Crypto World
Ethereum (ETH) Price Analysis: Major Whales Acquire 700K ETH Amid Bullish Technical Signals

Key Highlights
- Large Ethereum holders accumulated approximately 700K ETH from Thursday through Monday
- Spot ETH ETFs saw continuous inflows for eight days straight, totaling $493.7 million
- Bitmine acquired 101,627 ETH in their biggest weekly purchase of 2026
- The SuperTrend technical indicator turned bullish for the first time since the beginning of 2025
- Negative funding rates persisted for six consecutive days, creating downward pressure below $2,400
Ethereum is currently hovering near $2,300 following a period marked by substantial whale buying activity and robust ETF capital inflows, though futures market dynamics continue to constrain upward price movement.
Data from CryptoQuant reveals that addresses containing over 10,000 ETH added close to 700,000 ETH to their holdings from Thursday through Monday. Exchange reserves of Ethereum have declined by approximately 458,000 ETH since Thursday, indicating strengthening demand from buyers.
Institutional participation has also intensified. US-based spot Ethereum ETFs registered their eighth consecutive day of positive net inflows, accumulating a combined $493.7 million, based on data from SoSoValue.
Bitmine Immersion Technologies executed the year’s largest weekly ETH acquisition, purchasing 101,627 ETH. This transaction elevated their aggregate holdings to 4.976 million ETH. Chairman Tom Lee of Bitmine suggested that the cryptocurrency bear market might be nearing its conclusion sooner than market consensus anticipates, referencing historical cycle patterns dating back to 2015.
Bitmine Adds 101,627 ETH in Biggest Weekly Accumulation in 4 Months
Bitmine Immersion Technologies added 101,627 ETH last week, marking its fastest pace of accumulation since the week of December 15, 2025. As of April 19, 2026, the company holds a total of 4,976,485 ETH,… pic.twitter.com/j6EGixRZTK
— Wu Blockchain (@WuBlockchain) April 20, 2026
Lee highlighted that each cryptocurrency bear market since 2015 has aligned with equity market corrections exceeding 20%. By contrast, the 2026 equity pullback measured just 8%, forming the basis of his argument that the present downturn could prove more abbreviated.
Smart money analytics platform Lookonchain identified multiple significant whale movements throughout the week. Among them, a freshly created wallet pulled 35,000 ETH off Binance before moving the assets to custodial service BitGo.
Technical Indicator Turns Positive
Crypto analyst Ali Martinez shared on X that Ethereum’s daily SuperTrend indicator has switched to bullish territory for the first time since the start of 2025. Martinez observed that the previous occurrence of this technical flip was followed by an extended uptrend. He additionally noted that Bitcoin has yet to breach its corresponding SuperTrend resistance threshold.
SuperTrend flips bullish on Ethereum $ETH for the first time in over a year. pic.twitter.com/hMIDJ6ojrr
— Ali Charts (@alicharts) April 20, 2026
Derivatives Market Creates Headwinds
Notwithstanding robust demand in spot markets, Ethereum funding rates remained in negative territory for six consecutive days. This condition indicates that derivatives market participants maintain a bearish stance, contributing to price weakness below the $2,400 level.
Over the preceding 24-hour period, ETH experienced $53.4 million in total liquidations. Long position liquidations accounted for the majority at $28.4 million.
Examining the four-hour timeframe, ETH is positioned above its 20-period, 50-period, and 100-period exponential moving averages, which are grouped between $2,268 and $2,323. Immediate resistance is located at $2,388, while support levels are found at $2,267 and $2,263.
The 14-day Relative Strength Index registers 55, suggesting a slight advantage for buyers over sellers. Conversely, both the 9-day Stochastic and 14-day Stochastic RSI oscillators are positioned around 40, indicating diminishing upward momentum.
Over the past 30 days, ETH has climbed from approximately $2,155 to above $2,320, though it has retreated roughly 2% on the weekly timeframe from a peak of $2,450.
Crypto World
Ethereum Foundation Launches Clear Signing Standard


The initiative, anchored by ERC-7730 and a new attestation framework, aims to make human-readable transactions the default across wallets and protocols.
Crypto World
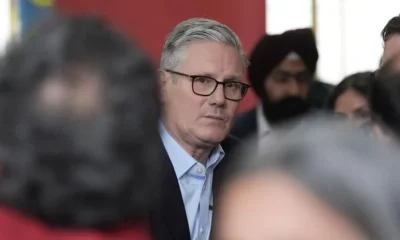
Senate confirms Kevin Warsh to Fed board ahead of expected Chair vote


The Senate confirmed Kevin Warsh to the Federal Reserve Board of Governors on Tuesday, moving President Donald Trump’s pick one step closer to becoming the next chair of the U.S. central bank.
Lawmakers approved Warsh in a 51-45 vote. Sen. John Fetterman (D-Pa.) was the only Democrat to support the nomination.
Warsh still must win a separate Senate vote to become Fed chair, which is expected Wednesday. Governors serve 14-year terms while the chair serves a four-year term.
If confirmed as chair, Warsh, 56, will replace Jerome Powell, whose eight-year term leading the Fed ends Friday. Powell, however, has said he plans to remain on the board until a federal probe into renovations at the Fed’s headquarters concludes.
Warsh enters the role as policymakers face renewed inflation concerns tied to the war in Iran and rising energy prices. Investors are also watching for signs of how the Fed may approach interest rates and financial market regulation under new leadership.
The former Morgan Stanley banker has drawn attention for his ties to the crypto industry. Financial disclosures filed with the Office of Government Ethics showed Warsh held investments in blockchain and digital asset companies tied to decentralized finance, crypto payments and tokenized networks through venture funds and private entities.
The holdings included exposure to firms connected to Bitcoin infrastructure, Layer 1 and Layer 2 blockchain networks and prediction markets. Warsh pledged to divest most of those investments if confirmed.
His prior investments suggest familiarity with crypto markets at a time when the Fed is weighing stablecoin regulation, bank crypto custody rules and research into digital payment systems.
Crypto World
Foundation unveils new ‘Clear Signing’ standard to stop users from approving malicious crypto transactions
The Ethereum Foundation and a group of major crypto wallet developers are rolling out a new security standard designed to stop users from accidentally signing away their funds, a problem that has fueled some of the industry’s biggest hacks and scams.
The initiative, called “Clear Signing,” aims to replace the confusing walls of code users currently see when approving Ethereum transactions with simple, human-readable explanations of what they’re actually agreeing to.
The effort comes after years of phishing attacks and wallet drains that often boil down to the same issue: users unknowingly approving malicious transactions they don’t understand. The Ethereum Foundation pointed to incidents like the Bybit hack as examples of how attackers exploit “blind signing,” where users approve transactions filled with unreadable technical data.
Right now, signing a crypto transaction can feel like clicking “accept” on a terms-of-service page written in another language. Wallets often display long strings of code that only highly technical users can decipher, leaving everyday traders vulnerable to fake apps, malicious links and compromised websites.
The new system would instead let wallets display clearer prompts such as what assets are moving, who is receiving them and what permissions are being granted before users hit approve.
The framework relies on a proposed Ethereum standard called ERC-7730 and a public registry where transaction descriptions can be reviewed and verified by independent security researchers. Wallets can then choose which trusted sources to use when presenting information to users.
The Ethereum Foundation’s Trillion Dollar Security Initiative said it plans to oversee the infrastructure behind the registry while encouraging wallets and developers across the ecosystem to adopt the standard.
The push highlights a growing realization inside crypto that better security may depend less on smarter code and more on making sure users actually understand what they’re signing.
“We welcome the Ethereum Foundation’s Clear Signing standard as a critical security advancement for our entire industry. This addresses a fundamental vulnerability that has plagued cryptocurrency users for years, blind signing. When users can’t understand what they’re signing, security becomes much more difficult. This standard changes that, and every wallet provider should embrace it,” said Tomáš Sušánka, chief technology officer of Trezor, in an email sent to CoinDesk.
Read more: Vitalik Buterin pushes ‘DVT-Lite’ to make Ethereum validator setup easier
Crypto World
Poland debates four crypto bills at once as ban proposal complicates vote


Poland’s Sejm is reviewing four rival crypto bills while the PiS opposition dangles a separate ban proposal, turning MiCA implementation into a high‑stakes regulatory brawl.
Summary
- The Polish Sejm has begun simultaneous review of four competing cryptocurrency regulatory bills, with a second reading vote expected Thursday, after President Karol Nawrocki vetoed related legislation twice.
- The central dispute is over how much power to give financial regulator KNF to freeze accounts and levy fines, with maximum penalties ranging from roughly 20 million zlotys ($5.5 million) in the presidential draft to 25 million zlotys ($6.9 million) in the Ministry of Finance version.
- The opposition Law and Justice party has thrown a wrench into proceedings by submitting a separate bill calling for a complete ban on crypto-related activities in Poland, the only such proposal among major EU member states at a time when MiCA is already in force across the bloc.
Poland’s lower house of parliament, the Sejm, is now reviewing four simultaneous and competing cryptocurrency regulatory bills after Speaker Włodzimierz Czarzasty confirmed the formal review process has begun, according to reporting by The Block. The four proposals come from the government, the presidential office, the Poland 2050 party and the Confederation party, reflecting a fractured political landscape in which no single faction commands enough support to pass a unified crypto framework on its own. A second reading vote is expected as early as Thursday.
Four bills, one parliament, and a ban proposal on the side
The legislative deadlock has roots in executive-legislative conflict. President Karol Nawrocki has already vetoed crypto-related legislation twice, and the current multi-bill review is in part a consequence of those vetoes forcing the Sejm to restart negotiations from scratch. The core technical dispute is narrow but consequential: how much enforcement power the Polish Financial Supervision Authority (KNF) should have over crypto firms, specifically its ability to freeze accounts and impose maximum fines. The presidential draft caps penalties at approximately 20 million zlotys, equivalent to about $5.5 million, while the Ministry of Finance’s version pushes that ceiling to 25 million zlotys, or roughly $6.9 million — a 25% gap that reflects a deeper disagreement about whether Poland’s crypto regulatory posture should prioritize innovation or investor protection.
Into that already complicated debate, the opposition Law and Justice party (PiS) dropped a separate bill on Monday calling for a complete ban on crypto asset-related activities in Poland. PiS had previously withdrawn support for earlier regulatory proposals, and its ban draft will only enter formal review after the four main bills are processed, according to Speaker Czarzasty. The Speaker also used the occasion to raise pointed questions about potential political financing issues in the crypto sector, specifically referencing Polish exchange Zondacrypto and asking whether industry funding had influenced political activities — a line of inquiry that injects a corruption subtext into what had been a relatively technical regulatory debate.
Poland’s crypto bill chaos in a post-MiCA Europe
The Polish parliamentary standoff is unusual within the European Union context. MiCA — the Markets in Crypto-Assets regulation — entered into full force across all 27 EU member states in December 2024, giving exchanges, stablecoin issuers and crypto asset service providers a harmonized licensing framework that national legislatures are supposed to implement rather than override. Poland is therefore not debating whether to regulate crypto under MiCA, which already applies, but rather how aggressively to set national enforcement parameters on top of the EU baseline, a distinction that makes PiS’s outright ban proposal legally problematic as well as politically radical.
For the broader European crypto market, Poland matters more than its size might suggest. The country has one of the largest retail crypto user bases in Central and Eastern Europe, and Zondacrypto — formerly known as BitBay — is one of the continent’s older and better-capitalized domestic exchanges, now operating under a MiCA transitional license. A regulatory outcome that imposes KNF account-freeze powers and $6.9 million penalty ceilings would be broadly workable for established players, while an outright ban, even if constitutionally and EU-law challengeable, would create immediate operational uncertainty. As a crypto.news story on Australia’s capital gains tax overhaul showed, retail-heavy crypto markets are highly sensitive to sudden shifts in the legal and tax treatment of digital assets, and Poland’s Thursday vote — whatever its outcome — will be closely watched by exchanges and compliance teams operating across the EU’s eastern flank.
Crypto World
Leading AI Claude Predicts the Shocking Price of Solana by the End of 2026
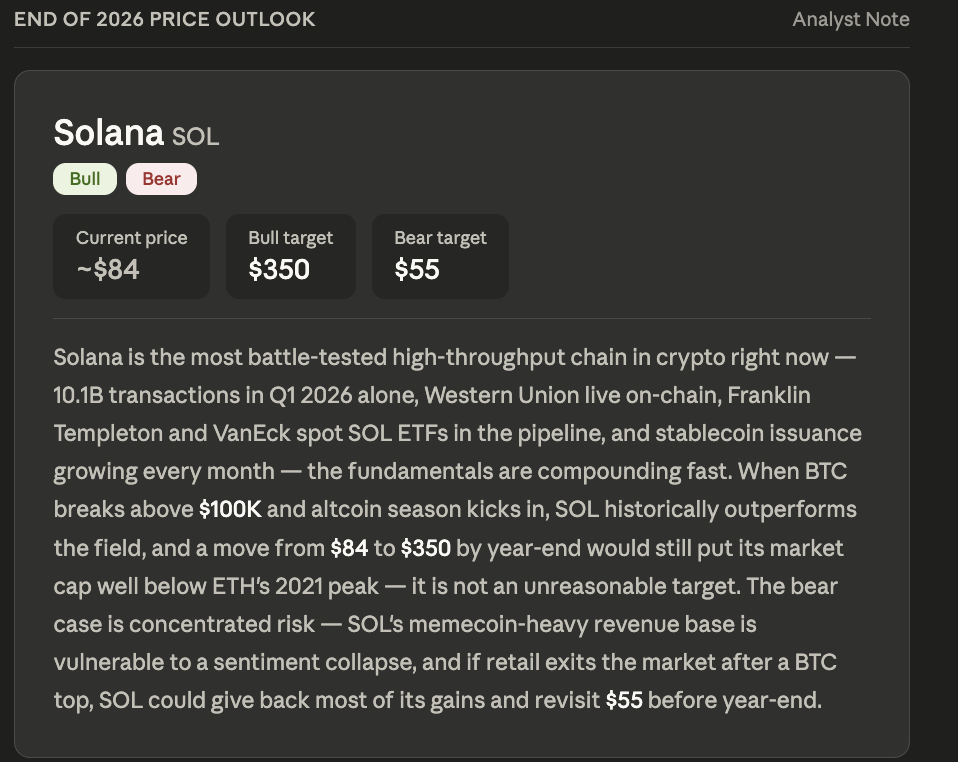
Recently, Solana traded like a chain nobody believes in anymore. Claude AI looked at the fundamentals and disagreed entirely and predicted a higher price.
The target it came back with was $350.
The argument starts with raw throughput data that is hard to argue with. Solana processed 10.1 billion transactions in Q1 2026 alone.
Western Union is live on-chain. Franklin Templeton has a product on the network. Stablecoin issuance is growing every single month.
These are not roadmap promises; they are numbers that are already happening, and Claude AI’s point is that the fundamentals are compounding faster than price is reflecting. The deeper argument is a market structure one: when BTC breaks above $100,000 and altcoin season rotates in, SOL historically outperforms the field by a significant margin.
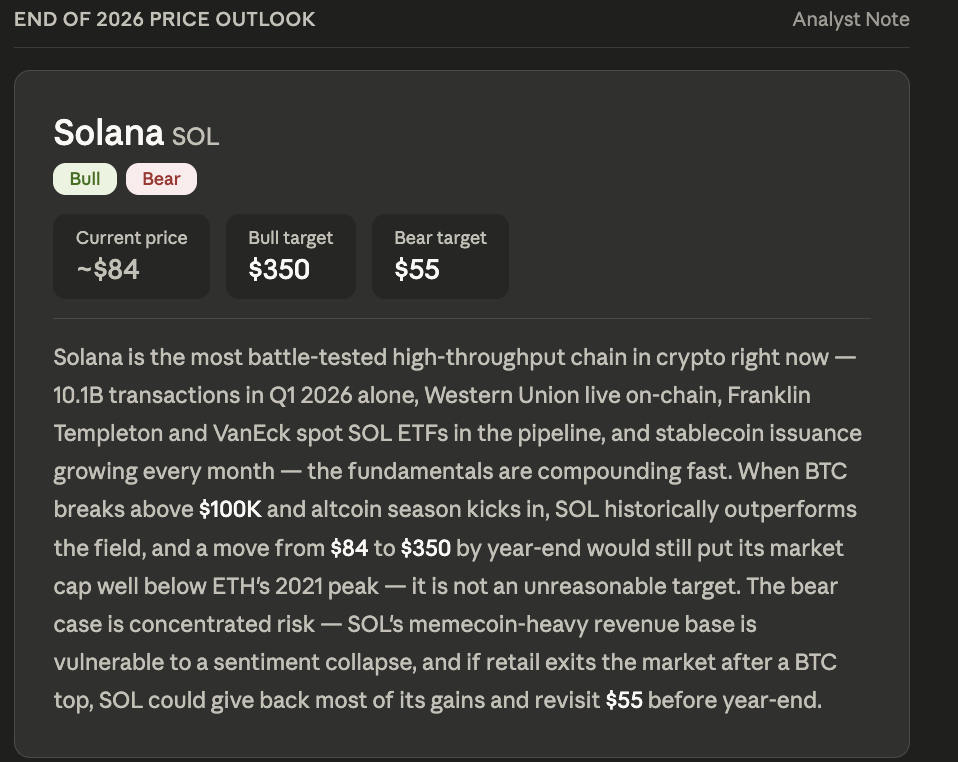
A move from $84 to $350 by year-end would still leave SOL’s market cap well below ETH’s 2021 peak, meaning the target is not asking for price discovery into uncharted territory; it is asking for a catch-up trade with precedent.
The bear case is the sharpest thing in the entire prediction. Claude identifies SOL’s memecoin-heavy revenue base as a concentrated risk that most bulls are not pricing in.
If retail exits the market after a BTC top and the memecoin economy collapses with it, Solana loses a disproportionate share of its fee revenue and narrative appeal. The AI puts the downside at $55 in that scenario, which, from the current price, is a 42% drawdown.
That is the trade: 4x up or nearly half down, depending entirely on whether this cycle’s retail wave arrives or doesn’t.
Solana Price Prediction: Chart Now Says Something Different, Can it Hit $350 as Claude AI Predicts?
Solana price is trading at $95.72 on the daily, and the chart frames the last 7 months as one of the more violent drawdowns in this cycle.
Price peaked around $255 in November 2025, collapsed to $70 by February 2026, and has been slowly rebuilding ever since.
The recovery has been choppy, but the direction has been consistent: higher lows, gradual compression toward the $100 level that now acts as the defining line for everything.
That $100 zone is the resistance that matters. It has been the ceiling since the February crash, and every rally attempt has stalled right at or just below it.
SOL is pressing into it right now at $95.72, which makes the next few daily closes the most important price action on this chart.
A clean break and hold above $100 flips it from resistance to support and opens the path toward $120 and then $150, which is where the next major supply cluster sits from the December consolidation on the way down.
Support below is $80 to $85, the base that has held through every dip since March, and where buyers have been consistent. Lose that, and $70 comes back into play fast, which is exactly the washout Claude flagged in the bear case.
LiquidChain Could Be The Next Big Winner, According to Claude
Large caps are stuck. BTC, ETH, and XRP are all pinned under resistance, waiting on macro conditions and institutional inflows that have not shown up yet. Until they do, upside stays limited, and moves stay slow.
That’s exactly when capital starts hunting for earlier-stage setups. The kind where upside is not already priced in and does not require billions in new inflows to move the needle.
LiquidChain is targeting that gap directly. The project is building a cross-chain execution layer that connects Bitcoin, Ethereum, and Solana into a single environment, removing the fragmentation that forces users and assets to inefficiently navigate between ecosystems. One deployment, three ecosystems, no friction.
The presale is sitting at $0.01454 with just over $700,000 raised. Early discovery phase, not a fully priced asset.
The tradeoff is honest. Execution, post-launch adoption, and liquidity remain unknowns. That is the nature of early-stage infrastructure. The potential is higher, and so is the risk.
The choice is simple. Large caps offer stability with conditional upside that depends on catalysts outside your control. LiquidChain offers earlier positioning with asymmetric potential and all the execution risk that comes with it.
Explore the LiquidChain Presale
The post Leading AI Claude Predicts the Shocking Price of Solana by the End of 2026 appeared first on Cryptonews.
Crypto World
LMAX Group Launches Digital Asset Collateral Solution for Institutions

Global cross-asset marketplace LMAX Group has launched Kiosk, a hosted portal that lets institutional clients deposit digital assets into LMAX Custody and use them as collateral to trade across its FX, metals, derivatives and crypto markets.
The product allows clients to post digital assets as collateral for spot foreign exchange, precious metals, contracts for difference, perpetual futures and digital assets, the company said Tuesday.
Kiosk includes tools for deposits, withdrawals, API credential management, WalletConnect, security controls and treasury management, according to LMAX.
The launch is part of LMAX’s broader push to connect traditional and digital markets by allowing crypto holdings to support trading activity across multiple asset classes.
“Hyper-efficient collateral will be the foundation of modern, converged capital markets,” said David Mercer, CEO at LMAX Group, adding that the new platform offers a compliant way for institutions to “integrate digital assets into their core trading infrastructure.”
The new platform is part of a broader trend to build more onchain collateral assets, following similar initiatives from institutions such as the Depository Trust & Clearing Corporation (DTCC) and Franklin Templeton.

LMAX Digital cryptocurrency platform. Source: Lmaxdigital.com
Institutions are experimenting with onchain collateral
Some of the largest financial institutions are experimenting with tokenized securities and onchain collateral assets.
Earlier in February, investment manager Franklin Templeton announced the launch of an institutional collateral program with crypto exchange Binance, which lets clients use tokenized money market fund (MMF) shares as collateral for trading activity, while the underlying assets remain in regulated custody, Cointelegraph reported.
Franklin Templeton said the model was designed to let institutions earn yield on regulated money market fund holdings while using the same assets to support digital asset trading, without giving up existing custody.
Related: Capital B raises $17.8M to expand its Bitcoin treasury
On May 4, the DTCC announced plans to launch a pilot for trading tokenized securities in July, aiming for the full launch of the service in October, Cointelegraph reported. DTCC said the service will offer tokenized real-world assets with the same investor protections and ownership rights as the assets held in traditional form.
Magazine: Strategy reveals why they would sell BTC, Trump Media posts loss: Hodler’s Digest, May 3 – 9
Crypto World
SparkLend Expands wBTC Limit to 30,000 in DeFi Push

TLDR
- SparkLend increased its wBTC deposit cap from 3,000 to 30,000, effective May 11, 2026.
- The previous 3,000 wBTC limit was reached shortly after the asset was listed on March 31, 2026.
- SparkLend uses an automated system that raises the cap by 500 wBTC every 12 hours.
- The protocol will take about 27 days to scale the limit fully to 30,000 wBTC.
- SparkLend reported total value locked of approximately $3.55 billion in May 2026.
SparkLend has lifted its Wrapped Bitcoin deposit cap from 3,000 to 30,000 wBTC, effective May 11, 2026. The DeFi lending protocol operates within the MakerDAO ecosystem and confirmed the update after reaching the previous ceiling. The change expands borrowing capacity and increases available liquidity for Bitcoin-backed positions on the platform.
SparkLend and wBTC: Deposit Ceiling Expands Tenfold
SparkLend listed wBTC on March 31, 2026, and users filled the 3,000 wBTC cap within weeks. The protocol was then approved for a tenfold increase to meet sustained demand. The new limit sets the maximum deposit level at 30,000 wBTC.
The platform uses a cap automator to adjust limits in scheduled increments. It increases the ceiling by 500 wBTC every 12 hours. At that pace, the system will require about 27 days to reach the full 30,000 wBTC threshold.
SparkLend confirmed the update took effect on May 11, 2026. The protocol stated that the automated process will continue until it reaches the new cap. The system does not raise the full amount at once but follows programmed intervals.
The protocol reported total value locked of about $3.55 billion in May 2026. Reports showed TVL reached $3.6 billion in April 2026. The figures reflect on-chain data tracked across supported assets.
Bitcoin-Linked Assets Shape Platform Growth
SparkLend also supports cbBTC and LBTC as Bitcoin-linked collateral options. These assets allow users to access decentralized borrowing across different networks. The protocol integrates them to expand liquidity sources tied to Bitcoin.
The expansion of the wBTC cap removes previous access limits for new depositors. Before the change, users could not deposit once the 3,000 wBTC ceiling was reached. The revised structure now permits additional participation over time.
wBTC maintains a 1:1 peg with Bitcoin through custodial backing. The asset depends on reserve transparency and operational integrity. Any disruption in that structure can affect protocols that hold wBTC.
Sharp Bitcoin price declines can trigger loan liquidations tied to wBTC collateral. Liquidations can increase selling pressure on underlying assets. This mechanism remains standard across decentralized lending platforms.
SparkLend stated that support for cbBTC and LBTC spreads exposure across Bitcoin-linked instruments. The protocol continues to operate within MakerDAO’s framework. The cap expansion process remains active as of May 2026.
Crypto World
Osero raises $13.5M in round led by Sky Ecosystem


Osero, a stablecoin yield infrastructure project incubated by Stablewatch and Soter Labs, raised $13.5 million in a round led by the Sky Ecosystem and co-led by Plasma.
The round included angel investors representing USDT0, Maple, Accountable, Four Pillars, RedStone, The Rollup and Kairos Research, according to an announcement.
Stablecoins have grown to more than $300 billion, according to DeFiLlama data. Most yield from the assets backing those stablecoins still goes to issuers like Circle and Tether, leaving holders with no direct return and fintech firms with limited ways to offer stablecoin savings products without managing assets themselves.
Osero is launching three products. Osero Earn which lets wallets, neobanks, custodians and exchanges embed the Sky Savings Rate into their own interfaces. Osero App, which gives users direct access to the rate across chains, and Osero Foundry, which gives asset managers and structured product issuers a way to bring yield products onchain.
Osero Earn is meant to be integrated with roughly 10 lines of code, according to the company. The product routes deposits into the Sky Savings Rate while Osero handles the underlying asset-management, routing and risk infrastructure.
Osero Foundry will provide up to $2.5 billion in allocation capacity for anchor funding, swap liquidity and lending liquidity. Each deployment will go through a Basel III-inspired risk review, Osero said.
The $13.5 million raise will fund capital requirements for Osero’s first Foundry allocations. The capital will be used to underwrite the first cohort of deployments under the risk framework used for the Sky Protocol’s assessment process.
Sky, formerly MakerDAO, has been expanding the balance sheet and distribution network around USDS and sUSDS. Sky received a B- rating from S&P last year, in the first credit rating assigned by the agency to a DeFi protocol.
Sky-backed projects have also pushed into yield-bearing real-world asset products. Obex said in March it was spreading $1 billion across credit, energy and AI assets to expand stablecoin yield.
Plasma, which co-led the round, is building a stablecoin-focused blockchain. Its token sale drew $373 million last year in an oversubscribed sale.
Crypto World
Ethereum’s Clear Signing standard tackles blind transactions with ERC-7730


Ethereum’s new ERC‑7730 Clear Signing standard replaces hex gibberish in wallet prompts with human‑readable, auditable transaction summaries to slash phishing and blind signing losses.
Summary
- The Ethereum Foundation’s Clear Signing working group and Ledger co‑designed ERC‑7730, a standard that turns today’s cryptic wallet calldata into plain‑language transaction summaries.
- Clear Signing uses a JSON description format, a public registry tied to contract addresses, and third‑party audits so wallets can show accurate, WYSIWYS intent without changing on‑chain logic.
- The push comes as phishing and approval scams outpace protocol hacks; incidents like the CoW DAO domain hijack and Binance’s 22.9M blocked phishing attempts show why legible prompts are critical.
The Ethereum Foundation’s Clear Signing working group has published a new open standard designed to replace the cryptic, machine-readable hex data that wallets currently display when users are asked to approve a transaction, according to an official Ethereum Foundation blog post. Built on the ERC-7730 specification, Clear Signing standardizes how transaction intent is described, displayed and verified across wallets, aiming to give users a plain-language summary of what will actually happen on-chain before they click approve.
ERC-7730 and the end of unreadable transaction prompts
The problem Clear Signing addresses is one of crypto’s oldest and most exploited UX failures. When a user interacts with a smart contract — whether approving a token spend, listing an NFT, or authorizing a DeFi position — most wallets today display raw calldata or a partial ABI decode that is unreadable to anyone who is not a developer. That gap between what the screen shows and what the transaction actually does is the core mechanic behind a significant portion of phishing attacks, where malicious dApps present a benign-looking interface while the underlying transaction drains a wallet. Ledger, which co-developed ERC-7730 alongside the Ethereum Foundation working group, has described the standard as a direct response to that attack surface, noting that “blind signing” has been one of the top two causes of significant user losses in hardware wallet incidents.
Clear Signing’s architecture has three components. First, a unified JSON-based description format tied to ERC-7730 that dApp developers use to annotate their contracts with human-readable explanations of each function call and parameter. Second, a public registry where those descriptions are stored, versioned and linked to deployed contract addresses so wallets can pull the relevant metadata at signing time. Third, an independent verification and auditing layer where third parties can review and attest to the accuracy of a contract’s descriptions, creating a trust chain between the dApp developer’s intent and what the wallet ultimately displays.
WYSIWYS: what changes for users and what stays the same
The standard is explicitly designed to be non-breaking. Clear Signing does not alter how transactions are structured, broadcast or settled on-chain, meaning existing smart contracts, Layer 2 networks and DeFi protocols require no changes to benefit from it. The improvement is entirely in the wallet presentation layer: instead of showing a raw hex string or a partial parameter dump, a Clear Signing-compatible wallet will display something like “Approve Uniswap to spend up to 500 USDC from your wallet” or “List CryptoPunk #4156 for sale at 40 ETH on OpenSea” — a precise, audited, human-readable description derived from the ERC-7730 registry entry for that contract.
For the broader Ethereum security ecosystem, Clear Signing arrives at a moment when wallet-level phishing and approval scams remain the dominant attack vector for retail users even as protocol-level exploits become harder to execute on mature, audited contracts. A recent crypto.news story on the CoW DAO domain hijacking incident — where attackers redirected users to a phishing site for 4.5 hours and induced them to sign malicious transactions — illustrated precisely the failure mode Clear Signing is designed to mitigate: users who could read what they were signing would have had a much better chance of catching the anomaly before approving the drain. In parallel, a crypto.news story on Ethereum’s Glamsterdam devnet progress detailed how the Foundation is simultaneously advancing execution-layer upgrades and leadership restructuring, with Clear Signing fitting into a broader push to make Ethereum safer and more accessible at every layer of the stack without waiting for protocol-level changes to propagate. As a crypto.news story on AI-enabled crypto fraud noted, Binance’s own security data shows 22.9 million phishing attempts intercepted in Q1 2026 alone — a volume that underscores why making transaction approval legible to ordinary users is no longer a UX nicety but a security imperative.
Crypto World
Ambiq Micro (AMBQ) Stock Soars 30% on Strong Q1 Earnings Driven by Edge AI Growth
TLDR
- Ambiq Micro shares soared 30% to reach $59.51 following first-quarter revenue of $25.1 million, representing a 59% year-over-year increase and surpassing the $21.5 million analyst forecast.
- The company’s adjusted loss per share of 25 cents outperformed Wall Street’s consensus projection of a 36-cent loss.
- Edge AI demand fueled growth, with over 80% of shipped units in the quarter executing AI algorithms.
- Second-quarter revenue guidance of $31–$32 million significantly exceeded the $25.7 million analyst consensus.
- AMBQ’s performance contrasted sharply with the broader semiconductor sector, as the iShares Semiconductor ETF dropped 5.8%.
Shares of Ambiq Micro (AMBQ) rocketed 30% higher to $59.51 during Tuesday’s trading session after the Texas-headquartered semiconductor company reported first-quarter financial results that substantially exceeded Wall Street projections across key metrics.
The company recorded first-quarter revenue of $25.1 million, marking a 59% increase compared to the prior-year period. This figure significantly outpaced the $21.5 million analyst consensus. On a per-share basis, the adjusted loss narrowed to 25 cents, representing an improvement from the 38-cent loss posted in the year-ago quarter and beating the Street’s expectation of a 36-cent deficit.
Since making its public debut last July at an initial offering price of $24 per share, AMBQ stock has more than doubled in value.
Chief Executive Officer Fumihide Esaka highlighted the company’s “exceptional momentum” during the first quarter, attributing the performance to “accelerating demand for edge AI capabilities.” The company specializes in chips engineered to execute AI processes locally on devices rather than depending on cloud-based infrastructure.
Ambiq’s semiconductor solutions are deployed across various applications including smart watches, industrial sensors, portable gaming devices, and connected home products. More than 80% of the units the company shipped during the first quarter were equipped to run AI algorithms.
Second-Quarter Outlook Exceeds Projections
Looking ahead to the current quarter, Ambiq projected net sales ranging from $31 million to $32 million. This forecast substantially surpassed Wall Street’s consensus estimate of $25.7 million.
The chipmaker remains unprofitable at current revenue levels. During the earnings conference call, Chief Financial Officer Jeff Winzeler indicated that quarterly revenue would need to reach approximately $47 million for the company to achieve breakeven status.
Winzeler expressed optimism that the company could attain this milestone by mid-2028, with a possibility of reaching it as soon as late 2027.
The company’s SPOT platform — featuring ultra-low-power chip architecture — serves as the foundation for its edge AI push. Management emphasized plans to broaden the technology’s application across additional form factors, customer segments, and market verticals.
Esaka cited “established technology leadership, positive demand trends, and a robust product roadmap” as key factors supporting his confidence in sustained growth momentum.
Outperformance Amid Semiconductor Sector Weakness
Ambiq’s impressive quarterly results provided a stark contrast to the broader semiconductor industry’s performance on Tuesday.
The iShares Semiconductor ETF (SOXX) tumbled 5.8% during the session, marking its steepest single-day decline since October, based on Dow Jones Market Data.
While the majority of chip stocks traded lower, AMBQ defied the sector-wide weakness by a substantial margin.
The company’s first-quarter non-GAAP loss per share of 25 cents compared favorably to the consensus projection of a 36-cent loss. Top-line revenue of $25.1 million exceeded analyst expectations of $21.49 million.
Ambiq’s second-quarter revenue outlook of $31–$32 million signals ongoing sequential expansion as the company progresses toward its profitability objective.
-

 Crypto World4 days ago
Crypto World4 days agoHarrisX Poll Found 52% of Registered Voters Support the CLARITY Act
-

 Fashion4 days ago
Fashion4 days agoWeekend Open Thread: Marianne Dress
-

 Crypto World5 days ago
Crypto World5 days agoUpbit adds B3 Korean won pair as Base token gains Korea access
-

 NewsBeat5 days ago
NewsBeat5 days agoNCP car park operator enters administration putting 340 UK sites at risk of closure
-

 Fashion1 day ago
Fashion1 day agoCoffee Break: Travel Steam Iron
-

 Fashion2 days ago
Fashion2 days agoWhat to Know Before Buying a Curling Wand or Curling Iron
-

 Tech3 days ago
Tech3 days agoAuto Enthusiast Carves Functional Two-Stroke Engine from Solid Metal
-

 Politics19 hours ago
Politics19 hours agoWhat to expect when you’re expecting a budget
-
 Politics3 days ago
Politics3 days agoPolitics Home Article | Starmer Enters The Danger Zone
-

 Business3 days ago
Business3 days agoIgnore market noise, India’s long-term story intact, say D-Street bulls Ramesh Damani and Sunil Singhania
-

 Tech1 day ago
Tech1 day agoGM Agrees To Pay $12.75 Million To Settle California Lawsuit Over Misuse Of Customers’ Driving Data
-
 Crypto World6 days ago
Crypto World6 days agoBlackRock CEO Larry Fink Discusses a New Asset Class
-

 Entertainment6 days ago
Entertainment6 days agoSarah Paulson Called Out For Met Gala ‘Hypocrisy’
-

 Entertainment5 days ago
Entertainment5 days agoGeneral Hospital: Ric & Ava Bombshell – Ric’s Massive Secret Exposed!
-
Sports6 days ago
NBA playoff winners and losers: Austin Reaves is not loving Lakers vs. Thunder matchup, but Chet Holmgren is
-
 Entertainment6 days ago
Entertainment6 days agoBold and Beautiful Early Spoilers May 11-15: Steffy Revolted & Liam Overjoyed!
-
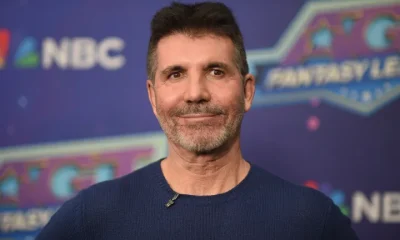
 Politics5 days ago
Politics5 days agoSimon Cowell Says He Was ‘Horrible’ To Susan Boyle During BGT Audition
-

 Crypto World6 days ago
Crypto World6 days agoRobinhood says Wall Street is building onchain
-
 Sports5 days ago
Sports5 days agoUEFA Champions League final schedule, teams, venue, live time and streaming | Football News
-

 Tech7 days ago
Tech7 days agoApple and Samsung are dominating smartphone sales so thoroughly that only one other company makes the top 10










You must be logged in to post a comment Login