Crypto World
Lazarus Group Uses Fake Meeting Hack


North Korea’s Lazarus Group has launched a new macOS malware campaign called Mach-O Man that uses fake online meeting invitations to trick crypto and fintech executives into executing malicious commands on their own devices, according to blockchain security firm CertiK.
Summary
- Lazarus Group’s new Mach-O Man campaign uses fake meeting invites to lure executives into pasting malicious terminal commands on their Macs.
- The malware auto-deletes after execution, making the breach nearly impossible to detect through standard forensic methods.
- CertiK links the same Lazarus push to over $500 million stolen from DeFi platforms Drift and KelpDAO in the past two weeks.
North Korea’s Lazarus Group is running a new campaign dubbed Mach-O Man that targets executives at crypto, fintech, and other high-value firms by disguising malware delivery as a routine technical fix during a fake business meeting, according to CertiK senior blockchain security researcher Natalie Newson. The campaign was disclosed on April 22 and represents one of the group’s most operationally sophisticated social engineering methods to date.
Lazarus Group Crypto Hack Hides Behind Routine Business Communications
The attack chain begins with an urgent-looking meeting invitation sent over Telegram, impersonating a Zoom, Microsoft Teams, or Google Meet call. The link leads to a convincing but fake website that tells the victim to paste a single command into their Mac terminal to resolve an apparent connection issue, a technique CertiK identifies as ClickFix. Once executed, the command installs a modular malware kit built from native Mach-O binaries tailored for Apple environments, which profiles the host, establishes persistence, and exfiltrates credentials and browser data through a Telegram-based command-and-control channel. Critically, the toolkit auto-deletes after completing its task, making detection and forensic analysis extremely difficult. “These fake verification steps guide victims through keyboard shortcuts that run a harmful command,” CertiK’s Newson told CoinDesk. “The page looks real, the instructions seem normal, and the victim initiates the action themselves, which is why traditional security controls often miss it.”
Why This Attack Is Harder to Catch Than Standard Phishing
Unlike traditional phishing attacks that rely on urgency cues or suspicious sender addresses, the Mach-O Man campaign is designed to look entirely routine at the moment of delivery. Executives in crypto and fintech routinely receive cold outreach from investors, researchers, and business partners, making the fake meeting invitation format a credible lure in a way that generalized phishing often is not. CertiK’s analysis notes that the Mach-O Man framework is tied to Lazarus’ Famous Chollima unit and distributed through compromised Telegram accounts specifically targeting high-value organizations in the digital asset space. Most victims will not realize they have been compromised until well after the malware has erased itself. “They likely don’t know it yet,” Newson said. “If they do, they probably can’t identify which variant affected them.”
The Scale of the Lazarus Threat to Crypto in 2026
CertiK has linked the Mach-O Man campaign to a broader Lazarus offensive that has siphoned more than $500 million from DeFi platforms Drift and KelpDAO in under two weeks, adding to a cumulative theft total estimated at $6.7 billion since 2017. The United Nations has previously estimated that North Korean hackers have stolen several billion dollars in digital assets to fund the country’s weapons programs. “What makes Lazarus especially dangerous right now is their activity level,” Newson said. “This isn’t random hacking. It’s a state-directed financial operation running at a scale and speed typical of institutions.” CertiK is advising crypto professionals to independently verify all meeting requests through a separate channel before clicking any link or downloading any attachment from an unsolicited invitation.
CertiK has shared indicators of compromise tied to the Mach-O Man campaign with the broader security community to support detection and defense efforts across the industry.
Crypto World
UK FCA Targets Illegal Crypto P2P Trading in Nationwide Raids

The United Kingdom’s Financial Conduct Authority (FCA) has raided multiple sites suspected of running illegal peer-to-peer (P2P) crypto trading operations.
The financial services and markets watchdog said Wednesday that it worked alongside HM Revenue & Customs and the South West Regional Organised Crime Unit to inspect eight locations linked to illegal crypto trading. Officials issued cease-and-desist notices on site, ordering operators to halt activity immediately, while gathering evidence tied to ongoing criminal investigations.
“Unregistered peer-to-peer crypto traders operating in the UK are doing so illegally and pose a financial crime risk,” Steve Smart, the FCA’s executive director of enforcement and market oversight, said.
P2P crypto trading allows individuals to buy and sell digital assets directly, bypassing centralized exchanges. In the UK, such activity requires registration under anti-money laundering rules. The FCA said no peer-to-peer crypto traders or platforms are currently registered with the regulator.
Related: Stratiphy reopens tax-free route to crypto ETNs for UK investors
FCA expands crypto crackdown
The raids mark the FCA’s first operation of this kind focused on P2P crypto trading, but follow a series of enforcement steps against the sector. Previous actions include prosecutions tied to illegal crypto ATM networks and arrests linked to unlicensed exchanges.
Earlier this month, authorities in the UK and other countries, including the US and Canada, froze millions of dollars linked to crypto scams as part of a coordinated enforcement effort called Operation Atlantic. The operation, carried out in March, was led by agencies including the UK’s National Crime Agency, the US Secret Service and Canadian law enforcement and securities regulators.

Officials said the operation identified more than 20,000 victims across the three countries and secured over $12 million in suspected criminal proceeds. Investigators also traced more than $45 million in additional stolen crypto linked to fraud networks.
“These raids mark a shift under the incoming FSMA crypto regime, unregistered OTC desks are no longer an AML-registration gap, they’re an unauthorised regulated activity, and enforcement will look more like traditional finance,” Slav Demchuk, CEO at AMLBot.com, told Cointelegraph.
He added that unregulated OTC brokers are one of the most consistent chokepoints in illicit flows, including “Iran-linked evasion corridors where actors cut off from regulated exchanges use informal desks to move USDT and BTC in and out of fiat.”
Related: UK plans payments rule changes for stablecoins, tokenized deposits
UK FCA pushes ahead with crypto rulebook
Earlier this month, the FCA opened a consultation on guidance for its upcoming crypto regulatory regime, which is expected to take effect in 2027. The guidance will cover key areas including stablecoins, trading platforms, custody and staking.
Companies are expected to be able to apply for authorization from September 2026, with full compliance required once the framework is implemented.
Magazine: Singapore isn’t a ‘crypto hub’ — it’s something better: StraitsX CEO
Crypto World
Aave Deposits Drop by $15B Following Kelp DAO Exploit
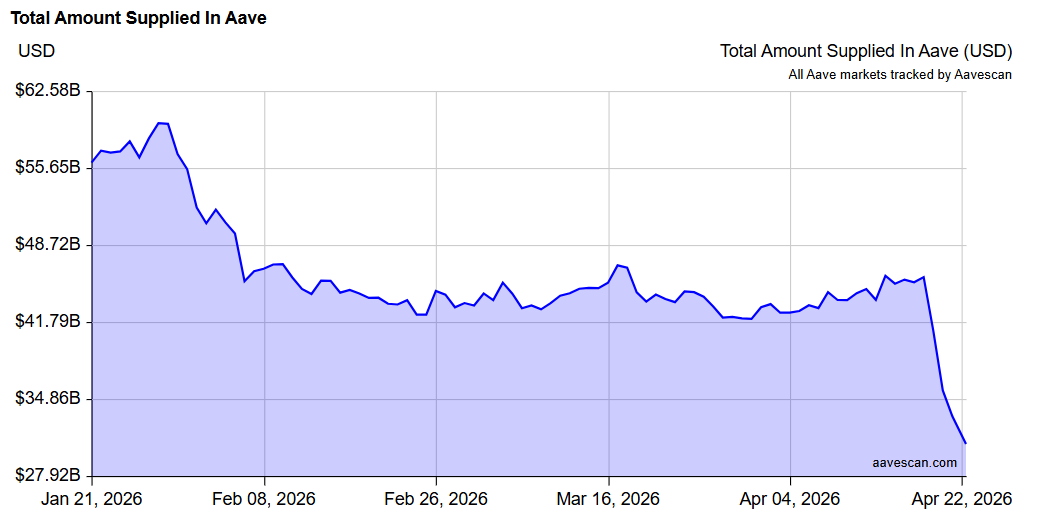
Aave, the largest decentralized lending protocol, has seen around $15 billion in deposits withdrawn since the Kelp Dao exploit on Saturday.
Total value supplied to Aave fell from $45.8 billion on Saturday to $30.8 billion on Wednesday, according to Aavescan data.
The decline followed an attack that drained about 116,500 restaked Ether (rsETH), worth roughly $293 million, from Kelp DAO’s LayerZero-powered rsETH bridge. The exploiter then used part of the stolen funds to borrow on Aave.
Aave’s incident report said 89,567 rsETH were deposited on the protocol and that the resulting shortfall could range from about $123 million to $230 million, depending on how losses are ultimately allocated.
The outflows reflect fears of contagion from Aave’s bad debt and broader capital flight from decentralized finance (DeFi), according to institutional digital asset trading platform Talos.
The bad debt created by the Kelp exploiter resulted in Aave’s v3 Wrapped Ether (WETH) market temporarily reaching 100% utilization and leaving no liquidity available for immediate withdrawals, Talos said in a Tuesday report.

SparkLend’s total value locked (TVL) has risen by $1.3 billion since the Kelp DAO exploit, signaling that the fourth-largest lending protocol was absorbing some of the funds withdrawn from Aave, blockchain analyst EmberCN said in a Wednesday post on X.
Related: Crypto hackers stole $17B over past 10 years: DefiLlama
Kelp exploit spreads through DeFi lending
The episode highlights how DeFi’s interconnectedness is a double-edged sword, as the Kelp DAO exploit spread across lending markets and escalated into a “broader liquidity crunch,” Tanay Ved, senior research associate at Talos, told Cointelegraph.
She said the asset bundled risks across restaking, bridging and lending layers, allowing the impact to spread far beyond the initial exploit, adding that the incident reinforces the need for a more robust collateral framework and a more holistic security approach to address the systemic vulnerabilities of yield-bearing assets.

Aave said it had unfrozen WETH reserves on the Ethereum Core V3 market on Tuesday, enabling users to supply WETH to the V3 lending protocol, but that WETH reserves across Ethereum Prime, Arbitrum, Base, Mantle and Linea remain frozen.
Related: Kelp DAO attacker moves $175M in Ether after exploit: Arkham
Traders bet Kelp DAO won’t socialize losses
On Monday, Aave’s risk manager outlined two potential scenarios for addressing the bad debt. The first scenario involves spreading the losses across all rsETH token holders on Ethereum mainnet and layer 2s, leaving about $123 million in bad debt on Aave.
The alternative would shift the shortfall entirely to layer-2 networks, resulting in about $230 million in bad debt on Aave.
Traders took to prediction markets to bet on the outcome, with only 20% of traders wagering on Kelp DAO socializing the losses across rsETH holders on mainnet, rather than L2 holders bearing the shortfall, Polymarket data shows.
Magazine: 53 DeFi projects infiltrated, 50M NEO tokens could be ‘given back’: Asia Express
Crypto World
Binance.US Cuts Spot Trading Fees to Near Zero


Update (April 22 7:49 PM UTC): This article has been updated to reflect the relationship between Binance.US and Binance in the eighth paragraph.
Binance.US has reduced spot trading fees to 0% for makers and 0.02% for takers across all trading pairs, extending near-zero pricing to all users without volume thresholds or subscription requirements.
The new pricing replaces the platform’s tiered fee structure and applies to all accounts, with the company saying the move could reduce trading costs by as much as 98% compared with competitors such as Coinbase.
Coinbase’s fees start at about 0.40% to 0.60% for lower-volume traders while Kraken’s fees start around 0.25% to 0.40% and decline with volume, according to information on those exchanges’ websites.
Last week, Charles Schwab, one of the largest US brokerage firms, said it will roll out spot cryptocurrency trading for retail clients in the coming weeks, starting with Bitcoin (BTC) and Ether (ETH) at a fee of 75 basis points per transaction.
According to an announcement shared with Cointelegraph, the updated Binance.US fee structure applies to every user with no portfolio minimums, volume tiers or subscription fees and takes effect immediately.
The change follows the appointment of Stephen Gregory as chief executive and expands the platform’s earlier zero-fee offering on select Bitcoin pairs to all spot markets.
The platform said the new fees are supported by its trading infrastructure and follow the completion of a SOC 2 Type II audit covering its systems and controls.
Binance.us is a separate legal entity and operates independently from Binance, according to a company spokesperson.
Related: Bitcoin inflows to Binance fall to 2023 low as BTC bulls set target on $80K
Binance under renewed US scrutiny over Iran-linked transactions
Binance’s operations in the United States have remained under close regulatory and political scrutiny since its 2023 settlement with authorities.
In 2023, the exchange reached a $4.3 billion settlement with US authorities over anti-money laundering and sanctions violations, with former CEO Changpeng “CZ” Zhao pleading guilty to a felony charge. The agreement also placed the company under a court-imposed monitoring program requiring ongoing oversight and reporting to US regulators.
In March 2025, scrutiny intensified after a UAE-based entity invested $2 billion in Binance using a stablecoin issued by a company linked to US President Donald Trump and his family, raising conflict-of-interest concerns among lawmakers. Later that year, Trump issued a pardon to Zhao following his four-month prison sentence.
Regulatory pressure has continued into 2026. In February, a group of US senators urged Treasury and Justice Department officials to conduct a comprehensive review of Binance’s compliance controls following reports that more than $1.7 billion in transactions linked to Iranian entities may have flowed through the platform.
Binance denied the allegations in a letter to Senators Richard Blumenthal and Ron Johnson, calling the reports “false” and unsupported by evidence. The company also said it had filed a defamation lawsuit against The Wall Street Journal.
Most recently, Blumenthal sent letters to the Justice Department and the Financial Crimes Enforcement Network to determine whether Binance is meeting its obligations under the 2023 court-imposed monitoring program.
Magazine: Adam Back says current demand is ‘almost’ enough to send Bitcoin to $1M
Crypto World
Bitcoin DeFi pitched in $46 million proposal ask by Cardano team

Input Output, the private engineering company that built and continues to develop the Cardano blockchain, is seeking about half the funding it requested last year from the project’s community treasury.
The company submitted nine proposals totaling $46.8 million for 2026 on Tuesday, down from $97.5 million in 2025. Several of the proposals focus on scaling Cardano to increase its transaction processing capacity and expanding into Bitcoin DeFi.
Cardano, like most major blockchains, maintains a shared pool of money funded by network fees, which community representatives vote to allocate toward development work. Input Output historically has been the largest recipient because it employs most of the engineers building the underlying software.
The reduced ask is the first concrete step in a plan to phase out that dependency. Input Output said it now aims to shrink its annual request each year until the company can sustain itself on its own revenue, with community funds going instead to a broader set of smaller engineering groups.
By the end of 2026, Input Output expects smaller, more specialized teams to take on most of the work it currently does in-house, including firms such as VacuumLabs and Midgard Labs that focus on specific layers of the Cardano software.
Scaling and bitcoin DeFi
The nine proposals group into two themes. The larger funds a consensus upgrade called Leios, which Input Output claims will increase Cardano’s transaction processing capacity by 10 to 65 times, targeting more than 1,000 transactions per second.
For context, that would move Cardano from a relatively slower chain to one competitive with Solana and the fastest Ethereum layer-2 networks on throughput alone. Leios is scheduled for a test release in June and full deployment by year-end.
The second flagship proposal funds a system called Pogun, which aims to bring Bitcoin-based decentralized finance to Cardano. In practice, it would let bitcoin holders borrow and earn yield on their holdings through Cardano without giving custody to a centralized intermediary. Pogun’s lending component is targeted for public release in the second quarter.
Smaller proposals cover performance improvements to Cardano’s smart contract engine, security testing infrastructure, developer tools, and expanded API services.
Each proposal names specific delivery leads and ties funding to delivery milestones rather than releasing money upfront. Imagine paying a contractor in stages as different parts of a house are completed, instead of handing over the full budget at the start of construction.
Voting opens Tuesday and runs through May 24. The decisions are made by roughly 1,000 elected delegates known as DReps, who represent ADA holders much as proxy representatives do in a publicly traded company. Charles Hoskinson, the founder of Input Output, is scheduled to release a video this week making the case directly to those delegates.
The vote will test whether Cardano’s governance, which has expanded significantly over the past two years, treats Input Output like any other grant applicant or continues to approve its requests largely on a basis of deference.
Last year’s $97.5 million proposal passed, but in the interim the Cardano Foundation has taken over the project’s grant-funding arm, and Intersect, the governance organization running this vote, has assumed stewardship of core Cardano software. Both shifts mean alternatives to Input Output now exist in a way they did not when previous votes went through.
Meanwhile, Input Output also cited progress in the ecosystem in its release. A new Cardano stablecoin, USDCx, reached 14.6 million tokens in circulation within weeks of its launch. Total assets deposited on Cardano, a common measure of a network’s usage, rose from $137.5 million to $142.7 million over the same period.
Whether the full slate passes, gets partially funded, or is reshaped entirely by DReps will signal how much the Cardano community’s thinking has shifted now that the tools to fund development without Input Output exist.
Crypto World
Phishing, Deepfakes To Fuel 2026’s Biggest Crypto Hacks
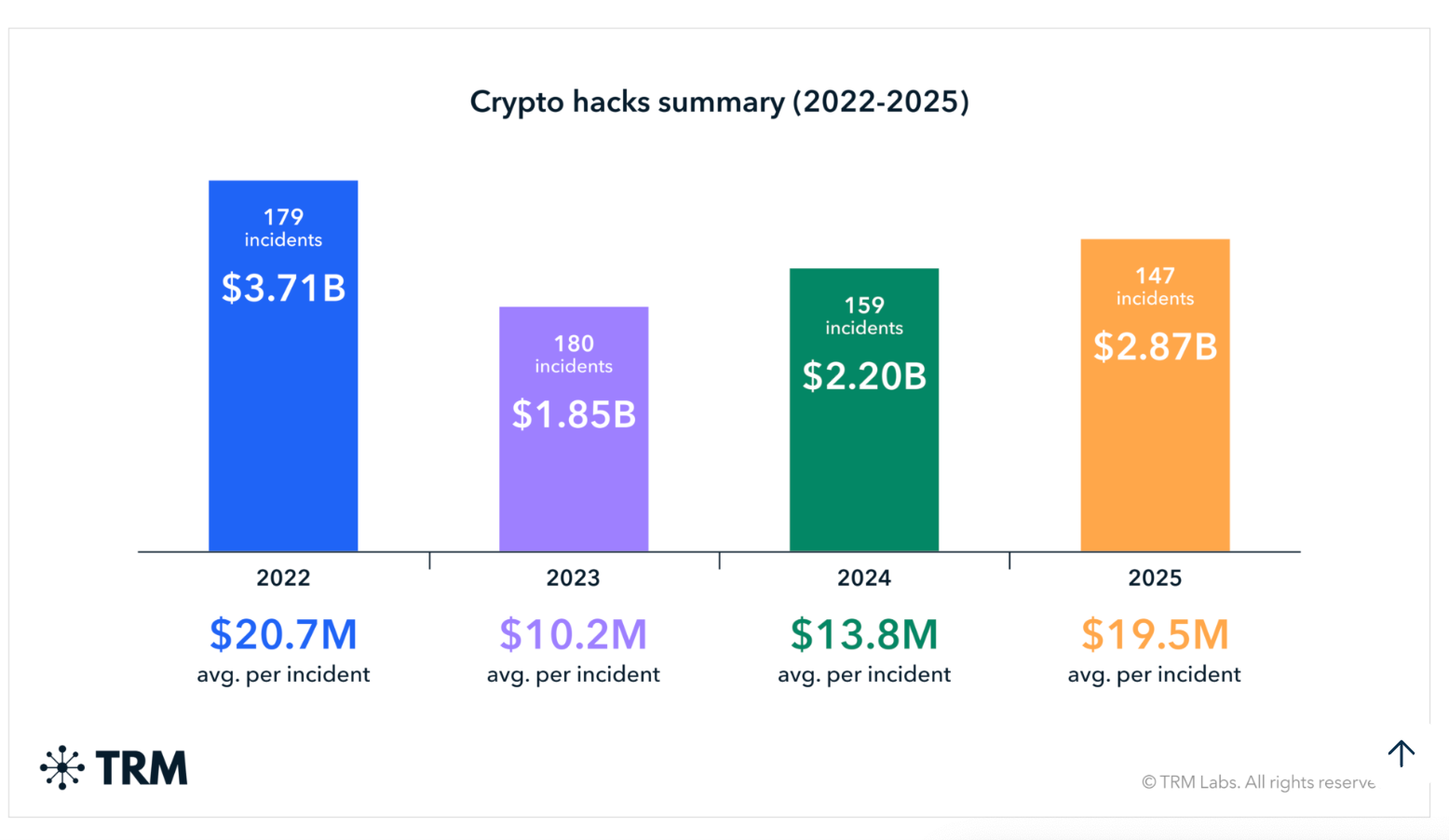
Real-time deepfakes, phishing attacks, supply chain compromises and cross-chain vulnerabilities will likely be the root of some of the biggest hacks in 2026, according to CertiK senior blockchain investigator Natalie Newson.
The industry has already lost over $600 million to hacks in 2026, due largely to two North Korea-linked crypto thefts in April, including the $293 million Kelp DAO exploit on Saturday involving a single point-of-trust failure in cross-chain messaging protocol LayerZero’s infrastructure, and the $280 million exploit of the Drift Protocol.
Another DPRK-linked attack involved the use of AI for social engineering. Crypto wallet Zerion revealed on April 15 that North Korean-affiliated hackers used AI in a long-term social engineering attack to steal about $100,000 from the company’s hot wallets.
Newson warned that, in “some aspects,” the acceleration of AI will only worsen crypto attacks.

“The best way for investors to protect themselves is to be aware of the current threats they may face… For instance, to protect yourself against phishing, always verify the authenticity of URLs and smart contracts,” Newson said.
Newson said that as exploits become more sophisticated, retail investors should explore storage options outside of crypto exchanges.
“Using cold wallets can help keep assets that you don’t use regularly safe and allows you to sign transactions without ever exposing your private keys,” she said.
AI could be used to defend against attacks
“There are now more convincing deepfakes, autonomous attack agents, and ‘agentic AI’ that can autonomously scan smart contracts for bugs, draft exploit code and execute attacks at machine speed,” she said.
On April 6, Cointelegraph reported that a threat actor known as “Jinkusu” was allegedly selling cybercrime tools designed to bypass Know Your Customer (KYC) checks at banks and crypto platforms, using deepfakes and voice manipulation.
“At the same time, AI can also be one of the biggest defenses,” said Newson.
Cointelegraph recently reported that an increase in AI use has led to a flood of bug bounty submissions, both valid and invalid. Anthropic’s AI model Claude Mythos, claimed to have the ability to find vulnerabilities in major operating systems, has been deployed defensively with a release to a limited set of tech firms.
Regulators are escalating in response
CertiK shared with Cointelegraph in December 2025 that crypto hackers stole $3.3 billion in 2025.
The company said supply-chain breaches emerged as the most damaging threat, accounting for $1.45 billion in losses across just two incidents, including the $1.4 billion Bybit hack in February 2025.
Related: Telegram CEO Durov warns EU age-verification app could enable wider tracking
“The Bybit exploit signals that well-capitalized, well-coordinated threat actors are becoming more active across the ecosystem,” the report said, predicting a rise in the “sophistication” of supply chain attacks as attackers target more infrastructure providers.
Regulators are responding. On April 9, the US Department of the Treasury’s Office of Cybersecurity and Critical Infrastructure Protection (OCCIP) announced on Thursday that it is expanding its cybersecurity threat identification program to include digital asset companies.
Magazine: Adam Back says current demand is ‘almost’ enough to send Bitcoin to $1M
Crypto World
Crypto Market Maker GSR Launches Multi-Asset Crypto ETF

Institutional crypto trading platform GSR launched its first crypto exchange-traded fund on Wednesday, recording nearly $5 million in trading volume on its first trading day.
The GSR Crypto Core3 ETF (BESO) tracks the spot price of Bitcoin (BTC), Ether (ETH) and Solana (SOL) and offers staking rewards, GSR said in a statement on Wednesday.
In a separate post on X, GSR said it will be adopting a “dynamic allocation strategy” to optimize returns for the fund, which carries a 1% management fee.

BESO saw 185,574 shares traded worth about $4.8 million on its opening day, Nasdaq data shows. The fund closed at $26.04 but rose to $33 in after-hours trading.
GSR’s market entry coincides with a wave of Wall Street firms that have recently launched or signaled their intention to launch a crypto ETF.
Among them is investment bank Morgan Stanley, which launched a spot Bitcoin ETF on April 8 that has already attracted $163.8 million in net inflows.
On April 14, Goldman Sachs filed for a Bitcoin Premium Income ETF, enabling investors to earn passive income while still benefiting from potential price appreciation in Bitcoin.
GSR was founded by former Goldman Sachs traders Cristian Gil and Richard Rosenblum in 2013, making it one of the most established crypto market-making platforms in the industry.
Related: Charles Schwab to roll out spot Bitcoin, Ether trading for retail clients
GSR CEO Xin Song said the company expanded into the crypto ETF market to make its services available to a broader range of investors, adding:
“Our ETF strategy reflects our deep understanding of how this asset class is evolving.”
Bitcoin takes back seat in GSR fund model portfolio
GSR said allocations between Bitcoin, Ether and Solana for BESO will be rebalanced weekly based on “research-driven signals designed to pursue additional returns.“
GSR published a model portfolio analysis on Wednesday showing an optimized allocation between the cryptocurrencies, with Ether and Solana dominating at 51.4% and 41.67% respectively, while Bitcoin holds a smaller position at 6.93%.
Magazine: Adam Back says current demand is ‘almost’ enough to send Bitcoin to $1M
Crypto World
Binance.US drops spot trading fees in challenge to rivals


Binance.US has reduced its spot trading fees to 0% for makers and 0.02% for takers across all trading pairs.
Summary
- Binance.US now charges 0% maker fees and 0.02% taker fees across all spot trading pairs.
- The exchange removed volume tiers and subscription rules, making near-zero spot fees available to every user.
- The move increases pressure on Coinbase, Kraken, and Schwab as crypto trading competition grows faster.
The exchange said the new pricing applies to every user and does not depend on trading volume, account size, or subscription plans.
The move replaces the platform’s earlier tiered structure and expands zero-fee access beyond a limited number of Bitcoin pairs. Binance.US said the change takes effect immediately and is designed to lower costs for retail traders using the platform.
New pricing targets pressure from rivals
The updated fee model puts Binance.US below many major rivals in the US market. The company said the new structure could cut trading costs by as much as 98% compared with some competing platforms, where lower-volume users often face higher charges.
Coinbase’s public pricing shows spot fees for lower-volume traders can range from about 0.40% to 0.60%. Kraken also uses a volume-based model, with entry-level fees starting near 0.25% for makers and 0.40% for takers.
Charles Schwab also said last week that it plans to launch spot crypto trading for retail clients, starting with Bitcoin and Ether at a fee of 75 basis points per transaction.
Moreover, Binance.US said the reduced fees are backed by its trading infrastructure and recent internal controls work. The company stated that it completed a SOC 2 Type II audit covering its systems and controls before rolling out the new pricing model.
The change also follows the appointment of Stephen Gregory as chief executive. Binance.US said the broader fee cut builds on its earlier strategy of offering zero-fee trading on selected pairs, but now extends that approach to all spot markets on the platform.
Exchange remains under US scrutiny
The fee cut comes as Binance-related operations continue to face political and regulatory attention in the United States. Binance reached a $4.3 billion settlement with US authorities in 2023 over anti-money laundering and sanctions violations. Former chief executive Changpeng “CZ” Zhao also pleaded guilty to a felony charge as part of that case.
Binance.US has said it operates as a separate legal entity from Binance. A company spokesperson said Binance.US “operates independently from Binance.” Even so, pressure on the broader Binance brand has continued.
In 2026, lawmakers asked federal agencies to review whether Binance is meeting its obligations under a court-ordered monitoring program. Binance denied claims tied to Iran-linked transactions and called the reports “false” and unsupported by evidence.
Fee cut comes as US crypto market gets more competitive
The new pricing shows Binance.US is trying to compete more directly for spot market share at a time when more firms are entering or expanding in the US crypto sector. Lower fees may help the platform appeal to cost-conscious users who trade often and want simpler pricing.
At the same time, the exchange is making that move while the wider Binance group remains under close watch in Washington. That leaves Binance.US trying to balance aggressive pricing with the need to reassure users and regulators about its operating standards.
Crypto World
ETH Buy Pressure Hits $5.5B As Price Nears Key Breakout
ETH derivatives show strong buyer dominance, leading traders to target $2,500 to $2,600 as the next crucial rally.
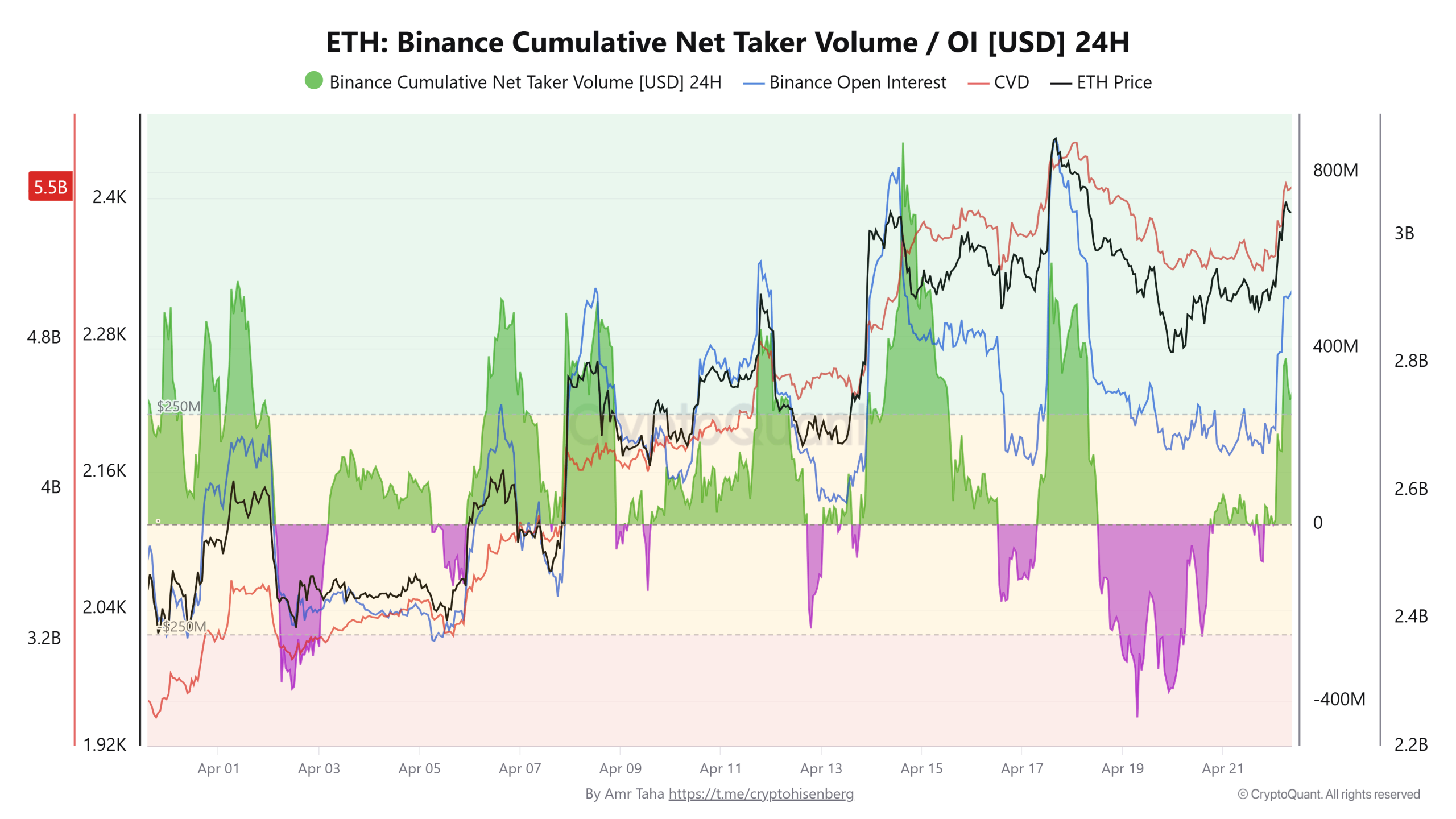
Ether (ETH) futures on Binance have risen to a near two-month high as aggressive buyers stepped into the market over the past week. Buy-taker volume rose above $5 billion, and the current setup suggests the ETH rally is poised to continue.
On Binance, the 24-hour cumulative net taker volume reached $5.5 billion, rising 72% from $3.2 billion earlier in the month. The metric tracks the difference between market buy and sell orders, indicating who is driving price action.

The 30-day average has stayed positive since March 1, returning to levels last seen in July 2022. The positive readings point to consistent buyer aggression.

Crypto analyst Amr Taha explained that when the buying spikes near local highs, it signals stronger conviction from participants. The sustained demand of this kind often keeps buyers in control of the short-term price direction.
Related: The quantum gap: Why Bitcoin and Ethereum are taking different paths on security
Ether’s $2,400 resistance hits a liquidity gap
The ETH price is compressing under the $2,400 level, a resistance that has been tested three times since Feb. 6. Each rejection has reduced the density of the overhead sell orders. A clean move above this level exposes the $2,475–$2,634 range, where a daily fair-value gap lies.
The gap formed during February’s sell-off marks an area where price moved quickly, leaving unfilled orders. ETH’s price may revisit these zones to rebalance flows as the momentum builds.

Ether is also attempting to reclaim the 100-day exponential moving average (EMA), a level associated with trend-continuation phases. The stability above this trend would reinforce the upward rally. The 200-day EMA is drifting toward the upper end of the imbalance zone near $2,634, creating a technical overlap with liquidity.
The derivatives positioning adds context. The futures cumulative volume delta (CVD) continues to climb toward $12.6 billion, while funding rates remain near neutral.
This indicates leverage has not expanded aggressively alongside price. The balance between buyers’ demand and measured leverage keeps the $2,475–$2,634 zone in focus as a near-term liquidity cluster.

Related: Singapore’s OCBC launches tokenized gold fund on Ethereum and Solana
This article is produced in accordance with Cointelegraph’s Editorial Policy and is intended for informational purposes only. It does not constitute investment advice or recommendations. All investments and trades carry risk; readers are encouraged to conduct independent research before making any decisions. Cointelegraph makes no guarantees regarding the accuracy or completeness of the information presented, including forward-looking statements, and will not be liable for any loss or damage arising from reliance on this content.

Crypto World
Bitcoin (BTC) Surges Past $79K as Derivatives Data and Geopolitical Hopes Align

Key Highlights
- BTC surged to $79,472 on Wednesday, marking its strongest monthly performance since April 2025
- The positioning index for Bitcoin climbed to 4.5 from February’s -10.9, indicating strengthening market sentiment
- Total open interest increased 6.7% within 24 hours to reach 260,000 BTC, while futures OI jumped nearly 9% to $62B
- Optimism surrounding potential US-Iran peace negotiations lifted risk-on assets across markets
- Critical resistance levels are positioned at $83,000–$88,000, while support maintains around $72,000–$75,000
Bitcoin achieved a monthly peak of $79,472 during Wednesday’s trading session, representing its most robust 28-day gain since April 2025. The flagship cryptocurrency advanced more than 4% within a single day, approaching the psychologically significant $80,000 threshold as various blockchain analytics and derivatives indicators exhibited positive momentum.

Cryptocurrency analyst Axel Adler Jr. highlighted that the Bitcoin positioning index advanced to 4.5, a substantial improvement from February’s reading of -10.9. This composite indicator monitors net taker flow patterns, open interest dynamics, funding rate behavior, and exchange balance shifts through a unified measurement.
Total open interest expanded by 6.7% across a 24-hour period, reaching 260,000 BTC. The rolling 30-day change in open interest currently registers at +14.5%, with 23 out of the last 30 trading sessions concluding in positive territory.
Futures open interest for BTC experienced a dramatic surge of nearly 9%, pushing above the $62 billion threshold. CME’s open interest advanced 0.50% while Binance registered close to 2% growth following President Trump’s remarks regarding diplomatic negotiations.
President Donald Trump indicated that diplomatic discussions between the United States and Iran could potentially commence as early as Friday, as reported by the New York Post. This announcement followed his determination to extend the Iran ceasefire agreement without a defined endpoint.
Equity markets in the United States also registered approximately 1% gains on Wednesday, with the S&P 500, Nasdaq 100, and Dow Jones Industrial Average all posting advances. Risk-oriented assets responded favorably across the board to the geopolitical developments.
Iranian officials have yet to confirm their participation in the proposed negotiations. Complicating matters, Iranian military forces reportedly seized two commercial cargo vessels near the strategically important Strait of Hormuz just hours following the ceasefire extension announcement, introducing additional uncertainty.
Critical Price Zones Under Observation
Bitcoin has successfully breached a downward-sloping trendline originating from its October 2025 all-time high near $126,000 and recaptured the 100-day exponential moving average. The immediate test zone sits at $81,000, where a fair-value gap indicates potential liquidity imbalances.
The $83,000–$85,000 range represents a probable profit-realization zone for short-term position holders. Beyond that threshold, the $88,000–$91,000 corridor marks a significant supply concentration where substantial trading volumes previously occurred.
The realized price for holders in the three-to-six-month cohort currently stands at $91,600, reinforcing this range as a pivotal decision zone for market participants.
Market analyst Ali Charts identified a Morning Star candlestick formation developing on Bitcoin’s monthly timeframe — a three-candle reversal pattern that he interprets as evidence of seller exhaustion and emerging buyer dominance. According to his historical analysis, price action typically experiences an approximate 8% retracement before the primary upward movement initiates.
Support Zones and Downside Scenarios
Analyst Crazzyblockk pinpointed the $72,000–$75,000 range as a robust support foundation, reinforced by realized price concentrations from intermediate-term holders. A decisive break beneath this band could force additional supply into underwater positions.
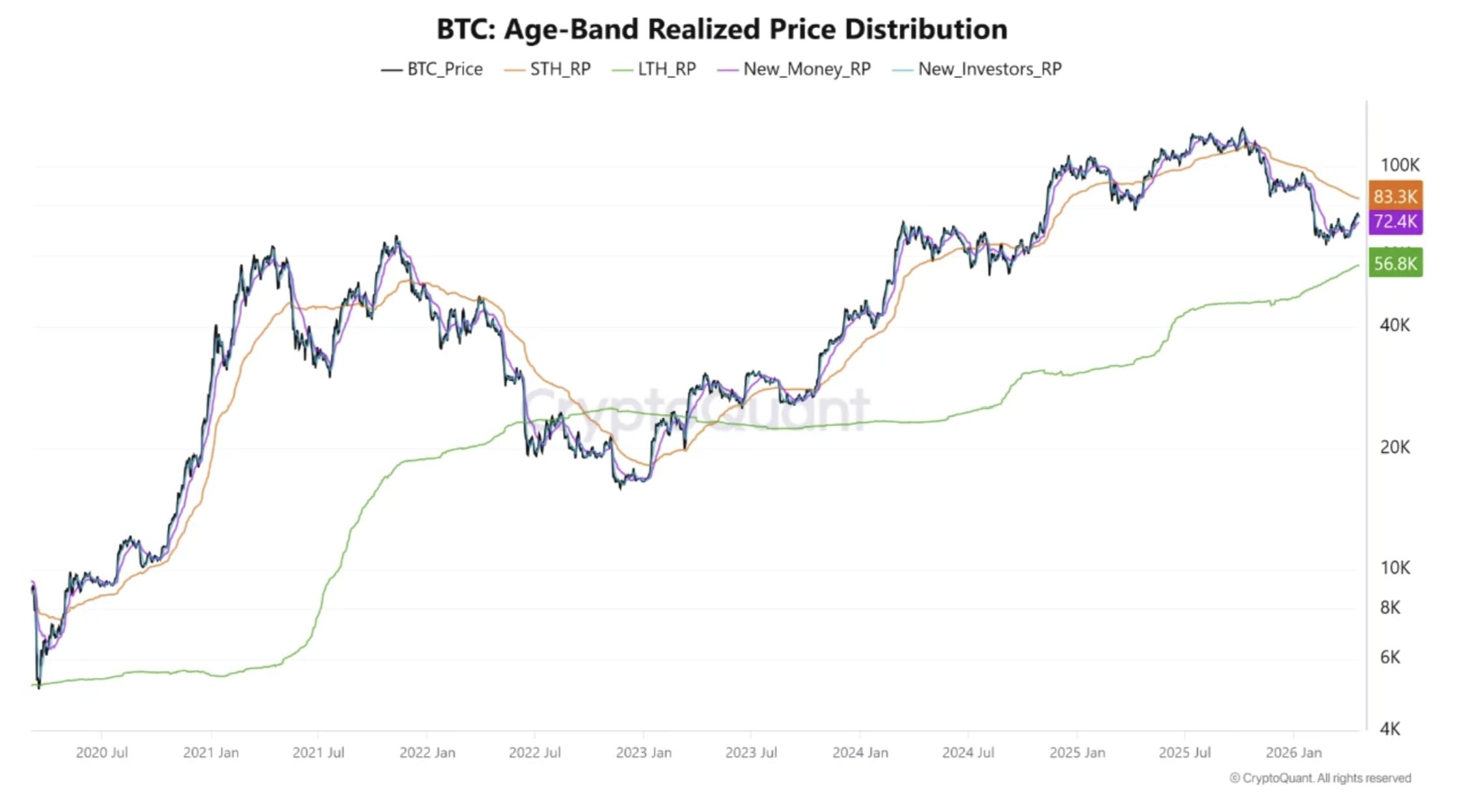
Grayscale Research had previously indicated that Bitcoin most likely established a bottom formation within the $65,000–$70,000 corridor. The Bitcoin Bull Index shifted to neutral territory for the first time in half a year, according to CryptoQuant’s head of research, Julio Moreno.
Trading volumes contracted by 32% throughout the price recovery, suggesting measured caution among market participants despite the upward price movement.
BTC futures open interest across both CME and Binance platforms continued their upward trajectory as of Wednesday afternoon, reflecting sustained positioning activity in derivatives markets.
Crypto World
SEC Near Tokenized Securities Exemption: Atkins Signals Policy Shift
The U.S. Securities and Exchange Commission is approaching the release of an innovation-focused exemption intended to enable limited onchain trading of tokenized securities within a clearly cabined and compliant framework. The revelation comes from remarks by SEC Chair Paul Atkins at the Economic Club of Washington, signaling a deliberate step toward regulated experimentation in tokenized markets while the agency continues to flesh out longer-term rules. According to Cointelegraph’s coverage of the remarks, the exemption would provide a structured pathway for market participants to facilitate trading of blockchain-based securities without altering the agency’s broader securities framework.
In remarks that have drawn attention across regulatory and market circles, Atkins described the move as a pragmatic mechanism to facilitate regulated activity in tokenized markets in the near term, even as the commission works toward more comprehensive, future rules. “We are on the cusp of releasing what I call an ‘innovation exemption,’ which will provide market participants with a cabined framework to begin facilitating the trading of tokenized securities onchain in a compliant fashion as the Commission works toward long-term rules of the road,” he said. The November timing and the framing as a temporary, work-in-progress measure reflect a balance between investor protection and practical market development.
The exemption would not grant a broad license to tokenize securities, but would establish a controlled pathway for entities seeking to support onchain trading of digital securities. It aims to unblock limited pilot activities that could yield insights into how existing securities laws apply to blockchain-enabled markets, while preserving a strong supervisory framework. Atkins’ comments come after months of SEC deliberations on how tokenized securities should fit within the agency’s jurisdiction and how markets might operate under a clearer, interim structure. As context, he noted in July 2025 that the agency had been weighing targeted relief to support tokenization and new trading methods, underscoring a phased approach rather than an immediate overhaul of securities law.
Earlier, Commissioner Hester Peirce indicated that staff were still developing the exemption, seeking to balance experimentation with careful assessment of how onchain markets interact with current securities statutes. These discussions are part of the SEC’s larger project to clarify digital asset classifications and their regulatory treatment, as the agency continues to refine its approach to tokenized instruments while pursuing longer-term policy objectives.
Key takeaways
- The SEC is nearing an “innovation exemption” to permit cabined, onchain trading of tokenized securities within a compliant framework.
- The exemption would create a structured pathway for firms to facilitate tokenized securities trading as the SEC develops longer-term rules.
- The move builds on the agency’s token taxonomy guidance and its broader effort to delineate which digital assets fall under securities laws.
- The White House is reviewing the related interpretive guidance, with a formal decision still pending as of the latest updates.
- Market participants—exchanges, issuers, broker-dealers, and banks—will need to align compliance programs, licensing considerations, and AML/KYC processes with the evolving framework.
Strategic rationale behind the innovation exemption
The proposed exemption represents a measured attempt to address real-world constraints that have limited the growth of tokenized securities in the United States. By providing a cabined framework, the SEC seeks to enable permissible experimentation with blockchain-based trading while ensuring investor protection, auditability, and ongoing regulatory oversight. The approach acknowledges a regulatory gap: tokenized securities can leverage the benefits of distributed ledgers and programmable settlement, yet lack a clear, interim path for compliant operation. The exemption is intended as a practical stepping stone, allowing market participants to explore onchain mechanics, settlement, disclosure, and oversight within defined guardrails as the SEC implements longer-term rulemaking.
We are on the cusp of releasing what I call an “innovation exemption,” which will provide market participants with a cabined framework to begin facilitating the trading of tokenized securities onchain in a compliant fashion as the Commission works toward long-term rules of the road.
According to Cointelegraph’s reporting on Atkins’ remarks, the emphasis is on a controlled, up-and-running pilot path rather than an open-ended market license. The approach is intended to reduce regulatory ambiguity, support orderly transitions from traditional markets to tokenized equivalents, and inform subsequent rulemaking through practical experience. In this framing, the exemption serves as a bridge between today’s securities framework and tomorrow’s potentially tokenized market structure.
Regulatory scaffolding: taxonomy, guidance, and interagency process
The development of an innovation exemption sits within the SEC’s broader effort to clarify how digital assets are treated under federal securities laws. In March, the agency issued interpretive guidance that outlined a token taxonomy, categorizing digital assets into digital commodities, collectibles, tools, and stablecoins, with tokenized securities placed under the SEC’s core jurisdiction. The taxonomy was described as a long-overdue clarifying step intended to delineate when securities laws apply to onchain activities and how the SEC intends to coordinate with other regulators, notably the Commodity Futures Trading Commission.
The interpretive guidance was presented as a transitional tool ahead of potential market-structure legislation and as a means to establish clearer lines of authority in the evolving digital-asset landscape. In late March, the agency circulated the proposed interpretation to the White House for review, a step that regulators commonly take before formal publication. As of the latest records, the proposal remained under White House consideration, illustrating the cross-cutting nature of tokenized markets and the need for interagency alignment. The ongoing review underscores the regulatory complexity and the potential for cross-border differences in treatment of digital assets, including how MiCA and similar frameworks may interact with U.S. policy goals.
In parallel, SEC officials and commentators have framed the taxonomy as a bridge to future market structure legislation and as a means to delineate the SEC’s role relative to the CFTC. Atkins has described the taxonomy as a necessary, long-overdue step toward clearer rules for digital assets, signaling that the agency’s stance is moving toward greater clarity even as it pursues incremental, testable reforms in the near term. The White House review and potential alignment with broader international standards are likely to influence the precise scope and conditions of any innovation exemption.
Implications for market participants and compliance programs
For exchanges, broker-dealers, asset managers, and banking counterparts, the proposed exemption signals a shift from theoretical policy debates to pragmatic, rules-based experimentation. If adopted, the cabined framework would require firms to implement enhanced controls around onboarding, AML/KYC, trade reporting, collateral management, and disclosures—areas where the SEC has consistently emphasized investor protection and market integrity. Compliance programs would need to stay adaptable, balancing rapid experimentation with robust risk management, and ensuring alignment with continuing rulemaking and enforcement priorities.
The exemption would also have implications for licensing and supervisory oversight. As tokenized securities trading onchain expands, firms may require specific registrations or exemptions under the Securities Act, along with ongoing supervision by the SEC. Cross-border participants could face additional considerations, given diverging regulatory approaches in other jurisdictions and the EU’s MiCA framework, which adds another layer to global coordination on tokenized markets. The approach aims to reduce the risk of regulatory gaps, but it also raises questions about the timing, scope, and sequencing of enforcement actions as activities scale beyond pilot phases.
From an enforcement and compliance perspective, the interim nature of the exemption means firms should monitor evolving guidance, interpretive interpretations, and White House decisions closely. The pathway emphasizes transparency, recordkeeping, and clear delineation of the activities permitted under the cabined framework. Market participants may need to adjust internal controls to differentiate between permitted tokenized trading and activities that remain outside the exempted scope, ensuring that participation remains within regulatory boundaries while contributing data and experience to inform longer-term policy design.
Closing perspective
The push toward an innovation exemption highlights a deliberate, regulator-led balance between enabling structured experimentation in tokenized securities and preserving core investor protections. As White House review progresses and the SEC’s token taxonomy guidance continues to shape jurisdictional boundaries, market participants should prepare for a transitional period in which pilot activity informs future rulemaking, licensing requirements, and cross-agency coordination. The coming months will reveal how progressively clarified rules will interact with ongoing developments in both U.S. policy and global regulatory approaches, including MiCA considerations and cross-border supervision.
-

 Sports6 days ago
Sports6 days agoNWFL Suspends Two Players Over Post-Match Clash in Ado-Ekiti
-

 Fashion5 days ago
Fashion5 days agoWeekend Open Thread: Theodora Dress
-

 Politics5 days ago
Politics5 days agoPalestine barred from entering Canada for FIFA Congress
-
Entertainment3 days ago
NBA Analyst Charles Barkley Chimes in on Ice Spice McDonald’s Fiasco
-

 Business4 days ago
Business4 days agoPowerball Result April 18, 2026: No Jackpot Winner in Powerball Draw: $75 Million Rolls Over
-

 Tech4 days ago
Tech4 days agoAuto Enthusiast Scores Running Tesla Model 3 for Two Grand and Turns It Into Bare-Bones Go-Kart
-
 Politics4 days ago
Politics4 days agoZack Polanski demands ‘council homes not luxury flats for foreign investors’
-

 Crypto World5 days ago
Crypto World5 days agoRussia Pushes Bill to Criminalize Unregistered Crypto Services
-
 Politics2 days ago
Politics2 days agoGary Stevenson delivers timely reminder to register to vote as deadline TODAY
-

 Business20 hours ago
Business20 hours agoRolls-Royce Voted UK’s Most Iconic Trade Mark as IPO Register Hits 150
-

 Politics11 hours ago
Politics11 hours agoDisabled people challenge government SEND proposals over segregation concerns
-

 Politics11 hours ago
Politics11 hours agoMaking troops accountable for war crimes threatens US alliance, ex-SAS colonel warns
-

 Business6 days ago
Business6 days agoCreo Medical agree sale of its manufacturing operation
-

 Crypto World5 days ago
Crypto World5 days agoRussia Introduces Bill To Criminalize Unregistered Crypto Services
-

 Politics12 hours ago
Politics12 hours agoStarmer handler McSweeney to be dragged from shadows by Foreign Affairs Committee
-

 Politics12 hours ago
Politics12 hours agoZack Polanski responds to home secretary’s taser threat
-
Politics13 hours ago
Wings Over Scotland | How To Get Away With Crimes
-

 Crypto World4 days ago
Crypto World4 days agoKelp DAO rsETH Bridge Hack Drains $292M as DeFi Losses Top $600M in Two Weeks
-

 Politics10 hours ago
Politics10 hours ago‘Iran is still a nuclear threat’
-

 Business7 days ago
Business7 days agoCheaper Doritos and Lays helps PepsiCo win back struggling snackers










You must be logged in to post a comment Login