Business
Gold, silver climb as US yields fall on softer retail sales

FUNDAMENTALS
Spot gold edged 0.3% higher to $5,038.73 per ounce by 0059 GMT.
U.S. gold futures for April delivery gained 0.6% to $5,060.60 per ounce.
Spot silver was up 1% at $81.49/oz, after falling more than 3% in the previous session.
U.S. yields fell on Tuesday after a raft of data suggested the economy may be softening, giving the U.S. Federal Reserve more cushion to cut interest rates. [US/]
Falling yields reduce the cost of holding metals and often come with macro signals that favour them.U.S. retail sales were unexpectedly unchanged in December as households scaled back spending on motor vehicles and other big-ticket items, potentially setting consumer spending and the economy on a slower growth path heading into the new year.
Federal Reserve Bank of Cleveland President Beth Hammack, however, said on Tuesday that the U.S. central bank faces no urgency to change the setting of interest rates this year amid a “cautiously optimistic” outlook for economic activity.
Investors expect at least two 25-basis-point rate cuts in 2026, with the first one expected in June. Non-yielding bullion tends to do well in low-interest-rate environments. [FEDWATCH]
Investors await the non-farm payrolls report for January, due later in the day, and inflation data on Friday for more cues on the Fed’s monetary policy path.
Indian investors piled into gold exchange-traded funds in January as prices soared amid rising geopolitical risks, surpassing flows into equity funds for the first time, industry data showed on Tuesday.
Spot platinum added 0.6% to $2,098.78 per ounce, while palladium rose 0.2% to $1,712.25.
DATA/EVENTS (GMT)
0130 China PPI, CPI YY January
1330 US Non-Farm Payrolls January
1330 US Unemployment Rate January
1330 US Average Earnings YY January
Business
'The Australian way': PM seeks to calm nation on fuel crisis

The Prime Minister has addressed the country, calling for calm in the face of uncertainty surrounding the war in Iran, while warning the situation could worsen.
Business
Lonza: Structural Growth Intact, CHI Exit Strengthens Focus, Recent Weakness Reinforces Entry Opportunity

Lonza: Structural Growth Intact, CHI Exit Strengthens Focus, Recent Weakness Reinforces Entry Opportunity
Business
Emart Launches First Private Brand Store in Thailand

Emart has opened its first No Brand outlet in Thailand, offering 2,300 products, including Korean snacks. This marks its first Korean retail store and aims to promote its brand in Southeast Asia.
Key Points
- Emart, Korea’s largest discount retailer, has launched its first No Brand outlet in Thailand at Central Bangna shopping mall, part of its global expansion strategy in partnership with Central Food Retail.
- The franchise agreement allows local partners to operate stores and grant subfranchises, marking Emart as the first Korean retailer to establish an offline store in Thailand.
- The outlet features approximately 2,300 products, including Korean snacks and meals, with a cooking station offering popular dishes like “gimbap” and “tteokbokki,” aimed at promoting Emart’s brand and Korean food in Southeast Asia.
Expansion of Emart in Thailand
Emart, recognized as South Korea’s largest discount retailer, has recently launched its first No Brand outlet in Thailand, marking a significant move in its global expansion strategy. The company has signed a master franchise agreement with Central Food Retail, enabling the establishment of its offline retail venture at the Central Bangna shopping mall in Bangkok. This outlet not only symbolizes Emart’s entry into the Thai market but is also noted as the inaugural offline store launched by a Korean retailer in the country. The franchise agreement allows Central Food Retail to operate and grant subfranchise rights within the specified region.
Diverse Product Offerings
The newly established No Brand outlet features an extensive selection of approximately 2,300 products. Among these are popular Korean snacks, instant noodles, and home meal replacement (HMR) items, catering to the preferences of both local and international customers. Additionally, the store highlights a cooking station where visitors can enjoy traditional Korean dishes, such as “gimbap” and “tteokbokki.” This focus on authentic cuisine not only enriches the shopping experience but also aims to promote Korean food in the Southeast Asian market. A company official emphasized that the outlet serves as a crucial bridge for advancing Emart’s brand presence in the region.
Strategic Implications
The establishment of the first No Brand store in Thailand is part of Emart’s broader strategy to boost its presence in Southeast Asia, following a successful launch in Laos in December 2024, where it has already opened four locations. By leveraging local partnerships, Emart aims to tap into the growing demand for diverse products while enhancing cultural connections through food. The company’s strategic initiatives are expected to facilitate its competitive position in the rapidly evolving retail landscape of Southeast Asia, expanding brand recognition and accessibility in the region.
Source : Emart opens 1st PB brand outlet in Thailand
Other People are Reading
Business
Innovate UK awards Agentic AI Pioneers Prize to leading UK startups

Innovate UK has unveiled the winners of its inaugural Agentic AI Pioneers Prize, marking a major step in the government’s ambition to position Britain as a global leader in next-generation artificial intelligence.
The competition, delivered in partnership with the Department for Science, Innovation and Technology, attracted more than 200 applications from across the UK’s high-growth sectors, highlighting the depth of innovation in areas such as advanced manufacturing, healthcare and the creative industries.
Designed to accelerate the commercialisation of “agentic AI”, systems capable of acting autonomously, collaborating with humans and managing complex workflows, the prize aims to support companies developing real-world applications of the technology.
The top award of £500,000 was granted to Danu Insights for its “Agentic Digital Twin Builder for the Life Sciences” platform.
The technology enables researchers to simulate biological systems and identify the most promising experimental pathways, helping to address growing complexity in drug discovery and biomanufacturing. By integrating modelling, validation and experiment planning into a single system, the platform is designed to reduce costs and accelerate the development of new therapies.
The judges highlighted its potential to deliver faster, more efficient and more sustainable innovation across the life sciences sector.
Two additional awards of £250,000 were presented to companies operating in advanced manufacturing and the creative industries.
In manufacturing, Singular Machine was recognised for CoEngen, a multi-agent engineering platform that coordinates design processes across disciplines using shared data models. The system allows engineers to optimise complex systems more quickly while maintaining traceability and safety standards.
In the creative sector, Tellme was awarded for a solution that delivers real-time, personalised museum experiences via smartphones. The platform enables visitors to interact with exhibits dynamically, receiving tailored information without the need for additional hardware, potentially transforming how audiences engage with cultural spaces.
Agentic AI represents a shift beyond traditional automation, focusing on systems that can take initiative, adapt to changing conditions and collaborate with human users. Applications range from industrial design and regulatory compliance to clinical decision-making and immersive digital experiences.
The competition demonstrated how these capabilities are already being applied to solve practical challenges, rather than remaining confined to theoretical research.
Sara El-Hanfy, head of AI and machine learning at Innovate UK, said the prize is intended to help promising companies move from early-stage innovation to scalable deployment.
“Our ambition is to support the companies set to shape the future of agentic AI and unlock its potential to drive growth across key sectors,” she said.
The initiative forms part of a broader strategy to position the UK at the forefront of AI development, particularly in areas where advanced technologies can deliver economic and societal impact.
By targeting sectors such as manufacturing, healthcare and creative industries, the programme aligns with the government’s industrial strategy priorities, focusing on areas where the UK has both strong research capabilities and commercial potential.
As AI continues to evolve, the emphasis is shifting from experimentation to implementation, with businesses seeking technologies that can deliver measurable productivity gains and competitive advantage.
The Agentic AI Pioneers Prize highlights how UK startups are beginning to translate cutting-edge research into practical solutions, with the potential to reshape industries and drive economic growth.
For Innovate UK, the challenge now is to ensure these early successes translate into scalable businesses capable of competing globally, reinforcing the UK’s position in the rapidly intensifying race for AI leadership.
Business
Australia’s Albanese says war’s economic shock will be felt for months; urges using public transport


Australia’s Albanese says war’s economic shock will be felt for months; urges using public transport
Business
‘Project Hail Mary’ box office success shows Amazon MGM can deliver
“Project Hail Mary” is setting records for Amazon MGM and lighting the path for a box-office revitalization.
The science fiction flick, starring Ryan Gosling, has tallied more than $300 million globally since its theatrical opening two weeks ago. That marks the best performance for an Amazon MGM film ever.
“The runaway success of ‘Project Hail Mary’ represents a key turning point for Amazon MGM giving the distributor its first $100 million plus domestic box office earner,” said Paul Dergarabedian, head of marketplace trends at Comscore.
“Project Hail Mary” has held notably strong at the box office since its debut, with only a 32% drop in ticket sales from its first weekend in the U.S. to its second and a nearly unheard of 5% decline internationally. A typical Hollywood blockbuster will see a 50% to 70% drop in ticket sales from opening weekend to the second weekend after the rush to the theater fades.
“When Amazon showcased ‘Project Hail Mary’ at CinemaCon exactly one year ago, it was clear the studio had big plans in mind,” said Shawn Robbins director of analytics at Fandango and founder of Box Office Theory. “After two incredible weekends so far, the movie is a major contributor in year-over-year box office gains.”
Domestically, the film has tallied about $165 million, helping to prop up first-quarter box-office numbers alongside Disney’s “Hoppers” and Paramount’s “Scream 7.” Through Sunday, the domestic box office has tallied $1.75 billion so far this year, up 23% from the same period last year.
Back in 2022, e-commerce giant Amazon and relative upstart movie studio MGM promised to spend around $1 billion each year on theatrical releases, a figure that would fund between 12 and 15 films annually. Last year, the company said it had 14 titles lined up for 2026.
This surge of theatrical content is just what the domestic box office needs. While blockbuster franchise films have been abundant in the wake of the pandemic, the overall number of wide releases has shrunk over the last decade. Even before Covid and dual Hollywood labor strikes slowed production down, Hollywood was making fewer and fewer movies each year, according to data from Comscore.
At the same time that studios were altering their film slates, movie houses were merging. The most recent union between the Walt Disney Co. and 21st Century Fox, first announced in 2017 and finalized in early 2019, resulted in the loss of between 10 and 15 film releases annually, Comscore data shows.
The pending merger of Paramount and Warner Bros. Discovery has Hollywood fearful of even fewer theatrical releases.
While Paramount has said it is committed to releasing 15 films from each studio, it’s unclear if the combined company will be able to keep up with that kind of production.
In the meantime, Amazon appears poised to fill a gap in the schedule.
The company’s upcoming slate is a diverse offering of films: Coming this year are features like “The Sheep Detectives,” a comedy murder mystery due out in May, the action-packed “Masters of the Universe” set for June and “Verity,” a psychological thriller adapted from the Colleen Hoover book of the same name, arriving in October.
Like “Project Hail Mary,” which is based on the book by Andy Weir, “Verity” may benefit from a built-in fanbase of readers who want to see the story translated to the big screen.
“Bottom line, ‘Project Hail Mary’ is the studio’s new gold standard for what they can accomplish in the world of cinema,” Robbins said. “That’s good news for an entire industry still adapting to the tailwinds of shorter windows, consolidation, and ever-evolving consumer habits. You can bet every studio, even the old guard, in the business will be looking at the takeaways from Amazon’s success with this film. The power of the moviegoing experience is on full display right now.”
Disclosure: Versant is the parent company of CNBC and Fandango.
Business
Anthony Albanese Will Address the Nation Regarding the Iran War


Prime Minister Anthony Albanese is scheduled to address the nation regarding the government’s response to the Iran War.
The address is scheduled to take place Wednesday night, specifically at 7 p.m. AEDT.
Albanese to Address Australia Wednesday Night
According to Sky News, Albanese is expected to go into detail regarding how his government has responded to the ongoing conflict in the Middle East.
The report notes that it is unusual for the prime minister to address the nation as a whole during times of crisis.
The last one to do so was Scott Morrison, who delivered a national address in 2020 as the world battled the COVID-19 pandemic.
Albanese to Discuss Fuel Crisis
Prime Minister Albanese is likewise expected to discuss concerns regarding the supply and price of fuel amidst the ongoing war.
According to ABC News, he is expected to asked Australians to save fuel for areas and industries that need it most.
He is likewise expected to stress that Australians must “play their part” as the crisis continues.
Sky News reports that ministers under the Albanese government has already limited their travel to save fuel.
Business
Boeing Vs. Airbus: The Iran War Shock And The Production Reality

Boeing Vs. Airbus: The Iran War Shock And The Production Reality
Business
RBC Capital upgrades Barratt Redrow stock rating on valuation

RBC Capital upgrades Barratt Redrow stock rating on valuation
Business
Delta flight to Atlanta returns to Brazil airport after engine issue

A Delta Air Lines flight bound for Atlanta returned to São Paulo, Brazil, shortly after takeoff Sunday night following an engine issue, according to the airline and local reports.
Delta Flight 104, operated on an Airbus A330-300, experienced a mechanical issue with its left engine after departing São Paulo International Airport, the company said.
The aircraft, carrying 272 passengers and 14 crew members, landed safely and was met by airport rescue and firefighting teams, Delta said. No injuries were reported.
UNITED AIRLINES WARNS AIRFARES COULD JUMP 20% AS OIL PRICES CONTINUE TO SURGE
Delta did not provide additional details about the nature of the mechanical issue or what may have caused it.
Brazilian outlet G1 reported that a passenger-recorded video appeared to show the left engine failing seconds after takeoff, though Reuters said it could not independently verify that report.
The incident also caused delays for other flights departing São Paulo International Airport, according to G1.
CLICK HERE TO GET FOX BUSINESS ON THE GO
Delta has not said whether the aircraft has been taken out of service. FOX Business has reached out to the airline for additional comment.
Reuters contributed to this report.
-

 News Videos6 days ago
News Videos6 days agoParliament publishes latest register of MPs’ financial interests
-
 Tech6 days ago
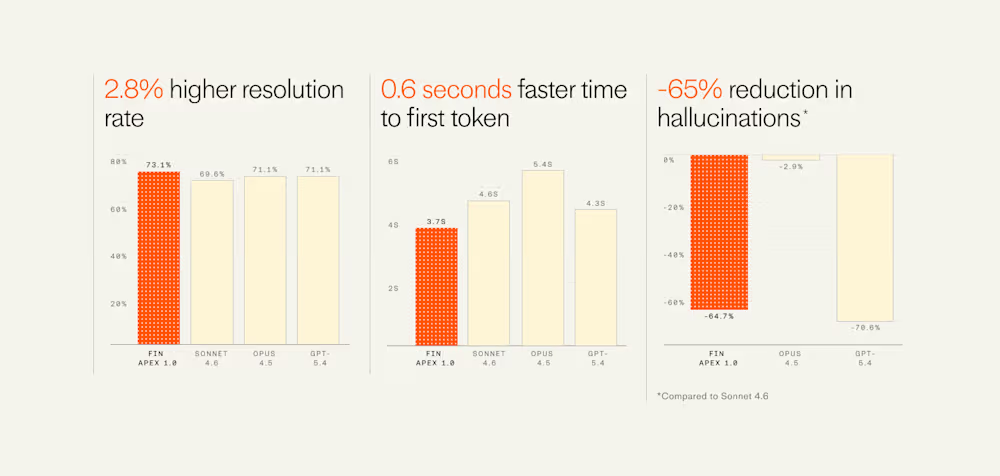
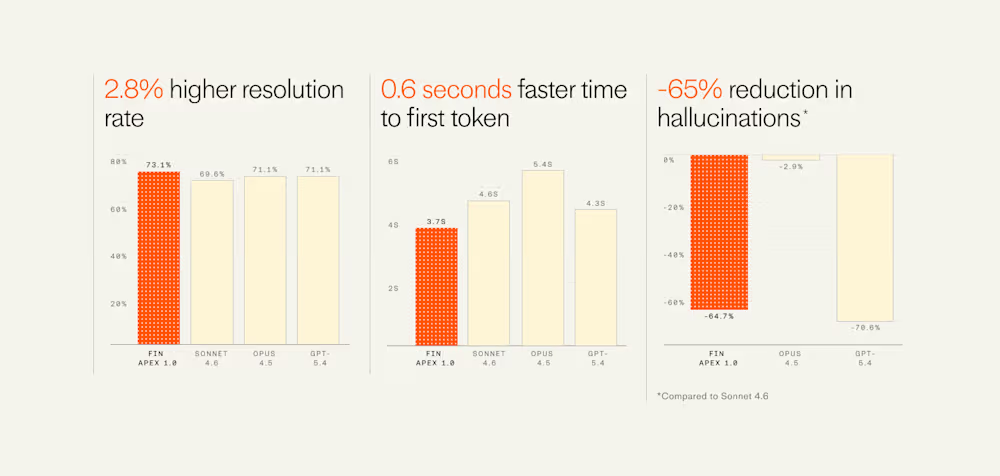
Tech6 days agoIntercom’s new post-trained Fin Apex 1.0 beats GPT-5.4 and Claude Sonnet 4.6 at customer service resolutions
-

 NewsBeat5 days ago
NewsBeat5 days agoThe Story hosts event on Durham’s historic registers
-

 Business6 days ago
Business6 days agoInstagram, YouTube Found Responsible for Teen’s Mental Health Struggle in Historic Ruling
-

 NewsBeat7 days ago
NewsBeat7 days agoTesco is selling new Cadbury Dairy Milk bar and people can’t wait to try it
-

 Sports5 days ago
Sports5 days agoSweet Sixteen Game Thread: Tide vs Michigan
-
Entertainment2 days ago
Fans slam 'heartbreaking' Barbie Dream Fest convention debacle with 'cardboard cutout' experience
-

 Entertainment4 days ago
Entertainment4 days agoLana Del Rey Celebrates Her Husband’s 51st Birthday In New Post
-
Crypto World23 hours ago
Dems press CFTC, ethics board on prediction-market insider trades
-

 Sports18 hours ago
Sports18 hours agoTallest college basketball player ever, standing at 7-foot-9, entering transfer portal
-

 Fashion7 days ago
Fashion7 days agoHow to Style Spring Like WeWoreWhat: Easy Outfit Ideas for 2026
-

 Tech2 days ago
Tech2 days agoThe Pixel 10a doesn’t have a camera bump, and it’s great
-

 Entertainment6 days ago
Entertainment6 days agoHBO’s Harry Potter Series Will Definitely Fail For One Big Reason, And It’s Not J.K. Rowling Or Snape
-

 Fashion6 days ago
Fashion6 days agoEn Vogue in Brown Leather and Tailored Neutrals by Atelier Savoir, Styled by J Bolin
-

 Crypto World1 day ago
Crypto World1 day agoU.S. rule change may open trillions in 401(k) funds to crypto
-

 Fashion6 days ago
Fashion6 days agoWhat Are Your Favorite T-Shirts for the Weekend?
-

 Fashion5 days ago
Fashion5 days agoWeekly News Update, 3.27.26 – Corporette.com
-

 Politics2 days ago
Politics2 days agoShould Trump Be Scared Strait?
-

 Sports1 day ago
Sports1 day agoWomen’s hockey camp eyes fitness boost, tactics ahead of WC 2026 campaign | Other Sports News
-

 Tech1 day ago
Tech1 day agoHow to back up your iPhone & iPad to your Mac before something goes wrong











You must be logged in to post a comment Login