
Modern fraud attacks look like a relay race where different tools and actors handle each stage of the journey from signup to cash-out.
When you only inspect one signal at a time, such as IP or email, attackers simply shift to a different part of the chain and still succeed.

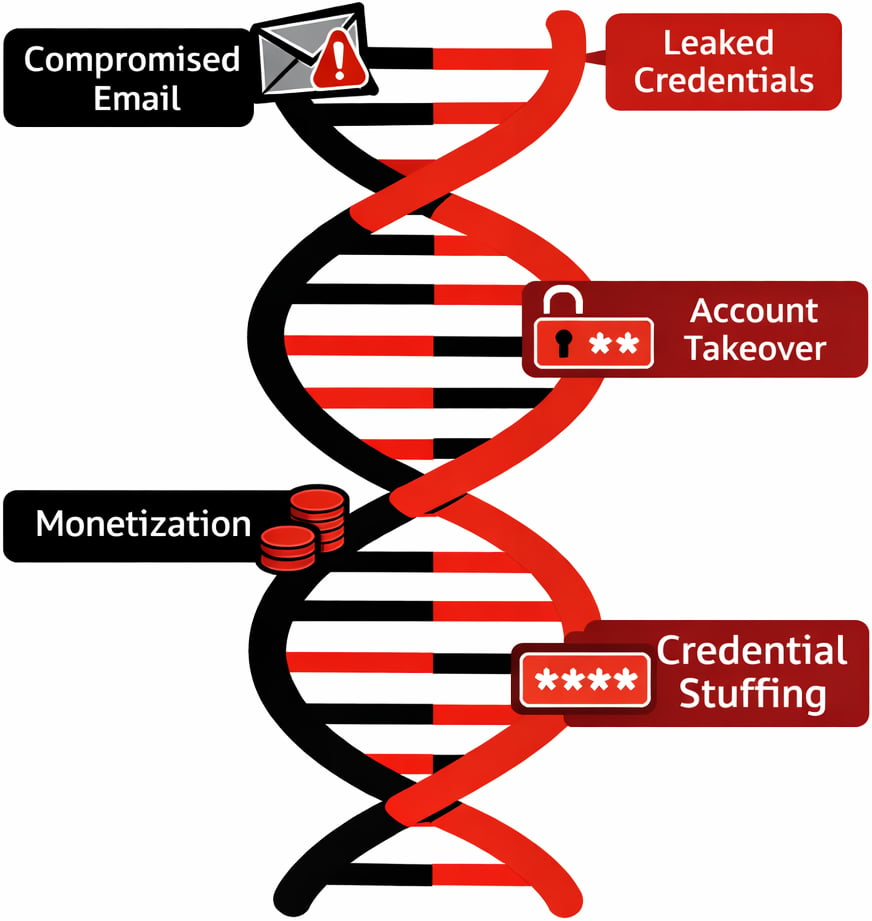
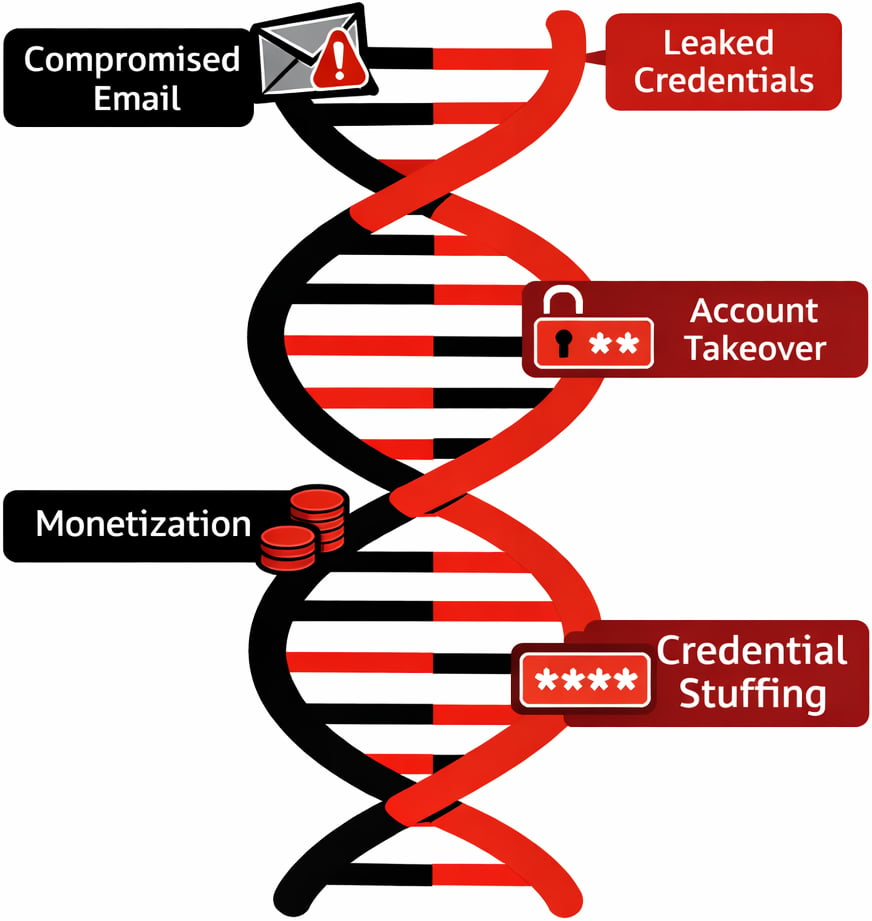
Anatomy of a Modern Fraud Chain
A typical attack chain starts with automation to create scale. Attackers use bots and scripts to open large numbers of accounts with minimal human effort, often rotating infrastructure to avoid rate limits and simple bot rules.
Those bots are usually powered by “aged” or compromised emails and leaked credentials so that every account looks like it belongs to a long standing user instead of something created yesterday.
Residential proxies then mask traffic behind real consumer IP ranges, making traffic appear like normal home users rather than data centers or known VPN services.
Once those accounts are established, they shift tactics from automation to slower, human driven sessions to blend into normal usage.
At this point the chain reaches account takeover and monetization, using malware links, phishing, and credential stuffing outputs to log in, change details, and push through high value transactions.
Throughout this lifecycle, the tools are mixed and matched. A single actor may move from a headless browser and proxy at signup to a mobile device emulator and different proxy provider at login, then hand off access to another party who specializes in draining funds or exploiting promo campaigns.
This is exactly why a point in time, single signal check rarely tells the full story
False Positives from Siloed Checks
When teams lean on one dominant signal, such as IP reputation, false positives become a daily problem. Legitimate users on shared Wi Fi, mobile carrier NATs, or corporate VPNs can inherit the poor reputation of a small number of bad actors on the same ranges, even though their intent is clean.
Blocking by email alone has similar issues, since free webmail domains are used by both sophisticated attackers and completely normal customers.
Identity centric controls on their own also hit a wall. Static data checks, like simple name and document matches, are easy to spoof for synthetic identities built from real data fragments.
Device centric controls that only look for rooted phones or emulators can miss fraudsters operating on seemingly normal devices that have been compromised earlier in the chain. Even bot specific solutions can create blind spots when they work alone.
Once a credential stuffing campaign ends and attackers pivot to manual logins with the same stolen credentials, pure bot tools see only “human” traffic and approve it. The result is a pattern where high risk users are blocked while determined adversaries adapt and slip through.
Multi-Signal Correlation in Practice
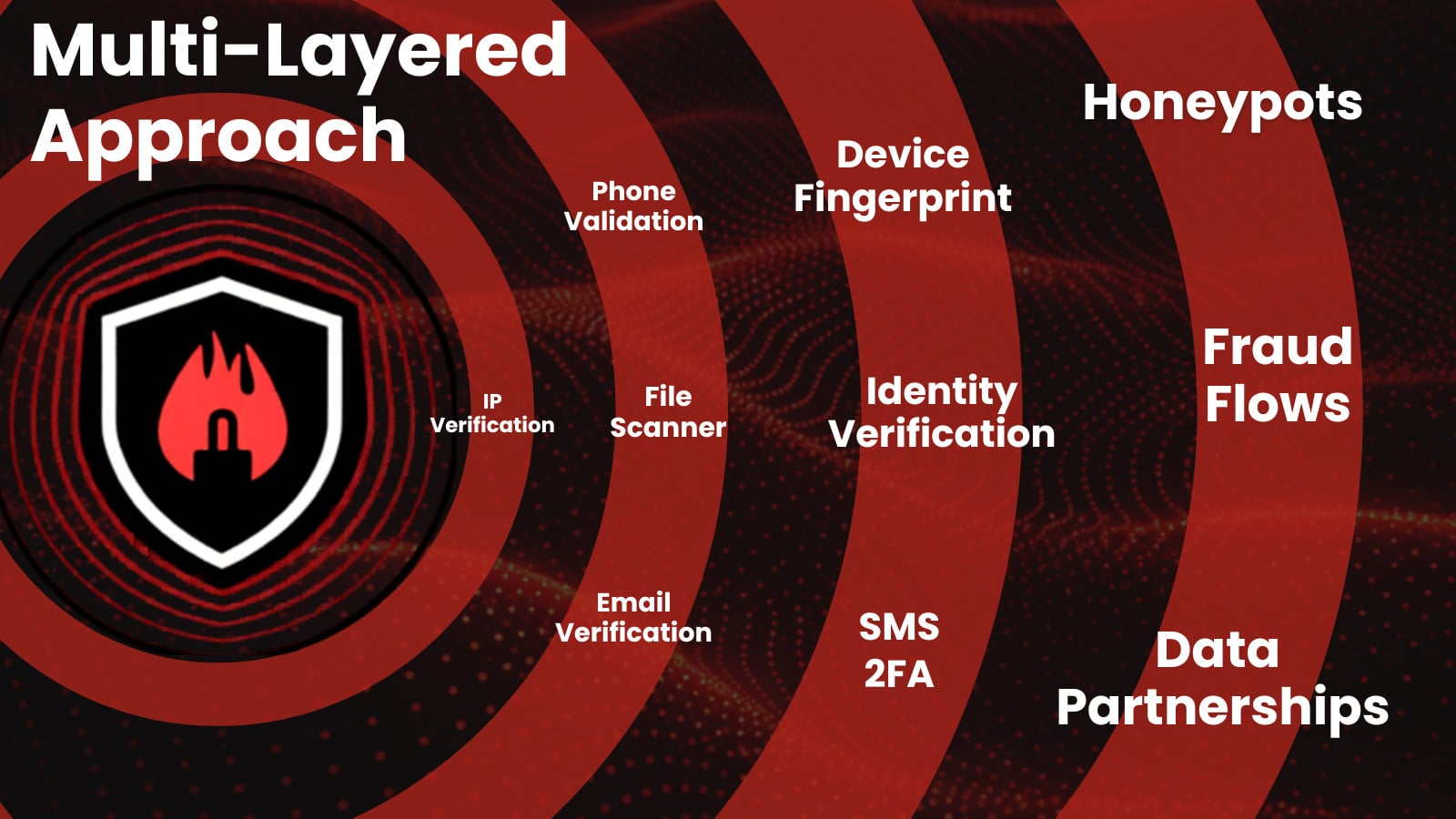
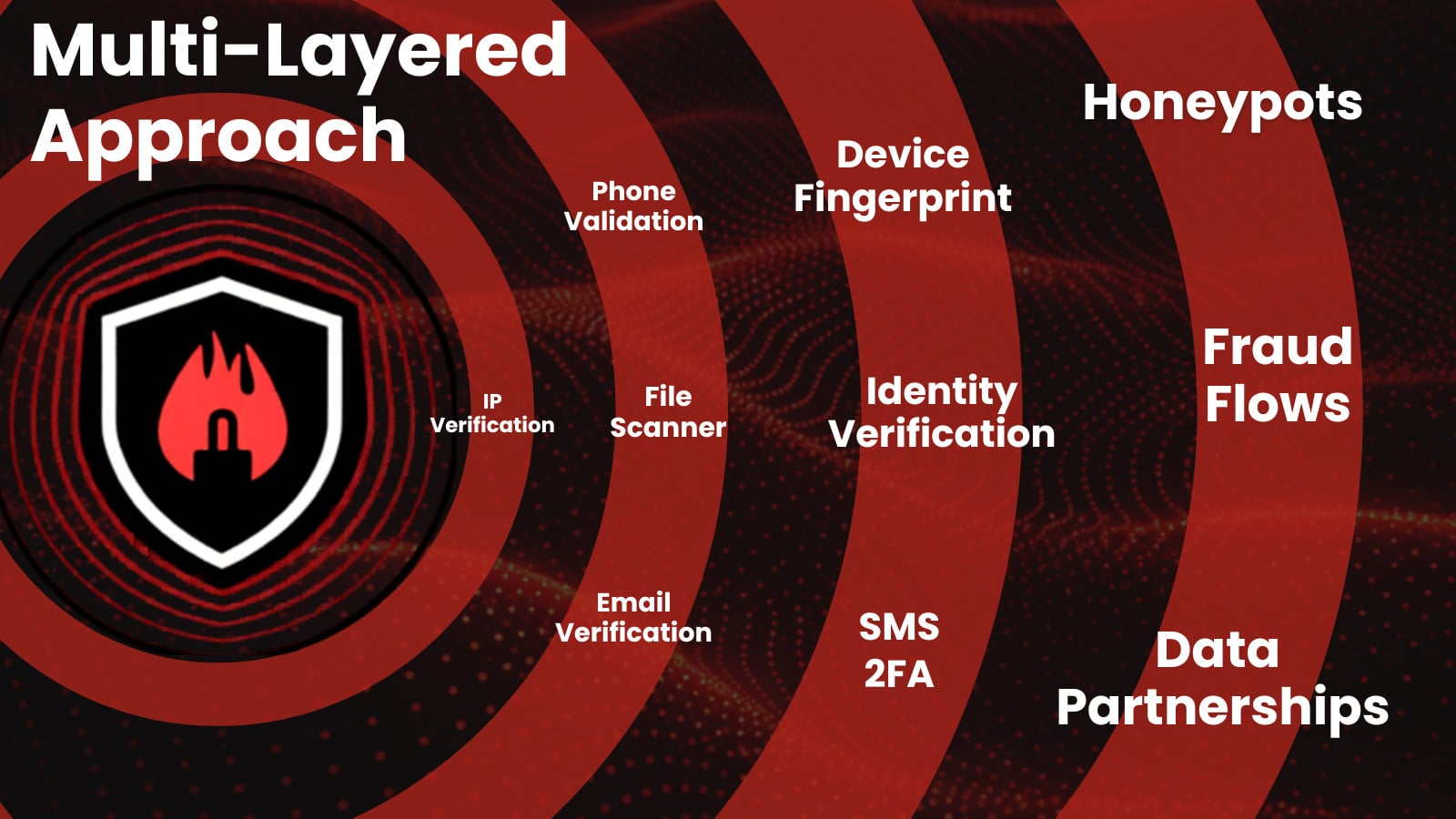
Effective fraud defense comes from correlating IP, identity, device, and behavioral signals at every step of the journey instead of evaluating each one in isolation.
An IP that looks slightly suspicious on its own becomes clearly abusive when tied to dozens of new accounts on the same device fingerprint and similar behavioral patterns during the first session.
Likewise, a user with an apparently normal device and clean email reputation can still be high-risk if login behavior reflects credential stuffing patterns or access follows known malware distribution campaigns.
Modern decision engines improve accuracy by weighing hundreds or thousands of data points together rather than enforcing rigid rules on a single attribute.
For organizations, that means unifying what were once separate views. IP intelligence, device fingerprinting, identity verification, and behavioral analytics should feed the same risk model so that each event is scored in context, not as a disconnected log line.
This multi signal approach is the most reliable way to raise the bar for attackers while reducing friction for genuine customers.
Prevent chargebacks. Stop account takeover. Recover revenue.
Leading enterprises use IPQS data to power their fraud prevention strategies, don’t leave yourself vulnerable. Seamlessly integrate with our APIs to reduce friction, prevent more fraud, and secure your business.
Free Sign Up
Case Study: Stopping Coordinated Signup Abuse
Consider a self service SaaS platform that offers a generous free tier and trials. As the product grows, abuse appears in the form of thousands of signups used to scrape data, test stolen cards, or resell access under the radar.
Early countermeasures rely on blocking certain IP ranges and obvious disposable email domains, but this only dents the problem and begins to impact small teams and freelancers on shared networks.
By shifting to a multi-signal model, the platform starts scoring signups across IP, device, identity, and behavior together.
New accounts that reuse the same device fingerprint with different emails, come from IPs recently seen in automated traffic, or immediately exhibit scripted behavior are grouped into coordinated abuse clusters instead of being evaluated one by one.
This lets the team apply precise responses, such as challenging only high risk clusters with additional verification or silently limiting their capabilities while letting low risk signups proceed without friction.
Over time, feedback from confirmed abuse and confirmed good users trains the scoring model, driving down false positives while pushing organized attackers to spend more effort for less return.
Outpacing Fraud Trends
Attackers are no longer tied to a single tool or weak point in your stack. They combine proxies, bots, synthetic identities, leaked credentials, and malware infrastructure across multiple stages, which means that single signal defenses will always lag behind.
To keep pace, fraud teams need correlation across IP, identity, device, and behavior in one coherent risk view rather than a collection of disconnected checks.
From here, the conversation shifts to how to operationalize that unified model, integrate it into existing workflows, and measure its impact on both loss reduction and customer experience.
Book a free consultation with a fraud expert today!
About IPQS
IPQS is a founder-led, self-funded company built on a simple principle: fraud prevention should be driven by real intelligence and a multi-layered approach. From day one, we’ve focused on owning the full lifecycle of our technology—developing and maintaining our own global data network, honeypots, and fraud intelligence specialists. This approach gives our customers a distinct advantage: faster insights, greater accuracy, and complete transparency into how decisions are made. By staying independent, we prioritize long-term innovation over short-term gains, continuously evolving our platform to stop fraud before it starts.
Sponsored and written by IPQS.





































































You must be logged in to post a comment Login