Crypto World
New malware scam targets crypto users through Obsidian notes app
A new social engineering scheme is leveraging the Obsidian note-taking app to deploy stealthy malware targeting cryptocurrency and finance professionals.
Summary
- Scammers are using LinkedIn and Telegram to trick crypto professionals into downloading malicious Obsidian plugins that deploy a remote access trojan.
- Elastic Security Labs discovered that the undocumented PHANTOMPULSE malware uses three different blockchain networks to receive commands and maintain persistence.
- Security researchers recommend that financial firms implement strict application-level plugin policies to prevent legitimate productivity tools from being exploited.
Elastic Security Labs released a report Tuesday detailing how attackers use “elaborate social engineering on LinkedIn and Telegram” to bypass traditional security by hiding malicious code within community-developed plugins.
The campaign specifically targets individuals in the digital asset space, capitalizing on the permanent nature of blockchain transactions. This vulnerability is particularly acute given that wallet compromises accounted for $713 million in stolen funds during 2025, according to Chainalysis data.
The infiltration begins with scammers posing as venture capital representatives on LinkedIn to initiate professional networking. These conversations eventually transition to Telegram, where the attackers discuss cryptocurrency liquidity solutions to build a “plausible business context.”
Once trust is established, targets are invited to access what is described as a company database or dashboard hosted on a shared Obsidian cloud vault.
Opening the vault serves as the initial access vector. The victim is directed to enable community plugin synchronization, which triggers the silent execution of trojanized software.
While the technical execution varies slightly between Windows and macOS, both paths result in the installation of a previously unknown remote access trojan (RAT) named PHANTOMPULSE.
This malware is designed to grant attackers full control over the infected device while maintaining a low profile to avoid detection.
PHANTOMPULSE maintains its connection to the attackers through a decentralized command-and-control (C2) system that spans three different blockchain networks.
By using on-chain transaction data tied to specific wallets, the malware can receive instructions without a central server.
“Because blockchain transactions are immutable and publicly accessible, the malware can always locate its C2 without relying on centralized infrastructure,” Elastic noted.
The use of multiple chains ensures the attack remains resilient even if one blockchain explorer is restricted. This method allows the operators to rotate their infrastructure seamlessly, making it difficult for defenders to sever the link between the malware and its source.
Elastic warned that by abusing Obsidian’s intended functionality, the hackers managed to “skirt traditional security controls entirely.”
The firm suggests that organizations operating in high-risk financial sectors should implement strict application-level policies for plugins to prevent legitimate productivity tools from being repurposed as entry points for theft.
Crypto World
how it happened, and what it means for DeFi
A roughly $292 million exploit over the weekend has rattled the crypto industry, exposing vulnerabilities in decentralized finance (DeFi) infrastructure and raising concerns about knock-on effects across lending protocols.
While investigations are still ongoing, early analysis suggests the attack centered on Kelp’s rsETH token — a yield-bearing version of ether (ETH) — and the mechanism used to move assets between blockchains.
The attacker appears to have manipulated that system to create large amounts of tokens without proper backing, then quickly used them as collateral to borrow and drain real assets from lending markets, mostly from Aave , the largest decentralized crypto lender.
The incident is the latest blow to DeFi, happening only a couple weeks after the $285 million exploit of Solana-based protocol Drift, further denting investor trust in the nearly $90 billion crypto sector.
How the attack worked
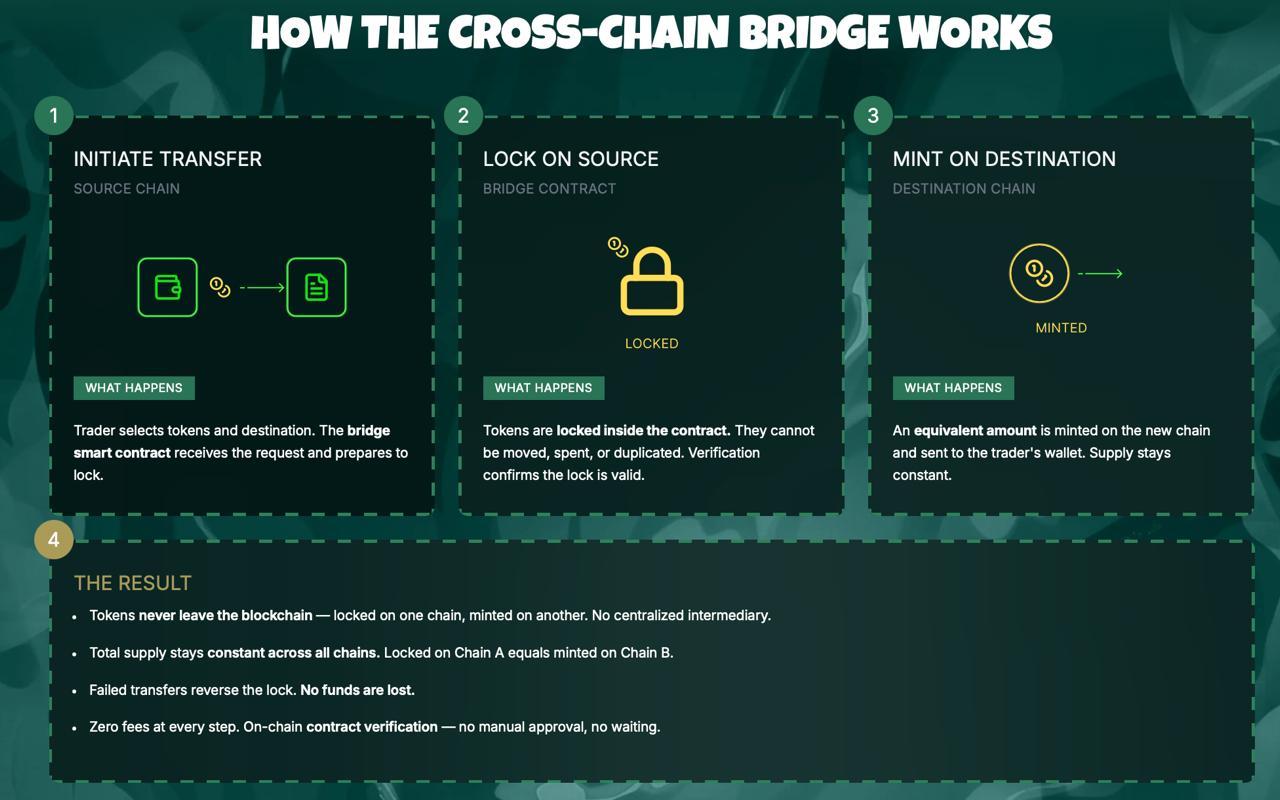
At a high level, the exploit targeted a LayerZero bridge component — a piece of infrastructure that enables assets to move across different blockchains, Charles Guillemet, CTO of hardware wallet maker Ledger, told CoinDesk in a note.
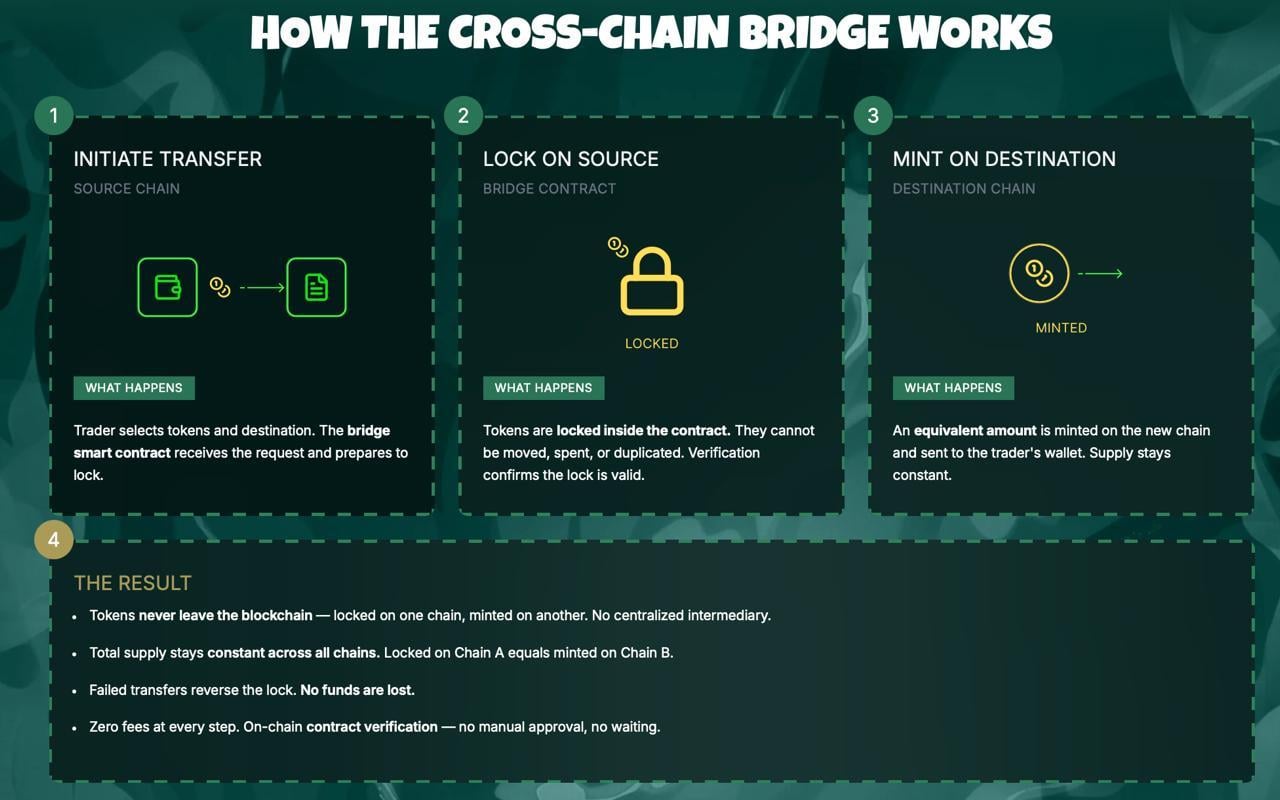
Bridges typically work by locking assets on one chain and minting equivalent tokens on another. That process depends on a trusted entity — often called an oracle or validator — to confirm deposits.
In this case, Kelp effectively acted as that verifier. According to Guillemet, the system relied on a single-signer setup, meaning just one entity could approve any transactions.
“It seems the attacker was able to sign a message … allowing him to mint large amount of rsETH,” he said. He added that it remains unclear how that access was obtained.
Michael Egorov, founder of Curve Finance, pointed to the same weakness in the system’s configuration.
“Things can happen when you trust one single party — whoever that would be.”
That setup allowed the attacker to effectively create unbacked tokens, even though no corresponding assets were locked on the source chain.
Once minted, the tokens were quickly deployed. The attacker “immediately deposited them in lending protocols mostly Aave to borrow real ETH against,” Guillemet explained.
That maneuver shifted the problem from a single exploit into a broader market issue. DeFi lending platforms are now left holding collateral that may be difficult to unwind, while valuable and liquid assets are already drained.
“Aave was left with rsETH which cannot be really sold and maxborrowed [sic] ETH, so no one can withdraw ETH,” Curve’s Egorov said.
As a result, Aave and other lending protocols may be sitting on hundreds of millions of dollars in questionable collateral and bad debt, he warned, raising concerns of a potential “bank run” dynamic as users rush to withdraw funds.
Aave saw about a $6 billion drop in assets on the protocol as users yanked their assets following the incident. The token associated with the protocol was down about 15% over the past 24 hours’ trading.
What we still don’t know
Key questions remain around how the validator was compromised. The system relied on LayerZero’s official node, raising uncertainty over whether it was hacked, misconfigured or misled.
“Was it hacked? Was it fooled? We don’t know,” Egorov said.
The attacker’s identity is also unknown, though Guillemet said the scale of the attack suggests a sophisticated actor.
“Clearly not some script kiddies,” he said.
Big blow for trust in DeFi
Beyond the immediate losses, the exploit the episode serves as another reminder that as DeFi grows more interconnected, failures in one layer can quickly cascade across the system.
Egorov argued that non-isolated lending models, where assets share risk across pools, amplify the impact of such events.
He also pointed to shortcomings in how new assets are onboarded to lending platforms, saying configurations like Kelp’s 1-of-1 verifier setup should have been flagged earlier.
However, Egorov said there’s a silver lining. “Crypto is a harsh environment which no bank would have survived — yet we are working with that,” he said. “I think DeFi will learn from this incident and become stronger than before.”
Still, even as incidents like this lead to protocol upgrades and redesigns, they also chip away investor confidence in the broader DeFi sector.
“All in all, the trust into DeFi protocols is eroded by this kind of event,” Guillemet said.
“And 2026 will most likely be the worst year in terms of hacks, again,” he added.
Read more: ‘DeFi is dead’: crypto community scrambles after this year’s biggest hack exposes contagion risks
Crypto World
Stablecoins Do Not Threaten Banking Just Yet: Analyst

The impact of stablecoins on the banking sector appears “limited” at the current phase of the adoption cycle, but banks could face increasing competition and an erosion of market share as the stablecoin sector and tokenized real-world assets (RWAs) grow in market capitalization.
“So far, the use of stablecoins remains limited, but their market capitalization exceeded $300 billion at the end of last year,” Abhi Srivastava, associate vice president of Moody’s Investors Service Digital Economy Group, told Cointelegraph.

The role of stablecoins in payments, cross-border commerce and onchain finance is “expanding,” despite their currently limited role, Srivastava said, adding that existing payment systems in the US are already “fast, low-cost and trusted.” He said:
“For the banking sector, at this stage, disruption risk appears limited. In the near term, US rules that prohibit stablecoins from paying yield mean they are unlikely to replace traditional deposits at scale domestically.”
However, over time, growing adoption of stablecoins and tokenized RWAs, traditional or physical financial assets represented on a blockchain by a token, could place “pressure” on the banking sector, leading to deposit outflows and reduced lending capacity, he said.
Stablecoin regulatory policy has become a hot-button issue among crypto industry executives and those in the banking sector, with fears that yield-bearing stablecoins could erode banking market share proving to be a stumbling block for the CLARITY crypto market structure bill in Congress.
Related: Stablecoins behave like FX markets as liquidity splits: Eco CEO
CLARITY Act stalled, as banks fight yield-bearing stablecoins
The Digital Asset Market Clarity Act of 2025, also known as the CLARITY Act, is a comprehensive crypto market regulatory framework that establishes an asset taxonomy, regulatory jurisdiction and oversight over the crypto markets.

It is now stalled in Congress after a group of crypto industry companies, led by cryptocurrency exchange Coinbase, publicly stated opposition to earlier drafts of the bill.
A lack of legal protections for open-source software developers and a prohibition on yield-bearing stablecoins were among some of the most contentious issues cited by crypto industry opponents of the legislation.
Several attempts have been made by US lawmakers and the White House to negotiate a bill acceptable to both the crypto industry and the bank lobby.
Earlier this month, North Carolina Senator Thom Tillis said he plans to release an updated draft bill proposal that would be acceptable to both sides; however, the bill has reportedly received pushback, according to Politico, and has yet to be publicly released.
However, other crypto industry executives and market analysts have warned that if the CLARITY Act fails to pass, it could open the crypto industry up to future regulatory crackdowns by hostile lawmakers and officials.
Magazine: Stablecoins will see explosive growth in 2025 as world embraces asset class
Crypto World
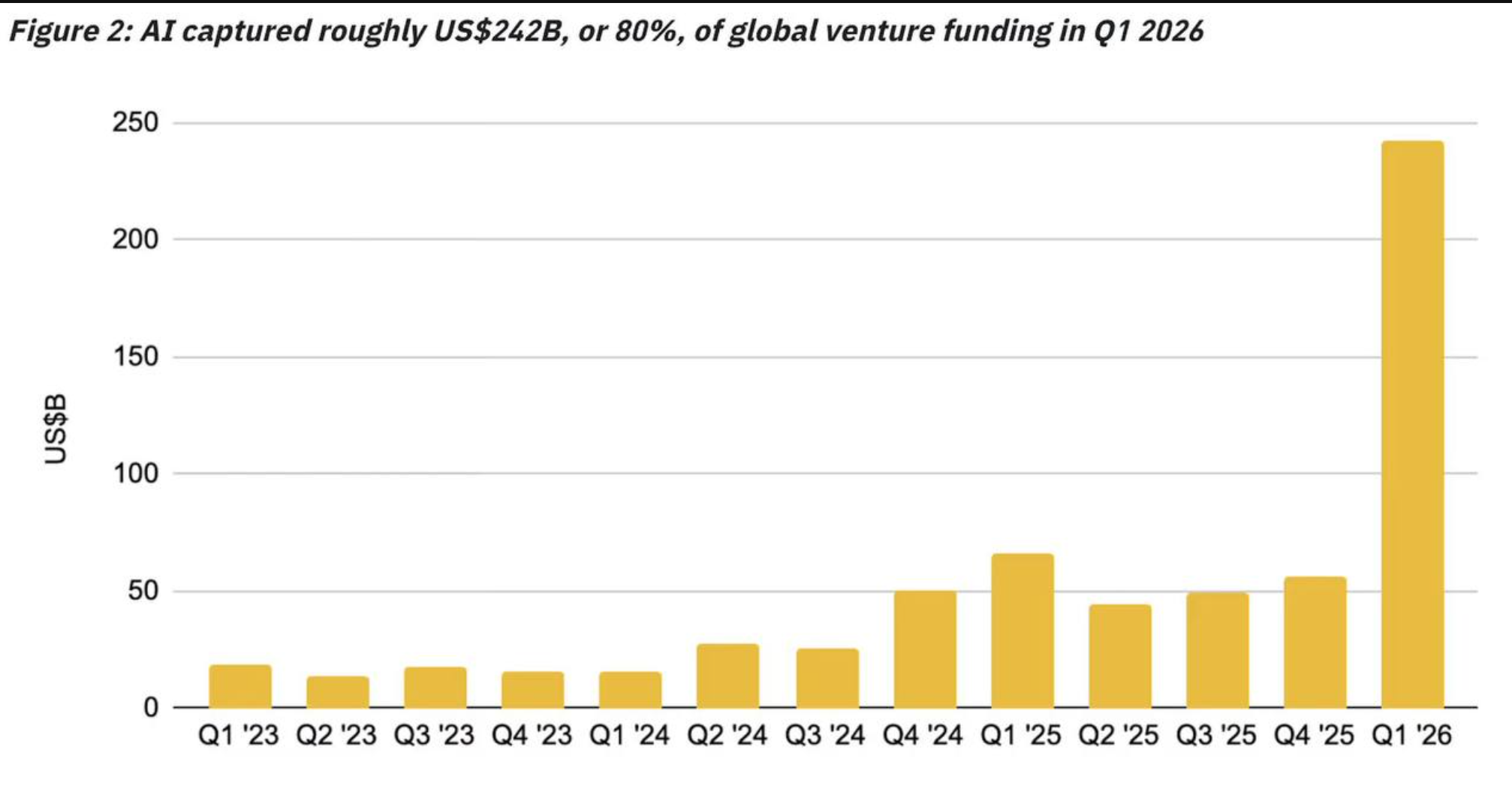
AI Absorbs $242 Billion in Q1 Venture Funding, Exceeding All of 2025 Combined
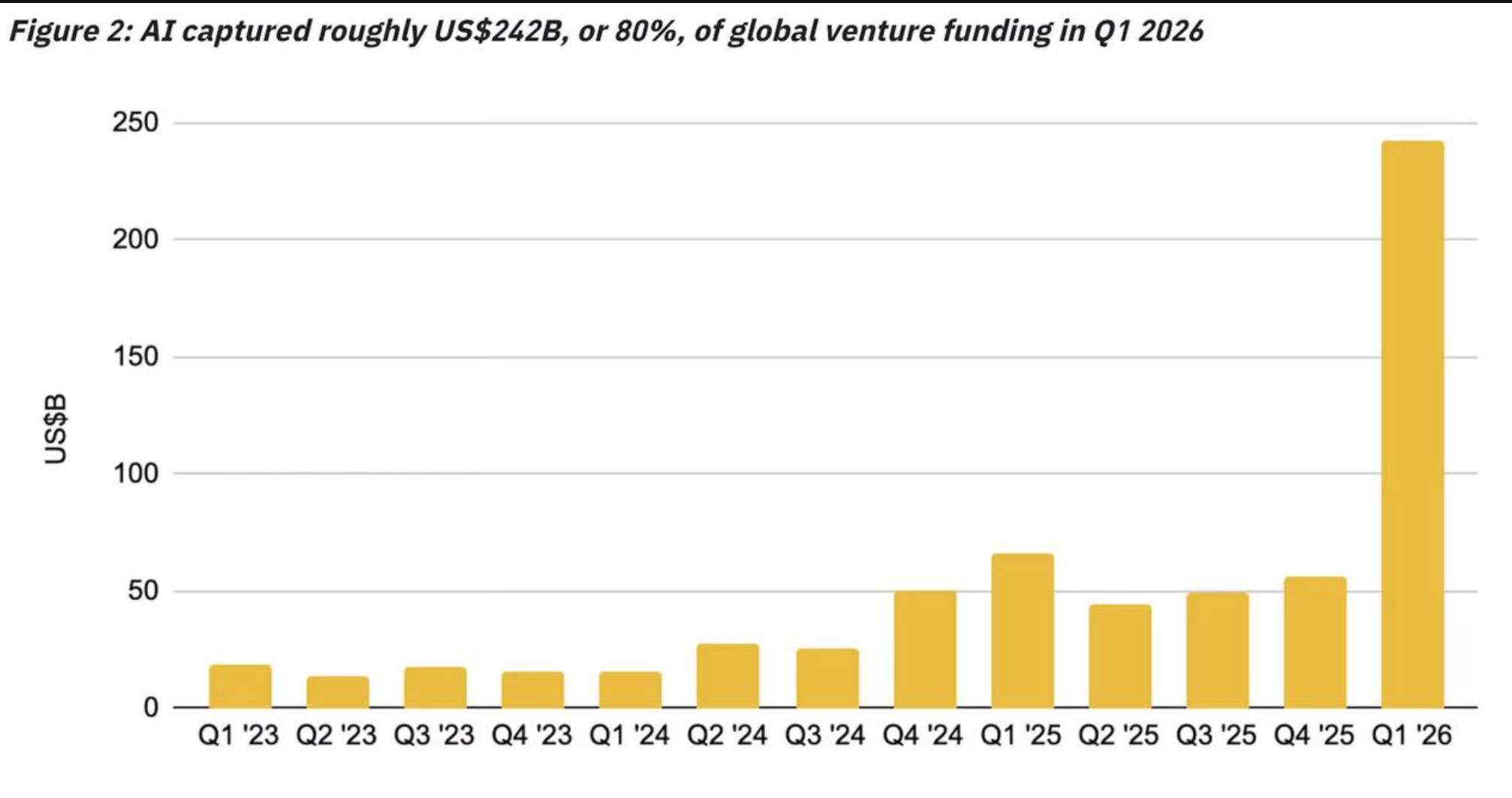
Artificial intelligence captured roughly $242 billion in venture capital funding during Q1 2026, accounting for 80% of all global startup investment in the quarter.
The figures mark a record quarter as total global venture investment reached approximately $300 billion across some 6,000 funded companies.
Mega-Rounds Drive AI Funding Surge
Four deals accounted for 65% of all global venture capital. OpenAI raised $122 billion, Anthropic secured $30 billion, xAI closed $20 billion, and Waymo brought in $16 billion. AI funding in Q1 alone exceeded all of 2025 combined.
However, the capital flood is hitting physical limits. A Bloomberg report found that roughly half of US AI data centers planned for 2026 have been delayed or cancelled.
Transformer shortages, grid strain, and supply chain bottlenecks are limiting the buildout. Only about one-third of the projected 12 GW of new capacity is under active construction.
AI Agents Enter the Workplace
Meanwhile, Coinbase CEO Brian Armstrong revealed the exchange is testing AI agents that operate alongside human employees in Slack and email.
Armstrong suggested Coinbase could eventually have more AI agents than human staff, reflecting a broader corporate shift toward autonomous systems.
The workplace transformation has also reignited political debate. Elon Musk proposed “universal HIGH INCOME” via federal government checks, arguing AI productivity would offset inflation. Andrew Yang echoed the call, urging faster action on AI-funded universal income.
Senator Bernie Sanders pushed back from a different angle, warning that AI firms plan to spend $300 million on 2026 midterm elections.
Sanders called on Democrats to resist industry pressure and confront what he called “the AI Oligarchs.”
The tension between record capital inflows and infrastructure bottlenecks suggests AI’s growth trajectory may face near-term friction even as its economic influence accelerates.
The post AI Absorbs $242 Billion in Q1 Venture Funding, Exceeding All of 2025 Combined appeared first on BeInCrypto.
Crypto World
Justin Sun Offers to Negotiate With KelpDAO Hacker After $292 Million Exploit
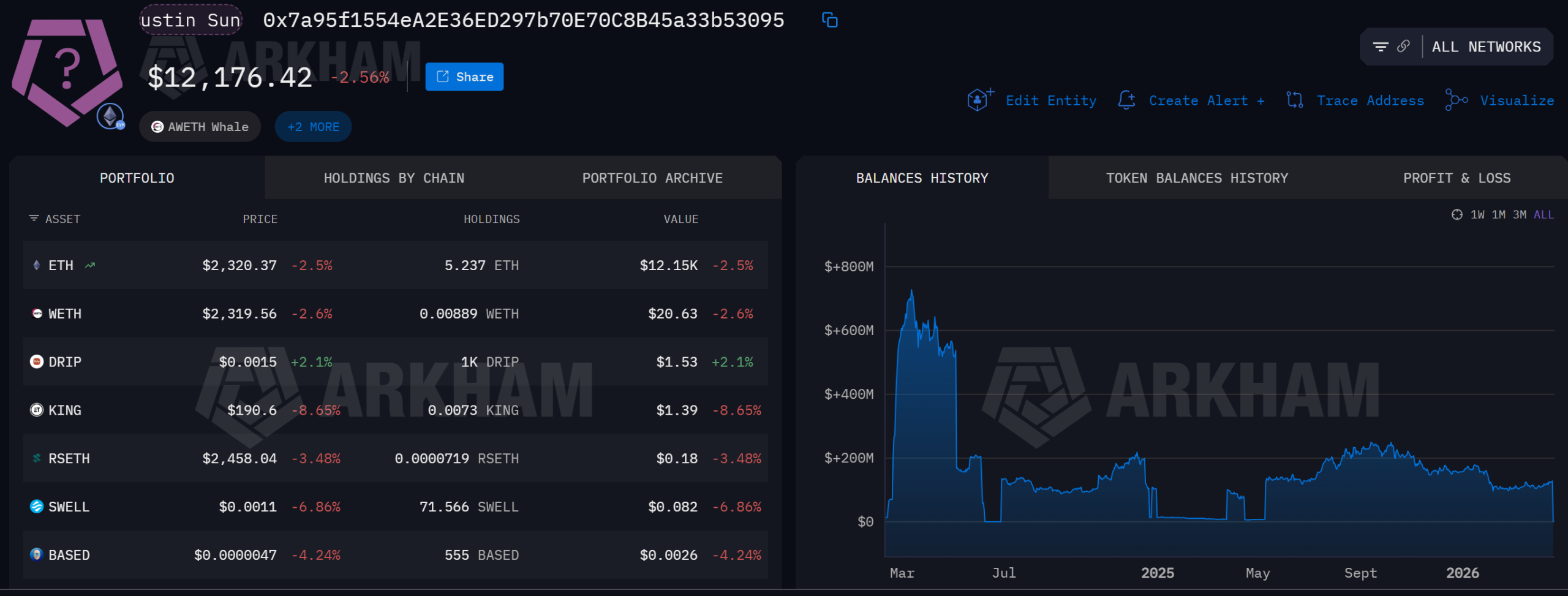
Tron founder Justin Sun publicly called on the KelpDAO bridge hacker to negotiate a return of the stolen funds, warning that a $292 million loss could bring down both Aave and KelpDAO.
Sun’s appeal followed the largest Decentralized Finance (DeFi) exploit of 2026, which drained 116,500 rsETH from KelpDAO’s cross-chain bridge on April 18.
Sun Moves Funds as Aave Takes the Hit
The attacker exploited a flaw in KelpDAO’s LayerZero-powered bridge, forging cross-chain messages to release rsETH without corresponding token burns.
The stolen tokens were then deposited as collateral on Aave V3, where the hacker borrowed large volumes of Wrapped Ether (WETH) against them.
Because the rsETH became unbacked, the positions are effectively unliquidatable, leaving Aave with over $236 million in bad debt.
Aave froze rsETH markets on both V3 and V4 within hours. Aave founder Stani Kulechov confirmed the exploit originated outside Aave’s contracts.
On-chain data shows Sun urgently withdrew 65,584 ETH, worth roughly $154 million, from Aave and deposited it into Spark shortly after.
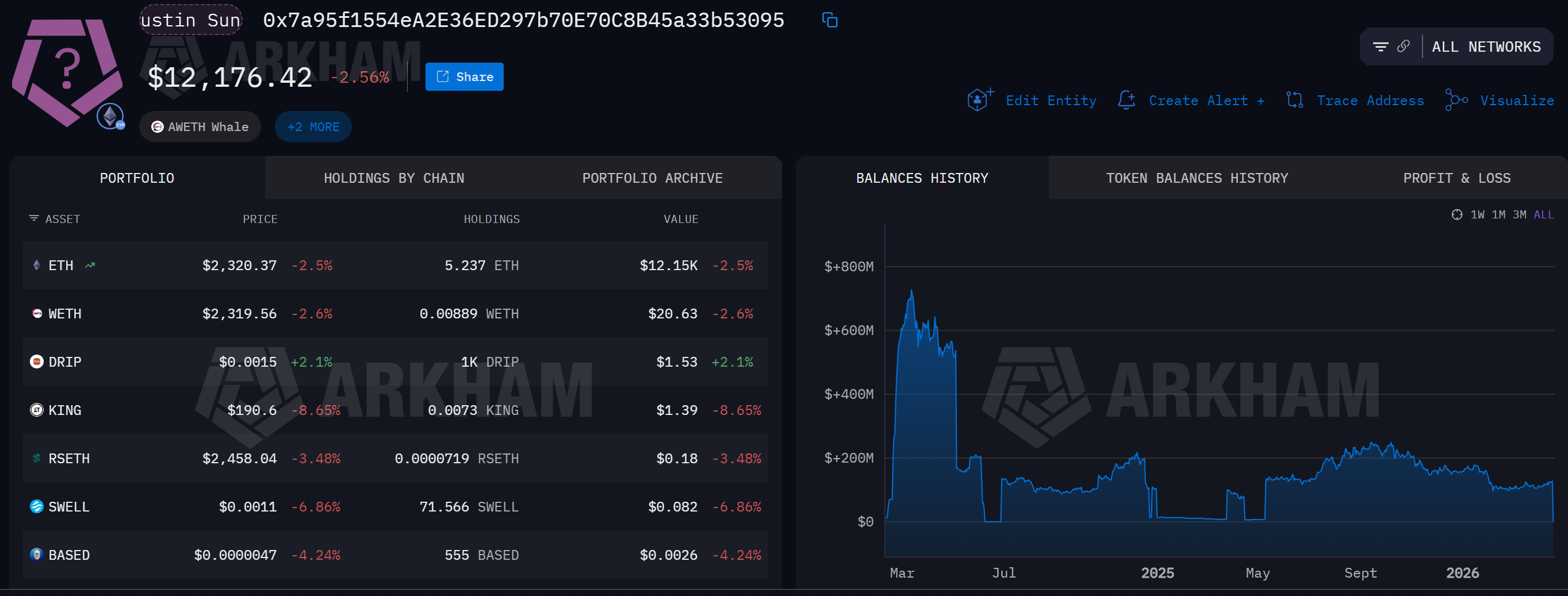
His total Aave exposure has reportedly dropped to $380 million, while his Sky and Spark holdings have risen to $2.13 billion.
“OK — Kelpdao hacker, how much you want? Let’s just talk. With KelpDAO’s help, of course. It’s simply not worth it to sacrifice both Aave and KelpDAO and let them go down over this hack,” wrote Justin Sun in a post.
Interoperability protocol Axelar also responded, expressing solidarity with LayerZero and urging the industry to adopt stronger bridge security standards.
Axelar pointed to the importance of multi-validator configurations, noting that Kelp’s single-validator setup may have enabled the breach.
The exploit overtakes the $285 million Drift Protocol hack from April 1 as the largest DeFi loss this year.
The post Justin Sun Offers to Negotiate With KelpDAO Hacker After $292 Million Exploit appeared first on BeInCrypto.
Crypto World
AI startup Cursor in talks to raise $2 billion funding round at valuation of over $50 billion

The Cursor logo arranged on a smartphone in New Hyde Park, New York, Nov. 20, 2025.
Gabby Jones | Bloomberg | Getty Images
Artificial intelligence startup Cursor is in talks to raise a $2 billion fundraising round at an over $50 billion valuation, which does not include the investment, a source familiar with the matter told CNBC.
Andreessen Horowitz is slated to co-lead the new investment round, in which Nvidia and Thrive Capital are also expected to participate, said the source, who was not authorized to publicly speak on the investment. Those three firms have all previously backed the AI coding startup.
Bloomberg News first reported that Cursor was raising capital.
The funding round underscores the venture capital industry’s enthusiasm for startups specializing in AI coding agents that can complete a range of software development tasks for users. Although Cursor was among the first major startups to focus on AI coding agents, other companies, such as Google, Anthropic and OpenAI, have since debuted similar tools.
Cursor announced in November that it closed a $2.3 billion funding round at a $29.3 billion post-money valuation. That financing came after a $900 million investment round in June.
Among Cursor’s current investors are Accel, DST Global, Coatue and Google, according to a corporate blog post.
The startup released in February various updates intended to help software developers, including giving AI agents the ability to test their coding changes and record their actions via videos, logs and screenshots.
Cursor did not immediately reply to a request for comment.
WATCH: Cursor CEO Michael Truell: We’re seeing success with our AI age, not just demand

Crypto World
Bitcoin’s 2024 halving cycle lags earlier cycles, analysts say

Bitcoin’s current market cycle is broadly viewed as weaker than its three prior halving-driven runs, according to Galaxy’s head of firmwide research, Alex Thorn. By weighing price action since the April 2024 halving against the patterns seen in 2012, 2016 and 2020, Thorn argues that volatility has cooled and upside potential appears more constrained this time around. Notably, the all-time high above $125,000, reached on Oct. 5, 2025, was only about 97% above the 2024 halving price near $63,000, illustrating a markedly tamer peak for the cycle so far.
Thorn’s comparisons hinge on a stark difference in how cycles unfold. The 2012 halving cycle saw a roughly 9,294% price surge to around $1,163; 2016 delivered about a 2,950% surge to near $19,891; and the 2020 halving generated a roughly 761% gain. In Thorn’s view, “Cycle four is dramatically underperforming prior cycles,” a conclusion he shared in an X post that raises a bigger question: is this the new normal, or will the cycle evolve in unforeseen ways?
Beyond price trajectories, the market’s behavioral foundations may be shifting. Thorn notes that volatility has declined with each successive halving, suggesting that BTC’s price could become more influenced by factors outside of the four-year cycle theory traditionally cited by traders. The 30-day Bitcoin Volatility Index has not surpassed 3.11% in the current cycle, with the last reading above that level recorded on Aug. 24, 2024. The latest 30-day figure sits at about 1.75%, according to Bitbo data.
Key takeaways
- Galaxy’s Alex Thorn concludes the current BTC cycle is dramatically weaker than the 2012, 2016 and 2020 halving cycles when comparing price action since the April 2024 halving.
- The all-time high above $125,000 in October 2025 was roughly 97% above the 2024 halving price around $63,000, signaling a much milder top versus prior cycles.
- Volatility has systematically compressed across cycles, with the 30-day BTC volatility staying well below the peaks seen in earlier halvings (latest around 1.75%).
- Market critics point to an early all-time high before the 2024 halving as an anomaly, underscoring that one-off catalysts can distort cycle comparisons.
Market dynamics and the pre-halving anomaly
Another layer of complexity comes from an event-driven impulse that disrupted typical cycle timing. BTC briefly hit an all-time high above $70,000 in March 2024—one month before the April 2024 halving. Analysts have attributed part of the outsized early move to the subsequent approval of spot Bitcoin ETFs in the United States in January 2024, which acted as a catalyst for price acceleration ahead of the halving. This premature peak is frequently cited by critics as a meaningful deviation from the classic halving-driven narrative.
In parallel, Fidelity Digital Assets has observed that Bitcoin’s drawdowns in this cycle have been less severe than in past bear markets. While declines of 80%–90% are not unheard of in older cycles, the drop from the all-time high to later troughs has so far been more contained in this phase. Fidelity’s analysis notes that even a journey back from peak levels remains substantial—BTC pulled back from the late-2021 highs to the roughly $60,000 area, a move just over 50% in magnitude from the peak levels cited by Fidelity’s framework.
Near-term outlook and the long arc
March brought a contrarian take from Jan van Eck, CEO of VanEck, who said BTC is close to bottoming and that a gradual recovery could begin in 2026. While such forecasts hinge on a confluence of macro factors, liquidity conditions, and investor sentiment, they align with a broader sense that BTC may enter a more protracted phase of consolidation after 2025’s peak, rather than repeating the rapid, cycle-driven surges seen in earlier eras.
As of the latest readings, Bitcoin was trading near $74,703, with fresh momentum up modestly over the past week. The price backdrop underscores Thorn’s observation of a more muted cycle, even as headlines around regulatory clarity, ETF developments, and institutional participation continue to influence sentiment.
What to watch next
The immediate question for investors and builders alike is whether this cycle’s subdued volatility and mixed momentum represent a lasting regime shift or a temporary deviation sparked by unique catalysts. Key developments to monitor include how macro conditions interact with BTC’s supply-demand dynamics, any concrete shifts in ETF-related inflows, and whether the market can align around a clearer, more repeatable set of catalysts akin to past halving narratives. As the market evolves, readers should watch for signs that long-run adoption, liquidity depth, and regulatory clarity begin shaping BTC’s trajectory in a way that differentiates this cycle from its predecessors.
Crypto World
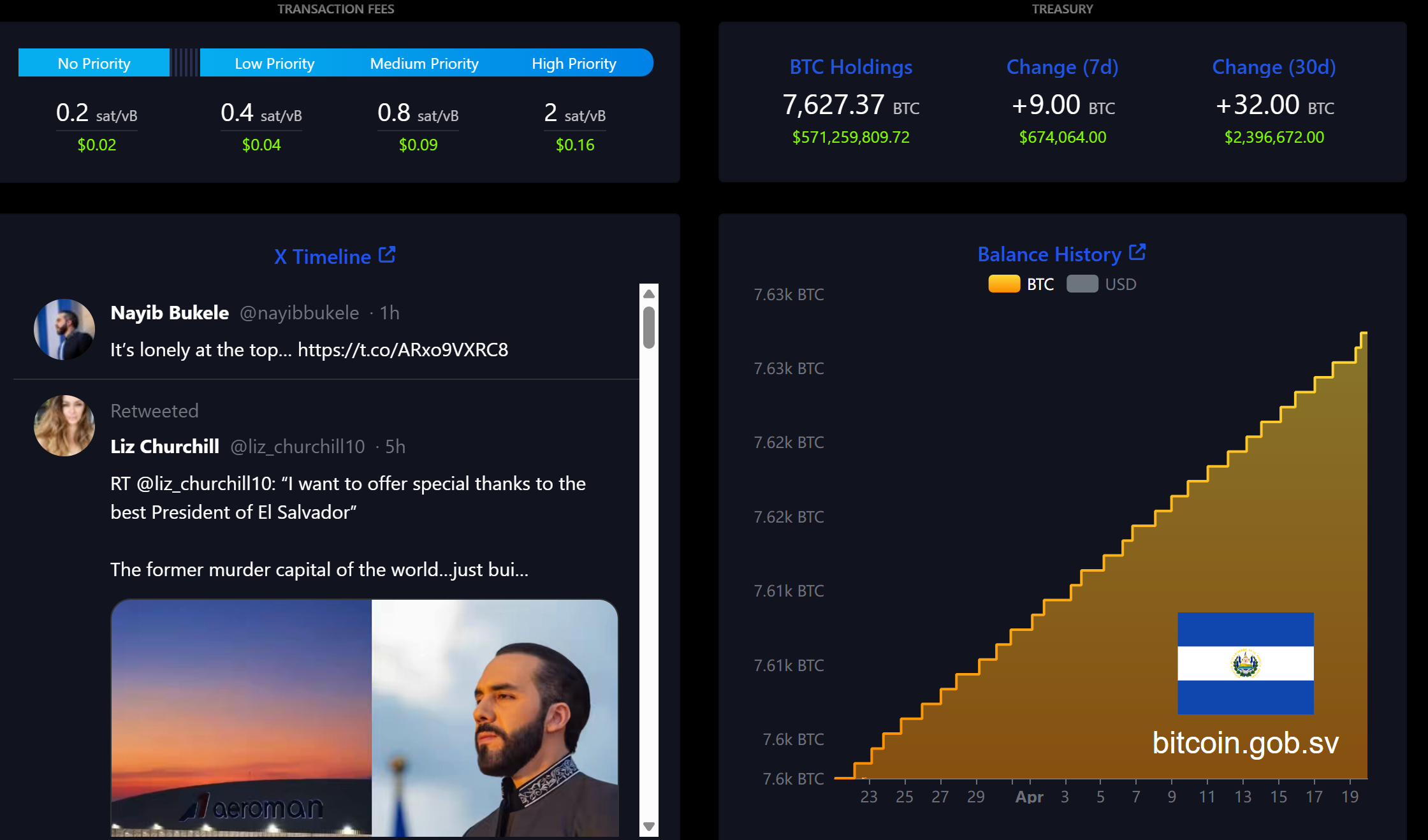
The President Who Pushed Bitcoin the Hardest Is Now the Most Popular Leader on Earth
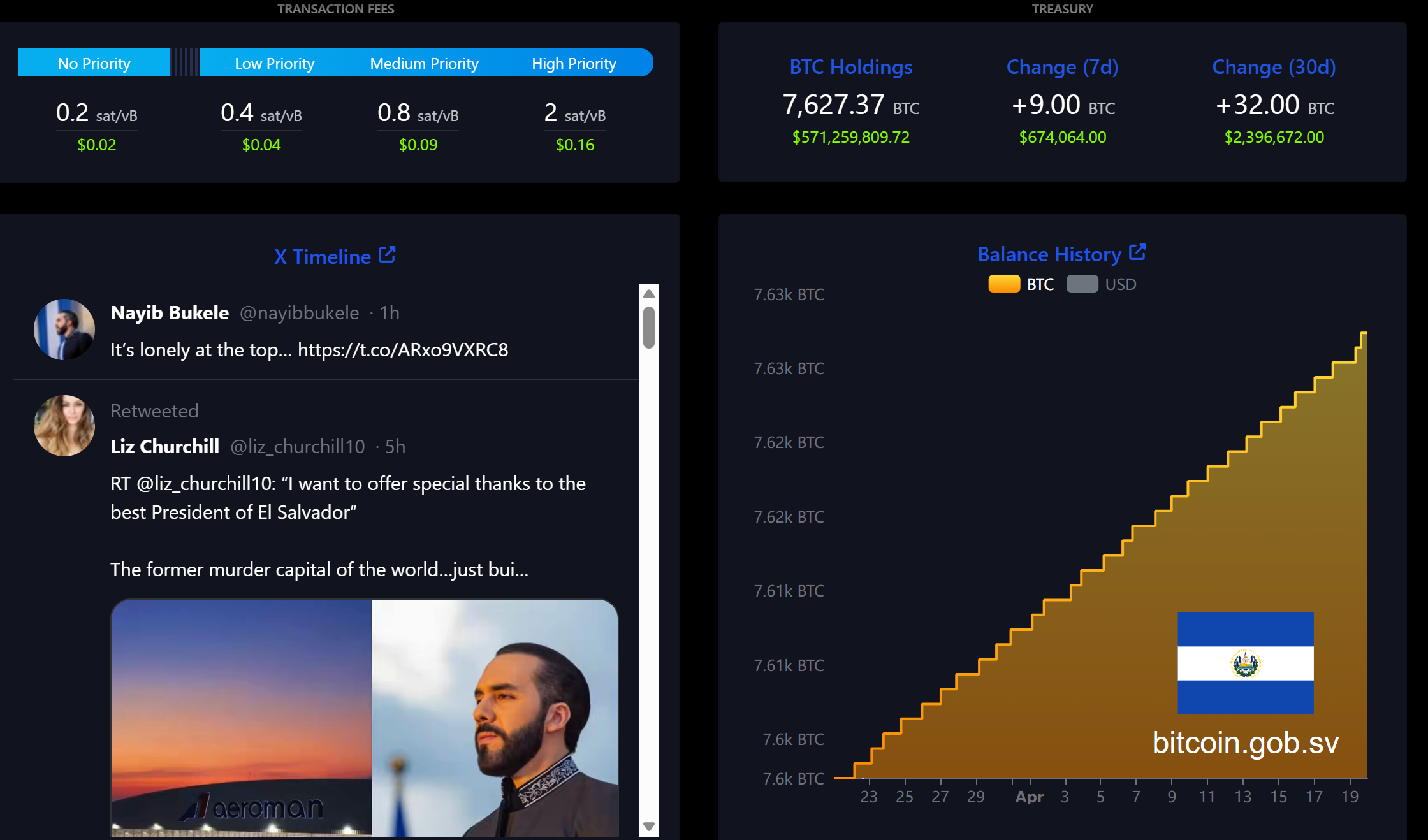
El Salvador President Nayib Bukele sits atop a global leader approval chart with a 94% rating, far outpacing every other head of state on the list.
The ranking measures approval for 26 world leaders. Bukele’s dominance highlights a striking detail for the crypto industry. The president who went furthest on sovereign Bitcoin (BTC) adoption is also the most popular leader on Earth right now.
The Bitcoin President Still Stacks Daily
El Salvador became the first country to make Bitcoin legal tender in 2021. The government continues purchasing roughly one BTC per day, pushing its national reserve past 7,600 BTC.
Polls show, however, that security gains from Bukele’s gang crackdown drive his approval far more than the Bitcoin experiment itself.
Only 2.2% of Salvadorans cited BTC as his biggest failure in a recent CID Gallup survey.
Where Other Leaders Stand on Crypto
South Korea’s Lee Jae-myung (63%) has declared crypto a national priority, pledging spot Bitcoin ETFs and a won-pegged stablecoin by 2026.
Javier Milei (48%) championed Bitcoin deregulation in Argentina but saw his credibility damaged after promoting the LIBRA meme coin, which collapsed and cost investors hundreds of millions.
Donald Trump (38%) signed an executive order establishing a US Strategic Bitcoin Reserve funded with seized coins, positioning the country as a future “Bitcoin superpower.”
Most remaining leaders on the list follow standard regulatory frameworks, with several EU heads of state backing stricter oversight through the MiCA regulation.
The chart suggests that bold pro-Bitcoin moves have not hurt leaders politically, even if domestic voters care more about security and the economy than digital assets.
The post The President Who Pushed Bitcoin the Hardest Is Now the Most Popular Leader on Earth appeared first on BeInCrypto.
Crypto World
Why Does the Next Fed Chair Own SOL Before His April 21 Hearing? Pepeto 300x Rotation Explained
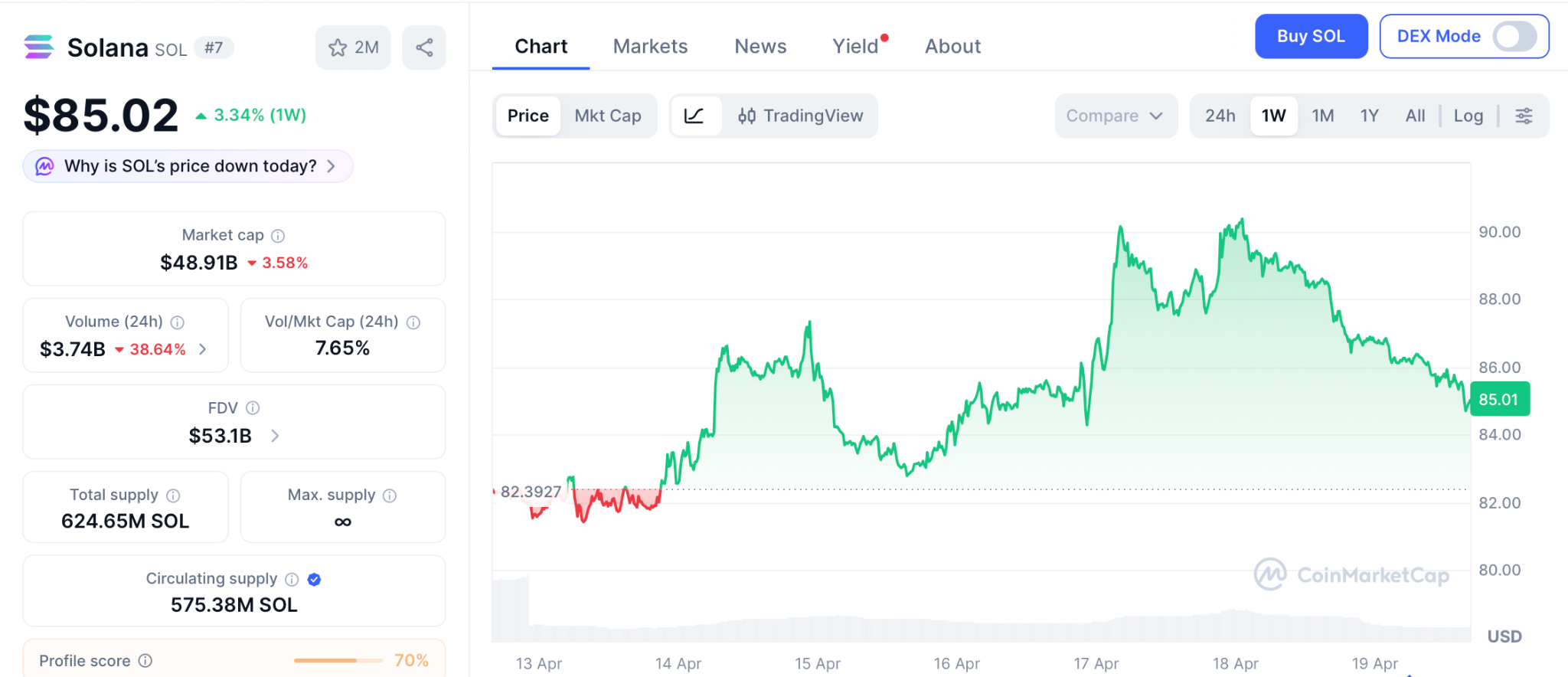
The solana price prediction just picked up a talking point nobody saw coming. Kevin Warsh, Donald Trump’s nominee to chair the Federal Reserve, disclosed indirect Solana holdings across multiple venture fund vehicles in his April 14 ethics filing, per Decrypt, with the Senate confirmation hearing locked for April 21. SOL trades at $85.02 with Bitcoin pushing past $77,300 and the tape finally turning green across the majors.
The numbers look strong, but SOL at a $50 billion market cap is simply too large to print the multiples that reshape a portfolio from a single position. That is where Pepeto steps in, a fresh presale trending hard across crypto feeds this quarter, carrying the kind of traction every cycle signals ahead of returns no large cap can match.
Warsh’s 69 page filing with the Office of Government Ethics lists indirect SOL positions held through the AVGF I venture fund alongside stakes in Optimism, Compound, dYdX, Polymarket, Blast, and more than 30 other Web3 names, per Yahoo Finance. Combined assets top $192 million, making this the broadest Web3 portfolio ever disclosed by a senior US financial nominee.
The Senate Banking hearing lands April 21, the same window that holds the CLARITY Act committee markup and the Fed’s April 28-29 meeting. Spot SOL ETFs have crossed $892 million in net assets, with Bitwise’s BSOL alone pulling $808 million in cumulative inflows per Bitcoin.com. The timing puts SOL at the intersection of every major US monetary and regulatory decision this month.
Solana Price Prediction Compared: SOL Setup and the Presale Opportunity Pepeto
The solana price prediction section below breaks down how even the bullish $180 target spreads across months, and for traders who want more, the audited exchange pulling capital in this quarter is the play worth watching. Pepeto gives retail access to tools large holders previously kept private, wrapped in a single platform.
A contract scanner built into the exchange screens each token before any deposit opens, putting buyers ahead of the news cycle. Presale wallets earn 181% APY through daily compounding staking as the rounds fill, meaning the earliest buyers hold the heaviest positions the second demand peaks.
A risk scoring engine reads momentum across the chain and flags suspect contracts before a dollar moves. The presale has pulled in $9.21 million at $0.0000001865, backed by a SolidProof audit and driven by the founder who pushed Pepe to $7 billion on 420 trillion tokens, now leading this exchange alongside a former Binance executive.
The entry window narrows every hour as the Binance listing draws closer. Once public trading opens, millions of new buyers set the price and the presale floor vanishes on the spot. Every past crypto recovery paid the wallets that moved while the crowd was waking up, and once Pepeto’s Binance listing lands, the 300x runway from presale pricing closes the same day.
Solana (SOL) Price Prediction: Can SOL Reach $180?
Solana (SOL) trades at $85.02 per CoinMarketCap, bouncing with the broader market, still 70% below the $293 peak from November 2021. SOL holders sit at 167 million monthly unique wallets per Solana Foundation data, a record set in April.
Standard Chartered’s $250 target rests on Alpenglow’s 150 millisecond finality upgrade and the spot ETF products giving institutions a regulated route in.
CoinCodex sketches a 2026 channel between $84 and $133.03 with the average near $119. Even the aggressive solana price prediction reaching $180 prints around 103% over several months. Strong for a large cap, but a presale at 300x math from one Binance listing event beats months of chart watching by a wide margin.
Conclusion:
The solana price prediction points at $180 to $250 on a long runway, and that kind of move sounds great until you stack it next to the 300x analysts are calling for on Pepeto presale pricing. Once the gap is visible, the SOL forecast starts looking modest, and the rotation into earlier entries starts to make sense.
The accounts that turned Pepe and DOGE into life changing positions were all built the same way. Capital went in before the coin hit every screen, the deposit held through the first exchange print, and compounding did the lifting from there.
Pepeto runs that exact playbook right now. The raise crossed $9.21 million, fresh capital keeps hitting the contract every day, and the Binance listing creeps closer hour by hour. The wallets depositing at $0.0000001865 today are the ones reading their own names in the millionaire headlines the next cycle writes.
Click To Visit Pepeto Website To Enter The Presale
FAQs
What does the solana price prediction target for 2026?
Standard Chartered places Solana (SOL) at $250 and CoinCodex models a $119 average for 2026, with $180 as a mid cycle target from the current $85.02 level. Fed Chair nominee Kevin Warsh disclosed SOL holdings in his April 14 filing ahead of an April 21 Senate hearing, while Pepeto at presale pricing targets 300x.
How does Solana (SOL) compare to Pepeto as an entry today?
Solana (SOL) at $85.02 projects toward $133 to $180 through 2026 per CoinCodex and Standard Chartered. Pepeto at $0.0000001865 with $9.21 million raised and a Binance listing days away offers a presale to listing return that beats even the strongest solana price prediction.
Disclaimer: This is a Press Release provided by a third party who is responsible for the content. Please conduct your own research before taking any action based on the content.
Crypto World
BitGo, Polygon Among Industry Giants Pushing Rate Limits After The Largest DeFi Exploit of 2026
A wave of protocol-level security responses followed the $292 million KelpDAO rsETH exploit on April 19, with BitGo, Polygon, and Katana moving swiftly to isolate potential contagion.
The attack drained 116,500 rsETH from Kelp DAO’s LayerZero-powered cross-chain bridge through a forged message that bypassed its Decentralized Verifier Network (DVN) configuration.
Protocols Move to Contain Fallout
BitGo, alongside BiT Global Trust, took down the LayerZero OFT DVNs for Wrapped Bitcoin (WBTC) as a precaution. The firm confirmed that user funds remain secure and pledged to share updates as more information becomes available.
Polygon stated that its chain, Agglayer, and broader ecosystem remain unaffected by the incident. The network noted it has safely processed over $2 trillion to date.
Katana paused the OFT path on Vaultbridge, which relied on a 2/3 DVN setup. Bridging through Agglayer, which verifies with zero-knowledge proofs rather than proof-of-authority multisigs, remained fully available.
Meanwhile, Cyvers CTO and co-founder Meir Dolev revealed that KelpDAO was just three minutes away from losing an additional $100 million. A rapid-response blacklist blocked the attacker before a second attempt could succeed.
Industry Leaders Call for Structural Rate Limits
The exploit has reignited calls for built-in rate limits across DeFi protocols. Ethena contributor Guy Young argued that asset issuers should implement throttled cross-chain transfers on top of standard LayerZero OFTs.
“We built a solution on top of the standard OFT to throttle cross chain transfers at $10m per hour for every DVN, in addition to the $10m per block rate limit on the mint contract. The former would have prevented Kelp, the latter Resolv,” he wrote.
Ethena’s configuration caps potential damage at $10 million per chain per hour even if a DVN is fully compromised. Young called the slight inconvenience for users a worthwhile tradeoff to avoid catastrophic losses.
Keone Hon, CEO and co-founder of Monad, proposed that pooled lending protocols adopt “smart caps” that limit how quickly collateral supply can grow.
He pointed to the Resolv hack in March, where the attacker minted infinite tokens but could only extract $24 million because exit pathways were small.
Hon argued that high supply caps should be seen as a liability, not a sign of stature. A supply limit slightly above current utilization, adjusting over hours to the true cap, would have saved rsETH depositors $200 million, he estimated.
The KelpDAO breach is now the largest DeFi exploit of 2026. Whether protocols adopt the rate-limiting measures these leaders are proposing may determine how large the next one gets.
The post BitGo, Polygon Among Industry Giants Pushing Rate Limits After The Largest DeFi Exploit of 2026 appeared first on BeInCrypto.
Crypto World
Europe Leads the Tokenization Charge as Banks, Regulators, and Depositories Align

TLDR:
- An ECB director stated tokenization restructures entire financial systems, surpassing all previous waves of technological change.
- The UK reversed its stablecoin payments policy, bringing digital assets into its formal regulatory perimeter for the first time.
- HSBC completed a tokenized deposit pilot covering issuance, transfer, and atomic settlement on the Canton Network successfully.
- Clearstream will custody and settle Ondo’s tokenized stocks and ETFs, embedding digital assets into core European market infrastructure.
Tokenization is gaining serious traction across Europe as regulators, central banks, and financial institutions move toward digital asset integration.
A European Central Bank director recently stated that tokenization’s effect on finance surpasses earlier waves of technological change.
Major institutions across the continent are responding with concrete steps. From regulatory reversals to live pilots and cross-border partnerships, Europe is emerging as a key driver of the global tokenization push.
European Regulators Set the Tone for a New Financial Era
A European Central Bank director drew a sharp distinction between tokenization and previous technological shifts in finance.
According to Ledger Insights, the director noted that these technologies do not merely improve one part of a system.
Rather, they restructure the entire logic of how financial systems operate. That assessment positions tokenization as a foundational change, not an incremental upgrade.
The statement carried weight given the ECB’s central role in shaping European financial policy. When a director at that level speaks about systemic change, institutions across the continent take notice.
The framing moved the conversation beyond speculation and into strategic planning. European banks and depositories began responding almost immediately.
Across the Channel, the UK government reversed its earlier position on stablecoins within payments regulation. Authorities confirmed plans to bring stablecoins into the country’s formal payments regulatory perimeter.
That reversal closed a policy gap that had kept digital assets outside mainstream financial oversight. Britain’s shift aligned it more closely with the direction Europe’s financial regulators are heading.
Together, these regulatory signals are creating a more predictable environment for tokenized finance. Institutions require clear frameworks before committing to infrastructure investments at scale.
With central bank commentary and government policy now pointing in the same direction, that clarity is forming. Europe’s regulatory posture is becoming one of cautious but deliberate acceptance.
European Institutions Move From Pilots to Permanent Infrastructure
HSBC completed a tokenized deposit pilot on the Canton Network, marking a practical step forward for European banking. The exercise simulated the issuance, transfer, and atomic settlement of its Tokenised Deposit Service.
All three functions were tested in a controlled environment, confirming operational readiness. The pilot demonstrated that large European banks are past the conceptual stage.
ABN Amro extended crypto access to its investment clients through a carefully structured approach. The Dutch bank introduced indirect exposure via Exchange Traded Products and Capital Protected Notes.
Both instruments are available through ABN Amro’s existing investment platforms, keeping the process familiar for clients. That design reflects how European institutions are balancing innovation with risk management.
The most structurally significant development came through the Ondo Finance, Clearstream, and 360X partnership.
Clearstream, Europe’s leading securities depository, will provide custody, settlement, and collateralization for Ondo’s tokenized stocks and ETFs.
This integration places tokenized assets directly inside established institutional workflows. It removes a barrier that had long kept digital assets separate from mainstream settlement infrastructure.
That partnership matters because Clearstream operates at the core of European capital markets. Anchoring tokenized securities within its framework gives institutional participants a trusted, regulated entry point.
European financial infrastructure is no longer sitting adjacent to tokenization. It is becoming part of it.
-

 NewsBeat7 days ago
NewsBeat7 days agoPep Guardiola and Gary Neville agree over Arsenal title problem that benefits Man City
-

 Crypto World6 days ago
Crypto World6 days agoThe SEC Conditionalises DeFi Platforms to Be Avoided for Broker Registration
-

 Fashion2 days ago
Fashion2 days agoWeekend Open Thread: Theodora Dress
-

 Crypto World6 days ago
Crypto World6 days agoSEC Signals Exemption for Crypto Interfaces From Broker Registration
-

 News Videos5 days ago
News Videos5 days agoSecure crypto trading starts with an FIU-registered
-

 Sports3 days ago
Sports3 days agoNWFL Suspends Two Players Over Post-Match Clash in Ado-Ekiti
-
 Crypto World6 days ago
Crypto World6 days agoSEC Proposes Certain Crypto Interfaces Don’t Need to Register as Brokers
-

 NewsBeat6 days ago
NewsBeat6 days agoTrump and Pope Leo: Behind their disagreement over Iran war
-

 Business8 hours ago
Business8 hours agoPowerball Result April 18, 2026: No Jackpot Winner in Powerball Draw: $75 Million Rolls Over
-

 Politics2 days ago
Politics2 days agoPalestine barred from entering Canada for FIFA Congress
-

 Crypto World2 days ago
Crypto World2 days agoRussia Pushes Bill to Criminalize Unregistered Crypto Services
-

 Sports7 days ago
Sports7 days agoNWFL opens Pathway for new Clubs ahead of 2026 Season
-

 Business3 days ago
Business3 days agoCreo Medical agree sale of its manufacturing operation
-

 Entertainment6 days ago
Entertainment6 days agoBrand New Day’ Footage Reveals the Devastating Impact of ‘Now Way Home’
-
 Politics13 hours ago
Politics13 hours agoZack Polanski demands ‘council homes not luxury flats for foreign investors’
-

 Crypto World7 days ago
Crypto World7 days agoTrump whales load up ahead of Mar-a-Lago luncheon.
-
Business7 days ago
Kering slides after Morgan Stanley downgrade, Gucci woes loom
-

 Tech7 days ago
Tech7 days agoGoogle adds E2E encryption to Gmail for iOS and Android enterprise users
-

 Tech7 days ago
Tech7 days agoApple glasses won’t go brand shopping like Meta did with Ray-Ban and Oakley
-
Entertainment7 days ago
How Euphoria Season 3 Premiere Paid Tribute to Eric Dane After Death













You must be logged in to post a comment Login