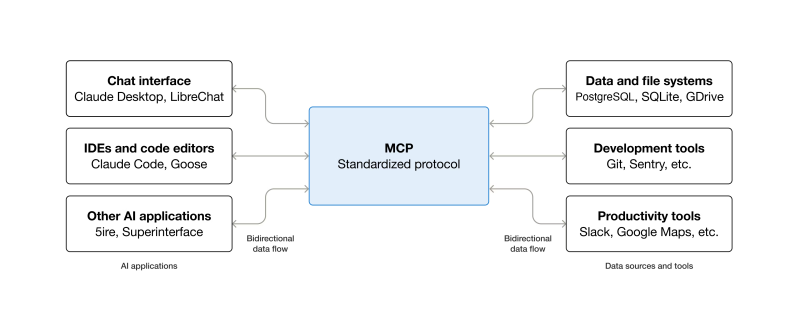
As part of the effort to push Large Language Model (LLM) ‘AI’ into more and more places, Anthropic’s Model Context Protocol (MCP) has been adopted as the standard to connect LLMs with various external tools and systems in a client-server model. A light oversight with the architecture of this protocol is that remote command execution (RCE) of arbitrary commands is effectively an essential part of its design, as covered in a recent article by [OX Security].
The details of this flaw are found in a detailed breakdown article, which applies to all implementations regardless of the programming language. Essentially the StdioServerParameters that are passed to the remote server to create a new local instance on said server can contain any command and arguments, which are executed in a server-side shell.
Essentially the issue is a lack of input sanitization, which is only the most common source of exploited CVEs. Across multiple real-world exploitation attempts on the software of LettaAI, LangFlow, Flowise and Windsurf it was possible to perform RCEs or perform local RCE in the case of the Windsurf IDE. Although Flowise had implemented some input sanitization by limiting allowed commands and the stripping of special characters, this was bypassed by using standard flags of the npx command.
After contacting Anthropic to inform them of these issues with MCP, the researchers were told that there was no design flaw and essentially had a ‘no-fix, works as designed’ hurled at them. According to Anthropic it’s the responsibility of the developer to perform input sanitization, which is interesting since they provide a range of implementations.
You must be logged in to post a comment Login