Crypto World
Saylor’s Strategy Spends Over $200 Million to Acquire 3,015 BTC: Details


Some of the comments below the company’s post said this purchase shows “conviction, not hesitation.”
After hinting about another purchase on Sunday, Strategy’s co-founder and former CEO, Michael Saylor, has made it official, indicating that his firm has splashed $204.1 million to acqure additional 3,015 BTC.
The average cost for the latest transaction was $67,700, and the company’s stash has grown to 720,737 BTC. It was purchased at an average price of just under $76,000, which means that the NASDAQ-listed firm continues to be deep in the red on its bitcoin position.
With the cryptocurrency’s price trading at around $66,000 as of press time, Strategy’s fortune is worth around $47.5 billion, which represents an unrealized net loss of over $7 billion.
Strategy has acquired 3,015 BTC for ~$204.1 million at ~$67,700 per bitcoin. As of 3/1/2026, we hodl 720,737 $BTC acquired for ~$54.77 billion at ~$75,985 per bitcoin. $MSTR $STRC https://t.co/rqDIhlUDNx
— Michael Saylor (@saylor) March 2, 2026
Most comments below Saylor’s posts outlined their support for the move, with one user calling the purchase of 3,015 BTC during the current macro conditions a show of “conviction” and not hesitation.
Strategy’s stock price has not opened for trading yet after the weekend events in the Middle East, but is down by 0.5% in pre-market trading. More volatility is expected when Wall Street opens in a few hours.
Binance Free $600 (CryptoPotato Exclusive): Use this link to register a new account and receive $600 exclusive welcome offer on Binance (full details).
LIMITED OFFER for CryptoPotato readers at Bybit: Use this link to register and open a $500 FREE position on any coin!
Crypto World
ARK Invest Snaps Up Netflix (NFLX) After Earnings Drop While Dumping Crypto Holdings
Key Takeaways
- Following a two-day trading pause, ARK Invest executed significant portfolio adjustments on Friday
- The firm acquired 26,161 Netflix shares valued at approximately $2.5M following a nearly 10% post-earnings decline
- Circle holdings worth $1.21M were liquidated as the company faces legal challenges related to the Drift Protocol incident
- ARK divested $1.36M in Bullish shares while Bitcoin climbed past $76,000
- The firm invested roughly $11.96M in Alamar Biosciences during its Nasdaq debut
Cathie Wood’s ARK Invest resumed active trading Friday, April 17, 2026, following a 48-hour hiatus. The investment firm executed a notable strategic pivot: liquidating cryptocurrency-related equities while accumulating positions in established technology and biotechnology companies.
The firm purchased 26,161 Netflix shares representing approximately $2.5 million in capital. This move came immediately after Netflix disclosed its Q1 financial results, revealing revenue of $12.25 billion alongside profits reaching $5.28 billion — figures that surpassed analyst expectations.
Despite delivering impressive financial metrics, Netflix stock plummeted nearly 10% to settle at $97.31. The decline followed co-founder Reed Hastings’ announcement that he wouldn’t pursue board reelection, coupled with the company’s conservative revenue projections for the remainder of 2026.
ARK’s acquisition indicates confidence that the market overreacted to the news. Netflix continues expanding into live sports broadcasting and advertising initiatives, with revenue projections approaching $3 billion for the current year.
Cryptocurrency-Linked Stock Divestment
Regarding sales activity, ARK liquidated Circle shares totaling $1.21 million. Circle operates as the issuer of USDC, ranking among the most significant stablecoins by total market capitalization.
The company currently confronts a class-action legal proceeding stemming from the Drift Protocol security breach. Plaintiffs allege Circle neglected to freeze compromised assets during the incident, introducing considerable legal exposure for shareholders.
Additionally, ARK disposed of $1.36 million in Bullish stock, despite the shares appreciating approximately 5% that trading session amid declining Middle East tensions.
Bitcoin maintained levels above $76,999 Friday, experiencing temporary upward momentum following reports of the Strait of Hormuz reopening. Crude oil prices declined roughly 10% on this development.
The optimism proved fleeting. By Saturday evening, Iranian officials declared the Strait closed once more, citing a U.S. naval blockade. This reversal underscored persistent geopolitical volatility.
Biotech Investment on Debut Trading Day
ARK acquired 537,463 Alamar Biosciences shares for approximately $11.96 million during the company’s inaugural Nasdaq trading session.
Alamar experienced a remarkable 33% surge during its debut, achieving a market capitalization of $1.53 billion. This transaction demonstrates ARK’s ongoing commitment to emerging biotechnology ventures alongside established technology positions.
Combined cryptocurrency-related divestments totaled $2.57 million spanning Circle and Bullish. Both positions saw reductions despite the broader cryptocurrency market maintaining strength above critical price thresholds.
These transactions illustrate a calculated adjustment in ARK’s Friday holdings — transitioning capital from elevated-risk cryptocurrency exposures toward large-capitalization technology and biotechnology assets amid continued global uncertainty.
ARK’s simultaneous purchases of Netflix and Alamar Biosciences shares represents one of the firm’s most substantial single-session portfolio rebalancing events in recent trading periods.
Crypto World
NSA taps Anthropic’s Mythos despite Pentagon risk warnings: report
The National Security Agency is utilizing Anthropic’s most sophisticated AI model, Mythos Preview, despite the Department of Defense labeling the startup a “supply chain risk.”
Summary
- The National Security Agency has secured access to Anthropic’s most advanced AI model despite official Pentagon warnings that the company poses a supply chain risk.
- The Pentagon is currently arguing in court that Anthropic’s tools threaten national security while it simultaneously expands the use of those same tools across military departments.
Two sources told Axios that the NSA has secured access to the high-powered model, which Anthropic has kept under tight wraps due to its potent offensive cyber capabilities.
While the Pentagon officially moved to sever ties with the company in February—even directing its vendors to do the same—internal demand for the technology appears to be overriding that directive.
This friction has led to a legal standoff where military officials are arguing in court that Anthropic’s tools threaten national security, while simultaneously expanding their use of those same tools across various departments.
The standoff over “all lawful purposes”
Renegotiations between the two parties soured earlier this year when the Pentagon demanded the company make its Claude model available for “all lawful purposes.”
Anthropic leadership pushed back, insisting on specific prohibitions against mass domestic surveillance and the development of autonomous weaponry. As a result of this, some Defense officials claimed the company cannot be trusted in critical military scenarios, a characterization Anthropic has denied.
The government’s interest in the model stems largely from its specialized utility. Most of the 40 organizations granted access to Mythos Preview use the tool to scan their own digital environments for exploitable vulnerabilities.
While Anthropic has publicly named only 12 of these partners, including the U.K.’s AI Security Institute, the NSA is reportedly among the undisclosed group of agencies.
Recent efforts to resolve the impasse have moved beyond the Pentagon’s halls. Anthropic CEO Dario Amodei met on Friday with White House Chief of Staff Susie Wiles and Treasury Secretary Scott Bessent to discuss how Mythos could be integrated across other government sectors.
Sources described the meeting as productive, indicating that the administration may look for ways to bypass the Pentagon feud to ensure other departments can utilize the cutting-edge technology.
Crypto World
Bitcoin Price Prediction: Iran War Goes On, Crypto Can’t Catch A Break

The Strait of Hormuz is back under Iranian control, Trump is threatening to level Iran’s power grid, and somehow BTC is still standing where altcoins would already be bleeding out. Something in the structure of this market has changed, but the Bitcoin price prediction is still bullish.
The weekend’s flare-up hit hard across traditional assets. Brent crude surged to $88, European natural gas futures spiked as much as 11%, and S&P 500 futures dropped 0.6% after Friday’s record close. Bitcoin’s 0.5% pullback looked almost serene by comparison.
This is now the fourth major Iran-related escalation since the conflict began on February 28, and the pattern is consistent. Each successive crypto sell-off is shallower than the last. Bank of England Deputy Governor Sarah Breeden warned April 18 that the war “heightens combined market stress risks,” yet BTC held above $70,000 throughout.
Discover: The best crypto to diversify your portfolio with
Bitcoin Price Prediction: $80K Still The Target
Bitcoin hit its 2026 low of $63,000 on February before bouncing to $78,000 on the ceasefire talk last week, liquidating $200 million in shorts in the process. The current $74K level sits in the middle of a well-defined five-week range between $73,000 and $78,000.
RSI showed a slightly oversold rebound after the April 1 wick; Chaikin Money Flow data points to active dip-buying despite elevated volatility, the same pattern as Bitcoin’s post-Ukraine invasion consolidation in 2022, with EMA 100 and 200 closing in for a golden cross.

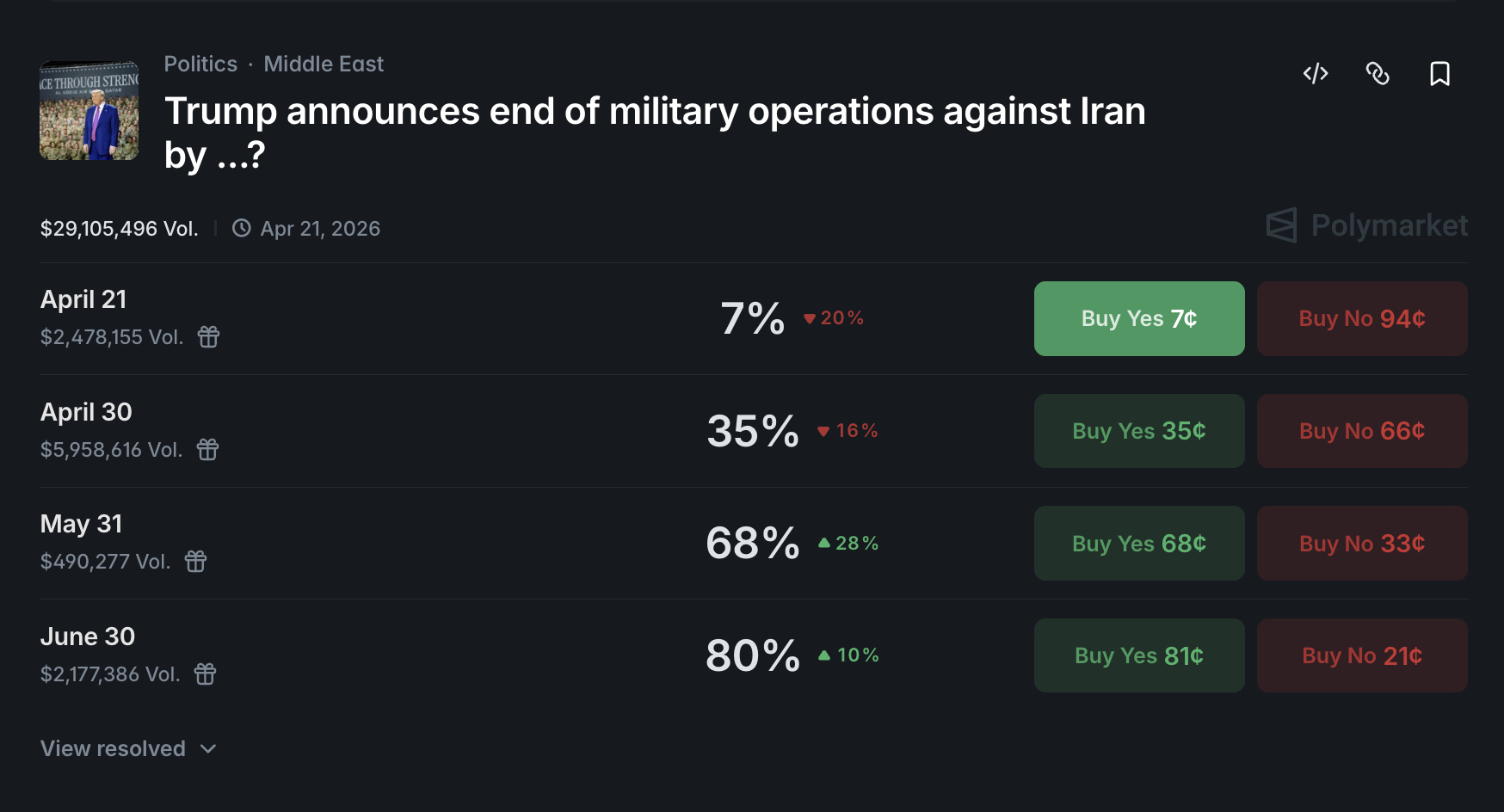
Key support sits higher, after the jump last week, at $73,000. Resistance is clustered at $76,000–$78,000. Polymarket currently prices an 80%+ probability of a deal by the end of June, which sets up a good scenario. Ceasefire confirmed, Strait reopens, then BTC breaks $78,000, targets $80,000–$94,000 range within weeks.
Bernstein maintains a $150,000 year-end 2026 target in a call backed, in part, by MicroStrategy’s purchase of 4,871 BTC ($329.9 million) between April 1–5, right into the conflict’s worst week.
Long-term holders are buying the fear. That doesn’t guarantee a near-term breakout, but it sets a credible demand floor.
Discover: The best pre-launch token sales
Bitcoin Hyper Bullish as BTC Grinds Through War-Risk Consolidation
Bitcoin above $74,000 sounds bullish until you map the resistance. $76,000 is a ceiling that’s been rejected twice already, and a full move to Bernstein’s $150,000 target implies months of sustained catalyst flows like a ceasefire, ETF inflows, and macro easing, all arriving in sequence.
There are a lot of dominoes to be pushed. Those looking for asymmetric upside without waiting for BTC to clear four layers of resistance are increasingly looking at the infrastructure layer being built on top of Bitcoin itself.
Bitcoin Hyper ($HYPER) is positioned at that intersection. It’s built as the first-ever Bitcoin Layer 2 with full Solana Virtual Machine (SVM) integration, bringing sub-second smart contract execution to the Bitcoin ecosystem without sacrificing Bitcoin’s base-layer security.
The pitch is direct: fix Bitcoin’s core limitations of slow transactions, high fees, and zero programmability, while preserving the trust that makes BTC worth building on. The presale has raised $32 million at a current price of $0.0136, with 36% APY staking available.
Hyper offers a real capital stack at a seed-stage price. Dig into the mechanics, because the raised size suggests this isn’t flying under the radar.
The post Bitcoin Price Prediction: Iran War Goes On, Crypto Can’t Catch A Break appeared first on Cryptonews.
Crypto World
Precious Metals Fall as US-Iran Conflict Escalates Ahead of Ceasefire Deadline


Gold, silver, and platinum prices declined on Monday as escalating tensions between the United States and Iran weighed on precious metals markets.
The US Navy fired on and seized an Iranian cargo ship in the Gulf of Oman, reviving concerns before the US-Iran ceasefire expires this week.
Gold, Silver, and Platinum Record Losses as Geopolitical Tensions Escalate
Precious metals have started to unwind last week’s rally. Silver had climbed more than 6% Friday to over $83 on hopes of de-escalation. Iran also temporarily reopened the Strait of Hormuz for commercial vessels.
However, that move reversed once shipping stalled again. Today, the silver price fell 1.07% to $79.89, per Trading Economics data. Platinum led the sell-off with a 2.22% drop to $2,094.20. Gold slid 0.85% to $4,792.48.
Copper retreated 0.80% to $6.0544, coming off its highest close since early February. Zinc and lead also declined.
Follow us on X to get the latest news as it happens
On the other hand, industrial and battery metals held up better than precious metals. Lithium gained 1.77%, while iron ore and steel nudged higher.
Brent jumped as much as 7.9%, and WTI climbed over 7% toward $90, reviving inflation concerns that trim Fed rate-cut expectations and weigh on non-yielding metals.
The crypto market was also part of the broader sell-off. BeInCrypto Markets data showed that the total market capitalization declined 1.15% over the past 24 hours. Bitcoin (BTC) dropped below $74,000 in early Asian trading hours today before settling at $74,190 by press time.
All attention now shifts to Wednesday’s ceasefire deadline and a possible new round of negotiations. Trump said US negotiators would fly to Islamabad on Monday.
Iranian state broadcaster IRIB said Tehran had no plans to join the next round, citing unnamed Iranian sources.
“There are currently no plans to participate in the next round of Iran-US talks.”
However, Al Jazeera reported that Iranian officials would “most probably” attend, citing preparations already underway in Islamabad. Further losses in precious metals hinge on whether either side returns to the table and on the outcome.
Subscribe to our YouTube channel to watch leaders and journalists provide expert insights
The post Precious Metals Fall as US-Iran Conflict Escalates Ahead of Ceasefire Deadline appeared first on BeInCrypto.
Crypto World
RaveDAO token crashes below $1 after ZachXBT exposes price manipulation


- RaveDAO token plunged 95% from $26 to under $1.
- RAVE launched in December 2025 on Binance Alpha.
- ZachXBT’s on-chain analysis also highlights MemeCore, River and MYX among questionable projects.
RaveDAO (RAVE) has plunged below $1, erasing more than 95% of its earlier rally to an all-time high of $26.
The sharp decline follows an investigation by blockchain analyst ZachXBT, which alleged clear signs of price manipulation.
The findings have raised broader concerns about potential insider-driven schemes affecting multiple tokens listed on centralised exchanges, contributing to selling pressure across the segment.
RaveDAO token dumps amid ZachXBT’s explosive allegations
ZachXBT, a pseudonymous investigator celebrated for dismantling multimillion-dollar crypto frauds, took to X on April 18, 2026, to dissect RAVE’s suspicious trajectory.
He pinpointed concentrated wallet activity controlling the token’s liquidity, engineering artificial pumps to trap retail buyers before orchestrated dumps.
“RAVE launched in Dec 2025 on Binance Alpha with a 1B total supply. The addresses below, linked to the initial distribution, control ~95% of the RAVE supply,” the on-chain sleuth posted.
Labelling it a textbook “pump-and-dump,” ZachXBT offered a $25,000 bounty for transaction proofs, urging platforms like Binance, Bitget, and Gate.io to launch probes.
He notes that the exchanges acknowledged his call, a move that could mirror past successes in securing refunds and bans.
Yet ZachXBT questioned why CEXs have waited for his call to acknowledge potential manipulation.
“While it’s good the exchanges responded, I find it unlikely this activity wasn’t spotted internally before I raised it publicly.”
RAVE’s price carnage unfolded mercilessly, plummeting from $26 to under $1 within 24 hours, with trading volume surging amid mass liquidations.
Billions of dollars in market cap vaporised, leaving holders stunned. The declines saw the token’s value drop to lows of $0.50, where it hovered as of writing on April 20, 2026.
Update: Three hours ago multisig 0x53d7 linked to the RAVE initial distribution which I flagged above sent ~23M RAVE ($23M) to two Bitget deposit addresses and the price dropped 40% from $1 to $0.6.
Deposit addresses
0x26aC542f5a04D574580881723224DAcD1EDB9B45… pic.twitter.com/Qi1asiFWsB— ZachXBT (@zachxbt) April 19, 2026
ZachXBT also hits other tokens
The potential price manipulation extends to similar tokens.
“RAVE is not the only token with manipulation we have seen on major centralized exchanges,” he posted.
“It’s just the most blatant, reaching a top 15 market cap within 10 days before dropping 95% in hours. Other projects with highly questionable price action recently include: SIREN, MYX, COAI, M, PIPPIN, RIVER.”
According to ZachXBT, all projects have exhibited “highly questionable price action” and supply dominance by the team.
MemeCore, RIVER and PIPPIN prices echoed the Rave token bleed, dumping double digits to erase recent gains.
Some retail traders commented on ZachXBT’s post, noting this could be an opportunity to short. His response:
I do not recommend shorting manipulated tokens with a high insider concentration.
— ZachXBT (@zachxbt) April 20, 2026
Data on CoinMarketCap showed M, River and Siren were down 7-9% in the past 24 hours as of writing.
Crypto World
Bitcoin price outlook as Iran casts doubt on peace talks after U.S. ship seizure


Bitcoin price briefly fell below $74,000 on Monday as fading prospects of U.S. Iran peace talks and escalating tensions in the Strait of Hormuz weighed on sentiment.
Summary
- Bitcoin briefly dropped below $74,000 as Iran ruled out U.S. peace talks and tensions escalated in the Strait of Hormuz.
- Iran retaliated to a U.S. ship seizure with drone and missile strikes, while conflicting signals over negotiations kept markets on edge.
- Oil prices surged, with WTI nearing $90 and Brent above $95, as renewed conflict raised fears of supply disruptions and broader market volatility.
According to reports, Iranian sources recently said that Iran will not show up for the peace negotiations with the U.S. that were set to be held in Islamabad today. This comes after the nation promised to retaliate against the U.S. for intercepting and seizing one of its cargo ships in the Strait of Hormuz.
The heightened volatility in the surrounding Gulf region after the war began had left markets on edge, with economists expressing concerns of a global recession if supply lines remained blocked.
Shortly following the U.S. intervention on the ship, Iran responded with its own offensive strategy, attacking U.S. military ships with drones and ballistic missiles.
The tensions between the two nations flared up earlier in the weekend. On Friday, Iran reopened the Strait of Hormuz amid its stated commitment to de-escalate. However, Tehran decided to close it again just hours later as the U.S. continued to maintain the naval blockade.
While the U.S. later announced that both parties would attend peace negotiations on Monday, Iran has refuted these claims entirely. Earlier, Iran had also dismissed Trump’s suggestion that it would give up on its uranium enrichment plan as part of any future deal.
Crude oil price, which fell earlier due to expectations of peace discussions between the nations and reopening of the strait, surged significantly following the recent breakdown in communication. Notably, West Texas Intermediate crude oil rose 6.7% to nearly $90 while Brent crude rose 6% to above $95 again.
Since crypto markets operate around the clock, they reacted immediately to the latest geopolitical developments over the weekend, with prices largely trending lower.
Bitcoin (BTC) had rallied to $78,400 on Friday, but the move was swiftly rejected, with the price slipping below $74,000 as hostilities resumed. At press time, the bellwether asset was trading just under the $75,000 level.
Further price swings may lie ahead as the ceasefire deadline passes without any clear extension. Overnight attacks have added to the uncertainty, while the absence of any concrete peace negotiations continues to weigh on market sentiment. Traders are now bracing for continued volatility as geopolitical risks remain elevated.
As such, if Bitcoin sharply falls below $74,000 again, it could slide further to $72,000, which acts as a major support level. Failure below the $72,000 mark might invite a broader selloff toward the $68,000 zone. On the other hand, if Bitcoin stabilizes over $76,000, it could embolden bulls to target a return to the $80,000 psychological threshold.
Disclosure: This article does not represent investment advice. The content and materials featured on this page are for educational purposes only.
Crypto World
Huawei Expands Financial Footprint in Vietnam with Major Bank Partnership

Key Points
- The Chinese technology firm Huawei has entered a strategic partnership with Vietnam’s SHB bank this past weekend
- The collaboration encompasses technology infrastructure design and comprehensive data platform construction
- Security and operational stability for banking systems form core components of the agreement
- This partnership joins existing Huawei collaborations with SCB, SeABank, and Home Credit across Vietnam
- Huawei secured major contracts in 2024 for Vietnam’s 5G infrastructure development
The Chinese technology conglomerate Huawei Technologies Group has formalized a strategic partnership with SHB, a prominent Vietnamese banking institution, signaling the company’s accelerating expansion throughout Vietnam’s financial landscape.
SHB publicly disclosed the partnership on Sunday. According to the arrangement, Huawei will provide expertise in crafting the bank’s technological framework and establishing robust data infrastructure. The agreement additionally ensures that SHB’s operational systems maintain consistent reliability and comprehensive security.
“The cooperation with SHB is an important milestone in the group’s market expansion in Vietnam,” said Spawn Fan, a senior Huawei executive, in the bank’s statement.
This isn’t Huawei’s inaugural venture into Vietnam’s banking industry. The technology powerhouse maintains established partnerships with multiple financial institutions including SCB, SeABank, and Home Credit, spanning initiatives in digital transformation, security protocols, data intelligence, cloud infrastructure, and banking platform optimization.
Strategic Expansion in Southeast Asia
The newly announced SHB collaboration strengthens Huawei’s increasingly substantial position within one of Southeast Asia’s most dynamic and rapidly expanding markets. Vietnamese financial institutions have aggressively prioritized digital infrastructure modernization, creating opportunities that Huawei has strategically pursued.
Huawei’s expanding influence in Vietnam represents a significant shift from previous policy positions. Until quite recently, Vietnamese authorities maintained strict restrictions preventing Chinese corporations from participating in the nation’s 5G telecommunications infrastructure.
This policy underwent a dramatic reversal in 2024 when Huawei successfully secured multiple contracts to develop significant portions of Vietnam’s 5G network. The current SHB partnership reflects a continuation of this evolving relationship — demonstrating strengthening connections between Vietnamese organizations and Huawei spanning both telecommunications and financial technology sectors.
Partnership Scope and Implementation
SHB ranks among Vietnam’s most significant privately-owned commercial banking institutions. The comprehensive partnership with Huawei encompasses multiple critical domains: architectural design for technology infrastructure, comprehensive data platform construction, and continuous operational assistance ensuring system stability and security.
These initiatives represent substantial commitments. Constructing data platforms and architectural frameworks for commercial banking operations requires extensive integration with fundamental banking technology systems.
According to statements from the Vietnam Banks Association, Huawei’s activities throughout Vietnam’s financial industry concentrate on digital transformation initiatives, cybersecurity enhancement, advanced data analytics, cloud computing solutions, and banking operational efficiency — capabilities that align directly with the SHB partnership framework.
The 5G infrastructure contracts Huawei won in 2024 marked a fundamental policy transformation from Vietnamese government authorities. This strategic pivot created pathways for expanded collaboration, with the SHB agreement representing one of the most substantial manifestations of this revised approach.
Spawn Fan, the Huawei representative referenced in SHB’s official announcement, characterized the partnership as a significant achievement — not solely for SHB’s technological advancement, but for Huawei’s comprehensive Vietnam market strategy.
The Vietnam Banks Association has verified that Huawei’s current financial sector engagements include SCB, SeABank, and Home Credit, with the SHB partnership now expanding that portfolio.
Crypto World
MicroStrategy’s Saylor signals larger BTC buys amid dividend chatter

Strategy co-founder Michael Saylor has stoked expectations of another large Bitcoin purchase just days after Strategy disclosed a roughly $1 billion buy in mid-April. The company revealed that between April 6 and 12 it acquired 13,927 BTC for about $1 billion, at an average price of $71,902 per coin. In a sign that Saylor may be signaling more activity, he posted on X with the message Think Even ₿igger, accompanied by a chart of Strategy’s purchase history—a pattern he has used in the past to hint at forthcoming buys, according to coverage of the episode.
In the same period, Strategy’s leadership publicly discussed a broader capital management move: paying its dividend more frequently, with a plan to double the cadence to semi-monthly payments. The intention, said Strategy CEO Phong Le, is to stabilize the STRC price, dampen cyclicality, improve liquidity, and expand demand for the stock. The stance comes as Strategy has prepared a preliminary proxy filing with the U.S. Securities and Exchange Commission; the definitive proxy is expected on April 28, with shareholder voting running through June 8 and potential implementation slated for mid-July if approved.
Key takeaways
- Strategy hints at another Bitcoin purchase after disclosing a $1 billion acquisition of 13,927 BTC in early April, with Saylor signaling via a post comparing Strategy’s past buys.
- The company is proposing to shift STRC dividend payments to a semi-monthly schedule (twice a month, on the 15th and month-end), aiming for 24 payments a year at an 11.5% yield.
- The move to semi-monthly dividends is framed as a way to stabilize price and liquidity, with Strategy describing it as a unique approach among preferred equities.
- Strategy holds the largest Bitcoin treasury among publicly traded companies, with 780,897 BTC worth about $58.2 billion, according to Bitbo data, and it has a habit of recurring weekly purchases.
- Despite the Bitcoin buys, the company reports significant unrealized losses on digital assets, totaling about $14.46 billion in its first-quarter results.
Strategy’s latest Bitcoin move and the social signal
The disclosed purchase of 13,927 BTC for roughly $1 billion occurred over a one-week window in April, at an average price near $71,902 per coin. The social signal accompanying the filing—Saylor’s “Think Even ₿igger” post with a chart of Strategy’s purchase history—has historically coincided with additional buying or hints of future transactions, a pattern analysts monitor as a potential short-term predictor of capital deployment. The development sits within a broader narrative of corporate Bitcoin treasury management where large hodlers weigh ongoing accretion against volatility and capital allocation priorities.
Dividend plan to stabilize price and liquidity
Le framed the dividend proposal as a mechanism to reduce price volatility and encourage steady demand for STRC. If approved, Strategy would pay semi-monthly dividends on the 15th and the last day of each month, totaling 24 payments per year at the current rate of 11.5%. Le noted that this cadence would position STRC as a highly distinctive instrument in the market, and the company has worked through multiple iterations to reach a viable schedule that accommodates NASDAQ’s rules on record and payment dates. Nasdaq-listed STRC would still need to comply with minimum gaps between record and payment dates—an issue the company acknowledged as an operational constraint.
The plan was detailed in an investor presentation linked to the proxy materials, with the preliminary filing submitted to the SEC and a definitive filing expected by April 28. If shareholders approve the proposal, the new semi-monthly schedule would take effect mid-July, subject to the usual regulatory and procedural approvals.
BTC treasury size, market backdrop, and investor reaction
Strategy’s balance sheet remains anchored in Bitcoin, with the company holding 780,897 BTC, the largest stash among publicly traded firms. Bitbo’s data places Strategy’s BTC holdings at approximately $58.2 billion in value, underscoring the scale of its treasury position. The stock market reaction to the ongoing program has been nuanced: Strategy’s shares (MSTR) rose by about 11.8% on a recent session to around $166.50, though they remain down roughly 47% over the past year. The dynamic underscores a complex investor calculus: large-scale BTC exposure paired with sensitive equity pricing and the potential impact of dividend policy changes.
On the accounting side, Strategy reported substantial unrealized losses on its digital asset holdings for the first quarter, tallying about $14.46 billion. The disclosures reflect the market’s swing in BTC prices and the accounting treatment for crypto holdings at scale, contributing to a broader conversation about risk management and liquidity needs for corporate treasuries tied to digital assets.
What to watch next
Investors will be keeping a close eye on the proxy process and whether the semi-monthly dividend plan gains shareholder approval. The timing of the next BTC purchase remains uncertain, but the social signaling by Saylor adds an element of anticipation around Strategy’s treasury strategy. As regulators and markets continue to refine frameworks for corporate crypto holdings and investor protections, Strategy’s moves could serve as a barometer for how publicly traded companies balance growth, income, and risk in a volatile asset class.
Sources and context for these developments were reported in coverage detailing Strategy’s recent Bitcoin purchases, the proposed dividend schedule, and the company’s regulatory filings. For reference, strategic data on Strategy’s Bitcoin holdings is tracked by market trackers such as Bitbo, and the proxy filing timeline aligns with the SEC’s typical review and voting windows.
Crypto World
Moody’s exec warns stablecoins could erode bank market share as adoption scales


Traditional banks could see their market dominance challenged by the rise of stablecoins and tokenized real-world assets as these digital currencies move beyond their current niche uses.
Summary
- Moody’s Investors Service suggests that the disruption risk for the banking sector remains limited at this stage because current U.S. rules prevent stablecoins from paying yield.
- The growth of tokenized real-world assets and stablecoins could eventually place pressure on traditional banks by causing deposit outflows and reducing their overall lending capacity.
Moody’s Investors Service Digital Economy Group associate vice president Abhi Srivastava told crypto media that stablecoin use remains “limited” for now, even though the sector’s market capitalization climbed past $300 billion by the end of last year.
While the role of these assets in cross-border commerce and on-chain finance is expanding, the existing US payment landscape is currently fast and trusted enough to keep disruption at bay.
Srivastava observed that “for the banking sector, at this stage, disruption risk appears limited,” largely because US rules prevent stablecoins from paying yield to holders.
According to him, domestic deposits are unlikely to be replaced at scale while these yield restrictions remain in place. However, long-term growth in stablecoins and tokenized RWAs—physical or financial assets represented by blockchain tokens—could eventually trigger deposit outflows.
Such a trend would reduce the lending capacity of traditional banks by placing “pressure” on their core business models, he added.
Legislative gridlock over yield and oversight
Regulatory policy regarding stablecoins has turned into a major point of contention between the crypto industry and the banking sector. The primary concern centers on yield-bearing stablecoins, which banks fear will directly compete for their customers.
This specific issue has become a major stumbling block for the Digital Asset Market Clarity Act of 2025, or the CLARITY Act.
The Digital Asset Market Clarity Act of 2025, or the CLARITY Act, has hit a wall in Congress as lawmakers struggle to balance the interests of the crypto industry with those of the bank lobby. The framework was designed to set clear rules for asset classification and regulatory oversight, but it stalled after major players like Coinbase voiced opposition to specific provisions.
The ban on yield-bearing stablecoins and a lack of legal safeguards for open-source developers remain the primary points of contention.
Banks have lobbied heavily against allowing stablecoins to offer interest, fearing such a move would trigger massive deposit outflows and sap their ability to provide loans. Srivastava warned that over time, the growth of tokenized RWAs—physical assets represented on a blockchain—could place significant “pressure” on traditional financial institutions.
Senator Thom Tillis of North Carolina recently signaled plans to introduce a compromise draft to bridge the gap between crypto firms and traditional banks. However, this updated proposal has already faced resistance and remains unreleased to the public.
Crypto World
Crypto ETFs Haul $1.37 Billion in Biggest Week Since January 2026, Altcoins Join Rally


Spot Bitcoin (BTC) and Ethereum (ETH) exchange-traded funds (ETFs) drew $1.27 billion in combined net inflows during the week ending April 17. This marked their strongest week since mid-January.
Across the five major spot crypto ETF products, total weekly inflows reached roughly $1.37 billion, including XRP, Solana, and Chainlink funds, a near 40% jump from the prior week.
Crypto ETF Flows Rebound After Q1 Drawdown
Bitcoin ETFs pulled in $996.38 million, while Ethereum ETFs added $275.83 million, according to SoSoValue data. Both marked the largest weekly inflows since the week of January 16.
The rebound comes after a difficult first quarter. BTC ETF assets fell nearly 35% from their $128 billion mid-January high to $83.40 billion by February 27.
In addition, ETH ETF assets dropped 46% over the same period. Now, the inflow surge has pushed total Bitcoin ETF net assets back above $100 billion.
Moreover, the move extends a third straight week of positive BTC ETF flows and a second for Ethereum products.
Follow us on X to get the latest news as it happens
The recovery was not isolated to the two largest assets. XRP ETFs took in $55.39 million, nearly matching their 2026’s peak week in mid-January. Solana funds drew $35.17 million, reversing three consecutive weeks of outflows, while Chainlink ETFs added $5.30 million.
This marked the largest inflow outside its December launch week. Notably, LINK ETFs have not recorded a single week of net outflows.
Inflows picked up on the back of easing expectations around US–Iran tensions, but the backdrop remains fragile. Sentiment could come under renewed pressure after US naval forces fired on and seized an Iranian cargo ship in the Gulf of Oman, marking a clear escalation in the conflict.
At the same time, uncertainty surrounding Iran’s participation in the upcoming talks in Islamabad has added to market caution. Geopolitical developments, including the trajectory of negotiations and potential retaliation risks, are likely to remain a key driver of market sentiment in the near term.
Subscribe to our YouTube channel to watch leaders and journalists provide expert insights
The post Crypto ETFs Haul $1.37 Billion in Biggest Week Since January 2026, Altcoins Join Rally appeared first on BeInCrypto.
-

 Crypto World7 days ago
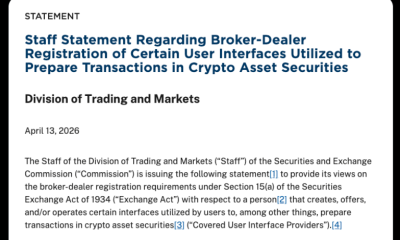
Crypto World7 days agoThe SEC Conditionalises DeFi Platforms to Be Avoided for Broker Registration
-

 NewsBeat6 days ago
NewsBeat6 days agoTrump and Pope Leo: Behind their disagreement over Iran war
-

 Fashion3 days ago
Fashion3 days agoWeekend Open Thread: Theodora Dress
-

 Crypto World6 days ago
Crypto World6 days agoSEC Signals Exemption for Crypto Interfaces From Broker Registration
-

 News Videos5 days ago
News Videos5 days agoSecure crypto trading starts with an FIU-registered
-

 Sports3 days ago
Sports3 days agoNWFL Suspends Two Players Over Post-Match Clash in Ado-Ekiti
-
 Crypto World6 days ago
Crypto World6 days agoSEC Proposes Certain Crypto Interfaces Don’t Need to Register as Brokers
-

 Business18 hours ago
Business18 hours agoPowerball Result April 18, 2026: No Jackpot Winner in Powerball Draw: $75 Million Rolls Over
-

 Crypto World2 days ago
Crypto World2 days agoRussia Pushes Bill to Criminalize Unregistered Crypto Services
-

 Politics3 days ago
Politics3 days agoPalestine barred from entering Canada for FIFA Congress
-

 Sports7 days ago
Sports7 days agoNWFL opens Pathway for new Clubs ahead of 2026 Season
-

 Business4 days ago
Business4 days agoCreo Medical agree sale of its manufacturing operation
-

 Entertainment6 days ago
Entertainment6 days agoBrand New Day’ Footage Reveals the Devastating Impact of ‘Now Way Home’
-
 Politics23 hours ago
Politics23 hours agoZack Polanski demands ‘council homes not luxury flats for foreign investors’
-

 Tech5 days ago
Tech5 days agoMicrosoft adds Windows protections for malicious Remote Desktop files
-

 Entertainment6 days ago
Entertainment6 days agoKarol G’s ‘Ultra Raunchy’ Coachella Set Gave ‘Satanic Vibes’
-

 Sports7 days ago
Sports7 days agoAaron Judge says Yankees need to ‘simplify’ approach amid offensive slump
-

 Entertainment7 days ago
Entertainment7 days agoPete Davidson Reveals ‘Brutal’ Mom Moment That Got Him Sober
-

 Entertainment6 days ago
Entertainment6 days agoHow Babylon 5 Turned Brief Side Story Into Emotional Masterpiece
-
 Tech6 days ago
Tech6 days agoWhat was the first ransomware attack to demand payment in Bitcoin?



 Futures are down big after this weekend’s Iran developments.
Futures are down big after this weekend’s Iran developments.






You must be logged in to post a comment Login