Crypto World
Goldman Sachs files for Bitcoin Premium Income ETF


Goldman Sachs has filed for a Bitcoin Premium Income ETF that aims to turn BTC’s volatility into yield via a covered‑call strategy built on spot ETF exposure.
Summary
- Goldman Sachs files with the SEC for a Bitcoin Premium Income ETF.info.
- The fund aims to generate yield from Bitcoin using a covered call strategy.news.
- Filing underscores Wall Street’s shift toward structured Bitcoin income products.
Goldman Sachs has filed a registration statement with the U.S. Securities and Exchange Commission (SEC) to launch a Bitcoin Premium Income exchange‑traded fund, marking one of the 157‑year‑old investment bank’s most direct moves into crypto to date.
According to the preliminary prospectus, the Goldman Sachs Bitcoin Premium Income ETF is designed to provide “current income with a secondary objective of capital appreciation,” giving investors Bitcoin exposure while generating additional yield through options.
The filing, made under the Goldman Sachs ETF Trust on April 14, 2026, proposes that the offering become effective 75 days after submission, which would put the earliest potential launch in late June or early July if regulators sign off.
Goldman Sachs will not hold Bitcoin directly in the new fund but will instead gain exposure through shares of spot Bitcoin ETFs and related instruments, mirroring structures used by rivals such as the iShares Bitcoin Premium Income ETF.
As explained in a breakdown by Arkham Research, a Bitcoin covered‑call ETF “is designed to transform Bitcoin from a passive asset into an income‑generating asset” by holding BTC exposure and then selling call options on that position to collect premiums.
Goldman’s registration statement says the fund will “sell call options generally representing 40% to 100% of the Fund’s exposure to Bitcoin,” a range that caps upside during sharp rallies but allows the ETF to harvest option income in sideways or modestly trending markets.
The proposal comes after the bank quietly ramped up its Bitcoin exposure via existing spot products, with earlier SEC filings showing Goldman holding roughly $1.27 billion of the iShares Bitcoin Trust ETF, an 88% increase on the previous quarter, according to TheStreet.
Industry outlets note that the move aligns Goldman with a broader Wall Street rush into yield‑enhanced Bitcoin vehicles, following similar covered‑call or premium income products from BlackRock and other issuers looking to monetise Bitcoin’s volatility for income‑focused clients.
Bitcoin‑linked structured products and ETFs have already been a recurring theme in crypto.news coverage of the spot ETF trade, with previous story pieces tracking how inflows into BTC funds and their derivatives have influenced the Bitcoin price, options skew and liquidity across major venues.
Investors tracking the implications of Goldman’s ETF filing on the underlying asset can monitor real‑time moves on the Bitcoin market‑cap page, alongside comparable data for Ethereum and other major tokens on their respective price pages as institutional product design around BTC continues to evolve.
Crypto World
CoW Swap users warned after Blockaid flags COW.FI frontend attack


Blockaid flags CoW Swap’s cow.fi frontend as malicious, urging users to revoke token approvals and avoid the dApp amid a broader wave of DeFi interface attacks.
Summary
- Blockaid flags CoW Swap’s main cow.fi frontend as malicious.
- Users are urged to revoke token approvals and avoid the dApp immediately.
- Incident highlights growing wave of DeFi frontend attacks across major protocols.
Blockchain security firm Blockaid has warned that CoW Swap’s primary website COW.FI has been compromised in a suspected frontend attack, marking the latest high‑profile exploit attempt against a major DeFi trading interface.
In an alert shared on X, Blockaid said its system “has detected a front-end attack targeting Cowswap” and confirmed that the cow.fi domain has been flagged as malicious inside Blockaid‑integrated wallets, advising users “to refrain from signing transactions and avoid interactions with the dApp until the issue is resolved.”
Following the warning, CoW Swap community channels and independent security commentators urged traders who had connected wallets to CoW Swap to immediately revoke any outstanding token approvals and to stop interacting with the platform’s frontend until further notice, even though underlying smart contracts have not been reported as compromised.
Blockaid’s latest alert comes amid a surge in so‑called frontend hijacks, where attackers compromise a project’s website or DNS rather than its on‑chain contracts, silently swapping legitimate transaction prompts for malicious ones that drain user wallets.linkedin+1
In February, Blockaid reported a similar frontend attack on tokenization platform OpenEden, warning users to “refrain from signing transactions and avoid interactions with the dApp until the issue is resolved,” while separate incidents have recently hit lending protocol Curvance and asset manager Maple Finance.
As highlighted in CoW Swap’s own DeFi security guides, these attacks target “people, devices, and transaction behavior instead of only attacking code,” making basic hygiene like checking URLs, using browser bookmarks and monitoring token approvals critical for retail and professional users alike.
Security platforms such as Kerberus and Revoke‑style tools recommend users regularly audit and revoke token approvals after any suspected incident, noting that revocation “only removes future permission for that contract to move your tokens” and cannot recover funds already drained.
For DeFi traders, the CoW Swap incident underscores a lesson that keeps recurring in crypto.news coverage of exchange exploits, bridge hacks and protocol drains: even when audited smart contracts remain intact, a single compromised frontend can still turn a routine swap into a total wallet loss if users sign blind.
Crypto World
Tether Introduces Multichain Self-Custodial Wallet

Self-custodial wallet tether.wallet supports Bitcoin, USDT, USAT and XAUT across multiple blockchains at launch.
Tether today unveiled its self-custodial crypto wallet using the open-source Wallet Development Kit (WDK) developed by the firm. According to an announcement from the firm, tether.wallet supports USDT, USAT, Bitcoin and XAUT, what the firm says represent “the only assets that truly matter for most of the people.”
Tether says the initiative, which it’s dubbing “the People’s Wallet” aligns with its mission to promote financial inclusion globally, particularly in developing countries and regions with high inflation.
Tether CEO Paolo Ardoino was quoted in the announcement on the firm’s aim of preserving self-custody, without compromising on user experience:
“The objective is to remove the complexity that has prevented broader adoption while preserving the properties that make the digital assets technology valuable. Users should be able to send value as easily as sending a message, without relying on intermediaries and without giving up control of their assets.”
As an example, the firm’s announcement notes that the wallet lets users pay fees in the asset being transferred, instead of needing to acquire or hold separate tokens for gas. The wallet also supports easily readable addresses for sending and receiving that look more like an email address, instead of the typical alphanumeric string.
Tether says at launch, the wallet supports USDT and XAUT on Ethereum, Polygon, Plasma, and Arbitrum, and USAT on Ethereum. It also supports Bitcoin both natively and via the Lightning Network. The firm plans to add support for “several other blockchains” in the future.
Last month, Tether announced that it had engaged a Big Four firm to conduct its first ever “full independent financial statement audit.”
This article was written with the assistance of AI workflows. All our stories are curated, edited and fact-checked by a human.
Crypto World
North Korea Used AI to Hack Zerion in Second Crypto Attack
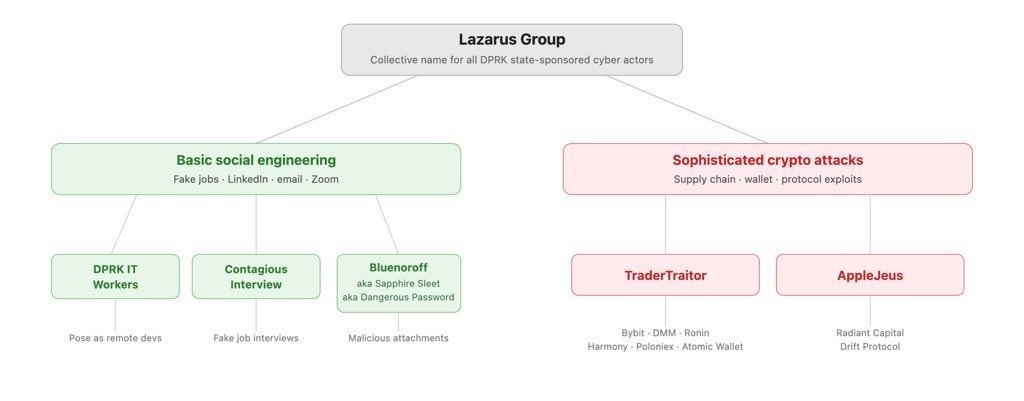
Crypto wallet Zerion revealed that North Korean-affiliated hackers used AI in a long-term social engineering attack to steal about $100,000 from the company’s hot wallets last week.
The Zerion team released a post-mortem on Wednesday, where it confirmed that no user funds, Zerion apps or infrastructure were affected and that it had proactively disabled the web app as a precaution.
While the amount was relatively small in crypto hacking terms, it is another incident of a crypto worker being targeted for an “AI-enabled social engineering attack linked to a DPRK threat actor,” Zerion said.
It is the second attack of this nature this month, following the $280 million exploit of the Drift Protocol, which was the victim of a “structured intelligence operation” by DPRK-affiliated hackers. The human layer, not smart contract bugs, has now become North Korea’s primary point of entry into crypto firms.
AI is changing the way cyber threats work
Zerion said the attacker gained access to some team members’ logged-in sessions and credentials, as well as private keys to company hot wallets.
“This incident showed that AI is changing the way cyber threats work,” the company said.
It confirmed that the attack was similar to those that had been investigated by the Security Alliance (SEAL) last week.
Related: Researchers discover malicious AI agent routers that can steal crypto
SEAL reported that it had tracked and blocked 164 domains linked to the DPRK group UNC1069 in a two-month window from February to April.
It stated that the group operates “multiweek, low-pressure social engineering campaigns” across Telegram, LinkedIn and Slack. Malicious actors impersonate known contacts or credible brands or leverage access to previously compromised company and individual accounts.
“UNC1069’s social engineering methodology is defined by patience, precision, and the deliberate weaponization of existing trust relationships.”
Google’s cybersecurity unit Mandiant detailed in February the group’s use of fake Zoom meetings and a “known use of AI tools by the threat actor for editing images or videos during the social engineering stage.”
DPRK’s social engineering is evolving
Earlier this month, MetaMask developer and security researcher Taylor Monahan said North Korean IT workers have been embedding themselves in crypto companies and decentralized finance projects for at least seven years.
“The evolution of the DPRK’s social engineering techniques, combined with the increasing availability of AI to refine and perfect these methods, means the threat extends well beyond exchanges,” blockchain security firm Elliptic said in a blog post earlier this year.
“Individual developers, project contributors, and anyone with access to cryptoasset infrastructure is a potential target.”

Magazine: How AI just dramatically sped up the quantum risk for Bitcoin
Crypto World
Bitmine sits on $10 billion ETH but books $3.6 billion loss
Bitmine Immersion Technologies has turned itself into the Ethereum version of Strategy, doubling its outstanding shares in six months and raising over $10 billion in equity to amass nearly 5% of all ether in existence.
it reported a $3.8 billion quarterly net loss in Tuesday’s 10-Q filing, with share count going from 232 million to 494 million between August 31 and February 28.
Additional paid-in capital jumped from $8.36 billion to $18.55 billion over the same period, and those funds went straight into ETH.
As of April 12, Bitmine held 4.87 million ether at an average cost of $2,206 per token, making it the largest corporate Ethereum treasury globally and the second-largest corporate crypto treasury behind Strategy.
The bet is underwater but not by much. Ether traded near $2,325 on Wednesday, roughly 5% above Bitmine’s average entry. The $3.78 billion in unrealized losses on the quarter’s income statement reflects the drawdown from the token’s August 2025 highs near $4,900, not a loss from its cost basis.
Under fair-value accounting rules adopted in 2024, those mark-to-market swings flow through the P&L regardless of whether the company has sold anything.
But the transformation from mining company to leveraged ETH treasury play is creating its own set of pressures.
Self-mining revenue collapsed 86% year-over-year to $219,000 for the quarter. Staking has replaced it entirely, generating $10.2 million of the company’s $11 million in total quarterly revenue.
General and administrative expenses hit $75 million for the quarter, up from $964,000 a year earlier. For the full six-month period, G&A reached $298.6 million against just $13.3 million in revenue. Some of that likely reflects stock-based compensation tied to the equity raises, but the gap between operating costs and operating revenue is stark for a company whose core product is now holding and staking a single token.
The filing also reveals derivatives exposure that wasn’t previously detailed.
Bitmine booked $65.3 million in unrealized losses on derivatives and $24.1 million in option premium income during the quarter, suggesting the company is running options strategies on its ETH holdings, possibly covered calls to generate additional yield.
Chairman Tom Lee said in March that the company views the ether pullback as “attractive, given the strengthening fundamentals,” and noted Monday that Bitmine has accelerated its buying pace over the past four weeks.
Bitmine held $879.6 million in cash as of February 28, along with 198 bitcoin, a $200 million stake in Beast Industries, and an $85 million position in Eightco Holdings.
Crypto World
Crypto Valley Captured 47% of Europe’s Blockchain Funding in 2025
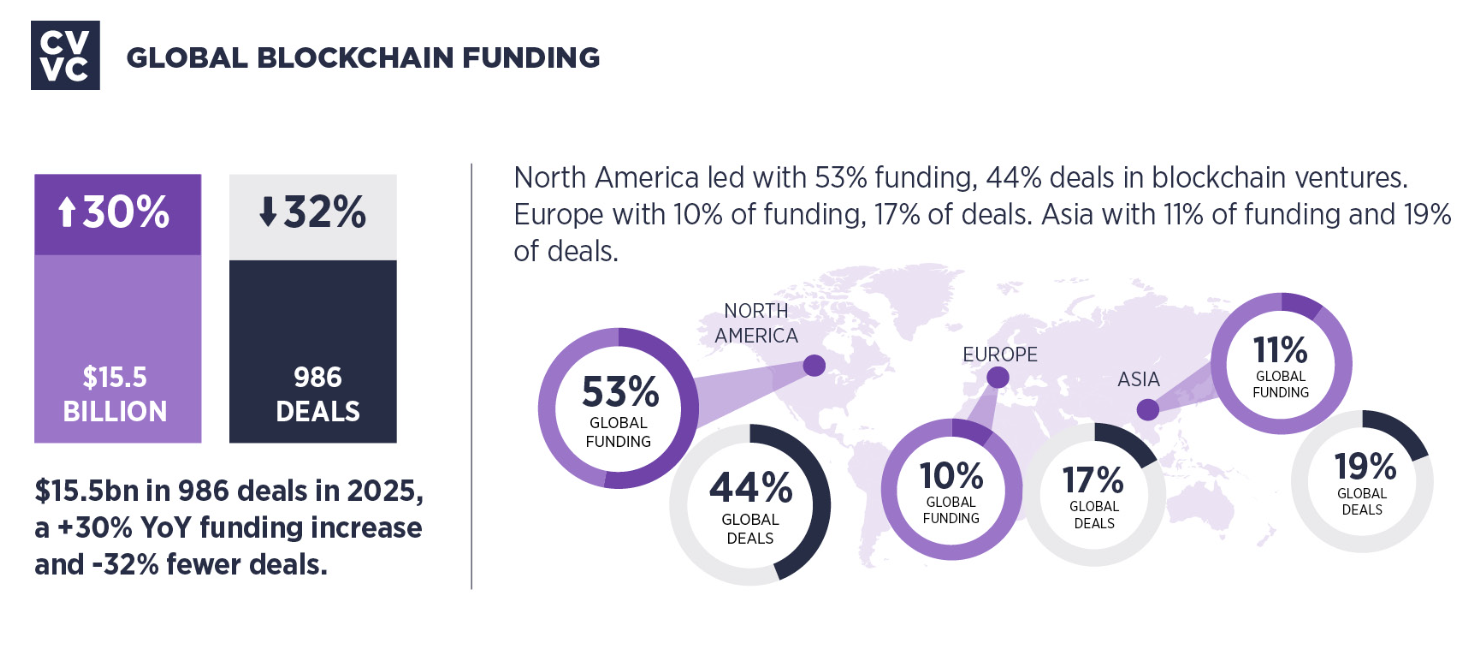
Switzerland’s Crypto Valley captured 47% of European blockchain venture funding in 2025, raising $728 million across 31 deals, according to an annual report released Wednesday by venture firm CV VC.
Globally, blockchain venture funding rose 30% to $15.5 billion across 986 deals last year, while Crypto Valley’s total climbed 37% from $531 million in 2024, the report said.
One deal did much of the heavy lifting. The Open Network (TON) accounted for $400 million of Crypto Valley’s 2025 funding haul, followed by Sygnum Bank at $58 million, stablecoin platform M0 at $40 million, Impossible Cloud Network at $34 million and CratD2C at $30 million, according to the report.
The figures suggest Switzerland remains Europe’s main blockchain funding hub, but they also show capital concentrating into fewer, larger rounds.

Blockchain networks attracted 62% of total funding, followed by infrastructure at 14%, centralized financial services at 10% and decentralized finance applications at 10%, the report said.

Crypto Valley took 47% of Europe’s funding
Crypto Valley’s $728 million accounted for 47% of the total VC blockchain funding across Europe and 5% of the global blockchain funding in 2025, highlighting the Swiss blockchain ecosystem’s growing role in the European blockchain industry.
“Nearly half of all European blockchain investment is now flowing into Crypto Valley,” said Mathias Ruch, founder and CEO of Crypto Valley, calling it a sign of a “maturing ecosystem” focused on infrastructure, finance and the convergence of “frontier technologies” driving digital innovation.
Still, the report’s own numbers show that growth came alongside a more selective market, with deal count falling even as capital deployed increased. That pattern was visible globally as well. CV VC said worldwide blockchain venture funding rose even as deal volume fell 32%, showing a shift toward fewer but larger transactions.
In Crypto Valley, the same dynamic helped push annual funding totals higher, even as the ecosystem’s headline valuation and unicorn count moved lower.

Crypto Valley now hosts 1,766 active blockchain companies, up 134% since 2020, according to CV VC. Companies based in Zug, Switzerland, accounted for 20 of the 31 total deals and 88% of disclosed capital, while Zurich-based companies followed with five deals.
Related: Cardano can now be used to pay at 137 Spar stores across Switzerland
The report also said Crypto Valley’s number of unicorns fell to 10 in 2025 from 17 a year earlier. Ethereum, Solana, Cardano, Hedera, Toncoin, Polkadot, Near Protocol, Internet Computer, Copper and Sygnum Bank now rank as the region’s top crypto companies.
A Crypto Valley spokesperson attributed the decline largely to weaker market conditions late in the year, which pushed six token projects below the $1 billion threshold. The spokesperson also said 21Shares left the ecosystem after its acquisition by FalconX.
Magazine: How crypto laws changed in 2025 — and how they’ll change in 2026
Crypto World
Morpho Unveils Fixed-Rate Protocol Morpho Midnight


Morpho is the second-largest lending protocol in DeFi, with $7.7B in TVL.
Morpho, DeFi’s second-largest lending protocol by value locked, has officially named its long-in-development fixed-rate product: Morpho Midnight.
Co-founder and CEO Paul Frambot announced the name on X today, April 14, emphasizing that Midnight is not a sequel to Morpho Blue. “It is a completely new paradigm for onchain lending, and should not be considered a ‘V2’ of Blue,” Frambot wrote.
The distinction is structural, according to Frambot’s X post. Morpho Blue offers pool-based, open-term variable-rate markets with externalized risk management. Midnight introduces intent-based, fixed-term, fixed-rate markets with externalized management of both risk as well as rate, a different mechanism for pricing and matching lenders and borrowers.
The two protocols will coexist and complement each other within the broader Morpho network, per the X post. Frambot first flagged the naming overhaul of Morpho’s fixed rate market in early March, when he dropped versioning terminology (Markets V1/V2) in favor of distinct brand identities for each product.
Frambot added in today’s announcement that more details on Midnight are expected as security audits finalize.
Morpho currently holds approximately $7.7 billion in total value locked, per data from DefiLlama, making it the second-largest lending protocol in DeFi, following Aave with $26.3 billion in TVL.
Last June, The Defiant reported on Morpho’s V2 launch, which introduced fixed-rate and fixed-term loans, with the aim to bring DeFi lending closer to traditional finance structures, which Midnight now builds on.
Last month, the Ethereum Foundation made its second deployment into Morpho Vaults, bringing its total commitment to nearly $19 million and citing the protocol’s immutable, open-source architecture as a model for cypherpunk-aligned DeFi infrastructure.
This article was written with the assistance of AI workflows. All our stories are curated, edited and fact-checked by a human.
Crypto World
Ethereum price opens 8% higher at $2,370


The Ethereum price jumped 8 percent to $2,370 Tuesday morning as Trump’s signals about potential Iran peace talks triggered a broad risk-on rally across crypto markets, with bitcoin touching $74,900 and the total crypto market cap approaching $2.6 trillion.
Summary
- Bloomberg data confirmed Ether rose 5 percent alongside bitcoin’s move to $74,400, with the synchronized gains across BTC, ETH, and XRP signaling genuine risk appetite returning to the asset class rather than a bitcoin-only safe-haven move.
- Ethereum is trading approximately 52 percent below its August 2025 all-time high of $4,953 and has faced sustained ETF outflows, with Ethereum investment products recording $129 million in net outflows on April 11 even as XRP pulled in $119.6 million.
- Standard Chartered maintains a long-term $15,000 price target for Ethereum, while Arthur Hayes has projected a $10,000 to $20,000 range, though both scenarios depend on macro conditions and regulatory clarity that the current Iran war environment has substantially delayed.
Yahoo Finance data shows Ethereum opened Monday at $2,191 and fell 4.1 percent from Sunday’s open as the naval blockade went live. Tuesday’s 8 percent reversal at the open demonstrates how directly Iran war headlines are driving Ether’s price action in the absence of a crypto-specific catalyst. The CLARITY Act markup window opening this week is the first regulatory catalyst Ethereum has had since the ceasefire rally, and passage of the bill would formalize Ethereum’s digital commodity classification under federal law for the first time.
When bitcoin rallies alone, it typically reflects either a bitcoin-specific catalyst or safe-haven rotation within crypto. When Ethereum rises 8 percent on the same day, it reflects a broader improvement in risk appetite across the asset class. Tuesday’s move included XRP gains, altcoin recovery, and total market cap approaching $2.6 trillion, meaning the Iran peace signal triggered a system-wide repricing rather than a single-asset move. That distinction matters because system-wide rallies have historically been more durable than single-asset moves driven by short squeezes.
What the ETF Outflow Divergence Means
XRP pulled in $119.6 million in weekly ETF inflows while Ethereum recorded $129 million in outflows on a single day. That divergence is striking and reflects different institutional narratives. XRP is being accumulated ahead of expected CLARITY Act clarity that would cement its digital commodity status. Ethereum’s ETF flows reflect institutional uncertainty about its regulatory classification and concerns about its economic model relative to bitcoin. The Ethereum Foundation completed a $143 million staking commitment in the same week as the ETF outflows, showing that on-chain conviction and product flows are telling different stories.
What Ethereum Needs to Sustain This Move
The price needs three inputs to sustain above $2,370: a credible Iran diplomatic development before April 22, a CLARITY Act markup announcement from the Senate Banking Committee, and continued bitcoin strength above $74,000. Without all three, the most likely outcome is a fade back toward the $2,150 to $2,200 range where Ethereum has consolidated for most of the Iran war period.
Crypto World
Bitcoin’s ‘your keys, your coins’ promise just got an expiry date from a new developer proposal


Bitcoin was built on a promise that no one can touch your coins without your private key. No government, no bank, nobody.
That promise is now, for the first time in Bitcoin’s 16-year history, being challenged from the developer community itself, as a part of measures to build defenses against future quantum computers that could compromise Bitcoin’s blockchain and steal your coins.
The proposal
Jameson Loop, one of the outspoken bitcoin contributors, and other cryptographers, have proposed a move that could force bitcoin holders to migrate their coins to new quantum-resistant addresses or face having their coins frozen permanently by the network itself. In that scenario, holders would technically still “own” the coins, but lose the ability to move them.
It is called Bitcoin Improvement Proposal (BIP)-361 and was updated in Bitcoin’s official proposal repository Tuesday with the title “Post Quantum Migration and Legacy Signature Sunset.”
This comes as a recently released Google report warned that a sufficiently powerful quantum machine could require significantly less firepower to compromise the Bitcoin blockchain than initially estimated. This prompted some observers to cite 2029 as the quantum deadline for bitcoin.
To understand the need to freeze coins, you need to know what it is protecting against.
Every Bitcoin wallet is secured by a form of cryptography called ECDSA, or Elliptic Curve Digital Signature algorithm. Think of it as a lock on your wallet. When you set up a wallet, two keys are generated: Private key, which is a unique password used to prove that you own the coins you are spending. Then there is a public key derived from the private key. This public key helps receive funds, verify transaction signatures, and ensure security without revealing the owner’s private key.
Here is the problem: your public key is revealed on the blockchain, permanently for anyone to see when you send funds. A sufficiently powerful quantum machine can use it to reverse engineer your private key and drain your funds.
As of March, the sum of all BTC in vulnerable addresses was approximately 6.7 million BTC, according to the Google study.
BIP-361 builds on the proposal put forward in February under BIP-360, which introduced a soft fork—a network upgrade—designed to enable a new transaction type called pay-to-Merkle-root (P2MR). The approach borrows from Bitcoin’s Taproot (P2TR) framework, but strips out the key-based spending path, removing an element widely viewed as exposed to potential quantum-era risks.
Three phases
The BIP 361 proposal structures the migration in three phases. The Phase A kicks in three years after potential activation, blocking anyone from sending new bitcoin to old-style, quantum-vulnerable addresses. You can still spend from these addresses, but cannot receive anything.
The Phase B, to kick in five years after activation, will render old style signatures (ECDSA and Schnorr) completely invalid such that attempts to spend from quantum-vulnerable wallets will be rejected by the network. In essence, your coins will be frozen.
Finally, Phase C, is a proposed rescue, still under research, where holder with frozen wallets could potentially prove ownership using a zero-knowledge proof, a way of proving the knowledge of a secret without revealing the secret itself. If it works, coins frozen by Phase B could be recovered.
Community backlash
The idea of freezing coins as a defense against quantum threats cuts directly against one of Bitcoin’s most fundamental promises: sovereign, permissionless control over funds.
At its core, Bitcoin is designed to ensure that whoever holds the private keys controls the coins – without exception. Introducing a mechanism that allows coins to be frozen, even under extraordinary circumstances like a quantum attack, implies that this principle can be overridden.
The community, therefore, is not happy with the proposal.
“This quantum proposal is highly authoritarian and confiscatory, but of course, it’s from Lopp. There is no good rationale for forcing the upgrade and rendering old spends invalid. Upgrade should be 100% voluntary,” one X user said.
“This reeks of central planning with the deadlines, behavior coercion, and forced migration,” another user said.
Developers, however, called it a defensive measure.
“This is not an offensive attack, rather, it is defensive: our thesis is that the Bitcoin ecosystem wishes to defend itself and its interests against those who would prefer to do nothing and allow a malicious actor to destroy both value and trust,” they said.
Crypto World
Tether Launches Wallet Supporting Bitcoin and Stablecoins

Tether, the company behind the world’s largest stablecoin, USDt (USDT), has launched a self-custodial wallet called tether.wallet.
Tether.wallet supports three Tether-issued assets: USDT, XAUt (XAUT) and the US-focused USAT (USAT), as well as Bitcoin (BTC), the company announced Tuesday.
Tether said the wallet allows users to transact without requiring them to hold separate network or gas tokens, with fees paid directly in the asset being transferred.
The wallet also uses human-readable @tether.me usernames, aimed at eliminating the need to interact with long wallet addresses. With some commentators highlighting the potentially “centralized” nature of such identifiers, it remains unclear whether they introduce any friction in terms of self-custody or security.
The launch marks Tether’s clearest push yet into direct consumer wallet distribution, packaging stablecoin and Bitcoin payments in a simpler interface while testing how much convenience users will accept inside a product marketed as self-custodial. The wallet builds on the work the company began when it launched its open-source Wallet Development Kit in late 2024. The WDK was designed to enable developers to integrate non-custodial wallets for USDT and BTC into any app, website or device.
Cointelegraph reached out to Tether for comment but had not received a response by publication.
The app is fully self-custodial by design, Tether says
The wallet is immediately available for download on mobile devices, with the website inviting users to install iOS or Android versions at launch.
“The application is fully self-custodial by design,” Tether said in the announcement, noting that all transactions are signed locally on the user’s device before being broadcast to the network.

“Private keys and recovery phrases are always in sole control of the user,” the company said, adding that the wallet’s self-custodial design aligns with Tether’s core principle of making financial systems “open, neutral, accessible, and in control of the user.”
“With more than 570 million people already using Tether’s technology, the next step is making that digital infrastructure more accessible and usable for end users,” Tether CEO Paolo Ardoino said, adding that the objective is to remove wallet complexities that have prevented broader adoption.
Related: Tether may delay fundraising if demand falls short at $500B valuation: Report
Private keys “safely backed to cloud”
At launch, the wallet supports USDT and XAUT on Ethereum, Polygon, Plasma and Arbitrum, while USAT is initially available exclusively on Ethereum. Bitcoin is supported both onchain and via the Lightning Network.
According to an X post by tether.wallet, the newly launched wallet allows users to control their private keys and “safely back up” to the cloud.

It’s unclear whether users can disable cloud-based private key backups. Cointelegraph will update the article pending Tether’s response.
Some users have opposed similar cloud-based key recovery solutions in the past, including on hardware wallets such as Ledger.
Magazine: Nobody knows if quantum secure cryptography will even work
Crypto World
Ethereum open interest jumps 11.6% as leverage piles into ETH

ETH derivatives open interest jumps 11.59% in 24 hours to $34.165B, with Binance, Gate, Bybit and OKX carrying most of the leverage as traders pile into Ethereum.
Summary
- ETH total derivatives open interest jumps 11.59% in 24 hours to $34.165 billion.
- Binance leads with $7.416 billion in ETH OI, followed by Gate, Bybit and OKX.
- Surge echoes March’s leveraged build‑up that pushed ETH OI above $30 billion.
Ethereum’s derivatives market has lit up again, with total ETH contract open interest jumping 11.59% in the past 24 hours to $34.165 billion as traders add fresh leverage across major venues.
According to Coinglass data, Binance accounts for roughly $7.416 billion of that exposure, while OKX holds $1.943 billion, Bybit $2.331 billion and Gate $4.36 billion, underscoring how concentrated ETH risk remains on a handful of centralized exchanges.
The move comes as ETH trades above $2,300, extending a derivatives‑driven upswing that previously saw open interest climb about 9% in a day to more than $30 billion in March, as detailed in a crypto.news story on Ethereum’s earlier leverage spike.
Derivatives tracker Coinglass, which aggregates futures and perpetual positions across venues, shows ETH open interest rising from around $30.6 billion to $34.165 billion over 24 hours, indicating a sharp increase in capital betting on Ethereum’s next leg.
In March, open interest swelled by nearly 9% in a day to roughly $30.4 billion as ETH climbed above $2,180, with Binance, Gate, Bybit and OKX holding most of the risk and raising “spillover” concerns if one venue suffered a squeeze or outage, according to a previous crypto.news story.
More recently, Ethereum derivatives open interest has also shown its capacity to move in reverse, dropping 5.62% in one 24‑hour window to $27.119 billion during a leverage flush that forced traders to close or liquidate positions, as covered in another crypto.news story on ETH risk reduction.
The latest 11.59% jump suggests traders are once again crowding into ETH futures, a pattern that can amplify both rallies and drawdowns when funding turns or liquidations cascade through the order books.
At the same time, exchange‑level data shows Binance, OKX, Bybit and Gate continuing to dominate crypto derivatives, with Binance and OKX controlling a combined 53.3% of global derivatives market share and Gate ranking third by open interest at $8.68 billion across assets, according to recent derivatives statistics.
As Ethereum’s leverage build‑up accelerates, traders watching ETH’s spot price on the Ethereum market‑cap page, as well as Bitcoin and other majors on their respective price pages, will be gauging whether the derivatives market is setting up a sustainable grind higher or yet another sharp liquidations event.
-

 Politics5 days ago
Politics5 days agoUS brings back mandatory military draft registration
-

 Sports5 days ago
Sports5 days agoMan United discover Nico Schlotterbeck transfer fee as defender reaches Dortmund agreement
-

 Fashion5 days ago
Fashion5 days agoWeekend Open Thread: Veronica Beard
-
 Politics5 days ago
Politics5 days agoMalcolm In The Middle OG Turned Down ‘Buckets Of Money’ To Appear In Reboot
-

 Politics3 days ago
Politics3 days agoWorld Cup exit makes Italy enter crisis mode
-

 Crypto World6 days ago
Crypto World6 days agoCanary Capital Files SEC Registration for PEPE ETF
-

 Business4 days ago
Business4 days agoTesla Model Y Tops China Auto Sales in March 2026 With 39,827 Registrations, Beating Cheaper EVs and Gas Cars
-

 Crypto World2 days ago
Crypto World2 days agoThe SEC Conditionalises DeFi Platforms to Be Avoided for Broker Registration
-

 Crypto World1 day ago
Crypto World1 day agoSEC Signals Exemption for Crypto Interfaces From Broker Registration
-

 Crypto World7 days ago
Crypto World7 days agoBitcoin recovers as US and Iran Agree a Ceasefire Deal
-

 NewsBeat2 days ago
NewsBeat2 days agoPep Guardiola and Gary Neville agree over Arsenal title problem that benefits Man City
-

 Business5 days ago
Business5 days agoOpenAI Halts Stargate UK Data Centre Project Over Energy Costs and Copyright Row
-

 Business4 days ago
Business4 days agoIreland Fuel Protests Enter Day 5 as Blockades Spark Shortages and Government Prepares Support Package
-

 Politics5 days ago
Politics5 days agoLBC Presenter Mocks Trump Over Iran War Failures
-

 Crypto World4 days ago
Crypto World4 days agoFederal judge blocks Arizona from bringing criminal charges against Kalshi
-

 NewsBeat3 days ago
NewsBeat3 days agoJD Vance announces ‘no agreement’ with Iran over nuclear weapons fear
-
 Tech5 days ago
Tech5 days agoA version of Windows 10 released a decade ago is now eligible for additional security patches
-
 Crypto World1 day ago
Crypto World1 day agoSEC Proposes Certain Crypto Interfaces Don’t Need to Register as Brokers
-
 Business4 days ago
Business4 days agoIMF retains floor for precautionary balances at SDR 20 billion
-

 NewsBeat21 hours ago
NewsBeat21 hours agoTrump and Pope Leo: Behind their disagreement over Iran war











You must be logged in to post a comment Login