Crypto World
Kaspersky Uncovers Google Tasks Phishing To Steal Credentials
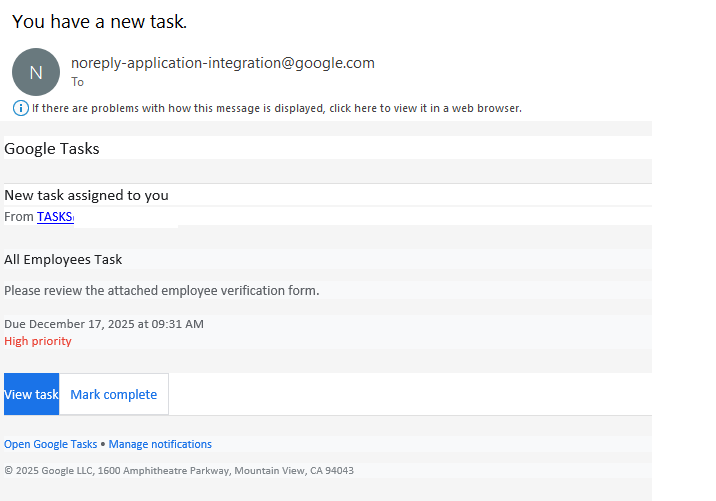
Editor’s note: The following briefing outlines a new phishing campaign uncovered by Kaspersky that hijacks legitimate Google Tasks notifications to steal corporate credentials. The attackers impersonate trusted services, leveraging the @google.com domain and intra-company cues to evade standard filters and pressure users into acting quickly. Victims are invited to click a link and complete a fraudulent employee verification form, exposing sensitive credentials that could grant unauthorized access. This advisory highlights the evolving tactics criminals use to exploit familiar tools and the importance of vigilance in enterprise environments.
Key points
- Attackers abuse legitimate Google Tasks notifications to steal corporate credentials.
- The campaign uses the trusted @google.com domain to bypass filters and build trust.
- Users are directed to a fraudulent employee verification form after clicking a link.
- The social engineering hinges on urgency and internal process appearance to lower defenses.
Why this matters
By exploiting familiar services, the campaign exploits trust in everyday tools, increasing the likelihood that employees reveal credentials. This approach bypasses many security filters and highlights the need for awareness and layered defenses in organizations. The incident underscores why training, MFA, and robust verification processes are critical as attackers continue to adapt to legitimate platforms.
What to watch next
- Look for more phishing attempts that imitate enterprise tools via trusted notification channels.
- Watch for fraudulent forms asking for corporate credentials and verify URLs before interacting.
- Ensure MFA and mail-server security measures are in place to protect accounts.
- Report suspicious activity to IT and update security policies as needed.
Disclosure: The content below is a press release provided by the company/PR representative. It is published for informational purposes.
Kaspersky discovers new phishing campaign exploiting Google Tasks notifications to steal corporate credentials
February 26, 2026
Kaspersky has uncovered a new phishing scheme that abuses legitimate Google Tasks notifications to trick corporate users into revealing corporate login credentials. By leveraging Google’s trusted @google.com email domain and notification system, attackers bypass traditional email security filters and exploit users’ trust in familiar services.
In this campaign, victims receive an authentic-looking notification from Google Tasks with the subject line “You have a new task.” The message creates the illusion that the recipient’s company has adopted Google’s task management tool, pressuring them to act quickly. The notification often includes elements of urgency, such as a high-priority flag and a tight deadline, to prompt the victim’s immediate response.
Upon clicking the embedded link, users are directed to a fraudulent form disguised as an “employee verification” page, where they are asked to enter their corporate credentials under the pretense of confirming their status. These stolen credentials can then be used for unauthorized access to company systems, data theft, or further attacks.
“Google’s vast ecosystem of services gets exploited by scammers. The scheme with Google Tasks is part of a broader trend observed before and continuing into 2026, where cybercriminals misuse legitimate platforms to distribute scams and phishing. Notifications originating from legitimate domains naturally evade many spam and phishing filters, while the social engineering aspect – making it seem like an internal company process – lowers the victim’s guard,” comments Roman Dedenok, Anti-Spam Expert at Kaspersky.
Read the article about this tactic on Kaspersky’s blog.
To counter this and similar threats, Kaspersky recommends:
- Treat unsolicited invitations from any platform with suspicion, even if they appear to come from trusted sources
- Carefully inspect URLs before clicking
- Do not call any phone numbers indicated in suspicious emails – if you need to call support of a certain service, it is best to find the phone number on the official webpage of this service
- Report suspicious emails to the platform provider and use multi-factor authentication for all accounts
- For corporate users, Kaspersky Security for Mail Server with its multi-layered defense mechanisms powered by machine learning algorithms provides robust protection against a wide range of evolving threats and offers peace of mind to businesses in the face of evolving cyber risks
- For individual users Kaspersky Premium offers AI-powered anti phishing features designed to help avoid phishing attacks and improve overall cybersecurity
About Kaspersky
Kaspersky is a global cybersecurity and digital privacy company founded in 1997. With over a billion devices protected to date from emerging cyberthreats and targeted attacks, Kaspersky’s deep threat intelligence and security expertise is constantly transforming into innovative solutions and services to protect individuals, businesses, critical infrastructure and governments around the globe. The company’s comprehensive security portfolio includes leading digital life protection for personal devices, specialized security products and services for companies, as well as Cyber Immune solutions to fight sophisticated and evolving digital threats. We help millions of individuals and nearly 200,000 corporate clients protect what matters most to them. Learn more at www.kaspersky.com.
Crypto World
Bitcoin price forecast as traders bet on $80,000 next


- Bitcoin trades above $70,700 as derivatives data shows $80,000 calls dominating on Deribit.
- BTC rebounded to near $72,900 on Wednesday as a US-Iran ceasefire eased oil pressures.
- Analysts see end of stress cycle, targeting $80,000 if $75,000 breaks.
Bitcoin’s resurgence to above $70,000, with intraday highs of $72,900, has crypto enthusiasts in an upbeat mood. The cryptocurrency hovers near $70,800 as of writing, off highs seen on Wednesday, but bulls are upbeat as fresh market signals point to a potential breakout.
Traders bet on next leg up for Bitcoin
Bitcoin is well off its year-to-date highs and has struggled since breaking lower in late January 2026. Bears are therefore still on the hunt.
However, this week has investor sentiment shifting bullish, fueled by the US-Iran ceasefire and key activity in Bitcoin derivatives. Data suggests investors are eyeing a potential rally to $80,000.
Options data from Deribit, the platform that accounts for the lion’s share of the global crypto options market, shows bullish bets on prices surging to $80,000 have increased.
Call options betting on BTC climbing beyond the $80k strike price have hit $1.6 billion. This is a stark reversal from recent months when $60,000 puts, which outline wagers on price drops, dominated the outlook.
On-chain data also supports the bullish case, with Morgan Stanley’s ETF debut netting over $34 million in volume.
Allyson Wallace, global head of ETFs at Morgan Stanley, commented ahead of the launch: “The demand, especially from the high-net-worth investors, has been quite high. Viewed at the firm level, this is an asset class that is not going away.”
Bitcoin price prediction
The crypto market began the week with all eyes on Bitcoin. Notably, BTC bounced to highs near $72,900, hitting levels last seen since March 18. The uptick saw buyers push from lows near $67,700 overnight Tuesday, April 7, amid news of a ceasefire between the US and Iran.

Investors buoyed by the prospect of an easing in oil prices helped BTC higher. With broader inflation concerns dissipating, a further strengthening in the ceasefire could see Bitcoin prices break to $75,000. If this happens, the next target will be $80,000 or higher.
However, geopolitical risks remain amid a likely fragile ceasefire. If fresh attacks begin and an escalation occurs, a surge in oil prices could send risk assets plummeting.
Crypto World
Nvidia (NVDA) Stock Tests Critical $185 Resistance Amid Iran Ceasefire Uncertainty
Key Takeaways
- NVDA slipped between 0.2%–0.5% Thursday, settling around $181.75 following Wednesday’s 2.2% rally
- Shares have remained confined within a $165–$195 trading channel for several months
- Market analysts identify $185 as a critical breakout threshold; $200 viewed as confirmation level
- Wednesday’s surge followed news of a two-week U.S.-Iran ceasefire, though durability concerns persist
- Technical analysts warn that breaching $170 support could trigger a decline toward $150
Nvidia’s recent price action reflects a prolonged period of consolidation. Despite its status as the market’s artificial intelligence powerhouse, NVDA shares have languished in a holding pattern since September 2025, oscillating within a $165–$195 corridor as traders await a meaningful catalyst.
Signs of a potential breakout emerged recently. The chipmaker mounted an impressive rally spanning six consecutive sessions—delivering gains exceeding 10% and marking its longest winning streak since October—before momentum stalled on Thursday.
The Wednesday surge of 2.2% followed President Trump’s announcement of a temporary two-week ceasefire agreement with Iran, which included the reopening of the strategically vital Strait of Hormuz. This development eased concerns about potential economic disruption. Nvidia emerged as one of the S&P 500’s top performers during that session.
Thursday’s trading painted a contrasting picture. Shares retreated approximately 0.5% to $181.75 as market participants expressed skepticism about the ceasefire’s sustainability. The broader S&P 500 index also traded relatively flat.
Geopolitical dynamics continue to influence risk sentiment across markets. Iran’s continued capability to disrupt shipping through the Strait of Hormuz maintains a degree of unease among investors.
Beyond geopolitical concerns, a fundamental question persists: will major cloud providers—including Microsoft, Google, and Amazon—realize meaningful returns on their substantial artificial intelligence infrastructure investments? This uncertainty has effectively capped NVDA’s upside potential in recent months.
Ishan Majumdar, founder of Baptista Research, shared his perspective with Barron’s, emphasizing that core AI demand dynamics haven’t changed. “Nothing about the cease-fire alters the structural AI demand story,” he noted. “If anything, removing macro volatility allows the market to refocus on those fundamentals.”
Technical Analysts Flag $185 as Pivotal Threshold
Jonathan Krinsky, chief market technician at BTIG, has identified the $185 price point as particularly significant. “If Nvidia sustains above $185, I would say the money is ready to run back in,” he explained. “The long-term trend remains positive.”
Buff Dormeier at Kingsview Partners believes a higher confirmation is necessary. He suggests NVDA must break through $200 to establish a convincing bullish trajectory. “If we started to get a signal of that, we could easily be back to the races,” he indicated.
Dormeier also highlighted improving valuation metrics. NVDA currently trades at approximately 20 times forward earnings—significantly below its historical 10-year average multiple of around 36—and now trades in line with the broader S&P 500. This represents a meaningful valuation compression for a stock that traditionally commanded a substantial premium.
Support Breakdown Could Trigger Further Weakness
Both technical strategists emphasize meaningful downside risks. The $170 price level represents crucial support. A sustained breach below this threshold could signal additional selling pressure ahead.
“If we were to break under there, I think shares could fall down to $150,” Dormeier cautioned.
Krinsky shared similar concerns about the sustainability of the recent bounce. “It doesn’t strike me as an all-clear that we recovered the $170 level so quickly,” he observed. “If it moves back to that level and closes under it again, that would be a more telling signal that Nvidia is likely to continue lower.”
For the immediate term, Dormeier frames the trading range as $165 representing the floor and $180 marking near-term resistance. NVDA settled Wednesday’s session at $182 before trading around $181.75 on Thursday.
Crypto World
Bitcoin Depot Reports $3.7M BTC Theft in Cybersecurity Breach
Bitcoin Depot, a leading operator of crypto ATMs in the United States, disclosed a security breach that led to the theft of about 50.9 Bitcoin, valued at roughly $3.7 million at the time of reporting, after an attacker gained access to credentials tied to the company’s corporate Bitcoin wallets.
The incident occurred on March 23, and, according to a filing with the U.S. Securities and Exchange Commission, the attacker took control of credentials connected to Bitcoin Depot’s corporate BTC wallets. The company emphasized that customer accounts, its platforms and personal data were not affected. The breach has not halted daily operations, and the firm has insurance that may cover a portion of the losses. The investigation is ongoing, and the full scope, nature, and impact of the incident remain uncertain.
Bitcoin Depot’s stock responded to the disclosure, closing up 15.6% at $2.74 on the day and moving higher in pre-market trading to around $2.90, according to Yahoo Finance data.
Key takeaways
- The breach resulted in an estimated 50.9 BTC theft, equating to about $3.7 million at the time of the notice, with attackers gaining access to corporate wallet credentials.
- Customer data and platform access were reportedly unaffected, and operations continued with insurers potentially covering part of the losses, though the full scope remains under investigation.
- Bitcoin Depot has faced intensified regulatory scrutiny across several U.S. states, including licensing actions in Connecticut, where regulators cited high fees and incomplete restitution to scam victims.
- Recent legal actions include a Massachusetts lawsuit over alleged overcharging and facilitating scams, and a Maine settlement of $1.9 million to compensate affected users; a June 2024 data breach also exposed tens of thousands of customers.
- Market and policy dynamics around crypto ATMs are tightening, with ongoing discussions in multiple cities about banning or restricting kiosk-based crypto access.
Operational risk, insurance, and ongoing investigations
The March breach underscores how credential compromise can enable unauthorized access to corporate wallets, even when consumer-facing services remain unaffected. Bitcoin Depot states that customer-facing platforms and personal data were not compromised, but the incident raises questions about internal security controls, credential management, and monitoring across enterprise systems. The company has indicated it carries insurance that may help offset losses, but the exact coverage and its applicability to a security incident of this type have not been disclosed publicly.
As regulators and investors await the full forensic findings, the evolving incident illustrates the broader risk landscape for crypto ATM operators, whose business model relies on a distributed, networked infrastructure across dozens or hundreds of locations. For users and institutions, it highlights the tension between enabling accessible crypto on-ramps and maintaining robust, verifiable security controls to deter credential compromise and unauthorized access.
Regulatory pressures and legal exposure mounting
Bitcoin Depot has faced mounting regulatory pressure across several states. In Connecticut, the company’s money transmission license was suspended, and regulators issued a cease-and-desist order over concerns including excessive fees and insufficient refunds to scam victims. Connecticut’s action adds to a growing list of state-level concerns about consumer protections and fee practices in the crypto ATM space.
Beyond licensing actions, the company has grappled with a high-profile Massachusetts lawsuit alleging overcharging and facilitating scams against consumers. Separately, Maine regulators required the company to compensate affected users, with a $1.9 million settlement designed to address prior consumer harms.
These developments come as the sector’s exposure to fraud and scams remains a headline risk for policymakers. In June 2024, Bitcoin Depot disclosed a data breach that exposed the personal information of tens of thousands of customers; authorities allowed the company to finalize notifications only after the investigation concluded in mid-2025. The combination of security incidents and consumer-protection actions underscores a regulatory trend toward tighter oversight of crypto ATMs and related consumer risks.
Markets, perception, and the ATM ecosystem
The regulatory and security headwinds have implications for investor sentiment around crypto ATM operators. Bitcoin Depot’s stock reaction—gapping higher on the news—reflects a nuanced investor calculus: the breach is managed as a cyber risk event with potentially limited direct impact on customers, yet it amplifies scrutiny of the underlying business model and governance controls. As with any security incident, the market response hinges on the clarity of the remediation steps, the breadth of the investigation, and the extent of insurance coverage.
In parallel, the broader U.S. landscape for crypto ATMs remains sizeable but contentious. Industry trackers estimate the United States hosts upwards of 30,000 Bitcoin ATMs, underscoring the scale of on-ramp infrastructure that regulators and consumer groups are weighing. The debate extends to local policy: Stillwater, Minnesota, banned crypto ATMs after residents were affected by scams; Spokane, Washington, moved to a citywide ban in mid-2023, describing kiosks as a preferred tool for scammers. Haverhill, Massachusetts, has entertained a motion to ban crypto ATMs, with a proposed 60-day removal window if enacted.
The regulatory climate, combined with security incidents, suggests continued scrutiny and potential accelerated policy responses at the city and state levels. For operators, this may translate into tighter compliance requirements, clearer consumer-protection standards, and enhanced cybersecurity expectations as part of operational licenses and ongoing audits.
For readers seeking context on the ATM landscape, sector trackers show that the density of crypto kiosks remains a notable feature of the U.S. crypto frontier, even as regulators seek to curb fraud and misuse. See data from CoinATMRadar for the current footprint of Bitcoin ATMs in the United States.
Looking ahead, investors and users should watch how regulators balance access with protection, how operators bolster credential hygiene and incident response, and whether insurance coverage translates into meaningful risk mitigation in the event of future breaches. The evolving mix of cyber risk, consumer protection actions, and local policy decisions will shape the healing path for crypto ATM reliability and trust in the months to come.
Readers should stay tuned for further disclosures from Bitcoin Depot and for updates on regulatory actions as investigators complete their forensic work and authorities finalize consumer-notification requirements. The next few months will likely reveal how much remedial work is needed to restore confidence in a sector that sits at the intersection of convenience, security, and enforcement.
Crypto World
Galaxy’s Novogratz touts $15 billion Helios valuation in first nasdaq annual letter


Galaxy Digital (GLXY) founder and CEO Mike Novogratz highlighted the firm’s key milestones in its 2025 annual report, marking its first 10-K filing as a Nasdaq-listed company.
Novogratz described the listing as more than a milestone, calling it “a declaration that the digital economy is real, and that Galaxy is built to lead it.”
Over the years, Galaxy has evolved from a pure-play digital asset firm into a diversified platform that includes asset management, institutional trading and AI-driven high-performance computing data centers.
Novogratz noted that the digital asset economy has evolved from a speculative, niche market into a mainstream industry, with even the United States now holding bitcoin on its balance sheet, something that would have been inconceivable a decade ago.
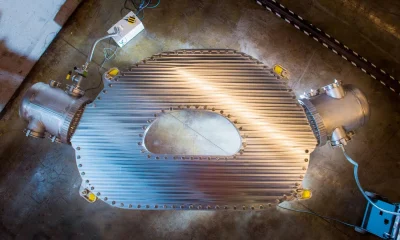
The company’s biggest growth tailwind is its artificial intelligence and high-performance computing strategy and Helios, its AI data center campus in West Texas. The site has secured more than 1.6 gigawatts of approved power capacity through ERCOT.
The initial 800 megawatts is already leased to AI cloud provider CoreWeave (CRWV), representing over $7.5 billion in capital investment. With an additional 830 megawatts approved for expansion, Helios is now valued at well above $15 billion, according to the report.
Novogratz’s longer-term goal is to build a multi-billion-dollar portfolio of digital infrastructure assets diversified across regions, tenants, and technologies. “Demand for compute is not a cycle, it is a structural condition that will define the next decade.”
On the digital assets side, Galaxy manages roughly $12.3 billion in platform assets as of December 31, 2025. Its offerings include over-the-counter spot and derivatives trading, lending, staking across 11 blockchains, including Ethereum and Solana, ETFs, and institutional-grade custody.
In October 2025, the firm expanded into retail with GalaxyOne, a fintech platform offering FDIC-insured high-yield accounts, commission-free trading in equities and crypto, and the option to automatically reinvest interest into bitcoin.
Despite the industry downturn in the fourth quarter of 2025, the company saw a net loss of $241 million. Novogratz remains optimistic, saying the firm is “more clear-eyed about our opportunity than we have ever been.”
Crypto World
Tokenized Commodities Push Crypto Platforms Into Direct Competition With Traditional Finance

Key Takeaways
-
Digital asset perpetual contracts expand market presence as legacy financial venues experience declining share in commodities
-
Blockchain-based silver contracts reach 40% of conventional futures market benchmark trading volumes
-
Insufficient market depth maintains legacy systems’ competitive advantage despite cryptocurrency sector expansion
-
Round-the-clock access provides digital platforms competitive differentiation versus traditional exchange operating schedules
-
Price discovery challenges hinder widespread acceptance of blockchain-based metals instruments
Digital asset trading venues are experiencing substantial expansion within commodities sectors, gradually capturing volume from conventional financial platforms while transforming worldwide market accessibility. Nevertheless, traditional institutions maintain leadership positions through superior market depth and established pricing mechanisms. Blockchain-based commodity instruments demonstrate continued expansion, yet structural constraints impede faster integration across conventional finance participants.
Blockchain-Based Commodity Products Show Strong Market Traction
Crypto exchanges are experiencing accelerated expansion across tokenized commodity sectors, mounting a credible challenge to traditional finance’s long-standing control of derivatives trading. Particularly noteworthy, perpetual silver contracts have achieved substantial trading activity when measured against conventional futures exchange benchmarks. Consequently, digital platforms persistently attract participants seeking ongoing market participation outside traditional exchange operating windows.
Throughout recent trading periods, blockchain-based silver instrument volumes have risen dramatically compared to conventional futures marketplace activity. This development signals growing appetite for adaptable trading solutions absent from traditional financial infrastructure. Additionally, cryptocurrency platforms capitalize on continuous availability, whereas legacy markets face constraints imposed by predetermined operating schedules.
Perpetual gold derivatives have similarly exceeded trading volumes on multiple regional conventional exchanges during recent measurement periods. This expansion demonstrates how digital platforms are progressively increasing their footprint within commodity markets historically controlled by traditional finance. Nonetheless, legacy institutions preserve commanding positions through well-established operational frameworks and established credibility.
Market Depth and Price Discovery Sustain Traditional Finance Leadership
Blockchain-based commodity instruments encounter ongoing obstacles that restrict their competitive positioning against conventional marketplace infrastructure. Available liquidity remains substantially thinner compared to traditional platforms, which leverage centralized settlement frameworks. As a result, price inconsistency issues persist, affecting operational efficiency relative to established financial standards.
Crypto markets function without interruption, contrasting with traditional exchanges that suspend operations during weekends and recognized holidays. This operational distinction generates volatility exposure and diminished price benchmarking during periods when conventional venues remain closed. Legacy financial structures continue delivering stability through synchronized trading sessions and aggregated liquidity resources.
Traditional financial markets sustain greater credibility through validated reserve attestations and uniform contractual specifications. Cryptocurrency trading venues currently lack uniform verification protocols matching transparency benchmarks established by conventional finance. Institutional capital allocation remains predominantly channeled within traditional environments notwithstanding emerging digital alternatives.
Operational Evolution Underscores Intensifying Market Competition
Cryptocurrency perpetual futures instruments maintain upward momentum as substitutes for traditional derivatives offerings. These products remove expiration constraints, delivering streamlined exposure compared to conventional futures agreements. Consequently, market participants increasingly embrace digital solutions while maintaining connections to established traditional instruments.
Trading analytics demonstrate robust volume growth, indicating escalating competition between crypto platforms and traditional exchange operators. Non-business-day trading patterns particularly emphasize operational advantages over conventional systems that pause during significant international developments. Therefore, digital platforms deliver accelerated response capabilities to market movements occurring beyond traditional operating hours.
Traditional finance maintains comprehensive integration throughout worldwide financial networks with unparalleled market depth and regulatory transparency. Cryptocurrency exchanges persistently enhance operational capabilities to reduce performance disparities with conventional operations. Accordingly, competitive dynamics between digital platforms and traditional finance are becoming increasingly pronounced as both ecosystems advance through rapid innovation cycles.
Crypto World
DOJ, CFTC Seek to Block Arizona Enforcement Action against Kalshi


The DOJ and CFTC filed to enjoin Arizona’s criminal and civil enforcement against prediction market platform Kalshi, arguing federally regulated event contracts fall under CFTC jurisdiction.
The U.S. Department of Justice and the Commodity Futures Trading Commission filed a motion in federal court on Thursday to block Arizona from pursuing criminal and civil enforcement actions against prediction market platform Kalshi. The regulators argue that event contracts regulated at the federal level under CFTC oversight fall outside the state’s jurisdiction.
The filing represents a direct challenge to state-level enforcement against prediction markets, asserting that federal commodity law preempts Arizona’s action. Kalshi operates as a CFTC-regulated derivatives exchange offering binary event contracts.
Sources: U.S. court documents
This article was generated automatically by The Defiant’s AI news system from publicly available sources.
Crypto World
Hims & Hers (HIMS) Stock Plummets 39% Amid GLP-1 Strategy Shift and Margin Pressure
Key Takeaways
- In March 2026, Hims & Hers transitioned away from compounded semaglutide to FDA-approved branded GLP-1 medications
- Bank of America reduced its HIMS price target to $21 from $23 while maintaining a Neutral stance
- Analysts project GLP-1 EBITDA contributions may decline by 50% compared to last year
- Amazon Pharmacy launched Eli Lilly’s oral GLP-1 medication Foundayo, intensifying market competition
- Year-to-date, HIMS shares have plunged approximately 39%, hovering near $20
In a significant strategic shift this March, Hims & Hers abandoned its compounded semaglutide offerings in favor of FDA-sanctioned branded GLP-1 treatments. Management positioned this decision as transforming the company into “the largest global consumer health platform for access to more affordable, approved medications.”
Hims & Hers Health, Inc., HIMS
This strategic reversal came after settling legal proceedings with Novo Nordisk. The resolution required Hims & Hers to distribute Novo Nordisk’s authorized GLP-1 medications instead of less expensive compounded alternatives.
Investors have responded harshly to these developments. HIMS shares have plummeted nearly 39% year-to-date through Wednesday, currently trading in the vicinity of $20.
BofA Securities analyst Allen Lutz reduced his price objective on HIMS this week from $23 down to $21. The analyst maintained his Neutral stance, pointing to valuation compression among comparable companies and anticipated near-term profitability headwinds.
Lutz’s forecast suggests 2026 EBITDA could land approximately 20% beneath current Wall Street expectations. His analysis indicates GLP-1-related EBITDA contributions might decline by up to 50% compared to the previous year.
Neverthstanding the conservative perspective, Lutz indicated his research team holds “slightly more optimistic” views regarding the company’s overseas expansion strategy. He further observed that the $149 monthly branded GLP-1 subscription plan might eventually deliver margins comparable to compounded options, contingent upon subscriber migration rates.
Subscriber Migration Rates Will Determine Success
BofA Securities projects that Hims & Hers might successfully transition between 40% and 50% of current subscribers to branded medication plans, while maintaining 5% to 10% on compounded alternatives. This conversion scenario would produce approximately $60 million to $90 million in GLP-1 revenues each quarter.
The telehealth platform is simultaneously pursuing international market opportunities. Management targets growing this division beyond $1 billion in annual revenue within a three-year timeframe, achieving mid-teens organic compound annual growth rates. Bank of America’s research into the Eucalyptus platform indicates approximately 90% of revenues will derive from branded GLP-1 distribution at roughly 40% gross profit margins.
Canaccord analyst Maria Ripps offered a more bullish assessment. She maintained her Buy recommendation, contending that the Novo Nordisk collaboration represents a “long-term tailwind” for the business. Ripps believes current valuations fail to recognize the value of the company’s telehealth infrastructure, customer base, and broadening treatment offerings.
Amazon Intensifies Competition With Foundayo Launch
Competitive dynamics became more challenging Thursday when Amazon Pharmacy revealed plans to distribute Eli Lilly’s recently authorized oral GLP-1 medication, Foundayo, featuring same-day delivery options. HIMS shares dipped 0.5% following this announcement. Novo Nordisk declined 1.5%.
Foundayo represents a once-daily oral therapy designed for adults managing obesity or overweight conditions with related health complications. Pricing begins at $25 monthly with insurance coverage, or $149 monthly for self-pay patients.
Amazon will provide same-day delivery across nearly 3,000 metropolitan areas, with plans to extend coverage to 4,500 locations before year-end. The e-commerce giant disclosed it has distributed GLP-1 medications since 2021, with customers saving over $200 million through automated coupon programs, where GLP-1 treatments represent the largest savings category.
Wall Street consensus on HIMS currently stands at Moderate Buy, based on four Buy ratings and 10 Hold ratings issued during the past three months. The mean price target of $26.36 suggests potential upside of approximately 36% from present trading levels.
Crypto World
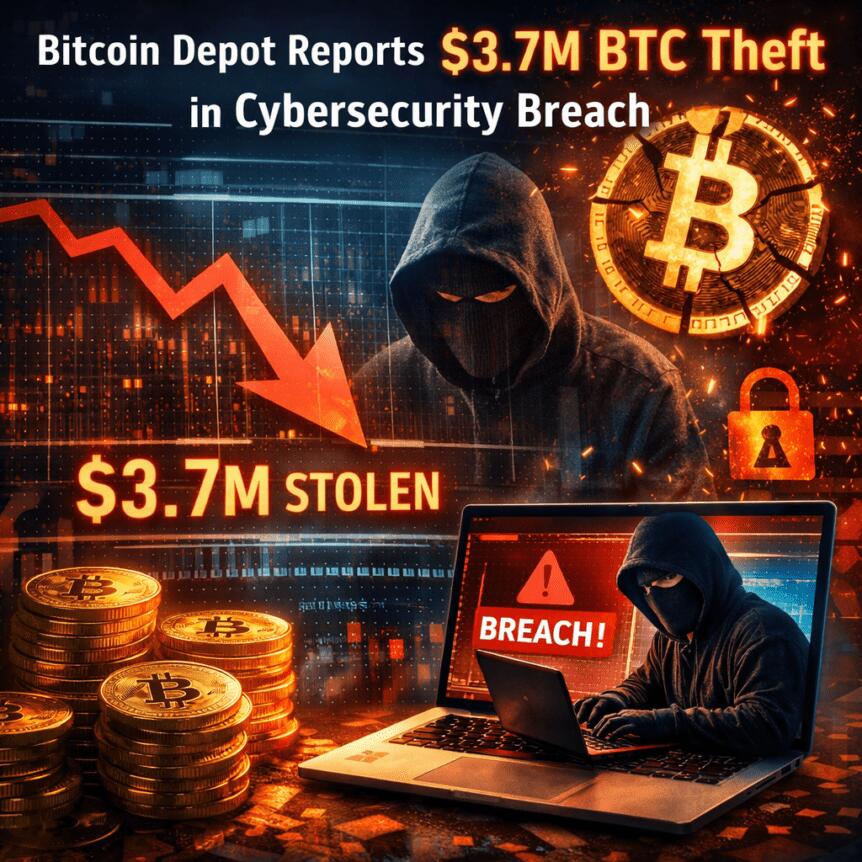
Bitcoin (BTC) trades flat as index declines
CoinDesk Indices presents its daily market update, highlighting the performance of leaders and laggards in the CoinDesk 20 Index.
The CoinDesk 20 is currently trading at 1982.06, down 0.6% (-12.51) since 4 p.m. ET on Wednesday.
One of 20 assets is trading higher.

Leaders: ICP (+1.5%) and BTC (+0.0%).
Laggards: AAVE (-3.6%) and XLM (-2.7%).
The CoinDesk 20 is a broad-based index traded on multiple platforms in several regions globally.
Crypto World
ADA could dip lower under broader market pressure


Key takeaways
- ADA is down 3% and is now trading around $0.2512 per coin.
- The bearish performance could see ADA slip below the $0.2400 support level.
Cardano (ADA) faces renewed selling pressure as bullish interest fades
Cardano (ADA) continues to face significant selling pressure, with the cryptocurrency extending its 4% loss from Wednesday, falling to the $0.2500 at the time of writing on Thursday.
The decline has been driven by intense long liquidations in ADA futures over the last 24 hours, signaling a diminishing bullish sentiment among traders. For a potential recovery, Cardano must reclaim the 50-day Exponential Moving Average (EMA) at $0.2672.
The broader market sentiment remains mixed, as the US-Iran ceasefire risks being undermined by Israel’s ongoing missile strikes on Lebanon. While Cardano futures initially saw some bullish interest following Tuesday’s ceasefire announcement, this has since diminished.
Data from CoinGlass reveals that liquidated ADA derivatives positions over the past 24 hours totaled $602,370, with $544,540 coming from long liquidations, indicating a significant wipeout of bullish positions. This liquidation pressure has contributed to an 6% drop in ADA futures Open Interest (OI), which now stands at $412.36 million.
Furthermore, the OI-weighted funding rate dropped to -0.0045% on Thursday, indicating that traders are increasingly shifting towards short positions.
ADA could dip below the $0.2400 support level
The ADA/USD 4-hour chart remains bearish and efficient following the recent day. ADA is currently trading below the 50-, 100-, and 200-day Exponential Moving Averages (EMAs).
Momentum indicators only hint at tentative stabilization rather than a clear bullish shift. The Moving Average Convergence Divergence (MACD) shows a marginally positive reading, while the Relative Strength Index (RSI) at 53 hovers just above the neutral midline level.

If the selloff continues, ADA could slip towards the March 29 low at $0.2328, with the February 6 low at $0.2205 providing further support.
On the flip side, if the bulls regain control, they would encounter initial resistance at the 50-day EMA around $0.2673. A daily close above this barrier would ease the immediate bearish tone and open the way toward the $0.2991 resistance level.
Crypto World
XRP Ripple Just Outpaced Bitcoin in Weekly ETP Inflows: Is $120 Million a Sign Institutions Are Loading Up?
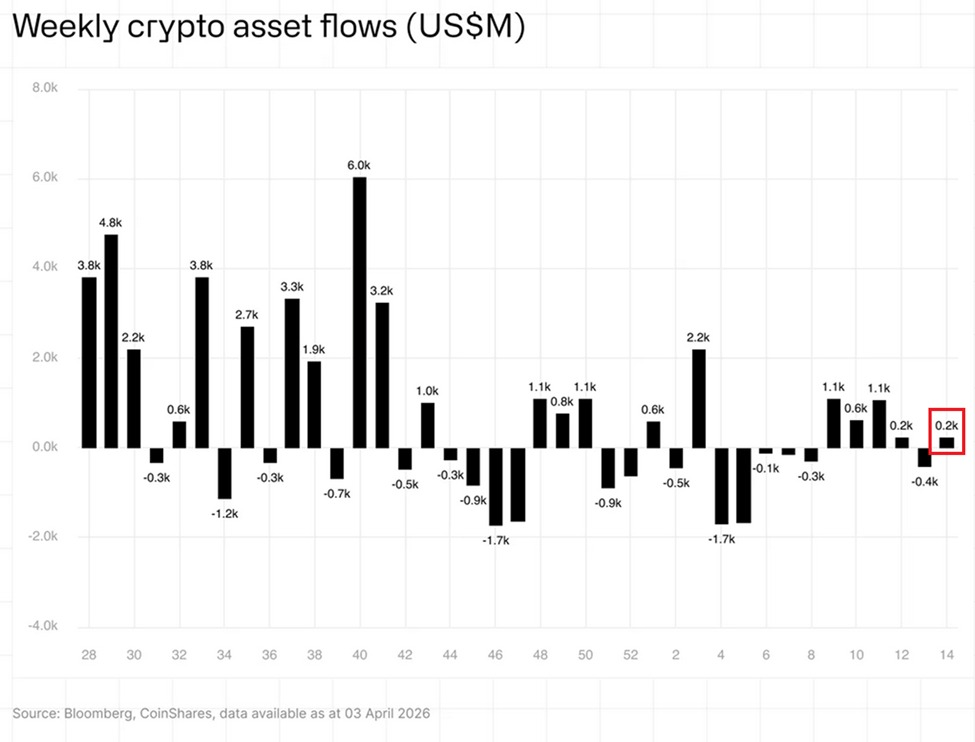
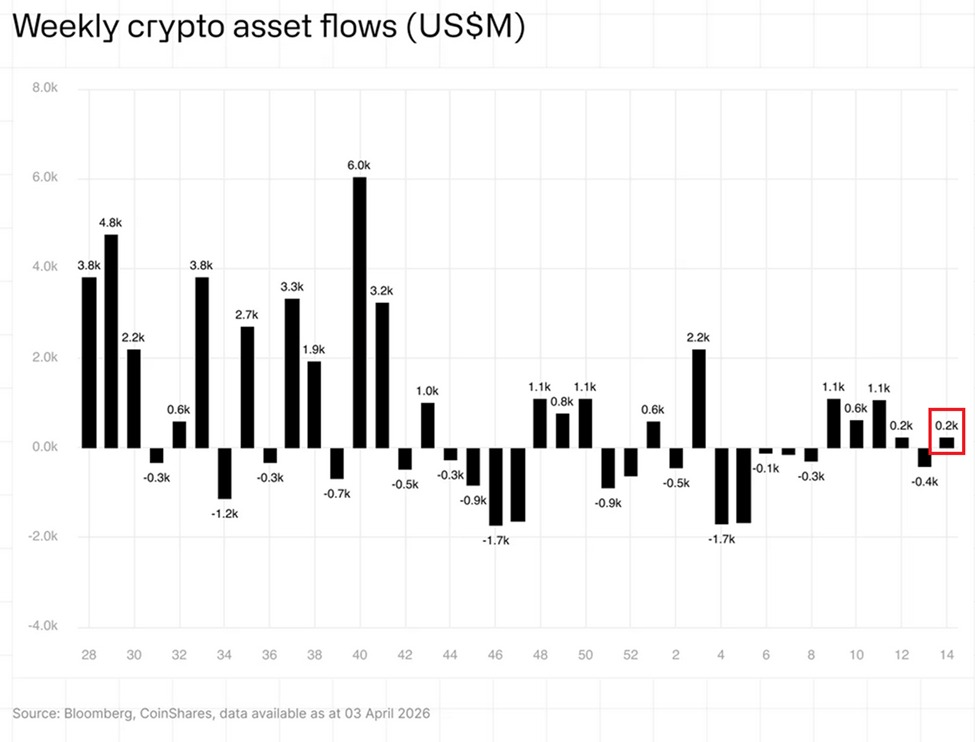
Ripple XRP recorded $120 million in weekly ETP inflows for the period ending April 7, 2026 – its strongest weekly haul since mid-December 2025 and the single largest contributor to global crypto ETP inflows that week, according to CoinShares data.
Total global crypto ETP inflows for the week hit $224 million, rebounding sharply from a prior $414 million outflow.
XRP’s $120 million slice outpaced Bitcoin’s $107 million and Solana’s $35 million, accounting for over 50% of the entire market’s weekly intake.
The core question now: is institutional investment in XRP building a permanent structural position, or is this a single-week rotation that evaporates on the next macro shock?
Discover: The best crypto to diversify your portfolio with
Ripple XRP Price Outlook: Can XRP Break $1.50 as Institutional Money Arrives?
Ripple XRP was trading in the $1.35–$1.40 range during the inflow week, posting a 5–6% weekly gain partially driven by US-Iran ceasefire optimism. The recovery looks constructive on the surface. Dig into the chart structure and the picture is considerably more complicated.
The 3-day chart is showing a death cross – the 50-day EMA has crossed below the 200-day EMA. That same pattern preceded a 54% price collapse in January 2026.

RSI sits near 44 on the daily, not yet oversold but well below the 50 neutral line, reflecting a market still in damage-control mode rather than recovery mode.
Key support levels sit at $1.28, $1.18, and $1.05 – the last being a major structural floor from the pre-ETF launch period. On the resistance side, XRP faces a descending trendline from early March capping near $1.48, with $1.65 and $1.85 as the next meaningful ceilings if that line breaks with volume.
Derivatives open interest has been declining alongside the price recovery, which signals thin conviction behind the bounce – institutions buying ETPs aren’t the same as leveraged longs pushing spot price.
A clean breakout above $1.48 with sustained daily volume opens the door to $1.65, with $1.85 as the macro target if broader crypto sentiment flips.
For us, the invalidation is simple: a close below $1.28 on the daily reopens the path to sub-$1.10 and calls the entire inflow thesis into question. Prior price analysis on the $119.6M inflow week flagged this same trendline resistance as the decisive level.
Discover: The best pre-launch token sales
Bitcoin Hyper Targets Early Mover Upside as XRP Tests Key Resistance
XRP’s institutional setup is real. But at a market cap north of $75 billion, the math on asymmetric returns gets harder to ignore.
A 10x from current levels requires XRP to reach a market cap larger than Bitcoin’s current valuation – that’s not a trade, that’s a thesis that needs decades and dominant global payment rail adoption to validate.
Bitcoin Hyper (HYPER) is currently in presale, targeting early-mover upside in the Bitcoin yield infrastructure layer – a sector drawing serious institutional attention as US spot Bitcoin ETFs pulled in $471.3 million in a single week.
The presale has raised $32 million to date, with the current token price at $0.0093 and staking APY running at 86% annualized for early participants.
The core technical differentiator: Bitcoin Hyper operates as a Bitcoin-native Layer 2 executing smart contracts with BTC as the settlement asset – bypassing the wrapped-token credit risk that plagues existing BTC DeFi infrastructure. That’s a specific, verifiable architecture claim in a space full of vague interoperability promises.
For traders watching XRP’s institutional flows but frustrated by the price-action disconnect, the asymmetry argument is straightforward: ETP inflows into large-cap assets move sentiment; early presale positioning in infrastructure plays moves portfolios.
Research Bitcoin Hyper here before the presale window closes.
The post XRP Ripple Just Outpaced Bitcoin in Weekly ETP Inflows: Is $120 Million a Sign Institutions Are Loading Up? appeared first on Cryptonews.
-

 NewsBeat7 days ago
NewsBeat7 days agoSteven Gerrard disagrees with Gary Neville over ‘shock’ Chelsea and Arsenal claim | Football
-

 Business7 days ago
Business7 days agoNo Jackpot Winner and $194 Million Prize Rolls Over
-

 Fashion6 days ago
Fashion6 days agoWeekend Open Thread: Spanx – Corporette.com
-

 Business5 days ago
Business5 days agoExpert Picks for Every Need
-

 Business4 days ago
Business4 days agoThree Gulf funds agree to back Paramount’s $81 billion takeover of Warner, WSJ reports
-

 Sports5 days ago
Sports5 days agoIndia men’s 4x400m and mixed 4x100m relay teams register big progress | Other Sports News
-

 Tech2 days ago
Tech2 days agoHow Long Can You Drive With Expired Registration? What Florida Law Says
-

 Business4 days ago
Business4 days agoNo Jackpot Winner, Prize to Climb to $231 Million
-

 Fashion3 days ago
Fashion3 days agoMassimo Dutti Offers Inspiration for Your Summer Mood Board
-
 Tech7 days ago
Tech7 days agoCommonwealth Fusion Systems leans on magnets for near-term revenue
-

 Fashion2 days ago
Fashion2 days agoLet’s Discuss: DEI in 2026
-
Politics6 days ago
Wings Over Scotland | The quality of mercy
-

 Business5 days ago
Business5 days agoAkebia Therapeutics, Inc. (AKBA) Discusses Pipeline Progress and Strategic Focus on Kidney Disease Treatments at R&D Day – Slideshow
-

 Fashion7 days ago
Fashion7 days agoStatement Sunglasses: The Accessory Shaping Modern Fashion
-

 Crypto World1 day ago
Crypto World1 day agoBitcoin recovers as US and Iran Agree a Ceasefire Deal
-

 Politics7 days ago
Politics7 days agoEast Jerusalem Palestinian families eviction orders
-

 Sports7 days ago
Sports7 days agoWhich German players will make final cut?
-

 Fashion7 days ago
Fashion7 days agoFor Love & Lemons’ Spring 2026 Line is for the Romantics
-

 Politics6 days ago
Politics6 days agoWhy so many children are now classified as ‘disabled’
-

 Fashion7 days ago
Fashion7 days agoCoffee Break: Santa Croce Tote












You must be logged in to post a comment Login