Tech
Google introduces AI-generated avatars to YouTube Shorts

A new feature that lets you create an AI avatar with your likeness is now live on YouTube. First in a blog post earlier this year, avatars are designed to be used in Shorts (provided you still them to show up), allowing you to insert yourself into video content in a way that YouTube deems to be safe and secure.
YouTube’s approach to combatting the AI sloppification of the internet and the proliferation of appears to be adding more and more AI features to its platform, framing this latest addition as a tool that gives creators more control of their digital identities. Any video generated using an avatar will feature YouTube’s AI disclosure and include visible watermarks and labels like SynthID and C2PA.
YouTube has published a pretty in-depth on how to create and use an avatar in either the YouTube or YouTube Create app, but here’s a brief summary of how to do it using the former. Once you’ve opened AI Playground, you’ll be taking a “live selfie” that also records your voice. You can then preview your photorealistic virtual self and either proceed with it or redo the process if you’re unhappy with anything. Creating an avatar in the YouTube Create app is broadly similar, but you have to navigate to the My Avatar homepage first.
YouTube recommends that you hold your phone at eye level and keep yourself centered as much as possible. Lighting is also important, as is ensuring your whole face is visible, you’re in a quiet area, and there’s nobody else in the background. You also have to be the account owner to create an avatar, and over the age of 18.
Once you have an avatar you like, you simply type in a prompt and wait for the AI to generate a video, which according to can be up to eight seconds long. Alternatively, YouTube will also let you add an avatar to existing “eligible” Shorts by tapping “Remix” and then “Reimagine” with your avatar selected.
Avatars can be deleted or retaken whenever you like, as can any video with your avatar in it. You can also limit who’s able to remix your videos, but deleting a video with your avatar in it won’t also delete the original video, or that avatar from your account. YouTube will automatically delete any avatar that hasn’t been used to create new video content for three years.
The new avatar feature will roll out gradually, and is the latest in a long line of AI-centric tools and updates YouTube has added to the platform in the last year, including for low-res videos, for creators and an for search results.
Tech
1TB M5 MacBook Pro With 24GB RAM Drops to Lowest Price Ever

Save $200 on an upgraded M5 MacBook Pro 14-inch this weekend – Image credit: Apple
Apple retailers are embroiled in a MacBook Pro price war this weekend, offering a $200 discount on the 1TB M5 14-inch model with an upgrade to 24GB of memory.
You can pick up the 1TB 14-inch MacBook Pro with 24GB of RAM for $1,699 at Amazon and B&H Photo. This reflects a $200 discount off MSRP.
Buy M5/24GB/1TB MacBook Pro for $1,699
Apple recently made an update to make 1TB of storage standard in the MacBook Pro range, eliminating the 512GB SSD option. This model has a bump up to 24GB of memory, which is 8GB more than the standard 16GB found in the entry model.
According to our M5 MacBook Pro Price Guide, Amazon and B&H’s $200 discount delivers the lowest price for the upgraded spec (model number MDE34LL/A).
You can also save on the 2026 MacBook Pro with an M5 Pro or M5 Max chip, which was released in March, with both 14-inch and 16-inch configs marked down. A highlight of the best MacBook Pro deals available today can be found below, with a full rundown of offers in our MacBook Pro Price Guide.
14-inch MacBook Pro M5 deals
14-inch MacBook Pro M5 Pro and M5 Max sale
- M5 Pro, 15C CPU, 16C GPU, 24GB, 1TB, Standard Display: $1,986.50 ($213 off)
- M5 Pro, 15C CPU, 16C GPU, 24GB, 2TB, Standard Display: $2,397 ($203 off)
- M5 Pro, 18C CPU, 20C GPU, 24GB, 2TB, Standard Display: $2,639.99 ($160 off)
- M5 Max, 18C CPU, 32C GPU, 36GB, 2TB, Standard Display: $3,359 ($240 off)
16-inch MacBook Pro M5 Pro and M5 Max discounts
- M5 Pro, 18C CPU, 20C GPU, 24GB, 1TB, Standard Display: $2,549 ($150 off)
- M5 Pro, 18C CPU, 20C GPU, 48GB, 1TB, Standard Display: $2,899 ($200 off)
- M5 Max, 18C CPU, 32C GPU, 36GB, 2TB, Standard Display: $3,699 ($200 off)
- M5 Max, 18C CPU, 40C GPU, 48GB, 2TB, Standard Display: $4,199 ($200 off)
Tech
200,000 MCP servers expose a command execution flaw that Anthropic calls a feature


Anthropic created the Model Context Protocol as the open standard for AI agent-to-tool communication. OpenAI adopted it in March 2025. Google DeepMind followed. Anthropic donated MCP to the Linux Foundation in December 2025. Downloads crossed 150 million. Then four researchers at OX Security found an architectural problem that affects all of them.
MCP’s STDIO transport, the default for connecting an AI agent to a local tool, executes any operating system command it receives. No sanitization. No execution boundary between configuration and command. A malicious command returns an error after the command has already run. The developer toolchain raises no flag.
OX Security researchers Moshe Siman Tov Bustan, Mustafa Naamnih, Nir Zadok and Roni Bar scanned the ecosystem and found 7,000 servers on public IPs with STDIO transport active — and estimate 200,000 total vulnerable instances extrapolated from that ratio. They confirmed arbitrary command execution on six live production platforms with paying customers. The research produced more than 10 CVEs rated high or critical across LiteLLM, LangFlow, Flowise, Windsurf, Langchain-Chatchat, Bisheng, DocsGPT, GPT Researcher, Agent Zero, LettaAI and others.
Kevin Curran, IEEE senior member and professor of cybersecurity at Ulster University, independently told Infosecurity Magazine the research exposed “a shocking gap in the security of foundational AI infrastructure.”
Anthropic confirmed the behavior is by design and declined to modify the protocol — characterizing STDIO’s execution model as a secure default and input sanitization as the developer’s responsibility. That characterization comes from OX; the only word Anthropic explicitly stated on the record is “expected.” Anthropic has not issued a standalone public statement and did not respond to VentureBeat’s request for comment.
OX says expecting 200,000 developers to sanitize inputs correctly is the problem. Anthropic’s strongest technical counter: sanitizing STDIO would either break the transport or move the payload one layer down. Both positions are technically coherent. The question is what to do while that debate plays out.
Every major outlet covered the disclosure. None built the prescriptive product-by-product audit a security director needs to triage her own MCP deployments. This piece does.
Five questions determine whether your MCP deployments are exposed, whether your patches hold, and what to do Monday morning.
Am I exposed?
If your teams deployed any MCP-connected AI agent using the default STDIO transport, yes. The insecurity is not a coding bug in any single product. It is a design default in Anthropic’s MCP specification that propagated into every official language SDK: Python, TypeScript, Java, and Rust. Every downstream project that trusted the protocol inherited it.
OX identified four exploitation families. Unauthenticated command injection through AI framework web interfaces, demonstrated against LangFlow and LiteLLM. Hardening bypasses in tools that implemented command allowlists, demonstrated against Flowise and Upsonic, where OX bypassed the allowlist through argument injection (npx -c). Zero-click prompt injection in AI coding IDEs, where malicious HTML modifies local MCP configuration files. Windsurf (CVE-2026-30615) was the only IDE where exploitation required zero user interaction, though Cursor, Claude Code, and Gemini-CLI are all vulnerable to the broader family. And malicious package distribution through MCP registries, where OX submitted a benign proof-of-concept to 11 registries, and nine accepted it without security review.
Carter Rees, VP of AI and Machine Learning at Reputation and member of the Utah AI Commission, told VentureBeat the framing needs to change entirely. “MCP stdio is a privileged execution surface, not a connector. Enterprise teams should treat it like production shell access. Deny by default, allowlist, sandbox and stop assuming downstream input validation will hold at scale,” Rees said.
The IDE family deserves particular attention because it hits developer workstations, not servers. A developer who visits an attacker-controlled website can trigger a modification to their local MCP configuration file — and in Windsurf’s case, the change executes immediately with no approval prompt. Cursor, Claude Code and Gemini-CLI require some form of user interaction, but if the UI presents a configuration change without surfacing the execution consequence, clicking ‘approve’ does not constitute informed consent.
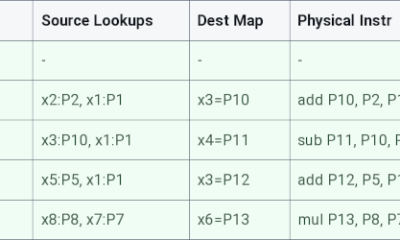
Did my vendor patch?
Some did. Some partially. Some have not confirmed. The matrix below maps each affected product against the exploitation family, patch state, and the gap that remains. The critical column is “Protocol fix?” Every row says no.
|
Product |
Exploit type |
Patched? |
Protocol fix? |
The gap |
Action |
|
LiteLLM |
Command injection via adapter UI |
YES |
NO |
LiteLLM is fixed. New STDIO configs outside LiteLLM inherit the same insecure default. |
Pin to v1.83.7-stable or later (CVE-2026-30623). Verify against GitHub advisory. Audit all other STDIO definitions. |
|
LangFlow |
RCE via public auto_login + STDIO |
Partial |
NO |
Auth token freely available via public endpoint. STDIO executes whatever follows. |
Block public auto_login. Sandbox all MCP services from the host OS. |
|
Flowise / Upsonic |
Allowlist bypass (npx -c argument injection) |
Hardened, bypass confirmed |
NO |
Allowlist gives false confidence. OX bypassed it. Trivial. |
Do not rely on command allowlists. Enforce process-level sandbox isolation. |
|
Windsurf (CVE-2026-30615) |
Zero-click prompt injection to local RCE |
REPORTED, unconfirmed |
NO |
Only an IDE with a true zero-interaction exploit. Hits developer workstations, not servers. |
Disable automatic MCP server registration. Review all active configs manually. |
|
Cursor / Claude Code / Gemini-CLI |
Prompt injection to local MCP config modification |
Cursor patched (CVE-2025-54136); others vary |
NO |
User interaction required, but config-change UI does not surface execution consequence. Approval does not equal informed consent. |
Audit MCP config files (~/.cursor/mcp.json, equivalent paths). Disable auto-registration. Review all pending config changes before approval. |
|
Langchain-Chatchat (CVE-2026-30617) |
RCE via MCP STDIO transport |
REPORTED, unconfirmed |
NO |
Downstream chatbot framework inherits the same STDIO default. Patch status unconfirmed. |
Inventory all Langchain-Chatchat deployments. Sandbox from host OS. Monitor vendor advisory for patch. |
|
MCP registries (9 of 11) |
Accepted malicious PoC without review |
N/A |
NO |
Registries lack submission security review. Install and risk a backdoor. |
Use registries with documented submission review. Audit installs against known-good hashes. |
Does the flaw survive the patch?
Yes. Every product-level patch in the matrix addresses the specific entry point in that product. None of them changes the MCP protocol’s STDIO behavior. A security director who patches LiteLLM today and configures a new MCP STDIO server tomorrow will inherit the same insecure default on the new server. The patches are necessary. They are not sufficient.
This was predictable. When VentureBeat first reported on MCP’s security flaws in January, Merritt Baer, chief security officer at Enkrypt AI and former deputy CISO at AWS, warned: “MCP is shipping with the same mistake we’ve seen in every major protocol rollout: insecure defaults. If we don’t build authentication and least privilege in from day one, we’ll be cleaning up breaches for the next decade.” The Cloud Security Alliance independently confirmed OX’s findings in a separate research note and recommended organizations treat MCP-connected infrastructure as an active, unpatched threat. The defaults did not change. The attack surface grew.
Rees argued that Anthropic’s position, while internally consistent, does not survive contact with enterprise reality. “It stops being a developer mistake and starts being a distributed failure mode when the same class of failure reproduces across that many independent implementations,” he told VentureBeat. “Guidance is not an architectural control. Relying on thousands of downstream implementers to consistently interpret a trust boundary is a known anti-pattern in enterprise security.”
Anthropic updated its SECURITY.md file nine days after OX’s initial contact in January 2026 to note that STDIO adapters should be used with caution, but made no architectural changes. The researchers’ assessment of that update: “This change didn’t fix anything.”
Rees took a more measured view. “It’s worth giving Anthropic credit where it’s due,” he told VentureBeat. “After the disclosure, they updated their security guidance to recommend caution with stdio adapters. That’s a meaningful step even if researchers argue it falls short of a protocol-level fix.”
What changed at the protocol level?
Nothing architectural. Anthropic has not implemented manifest-only execution, a command allowlist in the official SDKs, or any other protocol-level mitigation. OX recommended all three. The SECURITY.md guidance update was the only change. OX’s research began in November 2025 and included more than 30 responsible disclosure processes across the ecosystem before the April 15 publication.
The disagreement is substantive. Anthropic’s architectural argument deserves its full weight. STDIO is a local subprocess transport designed to launch processes on the machine that configured it. The trust boundary, in Anthropic’s model, sits with whoever controls the configuration file. If you can write to the MCP config, you are by definition someone authorized to execute commands on that machine. Under that logic, what looks like command injection is a feature working as intended. Restricting what STDIO can launch at the protocol level would either break the transport’s core function, since its purpose is to launch arbitrary local processes, or displace the attack surface into the launched process itself. The unopinionated-standard argument is also defensible: a universal protocol that hard-codes execution constraints stops being universal. OX’s counter, from their advisory: “Shifting responsibility to implementers does not transfer the risk. It just obscures who created it.”
Do not wait for a protocol-level fix. Treat every MCP STDIO configuration as an untrusted input surface, regardless of which product it sits inside.
Monday morning remediation sequence
Enumerate. Identify every MCP server deployment across dev, staging, and production. Search for MCP configuration files (mcp.json, mcp_config.json) in developer home directories and IDE config paths (~/.cursor/, ~/.codeium/windsurf/, ~/.config/claude-code/). List running processes that match MCP server binaries. Flag any using STDIO transport with public IP accessibility. OX found 7,000 on public IPs. Your environment may have instances you do not know about.
Patch. Pin every affected product to its patched release. LiteLLM v1.83.7-stable includes the fix for CVE-2026-30623. DocsGPT, Flowise, and Bisheng have also shipped fixes. Windsurf and Langchain-Chatchat remain in reported state as of May 1, 2026. Cursor was patched against an earlier related disclosure (CVE-2025-54136) but inherits the same protocol default. Check each vendor’s advisory in the morning you execute this step.
Sandbox. Isolate every MCP-enabled service from the host operating system. Never give a server full disk access or shell execution privileges. The Flowise/Upsonic allowlist bypass proves that restricting commands alone is not enough.
Audit registries. Review every MCP server installed from a third-party registry. Nine of 11 registries accepted OX’s proof-of-concept without a security review. Use registries with documented submission review processes. Remove any MCP server whose origin you cannot verify.
Treat STDIO config as untrusted. This step survives every future patch and every future product. The protocol-level default has not changed. Every STDIO server definition is a command execution surface. Treat it the same way you treat user input to a database query: assume it is hostile until validated.
Your exposure cannot wait for a protocol fix
Anthropic and OX Security disagree on where the responsibility for securing MCP’s STDIO transport belongs. That disagreement will not be resolved this week. What can be resolved this week is whether your MCP deployments are enumerated, patched, sandboxed, and treated as the untrusted execution surfaces they are.
As Rees put it: “The core question here is architectural policy, not exploit payloads.” Baer warned in January that insecure defaults would produce exactly this outcome. OX documented 200,000 servers running with a configuration field that doubles as an execution surface. The protocol’s designer says it is working as intended. Your Monday morning question is not who is right. It is which of your servers are exposed.
Tech
Nvidia could bring back the RTX 3060 12GB in July as memory crisis continues


The new claims come from the Chinese forum Board Channels. A user writes that production of the RTX 3060 12GB GPUs (as opposed to the 8GB variant) will resume in June before being allocated to add-in card manufacturers, with the retail (re)launch coming in July. The card was originally discontinued…
Read Entire Article
Source link
Tech
OpenAI Enables Marketing Cookies by Default for Free ChatGPT Users
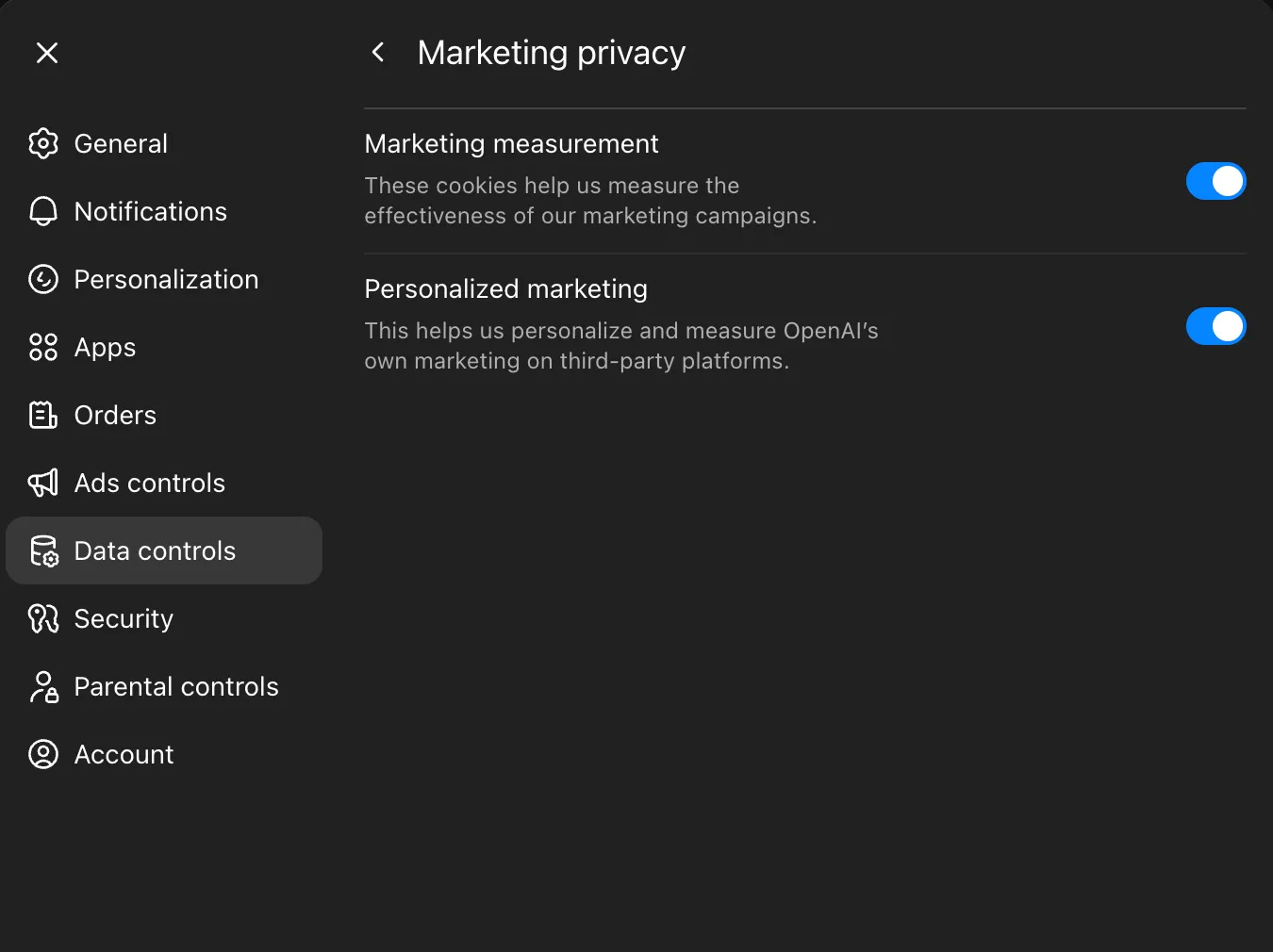
OpenAI is ready to target free users of its services with advertisements around the web, based on what it knows about them.
On Thursday, OpenAI sent an email to users laying out major changes to the AI company’s privacy policy in the US. “We’ll now use cookies to promote OpenAI products and services on other websites,” reads the email sent on April 30. “This does not impact your conversations in ChatGPT. Your conversations with ChatGPT are private and are not shared with marketing partners.” Cookies store information in users’ browsers as they explore the web.
Chats with the bot aren’t shared with third parties. Even so, details OpenAI collects as users interact with its services may soon be used to market those same services, like ChatGPT, outside the platform. This appears to be targeted at converting free users (WIRED found that marketing settings were “on” by default) and seeing how effective its ads are at conversions.
The move comes as OpenAI looks to expand its own advertising network inside ChatGPT. The company started rolling out ads at the bottom of ChatGPT outputs for US users in February. Competitors including Google are exploring how ads can be woven into the user experience of generative AI tools and features.
“Nothing about our policy of not sharing people’s conversations or other private user content with advertisers has changed,” says OpenAI spokesperson Taya Christianson. “Like many companies, OpenAI works with select marketing partners to help people learn about our products on third-party websites and apps, and we updated our privacy policy to clarify how this works. We do not share your conversations with these marketing partners. To make OpenAI marketing efforts more relevant and measure their effectiveness, we may share limited identifiers, such as cookie IDs or device IDs, and users can opt out at any time in settings.”
To help you better understand what recently changed, WIRED compared the new privacy policy to a previous version saved from OpenAI’s website earlier this month. The biggest change revolves around how your data is shared for marketing purposes.
Courtesy of Reece Rogers
Data Usage Now Includes Third-Party Promotions
In the Disclosure of Personal Data section, OpenAI expanded the paragraph detailing how it discloses personal data. OpenAI now says it may share “limited information” with partners to promote services like ChatGPT and Codex off of OpenAI’s platforms.
The company details this change in a new help page. It says it might send identifiers, such as users’ email addresses or cookie IDs, to advertising platforms. That way, OpenAI can check whether users have taken specific actions—like signing up for its Codex tool after they get shown an ad for it on Instagram.
Users can opt out of this kind of tracking by going to Settings > Data Controls > Marketing Privacy on the ChatGPT site. WIRED tested two free accounts and found that those settings were on by default. The two paying accounts WIRED checked, one Plus and the other Enterprise, did not have it on by default.
Old Privacy Policy
We disclose your Personal Data in the following circumstances:
Vendors and Service Providers: To assist us in meeting business operations needs and to perform certain services and functions, we disclose Personal Data to vendors and service providers, including providers of hosting services, customer service vendors, cloud services, content delivery services, support and safety services, email communication software, web analytics services, payment and transaction processors, search and shopping providers, marketing service providers, and information technology providers. We also work with service providers who help us with age and identity verification, and you can learn more here. Based on our instructions, these parties will access, process, or store Personal Data only in the course of performing their duties to us.
New Privacy Policy
We disclose your Personal Data in the following circumstances:
Vendors, Service Providers, and Marketing Partners: To assist us in meeting business operations needs and to perform certain services and functions, we disclose Personal Data to vendors, service providers, and marketing partners, including providers of hosting services, customer service vendors, cloud services, content delivery services, support and safety services, email communication software, web analytics services, payment and transaction processors, search and shopping providers, and information technology providers. We also work with service providers who help us with age and identity verification, and you can learn more here. When we work with Service Providers, these parties will access, process, or store Personal Data based on our instructions and only in the course of performing their duties to us. We also share limited information with select marketing partners who are not service providers in order to promote our products and services on third-party properties and help us assess the effectiveness of those efforts. Some of these partners may receive information through cookies and similar technologies. Learn more about these practices and the choices available to you here.
Assurance About ‘Sensitive Personal Data’ Removed in Error
OpenAI categorizes many different types of information as a user’s “Personal Data,” including birth dates, payment information, and any prompts a user might have written. In its privacy policies, it doesn’t explain which types of this data it considers “sensitive,” but OpenAI does promise that it doesn’t use this information to infer characteristics about consumers.
A sentence regarding “sensitive Personal Data” was briefly absent from the Privacy Policy on Friday as WIRED accessed the updated document. When WIRED reached out to OpenAI for comment, the company claimed this removal was an error and added a similar sentence back, in a different paragraph.
Tech
A Harvard study shows AI model can outperform physicians in emergency room diagnoses
In one case, a patient came into the emergency department with a pulmonary embolism. The condition initially improved with treatment, then worsened. Doctors suspected the medication was failing. The AI model, using the same electronic health records available at the time, flagged a possible history of lupus – an autoimmune…
Read Entire Article
Source link
Tech
This ultra-cheap, water-based iron battery could last 16 years without degrading


Researchers at the Chinese Academy of Sciences have developed an alkaline all-iron flow battery capable of more than 6,000 charge-discharge cycles without measurable capacity decay, according to a paper published in Advanced Energy Materials. The team estimates that performance is equivalent to around 16 years of daily use.
Read Entire Article
Source link
Tech
Today’s NYT Connections: Sports Edition Hints, Answers for May 2 #585

Looking for the most recent regular Connections answers? Click here for today’s Connections hints, as well as our daily answers and hints for The New York Times Mini Crossword, Wordle and Strands puzzles.
Today’s Connections: Sports Edition features a mix of difficulty. If you’re struggling with today’s puzzle but still want to solve it, read on for hints and the answers.
Connections: Sports Edition is published by The Athletic, the subscription-based sports journalism site owned by The Times. It doesn’t appear in the NYT Games app, but it does in The Athletic’s own app. Or you can play it for free online.
Read more: NYT Connections: Sports Edition Puzzle Comes Out of Beta
Hints for today’s Connections: Sports Edition groups
Here are four hints for the groupings in today’s Connections: Sports Edition puzzle, ranked from the easiest yellow group to the tough (and sometimes bizarre) purple group.
Yellow group hint: Steel City sports.
Green group hint: Baseball info.
Blue group hint: She shoots, she scores!
Purple group hint: Giddy up!
Answers for today’s Connections: Sports Edition groups
Yellow group: A Pittsburgh athlete.
Green group: Seen on an MLB scorebug.
Blue group: Teams in the PWHL playoffs.
Purple group: Horse racing Triple Crown winners.
Read more: Wordle Cheat Sheet: Here Are the Most Popular Letters Used in English Words
The completed NYT Connections: Sports Edition puzzle for May 2, 2026.
What are today’s Connections: Sports Edition answers?
The yellow words in today’s Connections
The theme is a Pittsburgh athlete. The four answers are Panther, Penguin, Pirate and Steeler.
The green words in today’s Connections
The theme is seen on an MLB scorebug. The four answers are count, inning, outs and score.
The blue words in today’s Connections
The theme is teams in the PWHL playoffs. The four answers are Charge, Fleet, Frost and Victoire.
The purple words in today’s Connections
The theme is horse racing Triple Crown winners. The four answers are Affirmed, Citation, Justify and Whirlaway.
Tech
Seattle mayor’s ‘bye’ to millionaires who leave state over taxes is no laughing matter to some in tech


Seattle Mayor Katie Wilson is being greeted with a bit of backlash over a recent “goodbye.”
During a conversation earlier this month at Seattle University, Wilson offered her take on the supposed threats of millionaires in Washington state who say tax policy will drive them to leave.
“I think the claims that millionaires are going to leave our state are, like, super overblown. And if — the ones that leave, like, bye,” Wilson said while offering a wave before laughing amid cheers from the crowd. (See the exchange at 39:09 in video below.)
The comments, which resurfaced online this week, have drawn criticism from some in Seattle’s tech community, who see them as emblematic of a broader hostility toward business in the region.
Wilson was joined by King County Executive Girmay Zahilay for an April 14 conversation with moderators about how their progressive approaches to politics and policies shape the future of the Puget Sound region. Both were elected in November.
The mayor was asked whether she thought progressive taxes — like the state’s recently passed 9.9% tax applied to taxable, personal annual income that exceeds $1 million — are an “easy and promising solution.”
“As someone who has been fighting for progressive taxes for a very long time, I can tell you they are not easy,” Wilson said, adding that she was “excited” to see the so-called millionaires tax pass the state Legislature.
Wilson acknowledged that Washington’s tax structure remains heavily regressive overall, and said her office is actively exploring progressive taxation options available to the city. While she noted that Seattle has more local taxing flexibility than the county, she cautioned that Seattle can’t stray too far from its neighbors — pointing to Bellevue as an example — without risking its competitiveness as a place to do business.
GeekWire reached out to the mayor’s office for comment and we’ll update if we hear back.
The debate over progressive taxation in Washington state has been building for months, with the tech community largely — though not uniformly — alarmed by what it sees as a hostile policy environment.
When the millionaires tax was still a proposal, a coalition of AI researchers, founders, and investors wrote to Gov. Bob Ferguson urging him to pause both the income tax and a proposed expansion of the capital gains tax, warning that the measures would push top talent and future startups out of the region.
Earlier, some startup leaders called a related capital gains proposal targeting startup equity an “extinction-level event,” with founders testifying in Olympia against the bill. The measure failed to pass.
Prominent voices like Microsoft President Brad Smith have been pointed in their criticism, warning that Washington risks taking its tech sector for granted and urging lawmakers to focus on economic development — not just revenue extraction.
Wilson’s wave and “bye” are drawing fresh scrutiny among some in Seattle’s tech community.
“Seattle is so f**ked,” longtime Seattle investor and entrepreneur Chris DeVore wrote on LinkedIn Friday. “When the person running the city doesn’t seem to understand that all jobs and tax revenue come from private employers, and driving employers away permanently hollows out her capacity to pay for her social programs, it’s clear that we’re in for a rough decade, if not a permanent decline.”
In an opinion piece earlier this month for GeekWire, DeVore expressed his frustration with Democrats at both the state and national level today who he said are turning capitalism into the enemy, “pursuing confiscatory tax policies that villainize entrepreneurial wealth.”
Charles Fitzgerald, another Seattle-area investor, warned earlier this year on GeekWire about the danger of Seattle becoming “the next Cleveland,” stating that the city’s success could unravel quickly in the wake of a deteriorating business environment.
On his Platformonomics blog on Friday, Fitzgerald posted several items — including a New York Post story about Wilson’s comments — under the “Don’t be Cleveland” header. Others included a report citing record office vacancy rates in Seattle, a downgrading of the state’s credit rating, and more.
Not everyone in the tech community shares the alarm. Jacob Colker, managing director at the AI2 Incubator, pushed back earlier this year on what he called a “breathless narrative” that Seattle is one tax bill away from collapse, arguing that a few points of additional taxation don’t outweigh the region’s deep bench of AI talent, investment capital, and quality of life.
“Should we be thoughtful about tax policy? Heck yeah,” Colker wrote. “But the breathless narrative that Seattle is one bill from collapse is not serious analysis.”
While Wilson’s physical goodbye wave ignited some backlash, a comment on DeVore’s LinkedIn post from Seattle entrepreneur and investor Diego Oppenheimer summed up some of the frustration with a single, wordless emoji comment — the facepalm.
Tech
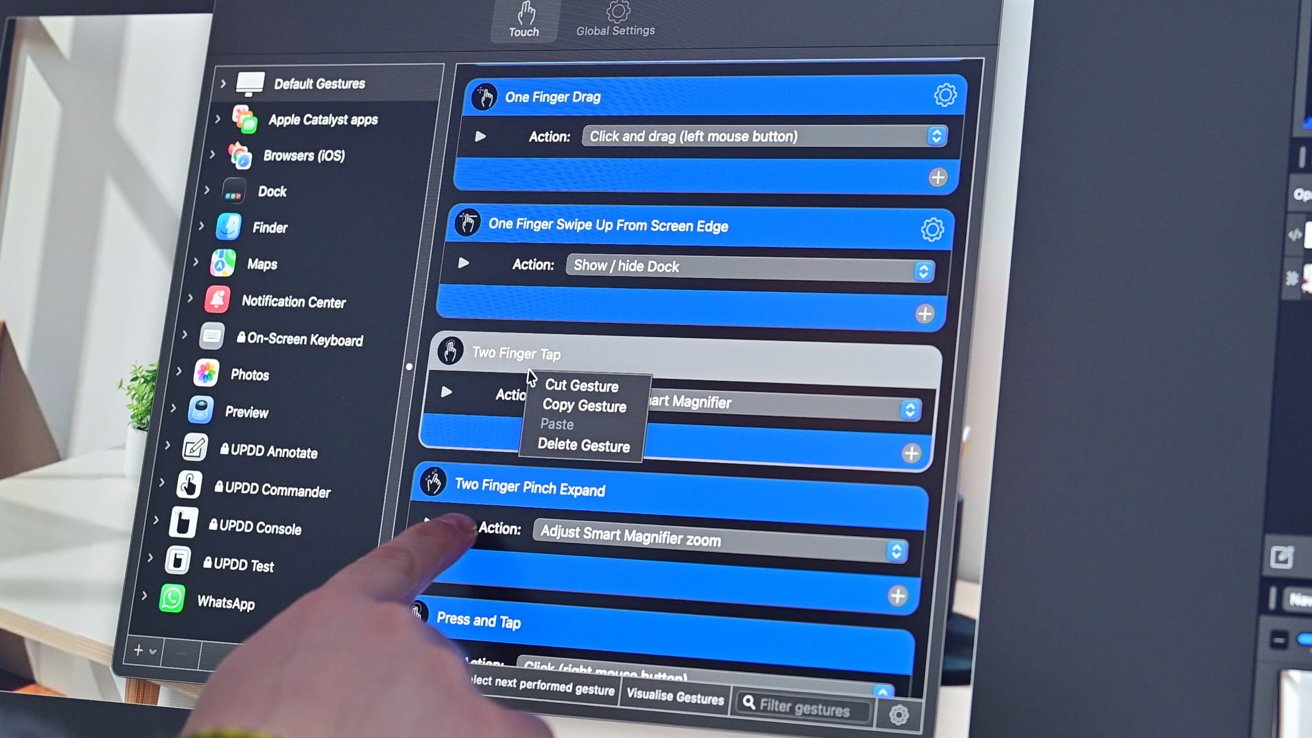
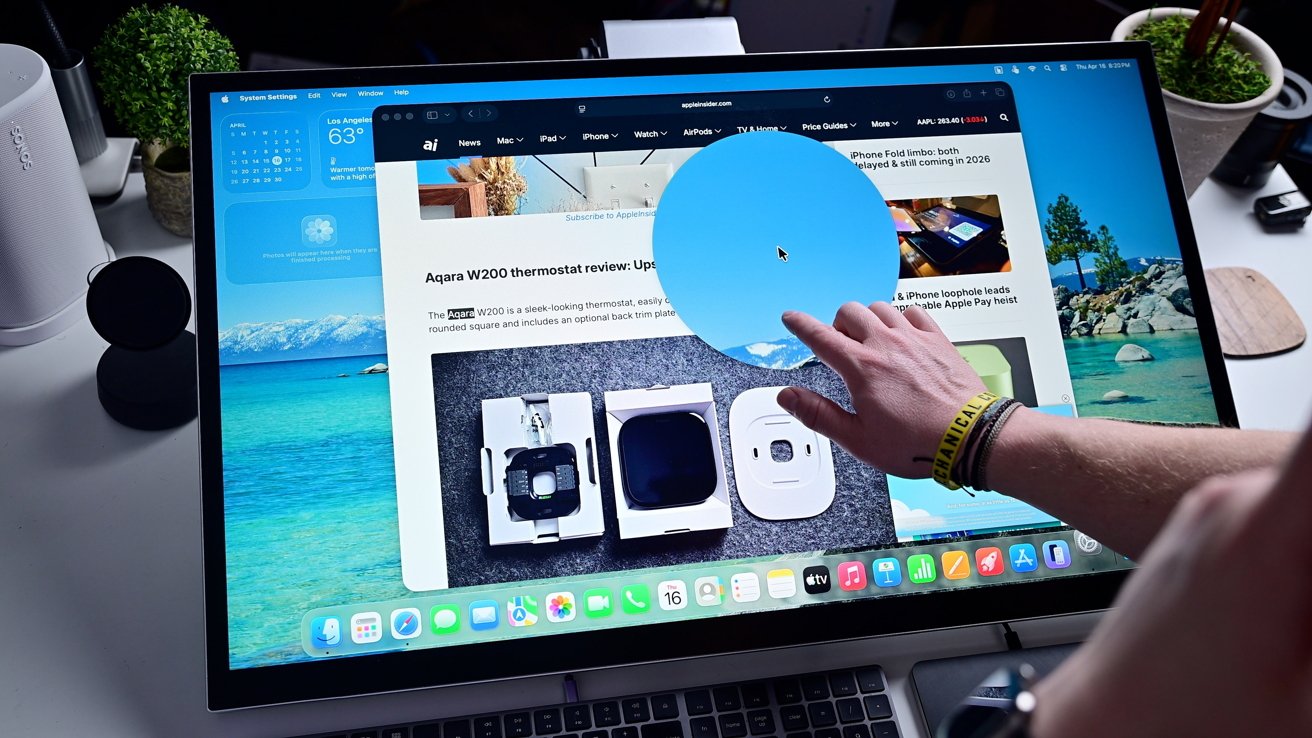
Here’s what a touchscreen Mac may be like

For years, Apple has been rumored to be bringing native touch functionality to the Mac. A new display gives us an early look at what that may be like, for better and worse.
Recently, I got an early look at the Aspekt Touch, a new monitor from Alogic. This isn’t the first touchscreen monitor from the brand, but the tilt functionality combined with macOS Tahoe gives early impressions about how a first-party solution could be implemented.
Feel free to check out Mike’s initial hands-on of the Aspekt Touch, but here’s the high-level. It’s a 32-inch 4K display that is also able to house a Mac mini in the bottom of the stand, and it can tilt nearly flat to be used more comfortably as a touchscreen.
A skeptic, early
I’m conflicted about the idea of a touchscreen Mac. I’ve been a detractor for ages, agreeing with Apple’s official stance that the iPad is the best touchscreen computer.
By and large, I haven’t felt the need for a touch interface on my Mac. Recently, though, that’s started to change.
I’ve gone from using my iPad and the Magic Keyboard over to my Mac and inadvertently kept poking at the display. If the iPad can get trackpad functionality, why can’t we get supplemental touch functionality on the Mac?
After a lot of thought, I think what matters is the approach. Based on current rumors, that approach could be what sets it apart.
Over on iPad, it is designed as touch first, with cursor support added for certain users when it makes sense. On the Mac, it will still be cursor first, with touch added as a supplemental interaction method.
During Windows’ push toward touch-first design, the UI was watered down to accommodate it. The result was a hodgepodge interface that felt smashed together, inconsistent, and didn’t seem to work well.
As long as macOS remains macOS, I think there could be some potential here, and it has been fun to explore with the Aspekt Touch.
Aspekt Touch monitor brings touch to macOS, with caveats
Alogic provides a simple driver package to add touch support to the Mac. You download the installer and grant it a few permissions, and you’re ready to go.
Once done, I could just start tapping away on the large 32-inch screen. I could scroll through Safari, zoom by pinching in and out, and even initiate a right-click.
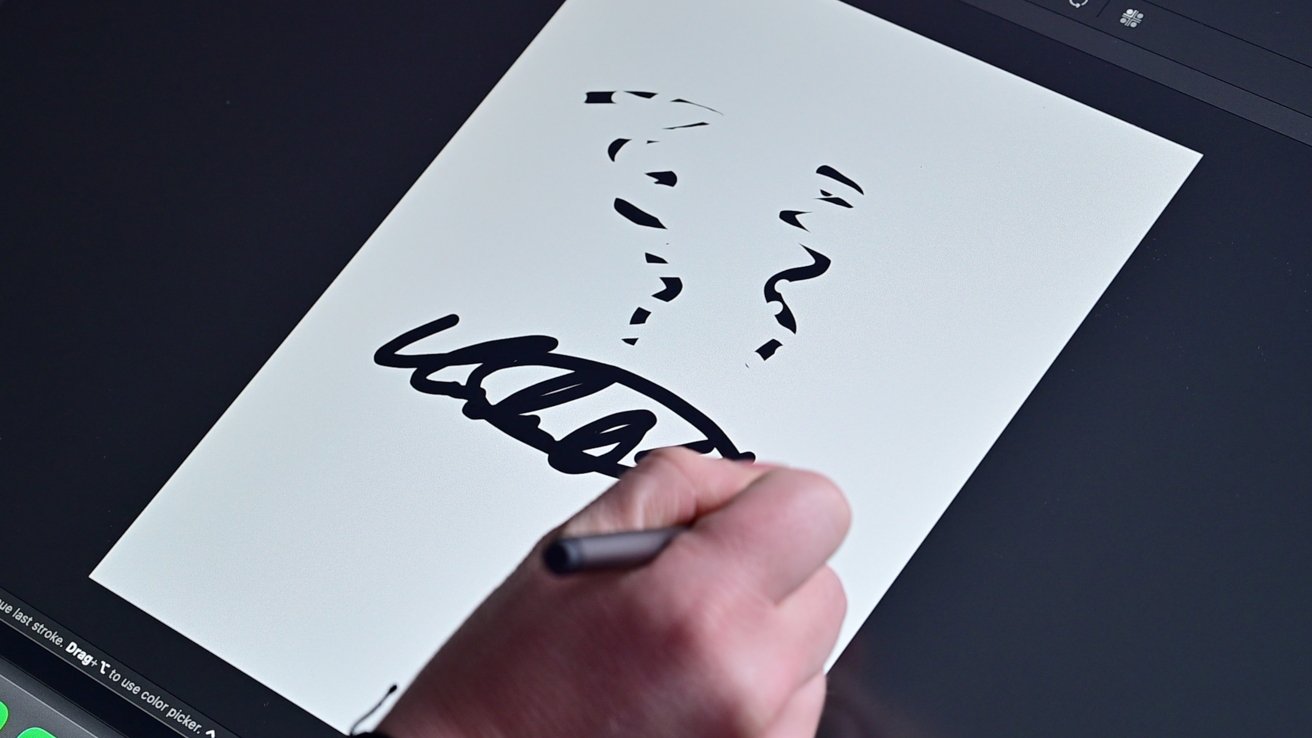
Using the stylus was a solid experience, too. Any capacitive stylus will work, but Alogic has its own with some extra features.
The stylus supports hover effects, so as I work in Affinity, I can see tooltips appear over the different tools. When you flip the stylus around, you can use the other side as an eraser to erase what you’ve drawn.
The stylus supports varying degrees of pressure, and I didn’t seem to have any issues with palm rejection.
When you dig into the Alogic app, you can fine-tune your experience. You can customize the touch effects on a per-app basis to get very granular in how you interact with macOS.
Overall, it’s a solid experience for being added with a third-party plugin. However, a native experience would need to go even further.
Liquid Glass arrives in macOS Tahoe
The problem with the non-native experience is that it’s cobbled together piecemeal from different existing macOS features. There’s no native touch layer that works universally, and many UI elements aren’t designed for touch.
For example, when using the zoom feature, many times it just initiates the magnifier from the accessibility settings. This gets the job done, sure, but not in the way I expected.
I also struggled tapping certain elements, like when editing in Affinity or Pixelmator. The sheer number and size of items made it hard to tap the exact one, especially if I was trying to move with any degree of urgency.
My biggest takeaway was how great Liquid Glass was. The UI elements that were skinned with Liquid Glass were easier to tap and felt more natural.
This offers an early glimpse of how touch functionality might be implemented. Liquid Glass may be divisive, but it suggests a more consistent cross-platform experience, and that includes touch support.
I’d also love to see native support for Apple Pencil. I don’t draw, but I do edit a lot of photos, and Apple Pencil is great for getting that done on iPad.
The Alogic stylus has noticeable lag, which is hardly ideal. I’d like to think that an Apple first-party implementation wouldn’t have that issue, just as it doesn’t on iPad.
Other Apple Pencil features could also debut, like the squeeze gesture to open up a tool palette or maybe something specific for Mac. I’d love it if I could squeeze the Apple Pencil Pro and see a collection of my favorite shortcuts to quickly run.
Probably not a 2026 experience
My biggest concern is that if touch is added, it needs to complement macOS. It shouldn’t try to replace what’s already there.
At the moment, it appears the first touchscreen Mac will be the redesigned M6 OLED MacBook Pro. Clearly, a keyboard and trackpad will be front and center to that experience.
That means we won’t be getting an iPad form factor running macOS, at least any time soon. I think that’s a good thing, but opinions vary amongst the AppleInsider staff, given that the Magic Keyboard with trackpad exists.
We’ll likely have to wait a bit longer to see though, as recent rumors say Apple’s redesigned MacBook Pro, first slated for the end of 2026, is now likely going to ship in early 2027. This isn’t because of developmental reasons, but rather component shortages that are plaguing the industry.
I’m still a bit skeptical here on whether macOS needs touch support or not. After using it for the last couple of weeks, I’m at least leaning towards more “for” than “against” at the moment.
Maybe we’ll get a clearer picture come WWDC with the preview of macOS 27. We’ll find out soon.
Tech
Samsung's chip profit jumped nearly 50-fold in a single year, execs warn the shortage will get worse
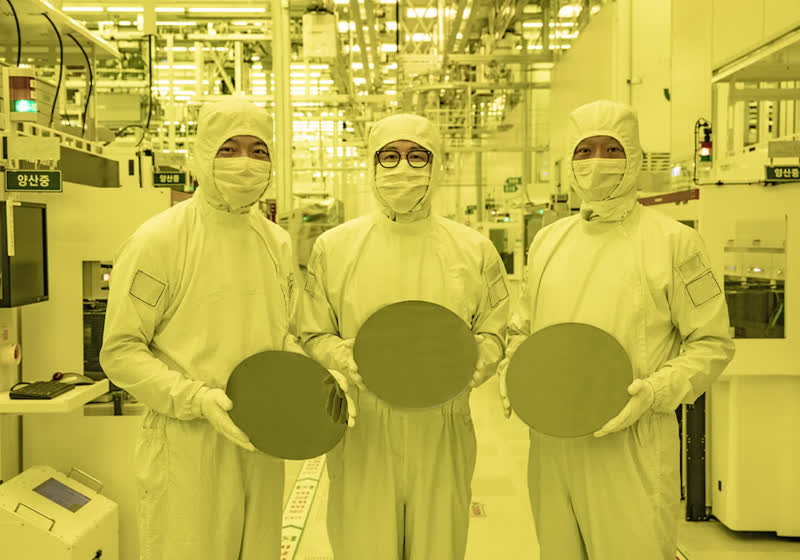
Operating profit in semiconductors climbed to 53.7 trillion won ($36.15 billion) for the January – March period, up sharply from 1.1 trillion won a year earlier. The figure accounted for roughly 94% of Samsung’s total operating profit of 57.2 trillion won. Revenue rose 69% year over year to 133.9 trillion won.
Read Entire Article
Source link
-
 Tech4 days ago
Tech4 days agoRegister Renaming | Hackaday
-

 Crypto World6 days ago
Crypto World6 days agoHyperliquid $HYPE Rally Builds Momentum as AI Sector Enters Prove-It Phase
-
 Politics4 days ago
Politics4 days agoDrax board avoid their own AGM, accused of greenwashing & environmental racism
-

 Tech4 days ago
Tech4 days agoImages of Samsung’s rumored smart glasses have leaked
-

 Tech5 days ago
Tech5 days agoWhy Blue Badges Disappeared From Toyota Hybrids
-

 Sports6 days ago
Sports6 days agoIPL 2026: Ruturaj Gaikwad registers slowest fifty of the season, enters all-time unwanted list | Cricket News
-

 Tech10 hours ago
Tech10 hours agoTrump’s 25% EU auto tariff breaches Turnberry Agreement that also covers semiconductors and digital trade
-

 NewsBeat6 days ago
NewsBeat6 days agoLK Bennett closes all stores after entering administration
-

 Fashion3 days ago
Fashion3 days agoKylie Jenner’s KHY Enters a New Era with ‘Born in LA’
-

 Entertainment6 days ago
Entertainment6 days agoMariah Carey Slams Deposition Claims In Brother’s Lawsuit
-

 Business3 days ago
Business3 days agoMost Commercial Energy Audits Miss the Real Losses
-

 Business5 days ago
Business5 days ago(VIDEO) Charlize Theron Climbs Times Square Billboard to Promote New Netflix Thriller ‘Apex’
-

 Crypto World4 days ago
Crypto World4 days agoCFTC’s AI will review U.S. crypto registration applications, chairman tells CoinDesk
-

 Sports9 hours ago
Sports9 hours agoPaul Scholes issues Marcus Rashford reality check as agreement emerges over Man United star
-

 Tech6 days ago
Tech6 days agoMicrosoft to roll out Entra passkeys on Windows in late April
-

 Business3 days ago
Business3 days agoBarclay Brothers Avoid Bankruptcy: HSBC Drops High Court Petitions After IVA Deal
-

 Tech6 days ago
Tech6 days agoOpenAI’s Sam Altman apologizes for not reporting ChatGPT account of Tumbler Ridge suspect to police
-

 Tech6 days ago
Tech6 days agoOpenAI CEO apologizes to Tumbler Ridge community
-

 Tech4 days ago
Tech4 days agoGet Ready for More Brain-Scanning Consumer Gadgets
-

 Business2 days ago
Business2 days agoTesla Officially Registers Elon Musk’s Stock: What Investors Need to Know















You must be logged in to post a comment Login