When Kim Whitman’s son was in kindergarten in 2015, it was the first time their school district rolled out a one-to-one device program, assigning an electronic device to every child. Beyond using it in the classroom, the children were required to bring it home each night to charge it — but with that came the temptation to use the device after hours.
“My children never had a device and suddenly they had these iPads at home I had to manage,” Whitman, now the co-lead for the Distraction-Free Schools Policy Project, says.
Over a decade later, personal devices are more ubiquitous in some classrooms than mechanical pencils. Device adoption catapulted during the COVID-19 pandemic, thanks to an influx of federal dollars and to usher children into virtual schooling. But that adoption rush created what some experts deemed as a bit of toothpaste-out-of-the-tube moment, where decisions were made without fully thinking through the ramifications.
“For a lot of logistical reasons and necessity through the pandemic, we sort of went all in — we had to,” says Kate Blocker, director of research and programs at Children and Screens: Institute of Digital Media and Child Development. “Digital programs and edtech broadly has come with a lot of promise, including improving student learning and improving teacher and administration efficiency. The question people are starting to ask themselves is, ‘Are we seeing those benefits?’”
Some legislators and advocates are pushing to roll back the reliance on devices, particularly at a younger level when children are more susceptible to distractions.
“You don’t tell smokers to sit next to a pack of cigarettes,” Angela Duckworth, a professor at the University of Pennsylvania and leader in the educational psychology sector, says. “You tell them to remove yourself from temptation.”
What Brought Us Here
With many parents thinking more critically about their children’s relationships with screen time comes a new swell of concern about personal devices, especially in learning environments. According to federal data, 9 in 10 public schools had a one-to-one program giving every student a school-issued device for the 2024–25 school year.
While research is sparse on the overall effects of personal devices like laptops and iPads in school, they are becoming a proven distraction in the classroom. Duckworth served as the lead investigator for a newly released study that found teachers estimate 1 in 3 students used laptops during class for non-academic purposes, including texting and social media scrolling.
“It was becoming clear to us, from our previous open-ended responses to the survey, that phones are not the only digital distraction in the classroom,” she says.
Duckworth herself has a “no technology” rule in her lecture hall, put in place after finding many of her students were using their laptops to watch movies, online shop or study for other classes.
“If you see a kid with a phone, you know they’re not supposed to be doing something,” she says. “With a laptop, kids become Oscar-winning actors and actresses: They look up and down and seem like they’re doing something they’re supposed to be doing.”
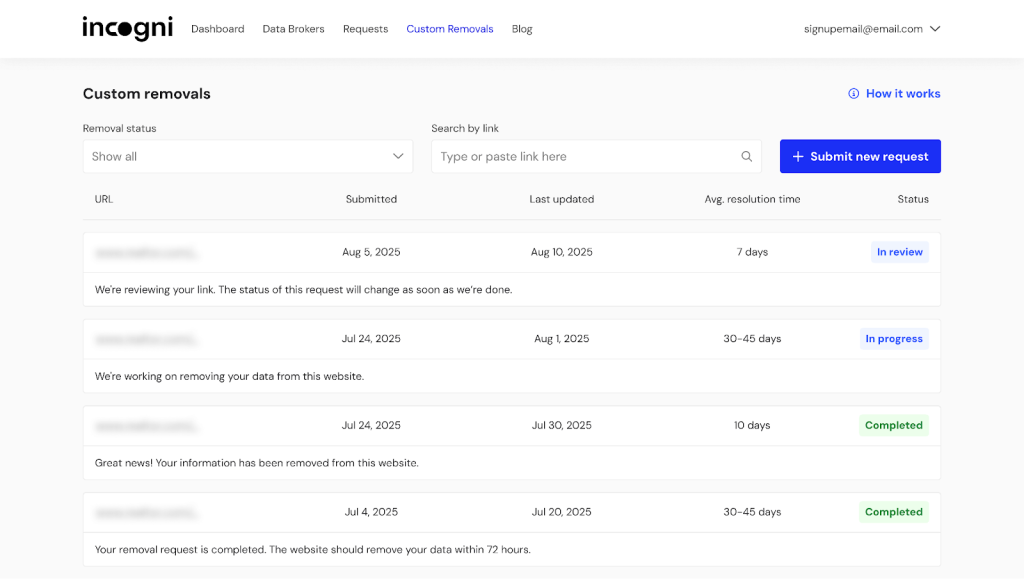
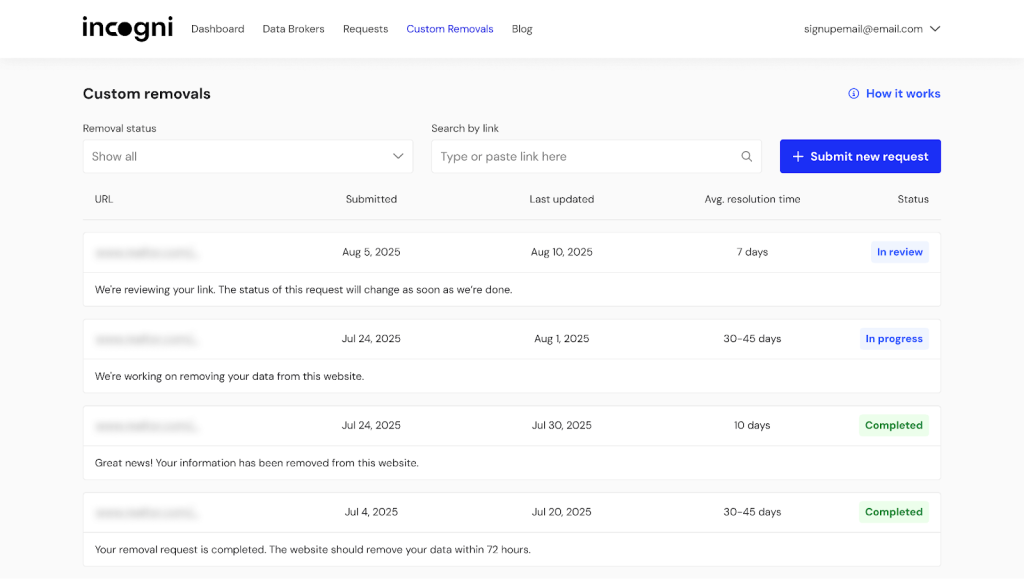
There is also the concern of data collection for unknowing students.
“I’m aware of pressure around data and data management, with questions around appropriate guardrails in place,” Blocker says. “So many companies hold an immense amount of student data. Is that being managed properly and held to the same standards as the curriculum?”
And the rise — and rising fear — of artificial intelligence may have also fueled this hard look at education technology and its devices.
“There’s the larger techno-panic happening around devices in schools especially now that AI has arrived,” says Carrie James, co-director of the Center for the Center for Digital Thriving at the Harvard Graduate School of Education. “In the past, schools have been very intentional: They have a school committee meeting and make very clear decisions about which pieces of technology they’re going to adopt. The challenge around generative AI is it arrived on everyone’s devices, and now schools have to reckon with it. I think that piece is exacerbating it.”
Reigning in Tech
Whitman says roughly nine states have presented some form of “Safe Schools Technology” legislation, following the lobbying of the Distraction-Free Schools Policy Project.
She is quick to point out the legislation is not seeking to ban technology entirely, but instead will require schools to limit it so that students don’t have “unsafe, ineffective or inappropriate experiences.”
“We believe in tech education,” Whitman says. “You need education on technology — how to use Excel, how to type — these are all really important skills for students to have. But it doesn’t mean we have to teach everything through the device.”
State policymakers are trying a few different methods of regulating edtech through legislation. There’s limiting screen time, but keeping the technology – a strategy particularly popular in elementary schools – and has been introduced in bills in Oklahoma, West Virginia and Missouri. Vermont introduced a bill earlier this year allowing parents to opt their kids out of using electronic devices in the classroom.
And some leaders in Kansas are attempting to ban hardware devices in elementary schools, but allow a shared-device model — like a computer lab — in middle schools, and limit classroom screen time to one hour a day. For high school students, that would be bumped up to 90 minutes a day.
There is also a focus on the edtech itself, with state efforts attempting to ensure it is certified in the same way other curricula are certified, outlining steps for evaluating and choosing products and communicating about that process to parents.
That is a particularly tricky conversation, with questions swirling around the onus of verification: if it is the school’s job or the company’s responsibility, or if that task belongs to a third party. Experts say there is no national, catch-all system that easily shows if an edtech company does what it claims to do, though the Internet Safety Lab and American Academy of Pediatrics have given some guidelines that can help.
Whitman pushed for third-party intervention.
“There is nobody right now that is confirming these products are safe, effective and legal,” she says. “It should not fall on the district’s IT director; it would be impossible for them to do it. And the companies should not be tasked with doing it — that would be like nicotine companies vetting their own cigarettes.”
But many districts, particularly those that serve low-income and minority populations, are in a tough spot with mitigating edtech usage and implementations. They often do not have the funds to purchase new textbooks, which typically cost more than their digital counterparts. They have also invested heavily — often through grants or federal funds — in digital devices.
“That is in fact the conundrum: School administrators are in a tug of war,” Blocker says. “They’ve invested in so much, and a lot of the products came with promise. It’s not like they grabbed a brick and said, ‘I’m going to make this work.’ They were told they were going to have all these benefits.”
And James, of the Center for the Center for Digital Thriving, said it is important to remember some student populations, such as her neurodivergent child, benefit greatly from the expanded access digital products can provide.
“Edtech and assistant technology are key for her learning,” James says, pushing against a sweeping blanket ban. “That’s where the decision has to be school-community specific. Educators know their community best, and these regulations have to be designed for their students.”
Widespread Adoption?
The new efforts targeting laptops and edtech tools follow a swell of states banning student cellphones in the classroom, with many restricting them in between class periods and lunch time as well. While that has been one of the rare successful bipartisan efforts at the state and federal levels, experts say going entirely device-free in schools is a much more nuanced conversation.
“School phone bans are less about technology for learning’s sake and more about technology interfering with learning,” Blocker says. “I think it was clearer for everyone to see why [banning phones] might have a good outcome. It is much harder with edtech; there is evidence, particularly for older students, that when used well it can be beneficial.”
Whitman disagrees, though, saying while it may be a slower uptick than phone bans, she does believe edtech bans will eventually reach that same level.
“Parents are becoming aware and coming together with collective action,” she says. “I think this will be similar to phone-free schools eventually. It will, but we’re on the cusp of it right now.”
James urges schools and districts to focus less on silver-bullet solutions like total bans and more on multifaceted approaches to integrating technology well.
“Bans might feel like they can be a starting point for better learning, but they can’t really be the finish line,” she says.
For the sake of children and teens, James adds, “we have to build agency and intentionality for using technology well, because as soon as they walk out of school, you typically have pretty incredible access to technology.”













.png)