If you opened TikTok recently, you probably saw some weird stuff happening. Maybe you couldn’t post a new video. Maybe the app asked for your precise location. Maybe you weren’t seeing as much stuff about ICE or the Trump administration’s latest assault on the global world order. If the latter is the case, you weren’t the only one.
Tech
Is Trump’s new TikTok censoring users?

When it comes to TikTok, the past week has been full of changes, challenges, and conspiracy theories. It was the first week of operations for the new company that’s running TikTok in the United States: the TikTok USDS Joint Venture LLC, a name that really rolls off the tongue. I like to call it TikTok USA so that it doesn’t sound so much like a military operation, but some are simply referring to the new company as TikTok’s MAGA makeover.
There are some reasons to suspect this. Many of the new company’s investors, including Oracle and Abu Dhabi-based investment firm MGX, have close ties to the Trump administration. President Donald Trump has even taken credit for “saving TikTok” by brokering the deal that avoided the app from being banned in the US over national security concerns. And in the past few days, users reported odd activity that seems very much in line with Trump’s agenda: direct messages mentioning Epstein won’t send, videos critical of ICE won’t upload, anti-Trump TikToks are getting suppressed. Oracle spokesperson Michael Egbert said on Tuesday that “a temporary weather-related power outage” impacted TikTok and led to “technical issues.”
What’s probably more significant than an outage and related glitches, however, is how the TikTok USA experience will be different from the classic TikTok experience. Even before the censorship complaints began, the company rolled out an updated privacy policy that collects even more data on its users. That includes their precise location, details of users’ AI interactions, and personal information that it will share with a broader ad network. There is also language in the new privacy policy that TikTok USA could collect data about “immigration status,” but that language was actually in the old privacy policy in order to comply with some state laws.
Then there’s the question of the algorithm. TikTok is what it is because its powerful algorithm consistently delights and surprises hundreds of millions of users with content that’s either uncannily specific or just plain compelling. When the Trump administration announced the terms of the deal to spin off TikTok USA last year, there were a lot of questions about who would own the algorithm for the American app and who would control it. The same goes for content moderation as well as trust and safety policies.
We now know that TikTok USA will control all of these levers. ByteDance, which retains a 19.9 percent stake in TikTok USA, will license the content recommendation algorithm to the new American company, which will host the algorithm as well as all US user data on Oracle servers. Oracle, MGX, and the private equity firm Silver Lake represent the new company’s three managing investors, and they each get a seat on the board. Other investors include firms linked to everyone from Michael Dell to former AOL chair Steve Case to early Facebook investor Yuri Milner. Adam Presser, TikTok’s former head of operations and trust and safety, is the new company’s CEO. Presser was also previously chief of staff to TikTok CEO Shou Chew, who is also on the board of TikTok USA.
We don’t yet know what the leadership of this new company will do. It’s not at all clear that this group of men running the company — yes, the board is all men — is actually a cabal of pro-Trump operatives eager to turn the platform into MAGA’s new mouthpiece.
Some have stronger Trump ties than others. Kenneth Glueck, an Oracle lobbyist and one of Larry Ellison’s lieutenants, played a key role in finalizing the Trump-backed deal and served on the transition team for Trump’s first administration after donating money to it. Jeff Yass, founder of Susquehanna International Group, which owns 15 percent of ByteDance, is possibly the guy who talked Trump into getting a TikTok deal a couple years ago, but he’s not on the board. Susquehanna managing director Mark Dooley is. Silver Lake co-CEO Egon Durban also helped broker the TikTok deal, and he worked closely with Jared Kushner, Trump’s son-in-law, to get Saudi Arabia’s Public Investment Fund in on a deal to acquire Electronic Arts. (Saudi crown prince Mohammed bin Salman is apparently a big gamer.)
Does knowing all of this make you want to delete your TikTok account? Apparently a lot of people already are. Daily uninstalls grew by 130 percent in the first four days of TikTok USA’s ownership compared to the previous 30 days. Smaller social media platforms would be happy to have you. UpScrolled, an app that’s been billing itself as a TikTok alternative, is currently second only to ChatGPT in Apple’s App Store.
It’s unclear if the “glitches” from earlier this week will persist or if the algorithm will suddenly start serving more MAGA-adjacent content, pushing more crypto schemes, or just show you more AI slop. This kind of thing has happened before when social media platforms changed hands.
What seems like the most obvious explanation for what’s happening at TikTok USA is that the formerly China-owned platform is becoming an American one. The updates to its privacy policy more or less mirror what companies like Meta and Google have been doing to their American users for years: collecting as much data and making as much money as possible. TikTok USA’s board has some probably pro-Trump guys on it, but Silicon Valley is full of them these days. Look no further than billionaire’s row at Trump’s second inauguration for evidence that the tech industry cares most about access to power.
If all this bothers you, delete the app. Heck, even if it doesn’t bother you, consider spending your attention elsewhere. TikTok was never very good for you.
A version of this story was also published in the User Friendly newsletter. Sign up here so you don’t miss the next one!
Tech
iCloud email goes down for some users in an Easter Sunday outage
Apple users encountered issues accessing iCloud, in what was a rare Sunday outage for the company’s email, cloud storage, and associated services.
Apple service outage icons
Users of iCloud, Apple’s online services, ware reporting issues in being able to access files. Sites including DownDetector and StatusGator showed a sudden surge of reports from thousands of users, encountering problems since 10 A.M. Eastern.
The reported issues, for the most part, raised iCloud as being the problem. The range of issues was wide, including claims of iCloud Mail being unavailable, Find My devices disappearing in the app, and an inability to access files stored on the service.
Continue Reading on AppleInsider | Discuss on our Forums
Tech
LinkedIn secretly scans 6,000+ browser extensions and fingerprints your device
In short: Every time you visit LinkedIn in a Chrome-based browser, a hidden JavaScript routine silently probes your browser for more than 6,000 installed extensions, collects 48 hardware and software characteristics about your device, encrypts the resulting fingerprint, and attaches it to every API request you make during your session. The practice, labelled “BrowserGate” by researchers, is not disclosed in LinkedIn’s privacy policy. LinkedIn says it is a security measure; critics say it is covert surveillance of a billion users’ browsing behaviour at industrial scale.
There is a routine that runs on your computer every time you open LinkedIn. You cannot see it, you were not told about it, and it is not described in the company’s privacy policy. According to an investigation published in early April 2026 by Fairlinked e.V., a European association of commercial LinkedIn users, the platform injects a 2.7-megabyte JavaScript bundle into its website that silently scans visitors’ browsers for the presence of more than 6,000 specific Chrome extensions, assembles a detailed fingerprint of their hardware, encrypts it, and transmits the result to LinkedIn’s servers, where it is attached to every subsequent action taken during the session.
The investigation, independently confirmed by BleepingComputer, which verified the scanning behaviour through its own testing, has been dubbed “BrowserGate.” LinkedIn disputes many of the report’s characterisations. The technical facts are not in dispute.
What the script does
LinkedIn calls its scanning system “Spectroscopy.” When a user loads the LinkedIn website, the script fires off up to 6,222 simultaneous requests, each one probing for a specific browser extension by attempting to access files associated with that extension’s ID. The presence or absence of a file in the response indicates whether the extension is installed. The entire operation runs silently in the background, without a visible prompt or notification of any kind.
Beyond extensions, the script collects 48 distinct characteristics of the user’s device: CPU core count, available memory, screen resolution, timezone, language settings, battery status, audio hardware information, and storage capacity, among others. Individually, these attributes are unremarkable. Combined, they form a device fingerprint specific enough to identify a user even after cookies are cleared.
Once compiled, the data is serialised to JSON and encrypted using an RSA public key, LinkedIn’s internal identifier for the key is “apfcDfPK”, before being transmitted to telemetry endpoints including li/track and /platform-telemetry/li/apfcDf. The fingerprint is then permanently injected as an HTTP header into every API request made during the session, meaning LinkedIn receives it with every search, every profile view, every message sent.
What it is looking for
The question of which extensions LinkedIn is scanning for makes the surveillance more sensitive than simple fraud detection would require. According to the BrowserGate report, LinkedIn’s list includes more than 200 products that compete directly with its own sales tools, among them Apollo, Lusha, and ZoomInfo. Because LinkedIn knows the employer of each registered user, systematically scanning for the presence of a competitor’s tool gives the platform visibility into which companies are evaluating or deploying rival products.
The list also reportedly includes tools associated with neurodivergent conditions, religious practice, political interests, and job-hunting activity, categories that, in the European Union, qualify as sensitive personal data subject to heightened protection under the General Data Protection Regulation. Knowing that a user is running a job-search extension, for instance, is a meaningful inference about their employment intentions, drawn without consent.
The scale of the operation has grown substantially over time. LinkedIn began scanning for 38 specific extensions in 2017. By 2024, that number had grown to 461. By February 2026, the list had reached 6,167, a 1,252% increase in two years. BleepingComputer’s testing confirmed the scanning was active as of early April 2026.
LinkedIn’s defence and the source of the report
LinkedIn’s response to BleepingComputer was pointed. “The claims made on the website linked here are plain wrong,” a spokesperson said. “The person behind them is subject to an account restriction for scraping and other violations of LinkedIn’s Terms of Service. To protect the privacy of our members, their data, and to ensure site stability, we do look for extensions that scrape data without members’ consent or otherwise violate LinkedIn’s Terms of Service.” The company added that it does not use the data to “infer sensitive information about members.”
The platform’s characterisation of the source matters. Fairlinked e.V. is connected to Teamfluence Signal Systems OÜ, an Estonian company whose managing directors include Steven Morell and Jan Liebling. Teamfluence makes a Chrome extension, also called Teamfluence, that LinkedIn restricted for alleged terms of service violations. The company subsequently filed a preliminary injunction against LinkedIn Ireland Unlimited Company and LinkedIn Germany GmbH at the Regional Court of Munich, alleging violations of the Digital Markets Act, EU competition law, and German data protection rules. In January 2026, the Munich court denied the injunction, finding that LinkedIn’s actions did not constitute unlawful obstruction or discrimination.
The financial dispute between the parties does not change the technical findings, which were verified independently. It does mean the framing of those findings is contested, and readers should weigh both the substance of the claim and its provenance.
The regulatory backdrop
This is not LinkedIn’s first serious encounter with European data protection enforcement. In October 2024, the Irish Data Protection Commission, which regulates LinkedIn in the EU through its Irish subsidiary, fined the company €310 million, approximately $334 million , for processing users’ personal data for targeted advertising without a valid legal basis. The decision found that LinkedIn’s consent mechanisms did not meet GDPR’s requirement that consent be “freely given.” LinkedIn was ordered to bring its data processing into compliance.
The BrowserGate investigation drops into that context. The legal question of whether scanning for 6,000 browser extensions constitutes processing of special-category personal data, and whether users’ lack of awareness of the practice renders any implied consent invalid, is exactly the kind of question the Irish Data Protection Commission has already shown it is willing to adjoin in court. Europe’s evolving digital regulation framework has been moving steadily toward requiring explicit disclosure of all significant data collection, and a scanning operation of this scale, conducted without any mention in a privacy policy, appears difficult to square with that direction of travel.
LinkedIn is a Microsoft subsidiary, acquired in 2016 for $26.2 billion. Microsoft has been aggressively expanding its AI capabilities in 2026, with LinkedIn’s vast dataset of professional identity and employment history forming a significant part of the data infrastructure on which those capabilities rest. The relationship between LinkedIn’s data collection practices and Microsoft’s broader AI ambitions is not addressed in LinkedIn’s privacy policy either.
What this means for users
LinkedIn has more than one billion registered users. The majority access the platform through Chrome-based browsers, meaning the Spectroscopy scan runs routinely on the devices of a significant fraction of the global professional workforce, collecting a fingerprint that is precise enough to persist across cookie resets and potentially across devices.
Short of using a non-Chromium browser such as Firefox, which would limit but not necessarily eliminate LinkedIn’s fingerprinting capabilities, there is no user-facing setting that prevents the scanning. The platform does not offer an opt-out, because it does not disclose the practice in the first place. The 2026 push for governed and transparent AI and data practices is built on precisely the premise that invisible data collection of this kind should not be the default.
Whether regulators move quickly enough to change that default at LinkedIn’s scale remains to be seen. Security firms increasingly built to detect exactly this kind of covert data harvesting are becoming a growth sector in their own right, a market indicator that the gap between what platforms collect and what users understand is still very wide. The year 2025 normalised AI-powered data collection at a pace that regulation has yet to match. BrowserGate is a case study in what that lag looks like from the inside of a browser.
Tech
Vibe coding drove an 84% jump in App Store submissions. Apple is cracking down.


In short: AI-powered “vibe coding” tools have driven an 84% jump in new app submissions to Apple’s App Store in a single quarter, according to reporting by The Information, the largest surge in a decade. The flood is straining Apple’s review infrastructure, with approval times ballooning from 24 hours to as many as 30 days. Apple has responded by pulling apps that violate its self-containment rules, triggering a standoff with the platforms fuelling the boom.
Apple’s App Store is receiving more new apps than at any point in the past ten years. The cause is not a wave of professional developers: it is a term that Collins English Dictionary named its word of the year for 2025, coined by Andrej Karpathy, a co-founder of OpenAI and former AI lead at Tesla, in a single social media post in February of that year. Vibe coding ,the practice of building software by describing what you want in plain language and letting a large language model write the code, has lowered the barrier to app development so dramatically that it is now overwhelming the infrastructure Apple built to gatekeep its platform.
According to reporting by The Information, the number of new apps submitted to the App Store rose 84% in a single quarter as vibe coding went mainstream. The figure corroborates broader data from Sensor Tower, which tracked a 56% year-on-year spike in iOS app launches in December 2025 and a 54.8% rise in January 2026, the highest growth rates in four years. Apple’s full-year 2025 total reached 557,000 new app submissions, the largest annual wave since 2016.
The tools behind the flood
The surge is attributable to a small cluster of platforms that have turned natural language into deployable software. Cursor, made by Anysphere and used by seven million developers, surpassed $2 billion in annualised revenue in March 2026 and was valued at $29.3 billion after a $2.3 billion funding round co-led by Accel and Coatue in November 2025. Lovable, which targets non-technical builders, reached $200 million in annualised revenue in late 2025, a fiftyfold increase in a single year, and raised $330 million in a Series B at a $6.6 billion valuation in December 2025. Replit generated $240 million in revenue during 2025, serves more than 150,000 paying customers, and is targeting $1 billion in revenue for 2026. Bolt.new has become a popular entry point for rapid idea-to-prototype work.
The commercial argument for these platforms is straightforward: anyone with an idea and an internet connection can now build and submit an app. The problem for Apple is that the same dynamic that makes vibe coding commercially compelling is structurally incompatible with how the App Store review process works.
Why Apple has a structural problem
Vibe coding’s power lies in generating and executing new code on demand, in response to user prompts, in real time, without a fixed codebase. Apple’s App Store review process was designed for a different model: a developer submits a static build, Apple reviews it, and the approved build is what users receive. Guideline 2.5.2 of Apple’s App Review Guidelines states explicitly that apps “may not download, install, or execute code which introduces or changes features or functionality of the app.” Vibe coding apps, almost by definition, do exactly that.
The volume consequences are already visible in Apple’s infrastructure. Developers submitting to the App Store in March 2026 reported review delays of seven to 30 or more days, against a historical baseline of 24 to 48 hours, with the majority of delay time spent in the “Waiting for Review” queue before a reviewer picks up the submission. The flood of AI-generated apps is straining a system designed for a world in which building an app took months, not minutes.
The crackdown begins
Apple’s enforcement response has been progressive and, at times, opaque. In mid-March 2026, reports emerged that Apple had quietly blocked updates for a set of vibe coding apps, including Replit and Vibecode, without public explanation. Developers described receiving rejections citing Guideline 2.5.2 but receiving no advance warning that enforcement was intensifying.
The most prominent casualty was Anything, an app that let users build small tools and automations through natural language prompts. Its co-founder, Dhruv Amin, said Apple had been preventing updates since December 2025 before pulling the app entirely on 30 March 2026. Amin attempted to reach a compromise by modifying the app so that vibe-coded outputs would be previewed in a web browser rather than executed inside the app itself; Apple blocked that update and removed the app regardless.
An Apple spokesperson told The Information that the company was not targeting vibe coding as a category but rather enforcing guidelines that prevent apps from changing their behaviour after review. The distinction, in practice, is narrow: the defining capability of a vibe coding app is its ability to generate and run new functionality on demand, which is precisely what Guideline 2.5.2 prohibits.
The counterargument
Critics of Apple’s position have been pointed. A CNBC column published at the end of March 2026 argued that Apple’s crackdown “puts it on the wrong side of history,” contending that the review-based model was conceived for a world that no longer exists and that blocking vibe coding apps disadvantages the platform against Android, which applies fewer constraints on dynamic code execution.
The deeper tension is one of gatekeeping economics. Apple’s App Store review process is not only a safety mechanism: it is the basis of the 15–30% commission the company collects on in-app purchases and subscriptions. A wave of vibe-coded apps that bypass review , by generating code outside the approved bundle, is also, in structural terms, a challenge to the business logic of the store itself. Regulators in Europe have been scrutinising Apple’s App Store gatekeeping under the Digital Markets Act, and the vibe coding dispute adds another dimension to that ongoing examination.
A platform reckoning
What vibe coding has exposed is a mismatch between the speed at which AI can generate software and the speed at which existing review infrastructure can evaluate it. Apple reviewed roughly 200,000 weekly app submissions at the height of its 2025 volume, and the surge has outpaced that capacity. The platform now faces a choice between expanding its review capacity significantly, updating its guidelines to accommodate dynamic code execution in controlled ways, or continuing to enforce existing rules and accepting the friction that creates with a rapidly growing class of developers.
The capital being deployed into AI infrastructure in 2026 makes it unlikely that the volume of vibe-coded apps will slow on its own. The tools are becoming faster and cheaper; the category is producing some of the highest-growth companies in the technology industry. As AI moves from novelty to commercial infrastructure, the question of who controls the distribution layer, and on what terms, is becoming the central battleground of the platform era. Apple built the App Store as an answer to that question. Vibe coding is making it ask the question again from the beginning. The AI acceleration of 2025 has arrived at the gate. Apple is deciding whether to open it.
Tech
Snap acquires assets from Rec Room as social gaming platform announces shutdown


Snap Inc. confirmed late Monday that it has acquired select assets from Rec Room Inc., following the news that the Seattle-based company plans to shut down its longtime social gaming platform.
Some of Rec Room’s employees will be joining Snap — but this does not appear to signal that Rec Room will be resurrected at Snap, at least not in its current form. Specifically, the Rec Room employees will work at Specs Inc., the Snap hardware subsidiary, to support its Specs eyewear and augmented reality initiatives, the California-based company said in response to an inquiry from GeekWire.
Snap, the parent company of Snapchat, has maintained a Seattle engineering center since 2015. The company did not disclose deal terms, pricing, or other details of the asset sale.
It’s not clear how many Rec Room employees will be hired as part of the transition.
The move comes in advance of the expected launch later this year of Specs, Snap’s next-generation glasses. Snap has been betting on high-tech glasses for years, and in January established Specs Inc. as a wholly owned subsidiary to focus on its Spectacles/Specs hardware business.
Snap said it was impressed with the Rec Room team’s expertise in building social, multiplayer XR experiences, the industry term for virtual reality, augmented reality, and mixed reality technologies.
Reached via phone, Nick Fajt, the Rec Room co-founder and CEO, said he was “very proud of the team,” thankful to the Rec Room community, and excited for what’s next.
Rec Room surprised the community earlier Monday with the news that it would shut down its platform on June 1, saying it had never found a way to make the business sustainably profitable despite reaching more than 150 million players since it was founded a decade ago.
“Our costs always ended up overwhelming the revenue we brought in,” it said, noting that recent changes in the VR market and broader challenges in gaming contributed to its decision.
Rec Room raised $294 million across six rounds of funding and was valued at $3.5 billion in 2021, making it part of a select group of Seattle-area startups to reach unicorn status.
PREVIOUSLY: Rec Room shutting down: Once valued at $3.5B, social gaming platform finds profits elusive
Tech
Today’s NYT Strands Hints, Answer and Help for April 6 #764
Looking for the most recent Strands answer? Click here for our daily Strands hints, as well as our daily answers and hints for The New York Times Mini Crossword, Wordle, Connections and Connections: Sports Edition puzzles.
Today’s NYT Strands puzzle features some complicated words. Some of the answers are difficult to unscramble, so if you need hints and answers, read on.
I go into depth about the rules for Strands in this story.
If you’re looking for today’s Wordle, Connections and Mini Crossword answers, you can visit CNET’s NYT puzzle hints page.
Read more: NYT Connections Turns 1: These Are the 5 Toughest Puzzles So Far
Hint for today’s Strands puzzle
Today’s Strands theme is: Fringe group
If that doesn’t help you, here’s a clue: Almost on the outside.
Clue words to unlock in-game hints
Your goal is to find hidden words that fit the puzzle’s theme. If you’re stuck, find any words you can. Every time you find three words of four letters or more, Strands will reveal one of the theme words. These are the words I used to get those hints but any words of four or more letters that you find will work:
- DARK, RAGE, MORE, NEST, DINE, DINES, DINER, DINERS
Answers for today’s Strands puzzle
These are the answers that tie into the theme. The goal of the puzzle is to find them all, including the spangram, a theme word that reaches from one side of the puzzle to the other. When you have all of them (I originally thought there were always eight but learned that the number can vary), every letter on the board will be used. Here are the nonspangram answers:
- EDGE, BRINK, BOUNDARY, VERGE, MARGIN, EXTREMITY
Today’s Strands spangram
The completed NYT Strands puzzle for April 6, 2026.
Today’s Strands spangram is OUTERLIMITS. To find it, look for the O that is six letters down on the far-left row, and wind down, over, and up.
Tech
Traffic violation scams switch to QR codes in new phishing texts


Scammers are sending fake “Notice of Default” traffic violation text messages impersonating state courts across the U.S., pressuring recipients to scan a QR code that leads to a phishing site demanding a $6.99 payment while stealing personal and financial information.
This is a new variation of the widely sent toll violation and unpaid parking ticket scams that users received in 2025, which claimed to be from state toll agencies.
This new campaign started a few weeks ago, with someone sharing a text targeting New York residents with BleepingComputer, and many other people reporting similar texts online for other states, including California, North Carolina, Illinois, Virginia, Texas, Connecticut, and New Jersey.
Unlike the previous campaign, which included a text message and links to phishing sites, this new variation instead includes an image of an alleged court notice with an embedded QR code.
“This notice constitutes a final and urgent warning regarding an outstanding traffic violation involving your registered vehicle within the State of New York,” reads the fake court notice.
“This matter has now entered the formal enforcement stage.”
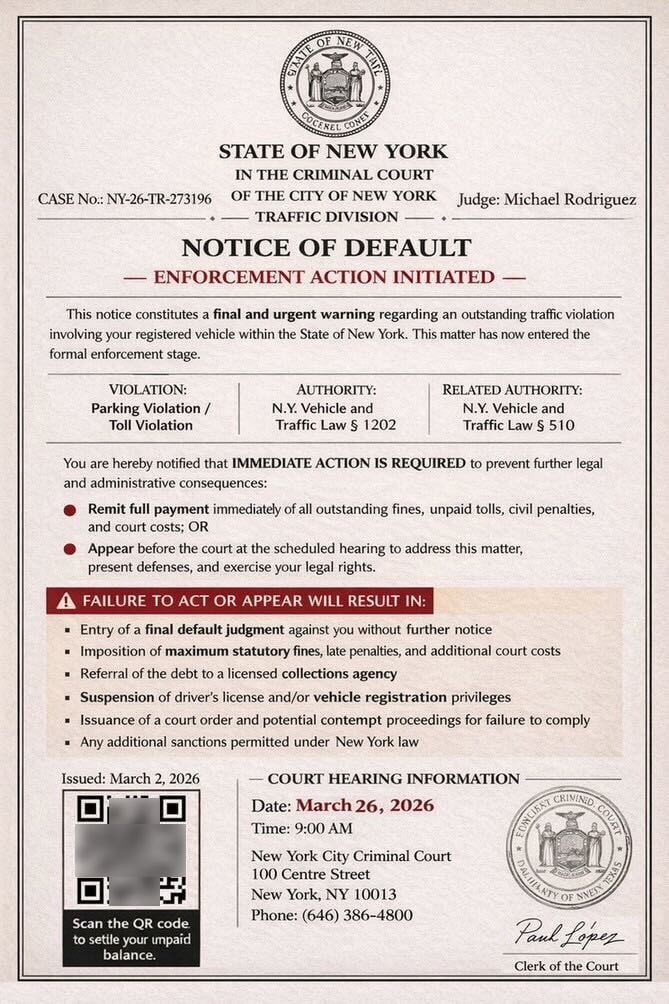
Source: BleepingComputer
The text message shared with BleepingComputer claims to be from the “Criminal Court of the City of New York”, stating that there is an unpaid parking or toll violation that must be paid immediately or the person must appear in court. Included are instructions to scan a QR code to settle the unpaid balances.
Scanning the QR code brings the targeted person to an intermediary site that first prompts you to solve a captcha to prove you are human. The QR codes and CAPTCHA are used to make it harder for automated security software and researchers to analyze the phishing campaign.
Solving the CAPTCHA redirects you to another phishing site that impersonates the state’s DMV or another agency, claiming there is an unpaid toll or parking ticket. In all examples seen by BleepingComputer, this outstanding balance is $6.99.
For example, phishing sites that impersonate the New York DMV use the hostname “ny.gov-skd[.]org” or “ny.ofkhv[.]life”.
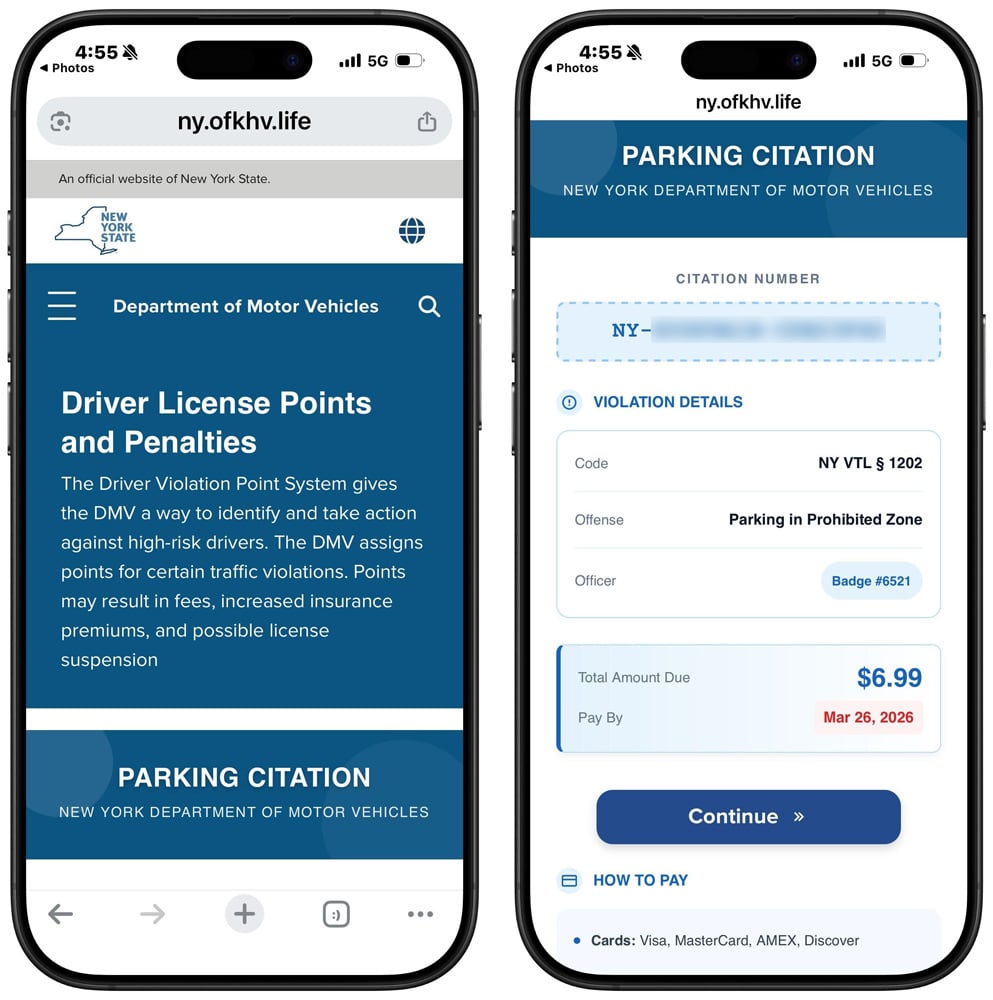
Source: BleepingComputer
Clicking continue will take you to a page where you can enter your personal and credit card information to pay the alleged charge.
This form is used to steal your data, including your name, address, phone number, email address, and, eventually, your credit card information.
This information can then be used for a wide variety of malicious activities, including follow-on phishing attacks, financial fraud, identity theft, and the sale of your data to other threat actors.
As a general rule, if you receive a text from an unknown phone number or email address requesting payment of a bill, ignore it.
State agencies have repeatedly stated in response to these scams that they do not use text messages requesting personal information or payment information.
Tech
The latest on the Artemis II mission to the moon, and more science stories
We got to share in a rare moment of collective awe this week as four astronauts blasted off toward the moon, beginning a 10-day journey that will take them farther from Earth than any humans have traveled in the last 50 years. It’ll still be a little while before they reach their destination — the Orion spacecraft is expected to loop around the moon on Monday — but they’ve already seen some pretty incredible stuff on the way there. Here’s the latest on the Artemis II mission, and other interesting science stories from this week.
Artemis II crosses the halfway point
After years of planning, NASA astronauts Reid Wiseman, Victor Glover and Christina Koch, along with Canadian Space Agency (CSA) astronaut Jeremy Hansen, are finally on their way to the moon for the Artemis II mission. This test flight is a crucial step in NASA’s plans to send humans to the surface of the moon again for the first time since Apollo 17, and the high-stakes launch went off without a hitch on Wednesday.
The Artemis II crew is now more than halfway to the moon, according to NASA. When Orion reaches the moon on April 6, the astronauts will have a six-hour window of opportunity to observe the partially lit lunar far side, which can’t be seen from Earth. If you’re curious about where exactly the astronauts are at any given moment, you can track the mission by visiting NASA’s Artemis Real-Time Orbit website. And, if you just want to see what space looks like from Orion, here’s a livestream from outside the capsule. The moon is now in view!
The crew did experience some technical difficulties after leaving the ground, though all were resolved fairly quickly. Early Thursday morning, Wiseman contacted mission control to troubleshoot some issues with a Surface Pro he was attempting to use, noting, “I have two Microsoft Outlooks and neither one of those are working.” Relatable. The Artemis II crew was also greeted by a malfunctioning toilet not long into the flight, and astronaut Koch had to work with the ground team to figure out a fix — which they thankfully were able to do. In a livestream later, the astronaut joked that she is now a space plumber.
Small issues aside, the Artemis II mission is off to a pretty amazing start. The Orion spacecraft completed its translunar injection burn on Thursday, officially taking it out of Earth orbit and putting it on its way to the moon. Commander Wiseman shared some pictures of the view from Orion’s windows afterward, and they are breathtaking. In one unbelievably crisp shot of Earth, you can even see two auroras. And there’s plenty more observations to come.
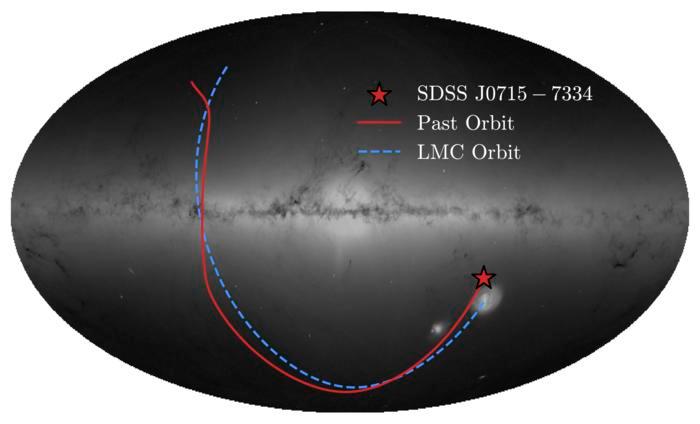
Students discover a nearly pristine ancient star
Using data from the Sloan Digital Sky Survey (SDSS), a group of undergraduate students at the University of Chicago has discovered what’s thought to be one of the oldest stars ever observed. Their analysis indicates that the star, called SDSSJ0715-7334, was born in the nearby Large Magellanic Cloud billions of years ago before eventually making its way to the Milky Way.
Vedant Chandra and the SDSS collaboration Background ESA/Gaia image, A. Moitinho, A. F. Silva, M. Barros, C. Barata, University of Lisbon; H. Savietto, Fork Research

The star was one of 77 that the students selected for closer observation after poring through the SDSS data in their “Field Course in Astrophysics” class, which is led by Professor Alex Ji, the deputy Project Scientist for SDSS-V. SDSS-V is an ongoing all-sky survey that’s mapping the Milky Way. After creating their list, they set out to observe the stars during a field trip to Carnegie Science’s Las Campanas Observatory in Chile, and honed in on SDSSJ0715-7334 on day two. The team found it’s made mostly of hydrogen and helium, with very little carbon and iron. In the paper published in the journal Nature Astronomy, the researchers note that this composition could be the product of a primordial supernova.
“This ancient immigrant gives us an unprecedented look at conditions in the early universe,” said Ji in a statement. Ji added, “The star has so little carbon that it suggests an early sprinkling of cosmic dust is responsible for making it. This formation pathway has only been seen once before.”
Before you go, be sure to check these stories out too:
Tech
Thinking Of Converting A Shipping Container Into A Garage? Here’s What To Know First

Shipping containers are a necessary component of nearly every cargo vessel that crosses the Atlantic. But while they’re built to hold a wide variety of goods, supplies, and a lot more, some people also use them for personal storage. If you’re one of these people and you’re thinking about converting a shipping container into a garage, there are some things you should know beforehand.
Shipping containers are durable and weather resistant, so you won’t have to worry about your vehicle. But a container is only about eight feet wide, which is a problem for bigger cars. Containers are customizable, so you can add doors, windows, and even insulation. But if you use one as-is, you’ll have to contend with a lack of ventilation due to its airtight construction. Plus, you’ll have to deal with temperature swings, because it heats up in the summer and cools down in the winter.
Shipping containers can be pricey, and once your start to modify it, costs only go up from there. However, they can be cheaper than building a garage from the ground up, and since they’re portable, you can move it later on if you need to. Additionally, once you get it in place, depending on what your plan is, you can have it ready in no time. Of course, unless you can haul it and set it up yourself, you’ll likely have to pay even more to a service to do it for you.
Understanding the laws regarding shipping container use
While there are pros and cons to using a shipping container as a garage, there are some legalities you should know as well. First off, whether or not you’re allowed to even use a container, is determined by your local zoning laws. These laws control how property can be used, as it may even be illegal to build a shed on your property without a permit. So you may need one before converting, or even placing, a container on your land.
But even if you pass the zoning requirements in your area, you may not be able to move forward. That’s because you may still need to get approval from local building departments in your area. These departments can use building codes to review your container to ensure it’s structurally solid, and it’s placed on a strong foundation. Then there’s how the container is classified, and whether or not it meets your local government’s requirements to be used as a garage. Finally, if you get all the paperwork in order and have the green light to move ahead, check with your homeowner’s association. They may have guidelines in place that can actually override what’s allowed by local law.
If you hit a roadblock, it’s not a good idea to go around the system. Setting up a container without proper approval can lead to fines. You may be ordered to stop work, or you may be forced to remove the container altogether.
Tech
5 Handy Uses For Smart Sensors You Probably Didn’t Think Of
We may receive a commission on purchases made from links.
A smart motion sensor typically detects the presence or movement of a person, while a smart switch is most often used to turn lights on or off. These devices are already useful just as they were designed, but did you know that you can actually program them to let you accomplish other useful things?
With a little creativity, you can use a smart sensor to warn you if you’re forgetting something, to catch if something goes wrong before it becomes a major problem, or to just generally make your life easier. Most of the features also do not require complex programming — you can either install the smart sensor directly where needed, or, at worst, add a timer via your preferred home app and keep notifications on.
Let’s look at a few handy uses for smart sensors that you probably haven’t considered yet. You might be surprised what these things can accomplish with a little bit of ingenuity.
Warn you if you left a door or window open
Contact sensors are pretty simple smart devices, as their primary purpose is to warn you when the two pieces are not in contact. These are most commonly used for doors and windows — you can program them to send a notification on your phone when you leave your house, and you left a window or door open. There are also several creative uses for contact sensors, including automatically turning on lights and running a home routine.
Though these sensors are typically attached to doors and windows, that does not mean they’re limited to those used for access. If you often second-guess yourself about whether you’ve properly closed your fridge door, especially when you’re on vacation for a couple of days, attaching a contact sensor to it will help you avoid that problem. You can then set the sensor to warn you if the door is open for too long. If you still need to check, just open your phone and check the device’s status.
You can also install the sensor inside a cupboard or cabinet if you’re guarding stuff. For example, if you keep chocolates in your pantry and don’t want your kids raiding your sweets without your knowledge, you can set the sensor to warn you when the cupboard door opens, allowing you to check your smart security camera to see who’s the culprit.
Get notifications for mail or packages
Smart mailbox alarms exist to ensure you don’t miss letters or packages that might’ve arrived when you were asleep or weren’t home. After all, we rarely receive snail mail these days, but the letters that do come in are quite important, like a jury duty summons or your tax return check. These sensors work similarly to a motion sensor in that they detect movement in your inbox.
Because of this, you do not need to purchase a smart mailbox alarm — if you already have an extra motion sensor at home, you can install it in your mailbox and set it to alert you if it detects movement. However, this might not work for larger packages that won’t fit in your mailbox. So, if you want to get alerted when an Amazon package arrives at your doorstep, consider getting a Ring camera.
This smart doorbell camera can tell you when someone’s at your door, but you can also program it to notify you if it detects movement on your porch. This means it can double as a security camera while simultaneously notifying you if someone leaves a package at your doorstep.
Control the exhaust fan bathroom automatically
Smart switches are often used for remotely turning on devices using voice commands. But because you can control them with an app, you can make them do a lot of other clever things beyond switching on or off on your command. One thing you can do is program your bathroom exhaust fan to work automatically based on which light you turn on.
The biggest problem some people encounter with bathroom exhaust fans is that they do not work optimally. Most exhaust fans turn on when you switch on the bathroom lights — this is a problem for some people, as it can cause a cold draft while they’re showering. And when you switch off the light after showering, it also turns off the exhaust, leaving excess moisture stuck inside your bathroom.
If you use a smart switch to control the lights and the exhaust fan in your bathroom, you can program it so that you don’t have to think about the exhaust fan. For example, you can set the exhaust fan to automatically turn on when you switch on the light for your toilet area to keep the area fresh. But for your shower, you can instead command the exhaust fan switch to turn on minutes after you turn off the light. That way, you don’t get chilly while you’re bathing, while the exhaust fan will still ensure that moisture is exhausted after you leave the restroom.
Avoid extensive water damage by catching leaks early
You might think that a water leak sensor is an unnecessary smart device for your home, especially if you live in a newly constructed dwelling. But if you live in an older home or experience freezing winters in your area, this might be a prudent investment. That’s because a leak sensor will warn you if you have a problem with your plumbing before it becomes a major issue, making it one of the smart gadget upgrades you can install in your bathroom or kitchen.
As the name suggests, these devices alert you when they detect a water leak. That way, you can immediately shut off your taps before the water spreads all over your floor. Since these smart devices send a notification to your phone, you also get warned wherever you are in the world as long as you’re online.
This is crucial if you’re away for an extended period. That way, you can immediately inform a trusted person to turn off the taps in your home and avoid coming home to extensive (and expensive) water damage.
Toggle perimeter and safety lights as necessary
Smart switches can be programmed to automatically turn on and off your perimeter and safety lights based on sunrise and sunset times. However, this only takes into account the position of the sun and does not consider meteorological effects. So, if you want to ensure that your lights turn on when the skies get too dark, you can install a smart light sensor.
With a smart light sensor installed, you can then use it to command all the lights around your home to switch on when it gets too dark — whether through the setting of the sun or because of a snowstorm — and turn off when there’s enough light to save on electricity costs. You can even use it to automatically adjust the dimmable lights in your home, ensuring a consistent brightness level throughout the day and night.
You can also pair a smart light sensor with a smart motion detector to specific areas in your home. That way, you can program lights in common areas, like your hallway or garden, to turn on only when someone is in the area and it’s dark. You can also use it to automatically lower or raise smart blinds to help keep the temperature in your home under control or to maximize natural light.
Tech
Iran-linked hackers use Cold War tricks and fake online identities to steal secrets from Apple and Microsoft users


- Charming Kitten relies on deception rather than exploiting technical software vulnerabilities
- Fake identities build trust before phishing attacks compromise sensitive user credentials
- Operations extend across Apple and Microsoft platforms, affecting diverse users globally
Iran-linked cyber operations are drawing renewed attention for relying less on advanced code and more on human manipulation to gain access to sensitive systems.
At the centre of this activity is Charming Kitten, a group associated with Iran’s security apparatus which has spent years targeting officials, researchers, and corporate employees.
Instead of exploiting technical vulnerabilities, operatives frequently impersonate trusted contacts, using carefully crafted messages to trick victims into revealing credentials or installing malicious software.
Article continues below
Cold War tactics and social engineering
These tactics echo intelligence strategies more commonly associated with Cold War espionage, where access and trust often proved more effective than technical superiority.
Fake online identities — including personas built around attractive or credible profiles — are used to establish relationships before launching phishing attacks.
This approach has enabled the group to operate across platforms used by both Apple and Microsoft ecosystems, exposing both Mac and Windows users to compromise.
Alongside external deception campaigns, investigators have raised concerns about insider threats linked to individuals embedded within major technology firms.
A high-profile case involving members of the Ghandali family centres on allegations of trade secret theft from companies including Google.
Prosecutors claim that sensitive data related to processor security and cryptography was extracted over time and transferred outside the United States.
Ex-counterintelligence officials describe the method as a “slow, deliberate extraction” carried out by actors with training or external direction.
Rather than relying on digital exfiltration tools, some of the alleged activity involved photographing computer screens — a low-technology method designed to avoid detection by cybersecurity systems.
“The most damaging breaches often originate from within,” one expert noted, adding that trusted access can bypass even advanced defenses.
Analysts argue that these operations reflect a wider intelligence framework that combines cyber activity, human networks, and surveillance capabilities.
Former officials state that Iran has developed a layered approach that includes recruitment, online intelligence gathering, and procurement channels.
One source described Iran as “the third most sophisticated adversary,” adding that its activities were underestimated for years compared with those of larger rivals.
The same networks have also been linked to monitoring dissidents abroad, indicating that operations are not limited to economic or military objectives.
This dual focus — external competition and internal control — complicates assessments of intent and scale.
Cases such as that of Monica Witt, who allegedly provided intelligence to Iran after defecting, reinforce concerns about insider cooperation.
Staying safe from phishing and espionage requires a layered approach to digital security. Users should verify identities before sharing credentials or sensitive information.
Strong, unique passwords combined with multi-factor authentication help limit account compromise.
Also, installing reliable antivirus software protects against known threats, while maintaining an active firewall prevents unauthorized access.
In addition, trusted malware removal tools can detect and eliminate suspicious activity before it spreads.
Via MSN
Follow TechRadar on Google News and add us as a preferred source to get our expert news, reviews, and opinion in your feeds. Make sure to click the Follow button!
And of course you can also follow TechRadar on TikTok for news, reviews, unboxings in video form, and get regular updates from us on WhatsApp too.
-

 NewsBeat3 days ago
NewsBeat3 days agoSteven Gerrard disagrees with Gary Neville over ‘shock’ Chelsea and Arsenal claim | Football
-

 Business3 days ago
Business3 days agoNo Jackpot Winner and $194 Million Prize Rolls Over
-

 Fashion2 days ago
Fashion2 days agoWeekend Open Thread: Spanx – Corporette.com
-
Entertainment7 days ago
Fans slam 'heartbreaking' Barbie Dream Fest convention debacle with 'cardboard cutout' experience
-

 Crypto World4 days ago
Crypto World4 days agoGold Price Prediction: Worst Month in 17 Years fo Save Haven Rock
-

 Business5 hours ago
Business5 hours agoThree Gulf funds agree to back Paramount’s $81 billion takeover of Warner, WSJ reports
-
Crypto World6 days ago
Dems press CFTC, ethics board on prediction-market insider trades
-

 Sports1 day ago
Sports1 day agoIndia men’s 4x400m and mixed 4x100m relay teams register big progress | Other Sports News
-

 Business4 days ago
Business4 days agoLogin and Checkout Issues Spark Merchant Frustration
-

 Tech6 days ago
Tech6 days agoEE TV is using AI to help you find something to watch
-

 Tech7 days ago
Tech7 days agoApple will hide your email address from apps and websites, but not cops
-

 Sports6 days ago
Sports6 days agoTallest college basketball player ever, standing at 7-foot-9, entering transfer portal
-

 Politics6 days ago
Politics6 days agoShould Trump Be Scared Strait?
-

 Tech6 days ago
Tech6 days agoFlipsnack and the shift toward motion-first business content with living visuals
-

 Fashion7 days ago
Fashion7 days agoThe Best Spring Trends of 2026
-
Tech6 days ago
Daily Deal: StackSkills Premium Annual Pass
-

 Crypto World6 days ago
Crypto World6 days agoU.S. rule change may open trillions in 401(k) funds to crypto
-

 Sports6 days ago
Sports6 days agoWomen’s hockey camp eyes fitness boost, tactics ahead of WC 2026 campaign | Other Sports News
-

 Tech6 days ago
Tech6 days agoHow to back up your iPhone & iPad to your Mac before something goes wrong
-
 Politics7 days ago
Politics7 days agoBBC slammed for ignoring author of The Fraud















You must be logged in to post a comment Login