Crypto World
Up just 0.2% on $36M loot
Since draining Japanese crypto platform UXLINK six months ago (and losing a chunk of the proceeds), the hacker behind the attack has been trying to hit it big on-chain.
It’s not going great.
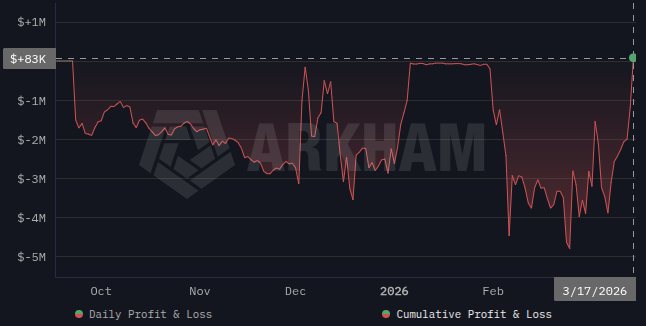
Blockchain analytics platform Arkham has been tracking the hacker’s trading history, highlighting recent ETH sales which brought them back to breakeven.
But given the market over the past six months, one could argue that breakeven is nothing to be sniffed at.
Read more: UXLINK goes from bad, to worse, to weird after hacker loses stolen tokens
The September attack unfolded in two stages. First, UXLINK’s multi-signature wallet was compromised and drained for $11 million worth of assorted crypto tokens.
Hours later, the project’s token contract, which had also been compromised, minted a billion tokens, with a theoretical dollar value in the nine figures.
The drama didn’t stop there, however. While dumping the UXLINK tokens, and cratering its price as liquidity depleted, the hacker fell for a phishing link, losing half the freshly-minted tokens.
Trading with house money
Since then, the hacker’s trading history shows swaps made mainly between the stablecoin DAI and WETH or WBTC.
Arkham’s profit and loss (PnL) calculations put the hacker’s cumulative PnL at $83,000 in the green.
While the gains are small, just 0.2% of the $36.6 million held in the wallets, it’s currently performing better than at any time since the hack.
PnL has been down-only, aside from brief periods of clawing back close to breakeven. But recent weeks have seen a sudden recovery from an all-time low of -$4.8 million in late February.
Read more: Venus Protocol hacker lost $4.7M after nine months of planning
Easy come, easy go
Hackers trading stolen funds have had mixed results in recent years.
Members of North Korea’s Lazarus Group traded the proceeds of 2024’s $50 million Radiant Capital attack, ending up $40 million in profit by last summer.
In October last year, a hacker who previously stole 400 bitcoins from a Coinbase user “panic sold” ether which they had bought with the ill-gotten gains.
During two crypto market crashes, a week apart, they realized a total of $10 million in losses.
Read more: Outdated algorithm caused $650M excess losses on Hyperliquid, report
A slightly more unsettling incident saw Lazarus-linked addresses liquidated for $500,000 on Hyperliquid in late 2024.
While some were happy to see the bad guys get wiped out, others were concerned the activity was testing for a potential future exploit.
Also on Hyperliquid, a wallet linked to the $30 million zKasino “rug pull” in April 2024 suffered a $27 million liquidation a year later.
Got a tip? Send us an email securely via Protos Leaks. For more informed news and investigations, follow us on X, Bluesky, and Google News, or subscribe to our YouTube channel.
Crypto World
Electric Capital Maps 501 Real-World Yield Sources, Finds 93% Untouched by DeFi


A new taxonomy from the venture firm identifies seven barrier clusters keeping most traditional yield sources off-chain, and argues that stablecoin growth is pulling them closer.
Electric Capital published a research report on Monday, cataloging 501 distinct sources of real-world yield and cross-referencing them against tokenized assets with meaningful on-chain traction today.
The venture firm found that only 34 of those yield sources have any on-chain presence above $50 million, and they cluster in familiar territory: U.S. Treasuries, private credit, corporate bonds, and non-U.S. sovereign debt.
The remaining 93% fall into seven groups defined by what’s blocking tokenization, ranging from legal structuring challenges for asset-backed securities to real-world integration hurdles for commodities and compute infrastructure.
Distribution is the Bottleneck
Perhaps the report’s sharpest observation concerns distribution. Of 35 yield-bearing non-stablecoin RWAs above $50 million, only two have crossed 2,000 holders. While some of that is by design — BlackRock’s BUIDL requires a $5 million minimum — the data underscores how dependent most tokenized assets remain on a handful of large deployers and vault curators.
The report highlights how Centrifuge’s JAAA, a tokenized AAA CLO that held $743 million at the time of data collection, lost 44% of its value in a single day on March 9 after Sky’s Grove protocol redeemed $327 million in one transaction.
BlackRock’s BUIDL faces a similar dynamic: its top 10 holders control 98% of supply, and those holders are largely other protocols — Ethena, Ondo, and Sky.
What Comes Next
Electric Capital argues five compounding forces will pull new asset types on-chain: a growing stablecoin base with diversifying yield preferences, competition among protocols for differentiated products, vault infrastructure that absorbs duration risk, tranching layers that expand buyer bases, and leverage loops that multiply demand for collateral-eligible assets.
The firm also flagged AI infrastructure spending — projected by Goldman Sachs to exceed $500 billion in 2026 — as a catalyst, noting that GPU leasing, data center construction, and energy contracts are natural candidates for on-chain financing.
This article was written with the assistance of AI workflows. All our stories are curated, edited and fact-checked by a human.
Crypto World
Google Threat Intelligence Sounds Alarm on Latest Crypto Malware Threat
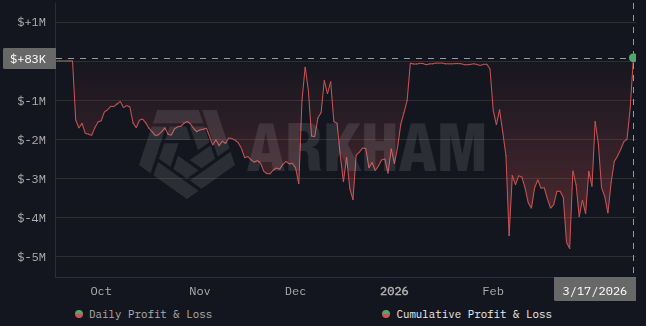
Google Threat Intelligence has identified a new form of crypto-stealing malware called “Ghostblade” that affects Apple iOS devices and is part of the “DarkSword” suite of browser-based malware tools designed to steal private keys and other sensitive information.
Ghostblade is written in JavaScript and designed for rapid data theft. The crypto-stealing malware activates, grabs sensitive data from the compromised device, and relays it to malicious servers, according to Google Threat Intelligence.
The Ghostblade malware does not run 24/7 on the compromised device, does not require extra plug-ins to function, and stops functioning after extracting data, making it more difficult to detect, the threat researchers said.

The malware also includes code that deletes crash reports from the compromised device, preventing Apple from receiving them and flagging the malicious software.
Ghostblade can access and relay messaging data from the iMessage texting application for Apple devices, Telegram and WhatsApp.
The malicious software can also steal SIM card information, identity, multimedia and geolocation data, and access system settings, according to the Google cybersecurity report.

DarkSword and its components are one of the latest cybersecurity threats identified by Google Threat researchers, shedding light on the evolving methods used by malicious actors to steal crypto and other valuable data from unsuspecting users.
Related: Google uncovers iOS exploit kit used in crypto phishing attacks
Hacks fall in February as malicious actors pivot to exploiting human error
Losses from crypto hacks fell to $49 million in February, a sharp decrease from $385 million in January, according to blockchain intelligence platform Nominis.
This drop reflects a pivot from code-based cyber threats to crypto phishing attempts, wallet poisoning attacks and other threat vectors that take advantage of human error, Nominis said in its report.

Phishing attempts typically use fake websites designed to look legitimate. These fake websites often use URLs that are nearly identical to the legitimate sites they masquerade as, tricking users into visiting them.
These sites embed malware that can steal crypto private keys and other valuable data when a user accesses the site or clicks any of its elements.
Magazine: WazirX hackers prepped 8 days before attack, swindlers fake fiat for USDT: Asia Express
Crypto World
Sam Bankman Fried’s past political cash gives AI PAC fuel for going after NY state lawmaker Bores


A political action committee with ties to major tech and crypto donors is raising the specter of disgraced ex-FTX CEO Sam Bankman-Fried to target New York congressional candidate Alex Bores as the state legislator faces a crowded Democratic field.
A sharply worded mailer distributed by Think Big PAC told voters that the Democratic primary candidate for New York’s 12th Congressional District once got more than $100,000 in support from the former head of the failed global exchange, and alleges that “Bankman-Fried’s buddies are bankrolling Bores for Congress.” It also criticizes Bores’ campaign financing and positions him as out of step with constituents, urging voters to “do better than Bores.”
The attack lands as Bores competes in a high-profile primary that has drawn several prominent Democratic contenders, including Jack Schlossberg — a member of the Kennedy family — and other well-connected figures such as George Conway. The race to succeed Rep. Jerry Nadler in the deep-blue Manhattan district is expected to be one of the most closely watched primaries in the 2026 cycle.
“For someone who’s railed against deep fake AI, candidate Bores doesn’t seem to have trouble creating his own reality. He raked in over $100,000 from Sam-Bankman Fried’s sordid political network but refuses to acknowledge the connection” a spokesperson for Think Big PAC told CoinDesk, which confirmed the amounts through state elections filings. “Bores is entitled to his own opinion but not his own set of facts on the role SBF has played in bankrolling his political career.”
Think Big PAC says it’s backing candidates aligned with pro-technology policies and opposing those seen as hostile to innovation of artificial intelligence. The group has previously deployed spending to influence Democratic primaries in Ohio.
Bores, a first-term assemblymember representing parts of Manhattan, has recently drawn attention for introducing legislation focused on artificial intelligence safety and accountability at the state level. The bill aims to impose guardrails on advanced AI systems, and that legislative push may have made him a target.
The mailer zeroes in on political spending tied to Bankman-Fried, who was convicted on fraud charges tied to the collapse of FTX. In the 2022 cycle, Bankman-Fried and other FTX executives were among the largest political donors in U.S. politics, supporting candidates across the political spectrum. A CoinDesk analysis found that 196 members of Congress — more than one-third — received campaign support from Bankman-Fried or affiliated executives during that period. But Bores was unusual as one of only two state-level candidates in New York to receive help from the SBF-affiliated PAC (the other being Lt. Gov. Antonio Delgado).
The Think Big PAC has already spent hundreds of thousands of dollars on ads targeting Bores, including earlier television and digital spots attacking his past work at Palantir. Bores’ campaign pushed back on those ads, sending a cease-and-desist letter accusing the PAC of making “false and defamatory statements” in its ads.
Bores’ campaign has not responded to CoinDesk’s request for comment.
Read more: Congress’ FTX Problem: 1 in 3 Members Got Cash From Crypto Exchange’s Bosses
Crypto World
Ledger Appoints John Andrews as CFO, Opens New York Office Amid U.S. Expansion Push

TLDR:
- John Andrews joins Ledger as CFO, bringing 25+ years of finance experience and Circle’s IPO background.
- Ledger opens a New York office as part of a multi-million-dollar investment to grow its U.S. institutional base.
- Ledger secures over 20% of the world’s crypto and more than 30% of retail-held dollar stablecoins globally.
- Ledger is reportedly preparing for an IPO with a potential valuation exceeding $4 billion, pending market conditions.
Ledger, the global leader in digital asset security, has appointed John Andrews as its new Chief Financial Officer. The announcement came alongside the opening of a new U.S. office in New York City.
Andrews joins from Circle, where he led capital markets and investor relations. The move signals Ledger’s growing ambitions in its largest global market.
Reports suggest the company is preparing for a potential IPO, with a valuation possibly exceeding $4 billion.
Andrews Brings Deep Finance Experience to Ledger’s Growing Team
John Andrews brings over 25 years of experience across corporate finance and financial services. He previously served as Head of Capital Markets and Investor Relations at Circle.
His role there included direct involvement in Circle’s own IPO process. That background makes him a strong fit for Ledger’s current growth trajectory.
At Circle, Andrews worked at the intersection of traditional finance and digital assets. That experience closely mirrors the institutional shift Ledger is now targeting.
Banks, asset managers, custodians, and stablecoin issuers are among the company’s growing client base. Andrews is expected to lead financial strategy as that demand continues to rise.
Ledger CEO Pascal Gauthier shared the news publicly, tying both announcements together. He wrote on social media: “John Andrews brings the institutional rigor and financial leadership needed to scale Ledger’s global vision.”
Gauthier added that Andrews’ experience at the crossroads of traditional finance and digital assets is “exactly what we need.” He also noted the New York office places Ledger Enterprise “at the heart of the financial world.”
Andrews, in turn, expressed confidence in the company’s market position. “Ledger has built the most trusted security platform for digital assets,” he said.
He added that institutions are increasingly seeking secure infrastructure to operate in this ecosystem. Andrews described Ledger as “uniquely positioned to support that transition.”
The IPO timeline remains uncertain due to current market volatility. However, preparations are already reported to be underway.
Andrews’ background in investor relations places him at the center of those efforts. Ledger has not yet confirmed a specific timeline for any public listing.
New York Office Anchors Ledger’s Push Into Institutional Markets
Ledger’s New York office represents a multi-million-dollar investment in the company’s U.S. presence. The office will serve as a strategic hub for Ledger Enterprise, its institutional infrastructure platform.
Dozens of roles are being created across enterprise and marketing functions. The expansion reflects the growing demand from financial institutions for secure digital asset tools.
Gauthier was direct about the role institutions now play in Ledger’s strategy. “Institutions today require the cryptographic certainty that only Ledger provides,” he stated.
He further noted that Ledger Enterprise Multisig and Tradelink give banks and asset managers “the tools to govern and trade assets with total control.” Those products sit at the core of the company’s institutional offering.
Andrews echoed that sentiment upon joining. “I’m excited to join the company at such an important moment for its growth,” he said.
He also expressed gratitude to Gauthier for the trust placed in him. Andrews called it an honor to join a team “respected across the industry for its leadership.”
The New York office will be formally celebrated on March 23rd. The event will bring together industry leaders, partners, and members of the digital asset ecosystem.
It follows a multi-year global partnership with the San Antonio Spurs. That deal further strengthened Ledger’s brand presence across the United States.
Ledger currently secures more than 20% of the world’s crypto assets and has sold over 8 million devices across 165 countries. The company also helps secure over 30% of dollar stablecoins held by retail investors.
As adoption accelerates, Ledger is positioning itself as the go-to infrastructure layer for institutional crypto operations. The New York office places the company firmly at the center of that shift.
Crypto World
Bitget CFD Hits 6B as Traders Move into Gold and Oil

The increase in the demand for commodities spurs up growth of volume
The more the price swings, the more traders have been moving towards the derivatives of gold and oil. Oil prices have also been increasing to multi-year levels, aided by the current conflict in Iran. Also, gold has been performing well, given that investors have turned to it to offer security in the midst of unpredictability in the market. The trend has motivated traders to spend outside of crypto assets and to invest in conventional instruments.
According to Bitget, the behavior of the users is noticeably changing as they abandon single-market exposure. Rather, it is now actively trading in a variety of asset classes on a single platform. As a result, the trading activity has become more dispersed among forex pairs, indices, and commodities, as well as digital assets, in response to correlated moves in the global financial systems.
The exchange has increased its services in terms of tokenized stocks, exchange-traded funds, and precious metals. In addition to this, Bitget has launched new features that enable traders to trade in the traditional market with crypto-friendly infrastructure. These improvements are meant to help users who desire to have integrated access to various financial markets.
Embedding of Crypto and Traditional Markets Increases
Bitget claimed to provide the CFD system that allows trading global assets with stablecoin margins. This system enables traders to trade various positions in one account. Furthermore, the platform underscored how traditional finance and digital assets still come together. With the growth of markets coalescing, traders tend to turn towards cross-asset strategies to realize the prospects. The increase in the CFD volume of Bitget indicates the increased demand for diversified trading opportunities. It also indicates the way in which the uncertainty in the world pushes traders to multi-asset exposure.
Crypto World
Ethereum Approaches Cycle Low as Bitmain Indicates Violent Belief
The present perspective is determined by historical correlations
Lee based part of his opinion on the analysis of a market technician named Tom DeMark. The data indicate that the recent price trend of Ethereum is highly correlated with the S&P 500 during the crash of 1987 and the correction of 2011. These trends suggest that Ethereum might already be at a bottom or nearing one.
As of today, Ethereum is trading at an approximate 22 percent discount to its real price of 2,241. The measure represents the mean price floor of every coin on-chain. Moreover, the same discounts were observed at the bottoms of past cycles, which supports the idea that selling pressure could be declining.
Bitmain has over 3 million staked Ether worth approximately 6.6 billion. The company also has close to 10 billion in crypto assets. The exposure indicates high confidence in Ethereum’s long-term recovery and has helped lift its stock during premarket trading on March 16. In addition, the size of its stake reflects growing institutional readiness to hold large crypto positions in bear markets. This movement continues to influence mood in digital-asset markets.
Bullish signals notwithstanding, mixed sentiment prevails
The bottom call does not find support among all market participants, regardless of the available data. Individual traders have reported that such claims have been made in the past few months without validation. Nonetheless, others refer to Ethereum’s historical trend, which has involved strong recoveries following extensive corrections. Ethereum has delivered high returns over the long run in the last ten years. In addition, analysts note that past cycles tended to experience prolonged periods of consolidation followed by recovery. This supports the view that the current market structure can be consistent with previous turning points.
Crypto World
Analyst warns traders pricing in TACO trade could face a rude awakening
Traders are underestimating how deeply the current conflict in the Middle East could reshape the macro backdrop, with some positioning around a so‑called “TACO trade”—short for “Trump always chickens out”—dominating chatter in crypto and broader markets. Nic Puckrin, founder of Coin Bureau, popularized the term to describe a supposed tendency for U.S. leadership to back away from geopolitical flare‑ups. But he cautions that the situation is far more intricate than a single decision by any one leader, and there are no quick exits from a widening conflict.
Oil prices have become a central barometer for the scenario. If crude stays above $100 per barrel, growth in the United States could slow while Personal Consumption Expenditures inflation rises, potentially by as much as one percentage point, according to Puckrin. That dynamic would complicate the Federal Reserve’s already delicate task of steering policy in an environment where inflation remains persistent and growth is uncertain. The risk of stagflation—the painful combination of rising prices with weak growth and employment—emerges as a real possibility if energy costs stay elevated through the second and third quarters.
Key takeaways
- Oil could stay a decisive driver: Sustained prices above $100 per barrel threaten growth and lift inflation in tandem, increasing stagflation risk.
- The TACO trade is not a guaranteed play: While the term captures a belief in limited appetite for geopolitical escalation, experts warn that policymakers and markets should expect a more complex, drawn‑out conflict with no easy exit.
- Strait of Hormuz disruption compounds the risk: Prolonged disruption through the vital chokepoint raises the energy price floor and feeds into broader inflation dynamics.
- Policy path remains uncertain: The Fed held rates at 3.5%–3.75%, with market odds of a near‑term cut fading and a non‑zero probability (about 12%) of a rate increase at the next meeting.
- Crypto and risk assets face a nuanced outlook: Higher energy costs and uncertain monetary policy can dampen liquidity for risk assets, even as some traders seek hedges or tactical exposure.
Oil shocks, chokepoints, and the market’s fragile balance
The incoming energy data and geopolitical risk have pushed crude higher in recent sessions, with WTI briefly touching the high‑end of the $110s and flirting with $120 per barrel as the conflict widened. The persistent tension around the Middle East has intensified concerns that global supply flows could be constrained if oil infrastructure faces sustained disruption. Market observers point to the Strait of Hormuz as a pivotal artery—through which a sizable portion of the world’s oil shipments pass—and note that any sustained closure or damage could push prices higher for an extended period.
Analysts emphasize that even a reopening of maritime routes would not instantly restore pre‑crisis conditions. “Disruption to the Gulf’s oil-producing infrastructure will take months to rebuild,” one commentator noted, underscoring the slow‑burn impact on prices and the broader economy. The energy price surge feeds through to a wide array of goods and services, often lifting inflation broadly rather than affecting a single sector in isolation. In such a regime, inflationary pressures can push the real cost of living higher while limiting the central bank’s ability to loosen financial conditions quickly.
Beyond the immediate supply shock, energy is a fundamental input into nearly all economic activity. When energy costs rise, every sector faces higher costs, and central banks can find themselves juggling the risk of inflation against the imperative to support growth. The macro calculus becomes especially delicate if markets price in a persistent energy premium that persists through the next several quarters, complicating any hopes of an early, policy‑driven risk‑on rally for crypto and other speculative assets.
Policy uncertainty and the Fed’s calculated stance
The Federal Open Market Committee’s decision to hold the Federal Funds rate at 3.5%–3.75% in March reflected a cautious stance in the face of renewed energy‑driven inflation risks. Market observers say that near‑term rate cuts have faded from the central scenario, while a minority of traders assign a non‑negligible probability to a rate move higher in the near term, as reflected by the CME Group’s FedWatch tool, which placed the odds of a hike at around 12% for the next meeting.
Fed Chair Jerome Powell acknowledged that the economic implications of the Middle East conflict are unclear in the near term. Speaking at a press conference, he stressed that while energy prices are a potential drag on inflation and growth, it is still “too soon” to accurately gauge the full scope of the disruption’s impact on the broader economy. The central bank’s ongoing assessment will hinge on incoming data, including energy price trajectories, inflation readings, and indicators of domestic demand.
Measured against today’s macro backdrop, the risk premium for risk assets, including crypto, could be influenced by how energy costs evolve and how quickly monetary policy adapts. If energy prices remain elevated and inflation proves more persistent than anticipated, the Fed may lean toward a tighter stance for longer, which could constrain liquidity in markets and temper speculative appetites. Conversely, any signs of cooling inflation or a surprise easing in market stress could renew expectations for looser policy and a more favorable environment for higher‑beta assets.
What readers should watch next
Investors should monitor three interconnected threads in the coming weeks: first, the trajectory of global oil prices and the duration of any supply disruptions through strategic chokepoints; second, the evolving assessment of inflation and growth signals that inform Fed policy; and third, how sentiment around geopolitical risk interacts with liquidity conditions in crypto markets. With the energy‑inflation nexus likely to dominate near‑term headlines, traders would be wise to differentiate between narrative positioning and data‑driven developments as markets digest the evolving risk landscape.
In this environment, the market’s reflex to geopolitical risk could remain biphasic: periods of reprieve followed by renewed volatility as new information emerges about the conflict’s scope, energy infrastructure resilience, and policy responses. Keep an eye on energy price momentum, central bank communications, and liquidity signals across major crypto and traditional risk assets to gauge where the next phase of the cycle may lead.
Crypto World
World Gold Council Proposes Shared Infrastructure for Tokenized Gold Products


The industry body co-authored a white paper with Boston Consulting Group outlining a “Gold as a Service” platform to standardize issuance and custody of digital gold.
The World Gold Council, the gold industry’s leading market-development body, announced Thursday it is building shared infrastructure designed to make digital gold products more interoperable, scalable, and easier to launch.
The initiative, detailed in a white paper co-authored with Boston Consulting Group, proposes a platform called “Gold as a Service” — an open middleware layer connecting physical gold custody with the digital systems used to issue and manage gold-backed products.
The platform would standardize backend processes, including custody coordination, reconciliation, compliance, and redemption, while leaving front-end product design and branding to individual issuers.
The tokenized gold market has ballooned in recent months but remains structurally fragile. Total market capitalization has surpassed $5 billion, but the sector is dominated by just two products, Tether Gold (XAUT) and Paxos Gold (PAXG), which control more than 95% of the market.
That concentration reflects the high barriers to entry that the WGC’s white paper aims to address. Launching a digital gold product today requires issuers to independently build custody relationships, compliance pipelines, audit frameworks, and redemption logistics, a fragmented setup that limits competition and hampers fungibility across products.
The WGC argues that a shared service layer could lower those barriers, enabling new issuers to enter the market while making digital gold products more interchangeable, a prerequisite for deeper liquidity and broader DeFi integration.
3 Layer Architecture
The proposed system is organized around three layers. A physical layer would manage sourcing, storage, transport, and redemption of actual gold. A digital layer would handle issuance, ownership records, and product-lifecycle management. Finally, an interface layer would allow issuers to build their own customer-facing experiences on top of the shared stack.
Under this model, issuers would compete on user experience, pricing, and distribution — not on custody infrastructure. The WGC envisions digital gold eventually serving as deployable capital, enabling use cases such as being pledged as collateral for borrowing.
Gold Drops
Gold is trading at around $4,500 per ounce after falling sharply from above $5,000 earlier in the week. Gold rose 64% in 2025, its strongest annual performance in decades, driven by central bank purchases and demand for safe-haven assets amid geopolitical uncertainty.
The rally has catalyzed a wave of tokenized gold activity. In January, the sector crossed $4 billion in market value.
Yet the sector’s growth has also highlighted its structural limitations — exactly the problems the WGC’s initiative is designed to solve. The WGC noted that above-ground gold supply is worth more than $30 trillion, dwarfing the current tokenized market and underscoring the growth potential that standardized infrastructure could unlock.
This article was written with the assistance of AI workflows. All our stories are curated, edited and fact-checked by a human.
Crypto World
TRON price: bulls target 7-month high as TRX holds $0.30 level


- TRON (TRX) is among altcoins seeing a slight uptick.
- The token hovered above $0.30 amid broader volatility across the cryptocurrency market.
- Bulls could target highs of $0.37 if momentum holds.
On Friday, March 20, TRX traded to highs of $0.308 across major exchanges, climbing about 3% in intraday performance that included a 7% spike in daily volume.
By maintaining prices above the critical support level, bulls could tap into factors such as regulatory clarity, trading expansion, and institutional demand to target levels last seen in August 2025.
TRX price holds $0.30: what’s bullish
TRX’s price outlook in the past 24 hours mirrors most top altcoins, including Ethereum, XRP, and Solana.
However, while ETH and SOL eye retest of recent highs, TRX looks positioned for an upside run to a 7-month high. Multiple potential bullish catalysts could converge to accelerate this.
TRX on Base
A key development includes TRON’s announcement of the TRX/USDC trading pair launch on Aerodrome Finance, the leading decentralized exchange (DEX) on Base.
The move integrates TRX into Base’s rapidly expanding DeFi ecosystem and bridges TRON’s established high-throughput blockchain with one of DeFi’s fastest-growing environments. Liquidity and trading could spark a TRX pump.
SEC/CFTC guidance
Adding momentum, the crypto market welcomes joint SEC and CFTC interpretive guidance classifying assets into clear regulatory classes.
We have digital commodities (BTC, ETH, SOL, XRP, ADA, LINK, and others), digital collectibles (NFTs, memecoins), digital tools (utility/access tokens), payment stablecoins, and digital securities.
The industry says this move puts crypto on the path to greater adoption.
“Clear enough to guide markets, flexible enough to accommodate innovation, and firm enough to protect investors.” https://t.co/Goxt1okKF5
— TRON DAO (@trondao) March 19, 2026
TRON Inc. purchases
Meanwhile, TRON Inc. persists in accumulating TRX. Other than bolstering its treasury strategy, the company is signaling long-term confidence.
These and other bullish triggers could accelerate TRX’s breakout above $0.30.
In the past 24 hours, TRON recorded over $577 million in volume, thanks to sentiment around this.
TRON price outlook
TRX is eyeing a potential breakout above $0.32. If this happens, bulls could target $0.37. The level marked the altcoin’s peak in August 2025.
On the weekly chart, TRX trades just above a downtrend line from last August.
The move to pierce the resistance zone means a potential breakout amid a cup and handle formation.

RSI is in neutral territory around 55, but is upsloping to signal room for further gains before overbought conditions come into play.
A close above $0.32 could trigger a rally targeting $0.35-$0.37 resistance.
The November 2025 high of $0.45 stands as the next hurdle.
However, failure to hold $0.30 risks a dip to $0.28 support. Below that would be $0.25.
Crypto World
Roblox (RBLX) Stock Dips as Platform Introduces Revenue Share on Brand Sponsorships
Key Highlights
- Platform will implement revenue sharing on brand sponsorships beginning May 4, 2026
- Updated advertising policies broaden the definition of promotional content to include any brand-compensated material or external product placement
- Age restrictions limit pharmaceutical and financial service advertisements to users 13 and older
- Dennis Durkin, previously CFO at Activision Blizzard, joins the company’s Board of Directors
- Current analyst consensus rates RBLX as a Buy with a price target of $110
After pursuing advertising opportunities for more than four years, Roblox is implementing its most significant policy transformation to date.
Beginning May 4, 2026, the platform will roll out comprehensive changes to its advertising framework — marking the first time the company will directly participate in revenue generated from brand partnerships within games hosted on its ecosystem.
The revised guidelines establish that promotional material includes any content funded by brands or featuring products available beyond the Roblox platform. This represents a more comprehensive and explicit framework than previous standards.
The updated policy also introduces age-specific restrictions. Players younger than 13 will not see advertisements for pharmaceutical products or financial services. Additionally, this demographic will be excluded from interactive ad experiences that provide in-game incentives for viewing or interacting with sponsored content.
According to the company, these changes aim to streamline brand integration. Through standardized guidelines, transparent pricing structures, and measurable outcomes, Roblox seeks to create a more attractive environment for advertising investment.
Years in Development
The pursuit of advertising revenue has been part of Roblox’s strategic plan since at least 2021. Leadership has consistently highlighted opportunities including video advertisements, virtual billboards, and branded virtual merchandise as potential revenue streams benefiting both the platform and its creator ecosystem.
Several independent creators have already generated substantial income — in some cases exceeding hundreds of thousands of dollars — through branded experiences and virtual items. The upcoming revenue-sharing framework formalizes these arrangements and ensures Roblox receives a portion of future deals.
Specific details regarding the revenue split structure remain under development. The company has indicated that comprehensive information will be released during the second quarter of 2026.
Roblox stock (RBLX) declined 1.23% at the time of reporting.
Industry Veteran Appointed to Leadership
On March 19, 2026, Roblox welcomed Dennis Durkin as an independent Class II director on its Board of Directors.
Durkin brings extensive gaming industry credentials, having served as CFO and President of Emerging Businesses at Activision Blizzard. His career also includes executive positions within Microsoft’s Xbox and gaming divisions — representing nearly 30 years of technology and gaming sector expertise.
He has been assigned to both the Audit and Compliance Committee and the Leadership Development and Compensation Committee.
Durkin’s compensation package includes standard cash retainers for board and committee participation, supplemented by time-based restricted stock unit grants aligned with the company’s established outside director compensation framework.
The board appointment was formally disclosed on March 20, 2026.
The latest Wall Street rating on RBLX maintains a Buy recommendation with a $110.00 price objective. TipRanks’ AI analyst assigns a Neutral rating, acknowledging robust cash flow generation and positive booking trends while highlighting ongoing profitability challenges, margin fluctuations, and balance sheet concerns.
-

 Crypto World7 days ago
Crypto World7 days agoHYPE Token Enters Net Deflation as HyperCore Buybacks Outpace Staking Rewards
-

 Tech5 days ago
Tech5 days agoYour Legally Registered ‘Motorcycle’ Might Not Count Under Proposed US Law
-

 Tech3 days ago
Tech3 days agoAre Split Spacebars the Next Big Gaming Keyboard Trend?
-
Sports6 days ago
Why Duke and Michigan Are Dead Even Entering Selection Sunday
-

 Business5 days ago
Business5 days agoSearch for Savannah Guthrie’s Mother Enters Seventh Week with No Arrests
-

 Business6 days ago
Business6 days agoUS Airports Launch Donation Drives for Unpaid TSA Workers as Partial Government Shutdown Enters Fifth Week
-

 Crypto World6 days ago
Crypto World6 days agoCoinbase and Bybit in Investment Talks: Could Bybit Finally Enter the US Crypto Market?
-

 Business4 days ago
Business4 days agoAustralian shares drop as Iran war enters third week
-

 Business6 days ago
Business6 days agoCountry star Brantley Gilbert enters growing non-alcoholic beer market
-
 Politics2 days ago
Politics2 days agoThe House | The new register to protect children from their abusers shows Parliament at its best
-

 Crypto World4 days ago
Crypto World4 days agoCrypto Lender BlockFills Enters Chapter 11 with Up to $500M in Liabilities
-

 News Videos2 days ago
News Videos2 days agoRBA board divided on rate cut, unusually buoyant share market | Finance Report | ABC NEWS
-

 Fashion4 days ago
Fashion4 days ago25 Celebrities with Curly Hair That Are Naturally Beautiful
-

 Tech15 hours ago
Tech15 hours agoinKONBINI Lets You Spend Summer Days Behind the Register
-

 Crypto World2 days ago
Crypto World2 days agoCanada’s FINTRAC revokes registrations of 23 crypto MSBs in AML crackdown
-

 Politics3 days ago
Politics3 days agoReal-time pollution monitoring calls after boy nearly dies
-

 Crypto World6 days ago
Crypto World6 days agoCrypto Losses Drop 87% in February, But Hackers Are Now Targeting People, Not Code
-
 NewsBeat2 days ago
NewsBeat2 days agoResidents in North Lanarkshire reminded to register to vote in Scottish Parliament Election
-

 Business4 days ago
Business4 days agoMeta planning major layoffs as AI spending and automation reshape workforce
-

 Politics5 days ago
Politics5 days ago9 Stylish Leather Jackets Perfect For Spring 2026











You must be logged in to post a comment Login