Tech
A microscope reveals the ghost of analog video hidden inside a LaserDisc


Jueden’s experiment began by accident. While using a low-cost digital microscope to inspect electronics, he turned it toward a LaserDisc out of curiosity. Under magnification, faint but recognizable images began to emerge – proof that LaserDisc’s analog encoding could still be decoded visually without a player, just by analyzing the…
Read Entire Article
Source link
Tech
Europe’s cyber agency blames hacking gangs for massive data breach and leak

The European Union’s cybersecurity agency said Thursday that a recent hack and data breach at the EU’s executive body was the work of a cybercriminal group known as TeamPCP.
In a new report, CERT-EU also reported that the hackers stole around 92 gigabytes of compressed data from a compromised Amazon Web Services (AWS) account used by the bloc’s executive, the European Commission, which included personal data containing names, email addresses, and the contents of emails.
The breach affected the cloud infrastructure of the Commission’s Europa.eu platform, which member states use to host websites and publications of the bloc’s institutions and agencies.
CERT-EU wrote that the data of at least 29 other EU entities may be affected, and that dozens of internal European Commission clients could have had data stolen as well.
The stolen data was then posted online by another hacking group, the notorious ShinyHunters.
While the size of the data breach is itself notable, the hack and subsequent leak of the European Commission’s data by two separate hacking groups highlights a growing trend of cybercriminals working together to extort their victims.
CERT-EU said that the breach originated on March 19 when hackers acquired a secret API key associated with the European Commission’s AWS account, following an earlier hack targeting the open-source security tool Trivy. The Commission inadvertently downloaded a copy of the compromised Trivy tool following the project’s recent breach, allowing the hackers to steal its secret API key and use that access to pivot to obtain data stored in the Commission’s AWS account.
While the service said it’s still analyzing the data published online, close to 52,000 files contain sent email messages. CERT-EU said the majority of these emails are automated with little to no content, but emails that bounced back with an error “may contain the original user-submitted content, posing a risk of personal data exposure.”
CERT-EU said it is already in contact with affected organizations.
Contact Us
Do you have more information about this breach? Or other cyberattacks? From a non-work device, you can contact Lorenzo Franceschi-Bicchierai securely on Signal at +1 917 257 1382, or via Telegram and Keybase @lorenzofb, or email.
A spokesperson for the European Commission told TechCrunch that the body is closed until next week, and would respond to a request for comment then.
A member of ShinyHunters did not respond to requests for comment.
Besides the Trivy beach, TeamPCP has been linked to ransomware attacks and crypto-mining campaigns, says Aqua Security, which develops Trivy. The hackers have more recently been behind a systematic campaign of supply chain attacks compromising other open source security projects, according to Palo Alto Networks Unit 42.
By targeting developers with keys to access sensitive systems, the hackers “then have the ability to hold compromised organizations for ransom, demanding extortion payments,” Unit 42 wrote.
Tech
Flat tire? Dead battery? Speedy’s serves stranded Seattle riders as a quicker e-bike picker-upper


If you’ve ever tried to lift and fit a big, heavy e-bike into the back of a car, Tyler Swartz feels your pain, and went to work on a solution.
Swartz, a Seattle native and cycling enthusiast, is the founder of Speedy’s, a roadside service for e-bike owners who are stranded by a flat tire, dead battery, or some other breakdown and need their bike transported to a shop for repair.
Speedy’s doesn’t do the fixing, but it does the heavy lifting, promising a 90-minute emergency response time.
The idea came to Swartz after he was laid off from his product manager job at Reddit in 2023 — during parental leave with his third child. While using his e-bike as the family errand and adventure wagon, he realized how hard it was to get the bulky machine to a bike shop if it stopped working. His brother pitched the idea of AAA for e-bikes — all he would need is a truck.
“My initial reaction was, ‘Wow, that sounds like driving a truck around,’” Swartz told GeekWire. “Doesn’t sound fun. Doesn’t sound like a sexy software solution.”
But the more he wrapped his head around the problem, the more he liked the idea of serving a community of e-bike enthusiasts in a city that values sustainability.
He launched Speedy’s in 2024 after purchasing an electric cargo van outfitted inside for e-bike transport and wrapped in pink outside with his branding. Two years later the bootstrapped service has attracted more than 325 active members and completed 384 trips across 1,900 miles with a team of five drivers.

Speedy’s is partnering with several Seattle-area bike shops, which are offering a free trial of the service with a new bike purchase. Swartz said it was important to him to convey that he was not out to steal the shops’ business — he wanted to help get customers back to shops.
The service costs $99 per year — covering all bikes in a family — and is good for up to six pickups. Speedy’s handles emergency calls and scheduled ones which can be arranged 24 hours in advance with the company’s calendar tool.
Speedy’s covers a big area across Seattle, Bellevue, Kirkland, Redmond, Bothell, and surrounding communities. And it guarantees its 90-minute response from 8 a.m. to 8 p.m. It’s been on time for every call it’s received so far.
Beyond the website, the user-experience is mostly text-based. Swartz did create a feature where he sends customers a link that tracks the location of the Speedy’s van, for an Uber-like experience as they wait.
Swartz is excited about Seattle’s robust e-bike market, especially with Washington state’s e-bike rebate program, which started accepting applications this week and will begin random selections on April 13.
His goal is to get to 600 customers this year so he can start paying himself. His long-term vision is to be in 30 cities across North America, serving 225,000 members.
“It’s just slow and steady growing,” Swartz said. “In software you’re used to nothing, nothing, and then it really accelerates. With local services, it’s slow and steady.”
Tech
Man Finds Xbox 360 Dev Kit At Garage Sale With A Hidden Gem Game Inside

Even over 20 years after its launch, there are still surprises surrounding the Xbox 360. There are numerous hidden features Xbox 360 players should know about, and there are discoveries made now and then pertaining to the console’s history. One that recently came to light stemmed from a garage sale of all places, where someone purchased what many might perceive as just an ordinary Xbox 360 for $5. This would be a solid deal on its own, but it’s even better with the knowledge that this was an Xbox 360 development kit — one with some remarkable stuff within it for “Grand Theft Auto” enthusiasts.
Word of the discovery hit the Internet via the GTAForums, where user janmatant revealed their incredible $5 score to the community. The console itself is the classic “fat” Xbox 360 model that has an Xbox 360 XDK label on the back and features the developer-used operating system Xshell. The only thing on the hard drive was a copy of “Grand Theft Auto IV,” specifically a 2007 pre-release version. That’s to say that it differs greatly from the official release of the game that hit shelves in 2008, including things that were cut before release or were previously only seen sparingly in gameplay trailers and cutscenes.
Not only is an Xbox 360 for $5 an incredible deal, but the treasure trove of previously unknown or considered possibly lost “GTA IV” content is staggering. As the fandom has combed through the files, some pretty stellar discoveries have been made.
This dev kit is a GTA IV unreleased content goldmine
With this story coming to light, the files from this dev kit were dumped online to the Internet Archive for “Grand Theft Auto IV” fans to dig through. In the aforementioned GTAForums thread dedicated to the “GTA IV” beta, some pretty incredible finds were churned up shortly after the file dump. Environmental assets, unused character models, all kinds of textures, voice lines, vehicles, weapons, and more were revealed, but none of these were quite the biggest discovery of them all. That honor went to an unfinished mini-game mode centered around zombies.
Yes, the same year fellow gaming giant “Call of Duty” brought its zombies mode to life for the first time, the minds behind the “GTA” franchise sought to explore this horror theme. The “GTA IV” beta find revealed bloodied assets of hospital beds and corpses, as well as weapon and health pickups that would presumably be scattered around to aid players’ survival. According to longtime Rockstar North technical director Obbe Vermeij, however, this mode didn’t get too far and was more a product of the “put zombies in everything” craze of the late 2000s into the early 2010s.
With “GTA VI” delayed yet again, this is all a nice bit of excitement to keep the fanbase engaged while the wait continues. Unfortunately, it seems like the fun might not last much longer.
Rockstar may have already stepped in
As thrilling as it is to finally have so much new “GTA IV” material to sift through almost two decades after its release, such a high-profile story was bound to reach the ear of the folks at Rockstar Games and its parent company, Take-Two Interactive. The two have built a collective reputation as particularly litigious and incredibly protective of their games, of what players do with them in terms of modding, and of how they’re actually played. Therefore, it wouldn’t be too surprising if they took legal action over this “GTA IV” discovery.
At the time of publication, the Internet Archive post for the dev kit file drop appears to have been removed, suggesting that Rockstar and Take-Two may have stepped in. Strangely, though, currently, no action has been taken against the GTAForums thread discussing all of the found materials, with no thread lock or post deletion. Neither Rockstar nor Take-Two has spoken on the matter, leaving some, like GTAForums user Glenni91, to theorize that perhaps the main issue wasn’t the unreleased material, but putting a complete build of “GTA IV” onto the Archive, which would bring the situation into copyright-violating territory.
No matter where it ends up going from here, this “GTA IV” beta drop was a welcome surprise. All these years, franchise expansions, and console generations after its release, it’s cool to see what the game could’ve been on top of what was ultimately offered.
Tech
NASA’s Artemis II is on a voyage around the Moon
NASA’s Artemis II successfully , with its crew on a 10-day mission to circle the Moon. It’s the and a major step toward humanity returning to our little neighbor in the future. Since launch, the vehicle has separated from its launch system and been manually piloted, testing how the Orion capsule will dock with future lunar landers. There have been some snags, however: The onboard toilet went awry, and .
Jokes aside, there is something magnificent about seeing humanity taking to the stars once again. That, for all of our worst instincts, we can still come together to solve problems and explore beyond our own horizons.
— Dan Cooper
The other big stories (and deals) this morning
The company is long on promises, short on evidence.
Donut Lab
At CES 2026, a Finnish–Estonian startup claimed to have invented a world-changing solid state battery. Rather than explain how it did so, it engaged in a lengthy campaign teasing out data that didn’t quite support its explosive claims. to separate truth from hype and found there’s little of the former and far, far too much of the latter.
It’s pricier than other portable mixers, but for good reason.
James Trew for Engadget
As James Trew says, $300 is a lot for a portable mixer in this class, but Roland’s brand new justifies its price. Unlike its predecessor, the Pro-X, it gets a second XLR port, MIDI connectivity and a display offering visible VU meters. That you can also use it as a desktop interface adds another layer of icing on an already sweet cake.
I’m actually rather excited about this one.
Sam Rutherford for Engadget
WWDC 2026 isn’t until the summer, but we’re already collating enough rumors from the mill to bring you the inside skinny. Early reports suggest , tidying up after itself inside its software rather than going hard on new features. Hopefully, that will see the gaudier excesses of Liquid Glass dialed down, a lot of trimmed cruft and stability improvements. Oh, and some guff about AI.
Who cares about sound quality when your speaker transforms!?
Sam Rutherford for Engadget
There are some things in life that would normally be a hard sell, a $1,400 boombox that could just about move around with poor sound quality being one of them. Dress it up as , however, and suddenly Sam Rutherford is racing for their wallet.
On the subject of expensive things…
Steve Dent for Engadget
Nebula’s built quite the track record for making projectors you’re actually proud to show off. Its latest is , which combines a beefy 4K projector with a 400-watt Dolby Atmos 7.1 speaker system. That’s a hell of a lot of tech in a single package and is clearly at home at the center of a backyard movie night under the stars. But is it worth the $5,000 asking price? For that, you’ll need to read Steve Dent’s review.
Tech
Perplexity’s ‘Incognito Mode’ Is a ‘Sham,’ Lawsuit Says

An anonymous reader quotes a report from Ars Technica: Perplexity’s AI search engine encourages users to go deeper with their prompts by engaging in chat sessions that a lawsuit has alleged are often shared in their entirety with Google and Meta without users’ knowledge or consent. “This happened to every user regardless of whether or not they signed up for a Perplexity account,” the lawsuit alleged, while stressing that “enormous volumes of sensitive information from both subscribed and non-subscribed users” are shared.
Using developer tools, the lawsuit found that opening prompts are always shared, as are any follow-up questions the search engine asks that a user clicks on. Privacy concerns are seemingly worse for non-subscribed users, the complaint alleged. Their initial prompts are shared with “a URL through which the entire conversation may be accessed by third parties like Meta and Google.” Disturbingly, the lawsuit alleged, chats are also shared with personally identifiable information (PII), even when users who want to stay anonymous opt to use Perplexity’s “Incognito Mode.” That mode, the lawsuit charged, is a “sham.”
“‘Incognito’ mode does nothing to protect users from having their conversations shared with Meta and Google,” the complaint said. “Even paid users who turned on the ‘Incognito’ feature still had their conversations shared with Meta and Google, along with their email addresses and other identifiers that allowed Meta and Google to personally identify them.” “Perplexity’s failure to inform its users that their personal information has been disclosed to Meta and Google or to take any steps to halt the continued disclosure of users’ information is malicious, oppressive, and in reckless disregard” of users’ rights, the lawsuit alleged.
“Nothing on Perplexity’s website warns users that their conversations with its AI Machine will be shared with Meta and Google,” Doe alleged. “Much less does Perplexity warn subscribed users that its ‘Incognito Mode’ does not function to protect users’ private conversations from disclosure to companies like Meta and Google.”
Tech
OpenAI Acquires Popular Tech-Industry Talk Show TBPN

OpenAI is acquiring tech news podcast TBPN, a fast-growing daily show hosted by John Coogan and Jordi Hays. OpenAI says TBPN will keep its editorial independence, even though the acquisition is widely viewed as part of a broader effort to influence public discourse around AI. CNBC reports: In the announcement, OpenAI CEO of AGI Deployment Fidji Simo wrote that their mission of bringing artificial general intelligence comes with a responsibility to have a space for “constructive conversation about the changes AI creates.” Altman has appeared on TBPN multiple times and is a frequent presence across media and podcasts, even hitting NBC’s “Tonight Show Starring Jimmy Fallon” in December.
The announcement says TBPN will maintain editorial independence and continue to choose its own guests. “TBPN is my favorite tech show. We want them to keep that going and for them to do what they do so well,” Altman wrote in a post on X. “I don’t expect them to go any easier on us, am sure I’ll do my part to help enable that with occasional stupid decisions.” OpenAI did not disclose the terms of the deal but said TBPN will be housed within its strategy organization. “While we’ve been critical of the industry at times, after getting to know Sam and the OpenAI team, what stood out most was their openness to feedback and commitment to getting this right,” wrote Hays in a statement. “Moving from commentary to real impact in how this technology is distributed and understood globally is incredibly important to us.”
Tech
Evolution of Ransomware: Multi-Extortion Ransomware Attacks

Ransomware’s Real-World Impact Across Industries
In February 2026, the University of Mississippi Medical Center (UMMC) fell victim to a ransomware attack. The incident took the Epic electronic health record system offline across 35 clinics and more than 200 telehealth sites, forcing the cancellation of chemotherapy appointments and the postponement of non-emergency surgeries. Medical staff were required to revert to paper-based workflows, leaving countless patients to bear the consequences.
UMMC is far from an isolated case. According to recent data, 93% of U.S. healthcare organizations experienced at least one cyberattack in 2025, and 72% of respondents reported that at least one incident directly disrupted patient care.
The manufacturing and financial sectors are equally exposed. In February 2026, payment processing network BridgePay suffered a ransomware attack that took its APIs, virtual terminals, and payment pages completely offline. Across all industries, publicly disclosed ransomware attacks surged 49% year-over-year in 2025, reaching 1,174 confirmed incidents.
As hospitals halt treatments, financial institutions freeze transactions, and manufacturers shut down production lines, ransomware has firmly established itself as a direct business risk with tangible operational consequences.
The Evolution of Ransomware: Double Extortion
Early ransomware operated on a straightforward premise: infiltrate a system, encrypt files, and demand payment in exchange for the decryption key. As organizations began countering this tactic by restoring from backups rather than paying ransoms, threat actors responded by developing a more lucrative model — double extortion.
In a double extortion attack, adversaries first exfiltrate sensitive files — such as patient records and billing data — before encrypting the target system. Victims are then pressured on two fronts: pay to receive the decryption key, or face public exposure of the stolen data.
Backups alone are insufficient against this model. Since attackers already possess the data, refusing to pay the ransom can result in the public release of sensitive files, exposing organizations to significant business losses and regulatory consequences.
The threat landscape has continued to escalate, with triple extortion cases on the rise — a tactic in which attackers directly contact a victim organization’s customers or partners to apply additional pressure.
As of 2025, 124 active ransomware groups have been identified, 73 of which are newly emerged.
The proliferation of AI-powered tools has lowered the barrier to entry for cybercrime, making ransomware capabilities increasingly accessible to less sophisticated actors.
D.AMO makes stolen data unreadable.
See how D.AMO defends against every stage of a ransomware attack.
A Defense Architecture for Multi-Extortion Threats
The rise of multi-extortion ransomware fundamentally changes the assumptions underlying traditional defense strategies. Perimeter-based prevention alone is no longer sufficient.
Organizations need a security posture that protects data from being weaponized after a breach — rendering exfiltrated data unreadable, blocking ransomware from accessing files in the first place, and enabling rapid recovery even when an attack succeeds.
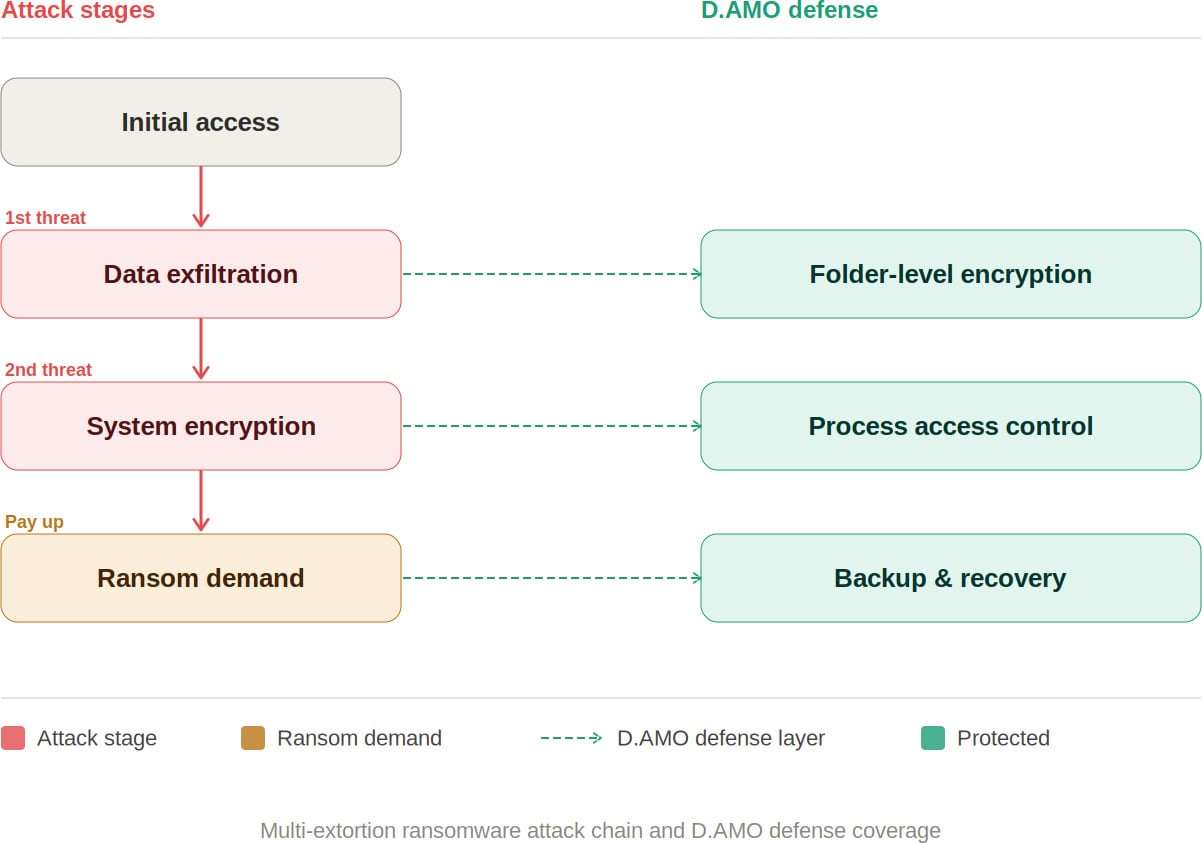
D.AMO: Blocking Every Stage of a Ransomware Attack
D.AMO, developed by Penta Security, is an encryption-based data protection platform designed to address every phase of a multi-extortion ransomware attack. It delivers integrated encryption, access control, and backup recovery across on-premises and cloud environments.
By applying file encryption and process-based access control technologies, D.AMO protects critical data stored on servers and PCs — safeguarding sensitive information against malicious programs through robust access enforcement. D.AMO’s key capabilities are as follows:
Folder-Level File Encryption
D.AMO KE encrypts all files within administrator-designated folders at the OS level. Deployable via an installer without source code modification, it operates using kernel-level encryption technology, enabling fast and secure encryption on existing systems with no disruption to the user experience.
Encryption policies are applied at the folder level, ensuring consistent protection with minimal operational overhead. Critically, even if an attacker exfiltrates sensitive data, the files remain encrypted — neutralizing the data exposure threat that is central to double extortion.
Access Control
D.AMO KE enforces strict access control over processes and OS users, permitting only explicitly authorized access. Ransomware and other malicious applications are automatically blocked from accessing encrypted folders, preventing unauthorized file manipulation.
All blocked activity is recorded through an audit log function and can be reviewed centrally via D.AMO Control Center.
Backup and Recovery
Even in the event of a successful attack, organizations can resume operations through an independently managed recovery system. With D.AMO in place, the ability to restore from backup significantly reduces dependence on decryption key negotiations with threat actors.
As multi-extortion tactics become the norm, neutralizing the data attackers seek to exploit has become a strategic priority. Organizations need the ability to render exfiltrated data unreadable, prevent ransomware from accessing files, and recover rapidly when incidents occur.
D.AMO addresses each stage of a ransomware attack within a single integrated platform — combining encryption, process-based access control, and backup recovery into a unified line of defense.
Want to learn more? Download the D.AMO Data Sheet.
Sponsored and written by Penta Security.
Tech
Samsung’s Color E-Paper Gives Retailers a Simple Way to Refresh Every Sign on the Spot
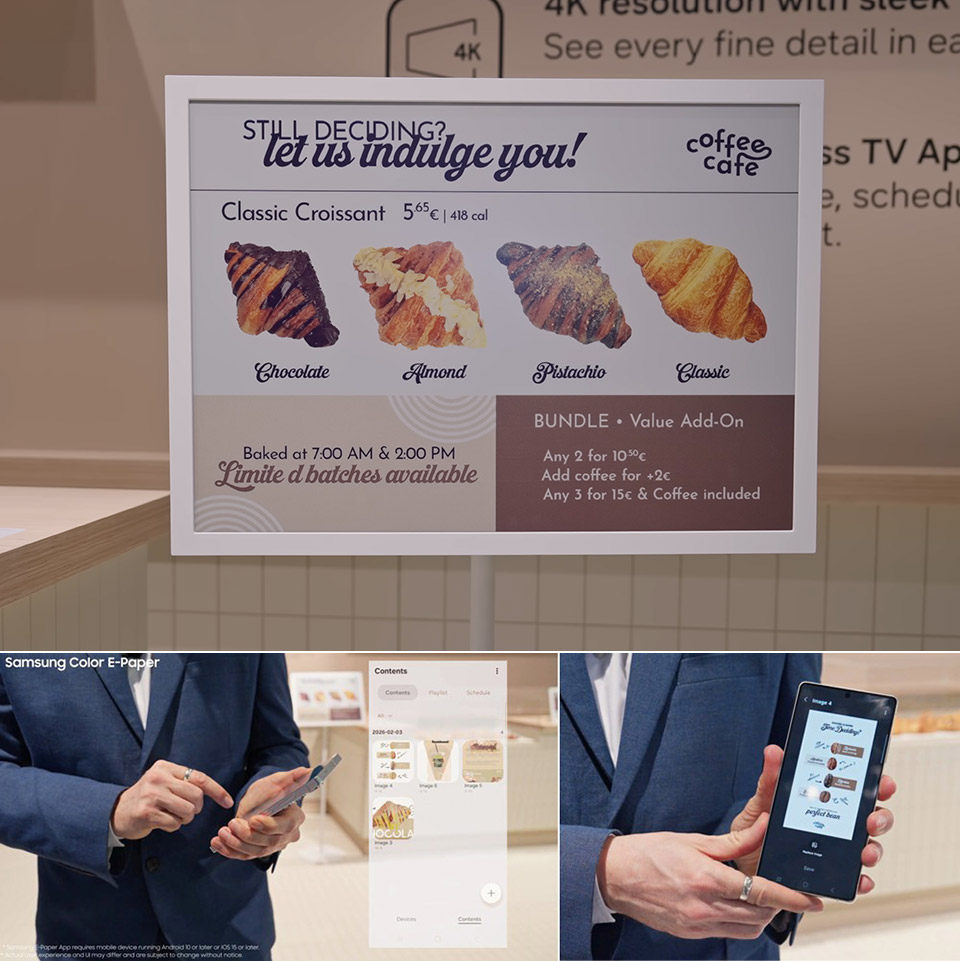
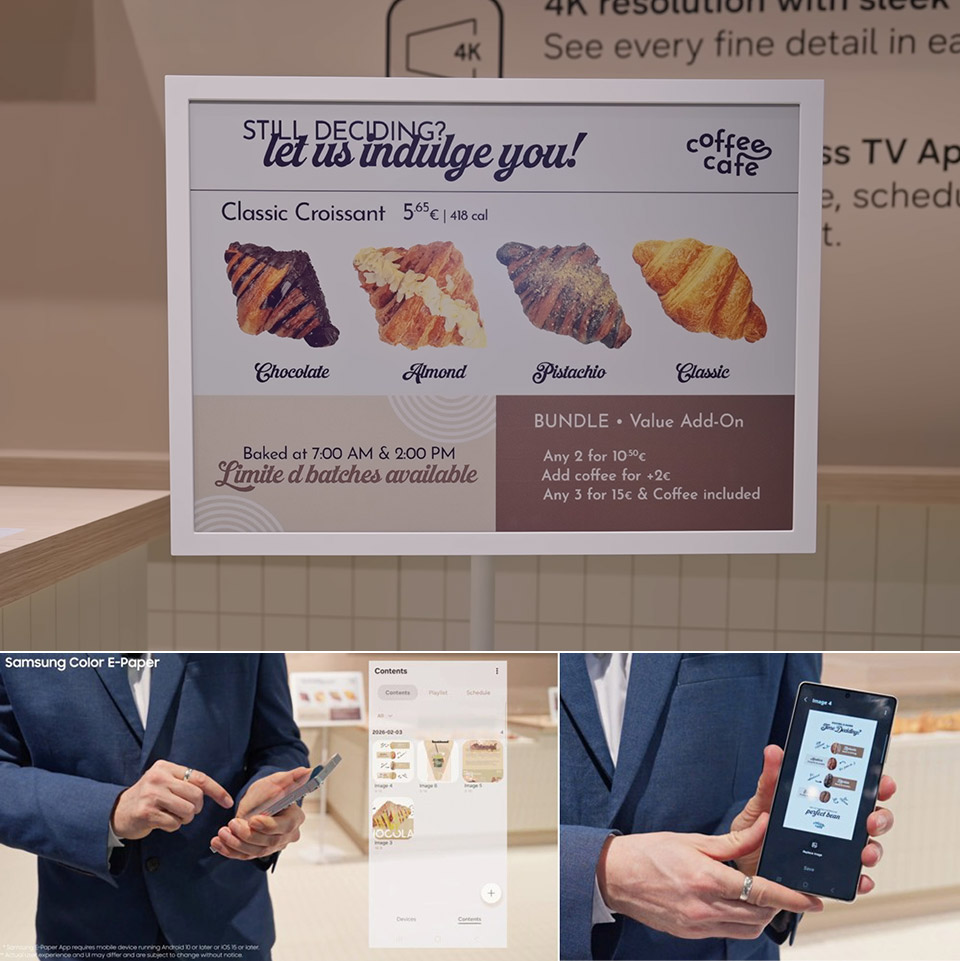
Retail locations have always employed posters and signage to capture the attention of customers, but changing them out on a daily basis is a time-consuming task for workers. Samsung has developed a solution: displays that appear like printed paper but feature digital flexibility. These are known as Color E-Paper and are available in a variety of sizes to meet your needs, including a 13-inch variant that is nearly identical to an A4 sheet, a 20-inch version that matches an A3, and a 32-inch choice if you have a large wall or window to fill.
Each of these display units is extremely thin (under 18mm) and light enough to hang almost anywhere. The 13-inch version may be hung on a door, slid onto a counter, or even fixed to a shelf without the need for additional hardware; simply use the brackets and stands that come with it. Inside each one are millions of very small receptacles, or tiny cups, filled with colored ink particles in red, yellow, white, and blue. Electric signals just nudge the appropriate ones to the top, forming the image or words you wish to view.
Sale
PhotoTag Smart Item Finder, Bluetooth Tracker Tag Works with Apple Find My & Google Find Hub (iOS…
- 【Works with Apple Find My & Google Find Hub】Compatible with both iPhone and Android, track your essentials with confidence. Allowing you to locate…
- 【Customizable Color E-Ink Display – Make It Truly Yours】Unlike ordinary tracker tags, PhotoTag features a customizable color E-Ink screen…
- 【“If Found” Contact Card – Help Lost Items Return】Turn your tracker into a smart return tag. Display your name, phone number, email, or…
Samsung engineers have devised a technique to mix and match those four colors to create a stunning 2.5 million different shades, almost as lovely as the real thing, and much like a real printed page, once the image is up, it consumes no electricity. The only time it requires power is when you change the content, and a full charge on the battery will last for weeks or even months, depending on how frequently you wish to update the data.
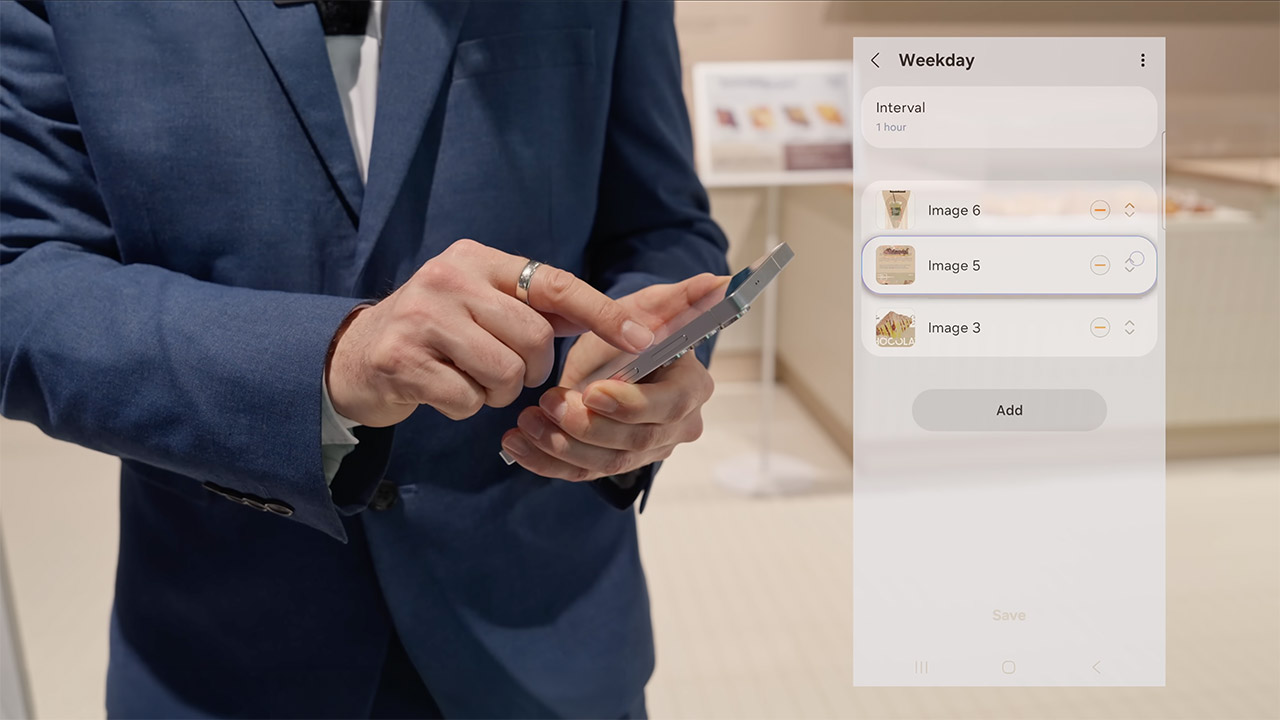
To get the fresh image on the screen, simply utilize the mobile app, which is accessible for most smartphones running the latest Android or iOS versions. Simply launch the app, select a layout, see how the colours will appear, and transmit it to the display. If you’re part of a large chain with multiple stores, Samsung has a cloud platform that can manage everything remotely and link with any other screens you already have in place. Bye bye ladder, heaps of paper to print, and no more waiting for the next delivery truck; it seems like a dream come true.
A handful of the models’ housings blend crushed recycled plastic with a special plant-based glue derived from the microscopic particles that floats on water, and the packaging is entirely made of paper rather than plastic. By selecting these solutions, retailers may reduce their environmental effect without sacrificing durability or the feel of real paper, which draws customers in. Retailers that have begun testing the displays have raved about the outcomes on shelves, café walls, and franchise shop gateways. You can swap out a menu board in a diner to go from breakfast to lunch in two seconds flat, highlight a flash sale in every single clothing store at the exact same time, and do the same thing for class schedules or seasonal notices in community areas without messing around.

Samsung plans to release the 20-inch models in the second half of 2026, but the smaller and larger sizes are now available in a few locations, and the early versions appear to be working properly in real stores as we speak. In the future, you may see updates that allow you to choose from different colors or batteries that last longer. For those tired of the never-ending cycle of printing, laminating, and continuously replacing signs, these displays quietly get the job done one gorgeous, low power panel at a time.
Tech
Apple's iPad is still showing the world how to do tablets, 16 years later

The iPad was mocked at launch, has been threatened by rivals throughout, and yet still remains the best-selling tablet ever made, 16 years after it first shipped to customers on April 3, 2010.

It’s easy to name alternatives to the iPad, you could be here all day listing myriad Android tablets. But it’s impossible to name even one true iPad competitor.
For after all of these years since it launched, and after all of the rival devices that have launched after that moment, there isn’t any one tablet that sells enough on its own to compete with the iPad. Its competition is the mass of cheaper rivals, which is not to be ignored, yet none of them have come close to the success of the iPad.
The closest is surely the Microsoft Surface, but if that’s the best and the best-known rival, it doesn’t appear to be doing all that well.
Continue Reading on AppleInsider | Discuss on our Forums
Tech
Python Blood Could Hold the Secret To Healthy Weight Loss

Longtime Slashdot reader fahrbot-bot writes: CU Boulder researchers are reporting that they have discovered an appetite-suppressing compound in python blood that helps the snakes consume enormous meals and go months without eating yet remain metabolically healthy. The findings were published in the journal Natural Metabolism on March 19, 2026.
Pythons can grow as big as a telephone pole, swallow an antelope whole, and go months or even years without eating — all while maintaining a healthy heart and plenty of muscle mass. In the hours after they eat, research has shown, their heart expands 25% and their metabolism speeds up 4,000-fold to help them digest their meal. The team measured blood samples from ball pythons and Burmese pythons, fed once every 28 days, immediately after they ate a meal. In all, they found 208 metabolites that increased significantly after the pythons ate. One molecule, called para-tyramine-O-sulfate (pTOS) soared 1,000-fold.
Further studies, done with Baylor University researchers, showed that when they gave high doses of pTOS to obese or lean mice, it acted on the hypothalamus, the appetite center of the brain, prompting weight loss without causing gastrointestinal problems, muscle loss or declines in energy. The study found that pTOS, which is produced by the snake’s gut bacteria, is not present in mice naturally. It is present in human urine at low levels and does increase somewhat after a meal. But because most research is done in mice or rats, pTOS has been overlooked. “We’ve basically discovered an appetite suppressant that works in mice without some of the side-effects that GLP-1 drugs have,” said senior author Leslie Leinwand, a distinguished professor of Molecular, Cellular and Developmental Biology who has been studying pythons in her lab for two decades. Drugs like Ozempic and Wegovy act on the hormone glucagon-like petide-1 (GLP-1).
-

 NewsBeat7 days ago
NewsBeat7 days agoThe Story hosts event on Durham’s historic registers
-

 NewsBeat21 hours ago
NewsBeat21 hours agoSteven Gerrard disagrees with Gary Neville over ‘shock’ Chelsea and Arsenal claim | Football
-

 Sports7 days ago
Sports7 days agoSweet Sixteen Game Thread: Tide vs Michigan
-
Entertainment4 days ago
Fans slam 'heartbreaking' Barbie Dream Fest convention debacle with 'cardboard cutout' experience
-

 Business16 hours ago
Business16 hours agoNo Jackpot Winner and $194 Million Prize Rolls Over
-

 Crypto World2 days ago
Crypto World2 days agoGold Price Prediction: Worst Month in 17 Years fo Save Haven Rock
-

 Entertainment6 days ago
Entertainment6 days agoLana Del Rey Celebrates Her Husband’s 51st Birthday In New Post
-

 Tech5 days ago
Tech5 days agoThe Pixel 10a doesn’t have a camera bump, and it’s great
-
Crypto World3 days ago
Dems press CFTC, ethics board on prediction-market insider trades
-

 Sports3 days ago
Sports3 days agoTallest college basketball player ever, standing at 7-foot-9, entering transfer portal
-

 Tech5 days ago
Tech5 days agoAvatar Legends: The Fighting Game comes out in July and it looks pretty slick
-

 Tech3 days ago
Tech3 days agoEE TV is using AI to help you find something to watch
-

 Fashion5 days ago
Fashion5 days agoAmazon Sundays: Soft Spring Layers
-

 Business2 days ago
Business2 days agoLogin and Checkout Issues Spark Merchant Frustration
-

 Fashion7 days ago
Fashion7 days agoWhen Evening Dressing Gets Colorful for Spring
-

 Tech5 days ago
Tech5 days agoElon Musk’s last co-founder reportedly leaves xAI
-

 Tech3 days ago
Tech3 days agoHow to back up your iPhone & iPad to your Mac before something goes wrong
-

 Tech4 days ago
Tech4 days agoApple will hide your email address from apps and websites, but not cops
-

 Crypto World4 days ago
Crypto World4 days agoU.S. rule change may open trillions in 401(k) funds to crypto
-

 Politics4 days ago
Politics4 days agoShould Trump Be Scared Strait?













You must be logged in to post a comment Login