Crypto World
Bitcoiners Propose Freezing Quantum-Vulnerable Coins Under BIP-361

Bitcoin researchers led by cypherpunk Jameson Lopp, along with five co-authors focused on quantum security, have put forward a controversial plan to shield the network from a future quantum-enabled theft. The proposal, labeled BIP-361 and titled “Post Quantum Migration and Legacy Signature Sunset,” would be implemented in three stages to migrate coins away from quantum-vulnerable output types — including Satoshi’s widely discussed stash — and to harden the network before quantum computers become practical threats. The draft was posted to GitHub this week as the second installment in the broader plan.
The impetus for the proposal is clear: researchers warn that roughly 1.7 million BTC stored in early P2PK addresses could be at risk if a quantum adversary gains access to powerful quantum hardware. Among these coins is the so‑called Satoshi stash, which some estimate could be valued in today’s dollars at around $74 billion. The aim, the authors argue, is to prevent a scenario in which quantum-enabled theft undermines trust in the Bitcoin network. The plan is framed as a defensive mechanism—a private incentive to upgrade—rather than an offensive maneuver to seize control of others’ funds.
Key takeaways
- BIP-361 is a three-phase plan that follows BIP-360’s soft-fork approach and aims to migrate vulnerable coins to quantum-resistant paths, addressing about 34% of Bitcoin’s supply that remains at risk unless moved.
- The phases are timed: Phase A begins three years after activation and would stop new BTC from being sent to old-style addresses, requiring users to migrate to quantum-resistant types.
- Phase B arrives five years after activation, invalidating old-style signatures and effectively freezing any funds remaining in vulnerable addresses.
- Phase C provides a zero-knowledge proof-based recovery mechanism for those who missed the deadline but can still demonstrate ownership via seed recovery, offering a potential rescue path.
- The proposal has drawn swift pushback from parts of the Bitcoin community, with critics calling it heavy-handed or confiscatory, arguing it undermines Bitcoin’s ethos of opt-in upgrades.
Context and the technical what-ifs
In February, developers released BIP-360, which proposed a soft fork introducing a new output type known as pay-to-Merkle-root (P2MR). The idea mirrors Bitcoin’s existing Taproot (P2TR) structure but removes the quantum-vulnerable key path from legacy addresses. While BIP-360 would protect funds moving forward, it does not automatically safeguard the substantial portion of the supply that remains vulnerable in old addresses unless owners proactively move funds to quantum-resistant forms.
BIP-361 extends this concept into a staged migration. Three years after activation, Phase A would bar transfers to old-style addresses, forcing users to adopt quantum-secure address formats. Then, five years after activation, Phase B would invalidate old-style signatures altogether, rendering coins in vulnerable addresses effectively unspendable unless they have already migrated. Phase C offers a potential rescue mechanism using zero-knowledge proofs to allow recovery for users who still possess their seed phrases but failed to upgrade in time.
Related: Bitcoin Magazine has noted the debate’s potential hard-fork implications, underscoring that the policy could center the fate of historical coins and alter the network’s long-term security model.
“This is not an offensive attack, rather, it is defensive: our thesis is that the Bitcoin ecosystem wishes to defend itself and its interests against those who would prefer to do nothing and allow a malicious actor to destroy both value and trust.”
Community reaction and the philosophical divide
The plan has ignited a robust discussion about Bitcoin’s core principles and the trade-offs of upgrading a global, permissionless system. Critics argue that forcing upgrades or rendering unupgraded UTXOs unspendable would mark a significant departure from Bitcoin’s ethos of non-coercive change and could set a dangerous precedent for future interventions.
Bitcoin protocol developer and researcher Mark Erhardt, who circulated BIP-361 on social media, faced immediate critique. Responders described the proposal as “authoritarian and confiscatory,” questioning the rationale for mandating upgrades and the legitimacy of rendering old spends invalid.
Other voices weighed in with skepticism as well. Bitcoin Magazine’s editors and contributors have been vocal in challenging the premise, while TFTC founder Marty Bent characterized aspects of the approach as inconsistent with the community’s expectations. Phil Geiger, head of business development at Metaplanet, offered a provocative take on the tension between protection and coercion. The broader sentiment remains unsettled: the consensus on whether a crypto-legalistic safeguard should override voluntary evolution is far from settled.
Cointelegraph reached out to Lopp for comment on the proposal; there was no immediate response at the time of publication. The GitHub draft, however, provides a concrete framework for discussion and potential future forks, even as many stakeholders call for a cautious, community-driven examination of the implications.
For readers tracking the evolution of quantum resilience in Bitcoin, the conversation now shifts from theoretical risk to concrete, staged mitigation. The three-phase design is designed to minimize disruption by letting the ecosystem migrate over time, but it also raises fundamental questions about asset-holding rights, upgrade incentives, and the governance of a decentralized network.
Implications for holders, users, and builders
From a practical standpoint, BIP-361 highlights two enduring tensions in Bitcoin’s path to quantum readiness. First, there is the temptation to act decisively to protect value, especially when the stakes include a multi-trillion-dollar network and the world’s most valuable cryptocurrency by market capitalization. Second, there is the risk that coercive upgrades or automatic penalties could fragment the ecosystem or erode trust among users who prefer to manage their own keys and seeds at their own pace.
For investors and developers, the proposal underscores the importance of forward-looking security models. If the plan progresses, the market could see increased demand for quantum-resistant wallets and services, as well as migrations that push older holders toward newer output types. The timeline—three years to Phase A and five to Phase B—provides a window for infrastructure teams to test compatibility, wallets to implement support for P2MR-like paths, and communities to debate the ethics and practicality of forced upgrades.
As the discussion unfolds, observers will be watching how this approach interacts with existing upgrade narratives, such as soft forks and user-initiated migrations. The zero-knowledge recovery proposed in Phase C is a particularly notable element: it aims to offer a path back to funds for those who missed the deadline, but the feasibility and privacy implications of such a mechanism will require rigorous scrutiny before any real-world deployment.
What to watch next
The BIP-361 draft opens a testing ground for how the Bitcoin community might address quantum threats without waiting for a single, sweeping upgrade. The next steps will likely involve broader discussions on GitHub, more technical vetting of the P2MR architecture, and public comment on the ethical and philosophical implications of effectively freezing or confiscating old UTXOs. Investors and builders should monitor how proponents respond to pushback from core developers and community voices, and whether practical consensus emerges around the timing and scope of any future activation.
As the conversation evolves, the central question remains: can a planned, staged migration deliver robust quantum protection without compromising Bitcoin’s foundational principles? The answer will shape not just security strategies, but the culture of upgrade, trust, and governance in the years ahead.
Crypto World
Binance says AI-driven security foiled $10B in fraud since 2025.
Binance says its AI-powered security tools prevented more than $10 billion in user fund losses to scams and fraud between 2025 and March 2026, according to a security-focused blog post from the exchange. The company reported that over 5.4 million users were protected from fraud between Q1 2025 and Q1 2026 after deploying more than 24 AI-driven initiatives and more than 100 models.
Over the 15 months to March 2026, Binance says it blocked $10.53 billion of potential losses and blacklisted 36,000 malicious addresses as its AI-enabled security protocols ran in the background. In the most recent quarter, the exchange highlighted a surge in activity: it intercepted 22.9 million scam and phishing attempts in Q1 2026 alone, saving $1.98 billion for users. The numbers, described in Binance’s security blog, underscore the rapid expansion of automated defenses as scams grow more sophisticated.
“AI-powered scams and exploits are accelerating,” Binance said. “The barrier to entry for scam perpetrators is falling fast, with AI accelerating the drop. What once required technical expertise can now be executed for next to nothing and at scale.” The warning reflects broader industry concerns that threat actors are leveraging artificial intelligence to enhance impersonation, social engineering and phishing campaigns. In the same vein, the FBI has noted elevated scam activity tied to crypto, citing substantial losses reported in the United States in recent periods.
Binance emphasizes that its AI tools are not just reactive, but embedded in real-time decisioning across its security stack. By integrating AI with its risk controls, the platform says it now intercepts attacks before user funds are moved and helps to differentiate legitimate activity from fraudulent patterns at scale. According to the blog, AI-driven decisioning now powers 57% of its fraud controls, contributing to a 60-70% reduction in card fraud rates relative to industry benchmarks. The company also pointed to ongoing work in identity verification to counter increasingly sophisticated deepfakes and synthetic identities.
Key takeaways
- Over 15 months ending in March 2026, Binance reports $10.53 billion in prevented losses and 36,000 malicious addresses blacklisted through AI-enhanced security measures, with more than 5.4 million users protected between Q1 2025 and Q1 2026.
- In Q1 2026 alone, the exchange intercepted 22.9 million scam and phishing attempts, saving $1.98 billion for users.
- AI-driven decisioning accounts for 57% of Binance’s fraud controls, with a claimed 60-70% reduction in card fraud rates versus industry benchmarks.
- The security stack employs computer vision to verify payment proofs, real-time language analysis to detect scam patterns, and enhanced identity verification to combat deepfakes and synthetic identities.
- The development comes amid a broader concern that AI-enabled scams are increasing in breadth and sophistication, reinforcing the need for robust defense mechanisms across exchanges and custodial platforms.
Inside Binance’s AI security toolkit
The security program described by Binance folds a wide range of AI capabilities into its existing risk controls. The company notes that computer vision components are used to detect fake payment proofs, while real-time language analysis monitors communications for suspicious patterns and indicators of fraud. On the identity side, the system is designed to counter deepfakes and synthetic identities that fraudsters may use to bypass traditional verification steps. Taken together, these tools are meant to reduce the likelihood that compromised or impersonated accounts can be exploited for exfiltration or manipulation of funds.
Binance also highlights a data-driven approach to governance and monitoring. By combining behavioral signals, transaction patterns and contextual data, the platform aims to flag unusual activity early and apply automated responses in real time. The emphasis on AI-driven decisioning—where a majority of fraud controls are now powered by AI—speaks to a broader shift in crypto security toward automated, scalable defense mechanisms that can adapt to evolving attack tactics.
Context, risk, and regulatory undertones
The concerns Binance raises about AI-enabled scams echo a broader industry risk landscape. Crypto-related fraud remains a persistent challenge for users and regulators alike, with authorities noting that attackers rely on social engineering, impersonation and increasingly convincing fake content. The FBI has flagged substantial losses linked to crypto scams, underscoring the importance of effective defense mechanisms as the technology that underpins these platforms scales in capability and reach. These dynamics place exchanges under pressure to demonstrate tangible security improvements while maintaining a user-friendly experience and transparent reporting.
From a market perspective, the deployment of AI in security can influence user confidence, willingness to engage with centralized exchanges, and the perceived risk profile of asset custodians. Investors and traders will be watching not only the absolute totals of funds saved or losses prevented but also how these tools perform across different jurisdictions, regulatory environments and product segments. The question going forward is how AI-driven security measures will balance proactive defense with user privacy, provide explainable risk signals, and scale with the growing volume and variety of crypto activity.
What to watch next
Readers should monitor whether Binance expands its AI security footprint beyond its current scope, including coverage of new product areas, regions, or asset classes. While the firm cites substantial quarter-to-quarter improvements, questions remain about the durability of these defenses as attackers adapt and as AI itself evolves. Expect more granular updates on the effectiveness of individual AI modules, potential cross-border enforcement considerations, and how other exchanges position their own AI-driven security programs in response to rising threats.
For a closer look at Binance’s security measures and the full set of claims, see the firm’s security blog post detailing the initiative and the metrics cited accompanying the 24 AI-driven initiatives and 100+ models. The post highlights the linkage between AI tools and real-time risk controls, emphasizing the intention to harden defenses as scammers grow more sophisticated. Binance security blog.
Alongside these developments, observers will continue to weigh the role of AI in fraud prevention against the risk of over-reliance on automated systems, potential false positives, and the need for ongoing user education. The crypto ecosystem remains a dynamic arena where defensive innovation and adversarial ingenuity co-evolve, and Binance’s latest figures offer a data point in that ongoing confrontation.
As the sector digests these disclosures, the key takeaway for users and investors is clear: AI-assisted security is becoming mainstream in crypto, but it is not a panacea. Ongoing transparency about performance, edge cases, and the safeguards around automated decisioning will be essential to gauge whether these tools translate into reliably safer experiences for the average user. The next few quarters should reveal whether the early momentum translates into sustained reduction in fraud across the broader ecosystem.
Crypto World
Qualcomm (QCOM) Stock Soars to Record Peak Fueled by AI Data-Center Push
Key Takeaways
- Qualcomm shares jumped 8.4% Monday, closing at an unprecedented $237.53
- Year-to-date gains stand at 39%, with a remarkable 32% surge in May alone
- CEO Cristiano Amon announced a custom data-center chip scheduled for delivery to a major hyperscaler in Q4 2026
- Daiwa Securities elevated its rating from Neutral to Outperform, setting a $225 target
- The stock’s five-session winning streak represents its strongest performance since April 2019
Qualcomm shares finished Monday’s trading session at $237.53, marking an 8.4% daily increase and surpassing the company’s prior record close of $227.09 from June 2024. The chipmaker ranked among the S&P 500’s top performers for the day.
This surge extends an impressive momentum streak. The stock has posted gains for five consecutive trading days, accumulating a 41% increase during that period. Market data from Dow Jones indicates this represents QCOM’s strongest five-day performance since late April 2019.
The upward trajectory follows Qualcomm’s April 29 fiscal second-quarter earnings release, which exceeded Wall Street projections for both top-line revenue and bottom-line earnings. While the financial results were impressive, subsequent announcements sparked even greater investor enthusiasm.
During the analyst call, CEO Cristiano Amon revealed that preliminary deliveries of a custom data-center chip are planned for the December quarter, destined for a significant hyperscaler client. While the customer’s identity remains undisclosed, Amon characterized it as a “large hyperscaler” and suggested an ongoing, multi-generation partnership. Additional information is anticipated during Qualcomm’s June investor day.
This announcement fundamentally altered market perception. While investors traditionally categorized Qualcomm as a smartphone-focused semiconductor company, the data-center initiative demonstrates a strategic pivot — transforming into a player in AI infrastructure at an enterprise scale.
Analyst Community Takes Notice
In the wake of the earnings announcement and Amon’s strategic revelations, several analysts revised their positions. Daiwa Securities upgraded QCOM from Neutral to Outperform while establishing a $225 price objective. Both Tigress Financial and Benchmark similarly increased their price targets.
Despite the optimistic trading activity, the consensus rating among more than 40 analysts surveyed by FactSet remains at Hold, with an aggregate price target of $176.72. Current trading levels place QCOM approximately 34% above that consensus forecast.
Broader semiconductor sector strength contributed to Monday’s rally. Intel shares rose 3.6% following reports of a tentative agreement to produce chips for Apple products. The PHLX Semiconductor Index recently recorded its most substantial 25-day advance since the dot-com era in 2000.
Diversification Strategy Unfolds
Qualcomm has systematically expanded its revenue portfolio beyond traditional smartphone components, incorporating automotive applications, internet-of-things devices, and AI-powered solutions. The company’s fiscal Q2 performance illustrated this strategic diversification, with meaningful contributions across multiple market segments.
Industry analysts project global semiconductor revenue will exceed $1 trillion this year, primarily driven by AI infrastructure and data-center expansion. This industry-wide catalyst has elevated the entire sector, and Qualcomm appears strategically positioned to capture market share in data-center segments where it hasn’t historically maintained a presence.
QCOM has appreciated 36% since the beginning of January. The trailing twelve-month performance shows a 56% gain.
The company plans to elaborate on its data-center strategy during its upcoming investor day scheduled for June.
Crypto World
Pi Network’s PI Token Falls Out of Top 50 Alts, Bitcoin (BTC) Stopped at $82K: Market Watch
Bitcoin initiated another breakout attempt in the past 12 hours or so, only to be rejected once again at $82,000 and driven south by more than a grand.
Most larger-cap alts have remained relatively flat on a daily scale, aside from ETH, which is under $2,300 once again. XRP and BNB keep fighting for the fourth spot in terms of market cap.
BTC Stopped at $82K
The previous business week saw a notable price surge from the larger cryptocurrency to a three-month peak of almost $83,000. Thus, the asset had added $8,000 from the previous Wednesday, and it seemed primed for a correction as many analysts warned about the rally’s structure.
BTC indeed slipped to $79,000 by Friday before the bulls stepped up and didn’t allow another breakdown. Instead, bitcoin started to recover some ground and quickly returned to over $80,000 during the weekend.
More volatility ensued on Monday morning when BTC first dipped to $80,250, before it shot up to $82,500, but it was rejected and dropped by two grand immediately when US President Trump deemed Iran’s latest peace proposal “totally unacceptable.”
It bounced again yesterday, but this time, its attempt was halted at $82,000. The subsequent rejection brought it south to a familiar territory of under $81,000, where it currently sits. Its market cap remains sideways at $1.620 trillion on CG, while its dominance over the alts is up to 58.3%.

BUILDon Enters Top 100, PI Exits Top 50
Today’s top performer from the largest 100 alts is BUILDon (B). The token is up a mind-blowing 44% to $0.63, making it the 93rd-largest cryptocurrency by market cap. In contrast, PI’s continuous declines have pushed the asset out of the top 50 alts by the same metric, after a 6% weekly decline.
CRO, STABLE, TON, and CC follow suit in terms of daily gains, while JUP, VVV, and PUMP have declined the most.
Ethereum has slipped by 2% daily and now trades well below $2,300. XRP, BNB, SOL, and DOGE have posted minor gains, while HYPE, ZEC, and LINK are down by over 1%.
The total crypto market cap has remained at the same level as yesterday, at around $2.8 trillion on CG.

The post Pi Network’s PI Token Falls Out of Top 50 Alts, Bitcoin (BTC) Stopped at $82K: Market Watch appeared first on CryptoPotato.
Crypto World
Cathie Wood’s Ark Invest chases Circle (CRC) stock as it hits a two-month high


Ark Invest bought $5.5 million worth of shares in Circle Internet (CRCL) on Monday as the stablecoin developer’s stock pumped following its first-quarter earnings report.
The St. Petersburg, Florida-based investment manager added 41,904 shares across three of its exchange-traded funds (ETFs): Innovation (ARKK), Next Generation Internet (ARKW) and Blockchain and Fintech Innovation (ARKF).
CRCL shares rose 16% to $131.76, the highest closing price since March 18, after the company posted estimate-beating earnings per share (EPS) of 21 cents.
Circle, whose USDC is the second-largest stablecoin, also revealed a $222 million raise for its Arc blockchain in a presale of the ARC token.
The purchase is Ark’s first of Circle stock since March 24, when it bought $16.3 million worth as the shares slumped 20%. It last sold CRCL on April 17, dumping $1.2 million worth on a day the stock closed at around $106.
The Cathie Wood-led company frequently buys into weakness in equities to capture greater value and rebalance the weighting of its ETFs. It is less common to see sizeable purchases that coincide with large share-price gains.
Crypto World
Galaxy Digital to manage Sharplink’s new $125 million onchain yield play


Galaxy Digital (GLXY) and Sharplink (SBET) are teaming up to put part of the latter’s staked ETH treasury into decentralized finance (DeFi) strategies.
The Galaxy Sharplink Onchain Yield Fund would receive $100 million from Sharplink’s staked ETH treasury and $25 million from Galaxy, the companies said.
Galaxy is set to manage the investment, which is expected to commence in the coming weeks under a non-binding memorandum of understanding.
The strategy will see capital deployed across DeFi liquidity protocols and other onchain yield strategies. The structure is designed to keep Sharplink’s core ETH exposure intact while adding an active yield strategy to its balance sheet.
Sharplink holds 872,984 ETH, according to separate first-quarter results. The company has generated 18,800 ETH in staking rewards since launching its ether treasury strategy in June 2025, the firm said.
The allocation is small relative to Sharplink’s ETH stack but large enough to mark a shift in the treasury model. At recent prices, $100 million equals roughly 43,000 ETH.
Crypto World
Will Bitcoin price drop below $80K as Coinbase premium stays negative?

Bitcoin price slipped back toward the $81,000 region on Monday as weakening U.S. institutional demand and renewed geopolitical uncertainty triggered another wave of profit-taking across the crypto market.
Summary
- Bitcoin price fell back toward the $81,000 region after another rejection near the $82,000 resistance zone amid rising geopolitical uncertainty.
- The Coinbase Bitcoin Premium Index remained negative, signaling weaker buying demand from U.S. institutional investors in recent sessions.
- Technical indicators showed BTC still trading inside an ascending channel, though weakening MACD momentum raised risks of a retest below the $80,000 support level.
According to data from crypto.news, Bitcoin (BTC) traded around $80,900 at press time on May 12 after briefly falling toward an intraday low near $80,700. The pullback followed another failed breakout attempt above the key $82,000 resistance zone, where sellers continued aggressively defending upside momentum.
One of the biggest bearish signals came from the Coinbase Bitcoin Premium Index, which remained deeply negative throughout the past several trading sessions. The metric measures the price difference between Bitcoin on Coinbase and offshore exchanges such as Binance and is commonly used as a proxy for U.S. institutional demand.
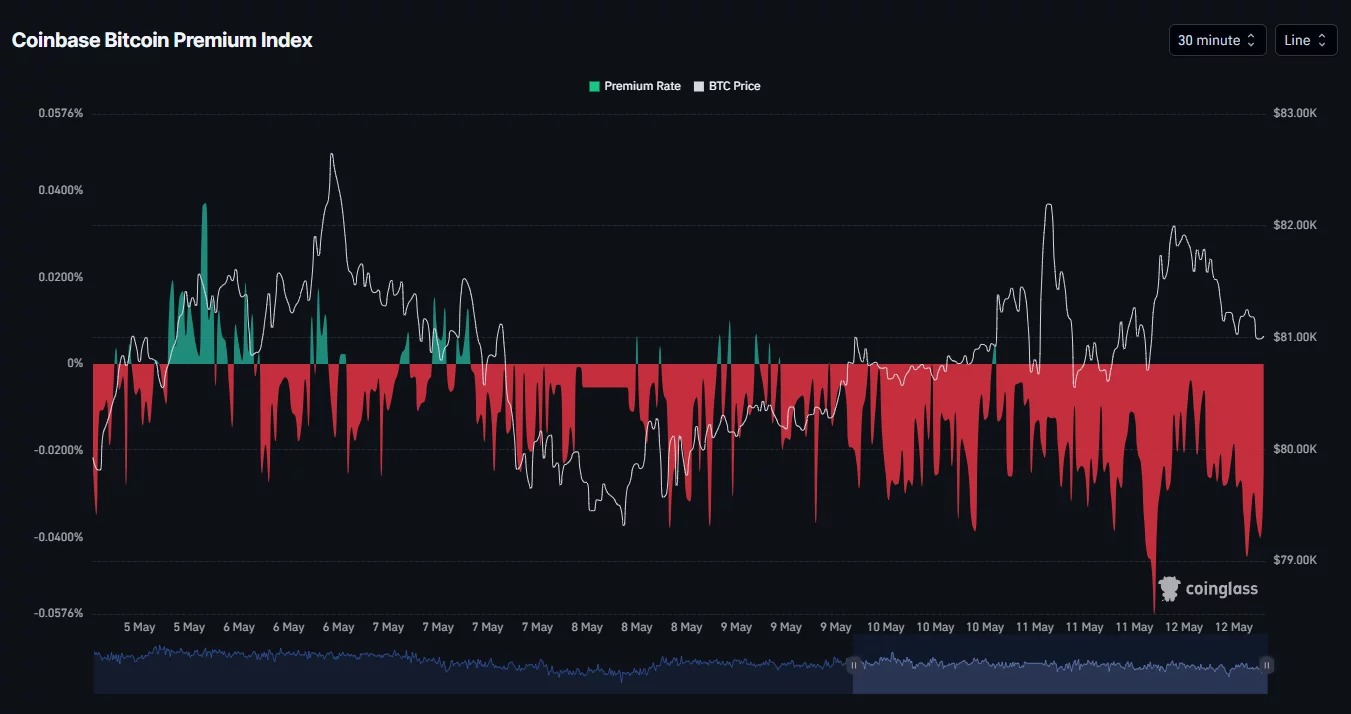
The persistent negative reading suggests that buying activity from U.S.-based investors has weakened considerably, even as Bitcoin attempted to stabilize above major support levels.
Market sentiment also deteriorated after reports indicated that U.S. President Donald Trump rejected a recent peace proposal from Iran, calling the offer “totally unacceptable.” The development renewed concerns that tensions between the two nations could escalate further, pushing investors away from risk assets like cryptocurrencies.
The geopolitical uncertainty triggered another rise in risk-off sentiment across global markets while oil prices remained volatile following the latest developments surrounding the conflict.
At the same time, traders continued locking in profits after Bitcoin’s recent rally toward the $82,700 region. Some analysts have also started warning that the latest rebound could potentially resemble a dead cat bounce following Bitcoin’s strong recovery from February lows.
Institutional flows have additionally shown signs of cooling in recent sessions. Spot Bitcoin ETFs reportedly recorded roughly $350 million in outflows during a recent 48-hour period, weakening short-term bullish momentum as markets repositioned around the weekly CME gap.
Bitcoin price analysis
On the daily chart, Bitcoin price continues trading inside a broader ascending parallel channel structure that has remained intact since late March. The bellwether recently touched the upper boundary of the channel before facing rejection near the $82,000 resistance region.

The chart also shows BTC struggling to sustain momentum above the key 0.786 Fibonacci retracement level near $80,000, a zone that continues acting as an important psychological battleground between bulls and bears.
Despite the recent pullback, Bitcoin still remains above the Supertrend support level near $75,600, indicating that the broader bullish trend structure has not yet fully broken down.
Meanwhile, the MACD remains in positive territory, although the histogram has started flattening considerably over recent sessions, suggesting bullish momentum may be weakening as buyers lose short-term control.
If selling pressure intensifies further, Bitcoin could retest the lower boundary of the ascending channel near the $80,000 psychological support zone. A decisive breakdown below that level could expose BTC to deeper downside toward the $76,000–$77,000 region.
On the upside, bulls would need to reclaim the $82,000 resistance area to restore bullish momentum and potentially reopen the path toward the next major resistance near $84,000.
Disclosure: This article does not represent investment advice. The content and materials featured on this page are for educational purposes only.
Crypto World
Anthropic warns against unauthorized stock exposure as token markets imply trillion-dollar valuation


Anthropic, the AI company behind Claude, is warning investors that tokenized products claiming to offer access to its private shares may be invalid, escalating a fight over whether restricted pre-IPO stock can be repackaged for retail traders.
In an updated investor-warning page first published in February, Anthropic said any unapproved sale or transfer of its stock, or any interest in its stock, is void and will not be recognized on its books.
“We do not permit special purpose vehicles (SPVs) to acquire Anthropic stock and any transfer of shares to an SPV are void under our transfer restrictions. Offers to invest in Anthropic’s past or future financing rounds through an SPV are prohibited,” the company wrote on an updated warning page. “This means that if someone purports to sell Anthropic shares without proper board approval, that transaction is invalid.”
It added that any third party claiming to sell Anthropic shares to the general public through direct sales, forward contracts, “tokenized securities,” or other mechanisms is likely either engaged in fraud or offering an investment that may have no value due to our transfer restrictions.
Over the past year, several crypto exchanges have set up offerings for pre-IPO exposure to some of the hottest tech companies on the planet, such as Anthropic, SpaceX, and Polymarket. However, not all offerings are the same.
Some are synthetic pre-IPO perpetuals, where no underlying shares are necessarily held, and traders are simply betting on a reference price tied to a private company’s implied valuation. Those instruments may not directly violate a company’s stock-transfer restrictions because no shares move, but they leave users with a derivative claim rather than equity exposure.
By contrast, products offering private market exposure through special purpose vehicles (SPVs) or secondary-market holdings, such as PreStocks’ tokenized single-asset offerings or the Robinhood Ventures Fund I, are closer to tokenized private-share exposure.
PreStocks’ terms of service state that buyers receive no equity or shareholder rights in the underlying company, only economic exposure tied to reserve backing, However, it does not specify whether this exposure is delivered through a special purpose vehicle, leaving uncertainty around the exact structure behind its Anthropic-linked tokens, which the company says may be invalid.
That model may be more intuitive to investors, but it also runs more directly into the restrictions private companies place on who can buy, sell or hold interests in their stock.
John Montague, a Florida-based crypto lawyer, previously told CoinDesk that private companies may challenge these structures.
“I think private companies may also initiate lawsuits alleging that this violates their governance documents, shareholders’ agreements, investor rights agreements, or bylaws,” he told CoinDesk last year. “I view it as the issuer’s right to control the terms of transfer.”
Aside from unauthorized stock transfers, another headache these markets create for companies is valuation. Tokenized markets can generate eye-popping implied price tags that appear to be legitimate public price discovery, even when the underlying liquidity is relatively small.
PreStocks’ dashboard recently showed that Anthropic had an implied valuation above $1.5 trillion and a market valuation of around $1.37 trillion, despite the platform holding roughly $23 million in total assets.
For private companies that raise capital through negotiated funding rounds rather than public markets, this creates a real narrative risk. Speculative token prices can begin to shape investor expectations and headlines about valuations beyond the company’s control.
Crypto World
Binance Says AI Security Stopped $10B in Fraud in 15 Months

Crypto exchange Binance says its artificial intelligence-based security tools have helped prevent the loss of more than $10 billion worth of user funds from scams and fraud between 2025 to March 2026.
Binance said in a blog post on Monday that it had protected more than 5.4 million users from fraud between the first quarter of 2025 and the first quarter of 2026 after rolling out over 24 AI-driven initiatives and more than 100 models.
“AI-powered scams and exploits are accelerating,” Binance said. “The barrier to entry for scam perpetrators is falling fast, with AI accelerating the drop. What once required technical expertise can now be executed for next to nothing and at scale.”
Scams and exploits have plagued crypto as highly organized threat actors have adopted AI to create more sophisticated attacks. The FBI reported in April that US citizens lost $11 billion worth of crypto to scams, with the impersonation of government officials or crypto companies being a key avenue used to dupe victims.
“AI is amplifying social engineering at an unprecedented level, powering deepfakes, phishing bots, fake platforms, voice cloning and impersonation across chat applications, exploiting trust and urgency,” Binance said.
Binance said that over the 15 months to March, it prevented $10.53 billion worth of user funds and blacklisted 36,000 malicious addresses via the integration of AI with its security protocols.
Related: DeFi can freeze stolen funds, but not everyone agrees it should
In the first quarter of 2026 alone, the exchange said it “intercepted 22.9 million scam and phishing attempts,” saving $1.98 billion worth of user funds.

Binance’s efforts to stop AI scams. Source: Binance
Binance said it has implemented computer vision to detect fake payment proofs and real-time language analysis to detect scam patterns, while also integrating the technology on the identity verification side to counter “increasingly sophisticated deepfakes and synthetic identities.”
“AI-driven decisioning now powers 57% of fraud controls, contributing to a 60-70% reduction in card fraud rates compared to industry benchmarks,” Binance said.
Magazine: AI-driven hacks could kill DeFi — unless projects act now
Crypto World
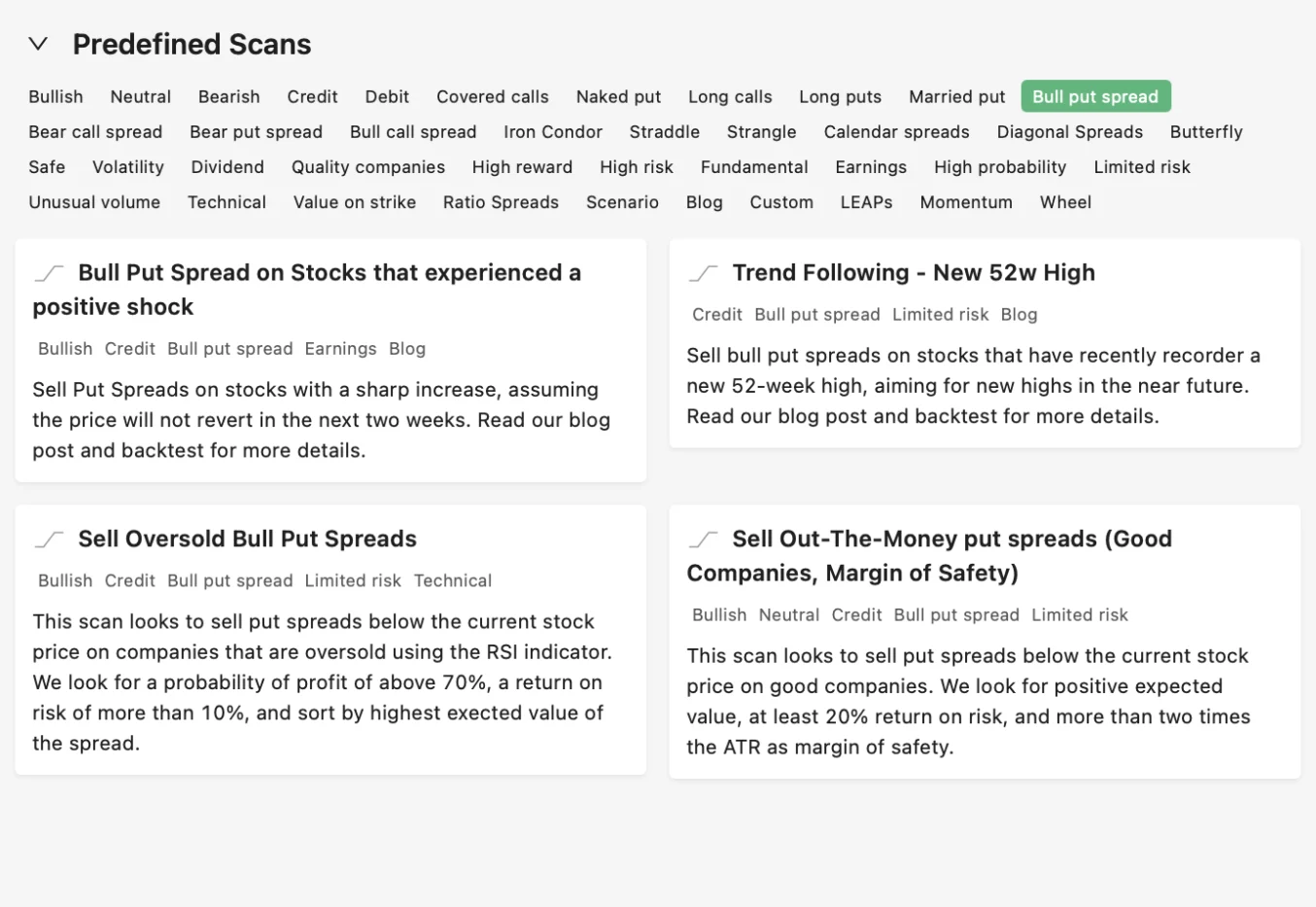
How to Scan the Market for Credit Spreads Using an Options Screener
Credit spreads are among the most popular strategies for generating consistent income with defined risk. The challenge is rarely understanding how they work. It is finding good candidates in a market with thousands of tickers and constantly shifting volatility. An option scanner built for multi-leg strategies changes this process entirely, replacing hours of manual searching with structured, repeatable workflows.
This guide explains how traders can use an options screener to identify credit spread opportunities that align with their outlook, risk tolerance, and income goals.
Why Credit Spreads Deserve a Screening Workflow
A credit spread involves selling one option and buying another at a different strike price, both on the same underlying and with the same expiration. The seller collects a net premium upfront and profits when the underlying stays within a defined range. The two most common types are the bull put spread, used when the outlook is neutral to bullish, and the bear call spread, used when the outlook is neutral to bearish.
The concept is straightforward, but execution depends heavily on the quality of the underlying stock, the pricing of the options, and how volatility is behaving at the time. A good-looking spread on a weak company or during a period of compressed volatility can quickly become a losing trade, even if the direction is right.
This is where using an easy to use options scanner adds value. Rather than browsing individual tickers and checking each one manually, an options screener filters the entire market based on the conditions that matter most for credit spread success: probability of profit, annualized return, spread width, volatility levels, and company quality.
What to Look for When Screening Credit Spreads
Probability of profit is often the first filter traders apply. A high probability of profit means the short strike is positioned far enough from the current price to give the trade room to work. Most options screeners allow filtering by delta or probability, letting traders set a minimum threshold before any results appear.
Annualized return matters because it normalizes the income across different expirations. A spread that returns 2% in 10 days looks different from one that returns 3% in 45 days when both are annualized. Filtering by annualized return helps compare setups on a level playing field.
Implied volatility context is equally important. Credit spreads are premium-selling strategies, and selling premium works best when implied volatility is elevated relative to its own history. Using IV Rank or IV Percentile as a filter ensures the premiums being collected are above average, not near the bottom of their range.
Liquidity and spread width round out the picture. Tight bid-ask spreads reduce slippage, and wider strike distances increase the credit received but also raise the maximum loss. An option scanner that includes these filters gives traders the ability to balance income against risk before placing any trade.
How Option Samurai Screens for Credit Spreads
Option Samurai includes predefined scans specifically designed for credit spread strategies. These scans are pre-built with filters that target high-probability setups on quality companies, making it easy to get started without configuring dozens of parameters manually.
The Bull Put Spread scans focus on neutral to bullish setups. They filter for companies with stable fundamentals, elevated implied volatility, and puts that offer attractive premiums relative to the risk. Results are sorted by probability of profit and annualized return, giving traders a clear view of the best available opportunities.
Here are some of the available bull put spread scans on Option Samurai:
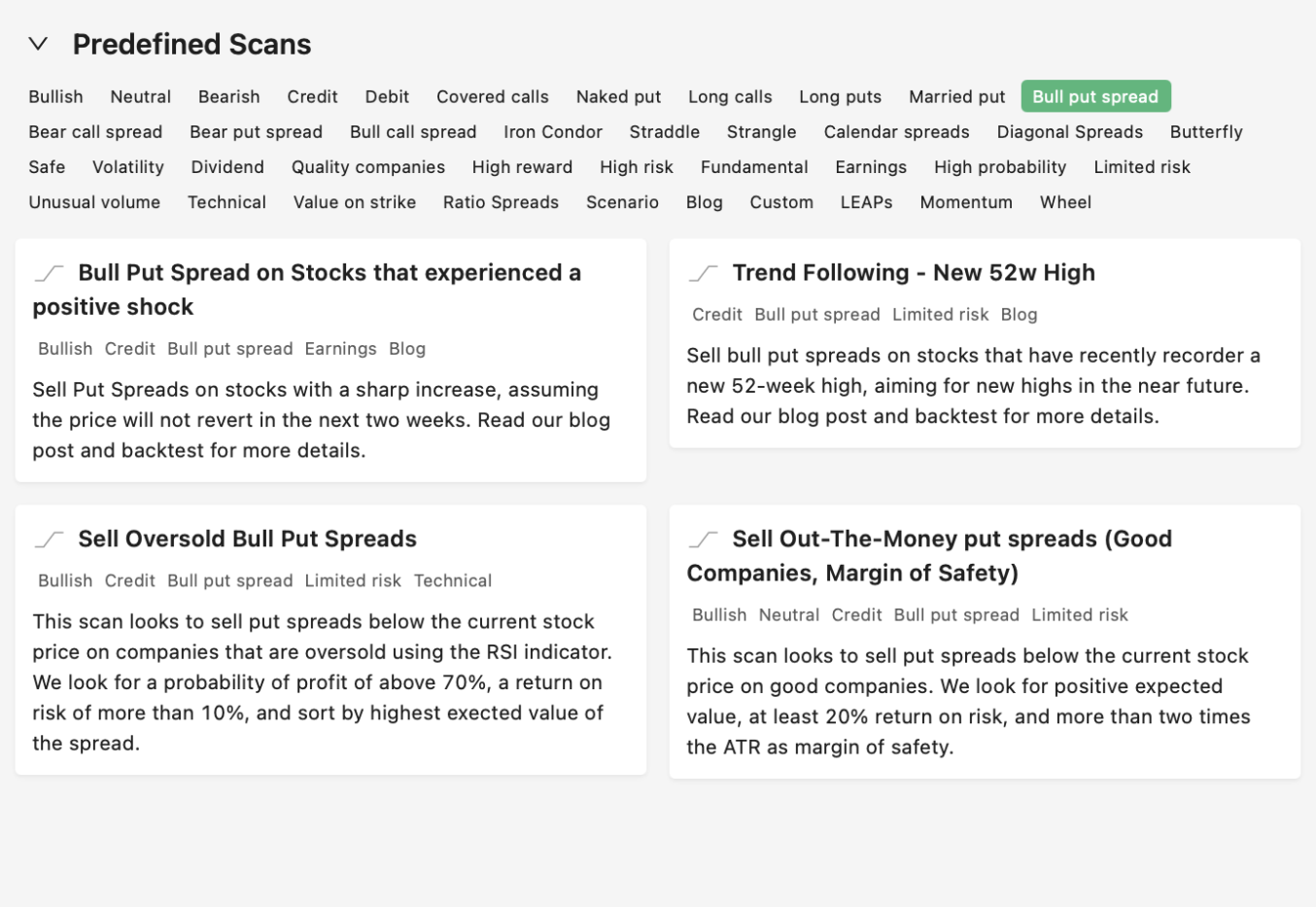
The Bear Call Spread scans apply the same logic in reverse, targeting stocks where the outlook is neutral to bearish and call premiums are rich enough to justify the trade. These scans are useful during periods of market strength when certain sectors or names appear overextended.
Again, this is a quick view of the scans users will find in Option Samurai:
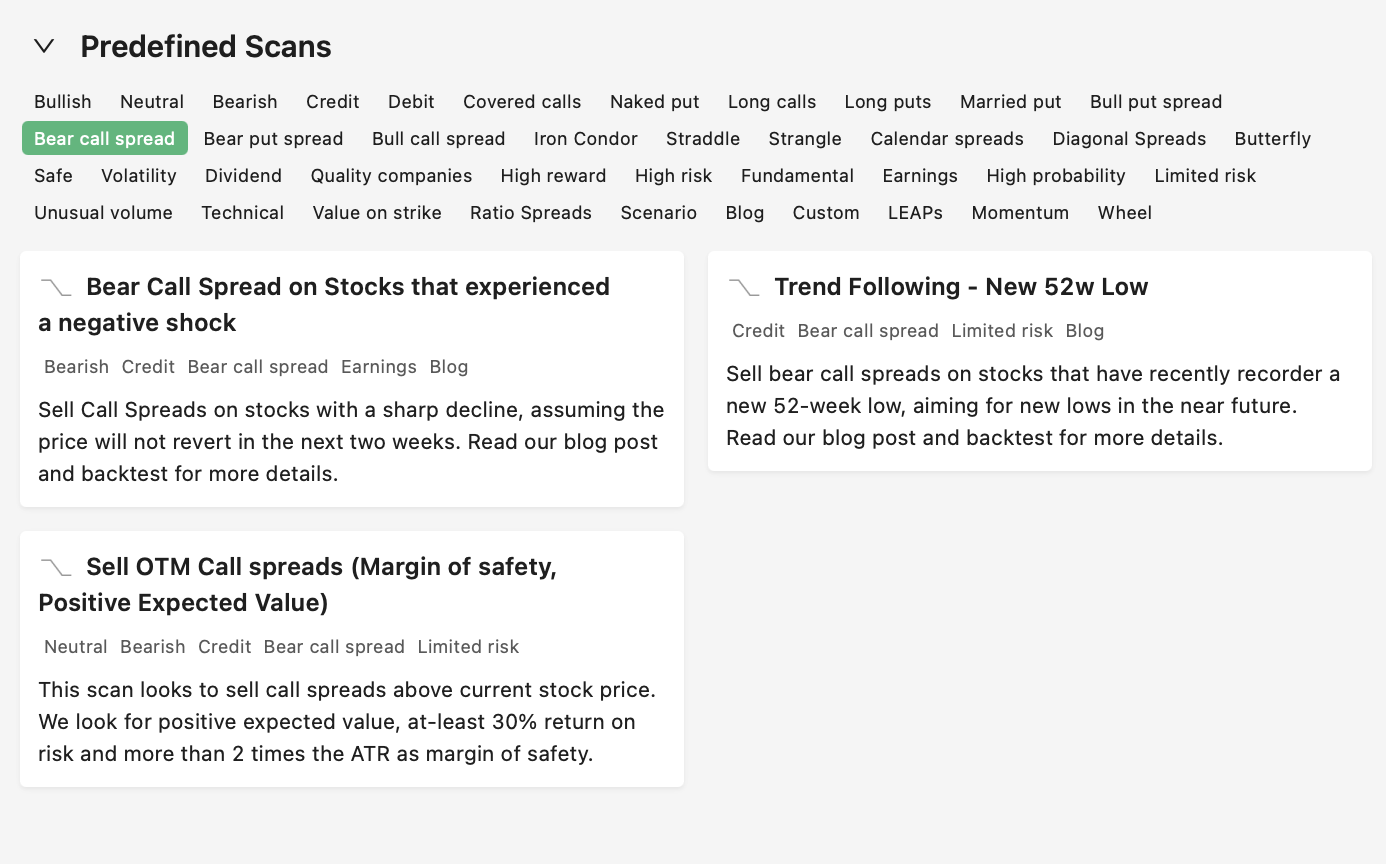
Both scan types benefit from the underlying quality filters built into Samurai’s options screener. Rather than surfacing credit spreads on low-quality or thinly traded stocks, the results are limited to names with sufficient liquidity, reasonable fundamentals, and option chains that support clean execution.
Refining Results with Volatility and Fundamentals
Once a set of credit spread candidates appears, traders can refine further by layering on volatility and fundamental filters. IV Rank is particularly useful here. A credit spread on a stock with an IV Rank above 50 means the options are priced above their median level for the past year, which generally favors premium sellers.
Comparing implied volatility to realized volatility adds another layer of insight. When IV is significantly higher than what the stock has actually been delivering in terms of movement, the market may be overpricing the risk. This creates a natural edge for credit spread sellers who are collecting premiums inflated by fear rather than by actual volatility.
Fundamental filters help avoid names that might look attractive on a volatility basis but carry hidden risks. A stock with elevated IV because of deteriorating earnings or a looming debt issue is not the same as a strong company experiencing a temporary spike in uncertainty. Filtering for quality, whether through predefined tags or custom criteria, keeps the focus on setups where assignment or adverse moves are manageable.
Managing Credit Spreads After Entry
Screening is only the first step. Once a credit spread is placed, ongoing monitoring determines whether the trade reaches its full potential or needs adjustment. The options screener can help here as well, since the same volatility and probability data used to find the trade can be used to evaluate whether conditions have changed.
If implied volatility drops after entry, the spread may reach its profit target faster than expected. If the underlying moves toward the short strike, the probability of profit decreases and a decision about rolling or closing becomes necessary. Tracking these metrics inside a structured platform avoids the common trap of holding spreads too long or exiting too early based on emotion rather than data.
Final Thoughts
Credit spreads are a core income strategy, but their effectiveness depends on finding the right setups at the right time. Screening the entire options market with structured filters removes the guesswork and ensures that each trade is backed by favorable probabilities, appropriate volatility conditions, and quality underlying companies.
An option scanner built for multi-leg strategies brings this process together in a single workflow, making it easier to identify, compare, and execute credit spreads with consistency and discipline.
Start your free trial today (no credit card required) and see how Option Samurai helps traders screen for credit spreads with greater clarity, structure, and confidence.
Crypto World
SanDisk (SNDK) Stock Soars as Susquehanna Sets Bold $2,000 Price Target
Key Highlights
- Susquehanna’s Mehdi Hosseini increased SNDK’s price target to $2,000 from $1,000, suggesting approximately 30% upside potential
- The stock has surged 3,685% in the past year and 554% in 2024 alone
- Multiple Wall Street firms issued upgrades following impressive Q3 results, with price targets between $1,000 and $1,800
- The company’s commitment to allocate 50% of free cash flow to stock repurchases may boost earnings by approximately 10%
- An insider transaction saw a director offload $870,300 in shares on May 8, close to the $1,600 peak
SanDisk (SNDK) shares experienced a modest decline on Monday, yet the stock continues to rank among the market’s top performers, having climbed 3,685% over a 12-month period and 554% since the start of the year.
Trading around $1,543, the stock sits just beneath its 52-week peak of $1,600.
Mehdi Hosseini from Susquehanna doubled his price objective for SNDK to $2,000 — up from his prior $1,000 forecast — while maintaining a Buy recommendation. This updated target represents approximately 29.62% potential appreciation from present price levels.
Hosseini’s adjustment followed SanDisk’s impressive fiscal third-quarter financial results, which led Susquehanna to revise its projections higher “across the board.”
Wall Street Piles On Bullish Calls
Susquehanna isn’t alone in its optimistic stance. Multiple prominent investment banks issued their own positive revisions following the earnings announcement.
BofA Securities increased its price objective to $1,550 from $1,080 with a Buy rating, noting that SanDisk exceeded both top-line and bottom-line forecasts. Cantor Fitzgerald pushed even higher to $1,800, pointing to a revised business model structure encompassing five clients that account for more than 33% of SanDisk’s projected NAND bits in 2027.
Bernstein SocGen Group established a $1,700 target, emphasizing robust earnings, forward guidance, and an advantageous pricing landscape. Jefferies adjusted its target to $1,400, emphasizing long-term customer contracts stretching past 2030. RBC Capital increased its forecast to $1,000, highlighting exceptional NAND results and gross margins nearing 80%.
Across 13 analysts surveyed, the consensus Wall Street recommendation stands at Strong Buy, with three Hold ratings. The mean price target registers at $1,409.06.
Analysts have taken particular notice of SanDisk’s strategy to allocate 50% of free cash flow toward share repurchases over the coming two years. Hosseini projects this initiative alone could generate approximately 10% earnings enhancement.
Hosseini further observed that roughly one-third of SanDisk’s fiscal 2027 revenue stream is already secured through contracts, with comparable revenue visibility anticipated for fiscal 2028.
Insider Transaction at Peak Levels
Not all stakeholders are maintaining full positions. Director Necip Sayiner disposed of 579 SNDK stock on May 8 at $1,503.11 per share, generating $870,300 in proceeds. Following this sale, he retains direct ownership of 2,900 shares, according to a Form 4 filing submitted to the SEC on May 11.
InvestingPro characterizes the stock as overvalued at present prices, noting a P/E ratio of 52.88.
Monday’s trading volume reached 7.31 million shares, falling short of the three-month daily average of 17.78 million.
The third-quarter earnings release that ignited the series of analyst upgrades demonstrated SanDisk surpassing both revenue and earnings per share projections, while its fourth-quarter outlook also exceeded Wall Street consensus — despite a sequential decline in bit shipments.
Cantor Fitzgerald drew attention to $42 billion in NAND bit commitments and $11 billion in financial assurances connected to the revised customer arrangements as additional confirmation of sustained long-term revenue streams.
-

 Crypto World4 days ago
Crypto World4 days agoHarrisX Poll Found 52% of Registered Voters Support the CLARITY Act
-

 Fashion4 days ago
Fashion4 days agoWeekend Open Thread: Marianne Dress
-

 Crypto World5 days ago
Crypto World5 days agoUpbit adds B3 Korean won pair as Base token gains Korea access
-

 NewsBeat5 days ago
NewsBeat5 days agoNCP car park operator enters administration putting 340 UK sites at risk of closure
-

 Fashion16 hours ago
Fashion16 hours agoCoffee Break: Travel Steam Iron
-

 Tech2 days ago
Tech2 days agoAuto Enthusiast Carves Functional Two-Stroke Engine from Solid Metal
-

 Fashion1 day ago
Fashion1 day agoWhat to Know Before Buying a Curling Wand or Curling Iron
-

 Politics11 hours ago
Politics11 hours agoWhat to expect when you’re expecting a budget
-
 Politics3 days ago
Politics3 days agoPolitics Home Article | Starmer Enters The Danger Zone
-

 Business3 days ago
Business3 days agoIgnore market noise, India’s long-term story intact, say D-Street bulls Ramesh Damani and Sunil Singhania
-

 Crypto World7 days ago
Crypto World7 days agoUAE Free Zone Deploys Blockchain IDs to Verify Registered Firms
-

 Tech1 day ago
Tech1 day agoGM Agrees To Pay $12.75 Million To Settle California Lawsuit Over Misuse Of Customers’ Driving Data
-
 Crypto World6 days ago
Crypto World6 days agoBlackRock CEO Larry Fink Discusses a New Asset Class
-

 Entertainment5 days ago
Entertainment5 days agoSarah Paulson Called Out For Met Gala ‘Hypocrisy’
-

 Crypto World5 days ago
Crypto World5 days agoRobinhood says Wall Street is building onchain
-
Sports6 days ago
NBA playoff winners and losers: Austin Reaves is not loving Lakers vs. Thunder matchup, but Chet Holmgren is
-

 Entertainment5 days ago
Entertainment5 days agoGeneral Hospital: Ric & Ava Bombshell – Ric’s Massive Secret Exposed!
-
 Entertainment6 days ago
Entertainment6 days agoBold and Beautiful Early Spoilers May 11-15: Steffy Revolted & Liam Overjoyed!
-

 Tech6 days ago
Tech6 days agoApple and Samsung are dominating smartphone sales so thoroughly that only one other company makes the top 10
-

 Fashion5 days ago
Fashion5 days agoThe Best Work Pants for Women in 2026










You must be logged in to post a comment Login