Have you noticed? We are entering a new era of wearables, as the screen-free tracker trend picks up the pace.
Everyone from Fitbit (an official tracker teased by Steph Curry) to Garmin (leaked information on the in-development Garmin Cirqa) has one cooking. These lifestyle wearables won’t pull your attention away with flashing notifications. And they will record your daily stats and exercise sessions while demanding no intervention at all.
Article continues below
Similar concept, different approach. Whoop has matured from an athlete-first wearable to a general lifestyle guide, with a highly-polished app that makes swathes of complex information easy to digest. On the other hand, the Polar Loop is a stylish and stripped-back wearable out to court those looking to get away from constant screen use. Crucially, it’s cheaper than the Whoop with no subscription fee.
And the Amazfit Helio Strap? It is by far the most affordable of the trio, being cheaper again than the Polar Loop. The design isn’t flashy, but it is not short on features. Let’s dig in further.
Price and availability

The Polar Loop and Amazfit Helio Strap are a reaction to the success of Whoop. But they’re based around a totally different kind of business model.
When you buy a Whoop you join one of three memberships, dubbed One ($149 / £169 / AU$249), Peak ($239 / £229 / AU$399) and Life ($359 / £349 / AU$599). That includes either a Whoop 4.0/5.0 or Whoop MG band, and a year’s access to the respective service plan — you pay more, you get more advanced data.
Once the year’s up, you’ll need to fork out for another year, or pay a monthly subscription depending on your desired tier: $25 for Whoop One, $30 for Peak or $40 for Whoop Life (available in “select renewal scenarios” according to Whoop).
There’s none of that nonsense with the Polar and Amazfit options. A Polar Loop costs $199, the Amazfit Helio Strap just $99.99. And there’s no obligation to pay more after that, and you can access all your core stats without a subscription. Bliss.
Of course, this being 2026 there are still premium subscriptions on offer from both Polar and Amazfit. Polar has the €9.99 euro Fitness Program (around $11.50 / £8.50 / AU$16) , but as it provides training plans it’s really a better fit for a hardcore Polar fitness watch than the Polar Loop. Amazfit offers the Zepp Aura Premium subscription, at $11.99 (around £9 / AU$17 a month) or $69.99 (around £55 / AU$100) for the year. Its focus is on sleep and wellness, and provides many soundscapes to help you get some rest. It’s neat, but not really necessary for most Helio Strap owners.
- Winner: Amazfit Helio Strap
Design

Whoop set the standard for screen-less wearable styling in 2015 with its first band, and very little has changed design-wise since then. The Amazfit and Polar wearables take a similar approach. There’s effectively a fitness tracker ‘brain’, sensor array and a Bluetooth chip attached to a fabric strap, sending information to your phone.
Whoop actually claims the Polar design is too close to its own, having sued the company on that very point. Tech brands sue each other at every possible opportunity, though, and these three are clearly not clones of one another.
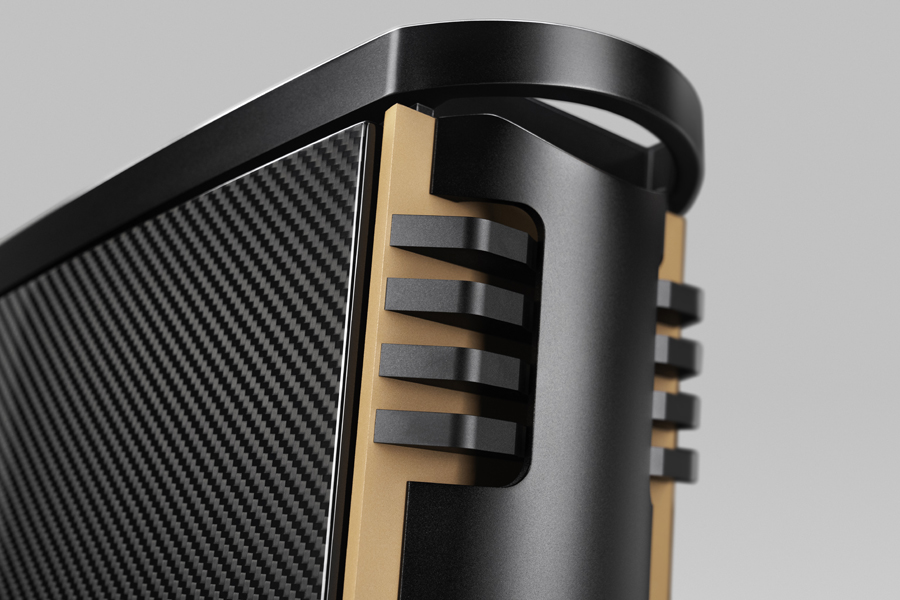
Their designs also give clues as to their three personalities — after a fashion — which bleeds through into their feature list too. The Polar Loop is the least hardcore of the trio, and has the look to match. The mottled fabric finish and metal accents throughout suggest Polar thinks people care about style as well as functionality. It weighs 29g including strap. Not heavy.
Whoop’s Band 5.0 continues the series’s signature style, as pretty much the only recognisable screen-free tracker these days. It too is part-metal with a fabric strap, and weighs 29g.
While it’s the classic screen-free wearable, we are not actually massive fans of one key element, the clasp. Its grip is not all that firm, and has a habit of coming undone by itself which is very annoying. This extends to its more premium sibling the Whoop MG, which we pointed out in our Whoop MG review.
The Amazfit Helio Strap is a little different. Its almost all-plastic design brings weight down to a super-low 20g. This makes it “disappear” on the wrist while wearing it, at least from the wearer’s own perception of additional weight. And while it has the plainest basic design of the three, it’s also available in a Hyrox edition with a luminous highlighter-yellow patch up top.
All three bands have effectively fairly similar water resistance. All are OK for pool swimming, but shouldn’t be used for scuba diving or anything similar. A Whoop 5.0 is rated at IP68, and for submersion at up to 10m depth. Polar rates the Loop at WR30, for “bathing and swimming” but not snorkelling or diving. The Amazfit Helio Strap has a 5ATM rating, which is the norm these days for all but the toughest wearables. It’s a case of three different standards that end up in the same place: you don’t have to take these wearables off to shower, or when at the swimming pool.
Features

The Helio Strap’s sporty design is the best clue as to what the Amazfit wearable is about. It’s positioned as the most fitness–driven of the three bands in the way the companion Zepp app presents data has more of a focus on workouts versus rest and recovery. It uses an Amazfit-created stat called Biocharge, which offsets exertion against sleep and rest quality.
The wearable’s image is that of a tool for busy folks who might realistically be at risk of overtraining if they don’t watch their training load. But it will also do the job as an all-round lighter fitness tracker.
Despite Amazfit’s Zepp Aura Premium being all about wellness and relaxation, there’s less sense of long-term holistic health tracking here. You do get a VO2 Max reading, which is handy for long-term fitness tracking. But the impression the software gives is more of a classic exercise-first fitness tracker, just without the display.
It does have a couple of neat extras not always seen in these screenless wearables, though. The Amazfit Helio Strap has a vibrate motor, for timers, alarms and “find my device” emergencies. It can also live-share its heart rate data with other devices that support the feature, which is useful.
Deeper insight is all part of the Whoop pitch, and part of why it claims to be worth a chunky paid ongoing subscription.
Subscribe to the mid-tier Peak Whoop membership or above and you get stats like your Whoop Age, as well as the Strain score supplied across all three of Whoop’s plans. There’s menstrual cycling tracking too, made possible using a skin temperature sensor.
Or to go all-out, the Life membership adds blood pressure observations and ECG, although this involves using a completely different Whoop MG wearable (it looks similar, admittedly). With that plan you end up paying an awful lot for stats some more conventional wearables do as standard, though, such as the best Garmin watches.
The Polar experience is a bit less focused than that of Whoop or Amazfit. In the Polar Flow app you see “cards” based on your recent activity, and of key stats the band has recorded.
There are zero extras here, though. The Polar Loop won’t share its heart rate readings, and doesn’t have a vibration motor. There’s no skin temperature sensor either, which rules out features like menstrual cycle tracking.
Performance

The Polar Loop, Amazfit Helio Strap and Whoop 5.0 may come across as part of a newly-popular category, but their sensor hardware is just like that of other wearables. All the stats rely on an optical heart rate sensor (which uses LEDs to estimate heart rate from information taken from your wrist) , motion sensors to determine movement and estimate step count, and for the WHOOP Band 5.0, a skin temperature sensor.
I compared the results of these screen-less trackers with one of the better Garmin watches out there, the Garmin Venu 4, which uses Garmin’s latest Elevate V5 heart rate sensor. We’ve tested this against top-of-the-range watches including the Apple Watch Ultra 3, as well as a Polar H10 chest strap, to determine accuracy, and have no qualms about the validity of the Garmin’s readings.
The results for heart rate tracking were commendably similar between the Garmin and the three other wearables we’re testing against. When peak heart rate results for automatically-tracked with the Amazfit Helio Strap and Polar Loop were typically within 2bpm of those of the Garmin Venu 4. And with early 2026 firmware, there were no obvious classic optical heart rate issues such as the first few minutes of a workout having entirely inaccurate readings, which often happens when the wearable struggles to tell the difference between your heart rate and run cadence.
Even in a static bike class (which can be tricky for bands), the Garmin, Amazfit and Polar wearables all recorded the same 167bpm maximum heart rate score. It’s a reassuring result.
When you use these screen-less wearables, though, it becomes pretty clear we’re not meant to obsess over heart rate date in too much fine detail. After all, for the most part it’s going to be down to the software when any specific activity ends, which will impact average heart rate stats across a session.
What about Whoop? We’ve had a bit more of a mixed experience with the Whoop bands, and the top-tier Whoop MG in particular had a few issues.
We find Whoop competitive with its peers for general heart rate accuracy during workouts and excellent for recovery tracking, but we did have a few issues with its ECG readings. Namely, it would often fail to register a recording. And unlike a watch with a screen, you don’t get that immediate feedback as to why this is the case
The core appeal for Whoop fans is the Strain score, though, and that doesn’t rely on ECG but the basics of the HR tracking. This is where Whoop wins, on generating cogent and actionable advice in the app that feels useful, right down to its in-app workout builder.
It tries fairly hard to insinuate its way into your life, though. You’ll be nagged to go to bed at the right time, and to put the band back on if you take it off, through phone notifications. Is that what you want? Our original reviewer wasn’t quite so sure.
Amazfit’s Zepp app is solid, but ultimately feels a bit more like standard fitness tracker fare than Whoop, leaning on Biocharge, Sleep and Exertion stats alongside familiar numbers including steps, VO2 max and your exertion load. It has a very sporty flavour, which may appeal to some.
Polar we had some more issues with. The Flow app feels less intuitive than either the Amazfit or Whoop apps, bombarding you with graphs rather than a slick interface full of helpful context. And over the months of testing we’ve had a few different issues.
Initially, pairing and sync’ing were intermittently clunky and/or problematic. More recently we’ve experienced issues with the Android app crashing completely when you try to look into a specific exercise session entry. There have been a few too many issues and irritations for what is one of the longest-standing names in fitness wearables.
And battery life? Here things are a bit more consistent. Whoop says the Band 5.0 can last up to 14 days, and with fairly intense use we got around nine days from it. Polar claims eight days for the Loop, and we got a week out of a charge. Amazfit was bang on the money with its 10-day claim too.
While Whoop was the furthest from its battery life claims, it’s also important to remember you can have more of an interactive participation with a Whoop (at its higher tiers) thank to the ECG support, which is a manual process. Whoop also allows you to charge it without taking it off your wrist via the charging puck.
Verdict

Is the screen-free life for you? Polar, Whoop and Amazfit can all provide their own take on the trend. And all deliver a largely fuss-free experience, with automatic activity logging and long battery life.
There are some other points to note, though. We’re not persuaded Whoop’s highest tier is necessarily worth it for many. It’s just a lot to pay, an an ongoing subscription, particularly when we had a few issues with collecting readings.
Polar’s key issue is in the software, which doesn’t have the slickness or information coherence of the other two — at least as of March 2026.
That leaves us with the Amazfit Helio Strap, the cheapest of the bunch, and perhaps the easiest to recommend if you want to try out the screen-free wearables life. No subscription, solid HR accuracy and an app that while a bit fitness and athlete-focused for some, doesn’t demand too much from you.
Follow TechRadar on Google News and add us as a preferred source to get our expert news, reviews, and opinion in your feeds. Make sure to click the Follow button!
And of course, you can also follow TechRadar on YouTube and TikTok for news, reviews, unboxings in video form, and get regular updates from us on WhatsApp too


































































You must be logged in to post a comment Login