Microsoft last week took Agent 365, its management platform for AI agents, out of preview and into general availability — a move that signals the software giant believes the governance challenge around autonomous AI is no longer theoretical but operational and urgent.
The product, first announced at Microsoft’s Ignite conference in November, positions itself as a unified control plane that lets enterprise IT and security teams observe, govern, and secure AI agents wherever they run: inside Microsoft’s own ecosystem, on third-party cloud platforms like AWS Bedrock and Google Cloud, on employee endpoints, and increasingly across a sprawling ecosystem of SaaS agents built by partner software companies.
But the most striking element of the launch isn’t the general availability milestone itself. It’s Microsoft’s aggressive push into discovering and managing local AI agents — the coding assistants, personal productivity tools, and autonomous workflows that employees are installing on their own devices, often without IT’s knowledge or blessing. Microsoft calls this phenomenon “shadow AI,” and it is an entirely new category of enterprise security risk that most organizations are only beginning to grapple with.
“Most enterprises are trying to figure out how to harness the potential of autonomous agents,” David Weston, Corporate Vice President of AI Security at Microsoft, told VentureBeat in an exclusive interview. “They’re trying to find a balance between what we call YOLO — just let anything run — and ‘oh no,’ where nothing works at all.”
Why Microsoft says rogue AI agents are already a security crisis inside the enterprise
The timing of Agent 365’s general availability reflects an uncomfortable reality: AI agents have already outpaced the governance infrastructure designed to manage them. Enterprises that spent years building controls for cloud applications and SaaS software now face a fundamentally different kind of sprawl — one where autonomous software can invoke tools, access sensitive data, chain together with other agents, and take actions on behalf of users or entirely on their own.
Weston described three specific categories of security incidents that Microsoft is already observing across its enterprise customer base. The first, and most common, involves developers rushing to connect agents to backend systems and inadvertently exposing sensitive infrastructure. “A canonical thing we’re seeing a lot across the board is these MCP servers that are then being connected to a sensitive back end system and then exposed unauthenticated to the internet,” Weston said. “That can lead to PII or data leaks.”
The second category involves what security researchers call cross-prompt injection — attackers embedding malicious instructions in data sources like software tickets, websites, or wikis that an agent is likely to ingest. “We are seeing attackers use untrusted data sources to put in what we call cross-prompt injection prompts, which will basically direct your agent to do whatever the attacker wants,” Weston explained. While he noted this attack vector remains less common, “when we do see it, it’s higher impact.”
The third and perhaps most pervasive issue is more mundane but no less dangerous: agents connected to data sources and DLP systems that simply aren’t designed to understand agentic access patterns. “Data sources and DLP systems that are not agent-aware are exposing high-sensitive data down to maybe a vendor,” Weston said, adding that such incidents carry “a lot of costs and a lot of risk.”
Inside Agent 365, the $15-per-user control plane for governing AI agents at scale
At its core, Agent 365 functions as a centralized registry and policy engine for AI agents. It provides IT administrators with a single view of every agent operating within their environment — whether that agent was built with Microsoft Copilot Studio, deployed on AWS Bedrock, running as a SaaS integration from a partner like Zendesk or SAP, or installed locally on a developer’s Windows machine.
The platform supports three distinct categories of agents, each with different availability status at launch. Agents working on behalf of users through delegated access — such as an inbox organizer operating with a user’s permissions — are now generally available within the control plane. Agents operating behind the scenes with their own access credentials, like an autonomous system triaging support tickets, are also generally available. A third category, agents participating in team workflows with their own access, enters public preview today.
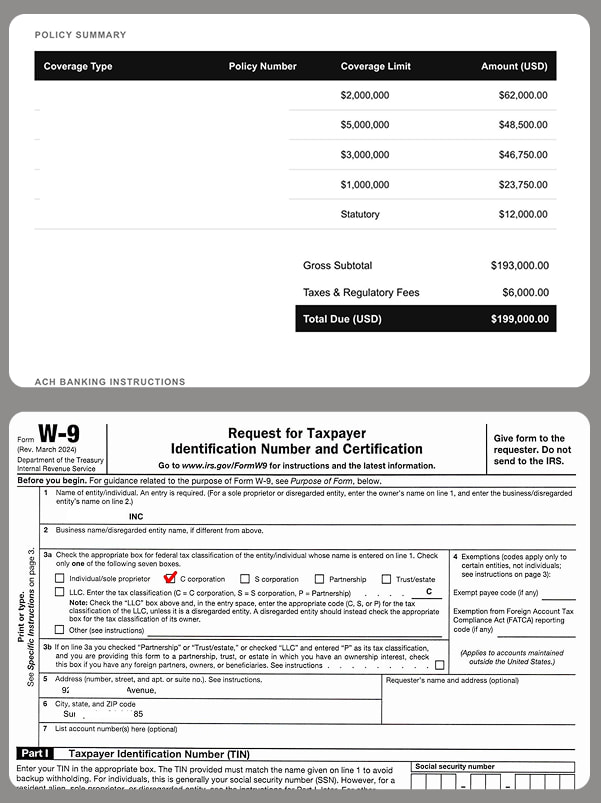
Agent 365 is available as part of the new Microsoft 365 E7 suite or as a standalone product priced at $15 per user per month. Each license covers an individual who manages, sponsors, or uses agents to work on their behalf. The pricing model is designed to scale predictably: organizations pay per person who interacts with the agent ecosystem, not per agent — a structure that acknowledges the reality that agent counts are a moving target in most enterprises.
How Microsoft hunts for unauthorized AI tools hiding on employee laptops
Perhaps the most significant new capability in today’s launch is Agent 365’s ability to discover and manage local AI agents — the tools that developers and knowledge workers are installing directly on their Windows devices, often without any oversight from IT.
Starting today, organizations enrolled in Microsoft’s Frontier program can use Agent 365, powered by Microsoft Defender and Intune, to detect OpenClaw agents running on managed Windows devices. Administrators can view which devices are running OpenClaw, and they can apply Intune policies to block common execution methods. A new “Shadow AI” page in the Microsoft 365 admin center serves as the central dashboard for this discovery process.
The choice to begin with OpenClaw was deliberate. “Our criteria is simply customer demand,” Weston told VentureBeat. “We’re hearing across the board that enterprises understand OpenClaw represents a new type of software. They want to be on the frontier, they want to leverage all the benefits, but they also want the deterministic control that lets them establish a clear boundary in their enterprise.”
Microsoft plans to expand local agent discovery to 18 different agent types by June 2026, including GitHub Copilot CLI and Claude Code. The company is leveraging its existing endpoint telemetry to identify applications calling inference endpoints, then surfacing that information to IT and security teams. “Using our visibility on the endpoint, we can see the variety of apps that are basically calling inference endpoints,” Weston explained. “And then we can give a collection of that to the IT and security folks, and they can decide whether that’s appropriate or something that’s putting them at risk.”
Microsoft Defender maps the ‘blast radius’ when an AI agent goes wrong
Starting in June, Microsoft Defender will provide what the company calls “asset context mapping” for each discovered agent. This feature builds a relationship graph showing which devices an agent runs on, which MCP servers it connects to, which identities are associated with it, and which cloud resources those identities can reach. The goal is to let security teams assess the potential blast radius if an agent is compromised or misbehaves.
Weston explained the technical underpinning: “Blast radius is computed by taking an asset inventory and converting each asset into a node in a graph. The edges represent how different assets or data sources are connected.” The system overlays contextual detail onto each node — for instance, flagging that a particular device runs an untrusted AI agent and is simultaneously connected to a critical business database or a machine with thousands of user accounts.
“It’s highly accurate because it’s computed from an asset graph that’s typically cloud-based, or built from endpoint data if you’ve got something like NDE deployed,” Weston said. “We’re computing it based on what you already have — which is essentially ground truth.” This kind of exposure mapping is precisely what CISOs are asking for, Weston added. “One of the first things you want to know when assessing agent risk is: what is this connected to? Is it connected to something I care about, or is it something moderate?”
The platform doesn’t stop at visibility. Agent 365 introduces policy-based controls that let administrators set guardrails for what agents can and cannot do. If a managed agent exhibits malicious behavior patterns — such as attempting to access or exfiltrate sensitive data — Microsoft Defender can block the agent at runtime and generate alerts with rich incident context for investigation. Weston emphasized that Defender’s existing classification capabilities translate directly to the agentic world. “Injecting code into the process that manages logins, whether you’re OpenClaw or browser, that’s always going to be a strong signal,” he said. Context mapping, policy-based controls, and runtime blocking will enter public preview through Intune and Defender in June 2026.
Agent 365 reaches into AWS and Google Cloud to govern agents across rival platforms
In a notable competitive move, Microsoft is extending Agent 365’s governance reach to rival cloud platforms. A new public preview of Agent 365 registry sync enables IT teams to connect with AWS Bedrock and Google Cloud (specifically, Google Gemini Enterprise Agent Platform, formerly Google Vertex AI). Through these connections, administrators can automatically discover and inventory agents running on those platforms and perform basic lifecycle governance actions such as starting, stopping, or deleting agents.
“If we’re going to be a single control plane, we have to meet customers where they are, and many of them are multi-cloud,” Weston told VentureBeat. He acknowledged that the depth of available controls varies somewhat by cloud provider. “Once you know it’s there, what kind of guardrails or blocking can you provide? And that’s going to be slightly different depending on what the cloud provider works with.” But he added that the platforms offer “pretty comparable capabilities” in most scenarios and expressed optimism that cross-cloud consistency will improve over time.
Also generally available today: Agent 365 extends Microsoft Entra network controls to cover agent traffic from Microsoft Copilot Studio agents and local agents like OpenClaw. These controls let security teams inspect agent network activity, identify unsanctioned AI usage, restrict connections to approved web destinations, filter risky file transfers, and help block malicious prompt-based attacks at the network layer before they result in harmful actions. The combination of cloud registry sync and network-layer enforcement gives Microsoft an unusually broad governance surface — one that spans cloud, endpoint, and network in a way few competitors currently match.
Windows 365 for Agents gives enterprises a sandbox for high-risk AI workloads
For organizations that want the productivity benefits of autonomous agents but aren’t comfortable running them directly on employee endpoints, Microsoft is also launching Windows 365 for Agents in public preview, currently limited to the United States. The offering creates a new class of Cloud PCs purpose-built for agentic workloads, managed through Intune, and governed by the same identity and security controls applied to human employees.
Weston framed the capability as a segmentation play. “From a security principle standpoint, the more segmentation you can achieve, the better,” he said. “If you don’t want this on your endpoint, but you still want the capability, you can choose to have it sandboxed, isolated. We’ve seen large companies like Nvidia talk about doing this. We’re creating this pattern for everyone.”
How critical that isolation is, Weston added, depends on context. “If you’re working in a military installation, it goes without saying, you probably want to segment away that information. If you’re working in a company that’s primarily creative and you have a little higher risk tolerance, you may not want to do that.” The public preview requires an Agent 365 license, an Intune license, and an active Azure subscription.
Microsoft builds a broad partner network to manage the agentic AI ecosystem
Microsoft is positioning Agent 365 not as a walled garden but as an open management layer. The company announced that ecosystem partner agents from Genspark, Zensai, Egnyte, Zendesk, and agents built on platforms including Kasisto, Kore.ai, and n8n are now fully enabled for management through Agent 365 — with no integration work required from IT teams. Additional software development company launch partners include Adobe, SAP, Manus, Nvidia, and Celonis.
For partner-built SaaS agents, onboarding begins with identity. “We have the ability for you to simply give it an identity and or use our SDK depending on the level of capability you need,” Weston explained. “Just starting with the identity, we’re able to basically see, especially for Entra users, what capabilities the application needs and what constraints should be put on that.” Deeper SDK integration provides richer observability data, but identity alone gives the platform substantial governance leverage.
On the services side, Microsoft has enlisted firms including Accenture, KPMG, Capgemini, Protiviti, Slalom, and nearly two dozen others as Agent 365 Launch Partners. These firms have collaborated with Microsoft engineering to build offerings around inventory assessment, least-privilege enforcement, compliance, multi-platform threat analysis, and ongoing lifecycle management.
Microsoft’s bigger bet: agents are the new apps, and they need the same enterprise controls
Microsoft’s bet with Agent 365 arrives at a moment when the enterprise software industry is racing to define what the “agentic era” actually looks like in production. Competitors including Google, Amazon, and Salesforce are all developing their own agent orchestration and governance tools, but Microsoft’s approach — leveraging its deeply entrenched position in endpoint management (Intune), threat detection (Defender), identity (Entra), and productivity (Microsoft 365) — gives it an unusual cross-surface advantage.
For enterprises considering Agent 365, Weston outlined a phased adoption model. “First things first, they’ll get visibility and an inventory — you can’t really secure what you don’t know about,” he said. “The next thing they’re able to do is assign identities and start to manage the access those agents have, which is a huge first step in managing the risk.” The deeper capabilities — isolation through Windows 365 for Agents, runtime blocking, blast radius mapping — come next. “Crawl is inventory. Walk is getting identity and access. Run is getting isolation, better control, deeper visibility,” Weston summarized. “I think that’s something that’s reasonable in a 90-day period.”
Whether enterprises actually move that fast will depend on the maturity of their existing security infrastructure and the pace at which shadow AI proliferates within their walls. A live “Ask Microsoft Anything” session on Agent 365 is scheduled for May 12, giving IT and security professionals a chance to press the engineering team on specifics.
But the most telling detail from the interview may have been the most offhand. “I have 18 agents running behind my team chat right now,” Weston said. If even Microsoft’s own security chief has a small army of autonomous agents operating in his daily workflow, the question for every other enterprise is no longer whether to govern the agentic workforce — it’s whether they can do it before the workforce governs itself.
































































You must be logged in to post a comment Login