- Nvidia CEO Jensen Huang predicts AI will make us “feel superhuman”
- Says he is “getting busier and busier” due to increased AI usage
- Huang also warns of “scaring” people about AI, says we need to be “a little bit more humble”
Jensen Huang has once again outlined his belief that harnessing the power of AI will help make humanity more effective, productive, and efficient.
Speaking at a Q&A session for media at Nvidia GTC 2026, the CEO and co-founder spoke on what AI can do for us, as well as his own personal experiences utilizing AI at work.
Huang revealed that he finds himself “getting busier and busier”, as AI processes speed up workflows across his business – but that he is positive about the long-term future for both the technology, and Nvidia as a whole.
Article continues below
Busier and faster
Asked about how his company is using AI in day-to-day work, Huang was unsurprisingly effusive in his praise for the technology – despite the burden it is putting on his inbox.
“Nvidia is moving faster than ever, but that’s because we use more and more AI and so work gets done faster, all of the projects are moving faster,” he said.
“I feel like I’m getting busier and busier to be honest…my experience with Nvidia today is that it’s making me busier than it was six months ago – and the reason for that is because results work is coming back to you much faster, work is coming back to you much faster, and the number of projects are growing much faster”
“I think this is the experience for everybody – a lot of people are saying AI is coming, we’re going to run out of jobs – but it’s exactly the opposite. The fact of the matter is PCs made us more busy, the internet made us more busy, mobile devices made us super busy…AI is going to get tasks done super fast…my sense is that AI is going to cause us to be able to do things so fast we’re going to end up doing more.”
“When was the last time you sat on a porch and drank lemonade? Are you kidding me? I don’t remember the last time except when I saw it in a movie about 100 years ago…so we’re busier than ever.”
AI safety
Given the incredible and often unchecked growth of AI, Huang was also asked about what we shouldn’t want the technology to do.
“AI shouldn’t break the law…or promise functionality it shouldn’t have,” he answered.
“For example, if a car says it could drive safely at 65 miles per hour, we’d like it not to blow out at 50 – these are very sensible things that humanity has learned over time.”
“I think we have to continuously learn and be a little bit more humble about what we know and don’t know – scaring everybody about a science fiction version of AI is a little bit too arrangement, too much of a risk for my taste – I prefer to learn my way into life, instead of scaring everybody else…warning people is one thing, scaring people is a completely different thing…I think human judgement would tell us there’s a difference between warning and scaring”
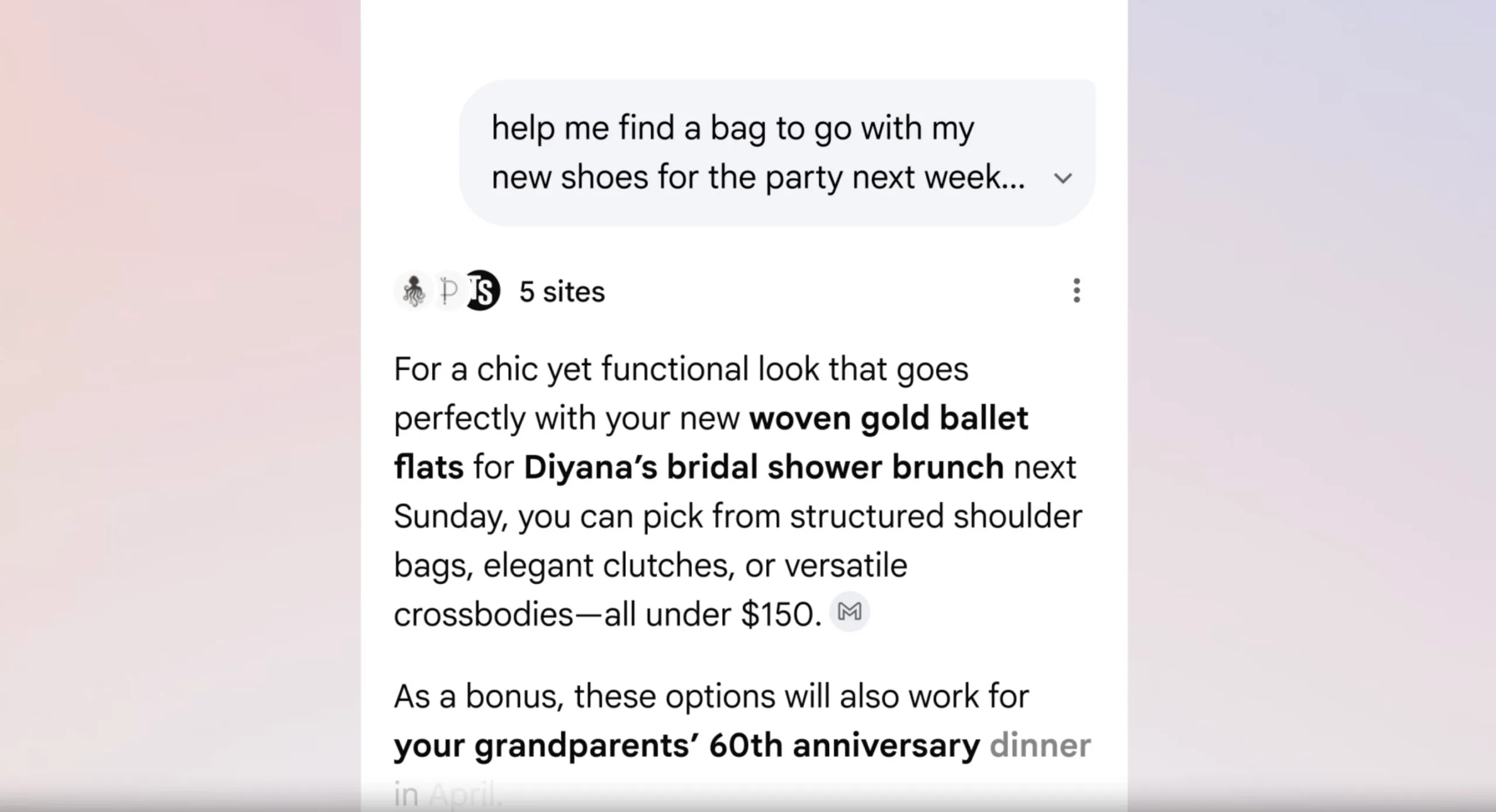
“We need AI to do a lot of great things for us…we need AI agentic systems to be in cybersecurity – week one, our companies need to be surrounded by white blood cells, just in case there’s an intruder, our cyber security agents could respond instantly and swarm the intrusion, just like white blood cells.”
Looking ahead
Finishing off, Huang was asked where he sees Nvidia in 10 years, a big question for any CEO.
“We’re going to be super busy – we will have hopefully have 75,000 employees, as small as possible, as big as necessary, (who will be) working with 7.5 million agents, working around the clock so hopefully our people don’t have to to keep up with them”
“We’re going to solve some really important problems – the things that we are thinking about today to solve – 10 years ago, nobody would even imagine that it would be solvable.”
“The impossible is actually quite practical – anything that takes millions of x factors of energy or cost, or time, you can shrink by billions of times – and so distances will be shorter, everything will be wired because of robotics…and the amount of energy we use for anything will be reduced tremendously…and we will all feel superhuman.”
Follow TechRadar on Google News and add us as a preferred source to get our expert news, reviews, and opinion in your feeds. Make sure to click the Follow button!
And of course you can also follow TechRadar on TikTok for news, reviews, unboxings in video form, and get regular updates from us on WhatsApp too.






























































You must be logged in to post a comment Login