Crypto World
Payward’s $550M Bitnomial deal aims to lock up U.S. crypto derivatives plumbing


Kraken parent Payward will buy Bitnomial for up to $550M, adding a full CFTC derivatives stack just as Deutsche Börse’s $200M stake backs its U.S. build‑out.
Summary
- Payward, Kraken’s parent, plans to buy 100% of U.S. crypto derivatives venue Bitnomial for up to $550 million in cash and stock, pending CFTC approvals in H1 2026.
- Bitnomial is the first crypto‑native platform to hold all three key U.S. derivatives licenses — DCM, DCO and FCM — giving Payward a vertically integrated, onshore futures and clearing stack.
- The move follows Deutsche Börse’s $200 million investment for a 1.5% stake in Payward, valuing Kraken at about $13.3 billion and underscoring Wall Street’s bet on its derivatives build‑out.
Payward Inc., the parent company of crypto exchange Kraken, has agreed to acquire Chicago‑based crypto derivatives venue Bitnomial in a deal worth up to $550 million in cash and stock, further accelerating its push into U.S. regulated futures and options. The companies expect the transaction to close in the first half of 2026, subject to customary regulatory approvals from the Commodity Futures Trading Commission (CFTC) and other U.S. authorities.
Bitnomial is the first crypto‑native operator to assemble the full CFTC derivatives stack, running a Designated Contract Market, a Derivatives Clearing Organization and a Futures Commission Merchant under one roof. According to Bitnomial’s own materials, its exchange and clearinghouse support “leveraged spot, perpetuals, futures, options, and prediction markets, all on one CFTC‑regulated exchange with crypto margin and settlement,” giving Payward an immediate onshore home for products that previously leaned on offshore venues.
Under the plan, Payward will plug Bitnomial’s trading and clearing infrastructure into Kraken, NinjaTrader and Payward Services, offering banks, brokerages and fintechs a single API into CFTC‑regulated crypto derivatives. Kraken has already been expanding in this direction; in a prior crypto.news story it acquired CFTC‑regulated Small Exchange for about $100 million to secure a DCM license, and later used that footprint to launch U.S. regulated derivatives tied to CME‑listed futures.
The Bitnomial deal lands just days after German exchange operator Deutsche Börse agreed to buy a 1.5% fully diluted stake in Payward for $200 million, in a transaction that values Kraken at roughly $13.3 billion. Deutsche Börse said the partnership is meant to “deepen” its role in regulated crypto, tokenized markets and derivatives, with a focus on “enhanced liquidity for institutional clients across geographies,” effectively giving Europe’s largest exchange group a front‑row seat in Kraken’s derivatives build‑out.
Regulators have also been preparing the ground for this shift. CFTC Commissioner Caroline Pham has pushed to bring leveraged spot crypto trading and perpetual‑style products onshore under full DCM and DCO oversight, arguing they can be offered safely if “brought into our markets under well‑defined rules and supervision.” In that context, Bitnomial’s December 2025 launch of the first‑ever leveraged retail spot crypto market under CFTC jurisdiction — which CEO Luke Hoersten called “a watershed moment for U.S. crypto markets” — looks like a dress rehearsal for the infrastructure Payward is now buying.
For institutional order flow, the battle increasingly turns on who controls the cleanest regulatory pipe: the combination of licenses, clearing and prime‑style services that let banks and asset managers trade crypto derivatives without touching offshore platforms. With Bitnomial’s stack and Deutsche Börse’s capital, Payward is positioning Kraken as a CME‑style hub for digital asset futures, options and leveraged spot inside the U.S., echoing its broader strategy to bridge tokenized assets, equities and derivatives through initiatives like its xStocks platform.
In addition, Kraken’s derivatives and market‑structure push includes stories on its U.S. derivatives rollout, the Small Exchange acquisition, and Deutsche Börse’s $200 million stake in Payward.
Crypto World
eToro (ETOR) Stock Declines 4% Despite Strong Q1 Performance and Strategic Expansion
Key Highlights
-
ETOR shares declined 4.81% following release of quarterly results showing revenue expansion.
-
Commodities segment momentum compensated for declining cryptocurrency trading volumes.
-
Strategic Zengo acquisition advances platform’s self-custody digital asset capabilities.
-
Artificial intelligence features and Agent Portfolios enhance platform’s product suite.
-
Platform reached 4.02 million funded accounts while assets under administration expanded.
Shares of eToro (ETOR) experienced downward pressure Tuesday despite the investment platform delivering solid first-quarter financial results and demonstrating product diversification. ETOR closed at $36.88, representing a 4.81% decline, after initially climbing above $41 earlier in the session. Market attention centered on cryptocurrency trading headwinds, artificial intelligence integrations, commodities segment performance, and the strategic Zengo transaction.
Shares Retreat Despite Impressive Quarterly Performance
eToro delivered improved first-quarter profitability as its diversified asset strategy benefited from commodities segment strength. Net contribution expanded 19% on an annual basis to $258 million, versus $217 million in the prior-year period. Management attributed the growth to accelerated commodities trading momentum.
Bottom-line performance strengthened significantly throughout the three-month period, with net income surging 37% year-over-year to $82 million. Adjusted net income posted a 28% increase to $86 million, while adjusted EBITDA jumped 35% to $109 million. Furthermore, adjusted diluted earnings per share came in at $0.91, representing growth from $0.77 in the comparable quarter.
Customer acquisition efforts yielded positive results during the reporting period. Funded accounts grew 12% annually to 4.02 million, driven by increased marketing investments. Assets under administration rose 15% to $17 billion, while the company maintained cash and short-term investments totaling $1.3 billion.
Digital Asset Trading Slows While Commodities Segment Accelerates
Cryptocurrency trading faced headwinds throughout the quarter, notwithstanding eToro’s ongoing digital currency platform development. Management disclosed that April cryptocurrency transactions decreased 32% year-over-year to 2 million. Average invested amounts per cryptocurrency trade fell 22% to $207.
Cryptoasset revenue contracted to $2.15 billion compared with $3.5 billion during the corresponding period last year. However, cryptocurrency-related expenses similarly declined sharply to $2.1 billion. The softer digital asset performance didn’t prevent eToro from delivering enhanced consolidated financial results.
The commodities division emerged as the platform’s primary growth engine. This segment generated approximately 60% of total trading commissions during the three-month period. Additionally, commodities volumes surged nearly fourfold annually following eToro’s introduction of round-the-clock trading for select instruments.
Artificial Intelligence Features, Strategic Acquisition and Platform Development Drive Forward Momentum
eToro maintained its product innovation pace across trading, investment, wealth advisory, and neo-banking services. The platform introduced continuous trading for specific commodities, equities and indices. Management also added Japanese equity access, providing users exposure to securities from 26 global exchanges.
Artificial intelligence capabilities received enhanced focus during the reporting period. eToro unveiled Agent Portfolios and expanded applications within the eToro App Store ecosystem. The platform incorporated xAI’s Grok 4.2 technology into Tori, its artificial intelligence-powered investment advisory tool.
The Zengo transaction continues playing a pivotal role in eToro’s cryptocurrency roadmap. The $70 million acquisition delivered self-custodial wallet capabilities to eToro’s expanding product ecosystem. Management intends to bridge conventional financial services with blockchain infrastructure, prediction markets, and cryptocurrency-native offerings.
Crypto World
Cardano Founder Praises Revised CLARITY Act Before Senate Vote
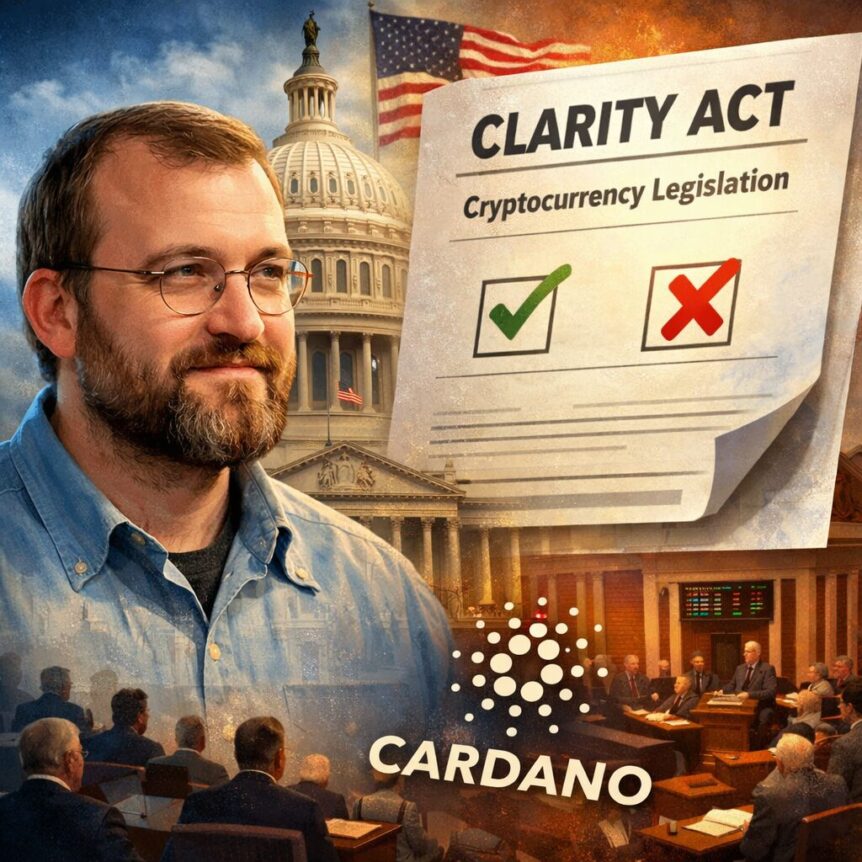
The latest draft of the CLARITY Act gained support from major crypto stakeholders before the Senate committee markup this week. Cardano founder Charles Hoskinson praised the revised text after criticizing earlier proposals. Meanwhile, senators continued negotiations over ethics provisions that could influence bipartisan backing for the bill.
Cardano Founder Supports Updated Crypto Bill
The Senate Banking Committee released the updated CLARITY Act draft before the scheduled May 14 markup session. The revised text introduced changes targeting decentralized finance protections and stablecoin regulations. Consequently, several crypto industry participants responded positively to the amendments.
Hoskinson described the latest draft as a major improvement compared to previous versions of the legislation. He had criticized earlier drafts because of concerns surrounding protections for decentralized finance activities. However, the revised proposal addressed several areas that crypto firms had previously challenged.
The updated bill includes provisions supporting decentralized governance structures and non-custodial staking activities. In addition, the draft recognizes distributed validator participation within decentralized blockchain networks. The legislation also preserves stablecoin rewards, although firms cannot distribute rewards on idle balances.
Senate Negotiations Focus on Ethics Provision
Senators continued private discussions to resolve remaining concerns before Thursday’s committee markup session. The ethics provision remained one of the most contested sections within the broader crypto legislation package. Therefore, lawmakers sought compromises that could secure bipartisan committee support.
Crypto journalist Eleanor Terrett reported that Republican and Democratic senators held meetings regarding the unresolved ethics language. The discussions could influence support from Democratic members before the committee vote. Moreover, lawmakers aimed to avoid delays that could threaten the bill’s momentum.
Democratic Senator Kirsten Gillibrand previously stated that stronger ethics rules remained necessary for the legislation’s passage. Senator Ruben Gallego and other committee Democrats could also shape the outcome. Meanwhile, Senate Banking Committee Chair Tim Scott continued efforts to advance the revised legislation.
Coinbase and Banks React to Revised Draft
Coinbase reviewed the latest draft details as negotiations between crypto firms and banking groups continued. The exchange participated in discussions surrounding stablecoin yield provisions within the revised legislation. Consequently, the company welcomed several compromise measures included in the updated text.
Coinbase Chief Policy Officer Faryar Shirzad indicated that the revised proposal reflected extensive negotiations among the parties involved. The company also supported progress toward the committee markup process scheduled this week. Besides, several crypto firms viewed the updated framework as more favorable for decentralized finance operations.
Banking groups maintained objections despite the latest revisions to the stablecoin sections. American Bankers Association CEO Rob Nichols urged bank executives to contact senators regarding remaining concerns. He warned that the draft could still increase the risk of deposit flight for traditional banks.
The CLARITY Act represents one of the most significant federal crypto regulatory proposals currently under Senate review. Lawmakers have worked to balance crypto industry demands with banking sector concerns throughout negotiations. Consequently, Thursday’s markup session could determine the legislation’s next stage within the Senate process.
Crypto World
South Africa Manufacturing Show 2026 to Spotlight Industry 4.0, AI and Smart Factory Innovation

South Africa’s manufacturing sector is entering a new phase of digital transformation as industrial leaders accelerate investments in smart manufacturing, AI-driven operations, cybersecurity, and supply chain modernization. Against this backdrop, the 33rd Edition of the South Africa Manufacturing Show 2026 will bring together key stakeholders shaping the future of industrial innovation across the African continent.
Organized by Exito Media Concepts, the event will take place on June 11, 2026, at Focus Rooms – Universe, South Africa. The summit forms part of Exito’s international event series focused on technology, digital transformation, cybersecurity, manufacturing, and emerging enterprise sectors.
As manufacturers continue integrating Industry 4.0 technologies into production ecosystems, the event aims to provide a strategic platform for discussions around operational resilience, automation, AI adoption, robotics, IoT, cybersecurity, and sustainable industrial transformation.
The summit is expected to convene more than 150 C-level executives, directors, technology leaders, and policymakers from South Africa’s leading manufacturing organizations and institutions.
According to the organizers, the event agenda will focus on practical strategies and frameworks designed to help businesses improve efficiency, modernize operations, and accelerate digital adoption across the industrial sector.
Key discussion topics will include:
- Smart manufacturing and AI-powered industrial systems
- Connected supply chains and logistics optimization
- Cybersecurity resilience for smart factories
- Robotics and operational automation
- Digital transformation in mining and automotive sectors
- Sustainable manufacturing practices
- Data-driven operational intelligence
- Workforce development for Industry 4.0 environments
The event will also feature several prominent industry leaders and executives, including Joseph Ndaba of Mafikeng Digital Innovation Hub (MDIHub), Irshaad Kathrada of the Localisation Support Fund, Tapiwa Samanga of the Production Technologies Association of South Africa, and executives from companies including Sasol, Mahindra South Africa, Omnia Holdings, Reckitt, and Metair Investments.
A major highlight of the summit will be the “Manufacturing 100” recognition program, which celebrates influential leaders driving innovation, digital transformation, and operational excellence across South Africa’s manufacturing ecosystem.
The South Africa Manufacturing Show 2026 is also CPD Certified, allowing attendees to earn up to eight hours of CPD points while participating in the summit.
For more information about the event, visit South Africa Manufacturing Show 2026
Crypto World
Roaring Kitty’s Deleted X Post Triggers 90% Crash in RKC Meme Coin

Roaring Kitty’s deleted post on X triggered a crash in the meme coin RKC, wiping out 90% of its value within hours.
Traders who bought into the hype lost hundreds of thousands of dollars, while the coin’s developer reportedly cashed out over $600,000 before it collapsed.
RKC Dev Profited Over $600K from Token
Keith Gill’s verified X account, popularly known by his 1.6 million followers as Roaring Kitty, ended a 16-month silence on May 11 with a post that sent traders into a frenzy. At around 21:13 GMT, the account shared a Solana Pump.fun contract address for a newly launched meme coin called Red Kitten Crew (RKC), alongside a short cartoon clip.
Minutes later, the account shared a second post featuring an image captioned “red bandit crew 4 life,” which was later deleted. The sudden activity started a rush of speculative trading that briefly sent RKC soaring before the deletions triggered panic selling, causing the token to crash 90% and wiping millions from its market cap.
Blockchain analytics firm Lookonchain later reported that the meme coin’s developer had already cashed out 6,260 SOL, worth around $611,000, before the posts were removed. According to them, the individual used 20 SOL worth roughly $1,950 across 10 wallets to acquire 395.18 million RKC tokens, representing 39.52% of the total supply, before selling the entire stash for $495,000.
Lookonchain also revealed that the developer earned an additional 1,209 SOL, worth approximately $118,000, through creator fees.
Roaring Kitty Meme Coin Posts Cause Hack Speculation
On-chain analysts are saying that the incident followed a pattern they’ve seen many times in crypto, where influencers create hype, developers cash out, and retail traders are left with losses. Others also questioned the authenticity of the posts, noting Keith Gill has built his online presence around GameStop commentary and has never publicly promoted meme coins before, leading to speculation that the account may have been hacked.
There’s been a trend of high-profile X accounts being compromised to promote meme coins, with similar breaches in the past targeting major public figures and companies such as Michael Saylor and Kylian Mbappé. The former’s account was used to push a fake Bitcoin giveaway, while the latter’s promoted a Solana meme coin scam, with both incidents resulting in a spike in trading volumes before a collapse.
At the same time, Pump.fun has also been involved in controversy, with researchers claiming that a large percentage of tokens launched on the platform display characteristics commonly associated with scams or wash trading. The Solana-based meme coin maker has also been targeted by two class-action lawsuits in the past, with both accusing it of violating U.S. securities laws by facilitating the launch of unregistered tokens and allegedly collecting up to $500 million in related fees.
The post Roaring Kitty’s Deleted X Post Triggers 90% Crash in RKC Meme Coin appeared first on CryptoPotato.
Crypto World
Galaxy SharpLink fund targets $125M DeFi yield


Galaxy Digital and SharpLink have launched the Galaxy SharpLink Onchain Yield Fund with $125 million to deploy into DeFi protocols.
Summary
- SharpLink will commit $100 million from its staked ETH treasury to the fund, with Galaxy Digital contributing $25 million and managing investments.
- Capital will be deployed across DeFi liquidity protocols and onchain yield strategies while maintaining SharpLink’s core Ethereum exposure.
- SharpLink holds 872,984 ETH in treasury and has generated 18,800 ETH in staking rewards since launching its Ethereum strategy in June 2025.
Galaxy Digital and SharpLink announced a non-binding agreement on May 11 to launch the Galaxy Sharplink Onchain Yield Fund, a $125 million limited partnership structured to put part of SharpLink’s staked Ethereum treasury to work across DeFi strategies. Galaxy will serve as investment manager.
SharpLink will contribute $100 million from its staked ETH position, with Galaxy adding $25 million of its own capital. Mike Novogratz, founder and CEO of Galaxy, said the infrastructure for institutional DeFi participation “has matured to a point where allocators can access yield, liquidity, and risk management with the same rigor they expect in traditional markets.”
What the fund will do
The fund will deploy capital across DeFi liquidity protocols and other onchain yield-generating strategies. The structure is designed to keep SharpLink’s core ETH exposure intact while adding an active yield layer on top of its existing staking operations.
SharpLink CEO Joseph Chalom said the strategy aims to provide liquidity to high-quality protocols while generating returns above the average Ethereum staking rate. “Operational rigor is non-negotiable,” he said, noting the fund’s risk management framework will apply the same discipline Galaxy uses across its lending, trading, and asset management businesses.
The announcement came alongside SharpLink’s Q1 2026 earnings, which showed revenue rising to $12.1 million from $742,000 in the same period a year earlier. SharpLink posted a net loss of $685.6 million for the quarter, driven by unrealized depreciation in its ETH portfolio as Ethereum fell from roughly $3,354 in mid-January to $2,104 by quarter-end.
SharpLink’s position in the Ethereum ecosystem
SharpLink holds 872,984 ETH and is the second-largest publicly traded corporate Ethereum holder, behind Bitmine Immersion Technologies. Its treasury has generated 18,800 ETH in staking rewards since June 2025 with over 90% of its holdings staked at all times.
The Galaxy fund marks a meaningful shift in how public companies are thinking about crypto treasury management, moving beyond passive staking toward active DeFi deployment. Galaxy also launched a separate tokenized cash fund with State Street last week built on Solana, signalling a broader push by the firm into institutional onchain yield infrastructure.
Crypto World
DTCC Expands Collateral Platform With Chainlink

TLDR
- DTCC integrated Chainlink infrastructure into its blockchain-based collateral management platform to support real-time operations.
- The Collateral AppChain operates on a Besu-based blockchain and enables 24/7 collateral movement.
- Chainlink provides pricing data, valuation inputs, and orchestration services for margining and settlement.
- DTCC aims to reduce delays and fragmentation in traditional collateral systems across global markets.
- The integration builds on the 2024 Smart NAV pilot involving JPMorgan, Franklin Templeton, and BNY.
- More than 50 firms joined DTCC’s tokenization working group with production trades planned for July.
The Depository Trust & Clearing Corporation has integrated Chainlink infrastructure into its blockchain-based collateral platform. The move extends prior collaboration into core collateral management functions across global markets. The system will support pricing, valuation, margining, collateral optimization, and settlement on a 24/7 basis.
DTCC Advances Tokenized Collateral Infrastructure
DTCC confirmed that its Collateral AppChain will operate on a Besu-based blockchain network. The platform will use tokenization to represent assets and enable continuous collateral management. It will also automate workflows through smart contracts and support near real-time collateral movement.
The firm said the system targets delays and fragmentation across current collateral processes. Assets often remain siloed across institutions and time zones under existing models. DTCC aims to enable faster collateral transfers across traditional financial markets and blockchain networks.
Nadine Chakar, managing director and global head of digital assets, outlined the objective. She said, “By leveraging tokenization and distributed ledger technology to modernize collateral mobility, our goal is to enable 24/7, near real-time collateral management across global markets and blockchains.” She confirmed that the company will modernize collateral operations through distributed ledger technology.
DTCC launched the tokenized collateral platform last year as part of its digital asset strategy. The company positioned collateral mobility as a core institutional blockchain use case. It built the AppChain structure to host tokenized assets within a controlled network.
Chainlink Provides Data and Orchestration Layer
Chainlink will supply the data and orchestration framework for the collateral system. The infrastructure will connect asset prices, valuations, and settlement instructions to the blockchain. It will also support eligibility checks and margin calculations in real time.
Chainlink operates as a decentralized oracle network that delivers external data to blockchains. Blockchains cannot access outside information without such services. The network feeds price data, APIs, and other inputs into smart contracts.
The integration builds on the Smart NAV pilot completed in 2024. DTCC and Chainlink tested bringing mutual fund net asset value data onto blockchains. JPMorgan, Franklin Templeton, and BNY joined the pilot to explore fund tokenization across multiple chains.
DTCC has also expanded tokenization beyond collateral services. The company said over 50 firms joined a working group for The Depository Trust Company’s tokenization service. It plans limited production trades in July and a broader launch in October.
DTCC subsidiaries processed $4.7 quadrillion in securities transactions in 2025. Its depository subsidiary provided custody and asset servicing for securities issues valued at $114 trillion. The firm continues to develop blockchain infrastructure within its existing market operations framework.
Crypto World
BFSI Innovation & Technology Summit South Africa 2026 to Focus on AI, Cybersecurity and Financial Transformation

South Africa’s banking, financial services, and insurance sector continues to evolve rapidly as institutions modernize operations, strengthen cybersecurity frameworks, and accelerate digital transformation initiatives. To support this transition, the 36th Edition of the BFSI Innovation & Technology Summit – South Africa 2026 will gather financial and technology leaders to discuss the future of innovation across the country’s financial ecosystem.
Hosted by Exito Media Concepts, the summit will take place on June 10, 2026, at Focus Rooms – Universe, South Africa, under the theme “Recalibrating South Africa’s Financial Edge.”
The event comes at a time when South African financial institutions are increasingly investing in intelligent automation, AI-powered systems, cloud technologies, real-time payment infrastructure, and advanced cybersecurity solutions to remain competitive in an evolving digital economy.
According to the organizers, the summit will host more than 200 senior decision-makers, including CTOs, CIOs, CISOs, digital transformation leaders, and executives from major banking and insurance organizations across the country.
Discussions throughout the event will focus on several major industry priorities, including:
- AI-powered financial transformation
- Cybersecurity and secure cloud adoption
- Financial inclusion through technology
- Data privacy and POPIA compliance
- Legacy infrastructure modernization
- ESG-focused and ethical finance strategies
- Hyper-personalized customer experiences
- Automation and operational resilience
The summit will feature presentations and panel discussions from influential executives and industry experts, including Lelané Bezuidenhout of the Financial Planning Institute of Southern Africa, Pragashani Reddy of Absa Group, Meshack Ndwandwe of First National Bank, Dr. Gavin Moss of Rand Merchant Bank, and other leaders shaping South Africa’s financial technology landscape.
One of the central highlights of the event will be the “BFSI 100” recognition initiative, which honors leading technology executives and innovators driving digital transformation across banking, financial services, and insurance sectors in South Africa.
The summit is CPD Certified and forms part of Exito’s global event portfolio, which includes more than 240 conferences annually across technology, cybersecurity, healthcare, manufacturing, and enterprise innovation sectors.
For additional information about the event, visit BFSI Innovation & Technology Summit South Africa 2026
Crypto World
Bitcoin briefly falls below $80,000, as stocks tumble, yields rise on ugly inflation print


Core consumer prices — which would have stripped out what everyone already knew were surging energy costs — rose 0.4% in April, double March’s 0.2% pace and higher than 0.3% expected by economists.
On a year-over-year basis, core CPI rose 2.8% versus 2.6% in March and 2.7% forecast.
Headline CPI — which does include energy costs — was higher by 3.8% in April versus just 3.3% in March and 3,7% expected. That 3.8% was the fastest pace of inflation since May 2023.
The data has market participants quickly pricing in Federal Reserve rate hikes — a massive change from weeks ago, when the question was how often the Fed would be cutting rates in 2026.
According to CME FedWatch, markets are seeing more than a 35% chance of one or more rate hikes this year.
The news has helped send stocks lower, led by the Nasdaq’s 1.3% decline.
Bitcoin (BTC), though, has been holding steady, currently trading at $80,500, roughly flat over the past 24 hours. Major altcoins like ether (ETH) and XRP (XRP) are down closer to 2.5%.
Crypto World
Privacy emerges as crypto’s next ‘killer app’, according to Bitwise CIO Matt Hougan


Arc, Canton and Tempo, three blockchains focused on stablecoins and tokenization, have raised more than $1 billion combined, highlighting rising institutional demand for privacy-focused crypto infrastructure, according to Bitwise CIO Matt Hougan.
Stablecoin issuer Circle (CRCL) recently raised $222 million at a $3 billion valuation for Arc, while Digital Asset is reportedly raising $300 million at a $2 billion valuation for the Canton blockchain. Tempo, backed by Stripe and Paradigm, previously raised $500 million at a $5 billion valuation.
In a Tuesday blog post, Hougan said the fundraising wave reflects three trends: clearer U.S. regulation, growing demand for private blockchain transactions and rising competition from corporate-backed crypto networks.
Blockchains have long faced a trade-off between speed, cost and security: faster, cheaper networks often make compromises on decentralization or resilience, while more secure chains can be slower and more expensive to use.
That tension is especially important for stablecoins and tokenization, where institutions need transactions to be fast and affordable, but also private, compliant and secure enough for real-world finance.
Hougan said privacy could emerge as a “killer app” for crypto as businesses and consumers become less comfortable with fully transparent blockchains like Ethereum and Solana.
“If you’re a business broadcasting every trade before it’s complete, or a worker whose paycheck is visible to anyone with a block explorer, that transparency is a bug, not a feature,” Hougan said.
He added that the fundraising boom also reflects growing confidence after Congress passed the Genius Act in 2025, giving institutions a clearer regulatory footing to invest in crypto infrastructure.
Read more: ‘Bitcoin transactions can be monitored’: Ray Dalio explains why central banks won’t touch BTC
Crypto World
Ethereum Foundation Launches Clear Signing Standard


The initiative, anchored by ERC-7730 and a new attestation framework, aims to make human-readable transactions the default across wallets and protocols.
-

 Crypto World4 days ago
Crypto World4 days agoHarrisX Poll Found 52% of Registered Voters Support the CLARITY Act
-

 Fashion4 days ago
Fashion4 days agoWeekend Open Thread: Marianne Dress
-

 Crypto World5 days ago
Crypto World5 days agoUpbit adds B3 Korean won pair as Base token gains Korea access
-

 NewsBeat5 days ago
NewsBeat5 days agoNCP car park operator enters administration putting 340 UK sites at risk of closure
-

 Fashion1 day ago
Fashion1 day agoCoffee Break: Travel Steam Iron
-

 Fashion2 days ago
Fashion2 days agoWhat to Know Before Buying a Curling Wand or Curling Iron
-

 Tech3 days ago
Tech3 days agoAuto Enthusiast Carves Functional Two-Stroke Engine from Solid Metal
-

 Politics21 hours ago
Politics21 hours agoWhat to expect when you’re expecting a budget
-
 Politics4 days ago
Politics4 days agoPolitics Home Article | Starmer Enters The Danger Zone
-

 Business3 days ago
Business3 days agoIgnore market noise, India’s long-term story intact, say D-Street bulls Ramesh Damani and Sunil Singhania
-

 Tech2 days ago
Tech2 days agoGM Agrees To Pay $12.75 Million To Settle California Lawsuit Over Misuse Of Customers’ Driving Data
-
 Crypto World6 days ago
Crypto World6 days agoBlackRock CEO Larry Fink Discusses a New Asset Class
-

 Entertainment6 days ago
Entertainment6 days agoSarah Paulson Called Out For Met Gala ‘Hypocrisy’
-

 Entertainment5 days ago
Entertainment5 days agoGeneral Hospital: Ric & Ava Bombshell – Ric’s Massive Secret Exposed!
-
Sports6 days ago
NBA playoff winners and losers: Austin Reaves is not loving Lakers vs. Thunder matchup, but Chet Holmgren is
-
 Entertainment6 days ago
Entertainment6 days agoBold and Beautiful Early Spoilers May 11-15: Steffy Revolted & Liam Overjoyed!
-
 Politics5 days ago
Politics5 days agoSimon Cowell Says He Was ‘Horrible’ To Susan Boyle During BGT Audition
-
 Sports6 days ago
Sports6 days agoUEFA Champions League final schedule, teams, venue, live time and streaming | Football News
-

 Crypto World6 days ago
Crypto World6 days agoRobinhood says Wall Street is building onchain
-

 Tech7 days ago
Tech7 days agoApple and Samsung are dominating smartphone sales so thoroughly that only one other company makes the top 10









You must be logged in to post a comment Login