Crypto World
Kaspersky flags RenEngine loader spread via pirated software

Editor’s note: In the ongoing battle against malware, RenEngine’s reach underscores how attackers exploit trusted software channels to broaden their victim base. Today’s briefing from Kaspersky Threat Research highlights a multi-stage infection that pivots beyond gaming into widely used cracked productivity tools. The findings emphasize the importance of verifying software sources and maintaining updated defenses across personal and corporate environments. As cyber threats increasingly blend with legitimate workflows, readers should review security practices, stay vigilant about unofficial installers, and consider how threat actors opportunistically adapt to new distribution methods. This update offers context for executives, IT teams, and security professionals navigating a rapidly evolving threat landscape.
Key points
- RenEngine loader is distributed via dozens of pirated software sites, not just cracked games.
- Final payloads include Lumma, ACR Stealer, and Vidar in various infection chains.
- The distribution pattern is opportunistic and regional rather than targeted.
- The campaign uses Ren’Py-based game installers with fake loading screens to deploy malware
Why this matters
The expansion from gaming to cracked productivity software widens the potential victim pool and raises risk for individuals and organizations. Attackers use multi-stage delivery, anti-analysis checks, and broad distribution to bypass defenses. Organizations should reinforce software provenance checks, user education, and behavior-based detection to identify malicious activity masquerading as legitimate software.
What to watch next
- Watch for new distribution sites or bundles carrying RenEngine via cracked software.
- Monitor for updates from security vendors on HijackLoader-based campaigns across multiple payloads.
- Track any new payload families linked to RenEngine or related loaders.
Disclosure: The content below is a press release provided by the company/PR representative. It is published for informational purposes.
Kaspersky identifies RenEngine loader distributed through pirated games and software
Kaspersky identifies RenEngine loader distributed through pirated games and software
February 23, 2026
Kaspersky Threat Research has revealed its analysis of RenEngine, a malware loader that has recently gained public attention. Kaspersky identified RenEngine samples as early as March 2025, with its solutions already protecting users from the threat at that time.
Beyond the cracked games highlighted in recent reports, Kaspersky researchers discovered that attackers created dozens of websites distributing RenEngine through pirated software, including graphics editors like CorelDRAW. This expands the known attack surface beyond the gaming community to anyone seeking unlicensed software.
Kaspersky has recorded incidents in Russia, Brazil, Turkey, Spain and Germany, among other countries. The distribution pattern indicates opportunistic attacks rather than targeted operations.
When Kaspersky first identified RenEngine, the loader was delivering the Lumma stealer. Current attacks distribute ACR Stealer as the final payload, and Vidar stealer has also been observed in some infection chains.
The campaign exploits modified versions of games built on the Ren’Py visual novel engine. When users launch infected installers, a fake loading screen appears while malicious scripts execute in the background. The scripts include sandbox detection capabilities and decrypt a payload that initiates a multi-stage infection chain using HijackLoader, a modular malware delivery tool.
“This threat extends beyond pirated games — attackers are using the same technique to distribute malware through cracked productivity software, which broadens the potential victim pool significantly.”
— Pavel Sinenko, lead malware analyst at Kaspersky Threat Research
“Game archive formats vary by engine and title. If an engine doesn’t check the integrity of its resources, attackers can embed malware that executes the moment you click play.”
Kaspersky solutions detect RenEngine as Trojan.Python.Agent.nb and HEUR:Trojan.Python.Agent.gen. HijackLoader is detected as Trojan.Win32.Penguish and Trojan.Win32.DllHijacker.
To stay protected, Kaspersky recommends:
- Download games and software only from official sources. Pirated content remains one of the most common malware delivery methods.
- Use a reliable security solution. Kaspersky Premium protects against threats like RenEngine through its Behavior Detection component, which identifies malicious activity even when malware is disguised as legitimate software.
- Keep your operating system and applications updated to ensure known vulnerabilities are patched.
- Be skeptical of “free” offers. If a paid game or software is available for free download on an unofficial site, the cost is likely your security.
About Kaspersky
Kaspersky is a global cybersecurity and digital privacy company founded in 1997. With over a billion devices protected to date from emerging cyberthreats and targeted attacks, Kaspersky’s deep threat intelligence and security expertise is constantly transforming into innovative solutions and services to protect individuals, businesses, critical infrastructure, and governments around the globe. The company’s comprehensive security portfolio includes leading digital life protection for personal devices, specialized security products and services for companies, as well as Cyber Immune solutions to fight sophisticated and evolving digital threats. We help millions of individuals and nearly 200,000 corporate clients protect what matters most to them. Learn more at www.kaspersky.com.
Crypto World
Chainlink’s 86% Correction May Be Over: Here’s Why $100 Could Be Next for LINK

TLDR:
- LINK has corrected over 86% from its 2021 high near $53, now compressing inside a key demand block at $5.60–$7.50.
- CryptoPatel identifies smart money absorption at macro support, with sell-side liquidity sweeps fully absorbed on the 3W chart.
- Three upside price targets are mapped at $26.30, $52.22, and $100, representing up to 1,675% return from the demand zone.
- The bullish setup is invalidated if LINK prints a three-weekly candle close below the critical support level of $4.76.
Chainlink’s native token, LINK, is currently priced around $8.30 after an extended period of price compression. Analyst CryptoPatel has released a high-timeframe technical forecast pointing toward a potential 10x move.
The setup is built on multi-year chart structure and accumulated demand at macro support. With volatility contracting sharply on the three-weekly chart, market participants are watching closely for a breakout confirmation.
LINK Accumulates Inside a Multi-Year Demand Block
LINK has been trading inside a descending channel on the three-weekly chart since its 2021 cycle high near $53. The token corrected more than 86% from that peak over the following years.
Price has since compressed into a demand block between $5.60 and $7.50. This zone is where CryptoPatel identifies strong smart money absorption taking place.
Multiple higher lows have formed within this demand block on the higher timeframe. Each successive low reflects buyers stepping in before price reaches prior lows.
CryptoPatel noted that sell-side liquidity sweeps into this support region have been fully absorbed. That behavior points toward sustained accumulation rather than distribution at current levels.
The analyst’s tweet reads: “Fractal Structure Mirroring Previous Cycle Compression Before Breakout.” This observation draws a direct parallel to prior accumulation phases in LINK’s price history.
Each of those phases was followed by a sharp directional expansion. The current setup carries a structurally similar pattern on the same timeframe.
Volatility on the three-weekly chart has contracted to an extreme degree, according to CryptoPatel. That level of compression typically precedes a larger expansion move in either direction.
Price is currently hovering near $8, described as range equilibrium within the analyst’s framework. The descending channel resistance from the 2021 all-time high remains the defining technical ceiling.
Key Price Levels That Could Trigger a Massive Upside Move
CryptoPatel has mapped out three upside targets: $26.30, $52.22, and $100. A move to the third target from current prices would represent a gain of approximately 1,110%.
The projected total return from the high-timeframe demand zone sits between 1,232% and 1,675%. These targets align with liquidity pools resting above current price on the higher timeframe chart.
The critical confirmation signal for this setup is a three-weekly candle close above the descending trendline resistance. A simultaneous break of the range high on that timeframe would further strengthen the bullish case.
Until that close materializes, the channel resistance remains structurally intact. Traders following this setup are waiting for that specific trigger before adding exposure.
CryptoPatel’s bullish bias holds as long as LINK stays above $4.76 on the three-weekly timeframe. That level marks the lower boundary of the high-timeframe demand zone.
A confirmed candle close below $4.76 would signal structural failure and open the door to further downside. That threshold functions as the hard invalidation point for the entire setup.
The analyst describes this as a high-timeframe, patience-based trade with asymmetric risk-to-reward. It is best suited for spot accumulation and long-term swing positioning, per the forecast.
No macroeconomic or fundamental variables are incorporated into the analysis. Traders are encouraged to conduct independent research before making any financial decisions.
Crypto World
Backpack Offers 20% Equity to Token Stakers Ahead of IPO
Crypto trading platform Backpack Exchange on Monday announced that stakers of its forthcoming Backpack token will be able to earn equity in the exchange, as the company moves toward a potential initial public offering.
“Users that stake the Backpack token for at least a year will have the opportunity to exchange those tokens for equity at a fixed ratio—20% of the company today,” said Backpack CEO and founder Armani Ferrante in a post to X on Monday.
20% of Backpack equity given to users who stake for a year.
Don’t just use the next big thing.
Own it. 🎒 pic.twitter.com/whdGUQ0XyH
— Backpack 🎒 (@Backpack) February 23, 2026
Speaking about the equity offering, Ferrante said many past token launches were built on “false promises” of utility — a pitfall he wanted to avoid. Instead, he said he wanted to offer users an alternative token structure showing long-term commitment.
“I came into crypto because I believe it’s going to change the world … But somewhere along the way, amidst the booms, the busts, the moonshots, the decentralization theater, and the straight up scams, we lost our way. I don’t know about you, but I’m just tired of false promises.”
Backpack’s offer would anchor the token’s value to company equity.
Backpack prioritizes users with tokenomics setup
Backpack first announced it would launch the Backpack token in a post on X earlier this month.
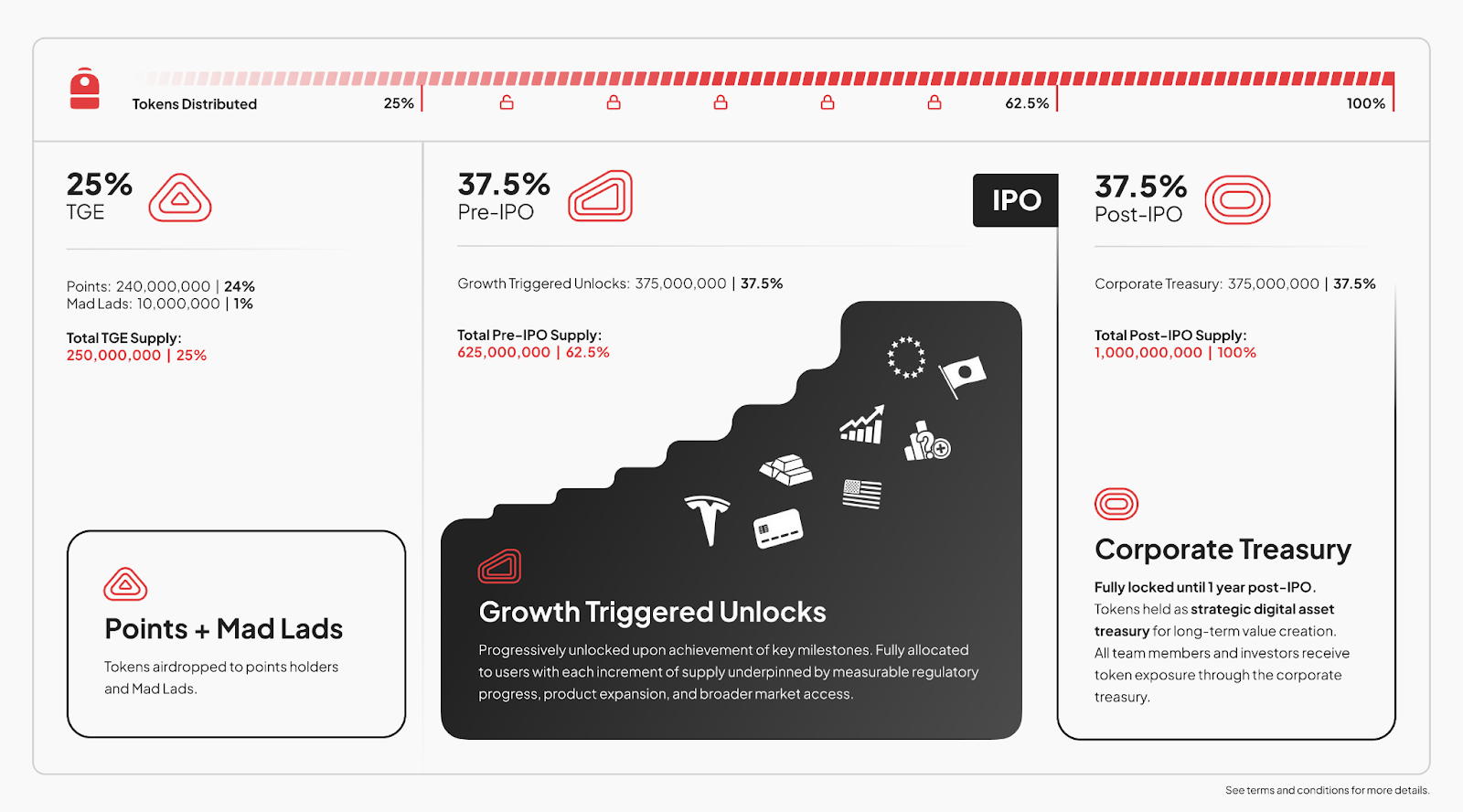
The tokens are intended to be unlocked in stages as the company moves toward a potential US IPO.
Backpack said 25% of the 1 million-token supply will be unlocked at the Token Generation Event, while the next 37.5% of the tokens will be released before the IPO, provided that Backpack reaches certain milestones, such as regulatory approvals and the launch of new products.
The first 62.5% of Backpack tokens will be distributed entirely to users, while the remaining tokens will be unlocked post-IPO for Backpack’s team members and investors.

Backpack said the tokenomics setup aims to invert a model that usually sees insiders receiving large allocations early, with time-based vesting creating predictable sell pressure on retail users who are often left holding the bag.
Backpack was founded in 2022 by Ferrante, who previously worked at the FTX-linked Alameda Research before the two entities collapsed in November of that year.
Related: Kraken acquires tokenization platform Magna ahead of potential IPO
While the Backpack TGE date has not been set, the token-equity announcement comes as Backpack partnered with Securities and Exchange Commission-registered transfer agent Superstate to bring tokenized stocks onchain in October.
Backpack acknowledges its plan isn’t perfect
Ferrante slammed the current state of crypto, stating: “We live in the most centralized era crypto has ever experienced,” and adding: “The more centralized something is, the less meaningful a token is.”
At the same time, Ferrante acknowledged that the token-equity offering would start out relatively centralized but added that plans are in place to progressively decentralize the token as the product evolves.
“I expect the token to represent more than anything a single company has to offer, but in the short run, it’s the best we can do to show our long term commitment to our users.”
Magazine: Bitget’s Gracy Chen is looking for ‘entrepreneurs, not wantrepreneurs’
Crypto World
Tom Lee Bets Big on Ethereum With 51,162 ETH Purchase as Vitalik Buterin Sells $21 Million Worth

TLDR:
- Bitmine acquired 51,162 ETH in a single week, pushing total holdings to 4.42M tokens worth $8.6 billion.
- Vitalik Buterin sold over 9,715 ETH in February 2026, totaling more than $21M as ETH fell below $2,000.
- Tom Lee cited tokenization, AI adoption, and the creator economy as key reasons to buy ETH during the dip.
- Bitmine’s staking operations now generate $171M annually, with projections reaching $249M at full MAVAN scale.
Tom Lee’s Bitmine Immersion Technologies made a bold move last week, acquiring 51,162 ETH amid a broader market pullback.
While Ethereum co-founder Vitalik Buterin was offloading millions in ETH, Lee’s company was buying aggressively.
The contrasting strategies have caught the attention of crypto market watchers globally as ETH continues trading below $2,000.
Tom Lee Doubles Down on ETH While Prices Slide
Tom Lee, serving as Bitmine’s Chairman, publicly addressed the current crypto downturn in a recent company statement.
“In the midst of this ‘mini crypto winter,’ our focus continues to be on methodically executing our treasury strategy and steadily acquiring ETH,” said Lee. Rather than pulling back, Bitmine moved forward with one of its most aggressive single-week purchases to date.
Lee made his conviction on Ethereum clear, pointing to three fundamental drivers he believes are gaining traction.
“Wall Street and their efforts at tokenization, AI and agentic-AI using smart blockchains, and the emerging creator economy’s desire to use blockchains for verification,” he outlined. These factors, in his view, make the current dip a buying window rather than a warning sign.
“In the past week, we acquired 51,162 ETH,” Lee confirmed. “Bitmine has been steadily buying Ethereum, as we view this pullback as attractive, given the strengthening fundamentals.”
He added that “the price of ETH is not reflective of the high utility of ETH and its role as the future of finance,” reinforcing the company’s long-term position.
Vitalik Buterin’s Selling Spree Puts Pressure on ETH Price
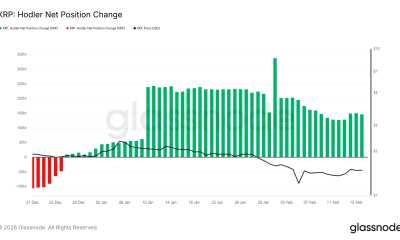
As Bitmine was accumulating, a very different story was unfolding on the other side of the market. Crypto analyst Crypto Patel flagged the activity on social media, writing, “After a 2-week break, Vitalik Buterin just withdrew 3,500 ETH worth $6.95M from Aave to sell.” Buterin then proceeded to sell 571 ETH shortly after the withdrawal.
This followed an earlier sale on February 5, when Buterin offloaded 9,144 ETH at approximately $2,170 per token, collecting $19.84 million.
Patel noted in his post, “Total Sold in Feb: 9,715+ ETH (~$21M+),” as ETH slipped below $2,000 during the selling period. The timing amplified negative sentiment around ETH at an already sensitive moment in the market.
Patel’s post openly questioned the motive behind the moves, asking, “Is the Ethereum co-founder losing confidence… or does he know something we don’t?”
The post drew sharp reactions across the crypto community, with many debating whether the sales reflected routine portfolio management or something more telling. Either way, the activity added pressure to an asset already struggling to hold key price levels.
Bitmine’s Staking Strategy Keeps Revenue Flowing Despite the Dip
Even as prices soften, Bitmine’s staking operations continue generating steady income. “Annualized staking revenues are now $171 million,” Lee stated, adding that Bitmine’s own staking operations generated a seven-day yield of 2.89%, above the broader Composite Ethereum Staking Rate of 2.81%. The company currently has 3,040,483 ETH staked, valued at approximately $6 billion.
Lee further noted that “at scale, when Bitmine’s ETH is fully staked by MAVAN and its staking partners, the ETH staking rewards is $249 million annually.”
MAVAN, the Made in America Validator Network, remains on track for an early 2026 launch. Bitmine is currently working with three external staking providers as it prepares for full deployment of the platform.
Bitmine’s total holdings, including $691 million in cash, a $200 million stake in Beast Industries, and a $17 million position in Eightco Holdings, bring the overall portfolio to $9.6 billion.
With Lee buying aggressively while Buterin sells, the two figures now represent opposite ends of the current Ethereum narrative.
Crypto World
ICP to add 20% revenue burn in new tokenomics shift


ICP adds 20% revenue-funded burns and usage-based node rewards to align supply with demand.
Summary
- 80% of Internet Computer cloud engine revenue will go to node providers, while 20% will buy and burn ICP, creating a usage-linked supply reduction.
- Node providers will shift from fixed subsidies to compensation tied directly to compute demand, aligning incentives with real network activity.
- The updated model mirrors other compute-focused chains that use fee-funded burns and demand-driven payouts to reward infrastructure and curb token inflation.
The DFINITY Foundation announced plans to update Internet Computer’s tokenomics to include a burn mechanism funded by network revenue, according to a statement from the organization.
Under the new model, 80% of revenue generated by Internet Computer cloud engines will be distributed to node providers operating the infrastructure, while the remaining 20% will be used to purchase and burn ICP tokens, the foundation stated. Node provider associations have begun preparations to market cloud engines, according to the announcement.
The current system provides node providers with fixed payments for maintaining network operations regardless of workload demand. The updated structure will tie node compensation directly to usage-driven revenue from compute services, linking incentives to actual network activity, the foundation said.
The change represents a shift from a fixed-subsidy model toward a usage-based economic framework for the Internet Computer network, according to DFINITY.
The revenue allocation directs a portion of funds to token burns, creating a demand-linked supply reduction mechanism as network adoption increases. The majority of revenue will flow to infrastructure operators to incentivize capacity provision and service reliability, the foundation stated.
Similar usage-based token economic models have been implemented in other compute-oriented blockchain networks, industry observers noted.
The transition aligns network incentives with usage while introducing a structural supply reduction mechanism tied to adoption levels, according to the foundation’s announcement.
Crypto World
Why DAO Governance Always Turns Political
“In a decentralized governance system, it’s unavoidable to develop politics.”
Rune Christensen explains why DAO governance becomes a struggle for resources, how the “iron law of bureaucracy” emerges, and why Sky redesigned its architecture to survive it.
Crypto World
SEC Approves WisdomTree Digital Money Market Fund to Trade at Fixed $1 Intraday Price

TLDR:
- The SEC issued an exemptive order on Feb. 23, 2026, allowing WisdomTree’s digital MMF to trade at $1 intraday.
- The order grants relief from Section 22(d) and Rule 22c-1, bypassing the standard next-calculated NAV pricing requirement.
- Registered broker-dealers with dealer agreements can now sell Covered Fund shares at a stable $1.00 on a principal basis.
- Rule 17d-1 Relief also permits WisdomTree’s affiliated dealer to transact with the fund under terms consistent with the Act.
WisdomTree Government Money Market Digital Fund has received a landmark exemptive order from the U.S. Securities and Exchange Commission.
The order allows investors to trade the fund’s shares at a fixed $1.00 price with a dealer on an intraday basis.
This approval marks a notable shift in how digital money market fund shares can be bought and sold, regardless of the fund’s end-of-day net asset value (NAV).
SEC Grants Pricing Relief for Intraday Transactions
The Division of Investment Management issued the order on February 23, 2026. It covers WisdomTree Digital Trust, WisdomTree Securities Inc., WisdomTree Digital Management Inc., and WisdomTree Transfers Inc.
Together, these entities filed the original application on May 8, 2025. An amendment followed on January 16, 2026.
The exemptive order grants relief from Section 22(d) of the Investment Company Act of 1940 and Rule 22c-1 under the Act. Under normal rules, fund shares must be sold at the next-calculated NAV. This order creates an exception specifically for digital money market fund shares.
Under the new structure, registered broker-dealers who enter a dealer agreement with a Covered Fund can trade shares at $1.00 on a principal basis.
This means individual and institutional investors alike can transact at a stable price throughout the trading day. The fixed price applies regardless of what the NAV calculates to at day’s end.
The SEC posted the development publicly, noting the order permits investors to trade shares at $1 with a dealer on an intraday basis.
Rule 17d-1 Relief Permits Affiliated Dealer Participation
Beyond the pricing relief, the SEC also granted Rule 17d-1 Relief under Section 17(d) of the Act. This portion of the order addresses transactions between the fund and its affiliated dealer, WisdomTree Securities Inc. Without this relief, such arrangements would be prohibited under the Act.
The Commission found that the affiliated dealer’s participation in these transactions is consistent with the Act’s provisions, policies, and purposes.
It also determined the arrangement is no less advantageous than participation by other parties. Both orders took effect immediately upon issuance.
A public notice of the application was issued on January 26, 2026. Interested parties had an opportunity to request a hearing, but no such request was filed. The Commission then moved forward without ordering a hearing.
The relief also extends beyond the Applicant Fund. It applies to any series of the Applicant Trust or other registered open-end management investment companies meeting specific criteria.
This broader scope means other digital money market funds could potentially benefit from the same pricing structure in the future.
Crypto World
MSTR acquired 592 BTC last week


Strategy (MSTR), the world’s largest publicly traded company holding bitcoin, made a small BTC acquisition last week, adding 592 coins for $39.8 million.
That’s an average purchase price of $67,286 per bitcoin, with the buys completely funded via sales of common stock, according to an SEC filing.
The company now holds 717,722 bitcoin acquired for $54.56 billion, or an average price of $76,020 per coin. With bitcoin currently trading just above $66,000, the position represents an unrealized loss of roughly $10,000 per coin, or about $7 billion in total.
This morning’s news is a milestone of sorts. According to a cheeky X post by Executive Chairman Michael Saylor, it was Strategy’s 100th announcement of a bitcoin purchase since the company (then named MicroStrategy) began acquiring BTC in August 2020.
MSTR shares are down 2.5% in pre-market action and more than 50% year-over-year.
Crypto World
Mexican billionaire Ricardo Salinas remains bullish on bitcoin after plunge


Mexican billionaire Ricardo Salinas, one of that country’s richest individuals, hasn’t been shaken by the recent crash in the price of bitcoin.
“Take advantage and buy now while it’s down,” said Salinas in a Sunday X post. “Investing in Bitcoin is protecting your money against inflation and keeping it out of the hands of those who want to steal it from you.”
The comment from the longtime bull came following bitcoin’s plunge in recent months to its current level of $66,000. Salinas shared the message alongside an older clip of him defending bitcoin’s ability to support freedom, doubling down on a stance he’s held for years.
Salinas, whose estimated net worth is around $4.9 billion, has been one of Latin America’s most vocal bitcoin advocates. In past interviews, he’s described fiat currency as a “fraud” and called bitcoin “the only way out” for preserving purchasing power.
In an interview last year, he said 70% of his liquid assets were linked to bitcoin. The remaining 30% was in gold and shares of gold mining firms.
Crypto World
What Supreme Court tariff ruling means for global trade, U.S. economy

The Supreme Court struck down President Donald Trump’s tariffs on Friday, but the trade tax turmoil is far from over. Fallout over the ruling is already threatening to further strain global trade relations, and the U.S. economy is likely to suffer, economists told CNBC.
In 6-3 decision, the high court ruled that President Trump did not have the legal authority to implement his sweeping tariffs imposed last April under the International Emergency Economic Powers Act, or IEEPA.
Trump later leveled new tariffs up to 15% effective immediately on an array of U.S. trading partners, further escalating global trade tensions. European Union leaders expressed dismay over the new tariffs, arguing that the U.S. policy shift would upend trade deals already reached with the EU as well as the U.K. last year. On Monday, the EU again postponed a key vote on its deal with the U.S.
The pushback against the latest U.S. tariff threat underscores deep frustration over the president’s erratic trade policies, and could push foreign governments to scale back U.S. trade and lead businesses to curb expansion, investment and hiring.
The result might hobble the U.S. economy. “It shifts how trade is done with the largest economy in the world, and that has economic consequences,” Mike Reid, head of U.S. economics at Royal Bank of Canada told CNBC, referring to the Supreme Court ruling and new tariff push.
Downside
The trade war drama is likely to contribute to a climate of caution among businesses and foreign governments alike, said Mark Zandi, chief economist at Moody’s Analytics, leading to “nothing but downside,” for the U.S. economy.
“Businesses don’t know” what’s going to happen next, Zandi told CNBC. “They’re going to invest less, they’re going to hire less, they’re going to be less aggressive in their expansions,” limiting U.S. growth.
Foreign governments could react similarly amid rising uncertainty, leading them to “continue to pull away from the U.S,” according to the economist.
“They’ve got to be pulling their hair out over all of this,” Zandi said. “Perceptions of the U.S. are increasingly that we’re a poorly managed economy, and objectively speaking, they’re right. It’s a bit of a mess that feels like it’s getting messier.”
That perception could lead to efforts to divert trade away from the U.S. to a variety of other trading partners, including China.
China’s exports grew 6.6% in U.S. dollar terms last December compared to the same month a year earlier, topping analyst expectations and sending the nation’s annual trade surplus to a record, according to Chinese customs data. Imports increased at their fastest pace in three months, the same data showed.
Trump trade taxes
The Trump administration will continue implementing its trade policy, and now plans to use a variety of sections in the Tariff Act of 1974, according to U.S. Trade Representative Jamieson Greer.
President Trump is pointing to section 122 of the Tariff Act to justify his new tariffs enacted this weekend, although that section limits their effectiveness to 150 days, until mid July, after which they would have to be approved by Congress.
But the administration is likely to use sections 232 and 301 of the Tariff Act to supplement its new section 122 tariffs, meaning the U.S. could continue to impose tariffs against its foreign trading partners over the next few years, at least.
Others say neither investors nor economists shouldn’t sound the alarm just yet.
The implementation of the new trade taxes “implies little change in the effective tariff rate or our inflation forecasts in the near term,” Citigroup economist Veronica Clark said in a note to clients.
“Eventual Section 301/232 tariffs could have an impact on certain goods prices in the future, but details are still highly uncertain,” Clark wrote. “While a 10% Section 122 tariff would likely have lowered the effective tariff rate by 3-4 [percentage points], a 15% tariff should keep the effective tariff rate essentially unchanged (if anything, lower by ~1pp or so).
While the total impact of the new tariffs remains uncertain, a few things are clear, Zandi said.
“The U.S. is pulling away from the world, and the rest of the world is now pulling away from the U.S.,” the economist said. “Deglobalization is a weight on the economy, and ultimately, the end state is a weakened economy.”
— With additional reporting provided by CNBC’s Alex Harring
Crypto World
Pantera leads $11.5M round in Based, a Hyperliquid-powered crypto app


Based, a Web3 consumer app for trading and spending crypto, has raised $11.5 million in a Series A round led by Pantera, with participation from Coinbase Ventures, Wintermute Ventures and Karatage.
The company said the fresh capital will be used to expand into new markets and build out its onchain financial infrastructure.
Launched eight months ago, Based combines perpetuals trading, prediction markets and real-world crypto spending into a single interface. Built natively on Hyperliquid’s execution environment, the platform seeks to pair institutional-grade speed and liquidity with a consumer-focused experience.
Beyond its app, Based is also extending its technology stack to power third-party venues such as HyENA, a Hyperliquid-native perpetuals platform.
“Most crypto products today are built for traders or builders, not for everyday people who want a complete financial life onchain,” said co-founder and CEO who goes by Edison, in a press release shared with CoinDesk. “We’re building Based so anyone, anywhere can access global markets and also use those funds to purchase things they actually need without jumping through hoops.”
Read more: Bitcoin will ‘massively’ outperform gold over 10 years, says Pantera’s Dan Morehead
-
 Crypto World7 days ago
Crypto World7 days agoCan XRP Price Successfully Register a 33% Breakout Past $2?
-

 Video4 days ago
Video4 days agoXRP News: XRP Just Entered a New Phase (Almost Nobody Noticed)
-

 Fashion3 days ago
Fashion3 days agoWeekend Open Thread: Boden – Corporette.com
-

 Sports7 days ago
Sports7 days agoGB's semi-final hopes hang by thread after loss to Switzerland
-
 Politics2 days ago
Politics2 days agoBaftas 2026: Awards Nominations, Presenters And Performers
-

 Tech7 days ago
Tech7 days agoThe Music Industry Enters Its Less-Is-More Era
-

 Sports6 hours ago
Sports6 hours agoWomen’s college basketball rankings: Iowa reenters top 10, Auriemma makes history
-

 Politics7 hours ago
Politics7 hours agoNick Reiner Enters Plea In Deaths Of Parents Rob And Michele
-

 Business6 days ago
Business6 days agoInfosys Limited (INFY) Discusses Tech Transitions and the Unique Aspects of the AI Era Transcript
-

 Entertainment5 days ago
Entertainment5 days agoKunal Nayyar’s Secret Acts Of Kindness Sparks Online Discussion
-
 Video7 days ago
Video7 days agoFinancial Statement Analysis | Complete Chapter Revision in 10 Minutes | Class 12 Board exam 2026
-

 Tech6 days ago
Tech6 days agoRetro Rover: LT6502 Laptop Packs 8-Bit Power On The Go
-

 Sports5 days ago
Sports5 days agoClearing the boundary, crossing into history: J&K end 67-year wait, enter maiden Ranji Trophy final | Cricket News
-

 Business2 days ago
Business2 days agoMattel’s American Girl brand turns 40, dolls enter a new era
-

 Business1 day ago
Business1 day agoLaw enforcement kills armed man seeking to enter Trump’s Mar-a-Lago resort, officials say
-

 Entertainment5 days ago
Entertainment5 days agoDolores Catania Blasts Rob Rausch For Turning On ‘Housewives’ On ‘Traitors’
-

 Business6 days ago
Business6 days agoTesla avoids California suspension after ending ‘autopilot’ marketing
-

 NewsBeat15 hours ago
NewsBeat15 hours ago‘Hourly’ method from gastroenterologist ‘helps reduce air travel bloating’
-

 Politics7 days ago
Politics7 days agoEurovision Announces UK Act For 2026 Song Contest
-

 Tech1 day ago
Tech1 day agoAnthropic-Backed Group Enters NY-12 AI PAC Fight











