TL;DR
The Trump administration announced the Tesla Model Y is the first car to pass NHTSA’s new driver assistance safety tests. The same agency is investigating 3.2 million Teslas for crashing while using the company’s more advanced system.
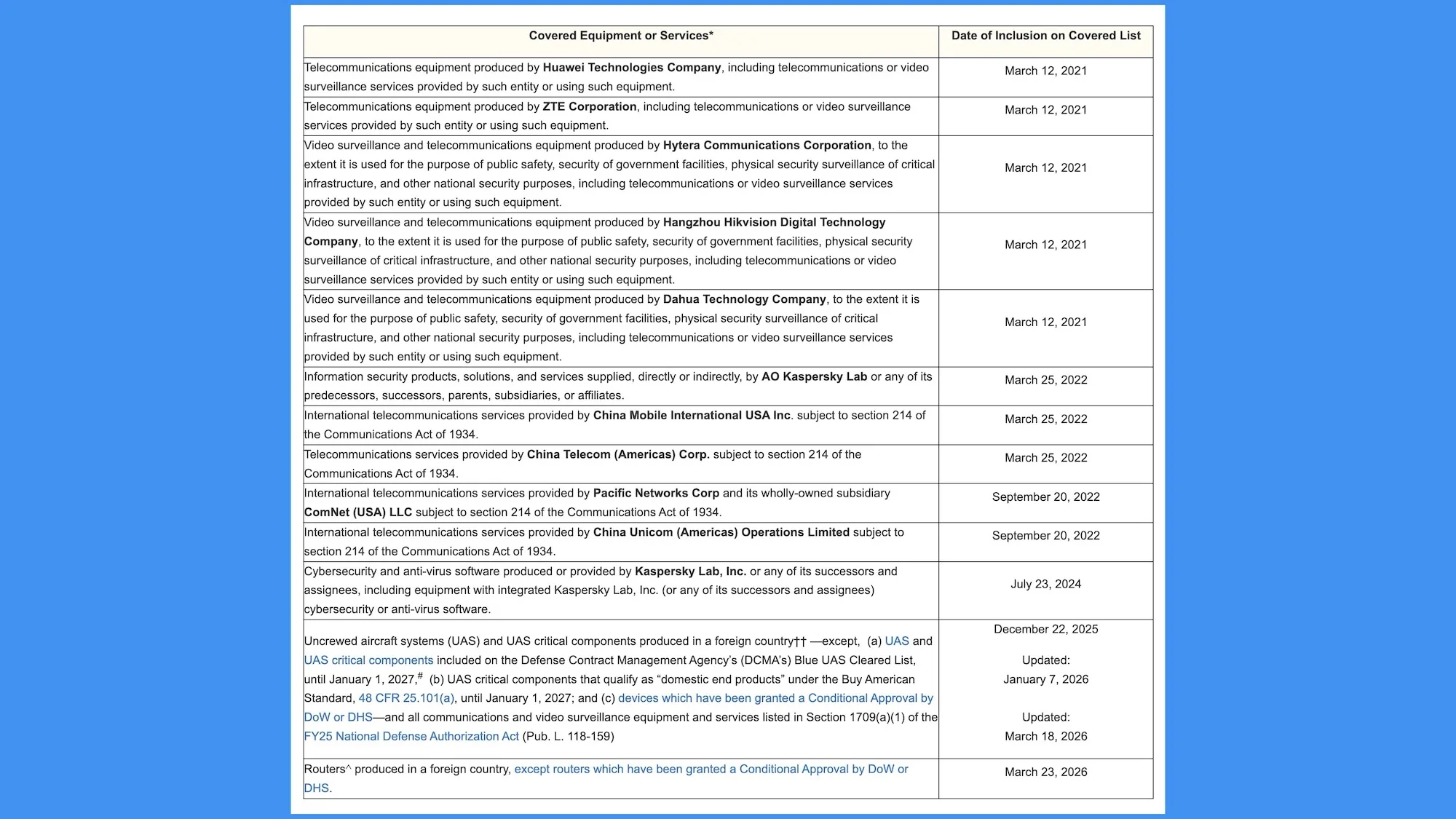
The FCC has officially added foreign-made routers to its Covered List, a list of equipment deemed a national security threat to the United States. This means no new foreign-produced routers can be sold in America, unless they are granted a special exemption.
If you are wondering what that means for your current router sitting in your living room, don’t panic yet. For now, the ban only affects new router approvals.
According to the National Security Determination issued on March 20, 2026, routers have become the target for hackers and state-sponsored cyber attackers. In the public notice the FCC released today, it said, “From disrupting network connectivity to enabling local networking espionage and intellectual property theft, foreign-produced routers present unacceptable risks to Americans.”

The notice points to a series of high-profile attacks as evidence, stating that “routers produced abroad were directly implicated in the Volt, Flax, and Salt Typhoon cyberattacks which targeted critical American communications, energy, transportation, and water infrastructure.”
The conclusion from national security agencies is blunt. Foreign routers are giving bad actors a “built-in backdoor to American homes, businesses, critical infrastructure, and emergency services.”
Not immediately. The notice does not address routers already in use by the public. It only talks about the routers’ sales going forward.
Foreign routers that have FCC authorization can still be sold. Router manufacturers that produce their devices abroad can apply for the Conditional Approval, which buys them time while they develop a plan to move manufacturing to the US.

You can find the names of brands under the Covered List and those that received Conditional Approval on the FCC’s website. Popular brands like TP-Link, which were already under investigation by the US government, will need to either relocate manufacturing or apply for these exemptions to continue selling new models in the US.
This is a significant move that will reshape the router market. Whether it will translate into better security for everyday users remains to be seen, but one thing is clear: the era of affordable, foreign-made routers dominating American homes could soon be coming to an end.


The Trump administration announced the Tesla Model Y is the first car to pass NHTSA’s new driver assistance safety tests. The same agency is investigating 3.2 million Teslas for crashing while using the company’s more advanced system.
TL;DR
The Trump administration announced on Wednesday that the Tesla Model Y is the first vehicle to pass NHTSA’s new advanced driver assistance safety tests. The same agency is simultaneously investigating 3.2 million Tesla vehicles for crashing while using the company’s more advanced self-driving system. The announcement celebrates Tesla for passing a test that measures whether a car can detect a pedestrian. The investigation examines whether Tesla’s cars can detect a pedestrian.
The distinction between the two is the distance between what the tests measure and what the technology attempts. The ADAS benchmark evaluates features that are standard equipment on dozens of vehicles from Toyota, Honda, Hyundai, BMW, and others. The investigation covers Tesla’s Full Self-Driving software, which operates at a level of autonomy that the ADAS tests do not assess. The press release and the probe exist in the same agency, issued weeks apart, about the same company.
The 2026 Model Y passed eight evaluations under NHTSA’s updated New Car Assessment Program. Four are legacy criteria that have been part of the programme for years: forward collision warning, crash imminent braking, dynamic brake support, and lane departure warning. Four are newly added: pedestrian automatic emergency braking, lane keeping assistance, blind spot warning, and blind spot intervention.
The new tests are pass-fail assessments of features that the automotive industry has been shipping as standard or optional equipment for years. Blind spot warning has been available on mainstream vehicles since the mid-2010s. Pedestrian automatic emergency braking is standard on most new cars sold in the United States. Lane keeping assistance is a feature that a 25,000 dollar Honda Civic includes at no additional cost.
The tests do not evaluate Tesla’s Autopilot or Full Self-Driving capabilities. They do not measure how the vehicle performs when operating autonomously. They measure whether the vehicle’s basic safety systems, the features that activate when a human is driving, function correctly. Passing them is necessary. It is not exceptional.
NHTSA finalised the updated NCAP criteria in late 2024 for implementation in model year 2026. In September 2025, the Trump administration delayed the requirement by one year to model year 2027, after the Alliance for Automotive Innovation, the industry’s main lobbying group, requested more time. Tesla, Rivian, and Lucid are not members of the alliance.
The delay means that most automakers have not yet submitted vehicles for the new tests, not because their cars cannot pass, but because the deadline has been pushed to 2027. Tesla submitted the Model Y voluntarily, ahead of the delayed timeline. It was the only manufacturer to do so. The result is a press release from the Department of Transportation announcing that Tesla is the “first vehicle” to pass tests that other manufacturers were told they did not yet need to take.
The announcement was titled “Trump’s Transportation Department Announces Tesla Model Y Is the First Vehicle to Pass NHTSA’s New ‘Advanced Driver Assistance System’ Tests.” The relationship between the Trump administration and Tesla’s regulatory environment is not incidental to the framing. The department delayed the tests, creating a window in which Tesla could be the only company to submit, then announced the result with the president’s name in the headline.
While NHTSA was certifying the Model Y’s basic safety features, its Office of Defects Investigation was escalating a probe into 3.2 million Tesla vehicles equipped with Full Self-Driving software. The engineering analysis, opened in March 2026, covers crashes in which FSD failed to detect common roadway conditions that impaired camera visibility, including glare, fog, and airborne debris.
The agency documented incidents in which vehicles running FSD crossed into opposing lanes, ran red lights, and struck pedestrians. Tesla’s robotaxi service in Austin has been involved in 14 crashes since launching, a rate that Electrek calculated at approximately four times worse than human drivers. NHTSA said the system “did not detect common roadway conditions that impaired camera visibility and/or provide alerts when camera performance had deteriorated until immediately before the crash occurred.”
The engineering analysis is a required step before a potential recall. Tesla has asked for, and received, multiple extensions to submit crash data to the agency. The investigation covers the software that Tesla charges up to 8,000 dollars for and markets under the name “Full Self-Driving,” a name that NHTSA itself has noted does not accurately describe the system’s capabilities.
The automotive and technology industries classify driver assistance on a scale from Level 0, no automation, to Level 5, full automation with no human oversight required. The ADAS tests that the Model Y passed evaluate Level 1 and Level 2 features: systems that assist the driver but require the driver to remain in control at all times.
Tesla’s Full Self-Driving software, which is the subject of the NHTSA investigation, attempts to operate at Level 2 with ambitions toward higher levels of autonomy. Companies like Wayve are targeting Level 4 autonomy, which means the vehicle can operate without human intervention in defined conditions. Wayve raised 1.2 billion dollars to develop autonomous driving systems that do not require a human safety driver.
The gap between Level 2, where a human must always be ready to take over, and Level 4, where the car handles defined conditions independently, is the gap between the ADAS benchmark the Model Y just passed and the Full Self-Driving system that NHTSA is investigating. Uber relaunched Motional’s robotaxi service in Las Vegas with a target of fully driverless operation by the end of 2026, using a system designed from the ground up for Level 4. Tesla is attempting to reach the same destination using cameras, consumer vehicles, and software updates.
Tesla reclaimed the global quarterly EV sales crown from BYD in the first quarter of 2026, selling 358,000 battery electric vehicles. The company’s market position depends on the perception that its technology leads the industry. The ADAS benchmark contributes to that perception. The FSD investigation complicates it.
The Model Y passing eight safety tests is a data point about a car that can detect a pedestrian in a controlled scenario. The FSD investigation is a data point about the same company’s software failing to detect pedestrians, red lights, and oncoming traffic in the real world. The tests and the investigation measure different things. But they measure the same company’s claim to be the leader in vehicle safety and autonomy.
NHTSA now occupies the position of simultaneously certifying Tesla’s basic safety features and investigating whether its advanced features are safe enough to remain on the road. The press release says Tesla is first. The investigation says Tesla may be defective. Both are true. Neither tells the whole story. The distance between a passed benchmark and an open investigation is the distance between what a car can do when the test is defined and what it does when the road is not.
California’s extensive canal network could become a massive source of clean energy while saving billions of gallons of water each year.
A University of California study found covering roughly 4,000 kilometers of canals with solar panels would generate 13GW of power annually and save 63 billion gallons of water.
That amount of water is enough to meet the residential needs of more than two million people every single year.
A small-scale demonstration called the Nexus project was built to test whether this concept actually works in real-world conditions.
The 1.6-megawatt Nexus installation sits on canals operated by the Turlock Irrigation District, and after one full irrigation season, the covered canal sections showed evaporation reductions of 50 to 70% beneath the solar arrays.
Algae growth dropped by 85%, which significantly reduces the cost of maintaining the canals and cleaning water pumps.
The shade also keeps the solar panels cooler than ground-mounted alternatives, improving their electricity output by roughly 2.5 to 5%.
India has already built similar canal-top solar projects, proving the concept works across different climates and geographies.
Despite the clear benefits, this idea faces resistance, and the major obstacle is cost.
Canal top solar requires heavy steel support structures that must span the width of the water channel below, and these structures alone can account for up to 40% of the total project cost, significantly more than ground-mounted solar farms.
Critics argue that canals are designed for water delivery, not as foundations for industrial infrastructure.
Such designs will require regular access to the canals by maintenance crews for desilting and repairs, and overhead panels would complicate that work significantly.
Some also point out California has plenty of cheap desert land where traditional solar panels can be installed at much lower expense.
Though a solar farm on desert land costs less and avoids the engineering complications, it does nothing to save water, a long-standing Californian issue, as the state has already lost 40% of its Colorado River allocation this year, and every drop saved matters.
The economic calculation of this idea shifts when water savings are given real monetary value.
Canal top solar prevents evaporation in a state that regularly faces severe drought conditions, and also generates electricity exactly where agricultural demand exists, reducing transmission losses from distant desert solar farms.
From another vantage point, canal top solar could ease data center power demand, which usually places enormous strain on local grids and water supplies.
It generates clean power exactly where it is needed, reducing transmission losses and avoiding the need for new transmission lines.
The water saved through evaporation reduction could be used to cool data centers instead of being lost to the atmosphere.
A single data center can use millions of gallons of water each year, and canal shading preserves that resource for productive use.
The 13GW of potential generation from California’s canals could power hundreds of data centers without requiring additional land or stressing the state’s overtaxed grid.
That said, preventing evaporation, which the canal top solar will do, is not a guaranteed win.
It will likely have minimal impact on the local humidity and can disrupt aquatic ecosystems by reducing dissolved oxygen, which is like solving one problem while creating another.
The Nexus pilot will continue collecting data to determine whether California scales the concept or decides the ecological and operational trade-offs aren’t worth the energy gains.
Via PV Magazine

Follow TechRadar on Google News and add us as a preferred source to get our expert news, reviews, and opinion in your feeds.
NVIDIA has confirmed in a statement for BleepingComputer that GeForce NOW user information has been exposed in a data breach.
The gaming and hardware giant has clarified that the impact is limited to Armenia, and was caused by a compromise of the infrastructure operated by a regional partner.
The company added that its own network was not impacted by the incident.
“Our investigation found no impact on NVIDIA-operated services. The issue is limited to systems run by a third-party GeForce NOW Alliance partner based in Armenia. We are working closely with the partner to support their investigation and resolution. Impacted users will be notified by GFN.am,” the company said.
The statement comes in response to a post last week on a hacker forum from a threat actor using the ShinyHunters nickname, claiming to have breached the GeForce NOW service and stolen millions of user records.
However, the ShinyHunters actor who published the breach on the hacker forum is believed to be an imposter.
According to the threat actor, the stolen information includes full names, email addresses, usernames, dates of birth, membership status, and 2FA/TOTP status.
The threat actor also posted samples of the stolen data and offered the full database for $100,000 paid in Bitcoin or Monero.
The NVIDIA GeForce NOW cloud gaming service lets users stream to their systems games running on more powerful hardware using NVIDIA GPUs in a datacenter.
GFN.am is the Armenian regional operator for GeForce NOW, responsible for operating NVIDIA’s service in the country.
Alliance partner environments can operate independent authentication systems, local customer databases, regional billing platforms, and locally managed infrastructure.
A statement posted by GFN.am confirms a cybersecurity incident that took place between March 20 and 26 and exposed the following information:
GFN.am has clarified that no account passwords were exposed in the incident, and any users who registered to the service after March 9 are not impacted.
According to NVIDIA’s help page, GFN.am is also responsible for managing GeForce NOW operations in Azerbaijan, Georgia, Kazakhstan, Moldova, Ukraine, and Uzbekistan, but no impact on those countries has been confirmed.
BleepingComputer found that the threat actor’s post has now been removed from the hacker forum.
It is unclear if the database has been sold to a buyer or if the seller or forum administrators deleted it.
Update [14:14]: Added information that the threat actor may be a ShinyHunters impersonator.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.


Diablo IV’s secret cow level – which according to the game’s former general manager Rod Fergusson did not exist – has finally been discovered by an enthusiastic player of Blizzard’s action-RPG series. Streamer LoatheBurger, a self-confessed Diablo fan since 1996, explained the convoluted steps required to unlock the hidden level,…
Read Entire Article
Source link


Most enterprise security programs were built to protect servers, endpoints, and cloud accounts. None of them was built to find a customer intake form that a product manager vibe coded on Lovable over a weekend, connected to a live Supabase database, and deployed on a public URL indexed by Google. That gap now has a price tag.
New research from Israeli cybersecurity firm RedAccess quantifies the scale. The firm discovered 380,000 publicly accessible assets, including applications, databases, and related infrastructure, built with vibe coding tools from Lovable, Base44, and Replit, as well as deployment platform Netlify. Roughly 5,000 of those assets, about 1.3%, contained sensitive corporate information. CEO Dor Zvi said his team found the exposure while researching shadow AI for customers. Axios independently verified multiple exposed apps, and Wired confirmed the findings separately.
Among the verified exposures: a shipping company app detailed which vessels were expected at which ports. An internal health company application listed active clinical trials across the U.K. Full, unredacted customer service conversations for a British cabinet supplier sat on the open web. Internal financial information for a Brazilian bank was accessible to anyone who found the URL.
The exposed data also included patient conversations at a children’s long-term care facility, hospital doctor-patient summaries, incident response records at a security company, and ad purchasing strategies. Depending on jurisdiction and the data involved, the healthcare and financial exposures may trigger regulatory obligations under HIPAA, UK GDPR, or Brazil’s LGPD.
RedAccess found phishing sites built on Lovable that impersonated Bank of America, FedEx, Trader Joe’s, and McDonald’s. Lovable said it had begun investigating and removing the phishing sites.
Privacy settings on several vibe coding platforms make apps publicly accessible unless users manually switch them to private. Many of these applications get indexed by Google and other search engines. Anyone can stumble across them. Zvi put it plainly: “I don’t think it’s feasible to educate the whole world around security. My mother is [vibe coding] with Lovable, and no offense, but I don’t think she will think about role-based access.”
In October 2025, Escape.tech scanned 5,600 publicly available vibe-coded applications and found more than 2,000 high-impact vulnerabilities, over 400 exposed secrets including API keys and access tokens, and 175 instances of personal data exposure containing medical records and bank account numbers. Every vulnerability Escape found was in a live production system, discoverable within hours. The full report documents the methodology. Escape separately raised an $18 million Series A led by Balderton in March 2026, citing the security gap opened by AI-generated code as a core market thesis.
Gartner’s “Predicts 2026” report forecasts that by 2028, prompt-to-app approaches adopted by citizen developers will increase software defects by 2,500%. Gartner identifies a new class of defect where AI generates code that is syntactically correct but lacks awareness of broader system architecture and nuanced business rules. The remediation costs for these deep contextual bugs will consume budgets previously allocated to innovation.
IBM’s 2025 Cost of a Data Breach Report found that 20% of organizations experienced breaches linked to shadow AI. Those incidents added $670,000 to the average breach cost, pushing the shadow AI breach average to $4.63 million. Among organizations that reported AI-related breaches, 97% lacked proper access controls. And 63% of breached organizations had no AI governance policy in place.
Shadow AI breaches disproportionately exposed customer personally identifiable information at 65%, compared to 53% across all breaches, and affected data distributed across multiple environments 62% of the time. Only 34% of organizations with AI governance policies performed regular audits for unsanctioned AI tools. VentureBeat’s shadow AI research estimated that actively used shadow apps could more than double by mid-2026. Cyberhaven data found 73.8% of ChatGPT workplace accounts in enterprise environments were unauthorized.
The audit framework below gives CISOs a starting point for triaging vibe-coded app risk across five domains.
|
Domain |
Current State (Most Orgs) |
Target State |
First Action |
|
Discovery |
No visibility into vibe-coded apps |
Automated scanning of vibe coding platform domains |
Run DNS + certificate transparency scan for Lovable, Replit, Base44, and Netlify subdomains tied to corporate assets |
|
Authentication |
Platform defaults (public by default) |
SSO/SAML integration required before deployment |
Block unauthenticated apps from accessing internal data sources |
|
Code scanning |
Zero coverage for citizen-built apps |
Mandatory SAST/DAST before production |
Extend the existing AppSec pipeline to cover vibe-coded deployments |
|
Data loss prevention |
No DLP coverage for vibe coding domains |
DLP policies covering Lovable, Replit, Base44, Netlify |
Add vibe coding platform domains to existing DLP rules |
|
Governance |
No AI usage policy or shadow AI detection |
AI governance policy with regular audits for unsanctioned tools |
Publish an acceptable-use policy for AI coding tools with a pre-deployment review gate |
The CISO who treats this as a policy problem will write a memo. The CISO who treats this as an architecture problem will deploy discovery scanning across the four largest vibe coding domains, require pre-deployment security review, extend the existing AppSec pipeline to citizen-built apps, and add those domains to DLP rules before the next board meeting. One of those CISOs avoids the next headline.
The vibe coding exposure RedAccess documented is not a separate problem from shadow AI. It is shadow AI’s production layer. Employees build internal tools on platforms that default to public, skip authentication, and never appear on any asset inventory, which means the applications stay invisible to security teams until a breach surfaces or a reporter finds them first. Traditional asset discovery tools were designed to find servers, containers, and cloud instances. They have no way to find a marketing configurator that a product manager built on Lovable over a weekend, connected to a Supabase database holding live customer records, and shared with three external contractors through a public URL that Google indexed within hours.
The detection challenge runs deeper than most security teams realize. Vibe-coded apps deploy on platform subdomains that rotate frequently and often sit behind CDN layers that mask origin infrastructure. Organizations running mature, secure web gateways, CASB, or DNS logging can detect employee access to these domains. But detecting access is not the same as inventorying what was deployed, what data it holds, or whether it requires authentication. Without explicit monitoring of the major vibe coding platforms, the apps themselves generate a limited signal in conventional SIEM or endpoint telemetry. They exist in a gap between network visibility and application inventory that most security stacks were never architected to cover.
Replit CEO Amjad Masad said RedAccess gave his company only 24 hours before going to the press. Base44 (via Wix) and Lovable both said RedAccess did not include the URLs or technical specifics needed to verify the findings. None of the platforms denied that the exposed applications existed.
Wiz Research separately discovered in July 2025 that Base44 contained a platform-wide authentication bypass. Exposed API endpoints allowed anyone to create a verified account on private apps using nothing more than a publicly visible app_id. The flaw meant that showing up to a locked building and shouting a room number was enough to get the doors open. Wix fixed the vulnerability within 24 hours after Wiz reported it, but the incident exposed how thin the authentication layer is on platforms where millions of apps are being built by users who assume the platform handles security for them.
The pattern is consistent across the vibe coding ecosystem. CVE-2025-48757 documented insufficient or missing Row-Level Security policies in Lovable-generated Supabase projects. Certain queries skipped access checks entirely, exposing data across more than 170 production applications. The AI generated the database layer. It did not generate the security policies that should have restricted who could read the data. Lovable disputes the CVE classification, stating that individual customers accept responsibility for protecting their application data. That dispute itself illustrates the core tension: platforms that market to nontechnical builders are shifting security responsibility to users who do not know it exists.
The RedAccess findings complete the picture. Professional agents face credential theft on one layer. Citizen platforms face data exposure on the other. The structural failure is the same. Security review happens after deployment or not at all. Identity and access management systems track human users and service accounts. They do not track the Lovable app a sales operations analyst deployed last Tuesday, connected to a live CRM database, and shared with three external contractors via a public URL.
Nobody asks whether the database policies restrict who can read the data or whether the API endpoints require authentication. When those questions go unasked at AI-generation speed, the exposure scales faster than any human review process can match. The question for security leaders is not whether vibe-coded apps are inside their perimeter. The question is how many, holding what data, visible to whom. The RedAccess findings suggest the answer, for most organizations, is worse than anyone in the C-suite currently knows. The organizations that start scanning this week will find them. The ones that wait will read about themselves next.


We may receive a commission on purchases made from links.
With gas prices soaring, electric bikes have become a popular alternative for commuting. It’s a great way to reduce road congestion, air pollution, and encourage a healthy lifestyle. However, as e-bikes become more popular, it can be tough to know which one is best for you. Walmart has a huge collection of e-bikes, but one has stood out with a 4.8 out of 5 stars after 1,419 reviews.
The Ancheer Gladiator electric vehicle is on sale for $430 at this time of writing, discounted from its usual $740 MSRP. However, customers feel it’s well worth the money. The 500W motor generates enough power to reach 20 miles per hour and the 48V, 10.4Ah lithium-ion battery offers 60 miles of range. Reviewers say that the battery performs well, with one reporting that their bike had only used about two-thirds of its battery life after a 35 mile trip into the countryside.
With a Shimano 3+7 shock absorption system and both front and rear disc brakes brakes, the Gladiator has capabilities that both city commutes and trail cruisers can appreciate. One reviewer said they bought the Gladiator for hunting, using it to go up and down steep dirt roads. Another added that it’s easy to pedal and that its LCD display is straightforward and easy to understand.
Ancheer squarely markets the Gladiator as a mountain bike, and much of the ad copy on the e-bike’s listing reflects that market segment. The brand mentions using the bike to cruise a mountain and explore new trails thanks to its ability to tackle “extreme conditions.” But how much of this is just PR language and how much is actual capability?
The truth seems to be closer to the latter. Someone who put 300 miles on their Gladiator, including a lot of pretty technical trails, found that the e-bike could really handle anything that was thrown at it without even getting a flat tire. They didn’t go so far as to call it a mountain bike, but they did report that riding it was a fun experience according to their Reddit review.
There are going to be performance limitations when you get an e-bike that is this cost-effective. Multiple reviews on Walmart felt the brakes were nowhere near where they should be. It’s not going to be as capable as more trusted brands focused on off-roading, and that’s reflected in the price difference — Yamaha’s mountain e-bikes cost upward of $6,500. However, SlashGear has previously mentioned the Ancheer Gladiator in our list of e-bikes built for rough terrain since it’s still plenty capable and reliable on easier adventures.

Spotify is leaning even harder into AI, and this time it wants your chatbot to double as a podcast producer.
The streaming service has launched a new beta feature called Save to Spotify. This lets AI agents like OpenClaw, Claude Code and OpenAI Codex generate personalised podcast-style audio briefings directly inside your Spotify library.
The idea is fairly simple: instead of reading through notes, schedules or research documents yourself, you can ask an AI assistant to turn them into an audio episode. You can then listen to it later. Spotify says the feature can handle everything from daily briefings and travel plans to study notes and deep dives into specific topics.
Once generated, the Personal Podcast is saved like a regular episode inside Spotify. It is ready to stream during a commute, workout or wherever else you normally catch up on podcasts.
Getting started is a little more developer-focused than Spotify’s usual features. Users need to install the Save to Spotify CLI tool from GitHub. Then they must connect their Spotify account through a browser login. After that, they prompt their AI agent to create a podcast. Spotify automatically adds the generated episode to the user’s library.
Spotify also shared a few examples of how to use the tool. One suggested prompt creates a five-minute morning briefing using your calendar, inbox and news feeds. Another turns holiday plans into an audio travel itinerary complete with restaurant recommendations and airport routes. You could even ask for a narrated explainer on this year’s World Cup.
The move shows how aggressively Spotify is embedding itself into the AI ecosystem beyond music streaming. The service already integrates with AI assistants like Claude and ChatGPT for playlist controls and recommendations. However, Save to Spotify pushes things much further by treating AI-generated audio as a first-class feature inside the app.
Spotify also quietly confirmed another AI update alongside the launch: users can now interact with the AI DJ in four additional languages beyond English and Spanish.
For now, Save to Spotify remains in beta. However, it’s a pretty clear sign of where Spotify sees the platform heading next — less passive listening, more AI-generated audio built around your own life.

The OnePlus 16 might still be months away, but if the latest rumours are accurate, OnePlus is preparing one of its most over-the-top flagship phones yet.
According to leaks shared by Digital Chat Station, the OnePlus 16 could arrive with a staggering list of specs. These may include a 240Hz display, LPDDR6 RAM, a 200MP zoom camera, and a massive 9,000mAh battery. In addition, Qualcomm’s next-gen Snapdragon 8 Elite Gen 6 Pro chip is also tipped to power the device.
Some of those upgrades make sense. Others feel like OnePlus is simply turning every number up to the maximum.
The jump to a 200MP zoom camera is probably the most believable move here. OnePlus phones have traditionally lagged behind Samsung and Google when it comes to camera consistency, so improving the telephoto hardware would be a logical next step.
The rest of the rumoured spec sheet, though, borders on excessive. A 240Hz refresh rate would comfortably outpace almost every flagship on the market. However, realistically, very few apps or games would fully support it. Even the OnePlus 15’s already-aggressive 165Hz panel felt beyond what most users actually needed.
The same goes for the supposed 9,000mAh battery. That would make it one of the biggest batteries ever fitted into a mainstream smartphone. In fact, it would be nearly double the size of the Galaxy S26 Ultra’s 5,000mAh cell.
What makes these leaks more interesting is the timing. Rumours surrounding OnePlus itself haven’t exactly been calm lately, with reports suggesting Oppo could scale back OnePlus operations in the US; the company has already scaled back operations in the UK and Europe in recent weeks.
Alternatively, they could potentially merge the brand more closely with Realme. Nothing has been confirmed either way, but the uncertainty has been enough to spark questions. People are wondering where OnePlus fits within Oppo’s wider strategy.
That’s partly why the OnePlus 16 rumours feel so aggressive. This doesn’t sound like a company playing it safe. Instead, it sounds like a brand trying to build a headline-grabbing flagship. Their aim is to remind people what made OnePlus exciting in the first place.
There’s also a reason to stay cautious. Digital Chat Station reportedly edited the original leak post to remove some of the speculation, suggesting the details may still be in flux. But even if only half of these rumours prove true, the OnePlus 16 already sounds like it’s aiming to be one of 2026’s most outrageous Android phones.


Security
All your compromised credentials are belong to us now instead of the other gang
There’s a mysterious framework worming its way through exposed cloud instances removing all traces of TeamPCP infections, but it’s not benevolent by a long shot: Whoever is behind this bit of malware may be cleaning up who came before, but only so they can take their place.
Discovered by security outfit SentinelOne’s SentinelLabs researchers and dubbed PCPJack for its habit of stealing previously compromised systems from TeamPCP, the worm was first spotted in late April hiding among a Kubernetes-focused VirusTotal hunting rule. It stood out from known cloud hacktools, said SentinelLabs, because the first action it always takes is to eliminate tools associated with TeamPCP attacks.
The script didn’t stop there, though.
“We initially considered that this toolset could be a researcher removing TeamPCP’s infections,” SentielLabs said. “Analysis of the later-stage payloads indicates otherwise.”
“Analyzing this script led us to discover a full framework dedicated to cloud credential harvesting and propagating onto other systems, both internal and external to the victim’s environment,” SentinelLabs continued. In other words, this thing will harvest credentials from everywhere it can get its hands on, and then find new, unsecured cloud environment targets to spread itself to.
TeamPCP came onto the scene late last year, and since then has made a name for itself primarily by undertaking a successful compromise of the Trivy vulnerability scanner. That act spread credential-harvesting malware which attackers then used to pivot to more valuable targets, and became one of the most notable supply chain attacks in recent memory.
Unlike TeamPCP’s campaign, which relied on the spread of compromised software by human actors, this one spreads on its own accord.
Infections start when already-infected systems look for exposed services, including Docker, Kubernetes, Redis, MongoDB, and RayML, as well as exposed web applications. Once it finds a vulnerable environment, it runs a shell script on the target system that sets up an environment to download additional payloads and searches for TeamPCP processes and artifacts to kill.
That part of the infection downloads the worm itself, along with modules to enable lateral movement, parse credentials and encrypt them for exfiltration, and for scanning the web for new environments to infect.
From there, the worm goes to work with the second module in its kit that conducts the actual credential thefts. This portion of the infection targets environment variables, config files, SSH keys, Docker secrets, Kubernetes tokens, and credentials from a list of finance, enterprise, messaging, and cloud service targets so long that we recommend taking a look at it here, or just assuming whatever you’re using is probably being targeted.
SentinelLabs noted that the lack of a cryptominer in the malware package is unusual, and said the particular services it targeted suggests its goal is either conduct its own spam campaigns and financial fraud with the stolen data, or to make the data it harvests available to those planning similar crimes.
The worm’s practice of removing TeamPCP files could be opportunistic, or could mean there’s drama going on in the cybercrime world.
“We have no evidence to suggest whether this toolset represents someone associated with the group or familiar with their activities,” SentinelLabs noted. “However, the first toolset’s focus on disabling and replacing TeamPCP’s services implies a direct focus on the threat actor’s activities rather than pure cloud attack opportunism.”
Because this is a worm relying on unsecured cloud and web app instances ripe for targeting, mitigation recommendations are pretty simple: Keep your cloud platforms secure, and ensure authentication is required even for instances of things like Docker and Kubernetes that aren’t exposed to the internet. ®

![]()
Hackers give operator Instructure until 12 May to ‘negotiate a settlement’.
Cyber extortion group ShinyHunters has claimed responsibility for a second breach into edtech giant Instructure – this time, for hacking into the Canvas login portal.
The hackers replaced the Canvas login page with a message that claimed responsibility for an earlier Instructure breach and threatened to leak stolen data if ransom demands aren’t met.
“ShinyHunters has breached Instructure (again). Instead of contacting us to resolve it they ignored us and did some ‘security patches’,” the message seen by news publications read.
“If any of the schools in the affected list are interested in preventing the release of their data, please consult with a cyber advisory firm and contact us privately at TOX to negotiate a settlement. You have till the end of the day by May 12 2026 before everything is leaked,” it continued.
Bleeping Computer reported that the threat actors’ message appeared in around 330 educational institutions’ portals. It was up for approximately 30 minutes before being taken down. ShinyHunters told the publication that the stolen data contains private messages, user records and enrolment data.
Canvas is used by more than 8,000 educational institutions globally, including several in Ireland, such as the University of Galway and Munster Technological University (MTU). The platform enables communication between students and faculty, and provides coursework management and grading services.
Earlier this week, MTU informed users of a cybersecurity breach into Instructure, which it believed, at the time, did not affect its services. Yesterday (7 May), the institution advised caution, and told staff and students that Canvas remains safe to use.
Meanwhile, in a statement to SiliconRepublic.com, the University of Galway said: “Services have been restored following a relatively low level of disruption in the last 24 hours. We are continuing to liaise with the company affected to understand the full nature and extent of the breach.”
According to the company’s status page, Instructure first began experiencing issues at around 6.30pm Irish Standard Time yesterday. At the time of publication, the services are back online for “most users”.
Last Friday (1 May), Instructure disclosed that it experienced a cybersecurity incident perpetrated by a criminal threat actor. ShinyHunters claimed responsibility for the attack and claimed to have stolen 280m records. The threat actor also published a list of more than 8,800 institutions that were affected by its attacks on Canvas.
On 6 May, Instructure said the stolen information includes “certain identifying information of users at affected institutions, such as names, email addresses and student ID numbers, as well as as messages among users”.
In March, ShinyHunters was linked to a breach of the European Commission’s Europa.eu platform, where 350GB of data, across multiple databases, was reportedly accessed and stolen.
Don’t miss out on the knowledge you need to succeed. Sign up for the Daily Brief, Silicon Republic’s digest of need-to-know sci-tech news.
Updated 8 May, 12.34 pm: The article has been updated with a statement from the University of Galway.


Channel 5 – All Creatures Great and Small series 7 new post


HarrisX Poll Found 52% of Registered Voters Support the CLARITY Act


Upbit adds B3 Korean won pair as Base token gains Korea access
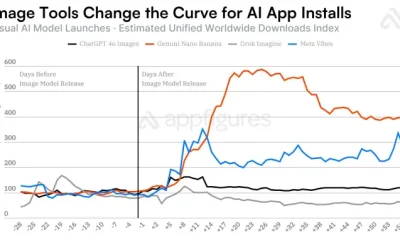

Image AI models now drive app growth, beating chatbot upgrades

NCP car park operator enters administration putting 340 UK sites at risk of closure


Kylie Jenner Hit With Second Lawsuit From Ex-Housekeeper


Cavaliers vs. Raptors Game 6 live score, updates, highlights from 2026 NBA playoffs first-round series


Young and the Restless Next Week: Cane Arrested & Matt’s Deadly New Scheme!
New Netflix Movies in May 2026 — My Top 3 Picks to Stream


Melissa Joan Hart and More Stars Attend 2026 Kentucky Derby

David Benavidez responds to team Canelo saying the fight will never happen

IPL 2026: ‘Love you darling’- Hardik Pandya’s reaction to MS Dhoni steals the show |Watch | Cricket News


Five killed in Texas plane crash identified as Amarillo pickleball players
Anna Nicole Smith’s Daughter Attends 2026 Kentucky Derby


Pi Network Mandates Protocol 23 Upgrade for All Mainnet Nodes Before May 15 Deadline


Bitcoin mining equities rise in 2026 as BTC lags behind


Luka Doncic Injury Update: Doncic’s Hamstring Recovery Slows Lakers’ Hopes Against Thunder: Can He Run Yet?


Can Victor Wembanyama Bring the NBA Ring to Spurs in 2026? Historic Playoff Run Fuels Title Dreams


Plane crash in Wimberley, Texas kills 5 pickleball players at tournament


Venus Williams’ Best Met Gala Looks Over the Years
You must be logged in to post a comment Login