Tech
Backed by Nvidia, Seattle’s Phaidra targets data center overheating with proactive AI


Phaidra, a startup using artificial intelligence to make data center operations more energy efficient, this week announced key collaborations with Nvidia, CoreWeave and Applied Digital.
The Seattle company revealed “groundbreaking methodology” that predicts and prevents data center heat spikes when computing workloads surge. Phaidra has been partnering with cloud provider CoreWeave and data center operator Applied Digital to test and deploy the cooling strategy.
As data center operations and deployments boom nationwide, demand for energy and water to run the facilities and cool the electronics is likewise surging. Operators are eager to find better strategies for building and operating such complex sites.
Phaidra is led by alumni from Alphabet’s AI research hub DeepMind, launched in 2019. Its technology uses an array of sensors to measure multiple metrics and analyzes that information. The company has raised a total of $120 million and has roughly 90 employees.
The startup is #78 on GeekWire 200, our list of the top privately held technology companies in Seattle and the Pacific Northwest.
“We envisaged a future where AI agents transform static infrastructure in self-learning, continuously improving infrastructure,” Phaidra CEO Jim Gao said on LinkedIn.
“That future became reality on the world stage,” Gao added, when Nvidia CEO Jensen Huang this week announced the collaboration between Phaidra, the global chip giant, and others.
Data centers typically hum at steady operating conditions, but demand can suddenly ramp up when AI training or other large workloads are dispatched. That cranks up the heat produced, which can cause chips to throttle performance to avoid overheating. To prevent this, data center operators often over-cool facilities, wasting power, water and limiting available compute capacity.
Phaidra’s fix is to use an AI agent that monitors power data as an early-warning signal of an impending operations spike so cooling can kick in proactively — rather than waiting for a temperature rise.
Tech
OpenAI Backs Bill That Would Limit Liability for AI-Enabled Mass Deaths or Financial Disasters
OpenAI is throwing its support behind an Illinois state bill that would shield AI labs from liability in cases where AI models are used to cause serious societal harms, such as death or serious injury of 100 or more people or at least $1 billion in property damage.
The effort seems to mark a shift in OpenAI’s legislative strategy. Until now, OpenAI has largely played defense, opposing bills that could have made AI labs liable for their technology’s harms. Several AI policy experts tell WIRED that SB 3444—which could set a new standard for the industry—is a more extreme measure than bills OpenAI has supported in the past.
The bill would shield frontier AI developers from liability for “critical harms” caused by their frontier models as long as they did not intentionally or recklessly cause such an incident, and have published safety, security, and transparency reports on their website. It defines a frontier model as any AI model trained using more than $100 million in computational costs, which likely could apply to America’s largest AI labs, like OpenAI, Google, xAI, Anthropic, and Meta.
“We support approaches like this because they focus on what matters most: Reducing the risk of serious harm from the most advanced AI systems while still allowing this technology to get into the hands of the people and businesses—small and big—of Illinois,” said OpenAI spokesperson Jamie Radice in an emailed statement. “They also help avoid a patchwork of state-by-state rules and move toward clearer, more consistent national standards.”
Under its definition of critical harms, the bill lists a few common areas of concern for the AI industry, such as a bad actor using AI to create a chemical, biological, radiological, or nuclear weapon. If an AI model engages in conduct on its own that, if committed by a human, would constitute a criminal offense and leads to those extreme outcomes, that would also be a critical harm. If an AI model were to commit any of these actions under SB 3444, the AI lab behind the model may not be held liable, so long as it wasn’t intentional and they published their reports.
Federal and state legislatures in the US have yet to pass any laws specifically determining whether AI model developers, like OpenAI, could be liable for these types of harm caused by their technology. But as AI labs continue to release more powerful AI models that raise novel safety and cybersecurity challenges, such as Anthropic’s Claude Mythos, these questions feel increasingly prescient.
In her testimony supporting SB 3444, a member of OpenAI’s Global Affairs team, Caitlin Niedermeyer, also argued in favor of a federal framework for AI regulation. Niedermeyer struck a message that’s consistent with the Trump administration’s crackdown on state AI safety laws, claiming it’s important to avoid “a patchwork of inconsistent state requirements that could create friction without meaningfully improving safety.” This is also consistent with the broader view of Silicon Valley in recent years, which has generally argued that it’s paramount for AI legislation to not hamper America’s position in the global AI race. While SB 3444 is itself a state-level safety law, Niedermeyer argued that those can be effective if they “reinforce a path toward harmonization with federal systems.”
“At OpenAI, we believe the North Star for frontier regulation should be the safe deployment of the most advanced models in a way that also preserves US leadership in innovation,” Niedermeyer said.
Scott Wisor, policy director for the Secure AI project, tells WIRED he believes this bill has a slim chance of passing, given Illinois’ reputation for aggressively regulating technology. “We polled people in Illinois, asking whether they think AI companies should be exempt from liability, and 90 percent of people oppose it. There’s no reason existing AI companies should be facing reduced liability,” Wisor says.
Tech
‘Negative’ Views of Broadcom Driving Thousands of VMware Migrations, Rival Says

“One of VMware’s biggest competitors, Nutanix, claims to have swiped tens of thousands of VMware customers,” reports Ars Technica. They said higher prices, forced bundling, licensing changes, and more strained partner relationships have frustrated customers and driven them away from the leading virtualization firm. From the report: Speaking at a press briefing at Nutanix’s .NEXT conference in Chicago this week, Nutanix CEO Rajiv Ramaswami said that “about 30,000 customers” have migrated from VMware to the rival platform, pointing to customer disapproval over Broadcom’s VMware strategy, SDxCentral, a London-based IT publication, reported today. “I think there’s no doubt that the customer sentiment continues to be negative about Broadcom,” Ramaswami said, per SDxCentral.
Nutanix hasn’t specified how many of the customers that it got from VMware are SMBs or enterprise-sized; although, adoption is said to be strongest among mid-market customers as Nutanix also tries wooing larger customers, often by starting with partial deployments. During this week’s press briefing, Ramaswami reportedly said that some of the customers that moved from VMware to Nutanix during the latter’s most recent fiscal quarter represented Nutanix’s “strongest quarterly new logo additions in eight years.” “Most of the logos came from our typical VMware migrations on to the [hyperconverged infrastructure] platform,” he said.
During the Nutanix conference, Brandon Shaw, Nutanix VP and head of technology services, said that Western Union has been migrating from VMware to Nutanix for six months, The Register reported. The financial services company is moving 900 to 1,200 applications across 3,900 cores. Shaw said that Western Union has been exploring new IT suppliers to help it become more customer-focused. Despite Broadcom’s history of “decent lines of communication” with Western Union, Shaw said that Western Union had “challenges partnering with them.”
Shaw also pointed to Broadcom’s efforts to push customers to buy the VMware Cloud Foundation (VCF), despite the product often having more features than companies need and at high prices. Since moving to Nutanix, the Denver-headquartered financial firm is also benefiting from having more flexibility around workload locations, which is important since Western Union is in over 200 countries, The Register said.
Tech
New VENOM phishing attacks steal senior executives’ Microsoft logins


Threat actors using a previously undocumented phishing-as-a-service (PhaaS) platform called “VENOM” are targeting credentials of C-suite executives across multiple industries.
The operation has been active since at least last November and appears to target specific individuals who serve as CEOs, CFOs, or VPs at their companies.
VENOM also seems to be closed access, as it has not been promoted on public channels and underground forums, thus reducing its exposure to researchers.
The VENOM attack chain
The phishing emails, observed by researchers at cybersecurity company Abnormal, impersonated Microsoft SharePoint document-sharing notifications as part of internal communication.
The messages are highly personalized and include random HTML noise such as fake CSS classes and comments. The attacker also injects fake email threads tailored to the target, increasing credibility.
A QR code rendered in Unicode is provided for the victim to scan for access. The trick is designed to bypass scanning tools and shift the attack to mobile devices.
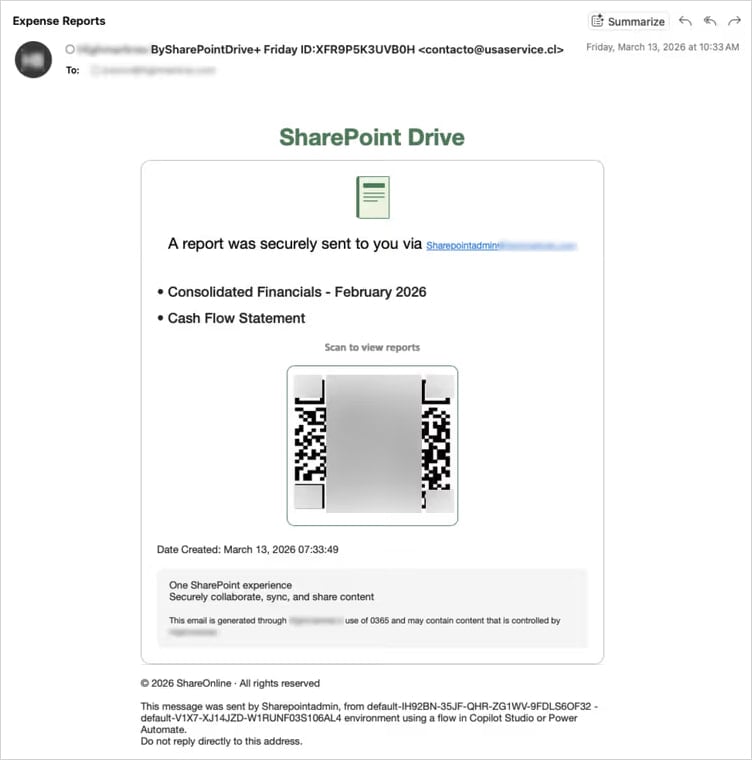
Source: Abnormal
“The target’s email address is double Base64-encoded in the URL fragment—the portion after the # character,” Abnormal researchers explain.
“Fragments are never transmitted in HTTP requests, making the target’s email invisible to server-side logs and URL reputation feeds.”
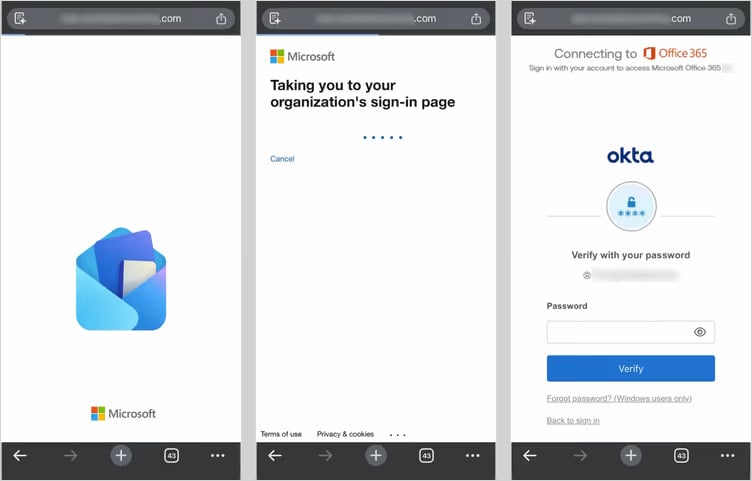
When the victim scans the QR code, they are taken to a landing page that serves as a filter for security researchers and sandboxed environments, ensuring that only real targets are redirected to the phishing platform. Users outside the threat actor’s interest are redirected to legitimate websites to reduce suspicion.
Those who pass the tests are taken to a credential-harvesting page that proxies a Microsoft login flow in real time, relaying credentials and multi-factor authentication (MFA) codes to Microsoft APIs and capturing the session token.
Source: Abnormal
Apart from the adversary-in-the-middle (AiTM) method, Abnormal has also observed a device-code phishing tactic in which the victim is tricked into approving access to their Microsoft account for a rogue device.
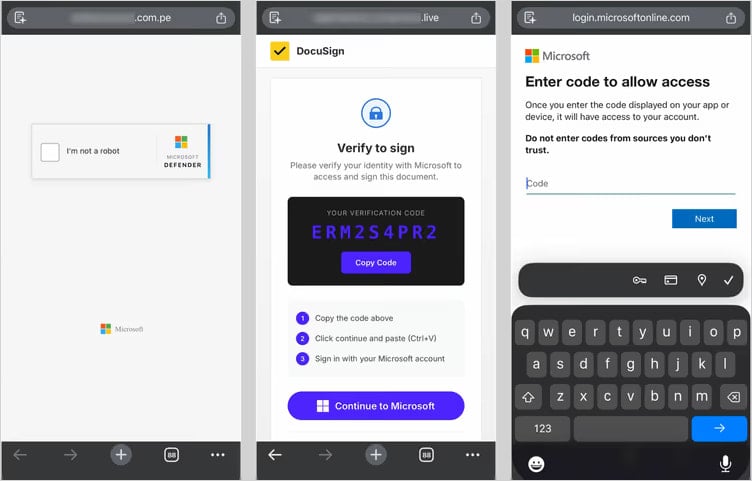
Source: Abnormal
This method has become very popular over the past year due to its effectiveness and resistance to password resets, with at least 11 phishing kits currently offering it as an option.
In both methods, VENOM quickly establishes persistent access during the authentication process. In the AiTM flow, it registers a new device on the victim’s account. In the device code flow, it obtains a token that also provides access to the account.
The researchers note that MFA is no longer sufficient as a defense. C-suite executives should use FIDO2 authentication, disable the device code flow when not needed, and block token abuse by implementing stricter conditional access policies.
Tech
Remembering Devoted IEEE Volunteer Gus Gaynor
Gerard “Gus” Gaynor, a long-serving IEEE volunteer and former engineering director at 3M, died on 9 March. The IEEE Life Fellow was 104.
Readers of The Institute might remember Gus from his 2022 profile: “From Fixing Farm Equipment to Becoming a Director at 3M.” Just last year, he and I coauthored twoarticles. One discusses how to leverage relationships to boost your career growth. The other weighs the pros and cons of pursuing a technical or managerial career path. He was 103 years old then. How many IEEE members can claim a centenarian coauthor?
I first met Gus in 2009 at the IEEE Technical Activities Board (TAB) meeting in San Juan, Puerto Rico. We sat together in the airplane on our way back to Minneapolis, our hometown. At home I told many of my friends about the remarkable person—who was 87 years young at the time—with whom I chatted during our six-hour flight.
A decade later, he and I met for lunch in Minneapolis. He drove himself to the restaurant, just asking for a hand to navigate the snowy sidewalk.
A dedicated IEEE volunteer
Gus’s involvement with IEEE predates the organization. He joined the Institute of Radio Engineers, a predecessor society, as a student member in 1942. Twenty years later he became an active IEEE volunteer.
He served on the TAB’s finance committee and the Publications Services and Products Board. He was president of the IEEE Engineering Management Society (now the Technology and Engineering Management Society ), and he was the Technology Management Council’s first president. He was the founding editor of IEEE-USA’s online magazine Today’s Engineer, which reported on government legislation and issues affecting U.S. members’ careers. The magazine is now available as the e-newsletter IEEE-USA InSight.
He authored several books on technology management, published by IEEE-USA.
 IEEE Life Fellow Gerard “Gus” Gaynor died on 9 March.The Gaynor Family
IEEE Life Fellow Gerard “Gus” Gaynor died on 9 March.The Gaynor Family
Most recently, after the formation of TEMS in 2015, he became an active member of its executive committee. He served two terms as vice president of publications.
At 100 years old, he led the launch of a new publication, TEMS Leadership Briefs, a novel short-format open-access publication aimed at technology leaders.
Gus, who is a former member of The Institute’s editorial advisory board, also worked with Kathy Pretz, The Institute’s editor in chief, to start an ongoing series of TEMS-sponsored career-interest articles. He coauthored several of them.
Throughout his 64 years as an IEEE volunteer, he received several honors. They include IEEE EMS’s Engineering Manager of the Year Award, the IEEE TEMS Career Achievement Award, and the IEEE-USA McClure Citation of Honor. In 2014 he was inducted into the IEEE Technical Activities Board Hall of Honor.
A 25-year career at 3M
Gus received a degree in electrical engineering in 1950 from the University of Michigan in Ann Arbor. He worked for several companies including Automatic Electric (now part of Nokia) and Johnson Farebox (now part of Genfare), before joining 3M in 1962.
During his successful 25-year career at 3M, he served as chief engineer for a division in Italy, established the innovation department, and led the design and installation of the company’s first computerized manufacturing facilities. He retired as director of engineering in 1987.
Last year, IEEE Life Fellow Michael Condry, a former TEMS president, organized a Zoom call with Gus and other leaders of the society to celebrate Gus’s 104th birthday. Gus looked well and was his usual upbeat self, telling everyone: “I’m good. Everything’s well. I can’t complain.”
Gus was married to Shirley Margaret Karrels Gaynor, who passed away in 2018. He lives on in the hearts and minds of his seven children, seven grandchildren, two great-grandchildren, and innumerable friends and IEEE colleagues.
From Your Site Articles
Related Articles Around the Web
Tech
Iran-linked hackers are now targeting industrial controllers in US infrastructure
Federal agencies, including the FBI, CISA, NSA, the Department of Energy, US Cyber Command, and the Environmental Protection Agency, issued an urgent joint advisory Tuesday, warning that an advanced persistent threat group linked to Iran has been exploiting vulnerabilities in programmable logic controllers since at least March 2026.
Read Entire Article
Source link
Tech
New ‘LucidRook’ malware used in targeted attacks on NGOs, universities


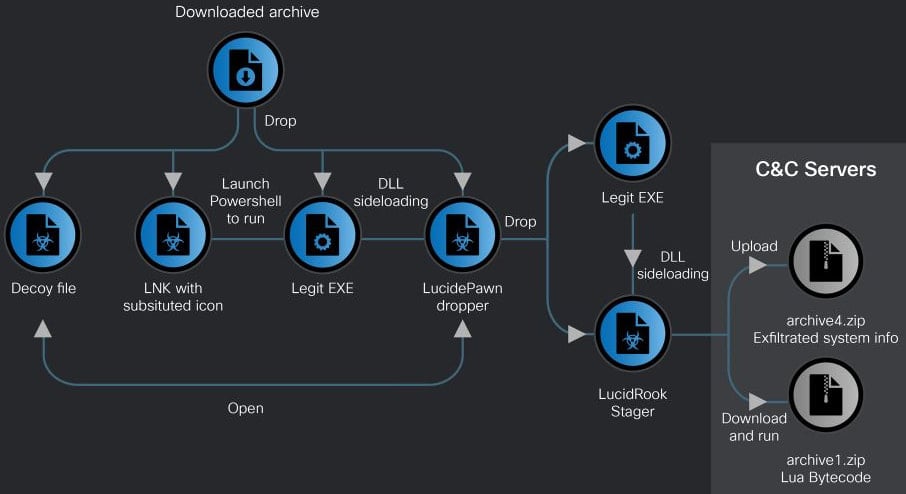
A new Lua-based malware, called LucidRook, is being used in spear-phishing campaigns targeting non-governmental organizations and universities in Taiwan.
Cisco Talos researchers attribute the malware to a threat group tracked internally as UAT-10362, who they describe as a capable adversary “with mature operational tradecraft.”
LucidRook was observed in attacks in October 2025 that relied on phishing emails carrying password-protected archives.
The researchers identified two infection chains, one using an LNK shortcut file that ultimately delivered a malware dropper called LucidPawn, and an EXE-based chain that leveraged a fake antivirus executable impersonating Trend Micro Worry-Free Business Security Services.
The LNK-based attack employs decoy documents, such as government letters crafted to appear as if they originate from the Taiwanese government, to divert the user’s attention.
Source: Cisco Talos
Cisco Talos observed that LucidPawn decrypts and deploys a legitimate executable renamed to mimic Microsoft Edge, along with a malicious DLL (DismCore.dll) for sideloading LucidRook.
LucidRook is notable for its modular design and built-in Lua execution environment, which allows it to retrieve and execute second-stage payloads as Lua bytecode.
This approach enables operators to update functionality without modifying the core malware, while also limiting forensic visibility. This stealth is further increased by extensive obfuscation of the code.
“Embedding the Lua interpreter effectively turns the native DLL into a stable execution platform while allowing the threat actor to update or tailor behavior for each target or campaigns by updating the Lua bytecode payload with a lighter and more flexible development process,” Cisco Talos explains.
“This approach also improves operational security, since the Lua stage can be hosted only briefly and removed from C2 after delivery, and it can hinder post-incident reconstruction when defenders recover only the loader without the externally delivered Lua payload.”
Talos also notes that the binary is heavily obfuscated across embedded strings, file extensions, internal identifiers, and C2 addresses, complicating any reverse-engineering efforts.
During its execution, LucidRook performs system reconnaissance, collecting information such as user and computer names, installed applications, and running processes.
The data is encrypted using RSA, stored in password-protected archives, and exfiltrated to attacker-controlled infrastructure via FTP.
While examining LucidRook, Talos researchers identified a related tool named “LucidKnight,” which is likely used for reconnaissance.
One notable characteristic of LucidKnight is its abuse of Gmail GMTP to exfiltrate collected data, suggesting that UAT-10362 maintains a flexible toolkit to meet varying operational needs.
Cisco Talos concludes with medium confidence that the LucidRook attacks are part of a targeted intrusion campaign. However, they were unable to capture a decryptable Lua bytecode fetched by LucidRook, so the specific actions taken post-infection aren’t known.
Tech
Fuel Prices Are Skyrocketing, But Most Of The Money Isn’t Going To Gas Stations

Gas prices have skyrocketed across the United States in 2026, with prices the highest they’ve been since 2022. As of early April, the average price for a gallon is $4, a rise primarily fueled by the Iran war. As a result, gas prices have changed daily — and sometimes multiple times a day — and drivers are starting to seethe while at the pump. But gas stations haven’t actually benefited from these ballooning gas prices.
According to Patrick De Haan, Head of Petroleum Analysis at GasBuddy, gas stations don’t make more money when prices rise — in fact, it’s the opposite. Speaking to AP News, De Haan said that “The margins shrink when prices go up because it’s harder for [gas stations] to pass along the increases as quickly as they themselves get them.” The profits, then, are going to the companies that extract and refine crude oil, not the retailers you buy your gas from.
Why do gas stations all have different prices if they don’t benefit?
If gas stations aren’t profiting from the increased gas prices, why do gas stations have different prices? There are actually a lot of factors that go into setting the price of a gallon, largely based on location and taxes.
The biggest factor is geography. For one, gas prices can change from state to state due to taxes. For example, California’s gas taxes and fees totaled about 71 cents per gallon last year — for the gas stations to make a profit, they have to raise the prices to offset these taxes. On the other side of the coin, some states have (or are close to) oil refineries, which makes for shorter delivery distances and lower prices.
Prices can also vary within states. The brand, as well as the volume of gas sold, will factor into the pricing. Some gas stations may be in very convenient locations off the highway, allowing them to get away with higher prices. And if there are two gas stations near one another, one may lower its prices, hoping to draw customers away from its rival. Thus, if you want to save some money as gas continues to rise, use a gas-finding app to locate the gas station with the lowest prices wherever you are.
Tech
Street Smarts: Waymo and Waze Turn Driver Data Into Pothole Repairs

Hitting potholes while driving is never fun. They can cause headaches, car accidents and damage to your vehicle, culminating in a frustrating commute. Waymo, the robotaxi company, and Waze, the free, community-driven GPS navigation app, have come together to do something about potholes.
On Thursday, the two companies announced a joint venture to target potholes that need patching. The new data-sharing pilot program will collect information on troublesome road conditions and communicate the necessary fixes to the city.
Waymo operates in 11 cities, and the pilot program will begin in five major markets: Austin, Texas; Atlanta; Los Angeles; Phoenix and the San Francisco Bay Area, with plans to expand to more cities in the future. So far, Waymo says it has tracked 500 potholes in the Bay Area alone.
“As Waymo’s autonomous fleet travels across San Jose, we appreciate the collaboration with Waymo and Waze as we explore how technology can help identify issues like potholes faster so we can respond more efficiently,” San Jose Mayor Matt Mahan said in an emailed statement.
Departments of Transportation for each city and state will be able to access this pothole information through the Waze for Cities app. Waymo stated in its blog post that the initial idea for this program was inspired by city officials who expressed the need for a better way to ensure safe road conditions.
Most cities still learn about road issues from residents — through either dialing 311 or using the my311 app — or via manual road inspections. This method has resulted in inadequate fixes and an incomplete understanding of a neighborhood’s road health and the resources needed to maintain it.
Waymo’s robotaxis use autonomous driving technology, including an array of high-end cameras, lidar, radar and other tracking sensors, making them the perfect platform for collecting road data.
Waze customers in cities where Waymo operates will also be able to view this data directly in the app, which is noteworthy given that Waze operates on a user-based reporting system to identify troublesome road conditions. You can already receive pothole data and locations in the app, but adding Waymo’s tracking data will help verify the data and improve the app’s accuracy.
“For years, drivers on Waze have helped each other by reporting potholes for a smoother, safer ride,” Andrew Stober, Waze strategic partner manager, said in the blog post. “This pilot program with Waymo adds another source of data to that effort, giving cities a clearer picture of road conditions through our Waze for Cities platform.”
A Waymo representative didn’t immediately respond to a request for further comment.
Tech
Apple has released macOS 26.4.1 with unspecified bug fixes

On April 9, Apple released macOS 26.4.1 to the public, alongside vague release notes that just discuss that the update contains bug fixes.

The new macOS 26.4.1 update is now available for download
While Apple hasn’t detailed exactly which bugs this new update addresses, there may be clues from other recent releases. The update comes just 24 hours after Apple also released iOS 26.4.1 and iPadOS 26.4.1.
Both updates applied a fix for one bug in particular. That bug caused some iCloud data not to sync correctly and affected both Apple and third-party apps, including Passwords.
Continue Reading on AppleInsider | Discuss on our Forums
Tech
A version of Windows 10 released a decade ago is now eligible for additional security patches


Did Microsoft really retire Windows 10 in October 2025? The company is now offering additional options to further extend the lifespan of an operating system first released in 2015. Redmond’s updated plans include several more years of security patches for Windows 10 Enterprise LTSB 2016 through the same Extended Security…
Read Entire Article
Source link
-

 Fashion6 days ago
Fashion6 days agoWeekend Open Thread: Spanx – Corporette.com
-

 Business4 days ago
Business4 days agoThree Gulf funds agree to back Paramount’s $81 billion takeover of Warner, WSJ reports
-

 Sports5 days ago
Sports5 days agoIndia men’s 4x400m and mixed 4x100m relay teams register big progress | Other Sports News
-

 Business6 days ago
Business6 days agoExpert Picks for Every Need
-

 Tech2 days ago
Tech2 days agoHow Long Can You Drive With Expired Registration? What Florida Law Says
-

 Business5 days ago
Business5 days agoNo Jackpot Winner, Prize to Climb to $231 Million
-

 Fashion4 days ago
Fashion4 days agoMassimo Dutti Offers Inspiration for Your Summer Mood Board
-

 Fashion2 days ago
Fashion2 days agoLet’s Discuss: DEI in 2026
-
Politics7 days ago
Wings Over Scotland | The quality of mercy
-

 Crypto World1 day ago
Crypto World1 day agoBitcoin recovers as US and Iran Agree a Ceasefire Deal
-

 Business5 days ago
Business5 days agoAkebia Therapeutics, Inc. (AKBA) Discusses Pipeline Progress and Strategic Focus on Kidney Disease Treatments at R&D Day – Slideshow
-

 Politics7 days ago
Politics7 days agoEast Jerusalem Palestinian families eviction orders
-

 Politics7 days ago
Politics7 days agoWhy so many children are now classified as ‘disabled’
-

 Crypto World13 hours ago
Crypto World13 hours agoCanary Capital Files SEC Registration for PEPE ETF
-

 Politics6 days ago
Politics6 days agoThe UK should not pay a penny in slavery reparations
-

 Politics7 days ago
Politics7 days agoNuclear rockets, moon bases and NASA’s Mars plan
-

 Tech7 days ago
Tech7 days agoThe Threadless Ball Screw Never Took Off, But Don’t Write It Off
-
 Business7 days ago
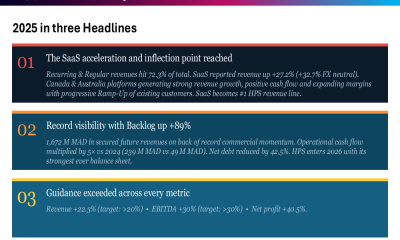
Business7 days agoHPS FY 2025 slides: SaaS inflection drives 22% revenue growth
-

 Fashion7 days ago
Fashion7 days agoTory Burch’s Spring 2026 Campaign Goes on a Getaway
-

 Fashion7 days ago
Fashion7 days agoFrugal Friday’s Workwear Report: Hammered Metallic Button Sweater Vest















You must be logged in to post a comment Login