Crypto World
Ethereum address poisoning spike, ‘wallets aren’t ready’ says researcher
On December 3, the Ethereum network executed the Fusaka upgrade which had one focus: “scaling without compromise.”
Gas fees, once a major impediment to Ethereum’s usability for all but those with the deepest of pockets, plummeted sharply, with transfers and swaps costing just a few cents per transaction.
Cheap transactions don’t just benefit regular users, however.
Indeed, the increased affordability of long-running address poisoning campaigns has seen losses, as well as activity, skyrocket since Fusaka.
Protos spoke to Andrey Sergeenkov, an independent researcher analysing address poisoning on Ethereum, who believes that “the wallets aren’t ready, and the protocol keeps scaling anyway.”
Cheap gas, a boon for users and scammers alike
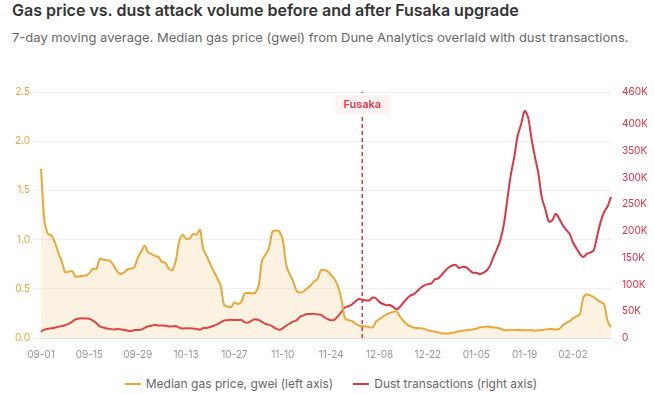
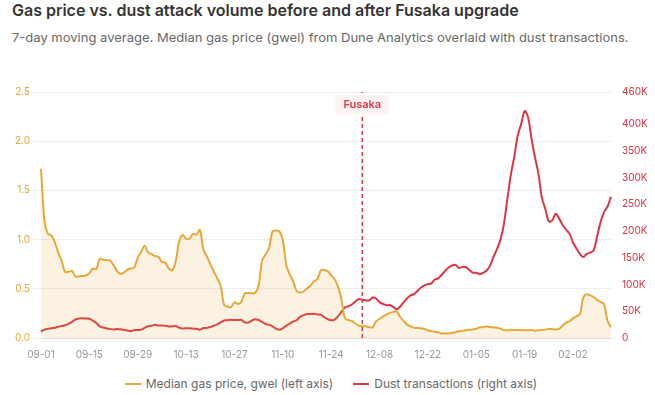
In an article published last month, Sergeenkov identified a six-fold reduction in gas costs resulting in an almost identical increase in the volume of address poisoning, from an average of 30,000 to 167,000 per day (5.6x).
The surge in transactions has, unsurprisingly, been accompanied by increased losses.
Sergeenkov tracked dust transactions of 101 tokens and identified “confirmed payoffs” over 73-day windows before and after Fusaka.
The value of funds stolen increased from $4.9 million pre-Fukasa to $63.3 million in the period after the upgrade.
He also observed a “2.6-fold increase in [the number of] successful payoff events.”
Even subtracting the largest post-Fusaka loss, a $50 million outlier just before Christmas, the total is “still $13.3M, a 2.7-fold increase over the pre-Fusaka rate.”
Sergeenkov told Protos that, since the end of the dataset used in his most recent article, there have been a number of significant losses. The top three of these were a $600,000 loss on February 17, a $157,000 loss the following day, a $30,000 loss on February 28.
In all, he identified almost $900,000 in losses from 91 victims between those discussed in his article and his response to Protos on March 9.
Adjusting for the recent losses, and ignoring the outlier, brings the average amount stolen per day to 2.1x that of the pre-Fusaka rate.
“The attack volume hasn’t slowed either,” he says, and is still picking up “200,000–350,000 poisoning transactions per day.”
While the individual transactions themselves may be cheap, the potential rewards justify splashing large sums on casting as wide a net as possible.
Read more: Copy, Paste, Rekt: Ethereum address poisoning strikes again
‘Scaling without compromise’
Ethereum’s efforts to reduce gas costs have been overwhelmingly successful.
First, demand was pushed onto cheaper, faster Layer Two (L2) networks, lowering activity on mainnet.
Though the advances in scaling (which don’t look to be slowing down) mean, in the words of Vitalik Buterin, that the “original vision of L2s and their role in Ethereum no longer makes sense.”
Later, the introductions of blobs (which did away with the ETH’s deflationary, “ultra sound” narrative) and the Fusaka upgrade, have seen the cost of gas mimic the chart of a classic DeFi slow-rug project.
Read more: Your L2 transaction fees are higher because of MEV spam, report
Sergeenkov notes that, despite a known link between low fees and attack volume, the upgrade “went ahead anyway.”
He says the “Ethereum Foundation has not proposed or implemented any protocol-level countermeasure” and Buterin “places user protection entirely at the wallet and UX layer.”
However, Sergeenkov points to research which claims that, of 53 wallets studied, only three “throw an explicit warning message” to users before transferring to address poisoning addresses.
According to Namefi CEO, Z. Victor Zhou, one potential solution is using leading zeros, making lookalike addresses much more costly and time-consuming for attackers to generate.
“One minute of your laptop’s GPU time creates an address that would cost an attacker 32 years to fake,” he claims. “The asymmetry is staggering.”
Emergent threats
Address poisoning isn’t the only attack vector which benefits from low gas costs.
Security researcher Daniel Von Fange notes that cheap gas makes for complex attack transactions which render “only the tiniest smidge of money” profitable.
“Spectacularly wasteful” MEV activity was seen to offset scaling improvements on L2 networks, negating any gas savings for regular users while looking to profit off their activity.
Other malicious behaviours can also be borne out of well-meaning upgrades.
“The system produces new attack vectors structurally, with each change to the protocol,” Sergeenkov says.
One example is EIP-7702, which brought wallet delegation capability. Wintermute research later found that 80% of addresses using the code were linked to malicious activity.
Does Sergeenkov have an antidote?
In terms of staying safe, Sergeenkov says “never copy addresses from your transaction history or a block explorer.” He also advises against making transfers if suffering from “lack of sleep, illness or anything else.”
But he has little faith that advice or educating users will be able to keep up with such “numerous and easily adaptable” attack vectors.
“What’s needed is a fundamentally different environment where users don’t have to learn how to avoid losing all their money from a single mistake. Where the risk-reward of an attack rules it out by itself.”
Got a tip? Send us an email securely via Protos Leaks. For more informed news and investigations, follow us on X, Bluesky, and Google News, or subscribe to our YouTube channel.
Crypto World
Bitcoin rangebound as altcoins rally while derivatives signal downside risk: Crypto Markets Today
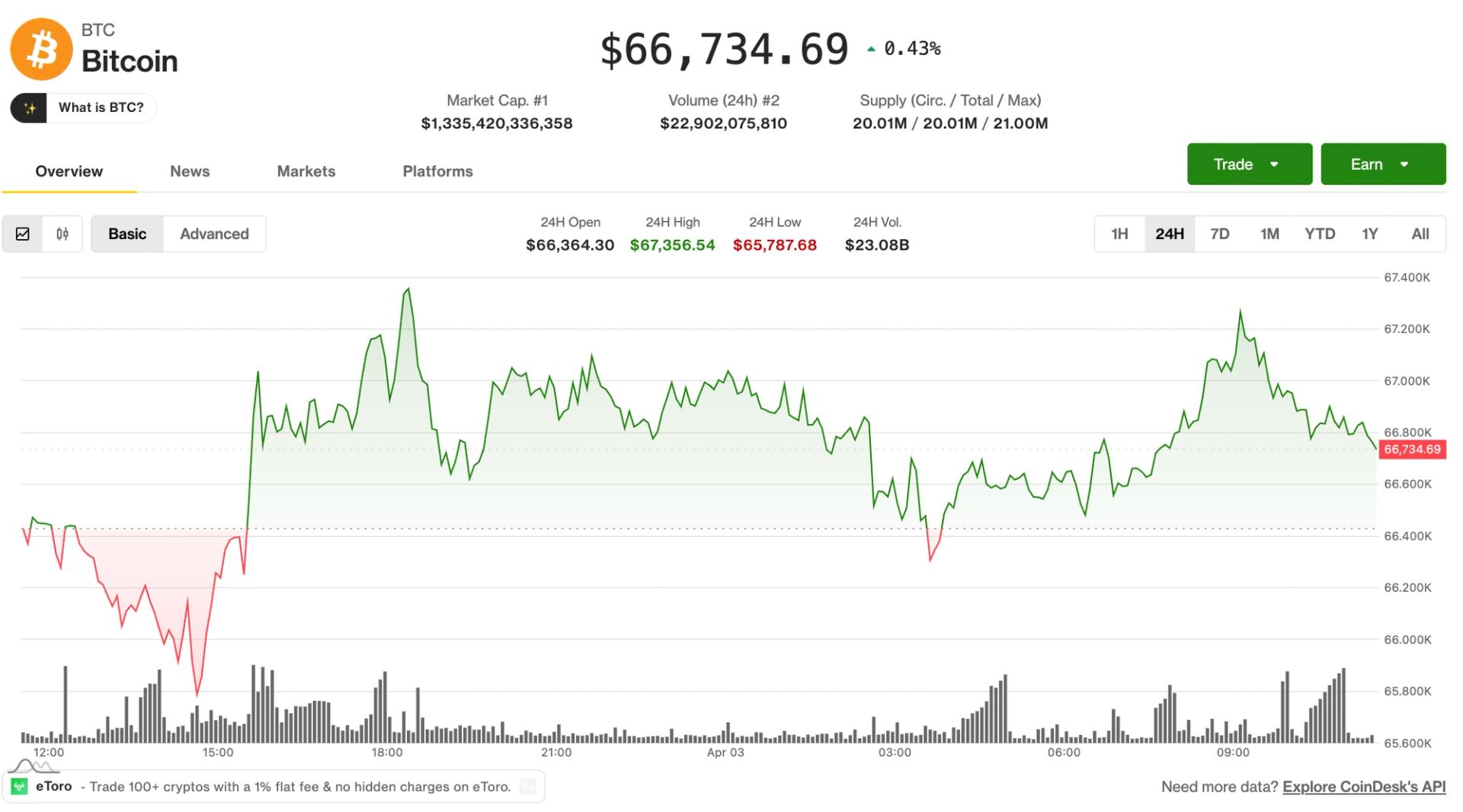
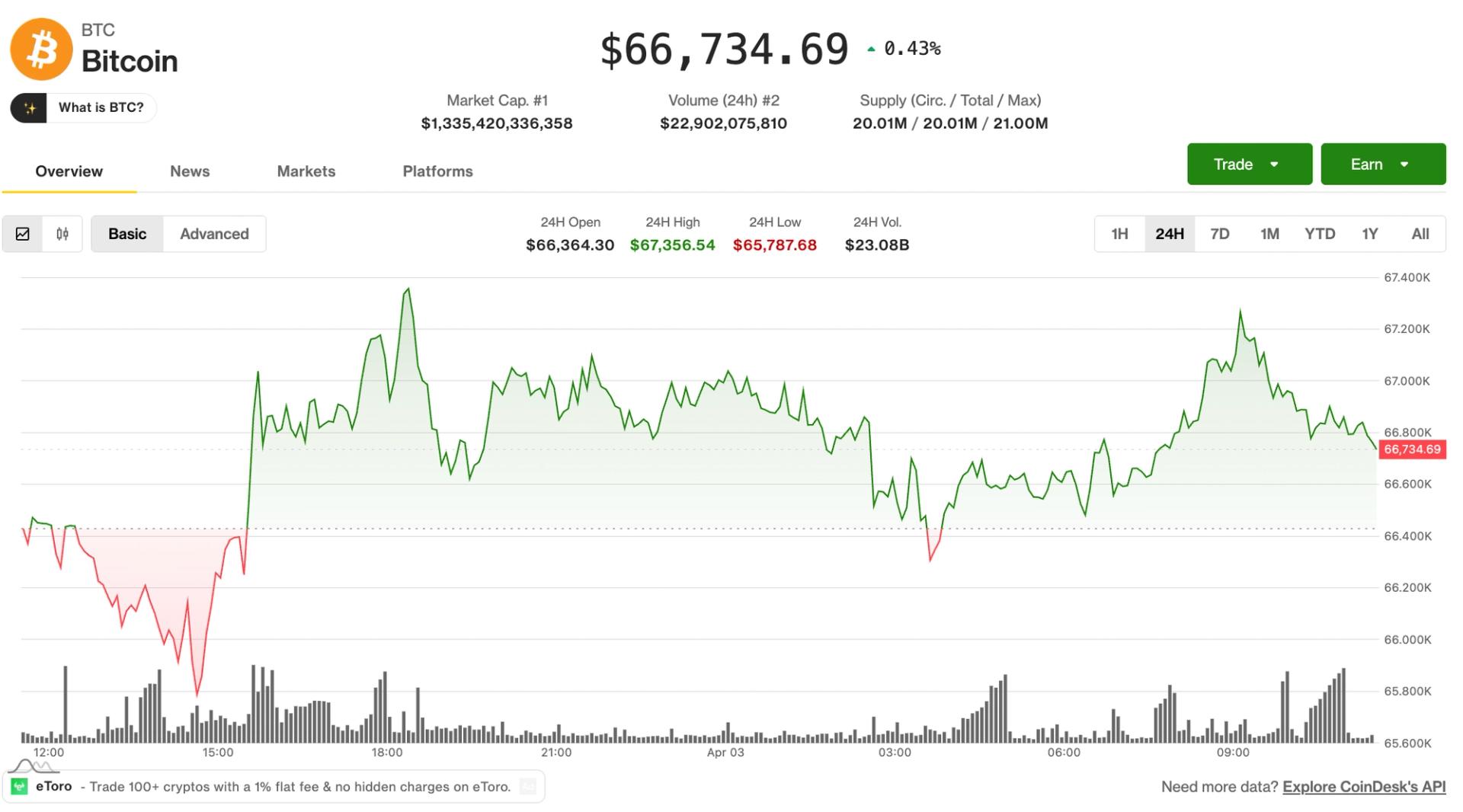
The crypto market continued to exhibit signs of choppiness on Friday, with bitcoin trading at $67,000 in the middle of a trading range that spans back to early February.
A selection of altcoins picked up during the lower liquidity Asia hours, prompting the likes of ALGO and RENDER to post double-digit gains over the past 24 hours.
But the wider picture remains the same; the crypto market is trading in a macro downtrend dating back to October, characterized by a series of lower highs nad lower lows.
U.S. equities trade flat on Friday as volatility continues to cool since Donald Trump’s comments about a potential end to the war in Iran on Monday.
Brent crude oil is trading at $109 a barrel, indicating that an end to the war is perhaps not as close as some analysts are predicting.
Derivatives Positioning
- Futures markets for Bitcoin and Ethereum remained subdued, with the extended holiday weekend keeping trading volumes thin. Open interest in both assets was largely unchanged over the past 24 hours.
- Open interest in Solana futures has climbed to over 65 million SOL, its highest level since Feb. 7. The increase, combined with negative funding rates and an OI-adjusted cumulative volume delta, suggests traders are increasingly positioning for downside, with short sellers showing greater conviction.
- Similar bearish market dynamics are present TRX and BCH.
- OI in Privacy-focused Zcash (ZEC) futures have steadied near 1.70 million ZEC for the third straight day. ZEC’s CVD is also the highest among majors. This combination suggests sustained positioning with strong directional conviction, likely driven by aggressive buying pressure.
- Bitcoin’s 30-day implied volatility index has declined to 51.28%, the lowest since Feb. The market shows no signs of panic whatsoever despite geopolitical concerns and energy market volatility.
- Ether’s volatility index has slipped to 72.55%, the lowest since Feb. 26.
- On Deribit, bitcoin and ether puts continue to trade pricier than calls, indicating a bias for downside protection.
- Glassnode said that the dealer gamma exposure below $68,000, all the way down to $50,000 is negative. This means that dealers could sell in a falling market to hedge their exposure, adding to downside volatility.
Token talk
- The altcoin market has been relatively resilient to crypto’s choppy behavior this week, certain portions of the market have outperformed bitcoin and crypto majors, particularly DeFi and AI tokens.
- The DeFi Select Index (DFX) is up by 1.3% since midnight UTC, while the CoinDesk Computing Select Index (CPUS) rose by 1.5%, beating the bitcoin-heavy benchmarks likes the CoinDesk 20 (CD20), which is up by just 0.16% on Friday.
- The outperformance of certain altcoins is symptomatic of a consolidating market. When bitcoin and the majors trade flat, traders often speculate on lower liquidity altcoins. That speculation typically grinds to a halt when bitcoin is back deciding the next major market move.
Crypto World
Pyth soars 9% following Polymarket integration. Will it rally higher?


Key takeaways
- PYTH is up 9% in the last 24 hours, outperforming other major cryptocurrencies.
- The rally comes following Pyth Network’s integration with Polymarket.
PYTH, the native coin of the Pyth Network, is one of the best performers in the crypto market over the past 24 hours. It could rally higher in the near term as the broader market recovers from Thursday’s slump.
PYTH rallies on Polymarket integration
On Thursday, Pyth Network revealed in a blog post that Polymarket, the world’s largest prediction market platform, has integrated Pyth Pro as its data source for a new suite of traditional asset contracts.
The initial offerings include gold, silver, and major equity index ETFs. Polymarket now relies on Pyth Pro’s data to power its daily up/down and daily close markets, with live price charts updated every second to ensure full transparency.
The integration has seen PYTH rally by 9% in the last 24 hours and now trades at $0.0420 per coin.
Pyth Pro provides real-time price data through WebSocket, which Polymarket samples every second to display as a live “price to beat” chart. This allows traders to monitor the market’s status relative to their position in real-time.
The selected assets span a wide range of traditional finance, including major equity indices, commodities like gold, silver, WTI crude, and natural gas, along with over a dozen high-profile U.S. equities such as TSLA, COIN, and PLTR.
Polymarket has integrated this real-time data as a key component of its perpetual futures trading platform. Pyth Pro delivers institutional-grade market data directly from top firms, ensuring it is accurate, transparent, and affordable across all asset classes and regions.
To enhance this, Pyth has partnered with industry leaders and government agencies like Cboe, Jane Street, Revolut, and the U.S. Department of Commerce. This collaboration has helped establish a new model to make market data more accessible, accurate, and transparent.
PYTH eyes $0.050 as bulls step in
The PYTH/USD 4-hour chart is bearish and efficient despite the coin adding 9% to its value in the last 24 hours.
The technical indicators have flipped bullish, indicating that the bulls are now in control of the market. The RSI of 63 is well above the neutral 50 and would enter the overbought territory if the rally persists.

The MACD lines are also within the positive region, indicating a strong bullish bias. If the rally continues, PYTH could retest the $0.050 psychological level for the first time since March 17.
However, if the bears regain control, PYTH could retest the Thursday low of $0.038 over the next few hours or days.
Crypto World
Drift Seeks Contact With The Hacker After $280M Exploit
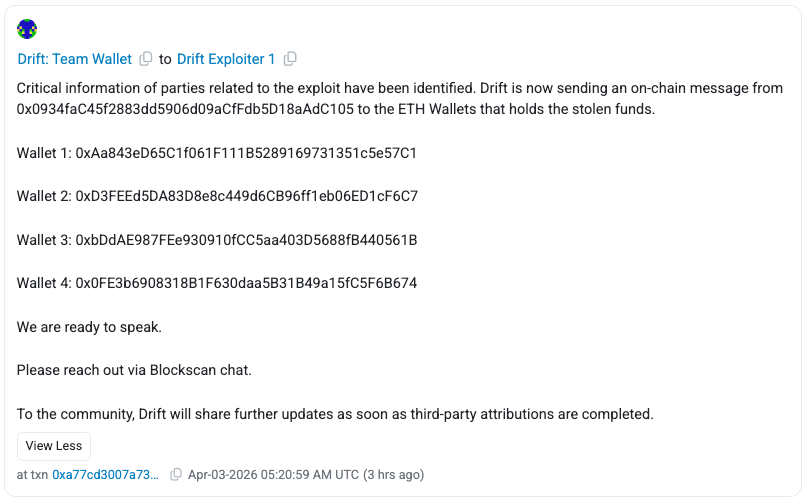
Drift Protocol, a Solana-based decentralized exchange (DEX), said Friday it had opened onchain contact with wallets tied to funds stolen in the exploit that outside firms have estimated at roughly $280 million to $286 million.
Drift said on X that it had initiated onchain contact with wallets holding the stolen Ether (ETH), seeking to open a line of communication.
The team sent onchain messages from its Ethereum address (0x0934faC) to four wallets linked to the exploiter at the time of publication, urging the attacker to reach out via Blockscan chat. “We are ready to speak,” Drift said.
Onchain messaging has become a common tactic in exploit response, allowing protocols to communicate directly with attackers while preserving anonymity. In past cases, such as the Euler Finance hack, similar outreach led to the partial recovery of funds.

Anonymous sender tries to pressure the attacker
Drift’s communication came hours after an unknown sender using the ENS name readnow.eth also reached out to wallets linked to the attacker on Thursday via onchain messages.
The sender claimed to know the identities behind the attack and demanded a payment of 1,000 ETH in exchange for withholding information.

The claims could not be independently verified and may represent an attempt to mislead or pressure the wallet holder. The incident highlights how, alongside official communications, unverified messages can circulate onchain after crypto exploits.
Solana fallout keeps spreading
According to SolanaFloor, Drift’s exploit has so far affected at least 20 Solana protocols, including the decentralized finance (DeFi) platform Gauntlet, which was estimated to be impacted to the scale of $6.4 million.
Blockchain security platform Cyvers said the impact was still expanding as of Friday morning, with no funds being recovered 48 hours past the attack.
Cyvers said that the attack was likely a “weeks-long, staged operation,” noting that the attacker set up durable nonces, a Solana feature allowing users to pre-sign transactions for future execution, days before the exploit.
Related: Crypto hackers steal $169M from 34 DeFi protocols in Q1: DefiLlama
“This closely mirrors the Bybit hack, different technique, same root issue: signers unknowingly approving malicious transactions,” Cyvers added.
Some industry observers, including Ledger chief technology officer Charles Guillemet, suggested the exploit may involve North Korea-linked actors, though details remain unconfirmed.
Magazine: Nobody knows if quantum secure cryptography will even work
Crypto World
Korea Investment & Securities Considers Coinone Stake: Report
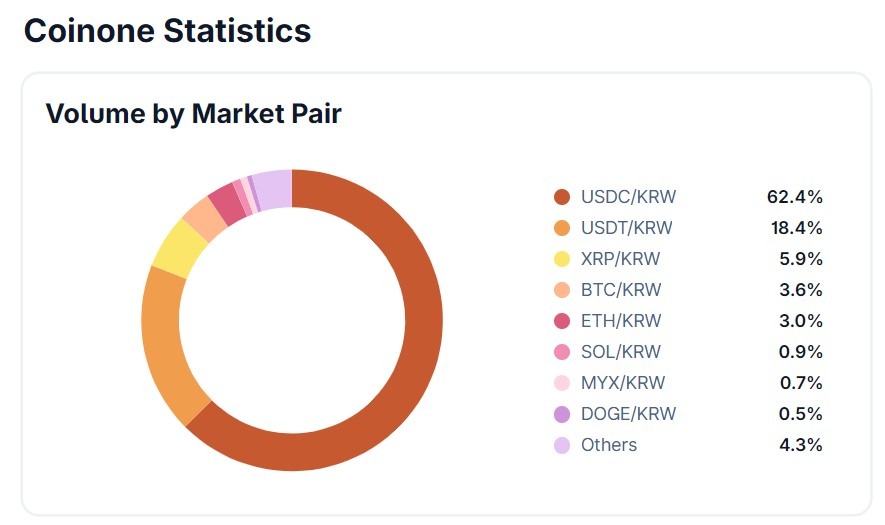
South Korean brokerage Korea Investment & Securities (KIS) is reviewing a potential stake in crypto exchange Coinone, according to Korean media reports and company comments, though no deal has been finalized.
Citing people familiar with the matter, the Korea Herald reported that KIS started engaging with regulators and politicians as part of a broader process tied to a potential investment in Coinone. Coinone also said no specific transaction had been decided.
The news comes as South Korea considers a proposal to cap major shareholders’ stakes in domestic crypto exchanges at 20%, a move that could force ownership changes across parts of the sector if enacted. Coinone Chairman Cha Myung-hoon reportedly controls about 53.44% of the exchange, meaning a stake sale could become one way to adapt if the proposed cap advances into law.
The move would position KIS alongside its rival, Mirae Asset Group, which agreed to acquire a controlling stake in crypto exchange Korbit, according to a February filing. KIS recorded a net profit of over 2 trillion won (about $1.3 billion) in 2025, making it a strong candidate for a potential stake acquisition in Coinone, Hankyung reported.

South Korea moves to cap crypto exchange ownership at 20%
The potential deal unfolds as South Korea moves to reshape ownership structures in its crypto exchange market.
On March 4, the South Korean government and ruling party agreed on a plan to cap ownership stakes of major shareholders in local exchanges at 20%. According to Herald Economy, the Democratic Party of Korea’s digital asset task force and the Financial Services Commission (FSC) agreed to set the maximum shareholding limit at 20% after discussions.
Related: South Korea tax agency seeks private crypto custodian after security lapses
Under the proposal, exchanges would have three years from the law’s enforcement to adjust their ownership structures if the measure is passed.
With Cha holding more than half of Coinone, the proposed cap could eventually require him to reduce his stake. The Herald said he could still retain management control even if a sale proceeds.
The reported talks follow other recent moves by major South Korean companies to secure positions in the crypto sector.
In late 2025, Naver Financial disclosed plans for a roughly $10.3 billion all-stock deal to acquire Dunamu, the operator of Upbit. On March 30, Naver Financial delayed its planned share swap with Dunamu, as regulatory reviews continued and trading volumes declined.
Magazine: Banks want to run Vietnam’s crypto exchanges, Boyaa’s $70M BTC plan: Asia Express
Crypto World
Bitcoin Profit Supply Nears Bear-Market Levels, Signaling Downturn

Bitcoin’s on-chain profit-and-loss metrics are edging toward the bear-market territory observed in prior cycles, according to CryptoQuant data analyzed by a CryptoQuant analyst known as Darkfost. The latest figures show about 11.2 million BTC in profit, with the trough of the last bear market recording roughly 9 million BTC in profit. On the loss side, around 8.2 million BTC are currently in loss, a level that Glassnode data indicate has not been seen since late 2022. Darkfost notes that during the previous bear market, the profit supply peaked around 10.6 million BTC, a level the market now approaches from a different angle.
The juxtaposition of sizable profit supply and rising losses is fueling a nuanced debate among analysts about what comes next for BTC. While some see the on-chain configuration as hinting at undervaluation similar to prior downturns, others caution that the signals reflect mounting market stress and may precede a period of consolidation rather than an imminent bottom.
Key takeaways
- Bitcoin profit-supply stands near bear-market-like thresholds, with approximately 11.2 million BTC in profit and about 8.2 million BTC in loss, according to CryptoQuant and Glassnode data.
- In the last bear market, profit supply reached around 10.6 million BTC, suggesting current levels are approaching historical extremes but not identical to prior cycles.
- Analysts diverge on interpretation: some see signs of undervaluation, while others flag rising market stress and potential pre-bottom consolidation.
- BTC has fallen roughly 52% from its all-time high this cycle, a drawdown notably smaller than the 77%–84% declines seen in many earlier bear markets.
- Macro backdrop remains challenging: a stronger U.S. dollar and tighter global liquidity could delay a sustained recovery, with rate cuts not broadly anticipated until late 2026 or 2027.
On-chain signals tightening toward bear-market parity
CryptoQuant data analyzed by Darkfost indicate that Bitcoin’s profit supply has climbed toward levels historically associated with bear markets. The current figure sits around 11.2 million BTC in profit, while the loss-side metric sits near 8.2 million BTC. Glassnode data corroborate that the loss-supply level is at a point not seen since late 2022. Darkfost emphasized that the last bear market had as much as 10.6 million BTC in profit, underscoring how the current scene sits near a store of historical extremes but remains distinct from past dynamics.
These metrics do not automatically spell doom, but they do illuminate a market where profit-bearing coins are plentiful even as a substantial portion of supply sits in loss. That configuration can complicate the price path, since a broad cohort of holders remains profitable, while others are under water—potentially influencing sentiment, risk tolerance, and selling pressure as conditions evolve.
Different readings: undervaluation versus market stress
In a contrasting view, Andri Fauzan Adziima, the research lead at the Bitrue exchange, argues that the data point to rising market stress rather than an imminent undervaluation. He notes that true capitulation bottoms historically accompany sharper pain: in 2022, supply in loss exceeded 50% and profit hovered around 45% or lower, with metrics such as net unrealized profit/loss (NUPL) and market value to realized value ratio (MVRV) at extreme levels.
“Current data points to early/mid-bear transition (potential structural bottom near $55,000), with more downside or consolidation likely before a full reset.”
Separately, coverage from Cointelegraph highlighted that Fidelity described Bitcoin’s drawdown this cycle as less dramatic than in some past cycles, illustrating the divergent interpretations across the market.
Beyond these readings, Bitcoin’s drawdown from its all-time high this cycle stands at about 52%, a smaller drop than typical bear markets, which have seen declines of approximately 77% to 84% from cycle highs. Such dynamics can be interpreted as evidence of a more resilient near-term setup, though they do not by themselves guarantee a sustained rally or a durable bottom.
Macro backdrop: dollar strength and liquidity constraints
Macro factors are shaping how traders assess on-chain signals. Timothy Peterson, a well-known commentator on Bitcoin markets, observed that BTC tends to struggle when the U.S. dollar is strong and the Chinese yuan is weak, a situation that tightens global liquidity and nudges capital toward cash and government bonds when yields remain elevated. The implication is that dollar strength acts as a headwind for risk assets, including Bitcoin, even as liquidity conditions shift with policy moves.
Peterson notes that a meaningful improvement for BTC would come only when U.S. interest rates fall and dollar yields lose their appeal, a development he expects is unlikely before the second half of 2026 or, more plausibly, in 2027. The U.S. dollar index (DXY) has risen about 5% over the past two months, according to data tracked on TradingView, adding to the macro hurdles facing a rapid BTC recovery.
Taken together, the on-chain signals and macro backdrop present a nuanced landscape: a market that, on one hand, shows pockmarks of bear-market-like behavior in profit metrics, but, on the other, is contending with a robust dollar and cautious liquidity that can prolong a period of consolidation rather than deliver a quick reset. Investors should watch for shifts in dollar dynamics, policy expectations, and changes in on-chain metrics such as NUPL and MVRV as new data come in over the coming quarters.
Looking ahead, the question remains what path Bitcoin will take as macro conditions evolve. If on-chain indicators begin to align with a genuine bottom—supported by a sustained weakening of the dollar and a more favorable liquidity environment—the next phase could reflect a gradual re-rating rather than an abrupt rebound. Conversely, if the macro regime remains restrictive and stress signals persist or intensify, the market may continue to drift below recent highs before any meaningful reset materializes.
Readers should keep an eye on evolving rate expectations, liquidity conditions, and the trajectory of on-chain risk metrics. The coming quarters will clarify whether Bitcoin’s current configuration marks the end of a broader drawdown or merely a protracted period of accumulation before a more decisive breakout.
Crypto World
CFTC and DOJ sue three states over prediction market oversight


The United States Commodity Futures Trading Commission and the Department of Justice have filed lawsuits against Illinois, Connecticut, and Arizona over the federal government’s authority to regulate prediction markets.
Summary
- The CFTC and Department of Justice have sued three states, arguing that prediction markets fall under exclusive federal derivatives oversight.
- Illinois and other states had issued cease and desist orders, claiming event contracts violated local gambling laws and licensing rules.
According to a complaint filed against Illinois Governor JB Pritzker, Attorney General Kwame Raoul, and the Illinois Gaming Board, the state gaming board improperly classified event contracts as “wagers” or “sports betting” instead of swaps.
In the lawsuits, the CFTC maintains that it has “exclusive jurisdiction” to regulate “Designated Contract Markets (DCMs),” which it says extend to prediction platforms under the Commodity Exchange Act (CEA).
Per the regulator, Illinois’s move to shut down such platforms “intrudes on the exclusive federal scheme Congress designed to oversee national swaps markets, prompted by the evolution of national financial markets and repeated conflicts with state law.”
“Unless restrained and enjoined by the court, defendants are likely to continue their attempts to subvert federal law and the exclusive jurisdiction to regulate event contract swaps conferred on the CFTC by Congress,” the lawsuit added.
The case stems from cease and desist letters issued by the states and their gaming regulators last year against platforms including Kalshi and Polymarket. The letters claimed that the contracts violated local gambling laws and licensing requirements.
Commenting on the developments, CFTC Chairman Mike Selig described the actions as “aggressive and overzealous attempts to overstep the CFTC,” in a separate statement after the lawsuits were filed.
“Our action today is meant to ensure we are able to effectively regulate the markets that Congress intended us to exclusively oversee,” he added.
Over the past year, at least 11 U.S. states, including Arizona, Nevada, Illinois, Maryland, New Jersey, Montana, Ohio, Connecticut, Tennessee, New York, and Massachusetts, have filed actions against prediction market operators.
Simultaneously, some lawmakers are advancing legislative proposals that would ban sports-related event contracts, while others seek to restrict participation in prediction markets tied to war.
Despite the legal pressure, prediction markets are witnessing rapid growth. As previously reported by crypto.news, transaction activity surged, with volumes increasing by more than 2,800% from the same period last year.
Crypto World
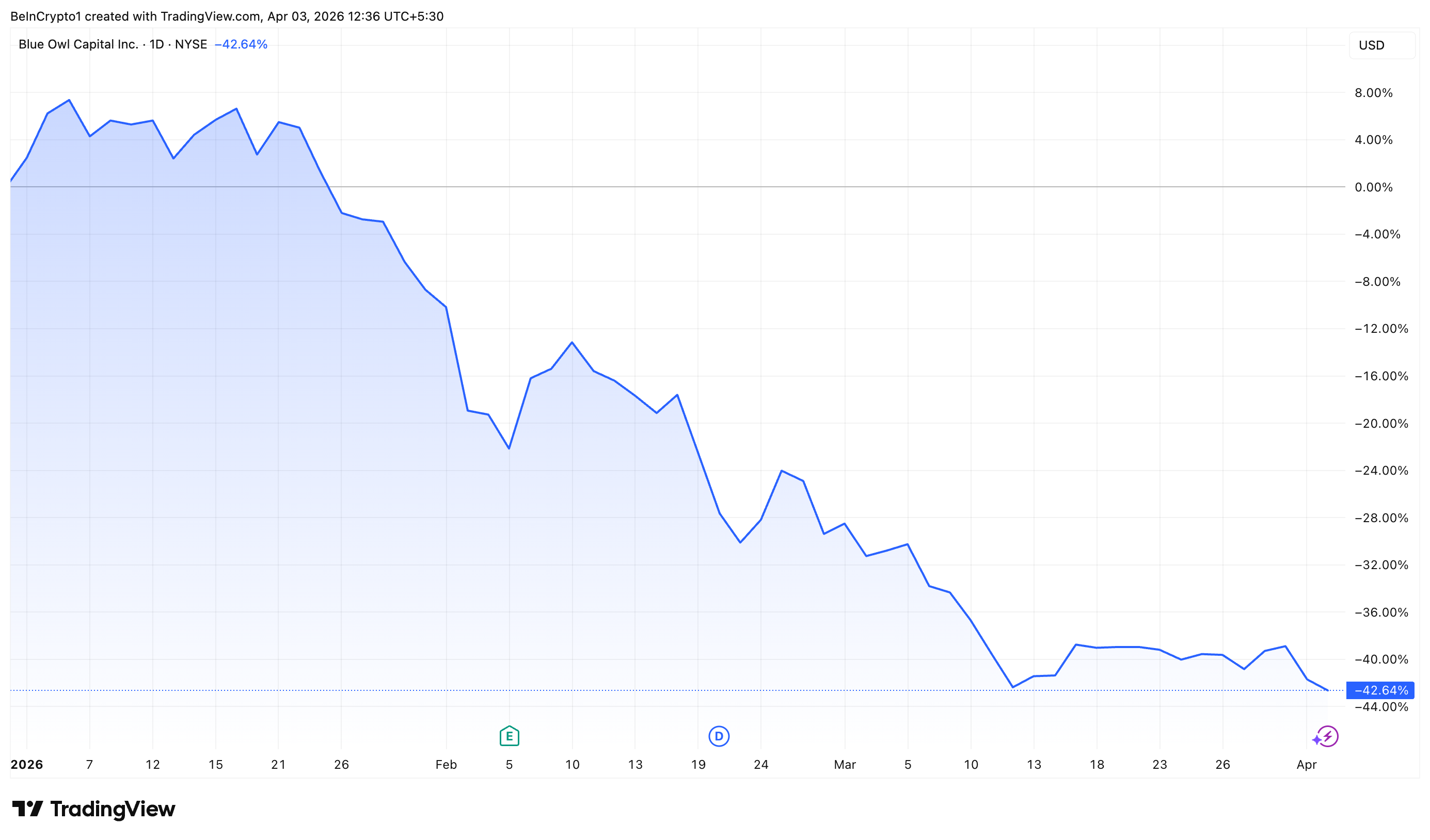
Blue Owl Stock Crashes to All-Time Low After $5.4 Billion Redemption Requests
Blue Owl Capital (OWL) stock sank to a fresh all-time low of $7.95 on April 2. This comes after the firm told investors it would cap withdrawals on two of its private credit funds, following $5.4 billion in redemption requests in the first quarter alone.
The private capital manager has now lost more than 40% of its market value year-to-date, as investor confidence in the $1.8 trillion private credit sector continues to erode.
Blue Owl disclosed that its $36 billion flagship fund, Blue Owl Credit Income Corp (OCIC), received redemption requests totaling 21.9% of shares outstanding during the first quarter.
It’s technology-focused Blue Owl Technology Income Corp (OTIC) saw an even more dramatic surge. Investors sought to withdraw 40.7% of shares from this $6.2 billion fund. In both vehicles, the firm opted to cap redemptions at 5%.
“We continue to observe a meaningful disconnect between the public dialogue on private credit and the underlying trends in our portfolio,” Blue Owl noted in the shareholder letters.
Blue Owl is far from alone. Apollo Global Management imposed an identical 5% cap after receiving redemption requests exceeding 11% of outstanding shares. BlackRock has also gated withdrawals from its $26 billion fund.
Follow us on X to get the latest news as it happens
Bloomberg data suggests that withdrawal requests across more than a dozen private credit funds have totaled approximately $13 billion as of late March. Private capital managers have faced mounting pressure as market turbulence and fears over AI-driven disruption to software borrowers push investors toward the exits.
The post Blue Owl Stock Crashes to All-Time Low After $5.4 Billion Redemption Requests appeared first on BeInCrypto.
Crypto World
Consolidation Ahead of NFP: Commodity Currencies Search for Direction

Commodity-linked currencies have entered a consolidation phase following recent directional moves, as market participants adopt a wait-and-see approach ahead of key US labour market data. Current price action reflects a balance between ongoing demand for the US dollar and attempts at a corrective rebound amid an uncertain fundamental backdrop.
Geopolitical tensions remain an additional factor influencing the market, sustaining elevated uncertainty and increasing volatility across commodity assets. Fluctuations in energy prices continue to affect commodity currencies, limiting the development of sustained trends and making market direction increasingly dependent on incoming macroeconomic data.
Traders have also taken note of yesterday’s remarks by Donald Trump, which included signals of potential shifts in foreign economic policy and approaches to international relations. Additional comments regarding a willingness to intensify pressure on Iran in the coming weeks have further raised geopolitical uncertainty. While the immediate market reaction has been relatively muted, such rhetoric increases the likelihood of renewed demand for the US dollar as a safe-haven asset, particularly if accompanied by strong US macroeconomic data.
Investor focus now turns to the upcoming US employment report. Key releases include Non-Farm Payrolls, the unemployment rate, and wage growth figures, all of which traditionally have a significant impact on currency markets. Strong data could revive bullish momentum in the dollar, while weaker figures may reinforce corrective sentiment and put additional pressure on the US currency.
AUD/USD
After declining over the past three weeks, AUD/USD has found support just above the 0.6800 level. A “bullish engulfing” pattern has formed on the daily timeframe, allowing buyers to push the pair towards 0.6960. However, the rally lost momentum following comments from the US President, although prices have managed to hold above 0.6900. Technical analysis suggests a potential test of resistance in the 0.6960–0.6980 range. A break below 0.6900 could lead to a retest of 0.6830.
Key events that may influence AUD/USD in the coming sessions:
- today at 15:30 (GMT+3): US average hourly earnings
- today at 15:30 (GMT+3): US Non-Farm Payrolls
- today at 16:45 (GMT+3): US services PMI

NZD/USD
NZD/USD has been trading sideways for several sessions. Buyers continue to defend support near 0.5700, but a strong fundamental catalyst would be required to trigger a downside breakout and extend the bearish move. A sustained move above 0.5780 could open the way for a deeper corrective recovery.

Overall, the market remains in a holding pattern ahead of a key macroeconomic event. The direction of commodity currencies will largely depend on the outcome of US labour market data, alongside the broader geopolitical backdrop, which continues to influence global financial markets. At present, trading activity remains subdued due to the holiday period, reducing the presence of major market participants. Under such conditions, the risk of false breakouts and short-term volatility spikes increases, calling for additional caution when interpreting price movements.
Trade over 50 forex markets 24 hours a day with FXOpen. Take advantage of low commissions, deep liquidity, and spreads from 0.0 pips (additional fees may apply). Open your FXOpen account now or learn more about trading forex with FXOpen.
This article represents the opinion of the Companies operating under the FXOpen brand only. It is not to be construed as an offer, solicitation, or recommendation with respect to products and services provided by the Companies operating under the FXOpen brand, nor is it to be considered financial advice.
Crypto World
The ultimate passive income showdown of 2026
Disclosure: This article does not represent investment advice. The content and materials featured on this page are for educational purposes only.
AI trading platforms like ConfluxCapital gain ground as investors shift from cloud mining to smarter income strategies.
Summary
- Investors shift from cloud mining to AI-driven platforms like ConfluxCapital for more stable passive crypto income.
- ConfluxCapital uses algorithms to automate trading, improving speed, efficiency, and decision-making over manual strategies.
- The platform offers a $20 bonus, strong security, and flexible withdrawals, appealing to both new and experienced users.
Amidst the persistent volatility of the cryptocurrency market, an increasing number of investors are beginning to re-evaluate various avenues for generating passive income.
In recent years, “cloud mining” was widely regarded as a popular entry point for the average individual to participate in crypto mining; however, as the market matures and technology advances, AI-driven quantitative strategy platforms — such as ConfluxCapital — are gradually emerging as the new mainstream choice.
A transparent distance separates cloud mining from AI quantitative trading
The profitability logic of cloud mining is built upon opaque hash rate leasing arrangements; hidden fees erode anywhere from 30% to 60% of returns, invested capital becomes locked once deposited, and the majority of platforms lack third-party security certification — precisely the root cause behind the rampant prevalence of Ponzi schemes in this sector.
Investors are left to passively rely on the appreciation of BTC prices, with no means to verify whether the mining farms they are investing in actually exist.
AI quantitative trading, conversely, is a completely different proposition: it is grounded in algorithmic trading within open markets, featuring traceable strategies and transparent returns, with funds available for withdrawal at any time, provided certain conditions are met.
Its two-way trading mechanism enables profitability in both bull and bear markets, while institutional-grade security protocols — bolstered by insurance coverage — offer new users a risk-free, zero-cost registration experience.
In short, cloud mining forces investors to gamble on market direction and the integrity of the platform; AI quantitative trading empowers users to rely on algorithms and transparent rules.
What is the ConfluxCapital quantitative strategy?
ConfluxCapital is an automated trading platform powered by artificial intelligence and quantitative financial models. Its core function lies in utilizing algorithms to analyze market data and automatically execute trades at the optimal moment.
Compared to manual trading, quantitative strategies offer greater stability and decisive execution, enabling the completion of complex trading decisions within extremely short timeframes. The platform integrates a dual-layer security system featuring McAfee® and Cloudflare®; new users receive a $20 trial bonus upon registration, and funds can be withdrawn at any time once the account balance reaches $100.
ConfluxCapital simplifies complex quantitative trading into three steps:
Step 2: Choose a Strategy Package: The platform offers a variety of quantitative strategy packages to suit different capital sizes and risk appetites.
| Strategy Name | unit price | Days | Total Revenue |
| Starter Strategy | $100 | 2 days | $100+$6 |
| Basic Strategy | $600 | 5 days | $600+$45 |
| Advanced Strategies | $5,000 | 15 days | $5,000+$1,215 |
| Elite Strategy | $25,000 | 25 days | $25,000+$11,250 |
| Quantum Strategy | $90,000 | 20 days | $90,000+$36,000 |
| Infinite Strategy | $200,000 | 25 days | $200,000+$110,000 |
Step 3: Activate AI and Enjoy Returns: After purchasing a strategy package, profits are automatically credited to an account the following day. Once the account balance reaches $100, users can withdraw funds to their personal cryptocurrency wallet or continue purchasing strategy packages to earn more profits.
ConfluxCapital: Why the Best Choice for 2026?
Platform Core Advantages
Founded in 2023 and headquartered in London, UK, ConfluxCapital is an AI-driven quantitative trading platform. Its core advantages are reflected in five aspects:
- Fully Managed AI Trading
The platform adopts a fully managed model. The AI system handles all market analysis, strategy execution, and trade scheduling, allowing users to enjoy automated trading without needing to master complex trading strategies or algorithm configurations.
- Institutional-Grade Infrastructure
The system runs on institutional-grade infrastructure, supporting the stability requirements of the cryptocurrency market 24/7. It employs dual security protection from McAfee® and Cloudflare®.
By simultaneously executing automated long and short strategies, it can profit in different market directions—even in a deep downtrend, the system can continue to profit through short-selling strategies.
- Transparent Operations Built around five core principles: Transparency (through visible performance metrics), Reliability (based on institutional-grade infrastructure), Ease of Use (reducing the complexity of getting started), Security (through risk control), and Performance (driven by quantitative strategies).
Summary
In today’s ever-evolving crypto market, what truly sets participants apart is no longer merely “holding assets,” but rather “how one employs strategy.”
Cloud mining represents a past opportunity; quantitative trading, conversely, constitutes the core competitive advantage of the future.
For more information, visit the official website and download the app.
Email: [email protected]
Disclosure: This content is provided by a third party. Neither crypto.news nor the author of this article endorses any product mentioned on this page. Users should conduct their own research before taking any action related to the company.
Crypto World
Q1 DeFi Hackers Stole $169M Across 34 Protocols, DefiLlama
The first quarter of 2026 saw crypto hackers siphon more than $168.6 million from 34 DeFi protocols, according to DefiLlama’s quarterly tally. The figure marks a sharp decline from the same window in 2025, which recorded roughly $1.58 billion in losses, largely driven by a $1.4 billion breach at Bybit.
Notable incidents in Q1 2026 included a $40 million private-key compromise at Step Finance in January, a $26.4 million ether drain from Truebit caused by a smart contract manipulation on January 8, and a March 21 private-key attack targeting stablecoin issuer Resolv Labs. DefiLlama notes that even a handful of high-value hacks can shape quarterly totals, underscoring the ongoing risk landscape in DeFi security.
Key takeaways
- DefiLlama records $168.6 million stolen across 34 DeFi protocols in Q1 2026, signaling a quieter quarter for hacks compared with 2025.
- The largest single incident was Step Finance’s $40 million private-key compromise in January.
- Bybit’s $1.4 billion breach in Q1 2025 dwarfed this quarter’s tally, illustrating how a few mega-hacks can skew year-over-year comparisons.
- Security experts caution that cyber threats in crypto correlate with market cycles and liquidity concentration, not with calendar quarters, emphasizing the need for continuous defense.
DefiLlama tally and incident snapshots
DefiLlama’s dataset highlights 34 security breaches across DeFi protocols in the first three months of 2026, totaling about $168.6 million in stolen funds. The quarter’s largest incident was Step Finance’s $40 million private-key compromise in January, followed by a $26.4 million Ethereum loss from a Truebit vulnerability on January 8. A third notable case involved a private-key breach targeting Resolv Labs, a stablecoin issuer, on March 21. The concentration of losses around a few high-value breaches demonstrates how theDeFi security landscape can be shaped by a small number of outsized events even as total losses remain lower than a year earlier. For context on the data source, see DefiLlama’s hack tracker at DefiLlama hacks.
Attacker incentives rise with liquidity and market activity
Analysts point to market dynamics as a core driver of cybercrime activity in crypto. Nick Percoco, chief security officer at Kraken, told Cointelegraph that threat actors tend to intensify during market cycles and around major product launches, when more liquidity and value are at stake.
“Bull markets, major product launches and fast-moving growth phases all create more attractive conditions for attackers because more value is at stake and new infrastructure can introduce risk.”
“That said, attacks are not confined to just these periods. Vulnerabilities can be exploited in any market environment, particularly in complex or rapidly evolving systems, underlining that security in crypto must be continuous.”
The takeaway is clear: as long as liquidity concentrates and new tech enters the ecosystem, attackers will adapt. The industry’s challenge is sustaining rigorous security practices across evolving platforms and infrastructures.
Threat actors and the evolving risk landscape
North Korea-linked actors have long been a persistent threat to crypto investors and Web3-native companies. Attacks attributed to these groups have grown in visibility, including a high-profile Drift Protocol incident described as involving a private-key leak that led to an estimated $285 million in losses. Security experts describe the current threat landscape as a broad and evolving mix—ranging from highly coordinated groups targeting core infrastructure to opportunistic hackers scanning for weaknesses in smart contracts and client-facing systems.
As one industry voice summarized, “the most attractive targets tend to be those combining large concentrations of value, technical complexity and gaps in operational security.” The transparency of crypto networks can also aid opportunistic attackers in spotting emerging weaknesses, underscoring the need for vigilant, ongoing security measures. In tandem with these dynamics, researchers have warned that 2026 could see more credential theft, social engineering, and AI-powered attacks, elevating the overall risk profile for users, builders, and investors alike. A related Immunefi security report notes that hacked tokens often suffer substantial price declines and rarely recover, highlighting the lasting impact of breaches. See the related piece here: Hacked crypto tokens drop 61% on average and rarely recover, Immunefi report says.
As Q1 2026 closes, the industry faces a critical test: can security teams keep pace with rapid innovation and increasing attack surface, or will the trend towards bigger, more sophisticated exploits outpace defenders?
Readers should watch for ongoing upgrades in key management, more robust credential protection, and collaborative threat intelligence efforts across exchanges and projects as the market moves forward. The evolving threat landscape will continue to shape risk assessments, investment decisions, and security priorities in the months ahead.
-

 NewsBeat7 days ago
NewsBeat7 days agoThe Story hosts event on Durham’s historic registers
-

 NewsBeat16 hours ago
NewsBeat16 hours agoSteven Gerrard disagrees with Gary Neville over ‘shock’ Chelsea and Arsenal claim | Football
-

 Sports7 days ago
Sports7 days agoSweet Sixteen Game Thread: Tide vs Michigan
-
Entertainment4 days ago
Fans slam 'heartbreaking' Barbie Dream Fest convention debacle with 'cardboard cutout' experience
-

 Entertainment6 days ago
Entertainment6 days agoLana Del Rey Celebrates Her Husband’s 51st Birthday In New Post
-

 Crypto World2 days ago
Crypto World2 days agoGold Price Prediction: Worst Month in 17 Years fo Save Haven Rock
-
Crypto World3 days ago
Dems press CFTC, ethics board on prediction-market insider trades
-

 Tech4 days ago
Tech4 days agoThe Pixel 10a doesn’t have a camera bump, and it’s great
-

 Sports3 days ago
Sports3 days agoTallest college basketball player ever, standing at 7-foot-9, entering transfer portal
-

 Tech3 days ago
Tech3 days agoEE TV is using AI to help you find something to watch
-

 Fashion5 days ago
Fashion5 days agoAmazon Sundays: Soft Spring Layers
-

 Business11 hours ago
Business11 hours agoNo Jackpot Winner and $194 Million Prize Rolls Over
-

 Business1 day ago
Business1 day agoLogin and Checkout Issues Spark Merchant Frustration
-

 Tech5 days ago
Tech5 days agoElon Musk’s last co-founder reportedly leaves xAI
-

 Crypto World3 days ago
Crypto World3 days agoU.S. rule change may open trillions in 401(k) funds to crypto
-

 Tech3 days ago
Tech3 days agoHow to back up your iPhone & iPad to your Mac before something goes wrong
-

 Tech4 days ago
Tech4 days agoAvatar Legends: The Fighting Game comes out in July and it looks pretty slick
-

 Tech4 days ago
Tech4 days agoApple will hide your email address from apps and websites, but not cops
-

 Politics4 days ago
Politics4 days agoShould Trump Be Scared Strait?
-

 Tech3 days ago
Tech3 days agoFlipsnack and the shift toward motion-first business content with living visuals









You must be logged in to post a comment Login