Crypto World
Lazarus-linked macOS malware targets crypto and fintech sectors

Security researchers have linked a fresh macOS malware campaign to the Lazarus Group, the North Korea-linked hacking outfit responsible for some of the crypto sector’s most consequential losses. The campaign, tracked by researchers as the Mach-O Man kit, is deployed through the ClickFix social-engineering framework that targets a broad spectrum of firms, including crypto companies.
According to Mauro Eldritch, an offensive security expert and founder of threat-intelligence outfit BCA Ltd., the Mach-O Man campaign leverages convincing calls to lure victims into executing commands that quietly pull down the malware in the background. The tactic enables attackers to bypass conventional security controls and slip into credentials and broader corporate environments, a pattern documented in a Tuesday report that cites the Any.run macOS analysis sandbox as a primary source of insight.
The operation culminates in a stealer payload designed to harvest a wide range of sensitive data, from browser extension data and stored credentials to cookies and macOS Keychain entries. Once collected, the information is zipped and exfiltrated through Telegram, after which the toolkit performs a self-deletion routine using the system rm command to erase traces without requiring user confirmation.
The emergence of Mach-O Man fits into a broader narrative around Lazarus’ evolving targeting beyond purely crypto-native incidents, underscoring the risk to corporate networks and supply chains alike. The group has long been associated with some of the industry’s largest heists, including the $1.4 billion attack on the Bybit exchange in 2025, cited as the era’s largest cryptocurrency breach to date.
For context, researchers emphasize that Lazarus has continued to widen its toolkit and attack surface in recent months. In April, the group was tied to AI-enabled social-engineering campaigns that breached Zerion by gaining access to team members’ sessions, credentials and private keys. The Zerion incident illustrated how attackers can blend social engineering with credential theft to reach privileged accounts and sensitive assets. Further coverage on that event is available from Cointelegraph.
Key takeaways
- Mach-O Man, a macOS malware kit attributed to Lazarus by researchers, is distributed via ClickFix social-engineering campaigns that reach traditional businesses and crypto firms alike.
- The final payload acts as a stealer, extracting browser data, credentials, cookies and macOS Keychain entries, with data zipped and exfiltrated through Telegram before the kit self-destructs using rm to erase traces.
- Victims are lured into fake Zoom or Google Meet calls, where they are prompted to run commands that trigger malware installation and deeper access, bypassing typical endpoint protections.
- The Lazarus operation continues to broaden its target scope beyond crypto-native companies, aligning with broader industry observations of the group’s expanding playbook and infrastructure access.
- Contextual benchmarks include the Bybit hack in 2025 and the Zerion breach in April, illustrating a pattern of high-stakes intrusions that blend phishing, social engineering and credential theft.
Mach-O Man: unraveling the attack sequence
At the core of the Mach-O Man campaign is a staged social-engineering flow centered on convincing calendar invites for popular virtual-meeting platforms. Victims receive a prompt that resembles a legitimate meeting notification, prompting them to join a so-called “Zoom” or “Google Meet” session. In the guise of a routine setup, victims are then steered to execute commands that quietly download and install the Mach-O Man components in the background. This stealthy delivery pathway helps attackers sidestep many traditional controls and allows credential harvesting to proceed with limited user friction.
Once the stealer is deployed, the toolkit targets data of high value to attackers. It raids browser extension data, stored credentials, cookies and Keychain entries, among other sensitive locally stored information. The extracted material is packaged into a zip archive and sent to the operators via Telegram, a channel chosen for its speed and relative resilience against standard enforcement actions. Following data exfiltration, the malware deploys a self-deletion routine, removing the entire kit from the host using the rm command—effectively leaving minimal traces and complicating post-incident forensics.
Context and implications for the crypto security landscape
The Lazarus Group’s alleged involvement in Mach-O Man extends a well-documented pattern of sophisticated, long-running campaigns that intensify the risk profile for crypto firms and their ecosystems. The group has become a persistent thorn in the side of exchanges, wallet providers and project teams, with past operations demonstrating a capacity to scale beyond traditional targets and adapt to evolving defense postures.
Bybit’s stunning $1.4 billion breach in 2025 stands as a benchmark for the scale of Lazarus-driven intrusions, underscoring not only the capital at risk but the potential for cascading effects across liquidity, market making and user trust. In parallel, the Zerion incident in April showcased how AI-augmented social engineering can accelerate the theft of credentials and private keys by exploiting legitimate team workflows and authorized sessions. The combination of social engineering with credential access remains among the most challenging vectors for defenders to preempt, particularly on macOS environments where threat actors have previously found gaps in application controls and user vigilance. Related reporting on Lazarus-linked activity continues to surface across industry coverage.
Defensive lessons and what to watch next
Mach-O Man reinforces the need for macOS-specific defense postures that blend user-education, application-control policies and robust-measurement of endpoint behavior. Key mitigations include enforcing least-privilege execution, deploying application allowlists, monitoring for anomalous download-and-execute sequences triggered from trusted apps, and tightening the wing of endpoint detection to catch command-and-control-like behaviors associated with staged infection chains. Given that the exfiltration route leverages Telegram, security teams should review outbound intelligence on uncommon channels used for data transfer and consider network-level constraints that challenge rapid egress of sensitive information.
For practitioners, the takeaway is clear: even as crypto-specific threats remain high-profile, attackers are expanding their targeting to encompass traditional businesses and cross-sector networks. This broadening of Lazarus’ reach increases the potential attack surface for exchanges, custodians and infrastructure providers alike, reinforcing the case for comprehensive, cross-platform threat intelligence integration and rapid response playbooks that can pivot as new malware kits surface. Any.run analysis provides a technical backdrop for understanding the Mach-O Man kit’s behavior and evolution.
As the industry absorbs these developments, observers will be watching for how defenders adapt to macOS-focused campaigns and whether new variants of Mach-O Man emerge with enhanced evasion techniques or more aggressive data-collection capabilities. The convergence of social engineering, credential theft and automated self-deletion marks a troubling trend—one that demands renewed emphasis on user education, secure access controls and vigilant incident-response strategies.
Readers should keep an eye on any updates about Lazarus’ tactics across platforms, especially as security teams track potential shifts in the group’s tooling, command channels and preferred data-exfiltration methods. The coming weeks may reveal whether Mach-O Man is a standalone spike or part of a broader, ongoing shift in the threat landscape facing the crypto ecosystem.
Crypto World
DOJ Charges SPLC With Fraud


The US Department of Justice has filed fraud charges against the Southern Poverty Law Center, alleging the civil rights organization made secret payments to extremist informants without proper disclosure.
Summary
- The DOJ charged the SPLC with fraud, alleging undisclosed payments were made to informants embedded in extremist groups.
- The charges represent one of the most significant legal actions ever taken against a major US civil rights organization.
- The SPLC has not yet issued a detailed public response to the allegations.
The US Department of Justice announced a federal indictment against the Southern Poverty Law Center on April 21, with acting Attorney General Todd Blanche alleging the group had been paying informants embedded inside white supremacist and other extremist organizations while concealing those payments from donors. The indictment, returned by a grand jury in Alabama, includes six counts of wire fraud, four counts of making false statements to a federally insured bank, and one count of conspiracy to commit money laundering.
DOJ SPLC Fraud Charges Shake the Civil Rights World
According to prosecutors, the SPLC secretly paid leaders and organizers of groups including the Ku Klux Klan, the Aryan Nation, and the National Alliance, using shell accounts under fictitious names to funnel the money and avoid detection. NPR reported that one informant who was a member of the neo-Nazi National Alliance received more than $1 million in payments between 2014 and 2023, while another allegedly helped coordinate transportation to the deadly 2017 Unite the Right rally in Charlottesville and was paid approximately $270,000. “As the indictment describes, the SPLC was not dismantling these groups. It was instead manufacturing the extremism it purports to oppose by paying sources to stoke racial hatred,” Blanche said at a press conference announcing the charges.
What the Charges Allege
The DOJ alleges the SPLC used funds in ways inconsistent with its stated nonprofit mission and that the organization failed to maintain adequate records of payments made to informants, according to NBC News which covered the charges in detail. Prosecutors have not specified the total amount allegedly involved, but the case centers on a pattern of payments rather than a single transaction. The SPLC has disputed elements of the government’s account but has not issued a comprehensive public defense as of the time of publication.
Broader Implications for Nonprofits and Civil Rights Groups
The charges are being closely watched across the nonprofit sector, where organizations that engage in undercover monitoring of extremist groups often walk a legal and ethical line in how they fund and manage informants. NPR reported that the case could set a precedent for how civil rights organizations document and disclose intelligence-gathering activities going forward. For the SPLC, which has an endowment of several hundred million dollars and significant political influence, the legal battle ahead carries both financial and reputational stakes.
The DOJ has not indicated whether additional individuals within the SPLC’s leadership structure face charges, but the investigation is described as ongoing.
Crypto World
ABTC Energizes More Than 11,000 New Bitcoin Mining Rigs

American Bitcoin (ABTC), a publicly traded mining company co-founded by United States President Donald Trump’s sons, has completed its energization of 11,298 application-specific integrated circuits (ASICs) at its Drumheller site in Alberta, Canada.
Following the acquisition of machines, the company now owns about 89,242 ASICs, the computers used to mine Bitcoin (BTC) and other proof-of-work (PoW) cryptocurrencies, according to the company’s announcement on Wednesday.
ABTC’s mining fleet now generates a total of about 28.1 exahashes per second (EH/s) of computing power, operating at an “average efficiency” of 16 joules per terahash, the company said.
Shares of ABTC surged by about 11.7% on Wednesday, rising to about $1.38 per share, according to data from Yahoo Finance.

The announcement followed a tough business quarter for the company, which posted a loss of $59.5 million in the fourth quarter of 2025, as the mining industry grapples with multiple economic challenges that are chipping away at revenue.
Related: Aluminum giant Alcoa to sell dormant smelter to Bitcoin miner NYDIG: Report
ABTC struggles amid challenging business environment for miners
Mining companies are grappling with reduced block rewards since the April 2024 halving, rising energy costs, and declining crypto prices from the ongoing crypto bear market.
The price of BTC declined by over 50%, reaching a low of about $60,000 in February, when ABTC filed its Q4 results with the United States Securities and Exchange Commission (SEC).
ABTC attributed its Q4 losses to a $227.1 million decline in the fair value of its BTC holdings as a result of the crash, but said it was able to “mine BTC at a 53% discount” to prices on the spot market.

Public BTC mining companies sold more BTC in the first three months of 2026 than all of 2025.
Mining companies MARA, CleanSpark, Riot, Cango, Core Scientific and Bitdeer collectively sold about 32,000 BTC in Q1, according to TheEnergyMag.
Sales in the period topped the previous record of 20,000 BTC sold by public mining companies during Q2 2022.
Magazine: AI may already use more power than Bitcoin — and it threatens Bitcoin mining
Crypto World
MemeCore ($M) Pumps 20% Today. Why Is This Meme Coin Still Rallying?

MemeCore (M) surged 20.77% on April 21, 2026, trading near $4.28 and extending a 30-day rally of roughly 145%. The move lifted the meme coin’s market capitalization above $7 billion.
The daily chart points to sustained momentum, while the hourly timeframe shows a clean retest of the ascending trendline. A March network upgrade and a pending Korean expansion deal help explain the underlying strength.
Daily Chart Shows Parabolic Structure Intact
MemeCore’s daily chart frames a parabolic advance that began in late March. Price sits at $4.28 after climbing 20.77% in the session. The April 18 all-time high of $4.72 remains within striking distance.
The Relative Strength Index (RSI) prints near 80 without showing bearish divergence against recent highs. That combination usually signals buyers remain in control, even though the indicator sits inside overbought territory.
MACD continues to widen in positive territory. The histogram has pushed to its tallest reading of the quarter, and previous selloffs from comparable readings required at least a stall in momentum. No such stall has appeared yet.
Fibonacci retracement levels drawn from the $1.19 low to the $4.72 ATH highlight $3.89 as the 0.236 support. A daily close below that zone would be the first sign the parabolic structure is breaking.
MemeCore Price Prediction Targets $4.61 Breakout
On the hourly timeframe, Bollinger Bands have widened after a brief period of compression. The BBWP (Bollinger Band Width Percentile) printed extreme readings during the latest leg higher.
Wide bands typically signal that volatility is feeding fresh directional momentum rather than mean reversion. The setup often precedes continuation rather than an immediate reversal.
The decisive level overhead is the April 18 swing high at $4.61. That level now acts as the most recent horizontal resistance on the hourly chart.
A four-hour close above $4.61 would open room toward the all-time high at $4.72 and then price discovery. Failure to clear it risks a pullback into the broken trend channel.
Downside risk is defined by the green support band near $2.80, where the ascending trendline was retested earlier this week. Bears need a break of that zone to flip the structure. Bulls only need to hold the current $4.00 handle to keep the setup intact.
Volume on the latest push is healthy, though still below the April 18 spike. That suggests participation is real without reaching euphoria, a detail worth watching if price stalls ahead of a possible reversal.
Why MemeCore Is Still Pumping
Four fundamental drivers help explain the $M rally.
First, altcoin capital rotation is accelerating. The CoinMarketCap Altcoin Season Index has climbed in recent weeks. Meme coins tend to lead once speculative flows return to higher-beta segments of the market.
Second, the pace of the move stands out. A 145% gain over 30 days is hard to attribute to a single catalyst. The tape points to either coordinated accumulation by larger wallets or organic community growth, since typical meme token pumps burn out in a few sessions.
Third, the March 25 MemeCore Hardfork implemented account abstraction. The upgrade cut gas fees from 1,500 gwei to 15 gwei, a 100x reduction. Cheaper transactions make the network more attractive for high-frequency traders and fresh token launches. That shift increases demand for $M as a settlement asset.
Fourth, MemeCore is acquiring a KOSDAQ-listed company to secure a Virtual Asset Service Provider (VASP) license in Korea. Success would enable KRW/M trading pairs and lay the groundwork for a domestic dApp layer. Traders have previously rewarded similar K-play rally stories.
The blend of technical momentum and fundamental catalysts explains why buyers keep stepping in after each shallow dip. The test now is whether $M can close a daily candle above $4.61. A breakout would open the path to a fresh all-time high.
The post MemeCore ($M) Pumps 20% Today. Why Is This Meme Coin Still Rallying? appeared first on BeInCrypto.
Crypto World
Virginia Approves New Congressional Map


Virginia voters have narrowly approved a new congressional map that could shift as many as four House seats from Republican to Democrat, delivering a major boost to the party’s bid to retake the House in the 2026 midterms.
Summary
- Virginia voters approved a redistricting referendum that replaces the state’s bipartisan commission map with one drawn by the Democratic-controlled legislature.
- The new map gives Democrats an advantage in 10 of Virginia’s 11 House districts, up from the six they currently hold.
- Republicans have filed legal challenges that could still block the new map from taking effect before the midterms.
Virginia voters narrowly approved a ballot measure on April 21 authorizing the Democratic-controlled state legislature to replace Virginia’s existing congressional map with one designed to favor Democrats in 10 of the state’s 11 House districts. According to the Associated Press, the “yes” side held a lead of approximately 3 percentage points with an estimated 97% of votes counted.
Virginia Congressional Map Reshapes the 2026 Midterm Battlefield
The new map leaves just one solidly Republican seat out of Virginia’s 11 congressional districts, a dramatic shift from the current arrangement in which Democrats hold six seats and Republicans hold five. NPR reported that Democrats could pick up as many as four seats under the redrawn lines, a gain that would significantly improve the party’s chances of reclaiming the House majority this fall. Virginia Democratic state House Speaker Don Scott said in a statement, “Virginia just changed the trajectory of the 2026 midterms.”
Republicans Challenge the Map in Court
The result does not guarantee the new districts will be used in the 2026 elections. Republicans have filed legal challenges against the referendum, arguing the process used to bypass Virginia’s bipartisan redistricting commission was procedurally flawed. NBC News reported that the Virginia Supreme Court declined to block the special election from proceeding, but reserved the right to rule on the legal questions after the vote, leaving the map’s ultimate status in litigation. Virginia House Republican Leader Terry Kilgore said “serious legal questions remain about both the wording of this referendum and the process used to put it before voters.”
The Wider Redistricting Battle Behind the Vote
The Virginia result is the latest move in a national redistricting fight that accelerated last year when President Trump urged Republican-controlled states including Texas, Missouri, and North Carolina to redraw their maps for GOP advantage. Democrats responded, successfully pushing new maps in California and now Virginia. Together, analysts say the net effect of the state-by-state redistricting moves may leave the parties roughly even in added seats, though Virginia’s four potential gains represent the most consequential single-state result of the Democratic counter-effort. Whether the new map survives its legal challenges will determine whether Democrats realize those gains before November.
Virginia Governor Abigail Spanberger said the state was committed to returning to its bipartisan redistricting process after the 2030 census.
Crypto World
UK targets illegal P2P crypto trading in nationwide raids

According to Cointelegraph, the United Kingdom’s Financial Conduct Authority (FCA) conducted on-site inspections at eight locations suspected of hosting illegal peer-to-peer crypto trading networks, in coordination with HM Revenue & Customs and the South West Regional Organised Crime Unit. Cease-and-desist notices were issued on-site as investigators gathered evidence for ongoing criminal probes.
The FCA emphasized that unregistered P2P traders operate illegally and can pose significant financial crime risks. In the UK, peer-to-peer trading falls under anti-money laundering rules, and the regulator stated that no P2P traders or platforms are currently registered with the FCA.
Steve Smart, the FCA’s executive director of enforcement and market oversight, described the operation as part of a broader crackdown on unregistered crypto activity, underscoring the financial crime risks associated with these networks.
Key takeaways
- The on-site actions targeted eight premises linked to illegal P2P crypto trading, with cease-and-desist orders issued and evidence collected for ongoing investigations.
- UK law requires AML registration for P2P crypto activity; current FCA records show no registered P2P traders or platforms.
- These raids represent the FCA’s first explicit enforcement operation focused on P2P trading, following prior actions against illegal crypto ATM networks and unlicensed exchanges.
- The incidents unfold amid broader regulatory preparations under the Financial Services and Markets Act (FSMA), with guidance on the forthcoming crypto regime published ahead of a 2027 implementation window and authorization access beginning in September 2026.
- Industry analysis indicates that enforcement against unregistered OTC desks could reshape illicit financial flows and tighten controls around cross-border crypto activity, with broader implications for compliance programs and licensing timelines.
Regulatory crackdown and the FSMA timeline
The eight-location operation sits within a wider UK regulatory trajectory designed to formalize oversight of crypto markets under FSMA. Earlier this year, the FCA opened a consultation on guidance for its upcoming crypto regime, which is slated to take effect in 2027. The framework will cover core areas such as stablecoins, trading venues, custody solutions, and staking services. Firms wishing to operate in the regulated space are expected to begin applying for authorization in September 2026, with full compliance required once the regime is fully implemented.
The forthcoming regime aims to close gaps that previously allowed unregistered activity to persist, particularly in over-the-counter and wholesale segments of the market. As the regulatory perimeter expands, entities that previously operated outside licensing expectations face heightened risk of enforcement, with penalties and corrective actions likely to mirror traditional financial conduct regimes.
Enforcement trajectory and cross-border context
The UK raids are part of a broader international enforcement wave targeting crypto-enabled financial crime. Earlier this month, law enforcement authorities in the UK, the United States, and Canada conducted a coordinated operation—Operation Atlantic—aimed at curbing crypto scam networks. Authorities reported the seizure of millions of dollars in funds and the freezing of assets tied to fraudulent schemes. The operation identified more than 20,000 victims across three countries and secured over $12 million in suspected criminal proceeds, in addition to tracing more than $45 million in stolen crypto linked to fraud networks.
Analysts note that unregistered over-the-counter (OTC) desks have long represented a chokepoint in illicit flows, enabling actors to move funds between crypto and fiat outside the traditional exchange rails. As the FSMA-aligned regime strengthens AML/KYC expectations, such gaps are increasingly unlikely to remain permissive, potentially driving a shift toward more centralized, regulated channels for over-the-counter activity.
Compliance implications for market participants
For crypto firms operating in or targeting the UK market, the enforcement actions underscore the urgency of aligning with evolving regulatory standards. The FCA’s forthcoming rulebook signals a transition toward formal licensing and ongoing supervisory oversight of critical activities, including P2P trading, custody, and staking services. In practice, this means enhanced due diligence, clearer registration obligations, and more rigorous regimes for monitoring suspicious activity, counterparty risk, and cross-border flows.
Industry observers have highlighted the potential implications for OTC desks and other non-exchange channels. Unregistered desks have been implicated in facilitating illicit flows and evading regulatory scrutiny. As the UK moves toward a unified AML framework under FSMA, OTC desks may be required to register, file suspicious activity reports, and adhere to standardized transaction monitoring and KYC practices, aligning with both domestic and international enforcement expectations.
From a policy perspective, these developments intersect with broader market structure considerations. While the EU, under MiCA, emphasizes licensing and operational standards for crypto asset service providers across member states, the UK’s approach follows its own timetable and regulatory architecture. The convergence toward robust oversight—coupled with cross-border enforcement cooperation—has clear implications for licensing strategy, incident response planning, and regulatory reporting for institutions operating in or beyond the UK.
Closing perspective
As the UK advances the FSMA-based regime, enforcement against unregistered OTC desks and P2P networks is likely to intensify. For market participants and risk, compliance, and legal teams, the evolving regulatory landscape underscores the need for solid AML/KYC controls, timely licensing readiness, and proactive engagement with supervising authorities to ensure lawful operation within the new framework.
Crypto World
Fed Nominee Warsh Defends Independence


Kevin Warsh, Donald Trump’s nominee to chair the Federal Reserve, told a Senate confirmation hearing on April 21 that he has made no commitments to the White House on interest rates and would act independently, even as Republican Senator Thom Tillis moved to block a committee vote on his nomination.
Summary
- Kevin Warsh told the Senate Banking Committee he would act as an independent chair and made no promises to Trump on interest rate cuts.
- Republican Senator Thom Tillis has placed a hold on Warsh’s confirmation until the DOJ drops a criminal probe into current Fed Chair Jerome Powell.
- The standoff raises fresh questions about Fed independence at a critical moment for monetary policy and crypto markets.
Kevin Warsh, President Trump’s nominee to lead the Federal Reserve, appeared before the Senate Banking Committee on April 21 and stated clearly that neither the president nor any other political actor had asked him to commit to a specific interest rate policy. “The president never once asked me to commit to any particular interest rate decision, and nor would I agree to it if he had,” Warsh said. “I will be an independent actor if confirmed as chair of the Federal Reserve.”
Federal Reserve Nominee Draws a Clear Line on Rate Independence
Warsh’s testimony was closely watched given that Trump has repeatedly and publicly demanded that the Fed cut interest rates, and has threatened to remove current Chair Jerome Powell for refusing to comply. CNBC reported that Warsh told senators he does not believe Fed independence is meaningfully threatened when elected officials state their views on rates, a position that drew criticism from Democratic senators who argued it underestimates the pressure the White House has applied. Senator Elizabeth Warren called Warsh a “sock puppet” and accused him of shifting his economic positions to align with Trump’s preferences.
Tillis Blocks the Nomination Over Powell Probe
Despite broad Republican support for Warsh, Senator Tillis has announced he will not allow the nomination to advance out of the Banking Committee until the DOJ drops its criminal investigation of Powell, which stems from alleged cost overruns on a renovation of the Fed’s Washington headquarters. NPR reported that Tillis told Warsh at the hearing, “Let’s get rid of this investigation, so I can support your confirmation,” framing his block as a procedural grievance rather than an objection to Warsh personally. The investigation is being led by the US attorney for Washington DC, who has already had a subpoena against Powell blocked in court and has vowed to appeal.
What the Confirmation Battle Means for Crypto Markets
The Federal Reserve chair appointment carries direct implications for digital asset markets, which have shown strong sensitivity to US rate policy throughout the current cycle. Crypto traders have already been pricing in fewer Fed rate cuts in 2026, a shift that analysts say constrains the liquidity conditions that historically fuel crypto bull cycles. Any perception that an incoming chair might face political pressure on rate decisions introduces further uncertainty into an already complex macro environment for digital assets. Powell’s term as Fed chair expires on May 15, and the Tillis block means Warsh’s path to confirmation remains unresolved ahead of that deadline.
Warsh has agreed to divest approximately $100 million in personal assets within 90 days of being sworn in, should the Senate ultimately confirm his nomination.
Crypto World
New York, Illinois Ban Officials From Prediction Markets
New York Governor Kathy Hochul has signed an executive order banning state employees from betting on prediction markets, following a similar move by Illinois earlier this week.
“Getting rich by betting on inside information is corruption, plain and simple,” Hochul said on Wednesday, adding: “Our actions will ensure that public servants work for the people they represent, not their own personal enrichment.”
Hochul also slammed the Trump administration and congressional Republicans for allowing an “ethical Wild West” to take hold around prediction markets without implementing any “meaningful ethical standards” to protect against insider trading.

Adoption in prediction markets is rapidly accelerating, with monthly trading volumes rising over the last seven consecutive months to an all-time high of $23.6 billion in March, with markets covering everything from sports and elections to financial results and cultural outcomes.
However, the rise has been accompanied by increasing concerns about insider trading and market manipulation.
Illinois Governor JB Pritzker also signed an EO banning state employees from betting on prediction markets on Tuesday, stating:
“Illinois is doubling down on its commitment to a transparent and ethical government by bolstering its current state laws to prevent insider trading amid the rapid growth of online prediction markets and event-based gambling contracts.”
Insider trading accusations in prediction markets
Hochul’s EO made reference to several suspected insider trading instances involving US military action.
One of them was a Polymarket trader who placed a low-odds bet that Nicolás Maduro would be ousted as Venezuelan president just hours before he was captured by US forces, profiting around $400,000.
Another related to suspicious trades placed on the invasion of Iran and the death of its Supreme Leader, Ayatollah Khamenei, in late February.
Hochul’s EO stated that any violation may result in dismissal and law enforcement action, and also noted that New York state employees and officers cannot assist others in profiting on confidential information through prediction markets.
Prediction markets, meanwhile, have been fighting potential insider traders their own way.
In February, Kalshi said it banned a former contender for governor of California after he had bet $200 on his own candidacy last year.
Kalshi did not name the politician. However, details in the enforcement summary align with public posts by Kyle Langford, a former Republican turned Democrat who is now running for election to the US House representing California’s 26th Congressional District.
Related: Charles Schwab, Citadel Securities are eying prediction markets
Kalshi faces regulators in Nevada and New York
The latest EO adds to a wave of action from US states to attempt to police prediction markets.
The New York State Gaming Commission sent prediction market platform Kalshi a cease-and-desist letter in October for illegally operating an unlicensed mobile sports wagering platform in the state.
Kalshi is also engaged in a court battle with the Nevada Gaming Control Board after a lower court temporarily blocked Kalshi from operating in the state, with the regulator arguing that Kalshi’s contracts facilitate unlicensed gambling.
Coinbase chief legal officer Paul Grewal has predicted that the case could reach the US Supreme Court, potentially creating precedent over the regulatory treatment of prediction markets and event-based derivatives.
Magazine: How to fix suspected insider trading on Polymarket and Kalshi
Crypto World
Solana Price Prediction: Can SOL Reach $600 After $1 Trillion Q1 and the Alpenglow Upgrade?
The Solana price prediction has turned sharply bullish after SOL climbed 3.4% this week to $88.40, backed by the network clearing more than $1 trillion of on-chain economic volume in Q1 2026 and pulling in 4,100 new developers to lift its developer share to 23% while Ethereum’s share slipped, per CoinGecko and AMBCrypto.
Bitcoin at $79,200 and institutional capital rotating into blue chips set the macro, but the sharpest upside every cycle sits with one early position held before the exchange debut. Pepeto’s presale now sits above $9.29 million raised with the Binance listing already scheduled, and the window between entry and debut is where the real math lives.
Solana recorded $1.1 trillion in Q1 economic activity and 25.3 billion on-chain transactions, outpacing Ethereum for a fifth straight week on dApp revenue. The network added 4,100 new developers in the quarter while ETH’s share declined, and SOL ETFs have crossed $1 billion in combined AUM across Bitwise, VanEck, Fidelity, Grayscale, and others.
Alpenglow is set to slash finality from 12 seconds to under 150 milliseconds. Standard Chartered has flagged a year-end target of $140 to $180 and a $2,000 reading by 2030. A move from $88.40 to $600 is a 7x trip, and even the bull case requires quarters of compounding, while presale pricing opens the door to that return in a single listing event.
Solana, Bitcoin, Pepeto, and the Solana Price Prediction Path to $600
Pepeto Presale at $9.29M Shows Why Capital Is Rotating Before the Binance Open
Most losses this cycle arrive through one mechanism. A fresh token passes the eye test, the swap confirms, and the wallet empties in the next block. Pepeto’s AI contract scanner reads every line of code before a transfer clears and delivers a clear verdict in seconds. The SolidProof audit cleared every Pepeto contract before the presale opened.
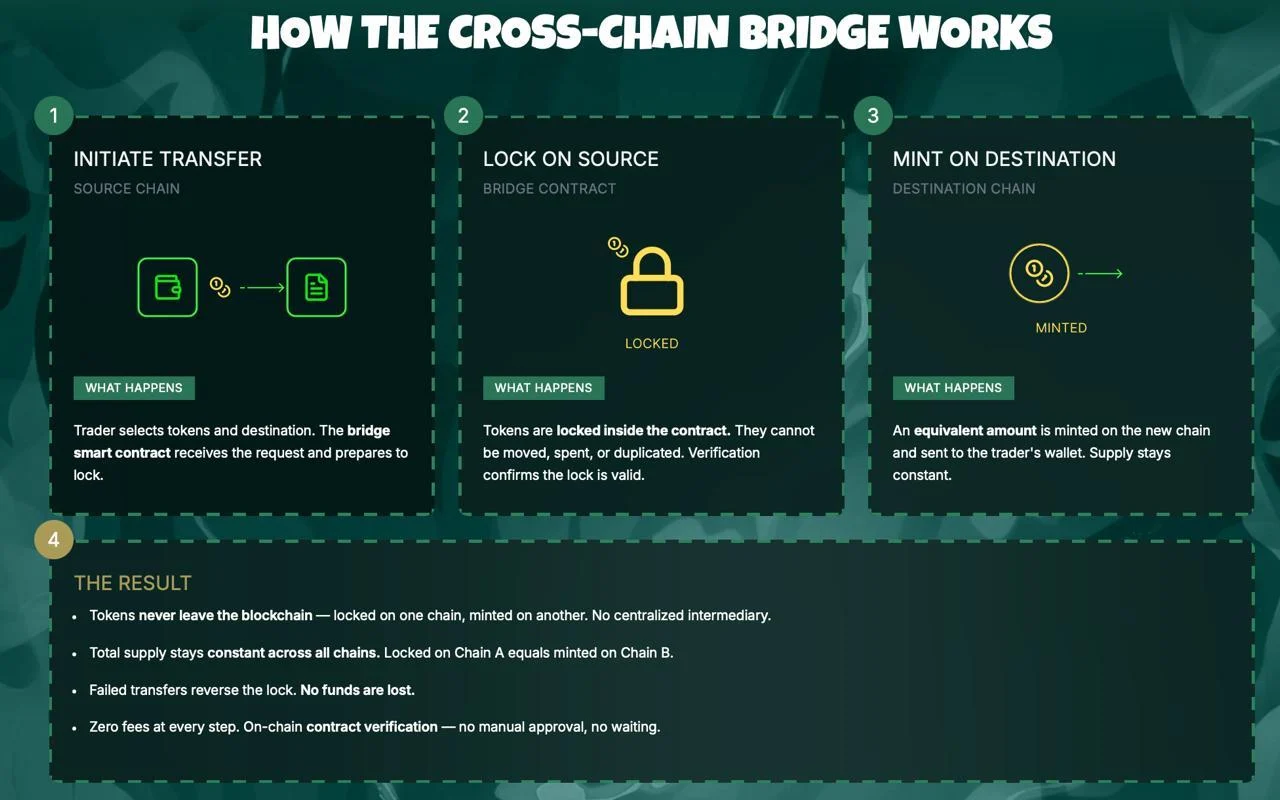
PepetoSwap processes each trade at zero cost across Solana, Ethereum, and BNB Chain, and the bridge carries capital between those networks with no gas charge. Whatever value enters the swap is the exact value that lands on the far side.
The presale has crossed $9.29 million at $0.0000001865 with staking paying 179% APY, pulling circulating supply out of reach before the Binance open. The creator behind the original Pepe run heads Pepeto directly, with a former Binance executive running technical delivery.
That same cofounder built an eleven-figure valuation on a 420 trillion supply with no shipped products. Pepeto is opening its debut with three live tools, audited contracts, a CoinMarketCap preview page confirmed, and the Binance listing on the calendar.
Solana (SOL) Price at $88.40 as $1 Trillion Q1 Volume and Alpenglow Set the $600 Case
Solana trades at $88.40 on April 21 with 24-hour volume climbing 29.5% to $4 billion, per CoinMarketCap. The Solana price prediction rests on four converging catalysts: Alpenglow finality dropping to 150 milliseconds, SOL ETFs crossing $1 billion in AUM, developer share rising to 23%, and Kamino PRIME closing in on $600 million in RWA lending.
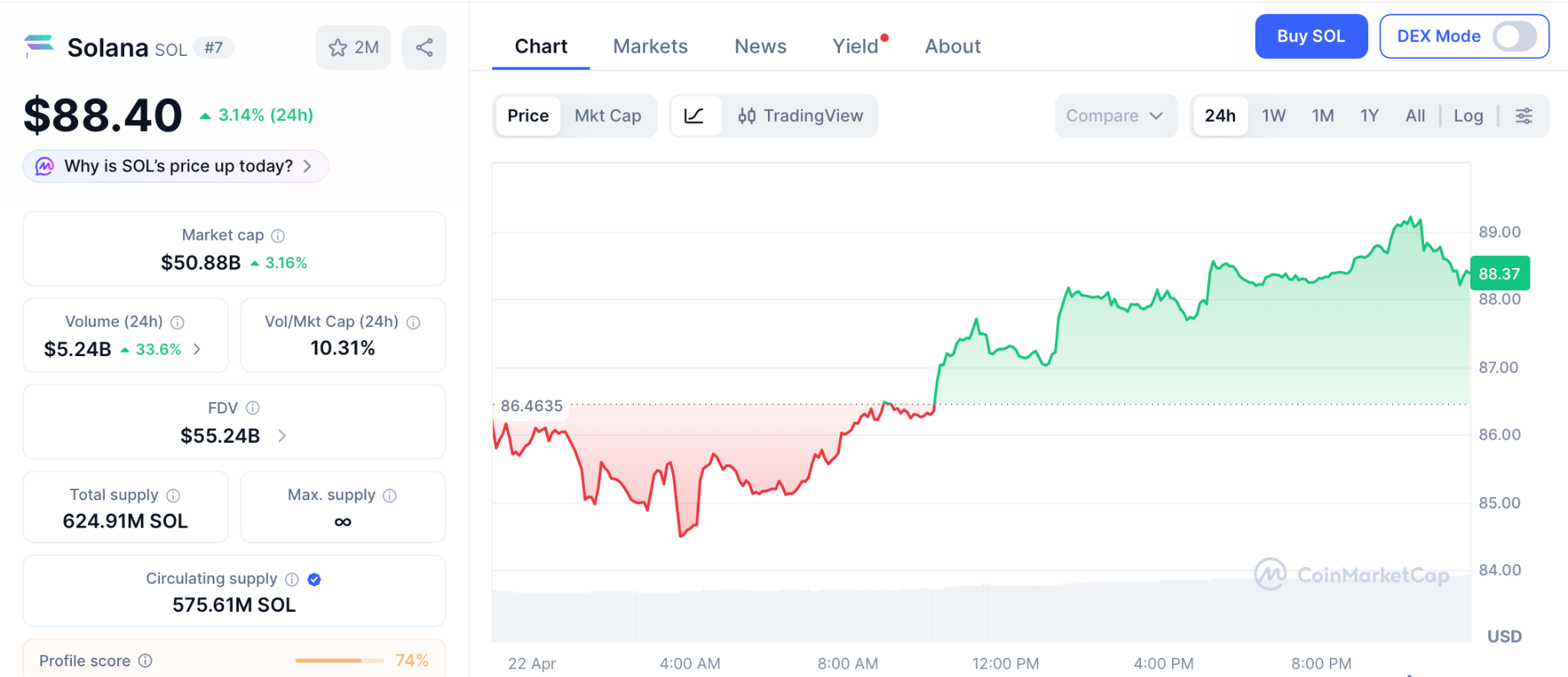
Support holds at $82 with $90 as first resistance. Clearing $90 opens $100, then $145 by year-end. A sustained cycle lifting SOL to $600 takes a full breakout run and billions in institutional flow.
Bitcoin (BTC) Price at $79,200 as Strategy Flips BlackRock in the ETF Race
Bitcoin trades at $79,200 on April 21 after rising 2.7% from Monday’s open. Strategy completed a $2.54 billion purchase of 34,164 BTC on April 20, flipping BlackRock as the single largest Bitcoin holder, while spot ETFs extended their inflow streak to five sessions with $238 million on April 21.
Support sits at $74,000 with $80,000 as the near-term ceiling. A full return to the $126,000 peak is 65% from here, and the broader macro bid lifts every presale with a working product and a confirmed exchange debut.
Conclusion
The Solana price prediction carries conviction after $1 trillion of Q1 on-chain volume, and Bitcoin pushing back toward $80,000 shows the lift is spreading into altcoins. But clawing back drawdowns and stacking real wealth are separate outcomes entirely.
Each cycle, the portfolios that finish richest hold blue chips alongside one early position the crowd missed. Pepeto is still accepting wallets. Binance is next on the calendar.
The gap between a recovered portfolio and one that prints generational numbers is a single presale position taken ahead of the debut. The accounts that act first always book the biggest returns, and presale performance across bull runs makes the case plainly while the rest carry the regret.
Click To Visit Pepeto Website To Enter The Presale
FAQs
What is the current Solana price prediction and how does $600 fit?
The Solana price prediction targets $100 to $145 near term on Alpenglow and ETF inflows, with $600 requiring a full cycle breakout. Pepeto aims for listing-scale returns in a single event.
What is Pepeto and why is capital rotating in?
Pepeto pairs a zero-cost swap engine, a multi-chain bridge, and PepetoAI contract scanning under a SolidProof audit. The raise sits at $9.29 million, staking pays 179% APY, and the Binance debut is confirmed from $0.0000001865.
Disclaimer: This is a Press Release provided by a third party who is responsible for the content. Please conduct your own research before taking any action based on the content.
Crypto World
Kalshi Bans 3 US Candidates Over Insider Bets on Elections

Two US congressional candidates and one sitting lawmaker have received fines and bans from Kalshi after they were found betting on the outcomes of their election races, as prediction market platforms crack down on insider trading.
Matt Klein, a sitting member of the Minnesota State Senate, was fined $539 for betting on his primary race in his bid for the US House of Representatives, which is set to take place in August. Ezekiel Enriquez, who ran for a US House seat in March, received a $784 penalty, according to Kalshi’s notice of settlement.
Another case involved Mark Moran, a candidate in Virginia’s US Senate race, who received a $6,229 penalty and was ordered to return any profits from his trades after allegedly refusing to cooperate with Kalshi to resolve the issue. All three were banned from the platform for five years.
Prediction markets, which let users trade contracts on the outcomes of future events, have faced growing scrutiny over insider trading and possible violations of gambling laws. Kalshi and Polymarket, the two largest platforms, have pledged to introduce stricter controls and crack down on unlawful activity.
Lawmakers offer reasons for insider trades
Moran said in a statement on X that he placed his wager to test Kalshi’s procedures and see how the platform would respond to insider trading.
“YES, I did bet ~$100 on myself on Kalshi because I wanted to get caught,” he said, adding that he “wanted to see (1) if Kalshi would come after me and (2) what their path would be.”

Klein said in a statement that he placed the wager out of curiosity about how prediction markets worked, but later learned it violated platform rules.
“In compliance with their request, I paid a penalty and agreed to be suspended from the platform. That was the only wager I have ever made on a predictions market,” he added.
Klein is a co-sponsor of a bill in the Minnesota Legislature that aims to ban wagers on the outcomes of real-world events such as elections or policy decisions.
Cointelegraph was unable to reach Ezekiel Enriquez for comment.
Kalshi’s ongoing insider trading crack down
Bobby DeNault, Kalshi’s head of enforcement, said Tuesday these cases violated Kalshi’s exchange rules but didn’t warrant referral to the US Commodity Futures Trading Commission or the Department of Justice for further investigation and prosecution.
Related: Charles Schwab, Citadel Securities are eying prediction markets
“Regardless of the size of a trade, political candidates who can influence a market based on whether they stay in or out of a race violate our rules. No matter how small the size of the trade, any trade that is found to have violated our exchange rules will be punished,” he added.
The platform issued a $2,000 fine and a five-year ban in February to a former California gubernatorial contender for betting on his own candidacy last year.
Magazine: How to fix suspected insider trading on Polymarket and Kalshi
Crypto World
NY, IL Ban State Employees From Prediction Markets

New York Governor Kathy Hochul signed an executive order barring state employees from participating in prediction-market betting, adding a formal layer of ethics rules to a sector that has seen rapid growth and rising scrutiny. The move follows a similar order issued by Illinois earlier in the week and underscores a broader policy shift as authorities weigh the implications of insider information and market manipulation in event-based markets.
Hochul framed the policy as a defense of public integrity, stating that “getting rich by betting on inside information is corruption, plain and simple.” The executive order also criticizes the federal policy environment for permitting an “ethical Wild West” around prediction markets without meaningful standards to curb insider trading. The directive makes clear that violations may lead to dismissal and could invite law enforcement action, while explicitly prohibiting state employees and officers from assisting others in profiting on confidential information through prediction markets.
Illinois moved in a parallel direction, with Governor JB Pritzker issuing an executive order that expands state ethics oversight in response to the rapid expansion of online prediction markets and event-based betting contracts. A formal statement from Illinois framed the action as a reinforcement of transparent governance and a preventative measure against insider trading as these platforms gain scale and reach across public life. The two states’ actions reflect a growing concern among policymakers that prediction markets, while useful for information aggregation, can become vectors for illicit trading if not properly restricted.
The movement comes amid mounting attention on how prediction markets operate when sensitive information may influence outcomes such as geopolitical events, military actions, or major policy decisions. Hochul cited specific cases that have drawn scrutiny over potential insider trades involving U.S. military action, pointing to instances where confidential information appeared to intersect with trading activity. These references illustrate why state-level ethics rules are becoming a focal point for both compliance programs in public administration and the private platforms that host these markets.
Key takeaways
- State-level ban on official participation: New York’s executive order prohibits state employees from engaging in prediction-market betting and signals a broader intent to curb conflicts of interest within public service.
- Parallel action in Illinois: Illinois issued a similar executive order, reinforcing ongoing regulatory attention to insider trading risks in prediction markets and setting a precedent for other states.
- Rapid market growth with regulatory risk: Prediction markets have seen sustained growth in volume, with March activity reaching a record level, highlighting the tension between information efficiency and insider-trading risk. According to Cointelegraph, monthly volumes climbed to $23.6 billion in March as markets expanded across sports, elections, and business outcomes.
- Notable enforcement activity: High-profile cases and platform actions illustrate tightening enforcement around insider trading, including actions involving traders and platform operators as scrutiny intensifies.
- Platform regulatory battles: Kalshi faces ongoing regulatory friction in multiple states, including cease-and-desist actions and court proceedings, with potential implications for how event-based contracts are treated under state gaming and wagering laws.
Insider trading concerns and enforcement dynamics in prediction markets
The discourse around prediction markets has increasingly moved from theoretical debates about market efficiency to concrete enforcement concerns. Hochul’s executive order anchors that shift in law, linking ethics violations with tangible consequences for public service employees. The references to suspected insider trading tied to U.S. military actions highlight the practical stakes when confidential information intersects with trading activity online. While platforms argue that they operate within a framework designed to protect against misuse, regulators have repeatedly signaled that gaps in oversight could undermine public trust and market integrity.
Market participants have noted that prediction markets often cover high-stakes events—ranging from geopolitical developments to corporate earnings—creating incentives for non-public information to leak into trading activity. In response, platform operators have pursued their own oversight measures. For example, reports on enforcement actions against participants who wager on personal candidacies or other sensitive events illustrate that private platforms are increasingly expected to police and sanction behavior that may hamper fair markets. The broader takeaway for analysts and compliance teams is that estimation of risk now must include a robust review of how information flows are managed and how enforcement mechanisms align with public ethics obligations.
Beyond individual cases, the regulatory zeitgeist is pressing for stronger framework alignment across jurisdictions. The mounting attention from state governments to predict-market governance dovetails with ongoing debates about how event-based derivatives should be regulated, including where they fit within general securities, gaming, or consumer-protection laws. While the federal approach to prediction markets remains unsettled, state-level actions are effectively shaping the practical operating environment for platforms and participants alike. For institutions, this translates into tighter internal controls, enhanced KYC/AML considerations, and a heightened focus on conflicts-of-interest policies when dealing with internal or confidential information that could influence trading decisions.
Kalshi, Nevada, and New York: regulatory friction products a broader compliance map
The regulatory landscape for prediction-market platforms has become a focal point in several states. The Kalshi platform, which operates on event-based contracts, has faced a series of regulatory challenges as states seek to determine whether such contracts constitute illegal gambling or require separate licensing regimes. In New York, the State Gaming Commission issued a cease-and-desist order related to Kalshi’s unlicensed mobile wagering activities within the state, highlighting the complexities of regulating digital prediction markets within traditional gaming frameworks. Separately, a lower court in Nevada temporarily blocked Kalshi from operating in the state, with regulators arguing that the contracts facilitated unlicensed gambling. The outcomes of these actions could have far-reaching implications for how prediction markets are treated under state licensing regimes and gaming laws.
Industry observers note that the regulatory tension surrounding Kalshi underscores a broader question about the status of prediction-market platforms in the U.S. If these platforms are deemed to operate as unlicensed gambling venues, they may face a cascade of licensing and enforcement actions across multiple states. Conversely, if authorities reconcile these products under a securities or commodity framework—or carve out a clear regulatory pathway—the sector could experience clearer compliance roadmaps. In public commentary, some industry participants have indicated that the regulatory question could eventually reach the Supreme Court, depending on how lower court rulings align with existing interpretations of gambling, securities, and commodities law. Such a development would carry implications for the permissible boundaries of event-based derivatives and the proper boundaries of government interference in private market activity.
For market participants and compliance teams, these regulatory dynamics call for heightened vigilance around platform governance, trade monitoring, and the handling of non-public information. As enforcement actions proliferate at the state level, firms must reassess internal controls, including the segregation of confidential information, conflict-of-interest disclosures, and the scope of permissible trading for employees and affiliated entities. The evolving precedent could also influence cross-border considerations, as global regulators evaluate whether similar governance models require standardized minimum standards or a more harmonized approach to event-based contracts and their financial or social risks.
Regulatory policy in a broader policy and market-structure context
While the U.S. state-level actions form a syndicate of ethics and compliance measures, observers are increasingly aligning these moves with broader policy debates. The rapid growth of prediction markets—driven by platforms that cover sports outcomes, elections, and business events—has intensified scrutiny of how these markets integrate with traditional financial and gaming regulatory regimes. In parallel, global policy evolution, including frameworks like the European Union’s MiCA, continues to shape how mainstream crypto-asset markets and related derivatives are governed. Although MiCA focuses primarily on crypto assets and their regulatory treatment, its approach to licensing, transparency, and cross-border activity offers a useful reference point for institutions navigating multi-jurisdictional compliance in rapidly evolving financial technologies. The comparative lens underscores the importance of robust, auditable governance structures, clear definitions of permissible activities, and consistent enforcement signals to support institutional adoption and compliance resilience.
For corporate counsel, risk managers, and financial investigators, the current trajectory suggests a dual emphasis: strengthening internal ethics regimes within public bodies and ensuring external platforms implement clear, enforceable standards that deter insider trading and manipulation. The thread tying these developments together is a clear move toward explicit governance of information flows, robust monitoring for suspicious activity, and a defined path for regulatory action when rules are bent or broken. This alignment is essential not only for market integrity but also for preserving trust among participants, investors, and the public sector that depends on orderly, predictable oversight of these innovative markets.
In sum, the surge in prediction-market activity is meeting a corresponding escalation in regulatory attention. State governments are taking concrete steps to limit conflicts of interest within public service, while enforcement against platform operators and traders intensifies the legal and regulatory risk landscape. As legal challenges unfold and potential Supreme Court consideration looms, market participants should expect continued clarity and continuity in compliance expectations, alongside ongoing innovations in platform governance and risk controls.
Closing perspective: the evolving regulatory framework for prediction markets will shape best practices across governance, monitoring, and cross-border operations. Institutions should monitor not just state actions but the legal ripples that may reach federal policy, court rulings, and potentially international standards as these markets mature.
-

 Sports6 days ago
Sports6 days agoNWFL Suspends Two Players Over Post-Match Clash in Ado-Ekiti
-

 Fashion5 days ago
Fashion5 days agoWeekend Open Thread: Theodora Dress
-

 Politics5 days ago
Politics5 days agoPalestine barred from entering Canada for FIFA Congress
-
Entertainment3 days ago
NBA Analyst Charles Barkley Chimes in on Ice Spice McDonald’s Fiasco
-

 Business4 days ago
Business4 days agoPowerball Result April 18, 2026: No Jackpot Winner in Powerball Draw: $75 Million Rolls Over
-

 Tech4 days ago
Tech4 days agoAuto Enthusiast Scores Running Tesla Model 3 for Two Grand and Turns It Into Bare-Bones Go-Kart
-
 Politics4 days ago
Politics4 days agoZack Polanski demands ‘council homes not luxury flats for foreign investors’
-

 Crypto World5 days ago
Crypto World5 days agoRussia Pushes Bill to Criminalize Unregistered Crypto Services
-
 Politics2 days ago
Politics2 days agoGary Stevenson delivers timely reminder to register to vote as deadline TODAY
-

 Politics10 hours ago
Politics10 hours agoDisabled people challenge government SEND proposals over segregation concerns
-

 Business18 hours ago
Business18 hours agoRolls-Royce Voted UK’s Most Iconic Trade Mark as IPO Register Hits 150
-

 Politics9 hours ago
Politics9 hours agoMaking troops accountable for war crimes threatens US alliance, ex-SAS colonel warns
-

 Business6 days ago
Business6 days agoCreo Medical agree sale of its manufacturing operation
-

 Crypto World5 days ago
Crypto World5 days agoRussia Introduces Bill To Criminalize Unregistered Crypto Services
-

 Politics11 hours ago
Politics11 hours agoStarmer handler McSweeney to be dragged from shadows by Foreign Affairs Committee
-

 Politics10 hours ago
Politics10 hours agoZack Polanski responds to home secretary’s taser threat
-
Politics11 hours ago
Wings Over Scotland | How To Get Away With Crimes
-

 Crypto World4 days ago
Crypto World4 days agoKelp DAO rsETH Bridge Hack Drains $292M as DeFi Losses Top $600M in Two Weeks
-

 Politics8 hours ago
Politics8 hours ago‘Iran is still a nuclear threat’
-

 Tech7 days ago
Tech7 days agoFord EV and tech chief leaving automaker












You must be logged in to post a comment Login