Crypto World
Mining Stocks Outperform Bitcoin in 2026 Amid AI Pivot
Publicly traded crypto mining companies are posting strong gains in 2026, even as the broader crypto market remains under pressure.
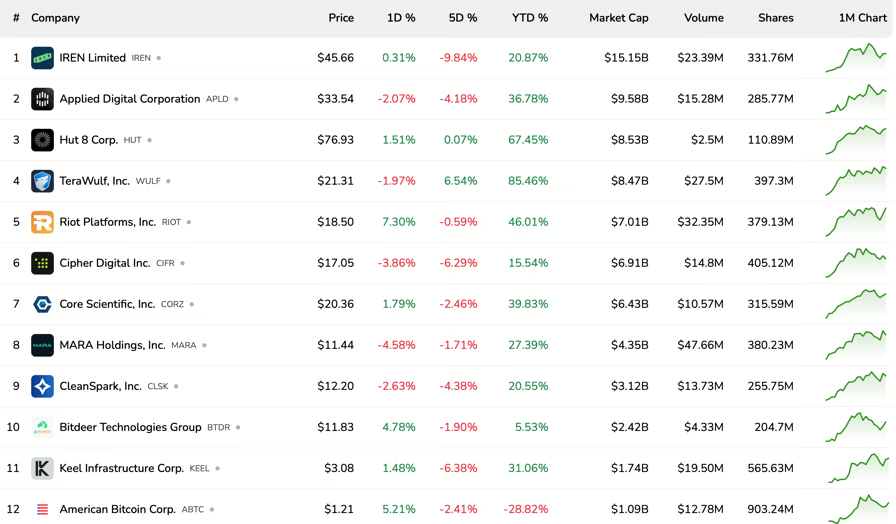
All ten of the largest publicly traded mining stocks are in positive territory year-to-date (YTD), with gains ranging from around 5% to more than 85%, according to data from Bitcoinminingstock.io.

Top Bitcoin mining stocks by market cap. Source: Bitcoinminingstock.io
TeraWulf, Inc. leads the group with gains of about 85%, followed by Hut 8 Corp. at roughly 67% and Riot Platforms, Inc. at around 46%.
Other major miners have also posted strong gains, including Core Scientific, Inc., up about 40%, and Applied Digital Corporation, which has risen roughly 37% year-to-date.
At the lower end, Bitdeer Technologies Group is up around 5%, making it the weakest performer among the top 10. Outside that group, American Bitcoin Corp., a Trump-linked Bitcoin mining and treasury company formed by Hut 8 and backed by Eric Trump and Donald Trump Jr., is down roughly 29%.
The move comes even as Bitcoin (BTC) remains down around 20% YTD, even after gaining about 17% in the past 30 days.

Source: CoinGecko
Related: Canaan, Tether deepen partnership on immersion-cooled mining systems
Top crypto miners move deeper into AI infrastructure
The gains come as many of the largest mining companies push deeper into artificial intelligence and high-performance computing (HPC).
On Thursday, Riot Platforms reported $167.2 million in revenue for the first quarter of 2026, with its data center business contributing $33.2 million, helping offset a decline in core mining revenue. CEO Jason Les described the quarter as an “inflection point,” as the company transitioned into a revenue-generating data center operator.
Core Scientific, Inc. is also scaling its infrastructure, with plans to develop a Texas site into an AI-focused data center campus with up to 1.5 gigawatts of capacity, including about 1 gigawatt available for leasing. The company said roughly 300 megawatts currently used for Bitcoin mining at the site will be repurposed for data center operations.
In February, HIVE Digital Technologies reported a 219% year-over-year jump in quarterly revenue as it built out its AI and high-performance computing business, as well as a $30 million contract to deploy Nvidia GPUs for enterprise AI cloud customers. That same month, MARA Holdings, Inc. acquired a 64% stake in French AI data center company Exaion.
A report from Bernstein last week said IREN Limited, the largest publicly traded miner by market cap, could eventually “sunset” its Bitcoin mining operations as it repurposes sites for GPU-based workloads.
Magazine: Why is Ethereum Foundation selling? BTC futures warning signs: Market Moves
Crypto World
Bitcoin Community Reaches Early Consensus on Quantum Computing Threat, Says Galaxy Digital

TLDR:
- Galaxy Digital Alex Thorn says Bitcoin holders broadly agree Satoshi’s coins should remain untouched.
- Satoshi’s BTC spans roughly 22,000 addresses, making a full quantum attack far harder than many assume.
- Exchanges and active entities can upgrade to post-quantum addresses, reducing their realistic vulnerability.
- Developers broadly support building post-quantum cryptographic tools now and storing them for future use.
The Bitcoin community is gradually forming a shared view on the risks posed by quantum computing. Alex Thorn, Research Director at Galaxy Digital, shared observations from recent discussions held in Las Vegas.
He noted that both skeptics and advocates are beginning to align on key positions. The emerging agreement covers Satoshi Nakamoto’s holdings, post-quantum cryptography development, and how the broader ecosystem should respond.
Satoshi’s Coins and the Case for Non-Interference
A central point of agreement is that Satoshi Nakamoto’s Bitcoin should remain untouched. Thorn noted that interfering with those holdings could seriously damage Bitcoin’s core value proposition around property rights. This position appears to be widely shared across different camps within the community.
Thorn also pointed out that the actual risk may be lower than commonly believed. Nakamoto’s coins are spread across roughly 22,000 addresses, each holding 50 BTC.
As he noted in a post on X, “a long range attack would have to crack them all,” meaning it is not a single concentrated target.
The larger risks, Thorn explained, sit with exchanges and active entities holding large amounts of Bitcoin. However, those parties can upgrade to post-quantum addresses when needed, reducing their vulnerability. This makes them less of a realistic target compared to concerns raised in earlier discussions.
Additionally, Thorn referenced the “hourglass proposal” as a potential measure if a long-range quantum attack ever appeared imminent.
He also cited data showing that Bitcoin markets have routinely absorbed over one million BTC in sell pressure. Even a sharp drawdown from Satoshi’s coins being cracked would likely be manageable, and most Bitcoin holders would accept that trade-off to preserve property rights.
Developing Post-Quantum Cryptography as a Precaution
The second area of emerging agreement involves post-quantum cryptographic research. Most people Thorn spoke with agree that developing new cryptographic tools for Bitcoin is a worthwhile effort. The work includes testing, signature compression, and debating how it could eventually be implemented.
There are, however, recognized risks with moving too fast. Thorn outlined concerns such as diverting developer resources, introducing untested technology into the protocol, and creating consensus gridlock that could stall other upgrades. These risks make the timeline and approach important factors.
A broadly accepted middle ground appears to be developing a post-quantum solution and placing it “on the shelf” for when or if it becomes necessary.
This approach allows preparation without forcing premature changes to the protocol. Thorn described this as “unequivocally a good thing” based on his conversations.
Thorn closed by noting that even a one percent chance of quantum computing affecting Bitcoin justifies continued work on the issue.
He also acknowledged that urgent warnings about the threat have helped push these critical discussions forward within the developer community.
Crypto World
Bitcoin Tests $78.6K Resistance for the Seventh Time as Liquidity Builds Above
TLDR:
- Bitcoin has tested the $78,657 daily resistance seven consecutive times since April 22 without a confirmed breakout.
- Open Interest fell just 0.69% while price advanced, pointing to spot demand rather than leveraged futures driving the move.
- Funding Rates briefly hit -2.24% on May 1, reflecting extreme short pressure and a potential setup for a rapid squeeze.
- A dense liquidity zone from $79.5K to $81K on the heatmap makes $82K the next natural target if $78.6K breaks cleanly.
Bitcoin is testing a key daily resistance at $78,657 on May 2. Since April 22, the price has challenged this zone seven times without a confirmed breakout.
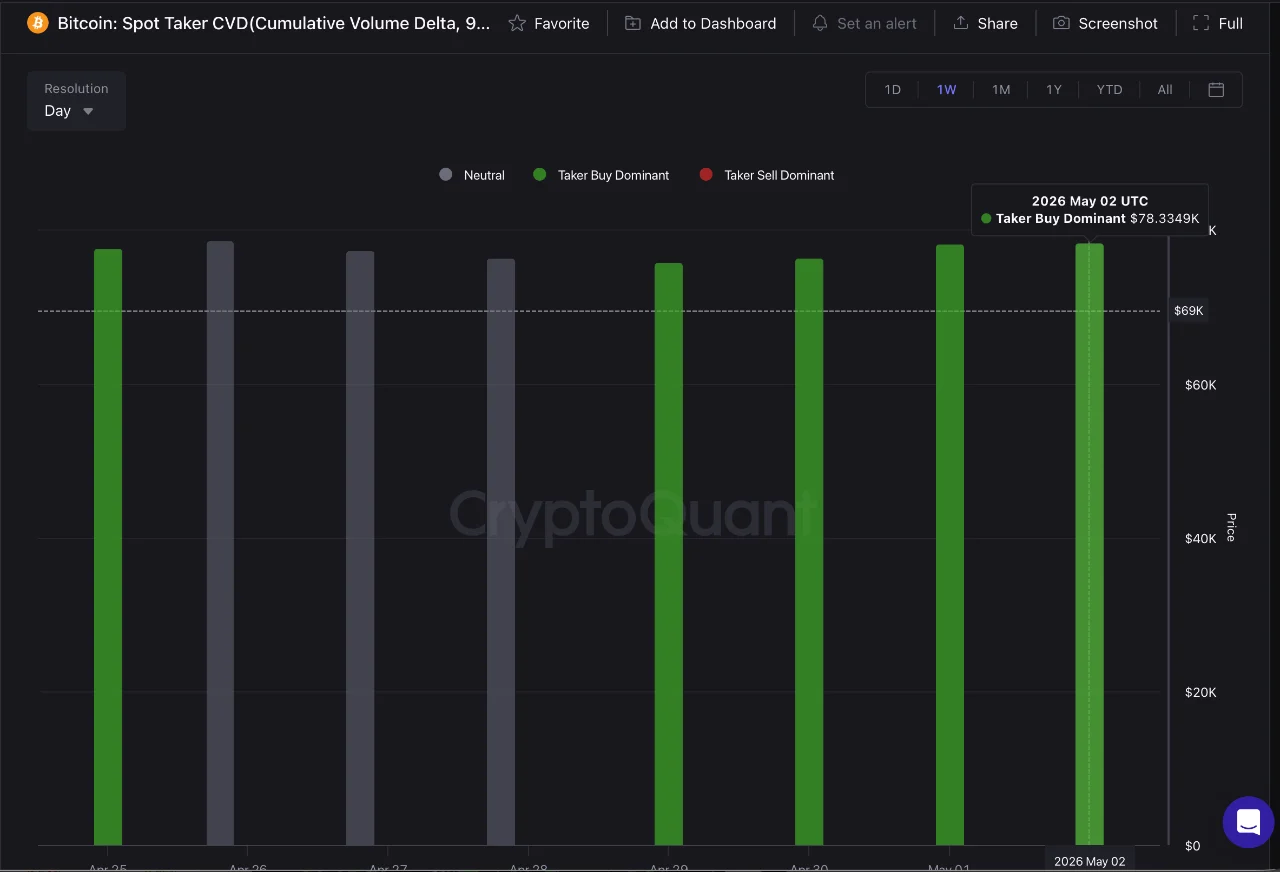
The Spot Taker CVD shows active buy-side demand, yet resistance keeps absorbing it. Derivative data adds tension to the picture.
A dense liquidity zone between $79.5K and $81K sits just above. This makes the current level critical for Bitcoin’s next major directional move.
Spot Demand Drives Price but Falls Short of a Breakout
The Spot Taker CVD is currently green, confirming buy-side dominance in spot markets. Even so, Bitcoin has not broken above $78,657 with clear conviction.
Source: Cryptoquant
The resistance zone continues absorbing incoming demand at a steady pace. Spot buyers remain active but not yet strong enough to force a clean breakout.
Meanwhile, Open Interest recorded only a minor decline during this period. It dropped from 26.737M to 26.552M, a fall of roughly 185M, or just 0.69%.
During that same window, the price moved from $78,480 up to $78,585. The recent advance was not driven by a fresh expansion in leveraged futures positions.
The pattern of rising prices alongside declining open interest points to spot-led action. When spot demand drives a move rather than futures, the resulting structure tends to be more stable.
A breakout could also occur through aggressive futures inflows. However, spot support would give any breakout a higher structural quality.
Crypto analyst Carmelo Alemán observed that buy-dominant spot activity aligned with minimal open interest change. This setup separates the current attempt from previous failed bids at $78,657.
It points to organic demand rather than speculative positioning. Buyers appear to be gradually building pressure at a firm resistance level.
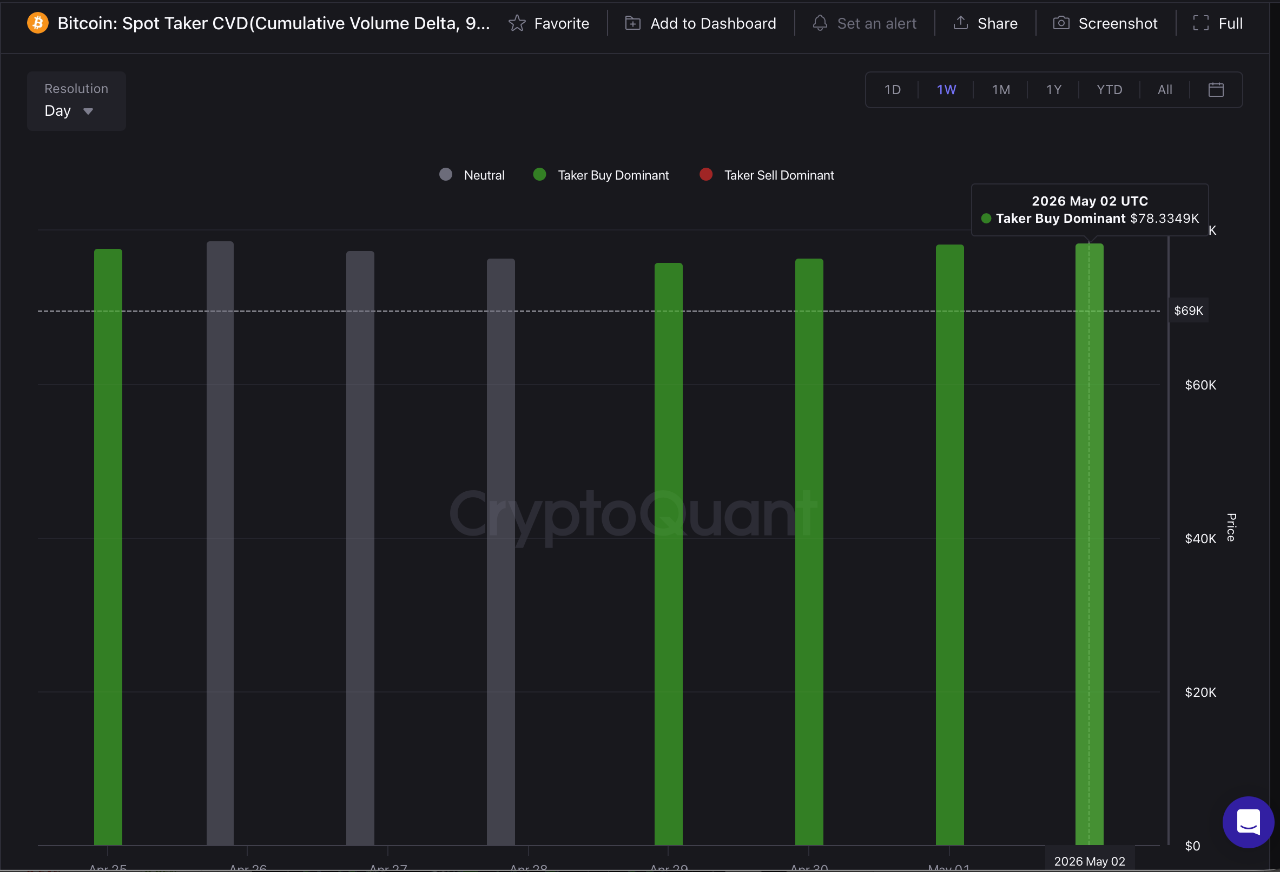
Funding Rate Extremes and Liquidity Zones Define the Upside Risk
The 1-minute Funding Rates showed extreme negative readings on May 1, briefly touching near -2.24%. This means short traders were paying long traders at a highly unusual rate.
Source: Cryptoquant
Such sharp funding episodes often reflect short-term market stress. They can also set up rapid price moves when short positions get squeezed.
The Estimated Leverage Ratio currently sits near 0.245, moderate but elevated versus earlier weekly lows. The market is not overly stretched at this reading. That said, any sharp directional move could still trigger meaningful liquidations on either side of the market.
On the liquidity heatmap, the zone from $79.5K to $81K appears clearly loaded. Leveraged positions at 5x and 10x are concentrated throughout this range.
If Bitcoin breaks above $78.6K, this liquidity cluster becomes the immediate upside target. Price momentum could accelerate sharply once the breakout pulls in those positions.
Beyond the $79.5K–$81K zone, $82K emerges as the next natural target for Bitcoin. Yet a clear risk follows any sweep of that liquidity cluster.
As leveraged positions close within that range, upside momentum may begin to fade. A price correction remains possible once the market digests the liquidity sweep above $78.6K.
Crypto World
a16z Calls “Stablecoin” a Leftover Word From Crypto’s Volatile Past


Andreessen Horowitz’s crypto arm says the word “stablecoin” has become a relic of crypto’s volatile early years. The label, the firm argued, will fall out of use as digital dollars settle into mainstream finance.
The firm argued that stability has stopped being the category’s defining feature. The technology has outgrown its original name. It now sits at the center of a global payment system.
Stability is the floor, not the feature
In a post published this week, a16z compared “stablecoin” to “horsepower.” Useful when explaining a new machine through a familiar one, then outdated, then stuck.
The original problem was simple. Wild crypto volatility kept the technology unusable for everyday savings, lending, or payments. Stability solved that. It is now a prerequisite, not the product.
Stablecoins today move value across borders for settlement in seconds, embed into consumer apps, and run on programmable rails. Monthly transfer volumes recently overtook America’s main payment network.
Stablecoin supply has climbed past $300 billion. Corporations are treating dollar-pegged tokens as a payments rail rather than a crypto trading tool.
“Stability is now table stakes. It’s a prerequisite, and not the point,” read an excerpt in the post.
What Replaces “Stablecoin”
a16z expects the category to be renamed quietly. The firm pointed to “digital dollars,” “digital euros,” and “on-chain assets” as alternatives.
Each label, it said, more accurately describes how users will engage with the asset.
The deeper change, it said, is that money now behaves like software, programmable and embedded directly into consumer applications.
The argument lands as the sector climbs to new highs. Firms including Fireblocks, Circle, and Western Union are already building infrastructure around the asset class.
The name, a16z said, may matter less than what comes after it. Whether “digital dollar” replaces the term or it simply fades into ordinary finance, the firm expects users to keep transacting either way.
The post a16z Calls “Stablecoin” a Leftover Word From Crypto’s Volatile Past appeared first on BeInCrypto.
Crypto World
Patoshi Pattern: The Cryptographic Fingerprint Linking Satoshi Nakamoto to 1.1 Million Bitcoin

TLDR:
- Patoshi Pattern: Researcher Sergio Lerner mapped ExtraNonce values across 50,000 blocks, revealing one dominant mining slope.
- The Patoshi miner accumulated 1.1 million BTC in 2009, worth over $115 billion and untouched for 16 years.
- Patoshi deliberately capped his hash rate at 50%, allowing other early miners to win blocks consistently.
- If the dormant stash ever moves, it would trigger the largest single asset liquidation in crypto market history.
The Patoshi pattern, identified over a decade ago, remains one of the most debated findings in Bitcoin’s history. In 2013, researcher Sergio Demian Lerner analyzed the earliest Bitcoin blocks and uncovered a unique mining fingerprint.
His findings pointed to a single miner controlling a massive early stash. That miner, later named “Patoshi,” accumulated approximately 1.1 million BTC. The coins remain untouched to this day, worth over $115 billion.
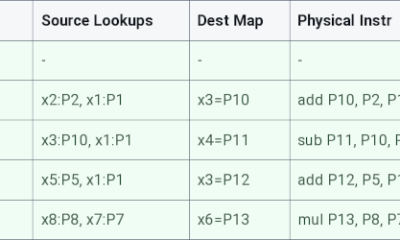
How the ExtraNonce Field Exposed a Single Dominant Miner
Every Bitcoin block contains a small data field called the ExtraNonce. Miners increment this value each time they attempt to generate a block. Different miners produce different ExtraNonce sequences based on their software behavior.
Lerner mapped ExtraNonce values across the first 50,000 Bitcoin blocks. When plotted on a graph, the values formed distinct slopes. Each slope represented a separate miner’s activity.
One slope stood out clearly from the rest. It appeared across roughly 22,000 of the first 36,000 blocks ever mined. The pattern showed consistent timing and identical software behavior throughout.
As @0xSweep noted on X: “Satoshi’s mining code incremented the ExtraNonce field differently than any other miner’s — an unintentional fingerprint built into the original Bitcoin client itself.” Cross-referencing with known transactions involving early developers like Hal Finney led the cryptography community to link Patoshi to Satoshi Nakamoto.
What the Patoshi Pattern Reveals About Satoshi’s Behavior
The Patoshi miner did not attempt to dominate the network completely. In 2009, the Bitcoin network had very few participants. Satoshi’s hardware was effectively the entire network at that time.
However, the data shows Patoshi deliberately limited his hash rate to around 50% of his actual capability. This allowed other miners to win blocks consistently. That behavior points to an intentional decision to support network participation.
The on/off mining pattern also followed a human daily rhythm. Patoshi stopped mining at similar times each day, resembling someone running a computer from a personal workspace rather than an industrial setup.
Around April 2010, the Patoshi pattern disappeared entirely from the blockchain. Satoshi sent his last public message in April 2011 and has not been heard from since. The 1.1 million BTC now sits across approximately 20,000 separate addresses, untouched for 16 years.
The dormant stash carries two possible outcomes for the market. If the coins move, the crypto market would face the largest single liquidation in its history. If they never move, Bitcoin’s true circulating supply is effectively smaller than current figures suggest.
Crypto World
CISA Flags Linux Copy Fail Flaw on Watch List, Crypto Infra at Risk
A new Linux vulnerability dubbed “Copy Fail” could impact most open-source distributions released since 2017, security researchers warn. The flaw enables attackers who have already gained code execution on a system to escalate privileges to root, potentially compromising servers, workstations, and services that form the backbone of crypto exchanges, node operators, and custody providers that rely on Linux for security and efficiency. On May 1, 2026, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) added Copy Fail to the Known Exploited Vulnerabilities (KEV) catalog, highlighting its significant risks to federal and enterprise environments.
Researchers describe the exploit as shockingly simple in principle: a 732-byte Python script, run after initial access, could grant root privileges on affected systems. In a striking assessment, one security observer called the vulnerability almost trivially exploitable, noting that a minimal piece of Python code could unlock administrator rights on many Linux installations.
The vulnerability has drawn attention in crypto circles because Linux powers a large portion of the ecosystem—exchanges, blockchain validators, and custodial services rely on Linux for reliability and performance. If attackers can breach a system’s initial foothold and then escalate privileges, the consequences could range from data exposure to full control of critical infrastructure components.
Key takeaways
- Copy Fail affects major open-source Linux distributions released in the last nine years, posing a broad attack surface for crypto infrastructure.
- Privilege escalation to root can be achieved via a very small Python snippet, provided the attacker already has code execution on the target system.
- Patches landed in Linux mainline on April 1, with CVE assignment on April 22 and public disclosure on April 29, 2026.
- CISA added Copy Fail to the Known Exploited Vulnerabilities catalog on May 1, 2026, underscoring its priority for federal and enterprise networks.
- Public discussion from researchers and security firms highlights how quickly a logic bug can become a universal risk across a broad set of distributions.
What is Copy Fail and why it matters
The core risk stems from a logic bug that allows an attacker, who has already managed to run code on a victim machine, to escalate privileges to the root level. In practical terms, if an attacker can trigger the script to execute on a compromised host, they could gain unfettered control over the system. The claim that a micro-script of about 700 lines of code could unlock root access has amplified concerns across the crypto sector, where Linux-based nodes, wallets, and hot or cold storage services demand robust security postures.
Independent researchers have characterized the flaw as a reminder that privilege-escalation bugs can be as dangerous as remote-code-execution flaws, especially when they arise in matured, widely deployed platforms. In the crypto space, where operators frequently deploy on commodity Linux distributions, a bug like Copy Fail could translate into a direct threat to network integrity, not just data confidentiality.
One prominent researcher in the field publicly highlighted the terse Python-based vector as a warning signal: “10 lines of Python may be all it takes to access root on affected systems.” While this framing emphasizes the exploit’s conceptual minimalism, experts caution that practical exploitation hinges on an attacker’s ability to run arbitrary code on the target host in the first place, which remains a critical prerequisite.
The crypto industry’s reliance on Linux for server infrastructure, validator nodes, and custodial operations amplifies the importance of timely patches and defense-in-depth controls. A compromised Linux host can serve as a pivot to more sensitive components or credentials, underscoring why operators should treat Copy Fail with urgency alongside other server-hardening measures.
From discovery to patch: a tight timeline
Accounts of how Copy Fail came to light reveal a collaborative, high-visibility sequence among researchers, production Linux teams, and security researchers. In a March disclosure cycle, a security firm disclosed to the Linux kernel security community that the flaw existed as a trivially exploitable logic bug affecting major distributions released over the last nine years. The bug’s reach, described as enabling a portable Python script to grant root on most platforms, added urgency to the ongoing patch process.
According to Theori, a cybersecurity firm whose CEO, Brian Pak, was involved in early discovery communications, the vulnerability was reported privately to the Linux kernel security team on March 23. The patching work progressed quickly, with fixes landed in mainline on April 1. A CVE identifier was issued on April 22, and public disclosure followed on April 29 with a detailed write-up and proof-of-concept examples. The rapid sequence from private reporting to public disclosure illustrates how the ecosystem can coordinate to close a critical flaw in a relatively short window, though not before attackers could attempt to weaponize it in the wild.
Industrial and security researchers noted comments from open-source researchers and distributors that the bug’s classification as a “trivially exploitable” logic flaw could portend a wider wave of post-incident scrutiny across Linux-based systems. The discussions also referenced early analyses that a compact Python script could suffice to escalate privileges in the right conditions, which has fueled a broader discussion about hardening practices across distributions and configurations commonly used by crypto operators.
In the crypto-tech community, the patch cycle matters not only for individual servers but for the resilience of entire ecosystems. As operators push for faster deployments and more automated hardening, the Copy Fail episode highlights the value of robust patch management, layered security controls, and rapid response protocols to minimize dwell time for potential attackers.
Implications for crypto infrastructure and the broader Linux ecosystem
Linux’s role in crypto infrastructure is well established. Enterprises running exchanges, node networks, and custodial services rely on Linux’ stability, performance, and security track record. A vulnerability that enables root access after initial access raises questions about supply chain and configuration hygiene across distributed deployments. For example, compromised hosts can become footholds for lateral movement, credential theft, or tampering with critical components such as wallet services or validator clients. The Copy Fail disclosure underscores why operators should prioritize configuration hardening, adherence to least-privilege principles, and timely application of kernel and distribution updates.
Security researchers have emphasized the importance of proactive measures: regular patching, account hardening, restricted network exposure for management interfaces, and monitoring for suspicious activity that may indicate attempts to escalate privileges. While Copy Fail is not a remote-code-execution flaw by itself, its potential impact once locally exploitable is a reminder of the layered approach needed in crypto environments—where even mature systems can harbor dangerous privilege escalation paths if left unpatched.
The KEV listing by CISA adds another layer to the conversation, signaling that Copy Fail is not merely a theoretical risk but an actively exploited or easily exploitable vulnerability in practice. For operators, this means aligning incident response playbooks with KEV advisories, validating patch deployment across all Linux hosts, and verifying that protective measures, such as endpoint monitoring and integrity checking, are in place to identify suspicious privilege escalations.
What readers should watch next
As patches continue to propagate through various distributions and enterprise environments, crypto operators should track both vendor advisories and KEV catalog updates to ensure timely remediation. The Copy Fail incident also invites a broader reflection on Linux security practices in high-stakes crypto contexts: how quickly can organizations detect, patch, and verify that root-level escalations are no longer possible on compromised hosts?
Researchers and distributors alike will likely publish deeper analyses and PoCs to help practitioners validate protections and test configurations. In the meantime, expect continued scrutiny of how privileged access is granted and audited in Linux systems powering key crypto infrastructure. The episode reinforces a basic takeaway for operators: even small, seemingly innocuous bugs can have outsized consequences in a connected, high-assurance ecosystem.
What remains uncertain is how quickly all affected distributions will fully integrate and verify the patches in diverse deployment environments, and how industry-wide best practices will evolve to reduce similar attack surfaces in the future. As the ecosystem absorbs this incident, the focus will likely sharpen on robust update processes, rapid verification, and a renewed emphasis on defense-in-depth practices that safeguard critical crypto services from privilege escalation threats.
Crypto World
Payward Closes Bitnomial Acquisition, Eyes Regulated US Crypto Derivatives
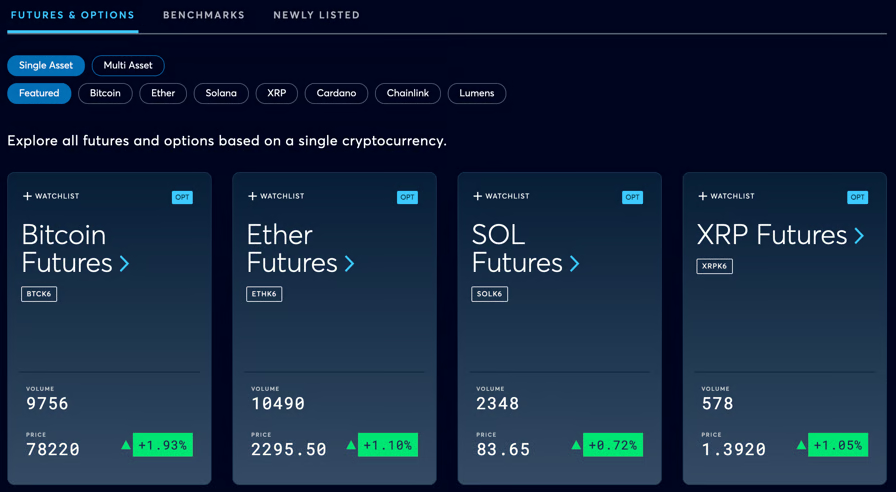
Payward, the parent company of Kraken, announced it has completed its acquisition of crypto derivatives venue Bitnomial, giving it control of a fully CFTC-regulated derivatives stack in the United States.
The acquisition gives Payward a Futures Commission Merchant, Designated Contract Market and Derivatives Clearing Organization, infrastructure it plans to use to expand CFTC-regulated products across Kraken and NinjaTrader, starting with spot margin, with perpetuals and options expected to follow.
Payward said Bitnomial will continue operating within its existing regulatory structure, with the deal enabling partners, including fintechs, banks and brokerages, to access US-regulated derivatives through the company’s infrastructure platform.
The “definitive agreement” to acquire the company was first announced on April 17, when Payward said it would use Bitnomial’s Commodity Futures Trading Commission (CFTC) licenses to expand regulated crypto derivatives offerings in the US.
According to Payward’s initial announcement, Bitnomial is the first crypto-native company in the US to hold licenses for exchange, clearing and brokerage functions under the CFTC.
Related: Kraken bundles crypto and tokenized stocks to attract investors seeking exposure to multiple assets
Crypto derivatives markets expand as US platforms build offerings
Crypto derivatives, including futures and options tied to assets such as Bitcoin (BTC), account for a majority of digital asset trading volumes, with a significant share of activity taking place on offshore platforms.
US regulators have acknowledged this trend. In a joint statement in September 2025, the Securities and Exchange Commission and the CFTC said regulatory fragmentation has pushed some crypto trading activity offshore and noted that perpetual futures have been limited in the US under current frameworks.
The agencies said they are exploring ways to bring derivatives activity onshore using existing authorities, including potential frameworks for products such as perpetual futures and efforts to align regulatory requirements across markets.
Against this backdrop, US platforms have begun expanding their crypto derivatives offerings. In April, CME Group, the largest derivatives exchange operator in the United States, said it plans to launch futures tied to Avalanche (AVAX) and Sui (SUI), pending regulatory approval, following a January plan to list contracts for Cardano (ADA), Chainlink (LINK) and Stellar (XLM).
About a month later, the company announced it would begin offering 24/7 trading for crypto futures and options at the end of May, pending regulatory approval.

Source: CME Group
Outside the US, crypto exchanges have been expanding derivatives offerings in other markets. In February, Kraken launched tokenized equity perpetual futures for non-US clients, offering 24/7 leveraged exposure to assets including US stock indexes, gold and equities, while in March, Coinbase expanded its derivatives offerings in Europe with new crypto and equity-index futures across 26 countries through its MiFID-regulated entity.
Other crypto exchanges, including One Trading, Gemini and Backpack have also launched regulated perpetual contracts in Europe.
Magazine: How to fix suspected insider trading on Polymarket and Kalshi
Crypto World
Linux Copy Fail: ‘A Trivially Exploitable Bug’


A newly discovered vulnerability could affect most open-source major Linux distributions released since 2017, according to security researchers.
The flaw, titled “Copy Fail,” caught the attention of the US Cybersecurity and Infrastructure Agency (CISA), who added it to the Known Exploited Vulnerabilities (KEV) catalog on Saturday, warning it poses “significant risks to the federal enterprise.”
“10 lines of Python” may be all it takes: Researcher
The vulnerability can allow attackers to gain root access across a wide range of Linux systems using a 732-byte Python script, though it requires prior code execution on the system to escalate privileges.
Researcher Miguel Angel Duran said that it only requires “10 lines of Python” to access root permissions on any affected system.
“This Linux vulnerability is insane,” Duran said.
Linux is a widely used operating system by cryptocurrency exchanges, blockchain nodes and custodial services, due to its security and efficiency, meaning the vulnerability could potentially pose risks to the sector if attackers gain initial access.
Exploit was initially reported in March
Xint Code said in an X post on Saturday that the flaw “is a trivially exploitable logic bug in Linux, reachable on all major distros released in the last 9 years.”
“A small, portable python script gets root on all platforms,” Xint Code said.
Cybersecurity firm Theori CEO Brian Pak said in an X post on Saturday that he reported the vulnerability “privately” to the Linux kernel security team on March 23.
“We worked with them on patches, which landed in mainline on April 1. CVE assigned April 22. We disclosed publicly on April 29 with a full write-up and PoC,” Pak said.
Crypto World
Trivially Exploitable, Impacts Crypto Infrastructure

Security researchers have highlighted a Linux vulnerability nicknamed Copy Fail that could impact a broad swath of open-source distributions released since 2017. The flaw has drawn the attention of U.S. authorities and was added to the Cybersecurity and Infrastructure Security Agency’s Known Exploited Vulnerabilities (KEV) catalog, signaling heightened risk to federal and enterprise systems, including cryptocurrency exchanges, node operators, and custodians that rely on Linux for reliability and performance.
At the heart of Copy Fail is a privilege-escalation flaw that, under the right conditions, can grant an attacker root access using a compact Python payload. Researchers emphasize that the exploit requires prior code execution on the target system, but what follows can be executed with astonishing brevity. “10 lines of Python may be all it takes to access root permissions on any affected system,” said one researcher, underscoring how a small foothold can escalate into full control.
Key takeaways
- Copy Fail enables root access via a short Python payload (reported as a 732-byte script) on Linux systems, provided the attacker already has code execution on the machine.
- The vulnerability potentially affects most major Linux distributions released over the past nine years, highlighting a broad attack surface for crypto infrastructure.
- CISA added Copy Fail to the Known Exploited Vulnerabilities catalog on May 1, 2026, marking the issue as a high-priority risk for federal and enterprise environments.
- Patch activity followed a rapid disclosure timeline: the vulnerability was privately reported on March 23, patches landed in mainline on April 1, CVE was assigned on April 22, and public disclosure with a proof-of-concept occurred on April 29.
- Industry observers warn that crypto exchanges, blockchain nodes, and custodial services—widely deployed on Linux—could face heightened risk if systems remain unpatched.
Exploitation mechanics and potential impact
The essence of Copy Fail lies in an error that can be exploited by a small, portable Python script to escalate privileges to root. While the prerequisite is initial code execution on the target host, the subsequent steps could be completed with minimal complexity, allowing an attacker to take full control of the machine. The prospect of such a compact, platform-agnostic payload has drawn particular attention from security researchers and operators of crypto infrastructure, where Linux is a common backbone for exchanges, validators, and custodial services.
As researchers have noted, the vulnerability’s discovery underscores how even widely used and well-audited systems can harbor exploit paths that emerge from seemingly small logic bugs. The fact that the attack can be so succinct—“10 lines of Python” in the words of one observer—amplifies the need for rigorous defense-in-depth, prompt patching, and routine credential hygiene across operations that interact with crypto networks.
Timeline of disclosure and patching
Details surrounding Copy Fail trace a fairly tight window of disclosure and remediation. A security firm and researchers privately reported the issue to the Linux kernel security team on March 23. In response, developers worked on patches that landed in the Linux mainline on April 1. The vulnerability was assigned a CVE on April 22, and a public write-up with a Proof of Concept (PoC) followed on April 29. The sequence of private disclosure, rapid patching, and public documentation reflects a concerted effort among kernel maintainers, researchers, and affected vendors to curb risk quickly.
Public commentary from researchers involved in the disclosure has highlighted the rapid collaboration between the security community and kernel developers as a model for handling high-severity issues. The early patching and subsequent CVE assignment helped standardize response workflows for organizations that rely on Linux in security-sensitive environments, including crypto-asset platforms and nodes that require minimal downtime and robust access controls.
Implications for crypto infrastructure
Linux remains a foundational element for crypto operations—from exchange platforms to validator nodes and custody services—primarily because of its security track record and performance characteristics. Copy Fail adds a realistic reminder that even mature ecosystems can harbor exploitable gaps that threaten the integrity of digital asset ecosystems if left unpatched.
Industry observers urge operators to treat the KEV listing as a high-priority signal and to accelerate remediation cycles where necessary. In practice, that means applying the Linux security patches promptly, validating configurations to minimize exposure, and ensuring that systems with privileged access are protected by strong authentication and least-privilege policies. The convergence of Kubernetes-orchestrated workloads, cloud-native deployments, and edge nodes in crypto networks makes a consistent, organization-wide patching strategy more critical than ever.
For investors and builders, Copy Fail reinforces a broader narrative: operational security and software supply-chain hygiene are as important as creative product design in sustaining long-term adoption. While crypto resilience depends on robust protocol innovations and liquidity dynamics, it increasingly hinges on the reliability of infrastructure underpinning trading, staking, and custody.
What remains uncertain is how quickly all affected distributions will complete universal patch deployment and how quickly threat actors will adapt to new mitigations. As the Linux ecosystem evolves in response to Copy Fail, observers will be watching whether crypto platforms accelerate modernization efforts, adopt more aggressive containment measures, and invest in proactive vulnerability management to prevent similar exposures in the future.
Readers should stay tuned for updates on patch adoption rates across major distributions and any follow-up analyses from researchers detailing real-world exploitation attempts or improved mitigations.
Crypto World
From Regulatory Fog to Institutional Clarity: What the CLARITY Act Means for Bitcoin
TLDR:
- The CLARITY Act classifies Bitcoin as a digital commodity, potentially ending years of Howey test uncertainty in the U.S.
- Senate disputes over stablecoin yields and DeFi liability continue to delay a landmark decision for the crypto industry.
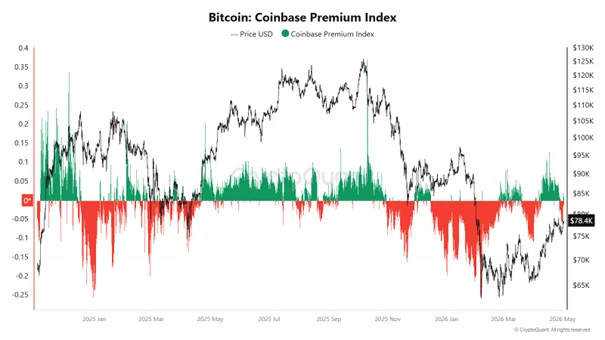
- Coinbase Premium Index has stayed negative throughout 2025, revealing weak U.S. spot demand behind recent Bitcoin price rebounds.
- Improved custody rules under the CLARITY Act could remove institutional balance sheet barriers and shift Bitcoin toward anchored demand.
Regulatory fog has long shadowed Bitcoin’s path toward mainstream institutional adoption in the U.S. The Digital Asset Market Clarity Act of 2025 now stands at the center of that debate.
It passed the House and awaits a Senate decision that could reshape crypto oversight. The bill proposes designating Bitcoin and Ethereum as digital commodities under CFTC jurisdiction.
That single classification could remove the Howey test uncertainty that has constrained the market for years.
A Fork in the Road: Senate Battles Threaten to Extend the Fog
The CLARITY Act cleared the House, but the Senate remains a different challenge altogether. Disputes over stablecoin yield restrictions have created friction between lawmakers and the crypto industry.
DeFi developer liability has added another layer of disagreement that is difficult to resolve quickly. Together, these conflicts reflect a broader structural clash between legacy finance and digital asset markets.
Jurisdictional lines between the SEC and CFTC have not been firmly drawn yet. Both agencies continue negotiating the boundaries of their respective authority over digital assets.
That ongoing back-and-forth has delayed resolution for exchanges and institutional firms awaiting clear guidance. Until those lines are set, operational decisions remain constrained by uncertainty.
Compliance costs for brokers and exchanges are expected to rise once the bill takes effect. Firms will need to restructure operations to meet stricter regulatory standards.
In the short term, that creates financial pressure across the industry. Over time, however, clearer rules tend to attract the institutional capital that spot markets currently lack.
Bitcoin’s Inflection Point: Liquidity Returns, But Confidence Has Not
Coinbase Premium Index readings have remained persistently negative throughout 2025. That data points to weak U.S. spot demand even as prices have bounced from recent lows.
Source: Cryptoquant
Current rallies appear to be futures-driven rather than anchored in genuine spot accumulation. That distinction matters because futures activity does not reflect sustained institutional conviction.
This pattern directly explains why Bitcoin’s price action has remained range-bound and unstable. Market participants are watching closely, but they are not moving capital into spot positions at scale.
The regulatory fog is keeping larger players on the sidelines, waiting for structural certainty before committing. That hesitation has capped upside even during periods of improved global liquidity.
The CLARITY Act could serve as the turning point that shifts Bitcoin’s demand structure. Improved custody rules may lift balance sheet restrictions that currently prevent institutional spot participation.
As those barriers fall, the market could transition from speculative to structurally supported demand. That shift would mark Bitcoin’s true inflection point — not a price milestone, but a change in who is buying and why.
Crypto World
TRON Powers 500% Surge in Crypto Card Spending as Stablecoin Payments Hit $600M Monthly

TLDR:
- Crypto card spending volume has surged 500% since September 2024, now reaching approximately $600M per month.
- TRON serves as the backend settlement layer for Visa-linked stablecoin cards due to its low cost and high throughput.
- Merchants receive fiat-equivalent value instantly while users pay in stablecoins, bridging crypto and traditional commerce.
- Sustained monthly growth signals a behavioral shift as consumers increasingly use crypto cards for everyday purchases.
Crypto card usage is accelerating sharply into 2026, with monthly spending volumes now approaching $600 million.
Since September 2024, transaction volume has climbed by 500%, reflecting a measurable shift in how consumers use digital assets daily. This growth is not driven by speculation.
Instead, it traces back to real merchant payments and everyday consumer transactions settling through Visa-linked stablecoin cards across global commerce.
TRON Emerges as a Core Settlement Layer for Consumer Payments
Visa-linked crypto cards are changing how stablecoin transactions move between consumers and merchants. Users pay with stablecoins such as USDT, and merchants receive the fiat-equivalent value almost instantly.
The backend settlement happens on TRON’s network, which handles high transaction throughput at low cost. This setup removes friction from crypto-to-fiat conversion at the point of sale.
TRON’s infrastructure is proving reliable enough to support this growing payment volume consistently. Its transaction speed and cost structure align well with what consumer-to-business, or C2B, payments demand at scale.
As Yaba (@yabarich) noted on X, “TRON provides high throughput, low transaction cost, and reliable settlement infrastructure,” making seamless crypto payments in everyday commerce possible.
The network’s role goes beyond processing speed. TRON already holds a strong position in stablecoin circulation, making it a natural fit for card-based payment flows.
As more consumers adopt crypto cards, the volume moving through TRON’s rails continues to grow steadily. This positions the chain at a functional intersection between decentralized finance and traditional payment networks.
What this reflects is a broader structural change in crypto utility. Digital assets are transitioning from being primarily held as stores of value toward active use as a medium of exchange. That shift is now showing up in monthly transaction data, not just in market commentary or forecasts.
Expanding Merchant Acceptance Drives Mainstream Payment Adoption
Growing merchant acceptance is one factor sustaining the 500% rise in crypto card spending volume. As more businesses accept stablecoin-settled payments, consumer confidence in using crypto cards for daily purchases also increases.
The two trends reinforce each other over time. This cycle is expanding the practical reach of crypto beyond exchanges and wallets.
The infrastructure alignment between stablecoin networks and global card payment systems is also supporting this momentum.
Visa’s involvement provides the connectivity layer that bridges crypto settlement with traditional point-of-sale systems.
This reduces the complexity for both merchants and cardholders. The result is a payment experience that functions similarly to conventional card transactions.
The data from the past 18 months shows that this is not a temporary spike. Sustained volume growth across consecutive months points to changing consumer behavior rather than short-term activity.
Users are returning repeatedly to crypto cards as a primary payment method. That behavioral pattern carries more weight than any single month’s figures.
As DeFi, payments, and real-world usage converge, the chains enabling that movement stand to gain lasting relevance.
TRON’s current positioning within stablecoin payments and card settlement infrastructure places it directly in that path. The next phase of crypto adoption may well be measured by where people spend, not just what they hold.
-
 Tech5 days ago
Tech5 days agoRegister Renaming | Hackaday
-
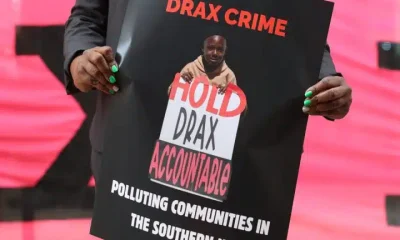
 Politics5 days ago
Politics5 days agoDrax board avoid their own AGM, accused of greenwashing & environmental racism
-

 Tech6 days ago
Tech6 days agoWhy Blue Badges Disappeared From Toyota Hybrids
-

 Tech5 days ago
Tech5 days agoImages of Samsung’s rumored smart glasses have leaked
-

 Sports7 days ago
Sports7 days agoIPL 2026: Ruturaj Gaikwad registers slowest fifty of the season, enters all-time unwanted list | Cricket News
-

 Tech1 day ago
Tech1 day agoTrump’s 25% EU auto tariff breaches Turnberry Agreement that also covers semiconductors and digital trade
-

 NewsBeat7 days ago
NewsBeat7 days agoLK Bennett closes all stores after entering administration
-

 Fashion4 days ago
Fashion4 days agoKylie Jenner’s KHY Enters a New Era with ‘Born in LA’
-

 Business4 days ago
Business4 days agoMost Commercial Energy Audits Miss the Real Losses
-

 Crypto World5 days ago
Crypto World5 days agoCFTC’s AI will review U.S. crypto registration applications, chairman tells CoinDesk
-

 Business6 days ago
Business6 days ago(VIDEO) Charlize Theron Climbs Times Square Billboard to Promote New Netflix Thriller ‘Apex’
-

 Tech7 days ago
Tech7 days agoOpenAI’s Sam Altman apologizes for not reporting ChatGPT account of Tumbler Ridge suspect to police
-

 Business4 days ago
Business4 days agoBarclay Brothers Avoid Bankruptcy: HSBC Drops High Court Petitions After IVA Deal
-

 Sports1 day ago
Sports1 day agoPaul Scholes issues Marcus Rashford reality check as agreement emerges over Man United star
-

 Tech7 days ago
Tech7 days agoOpenAI CEO apologizes to Tumbler Ridge community
-

 Entertainment6 days ago
Entertainment6 days agoAlicia Keys Calls Out Music Industry ‘Boys Club’
-

 Business3 days ago
Business3 days agoTesla Officially Registers Elon Musk’s Stock: What Investors Need to Know
-

 Tech5 days ago
Tech5 days agoGet Ready for More Brain-Scanning Consumer Gadgets
-
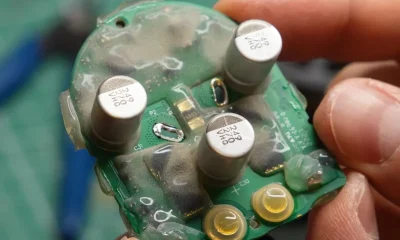
 Tech6 days ago
Tech6 days agoDyson Vacuums And The Curse Of Cooked Capacitors
-

 Crypto World5 days ago
Crypto World5 days agoRobinhood Phishing Scam Exploits Gmail Dot Feature to Bypass Security









You must be logged in to post a comment Login