced that Iranian entities were charging vessel operators fees in cryptocurrency for unobstructed passage through the Strait of Hormuz. Cryptocurrency has reportedly become one of the primary payment options for these transactions.
The practice appears to have been quite successful, suggesting that digital assets will continue to be used for similar purposes.
Against this backdrop, adding Nobitex to the SDN List by analogy with Garantex may seem like a logical step, even though such flows usually don’t pass through retail platforms. Yet that hasn’t happened.
The U.S. Treasury Department has previously sanctioned Iran-linked cryptocurrency exchanges, but those platforms were registered in the United Kingdom. Nobitex, by contrast, is incorporated in Iran as a purely local company.
Crucially, on the same day Reuters published its investigation into Nobitex, OFAC clarified that Iranian digital asset exchanges are already considered blocked financial institutions, regardless of whether they are individually named on the SDN List.
For a platform physically based in Iran, however, this has little practical effect: its core operations revolve around Iranian users and neutral foreign intermediaries.
An SDN listing functions differently. It triggers secondary sanctions against any non-U.S. counterparties worldwide, provides direct justification for bulk asset freezes by stablecoin issuers, and compels foreign exchanges and OTC desks to sever ties or risk being designated themselves.
Why an individual SDN listing may be redundant
The U.S. Treasury has not explained why an individual SDN listing for Nobitex has not followed. However, it is worth noting that the department has never added platforms incorporated within Iran to the list — and there are several of them.
OFAC’s strategy toward Iran’s local crypto market is built around targeted measures. Three main approaches stand out:
- Sanctions against specific addresses.
- Designation of exchange houses — a recent example being the addition of exchanges allegedly servicing the state’s shadow oil revenues.
- Designation of individuals and OTC brokers.
When it comes to Nobitex itself, any explanation can only be speculative. The first has already been outlined: OFAC employs a different strategy toward local Iranian platforms, and Nobitex simply falls within that logic rather than outside it.
The U.S. Treasury may also consider such measures redundant. As previously noted, U.S. persons are already prohibited from transacting with Iranian exchanges; from the standpoint of formal access, an individual listing adds little to existing restrictions.
There is also the “human shield” hypothesis. Speaking to Reuters, Nick Smart, Chief Intelligence Officer at Crystal Intelligence, noted that the platform hosts a high concentration of activity from ordinary Iranians. He suggested that separating the regime from the citizens using the exchange is nearly impossible, as their assets are commingled.
In this context, the Garantex case looks like the opposite scenario: the platform operated as a B2B hub for shadow capital. That made it possible to physically seize its servers without causing social damage to retail users.
There is no direct public confirmation that this is the logic holding OFAC back.
Finally, a strike against Nobitex may be viewed as less effective without a simultaneous move against external “exits.” The value of sanctions arises not at the “entry point,” but where funds leave the country: foreign exchanges, stablecoin issuers, OTC brokers, banks, and other intermediaries.
The double-edged sword
The Nobitex case is another reminder that the mass adoption the industry dreams of is a double-edged sword.
On one hand, the exchange gives Iranians cut off from the world a measure of financial freedom: a way to shield savings from rial inflation and retain at least some access to dollar liquidity. On the other, the state uses the same infrastructure for its own purposes, ranging from central bank currency interventions to transfers to regional proxies.
The key point is that this is no longer an isolated practice. Chainalysis places Iran alongside Russia and North Korea, noting that for all three states, “what were once experimental and opportunistic tactics have matured into institutionalized strategies embedded within national economic and security policy.”
The Iranian model — a mass retail platform based in an unreachable territory coupled with offshore proxy structures — looks like a working template. Future sanctioned regimes will likely look to this experience.
That raises a reverse question — this time for regulators themselves.
What is the acceptable cost of sanctions pressure when the regime’s funds and the savings of millions of ordinary users are physically commingled on a single platform? Can the assets of 11 million people be frozen to cut off the state’s financial channel — or is that precisely the line the SDN mechanism, in its current form, does not cross?
OFAC has yet to provide a public answer, and the Nobitex case only sharpens the debate.
Crypto World
Trump Media’s Q1 loss widens to $406 million on bitcoin, CRO markdowns


Trump Media & Technology Group (DJT) reported a $405.9 million first-quarter net loss on $871,200 in revenue, widening from $31.7 million a year earlier as unrealized losses on its crypto holdings weighed on results.
The parent company of Truth Social booked $244 million in unrealized losses on its cryptocurrency holdings. It also recorded a $108.2 million investment loss tied mostly to equity securities.
Trump Media held 9,542.16 bitcoin at the end of March, with a cost basis of $1.13 billion and a fair value of $647.1 million, the firm wrote in a filing with the SEC. That position is now worth around $770 million.
The company also held 756.1 million with a cost basis of $113.9 million and a fair value of $53 million. Trump Media closed the purchase of $105 million in CRO last year as part of a Crypto.com deal that tied the token to Truth Social and Truth+ rewards.
Trump Media reported $17.9 million in operating cash flow for the quarter, helped by the sale of previously purchased put options on pledged bitcoin and bitcoin-related securities.
A portion of the firm’s bitcoin is locked up. Trump Media said 4,260.73 BTC, worth $289 million at quarter-end, served as collateral for convertible notes.
DJT also held covered call options on 4,000 BTC with a counterparty to hedge its exposure to the cryptocurrency’s volatility. Those options require 2,000 BTC to be held as collateral with the counterparty.
The company raised $2.5 billion for a bitcoin treasury strategy last year, then disclosed a $2 billion bitcoin stack in July.
Revenue rose 6% from $821,200 a year earlier. Media revenue was $810,100, while Truth.Fi generated $61,100 in management fees tied to ETF offerings.
Crypto World
Sports betting should be regulated as a financial product, not gambling, aspiring prediction market provider says


MIAMI BEACH, Fla. — Sports betting should be regulated as a federal financial product rather than a state-licensed casino product, two panelists said Thursday.
Appearing at Consensus Miami 2026, Jacob Fortinsky, co-founder and CEO of sports betting platform Novig, said the legacy sportsbook model is structurally broken because it treats winning bettors as cheaters.
“Sports betting is really the only industry in the country that regularly limits and bans their power users,” Fortinsky said. He framed sports event contracts as binary financial instruments that “for so long have been treated as a gambling product and instead should really be treated as a financial product.” Globally, he said, sports betting is “a $2 trillion asset class still dominated by these legacy casinos.”
Adam Mastrelli, founder of 57 Maiden, a firm that builds AI-driven trading strategies for prediction markets, validated the critique with personal experience.
“My partner and I got kicked off of two big sportsbooks within two months of trading because we were sharp,” he said, It’s like “LeBron James getting kicked out of the NBA for being too good,” he added.
Mastrelli said the team turned to Novig, which he said charges no fees and allows traders to create synthetic positions.
Mastrelli said his firm’s edge decayed quickly, and of 154 proposed trading strategies, only three currently run profitably.
“This edge will go away,” he said, “so if you can build systems that can keep up with that edge and that alpha… then it becomes really, really intriguing.” His most profitable season, he said, was the WNBA.
Fortinsky said Novig is on track to transition this summer from a sweepstakes model live in 35 states to a federal DCM framework that will let it operate in all 50 states. An earlier attempt to be regulated at the state level in Colorado, he said, was a wake-up call. “Regulators told us essentially you’re naive if you think we care about consumer protection or innovation or market efficiency. We really just care about our tax revenue,” he said.
The federal-state fight, Fortinsky added, is “going to get to the Supreme Court in the next two or three years,” with 15 pending lawsuits between the Commodity Futures Trading Commission, Kalshi, Robinhood and various states. Within prediction markets, he argued sports is “counterintuitively actually the safest vertical,” given the bigger insider-trading and manipulation concerns around political and event-driven contracts.
Mastrelli, who said he avoids offshore platforms entirely, compared prediction markets to equities exchanges: “When I see a robust equities market now, this is AQR against SIG. It doesn’t go away.”
Crypto World
2017 Linux flaw resurfaces as a risk to crypto infrastructure

The Linux bug nicknamed Copy Fail is drawing heightened attention from cybersecurity authorities, government agencies and the crypto sector. Described as a local privilege-escalation flaw, Copy Fail could let an attacker with basic user access gain full root control on affected systems. The issue has earned a place in the Cybersecurity and Infrastructure Security Agency’s Known Exploited Vulnerabilities catalog, signaling a high-priority risk for organizations worldwide. Given how deeply Linux underpins crypto infrastructure—from exchanges and custody platforms to validators and node operators—a kernel-level vulnerability of this kind threatens to ripple through the ecosystem even though the flaw does not target blockchain protocols directly.
Security researchers from Xint.io and Theori identified Copy Fail, which hinges on a logic error in how the Linux kernel handles memory operations within its cryptographic subsystems. In pragmatic terms, a regular user could manipulate the kernel’s page cache—the temporary storage the system uses to speed up file I/O—to escalate privileges. What makes this flaw particularly alarming is how accessible the exploit appears to be: a compact Python script can trigger the vulnerability with only modest modifications, enabling root access on many Linux installations. Researcher Miguel Angel Duran has highlighted that the exploit can be demonstrated with roughly 10 lines of Python code on affected machines.
Key takeaways
- Copy Fail (CVE-2026-31431) is a local privilege-escalation vulnerability affecting many mainstream Linux distributions released since 2017, not a remote-exploit against blockchain protocols.
- A working proof-of-concept exploit is publicly available, increasing the risk of rapid exploitation after the initial foothold.
- The flaw stems from how the kernel manages its page cache during memory operations, allowing basic users to gain root control on vulnerable systems.
- Crypto infrastructure—validators, nodes, exchanges, custody services and cloud-based trading—could face indirect but serious consequences if attackers compromise underlying Linux servers.
Copy Fail: how the exploit works and why it matters for crypto
Root access in a Linux server equates to the “master key” to the machine. With it, an attacker can install or remove software, view or exfiltrate sensitive data and reconfigure protections, potentially turning off monitoring tools or altering security settings. Copy Fail exploits a flaw in the kernel’s handling of the page cache, a fast-access memory area used to accelerate file operations. By manipulating cached data under specific conditions, an attacker can bypass intended permission checks and elevate privileges.
The exploit is not a remote attack. A target must already be reachable—via phishing, compromised credentials or another initial access vector—before privilege escalation can occur. Once foothold is established, the attacker can expand control across the host and, in the context of crypto operations, threaten custodial wallets, hot nodes, and trading or node-management infrastructure.
The crypto industry’s dependence on Linux is wide-ranging. Validators and full nodes rely on Linux-based servers; mining operations and pools run on Linux ecosystems; centralized and decentralized exchanges depend on Linux-driven backend stacks; custodial services and wallet infrastructure are Linux-backed; and cloud-based trading systems often sit upon Linux infrastructure. A kernel vulnerability that enables rapid, broad privilege escalation thus carries outsized risk for operational continuity and key security.
Public commentary and analyses emphasize several factors that compound the risk: the flaw affects a broad set of distributions, a working PoC is publicly available, and the vulnerability has persisted in kernels going back to 2017. As security firms and researchers underscore, once exploit code circulates, threat actors can quickly identify unpatched hosts for exploitation. The timing also matters: disclosures arrive as the cybersecurity community increasingly examines how artificial intelligence can accelerate vulnerability discovery and weaponization.
AI, vulnerability discovery and crypto’s exposure
The Copy Fail disclosure arrives amid a broader push to incorporate artificial intelligence into vulnerability research. Initiatives like Project Glasswing, backed by a coalition including Amazon Web Services, Anthropic, Google, Microsoft and the Linux Foundation, highlight a trend where AI tooling is rapidly improving at identifying and instrumenting weaknesses in code. Anthropic and others have argued that modern AI models can outperform humans in spotting exploitable bugs within complex software, potentially accelerating both offense and defense in cybersecurity.
For the crypto sector, the intersection of AI-driven vulnerability discovery and kernel-level flaws raises red flags. Crypto systems—built on layered open-source technologies and deployed across heterogeneous infrastructures—can be particularly susceptible to AI-enhanced attack patterns. If adversaries combine initial access with quick privilege escalation on Linux-based servers, the knock-on effects could include compromised validators, tainted node operators and disrupted service for exchanges and custodians.
In practical terms, even if a direct blockchain protocol breach is unlikely, the integrity of the underlying systems powering the crypto economy remains a critical concern. Large exchanges and custodial platforms operate at scale on Linux-centric stacks, and a successful, widespread kernel exploit could lead to downtime, credential leakage or wallet exposure—outcomes that would reverberate through trading and settlement services globally.
Defense in depth: practical steps for organizations and users
Addressing Copy Fail requires a coordinated mix of rapid patching, access control and proactive monitoring. The guidance emerging from security briefs points to a structured response for different actors in the crypto ecosystem:
For cryptocurrency organizations and infrastructure teams
- Implement and verify official kernel and system patches as soon as they are released by upstream vendors and distribution maintainers.
- Limit local user accounts and permissions; enforce the principle of least privilege across all Linux hosts.
- Regularly audit cloud instances, virtual machines and physical servers for unusual privilege-escalation activity.
- Improve monitoring for anomalous authentication attempts and privilege escalations; implement robust SSH hardening and key management.
- Review container orchestration, cloud IAM policies and network segmentation to minimize blast radius if a host is compromised.
For everyday crypto users
- Keep operating systems and essential software up to date with the latest security patches.
- Avoid unverified software sources and crypto tooling; prefer hardware wallets for significant holdings.
- Enable MFA wherever possible and isolate high-value wallet activity from routinely used devices.
For node runners, validators and developers
- Prioritize prompt kernel and security updates; subscribe to relevant security bulletins and advisories.
- Audit container environments, orchestration tools and cloud permissions for over-privileged configurations.
- Enforce the minimum viable privileges for administrators and ensure robust change controls around critical systems.
What to watch next and why it matters
The Copy Fail disclosure reinforces a broader truth: the security of crypto systems is as much about the integrity of the operating environment as it is about protocols, keys and consensus. While the vulnerability does not directly attack blockchain networks, its potential to destabilize the servers and services that support crypto ecosystems makes urgent patching and hardening essential. As AI-driven tools reshape vulnerability discovery, readers should expect rapid cycles of disclosure and remediation, making timely updates and vigilant security hygiene more important than ever for exchanges, validators and users alike.
Looking ahead, market participants should monitor how major Linux distributions respond, the pace of patch deployment across exchanges and custodians, and any changes in incident response practices within the crypto infrastructure community. If threat actors begin exploiting Copy Fail at scale, the next few quarters could test the resilience of large-grade crypto operations and highlight the ongoing need for defense-in-depth in both software supply chains and operational security. For now, the focus remains clear: patch early, monitor closely and assume that privileged access, once obtained, can rapidly cascade unless defenses hold firm.
Sources and related context include official sector advisories and technical analyses from security researchers and industry researchers, with updates referenced from CISA’s KEV catalog and reporting on the Copy Fail vulnerability, public PoCs, and AI-assisted vulnerability research initiatives.
Crypto World
Crypto industry cheers Senate Clarity Act markup date as market structure push resumes


The Senate Banking Committee will meet on Thursday, May 14, to consider the Digital Asset Market Clarity Act of 2025, putting the crypto market structure bill back on the calendar after a January postponement.
The notice follows months of talks over regulatory jurisdiction, consumer protections, developer protections and stablecoin rewards. CoinDesk reported last week that crypto firms had backed a stablecoin yield compromise meant to unlock the bill.
Cody Carbone, CEO of The Digital Chamber, said the notice marks “a major step” toward clarity for more than 70 million Americans who use cryptocurrencies..
Blockchain Association CEO Summer Mersinger called the markup notice “an important step toward establishing clear rules for digital asset markets.”
“This work reflects months of serious engagement on difficult questions, from SEC-CFTC jurisdiction to consumer protection and developer protections,” Mersinger said. “Clear statutes are what American consumers, businesses, and innovators deserve.”
Kristin Smith, president of the Solana Policy Institute, called the markup “a make or break moment for American leadership in financial markets.” Miller Whitehouse-Levine, the group’s CEO, said the date is “the first step” toward giving builders and financial institutions certainty to build onchain in the U.S.
Ji Hun Kim, CEO of the Crypto Council for Innovation, said “the momentum is real, and the time is now.” The markup, he said, brings the U.S. closer to a framework that safeguards consumers, gives investors clear disclosures, protects developers and supports responsible innovation.
The markup gives Senate Banking another shot at moving the bill before the White House’s July 4 target for Clarity Act passage.
Though the crypto industry is cheering the hearing date, the banking industry said it still has concerns.
A joint letter addressed to Senate Banking Committee leaders Tim Scott and Elizabeth Warren from a coalition of banking trade associations said that they still had some concerns with the bill, proposing edits to the text of the legislation.
Crypto World
Nvidia (NVDA) vs AMD: AI Chip Stocks Face Off in 2025
Key Takeaways
- Nvidia achieved $215.9 billion in fiscal 2026 revenue, marking a 65% year-over-year surge
- The Data Center division at Nvidia delivered $193.7 billion throughout the fiscal year
- AMD’s full-year 2025 revenue reached $34.6 billion, with Data Center sales climbing 32% to $16.6 billion
- Nvidia’s Data Center business exceeds AMD’s by more than 11-fold
- Export restrictions on AMD’s MI308 GPU resulted in $440 million in charges
The artificial intelligence chip sector features two heavyweight competitors in Nvidia and AMD, yet recent financial disclosures reveal a significant gap in their operational scale.
For fiscal 2026, Nvidia announced revenue totaling $215.9 billion. This represented a 65% jump compared to the previous fiscal period. The company maintained a gross margin of 71.1%.
The fourth quarter performance alone delivered $68.1 billion in top-line results. Within that timeframe, Data Center operations contributed $62.3 billion.
Across the entire year, Nvidia’s Data Center division produced $193.7 billion in revenue. This segment has evolved into the company’s primary engine, fueled predominantly by artificial intelligence infrastructure investments from major cloud providers and tech giants.
Nvidia’s business model extends beyond silicon. The company provides an integrated ecosystem encompassing accelerators, networking equipment, complete systems, and proprietary software platforms. This comprehensive approach creates significant switching barriers for enterprise customers.
The primary vulnerability for Nvidia lies in customer concentration. A substantial portion of revenue derives from a narrow window of heavy capital expenditure by hyperscale data center operators. Any deceleration in this investment wave could materially impact financial performance.
AMD’s Financial Performance
AMD disclosed full-year 2025 revenue of $34.6 billion. The Data Center division contributed $16.6 billion, representing 32% growth versus 2024. This expansion was fueled by EPYC server CPU sales and Instinct AI accelerator deployments.
Advanced Micro Devices, Inc., AMD
During the fourth quarter, AMD reported a 54% gross margin alongside $1.8 billion in operating income and $1.5 billion in net income.
While these figures demonstrate strength, Nvidia’s yearly Data Center revenue still dwarfs AMD’s by more than 11 times. This disparity underscores how nascent AMD’s position remains in the AI infrastructure landscape.
AMD doesn’t require dominance over Nvidia to achieve substantial growth. Even modest market share gains in server processors and AI accelerators can generate significant revenue increases.
However, challenges persist. AMD absorbed approximately $440 million in charges throughout fiscal 2025 stemming from U.S. export restrictions affecting its MI308 data-center GPU.
This development highlights both regulatory exposure and the difficulty of eroding Nvidia’s entrenched market leadership.
Wall Street Perspective
Analyst sentiment favors both stocks, though Nvidia commands stronger conviction. MarketBeat data shows 54 analysts following Nvidia with a Buy consensus. The breakdown includes 48 buy ratings, 4 strong buys, and 2 hold ratings. The consensus 12-month price target stands at $275.25.
AMD draws attention from 40 analysts with a Moderate Buy rating. This comprises 1 strong buy, 31 buys, and 8 holds. The average price target reaches $296.44.
Nvidia’s more bullish consensus rating mirrors its commanding market position and superior profit margins.
Interestingly, AMD’s average price target of $296.44 exceeds Nvidia’s $275.25 target. This implies analysts perceive greater potential appreciation from AMD’s current valuation, despite Nvidia’s superior operational metrics.
Crypto World
It might be too late for bitcoin’s quantum migration, Project Eleven report argues
More than $3 trillion in digital assets could eventually become vulnerable to theft within the next four to seven years, according to a new report from Project Eleven.
Project Eleven focuses on post-quantum security and migration for digital assets and recently announced a collaboration with the Solana Foundation to prepare its network against the threat of quantum computing.
“The digital asset industry holds over $3 trillion in aggregate value, and virtually all of it is secured by the same class of cryptographic primitive: elliptic curve digital signatures,” which are vulnerable to quantum computing attacks, the report said.
But it is not only crypto that is at stake here. The report states that the same public-key cryptography security used by bitcoin, ether and stablecoins also underpins banking systems, cloud infrastructure, authentication networks and military communications.
The 110-page report by Project Eleven, whose CEO Alex Pruden was on stage at Consensus Miami 2026, also states that sufficiently powerful quantum computers could use Shor’s algorithm to derive private keys from public keys, allowing attackers to forge signatures and take over control of wallets and digital accounts secured by the elliptic curve cryptography.
This means blockchains, banking infrastructure, cloud systems, military comms and other digital identity systems are also vulnerable, not just bitcoin, ethereum, stablecoins, and other blockchains, the report emphasizes.
Project Eleven says a “Q-Day” scenario, the arrival of cryptographically relevant quantum computer cable of breaking widely used public-key cryptography, could be as early as 2030, no later than 2033.
“Our analysis suggests that, based on current trends, Q-Day is more likely to occur than not by 2033, and potentially even as soon as 2030,” the report reads. “The window for the world to migrate to post-quantum cryptography is narrowing.”
And here is why it is becoming so complicated, the report explains: large systems often take between five to more than 10 years to migrate, depending on how complex their networks are.
Another difficult challenge is how the transition actually takes place, as migrating all quantum vulnerable systems and blockchains to secure networks involves a process that requires a coordinated, simultaneous transition from all users, exchanges, custodians, wallet providers and miners.
Read more: To freeze or not to freeze: Satoshi and the $440 billion in bitcoin threatened by quantum computing
“The gap is not technical,” the report says. “The gap is entirely coordination, urgency, and willingness to accept the costs of migration.”
When it comes to Bitcoin, things get even more complicated because upgrades historically move slowly and often become politically contentious.
“The Bitcoin SegWit upgrade — a relatively modest change compared to PQC migration — took over two years from proposal to activation (2015-2017) and triggered a contentious chain split,” the report recalled.
Read more: What the Fork? Why Bitcoin Tech Changes Impact Price
“The distributed nature of blockchain networks means that migration to post-quantum cryptography may take the better part of a decade, longer than other centralized systems.”
Pruden, who authored the report along with CTO Conor Deegan, warned that Bitcoin’s migration to post-quantum cryptography could prove even harder than Taproot because it would require coordinated action across users, exchanges, custodians and miners. He also said he personally leaned toward “recycling” the 5.6 million to 6.9 million vulnerable BTC tokens, worth up to roughly $500 billion at current prices back into the bitcoin’s supply curve rather than allowing a quantum attacker to eventually sweep them.
The report by Pruden’s Project Eleven ultimately acknowledges that the issue creates tension between bitcoin’s fixed-supply ethos and its commitment to property rights.
Read more: Bitcoin’s quantum debate splits as Adam Back pushes optional upgrades over forced freeze
Crypto World
Why a 2017 Linux bug is now a major concern for the crypto industry

1. Copy Fail: The Linux vulnerability affecting crypto infrastructure security
A recently uncovered security flaw in Linux is drawing concern from cybersecurity specialists, government agencies and the cryptocurrency sector. Codenamed “Copy Fail,” the vulnerability affects many popular Linux distributions released since 2017.
Under specific circumstances, the flaw could let attackers escalate privileges and gain full root control of affected machines. The Cybersecurity and Infrastructure Security Agency (CISA) has added the issue to its Known Exploited Vulnerabilities catalog, highlighting the serious threat it poses to organizations worldwide.
For the crypto industry, the implications go well beyond a standard software bug. Linux powers much of the underlying infrastructure for exchanges, blockchain validators, custody solutions and node operations. As a result, an operating system-level vulnerability could create significant disruptions across large parts of the cryptocurrency ecosystem.
2. What is “Copy Fail”?
“Copy Fail” refers to a local privilege-escalation vulnerability in the Linux kernel, identified by security researchers at Xint.io and Theori.
In simple terms, it allows an attacker who already has basic user-level access on a Linux system to elevate their permissions to full administrator or root control. The bug stems from a logical error in how the kernel handles certain memory operations within its cryptographic components. Specifically, a regular user can influence the page cache, the kernel’s temporary storage for frequently accessed file data, to gain higher privileges.
What stands out about this vulnerability is how easy it is to exploit. A compact Python script, requiring minimal changes, can reliably trigger the issue across a wide range of Linux setups.
According to researcher Miguel Angel Duran, it only requires roughly 10 lines of Python code to gain root access on affected machines.

3. Why this vulnerability stands out as particularly risky
Linux security issues range from highly complex attacks that require chained exploits to simpler ones that need just the right conditions. “Copy Fail” has drawn significant attention because it requires relatively little effort after an initial foothold.
Key factors contributing to the vulnerability include:
- It affects most mainstream Linux distributions.
- A working proof-of-concept exploit is publicly available.
- The issue has existed in kernels going back to 2017.
This mix makes the vulnerability more concerning. Once exploit code circulates online, threat actors can quickly scan for and target unpatched systems.
The fact that such a critical flaw stayed hidden for years underscores how even well-established open-source projects can contain subtle vulnerabilities in their foundational code.
Did you know? The Bitcoin white paper was released in 2008, but Linux dates back to 1991. That means much of today’s crypto infrastructure is built on software foundations older than many blockchain developers themselves.
4. How the “Copy Fail” exploit works
It is important to first understand what full “root” control means on a Linux server. Root access is essentially the highest level of authority over the machine.
With it, an attacker could:
- Add, update or delete any software
- View or steal confidential files and keys
- Modify critical system settings
- Access stored wallets, private keys or authentication credentials if they are present on the affected system
- Turn off firewalls, monitoring tools or other defenses
The exploit takes advantage of how the Linux kernel manages its page cache. The system uses a small, fast memory area to speed up file reading and writing. By abusing how the kernel handles cached file data, an attacker can trick the kernel into granting higher privileges than intended.

Crucially, this is not a remote attack that can be launched from anywhere on the internet. The attacker first needs some form of access to the target machine. For instance, they could gain access through a compromised user account, a vulnerable web app or phishing. Once they have that initial foothold, the attacker can quickly escalate their permissions to full root control.
5. Why this matters for the cryptocurrency industry
Linux is widely used across cloud, server and blockchain node infrastructure, making it important to many crypto operations.
Core parts of the crypto ecosystem run on it, including:
- Blockchain validators and full nodes
- Mining farms and pools
- Centralized and decentralized cryptocurrency exchanges
- Custodial services and hot/cold wallet infrastructure
- Cloud-based trading and liquidity systems
Because of this deep dependence, a kernel-level vulnerability like “Copy Fail” can create indirect but serious exposure across the crypto world. If attackers successfully exploit it on vulnerable servers, the possible consequences include:
- Stealing private keys or administrative credentials
- Compromising validator nodes to disrupt operations or support broader network attacks
- Draining funds from hosted wallets
- Causing widespread downtime or launching ransomware
- Exposing user data stored on affected systems
While the vulnerability does not attack blockchain protocols directly, breaching the underlying servers that support them can still lead to major financial losses, reputational damage and operational disruption.
Did you know? Major crypto exchanges rely on large-scale cloud, server and Kubernetes infrastructure to process trading activity, run blockchain nodes and support market-data operations around the clock. Coinbase, for example, has publicly described infrastructure tied to blockchain nodes, trading engines, staking nodes and Linux production environments.
6. Why initial access still poses a major threat in crypto environments
Some users downplay this vulnerability because it requires a certain level of existing access to the target system. However, most real-world cyberattacks unfold in multiple phases rather than striking all at once.
A typical attack sequence looks like this:
- Attackers first break in using phishing campaigns, leaked passwords or infected applications.
- They secure a basic foothold with ordinary user-level rights.
- They then use flaws like “Copy Fail” to quickly escalate to full administrator privileges.
- From there, they expand their reach across the network.
This pattern is especially dangerous in the cryptocurrency space, where exchanges, node operators and development teams are prime targets for phishing and credential theft. What starts as a minor breach can quickly escalate into a full takeover when reliable privilege-escalation tools are available.
7. Why security teams are particularly concerned
CISA’s decision to include “Copy Fail” in its Known Exploited Vulnerabilities (KEV) catalog signals that the flaw is viewed as a high-priority risk.
Red flags include the public release of working exploit code. As soon as proof-of-concept scripts become widely available, threat actors begin automated scans to look for unpatched systems to target.
Many organizations, particularly in finance and crypto infrastructure, also tend to delay kernel updates. They prioritize system stability and avoid potential downtime or compatibility issues. However, this approach can leave systems exposed for longer during critical vulnerability windows, giving attackers more time to strike.
Did you know? In simple terms, “root access” is like having the master key to an entire building. Once attackers gain it, they can potentially control nearly every process running on the system, change protected files and interfere with core security settings.
8. The AI connection: Why this vulnerability could signal bigger challenges ahead
Copy Fail was disclosed at a time when the cybersecurity world is increasingly focused on the role of artificial intelligence in vulnerability discovery.
The timing coincides with the introduction of Project Glasswing, a collaborative effort backed by leading tech organizations such as Amazon Web Services, Anthropic, Google, Microsoft and the Linux Foundation. Participants in the project have highlighted how rapidly advancing AI tools are becoming better at identifying and weaponizing weaknesses in code.
Anthropic has stressed that cutting-edge AI models are already outperforming many human experts when it comes to finding exploitable bugs in complex software. The company says these systems could greatly speed up both offensive and defensive cybersecurity work.
For the cryptocurrency industry, this trend is particularly concerning. Crypto systems are high-value targets for hackers and are often built on layered open-source technologies, making them potentially more exposed as AI-driven attack methods evolve.
9. What this means for everyday crypto users
For most individual crypto holders, the direct risk from this specific Linux issue remains low. Everyday users are unlikely to be personally singled out.
That said, indirect effects could still reach users through:
- Breaches or downtime at major exchanges
- Compromised custodial platforms holding user funds
- Attacks on blockchain validators or node providers
- Disruptions to wallet services or trading infrastructure
Self-custody users should take note if they:
- Run their own Linux-based blockchain nodes
- Operate personal validators or staking setups
- Maintain crypto-related tools or servers on Linux
Ultimately, this situation highlights an important reality: Strong crypto security is not just about secure smart contracts or consensus mechanisms. It also depends heavily on keeping the underlying operating systems, servers and supporting infrastructure up to date and protected.
10. How to stay protected
“Copy Fail” is a reminder of how quickly underlying operational vulnerabilities can escalate into major security threats in the digital space. The positive side is that most of these risks are manageable. Organizations and users can significantly reduce their exposure by applying security updates promptly, enforcing stricter access controls and maintaining strong overall cybersecurity practices.
For cryptocurrency organizations and infrastructure teams
Companies running Linux-based systems should prioritize these steps:
- Deploy official security patches as soon as they become available
- Minimize and strictly control local user accounts and permissions
- Regularly audit cloud instances, virtual machines and physical servers
- Set up strong monitoring for unusual privilege-escalation attempts
- Strengthen SSH access, key-based authentication and overall login security
For everyday crypto users
Individual holders can lower their exposure by:
- Keeping operating systems and software fully updated
- Avoiding downloads from unverified sources or unofficial crypto tools
- Using hardware wallets for significant holdings
- Enabling multi-factor authentication (MFA) wherever possible
- Isolating high-value wallet activities from everyday computers and browsers
For node runners, validators and developers
Those managing blockchain nodes or development environments should:
- Apply kernel and system updates without delay
- Closely follow Linux security bulletins and advisories
- Review container setups, orchestration tools and cloud permissions
- Limit full administrator rights to the bare minimum
Crypto World
XRP Price Prediction Strengthens After Ripple, JPMorgan, Mastercard Settle First Cross Border Tokenized Treasury on XRP Ledger: Pepeto Holds the Bigger Multiple
The XRP price prediction picked up serious momentum after Ripple, JPMorgan, Mastercard, and Ondo Finance completed the first cross border, cross bank redemption of a tokenized US Treasury fund on the XRP Ledger, as reported by CoinDesk. The pilot settled in under five seconds outside normal banking windows, plugging a public blockchain into JPMorgan’s $3 trillion Kinexys settlement platform.
This is the kind of plumbing that turns XRP from a payments narrative into live institutional infrastructure, with JPMorgan delivering US dollars to Ripple’s Singapore bank in the same flow that cleared the asset side on XRPL.
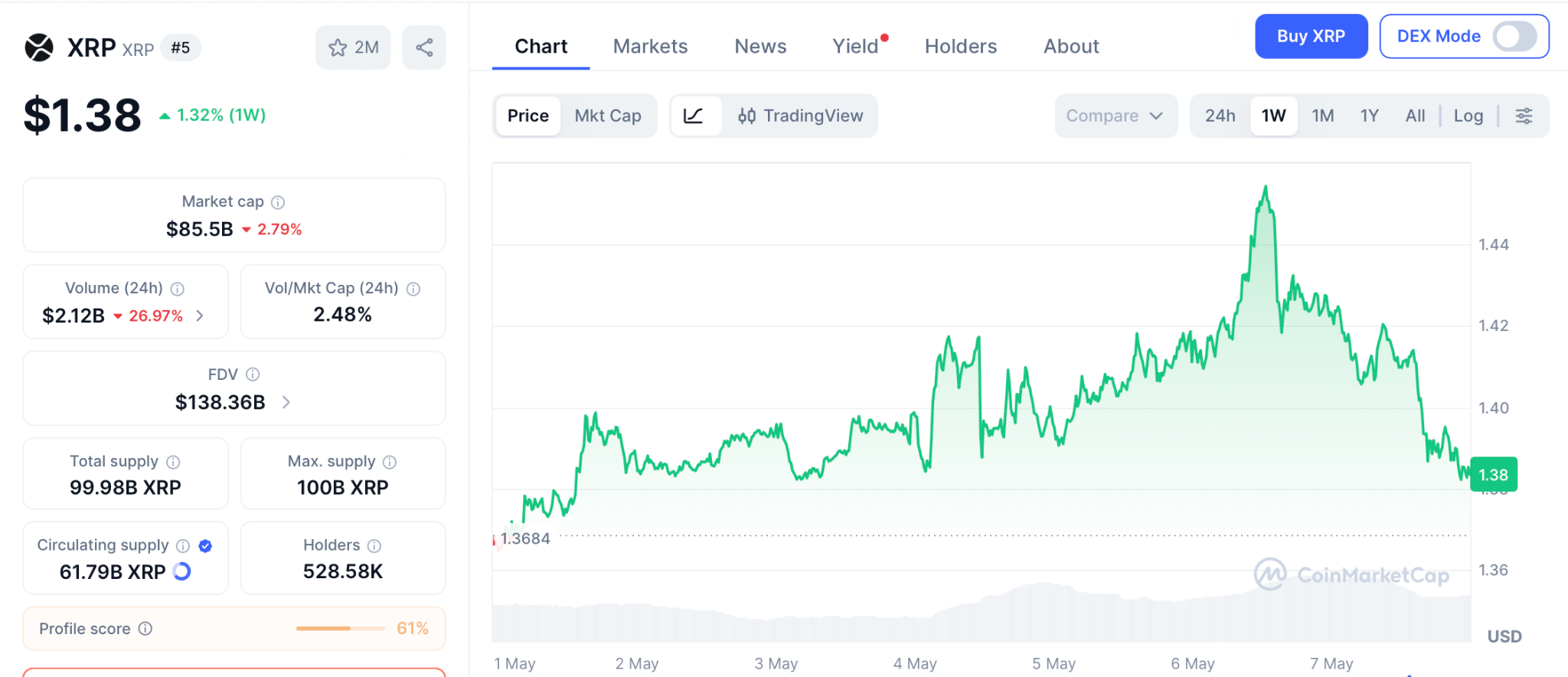
XRP trades at $1.38 today after a 2.34% pullback. While XRP price watchers track whether $1.45 breaks first, Pepeto is drawing capital from wallets that know presale entries reprice the moment a Binance listing arrives. With $9.86 million already raised at $0.0000001869, the math is too clean to ignore.
XRP Price Prediction Gets a Major Boost as Tokenized Treasury Settlement Lands Live on XRPL
The Ondo OUSG redemption used the XRP Ledger as the asset rail, with Mastercard’s MTN routing instructions and JPMorgan delivering dollars across borders. The pilot is the first time a public blockchain and global banking infrastructure handled a cross border tokenized fund redemption as one continuous flow.
XRPL adoption keeps building. RLUSD handled the bridging while a fraction of XRP paid the network fee, which proves what XRP holders always pointed at: when banks plug in, the network underneath gets repriced.
But the XRP price barely moved on the news, up just 1% before pulling back, because an $80 billion network gets revalued slowly.
XRP Price Prediction Versus the Pepeto Setup at Presale Entry
Smart capital does not chase the headline coin. It looks for the next setup that mirrors what worked, and Pepeto is that setup right now, lining up with projects that delivered three figure returns within twelve months of hitting Binance.
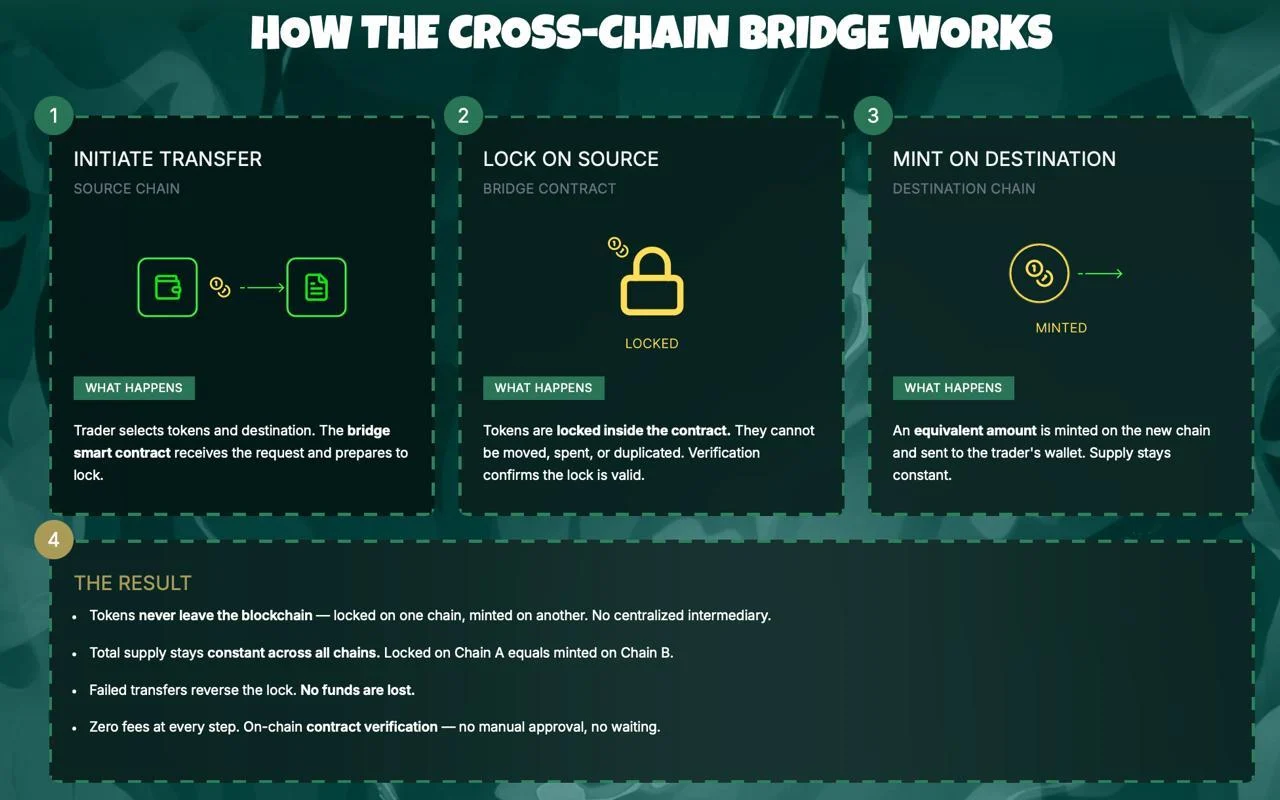
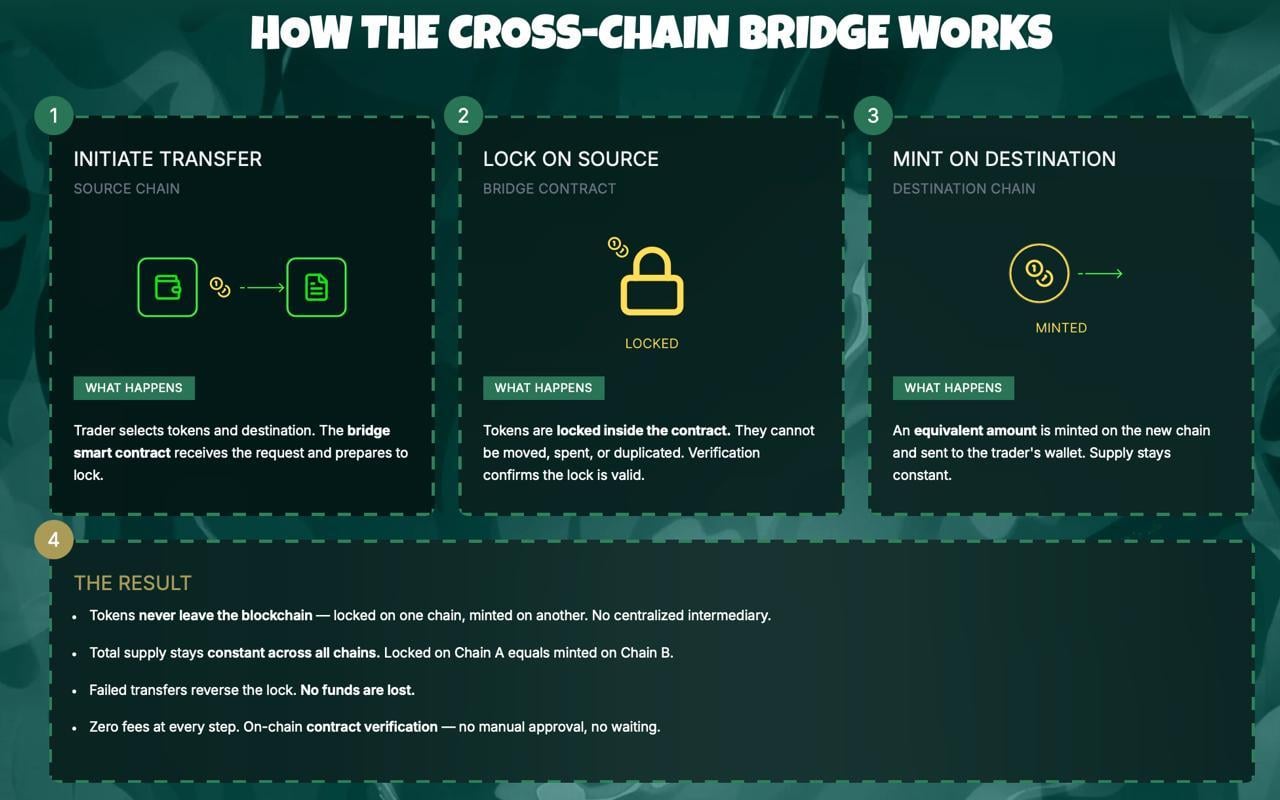
The exchange is already live, with three pieces shipping today instead of sitting in a roadmap. PepetoSwap clears swaps on Ethereum, BNB Chain, and Solana at zero cost so the position lands intact, and the cross chain bridge ships tokens between networks without taking a cut. The contract scanner sits in front of every wallet approval and reads the code first, catching risky approvals at the door instead of after the loss.
The track record turns presale conviction into actual returns. The original Pepe cofounder who pushed a meme launch from zero to $11 billion on a 420 trillion supply leads the build, while a former Binance executive runs the listing path, so the people steering this presale already know how to land a meme token on a tier one exchange.
SolidProof audited the codebase before any dollar entered, $9.86M is locked in, 175% APY staking compounds every position daily, and at $0.0000001869 the entry sits where it does only until the Binance listing flips trading live.
XRP Price Forecast: Where Does XRP Go From $1.38?
XRP trades at $1.38 today per CoinMarketCap, sitting above the $1.40 breakout zone with $1.45 to $1.47 capping upside. The XRP price prediction for 2026 targets $2.80 per Standard Chartered, roughly a 2x from here, with $8 in play if the CLARITY Act passes this summer.
XRP ETF inflows have continued and the JPMorgan settlement deepens institutional confidence, but the move from $1.38 to $2.80 plays out over months, and 2x is not the 100x a presale to listing event delivers.
Conclusion
The XRP price prediction for 2026 keeps strengthening as Ripple, JPMorgan, and Mastercard tie XRPL into live institutional banking, but the early days of XRP returns ended a long time ago. Picture the trader who watched Shiba Inu trade at fractions of a cent and said the entry would be there next month.
Picture the wallet that found Dogecoin in the early rounds and waited one more week before locking in. From $1.38, even the most bullish XRP targets pay a fraction of what those entries delivered, and the same window is open right now on a project that has not seen its first Binance candle.
No other 2026 project combines the Pepe cofounder track record, a working exchange with audited tools, and meme coin energy at presale pricing. The Pepeto page is where this entry stays open until the listing flips live, and once that switch is thrown the wallets reading and waiting are the ones who read about it next month and ask what they were doing today.
Click To Visit Pepeto Website To Enter The Presale
FAQs
What is the XRP price prediction for 2026 after the JPMorgan tokenized treasury settlement?
XRP trades at $1.38 with Standard Chartered targeting $2.80 in the moderate case and $8 if the CLARITY Act passes the Senate. Pepeto at presale targets 100x from one Binance listing.
Why is Pepeto considered the strongest crypto presale right now?
Pepeto is the presale exchange combining zero fee swaps, a cross chain bridge, and an AI risk scanner at $0.0000001869, with $9.86M raised and SolidProof audit complete. The XRP price prediction shows 2x while Pepeto targets 100x on listing day.
Disclaimer: This is a Press Release provided by a third party who is responsible for the content. Please conduct your own research before taking any action based on the content.
-

 Crypto World1 day ago
Crypto World1 day agoHarrisX Poll Found 52% of Registered Voters Support the CLARITY Act
-

 NewsBeat6 days ago
NewsBeat6 days agoChannel 5 – All Creatures Great and Small series 7 new post
-

 Crypto World2 days ago
Crypto World2 days agoUpbit adds B3 Korean won pair as Base token gains Korea access
-
 Tech5 days ago
Tech5 days agoImage AI models now drive app growth, beating chatbot upgrades
-

 News Videos6 days ago
News Videos6 days agoAP Dhillon – Old Money (Official Audio)
-

 Fashion1 day ago
Fashion1 day agoWeekend Open Thread: Marianne Dress
-

 NewsBeat2 days ago
NewsBeat2 days agoNCP car park operator enters administration putting 340 UK sites at risk of closure
-

 Sports7 days ago
Sports7 days agoFive killed in Texas plane crash identified as Amarillo pickleball players
-
Entertainment7 days ago
New Netflix Movies in May 2026 — My Top 3 Picks to Stream
-
Entertainment7 days ago
Anna Nicole Smith’s Daughter Attends 2026 Kentucky Derby
-

 Entertainment7 days ago
Entertainment7 days agoVenus Williams’ Best Met Gala Looks Over the Years
-

 Crypto World7 days ago
Crypto World7 days agoBitcoin mining equities rise in 2026 as BTC lags behind
-

 Entertainment7 days ago
Entertainment7 days agoMelissa Joan Hart and More Stars Attend 2026 Kentucky Derby
-

 Business6 hours ago
Business6 hours agoIgnore market noise, India’s long-term story intact, say D-Street bulls Ramesh Damani and Sunil Singhania
-

 Business7 days ago
Business7 days agoLuka Doncic Injury Update: Doncic’s Hamstring Recovery Slows Lakers’ Hopes Against Thunder: Can He Run Yet?
-

 Sports7 days ago
Sports7 days agoIs Man United v Liverpool on TV? Channel, streaming and how to watch Premier League fixture
-

 Entertainment7 days ago
Entertainment7 days agoNetflix’s 10-Part Miniseries Based on a True Story Is a Perfect Weekend Binge
-

 Business6 days ago
Business6 days agoWinning Numbers Drawn as Jackpot Resets to $20 Million
-
Entertainment7 days ago
“Storage Wars” star Darrell Sheets' ex-wife breaks silence on his death
-

 Crypto World7 days ago
Crypto World7 days agoQ1 2026 Tech Layoffs AI Wave Hits 81,747 as Firms Shift to AI Infrastructure











You must be logged in to post a comment Login