Crypto World
Blockchain Identity Management Solutions for Risk-Free Operations

Identity today sits at the center of nearly every digital interaction, including onboarding customers, approving transactions, accessing services, and ensuring compliance. Yet most identity systems enterprises rely on were designed for a different era.
They are centralized, fragmented, and vulnerable. With the digital ecosystems expanding, their weaknesses are becoming harder to ignore. Data breaches, identity fraud, duplicate identities, and verification delays are no longer occasional problems; they are recurring business risks.
It is exactly the reason why enterprises are actively exploring blockchain identity management solutions as a structural upgrade, not a technological experiment. The reason behind this is that identity is no longer just an IT concern. It is a business-critical asset.
What’s Broken in Traditional Identity Systems
Many organizations still operate with legacy identity frameworks built on siloed databases and third-party verifiers. These models introduce several vulnerabilities.
Centralized Data Silos
Traditional identity systems store sensitive user data in centralized repositories. These become prime targets for cyberattacks. One breach can expose millions of identities, damaging trust and triggering regulatory consequences. For enterprises, this means financial loss, reputational damage, and compliance scrutiny.
Repetitive Verification Processes
Users often verify their identity multiple times across services. This creates:
- Poor user experience
- Higher onboarding costs
- Longer verification cycles
Enterprises lose conversions when onboarding feels slow or intrusive.
Limited User Control
In most traditional systems, organizations control identity data, not users. This, in turn, increases privacy concerns and reduces transparency. Modern consumers increasingly expect control over how their data is used.
Fraud & Identity Theft
Centralized databases make identity manipulation easier. Synthetic identity fraud and credential theft continue to rise globally. For enterprises, this directly impacts fraud management costs and regulatory risk.
Compliance Complexity
Regulations such as KYC, AML, GDPR, and data localization laws require strict identity handling. Managing compliance across jurisdictions becomes complex and costly.
Identity as a Revenue Enabler, Not Just a Security Layer
Traditionally, identity systems were viewed as compliance & security necessities and cost centers rather than value drivers. However, blockchain identity management solutions change that perspective. With verifiable, user-controlled identity frameworks, organizations can unlock:
- Faster customer onboarding
- Reduced KYC friction
- Cross-platform identity reuse
- Lower fraud-related losses
- Personalized digital services
This, in turn, plays a significant role in transforming identity from a back-end obligation into a front-end business enabler.
For instance, fintech platforms can onboard users in minutes instead of days. Healthcare systems can share verified credentials without repeated paperwork. Marketplaces can reduce fake accounts and chargebacks.
In other words, strong identity infrastructure improves revenue efficiency, not just security. Forward-looking enterprises now treat digital identity as part of their growth stack, not just their compliance stack.
Want to Fix Loopholes in Traditional Identity Systems with Blockchain?
How Blockchain Identity Management Changes the Model
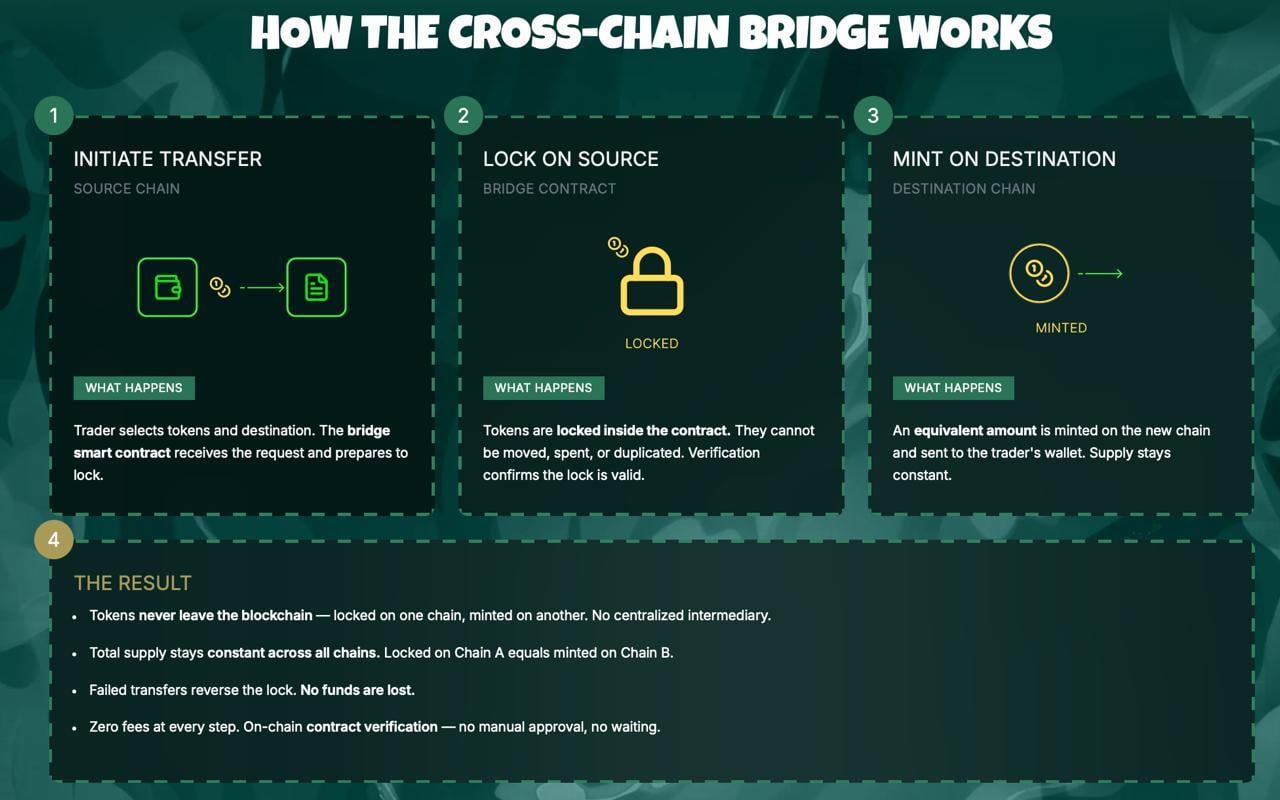
Blockchain introduces a decentralized and tamper-resistant identity framework. Instead of relying on a single authority, identity verification becomes distributed, secure, and verifiable.
Decentralized Identity Storage
Data is not stored in one central database. Instead, blockchain enables distributed identity references with cryptographic security. This plays a significant role in reducing breach risk. Even if one node is compromised, the system remains secure.
Self-Sovereign Identity (SSI)
Users have complete control over their identity credentials. They decide what to share and with whom. Enterprises verify credentials without storing excessive personal data, which readily improves privacy compliance and builds user trust.
Tamper-Proof Records
Blockchain records cannot be altered retroactively. Verification history remains fully transparent and reliable, thereby reducing the chances of fraud and simplifying the overall audit process.
Faster Verification
Reusable credentials allow verified identities to be shared across platforms. This helps accelerate the onboarding process while lowering operational costs.
Smart Compliance
Blockchain can embed compliance logic into identity flows. KYC or AML checks can be verified instantly through trusted credentials, reducing repetitive checks.
Real Business Value for Enterprises
Blockchain identity management solutions are not just about security upgrades. They drive measurable business benefits.
Reduced Fraud Losses
Tamper-resistant identity systems lower fraud risk and prevent duplicate identities.
Faster Customer Onboarding
Streamlined verification reduces drop-offs and improves conversion rates.
Lower Compliance Costs
Automated verification reduces manual review and regulatory complexity.
Stronger User Trust
Privacy-centric identity models resonate with modern consumers.
Trust translates to retention.
Interoperable Identity Ecosystems
Identity credentials can work across partners, platforms, and regions, enabling collaboration.
Where Do Enterprises Need to Be Careful?
Adopting blockchain identity requires strategic planning. Here are a few of the most common mistakes committed by enterprises:
- Over-engineering early stages
- Ignoring regulatory nuance
- Poor integration with legacy systems
- Focusing on tech instead of user experience
Identity management transformation should be phased and goal-driven, which is exactly where enterprises need to be cautious.
Why Choosing the Right Digital Identity Solutions Provider Matters
A full-scale blockchain identity management solution touches:
- Security architecture
- Compliance frameworks
- User experience design
- Infrastructure scalability
- Integration layers
Enterprises should understand that it is not a plug-and-play deployment. A capable digital identity solutions provider understands regulatory environments, enterprise infrastructure, and decentralized identity frameworks. Moreover, it is essential to note that poorly designed identity systems create friction rather than trust.
Final Thoughts
Traditional identity systems are showing structural cracks in a digital-first world. On the other hand, blockchain identity management solutions offer a path toward secure, user-centric, and scalable identity ecosystems.
Enterprises adopting it are not just fixing loopholes; they are future-proofing their digital interactions. Antier, as a trusted digital identity solutions provider, works with organizations to design and implement blockchain-based identity systems that align with security, compliance, & user expectations. It is because in the digital economy, trust begins with identity.
Crypto World
Iran’s Telegram ban backfired, stoking crypto concerns

The Iranian government’s bid to shutter Telegram in the country appears to have backfired, as millions of users find workarounds to stay online through privacy-centric tools and VPNs, according to Telegram founder Pavel Durov.
In a post on X, Durov said Tehran’s attempt to clamp down on the messaging app “years ago” has instead fueled a broader wave of circumvention. He noted that tens of millions of Iranians remain connected via VPNs and similar technologies, and he highlighted a cross-border effect as VPN-driven connectivity accelerates in Russia as well.
“The government hoped for mass adoption of its surveillance messaging apps, but got mass adoption of VPNs instead. Now, 50 million members of the digital resistance in Iran are joined by over 50 million more in Russia.”
Decentralized technologies—ranging from blockchain-based messaging to encrypted, distributed networks—are increasingly pitched as a way to counter state-imposed online restrictions and surveillance, offering users a path to private communications even when central authorities exert control.
Key takeaways
- Iran’s Telegram ban did not end use; tens of millions continue to access the service via VPNs and related tools, per Pavel Durov.
- The stance has produced a broader migration toward privacy-preserving and decentralized messaging technologies beyond a single app.
- Even as governments restrict access, parallel connectivity channels such as Starlink and device-to-device mesh networks emerge as potential backstops for communication.
- Evidence from protests in Nepal and Madagascar shows spikes in downloads of decentralized messaging apps during periods of social unrest, underscoring demand for censorship-resistant tools.
- For investors and builders, the episode highlights a growing divergence between regulatory attempts to control information flow and a user base willing to adopt privacy-native infrastructure at scale.
Regulatory push, user resilience
Iran’s January 2026 nationwide internet blackout, enacted amid escalating protests and ongoing regional tensions, marked a decisive move to curb online mobilization. While the blackout remains in effect, residents retain some access through alternative means—most notably satellite-backed networks such as Starlink, which the government has not fully blocked—and through local, privacy-forward apps capable of wading through censorship filters.
Among the most discussed workarounds is BitChat, a messaging application built to operate over Bluetooth and mesh networks. BitChat turns each participating device into a relay node, effectively stitching a communications mesh that can bypass traditional networks and satellite backbones. Its decentralized design aims to keep conversations flowing even when centralized infrastructure is restricted.
The broader ecosystem around decentralized technologies is also expanding to address similar scenarios elsewhere. BitChat’s architecture has drawn attention for its potential to offer an alternative communication channel when internet access is compromised. The project’s technical approach and practical uses were detailed in public repositories and whitepapers, illustrating how mesh networking can complement or substitute conventional connectivity in crisis conditions.
Decentralized messaging in the crucible of unrest
The wave of protests that swept across Nepal in 2025 and 2026 brought a notable surge in interest for censorship-evading communication tools. Cointelegraph reported a sharp uptick in BitChat downloads in Nepal during the social-media crackdown, described as a period when the government’s grip on information intensified. In the same breath, Nepalese protests were described as having a transformative political effect within the month, with the government reportedly toppled by demonstrators in that period.
Similar dynamics were observed in Madagascar, where a related surge in decentralized messaging adoption accompanied political turbulence. These patterns illustrate a practical use case for privacy-preserving and distributed communications during periods of blackout and unrest, rather than a speculative tech experiment.
Proponents argue that the trend signals more than isolated incidents. As governments seek to regulate or disable centralized platforms, users appear to gravitate toward tools that improve resilience, privacy, and autonomy. This shift aligns with a broader discourse in the crypto and decentralized tech communities about building communications layers that remain accessible despite state-level interference.
What this means for markets, users, and builders
The episode offers a tangible case study in how regulatory pressure can inadvertently accelerate adoption of decentralized and privacy-first technologies. For traders and investors, the takeaway is not a call for quick price moves but a recognition that demand for censorship-resistant communications could expand alongside ongoing geopolitical frictions and regulatory crackdowns in various regions.
For developers and infrastructure builders, the narrative underscores several priorities: enhancing the reliability of offline and mesh-based communications, improving the security and usability of decentralized messaging, and developing interoperable layers that can bridge traditional networks with privacy-focused protocols. The convergence of encrypted messaging with crypto-inspired incentives and governance mechanisms could shape new kinds of platforms that prioritize user sovereignty and resilience over centralized control.
While the exact regulatory responses and technological adoption timelines remain uncertain, the Iranian case—paired with parallel developments in Nepal and Madagascar—highlights a clear, growing demand for alternatives that keep people connected when conventional networks falter.
As the situation evolves, watchers should monitor how governments respond to a populace that increasingly expects and deploys private, censorship-resistant channels. The next developments could redefine how citizens, developers, and policymakers think about online rights, access, and the role of decentralized technology in everyday communication.
Source references and ongoing reporting from Cointelegraph and related coverage underscore the continuity of this trend as it unfolds across regions facing varying degrees of internet control and regulatory pressure.
Crypto World
Telegram Has Been Downloaded Over 50M Times in Iran, Despite Ban: Durov

The Iranian government’s attempt to block the Telegram messaging application in the country has backfired, as users find ways to circumvent national firewalls and online controls, according to Telegram co-founder Pavel Durov.
“Iran banned Telegram years ago,” Durov said on Friday; however, tens of millions of users in the country have managed to access the application via virtual private networks (VPNs) and other similar tools, he added.
VPNs route web traffic through servers distributed around the globe to mask the true Internet Protocol (IP) addresses of users and obscure their locations. This allows individuals with VPN access to bypass national online restrictions. Durov said:
“The government hoped for mass adoption of its surveillance messaging apps, but got mass adoption of VPNs instead. Now, 50 million members of the digital resistance in Iran are joined by over 50 million more in Russia.”

Decentralized technologies like blockchain, crypto and encrypted messaging applications can mitigate or neutralize state-imposed online restrictions and surveillance infrastructure, promoting individual liberty, proponents of decentralized technology say.
Related: Global turmoil pushes uptake of decentralized messengers, social media
Users turn to decentralized alternatives amid online blackouts
The government of Iran imposed a nationwide internet blackout in January 2026, amid growing protests and civil unrest, which is still in effect due to the ongoing war between Israel, the United States and Iran.
Residents in the country can still access the internet through Starlink, a satellite-based network, or communicate via BitChat, a messaging application that uses Bluetooth radio waves to form a mesh network between devices.
BitChat’s mesh network transforms each device into a relay node that transfers data to other devices running the application within range, bypassing online and satellite-based systems entirely.

The government of Nepal imposed a social media ban in September 2025 amid growing protests, causing a spike in BitChat downloads.
Bitchat was downloaded over 48,000 times in Nepal the week of the social media ban, and the government of Nepal was toppled by protestors that same month.
The application recorded a similar download spike in Madagascar amid protests, which also occurred around the same time as the political revolution in Nepal.
Magazine: Did Telegram’s Pavel Durov commit a crime? Crypto lawyers weigh in
Crypto World
Bitcoin Faces Liquidation Risk Amid Falling Volume and Rising Shorts
Bitcoin leverage rises as spot demand weakens across markets. Negative funding rates reflect stronger short positioning pressure. Institutional accumulation offsets declining retail spot activity.
Bitcoin traded near $67,150 as derivatives activity shaped short-term price behavior. Market data showed declining spot volume alongside rising leverage metrics. The trend pointed to increased reliance on futures positioning rather than direct buying.
Falling Spot Volume Signals Weak Market Participation
Bitcoin recorded a steady drop in daily spot volume over recent weeks. Activity declined from 42,026 BTC on March 17 to 35,590 BTC on April 2. The contraction reflected weaker participation in direct market transactions.
At the same time, open interest declined from $23.33 billion to $21.26 billion. However, the drop remained smaller compared to spot volume losses. This difference suggested that derivatives exposure stayed relatively elevated.
The estimated leverage ratio increased from 0.2207 to around 0.225. The shift indicated that traders relied more on leveraged positions. As a result, price action became less dependent on organic spot demand.
Rising Short Pressure and Liquidation Risk Build
Funding rates remained mostly negative across perpetual futures markets. This pattern showed that short positions dominated trader sentiment. It also indicated persistent pressure against upward price movement.
Liquidity zones below the current price appeared closer than those above. This structure increased the probability of downward moves in the short term. Long positions faced a higher risk of forced liquidations under such conditions.
At the same time, analysts highlighted that leverage-driven markets tend to amplify volatility. Price swings often accelerate when liquidation cascades begin. Therefore, short-term direction remained sensitive to derivatives positioning.
Institutional Demand Contrasts with Weak Spot Activity
Despite weaker spot demand, institutional buying activity continued to absorb supply. Exchange reserves dropped by 66.3K BTC over the past 30 days. The decline reflected ongoing accumulation outside public trading venues.
Over-the-counter transactions accounted for 92.1% of recent flows. In contrast, regular market volume contributed only 7.9% during the same period. This imbalance showed that large buyers dominated current demand trends.
Broader macroeconomic uncertainty still influenced market stability. External shocks could quickly push assets back onto exchanges. Such shifts may increase available supply and trigger rapid price adjustments.
Market Structure Reflects Mixed Signals
Bitcoin’s current structure combined strong institutional accumulation with weak retail participation. This mix created uneven support across different market segments. It also increased reliance on leveraged trading activity.
At the same time, declining spot demand limited organic price growth potential. Derivatives markets continued to play a larger role in price discovery. This dynamic added complexity to short-term market direction.
Overall, the market showed signs of fragility despite ongoing accumulation. Liquidity positioning and leverage trends suggested elevated risk levels. As a result, near-term movements remained vulnerable to sudden shifts.
Crypto World
Solana’s Drift Floats Airdrop After $285 Million Hack, Faces Backlash

Solana-based perpetual futures exchange Drift Protocol is facing mounting scrutiny following the catastrophic $285 million exploit it suffered this week.
The backlash is being driven by a highly speculative recovery strategy and suspicious post-hack token movements.
Drift Team Linked Wallet Shifts Over $2 Million Tokens
On April 4, blockchain analysis platform Onchain Lens reported that a wallet linked to the Drift team deposited 56.25 million DRIFT tokens into centralized exchanges Bybit and Gate after the hacking incident. The tokens were valued at $2.44 million.
Transfers to exchanges are typically interpreted as a sign of potential selling activity. The timing has added to the concern, with the token falling to an all-time low of $0.03343 over the past 24 hours.
The move has drawn significant scrutiny from the community because it comes while the project is still dealing with the fallout from the hack.
That has made the transfer of internal funds to secondary markets during a severe liquidity crisis especially contentious. It has also raised fresh concerns about possible asset flight and complicated efforts to rebuild user trust.
On April 1, North Korean attackers hacked Drift Protocol, draining around $280 million. This slashed the platform’s total value locked from $550 million to about $230 million as of press time.
The April 1 attack ranks as the largest decentralized finance hack of 2026 so far. The fallout has continued to spread, with reports indicating that the number of affected projects has now risen to 20.
The breach also stands as the second-largest hack in Solana’s history, behind only the $326 million Wormhole exploit in 2022.
Solana Co-Founder Proposed Recovery Strategy
Amid the ongoing crisis, Solana co-founder Anatoly Yakovenko publicly suggested that Drift could survive by executing an “airdrop” of IOU tokens.
This mirrors the strategy employed by the centralized exchange Bitfinex following its $72 million hack in 2016.
Yakovenko said a core engineering team could rebuild the platform and use the IOU tokens to eventually make affected users whole.
Market analysts, however, point to major structural differences between the two cases.
Bitfinex benefited from a dominant position in centralized trading and recurring fee revenue during a historic crypto bull market. This allowed the exchange to gradually buy back its debt tokens at a 1:1 ratio.
Drift, by contrast, operates as a decentralized exchange in a highly competitive and fragmented market. With user confidence damaged and liquidity cut roughly in half, the protocol lacks the predictable revenue base needed to support an unsecured debt instrument.
Analysts have also argued that describing such an issuance as an “airdrop” risks obscuring the core issue. Without a solvent protocol and a viable path to repayment, the tokens would carry no intrinsic value beyond speculation on a future recovery.
The post Solana’s Drift Floats Airdrop After $285 Million Hack, Faces Backlash appeared first on BeInCrypto.
Crypto World
Ripple (XRP) Down 7% This Month, Investors Move to Taurox (TAUX) as Pre-KYA Opening Might Start a Rally

XRP trades near $1.32 with growing optimism. April has historically been XRP’s strongest month, posting average returns of 24.8% since 2014, driven by the upcoming CLARITY Act Senate Banking Committee markup scheduled for the second half of the month.
Taurox, an AI-driven trading protocol, positions itself to harness this momentum through autonomous agents that deliver diversified, risk-managed yields to stakers in the evolving crypto landscape.
Navigating XRP Volatility with Taurox’s Structured Edge
XRP’s recent price action remains choppy despite partnerships and regulatory progress, with escrow unlocks adding supply pressure and exposing holders to frequent 20-30% whipsaws. Taurox counters this by pooling deposits of USDT, BTC, or XRP into a shared trading pool. Global developers, quants, and AI engineers build the agents that generate proportional net profits.
Each agent is capped at 2% of pool AUM, while KYA tiers enforce conservative, moderate, or aggressive risk levels. Enforced Sharpe ratios ≥1.5 and maximum drawdowns below 15% deliver smoother returns than direct exposure or traditional 2% management-fee hedge funds.
Pre-KYA Registration Now Open: Accelerating the Agent Pipeline
Taurox has hit a major roadmap milestone ahead of schedule by opening the Pre-KYA Registration Table. This early entry point allows developers, quants, and AI builders to pre-register their trading agents before the full Know Your Agent (KYA) system goes live. Pre-registered agents receive priority Proving Ground access, jumping the queue for faster entry and earlier capital allocation.
They also qualify for bonus incentives from the dedicated Agent Creator Fund, which represents 10% of total TAUX supply. Anyone with a working trading strategy can now position their agent among the first wave in the Taurox ecosystem.
Taurox Mechanics: On-Chain AI Trading with Rigorous Controls
Taurox aggregates staker deposits into a central trading pool and mints txTokens at the prevailing NAV per share, starting at $1.00. The protocol maintains a 15% stablecoin reserve buffer and directs the remainder to agents through a performance-weighted algorithm. Agents execute strategies like statistical arbitrage via on-chain vaults or CEX sub-accounts.
Every agent must complete the Proving Ground until achieving statistical significance, such as ≥500 trades. Risk controls include 2% daily stop-losses, 5% single-trade limits, and 5% pool-wide drawdown halts. KYA tiers enforce strategy fidelity in a fully verifiable decentralized quant framework.
TAUX Tokenomics: Fixed Supply and Burn-Driven Scarcity
TAUX has a fixed 2 billion non-mintable supply. Unlike traditional hedge funds, Taurox charges no upfront fees and takes only 5% of gross profits, purchased as TAUX on-market. Of this revenue, 30% is permanently burned, while 70% supports the DAO treasury.
The remaining 95% distributes progressively to stakers and creators, with stakers receiving 80% at 0-20% returns, tapering to 43% above 300%, based on high-water mark net profits. Allocations include 40% for presale, 15% for staking rewards, 10% for agent incentives, and 5% for the team with 6-month cliff vesting.
Taurox Presale: Asymmetric Entry with Strong Fundamentals
Taurox Presale has entered Phase 4 and surpassed $950K raised. TAUX currently trades at $0.018. Phase 4 investors stand to gain almost 4.5x at listing when TAUX launches at $0.08. If Taurox reaches its $1B target pool, these investors could see up to 103x returns as TAUX reaches $1.85. A $500 investment today would grow to about $2,220 at listing and nearly $28,000 when TAUX hits $1 valuation.
The presale features a 1-month cliff and 20% monthly unlocks from months 2-5, enabling immediate staking while limiting early sell pressure. Combined with 30% fee burns and progressive splits, it offers strong upside for short and long-term horizons.
Taurox as the Decentralized Quant Layer
Taurox blends AI autonomy, strict on-chain risk controls, and deflationary mechanics into next-generation DeFi. Its global agent ecosystem and burn-driven scarcity position it for sustainable growth as the crypto space evolves.
Learn More
Buy TAUX: https://taurox.io
Whitepaper: https://docs.taurox.io/
Official Telegram: https://t.me/tauroxlabs
Official X/Twitter: https://x.com/TauroxProtocol
Disclaimer: This is a Press Release provided by a third party who is responsible for the content. Please conduct your own research before taking any action based on the content.
Crypto World
Bitcoin tends to outperform gold and stocks after global shocks, Mercado Bitcoin finds
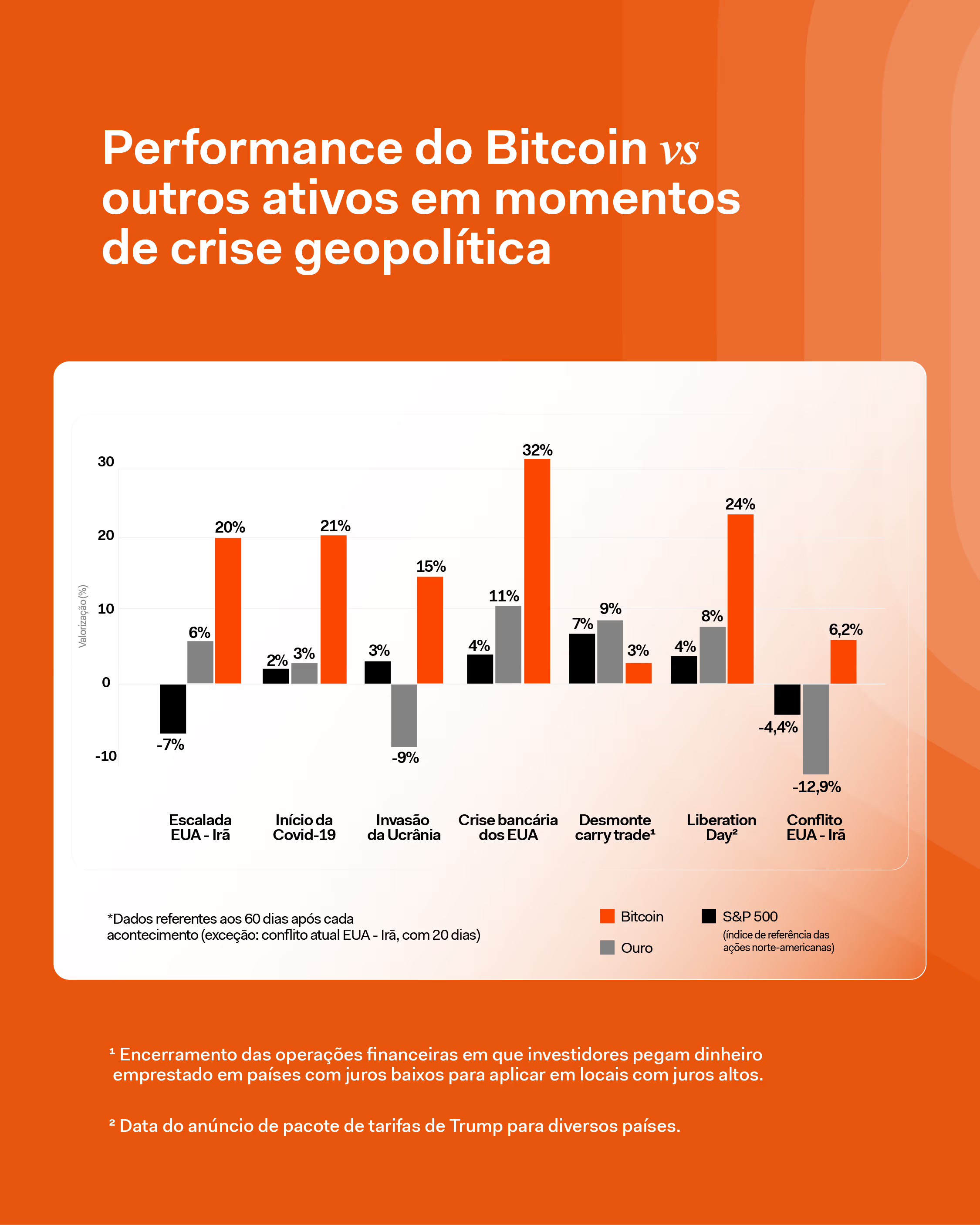
Bitcoin tends to outperform traditional safe haven assets like gold in the two months following major global crises, according to new analysis from Brazilian crypto exchange Mercado Bitcoin.
The study, led by Rony Szuster, head of research at the Latin American crypto platform, examined 60-day windows after economic or geopolitical shocks such as the COVID-19 outbreak and U.S. tariff escalations. Bitcoin posted stronger returns than both gold and the S&P 500 in each of the periods analyzed.
In April last year, after the Trump administration announced sweeping tariffs, the price of bitcoin jumped 24% over the following 60 days. Gold rose 8%, and the S&P 500 gained 4%, the firm found.
A similar pattern emerged at the onset of the COVID-19 pandemic in March 2020, when BTC rose 21%, while the other assets trailed.

Szuster cautioned that judging bitcoin’s performance too soon after a crisis can be misleading.
“It’s like watching the first few minutes of a movie and thinking you already know how it ends,” he said. “In moments like this, investors sell positions to reduce risk or raise cash, and even defensive assets can fall.”
That happens as investors scramble for liquidity, yet bitcoin has consistently bounced back, the firm found. The pattern appears to be repeating in the current U.S.-Iran conflict, where bitcoin is the only one of the three assets in positive territory so far, according to Szuster.
Data backs this up. Since the war started, bitcoin has risen by more than 2.2%, from around $65,800 to $67,300 at the time of writing. Gold, the traditional safe haven, has meanwhile dropped around 11%, while the S&P lost 4.4% of its value in the index’s steepest monthly drop since 2022.
Despite its volatility, bitcoin was the best-performing asset over the past decade, he added.
Read more: Bitcoin’s recent crash to $60,000 warned stocks first – now they’re following
Crypto World
ProductionReady’s Jimmy Song Pitches Case for Conservative Bitcoin Software
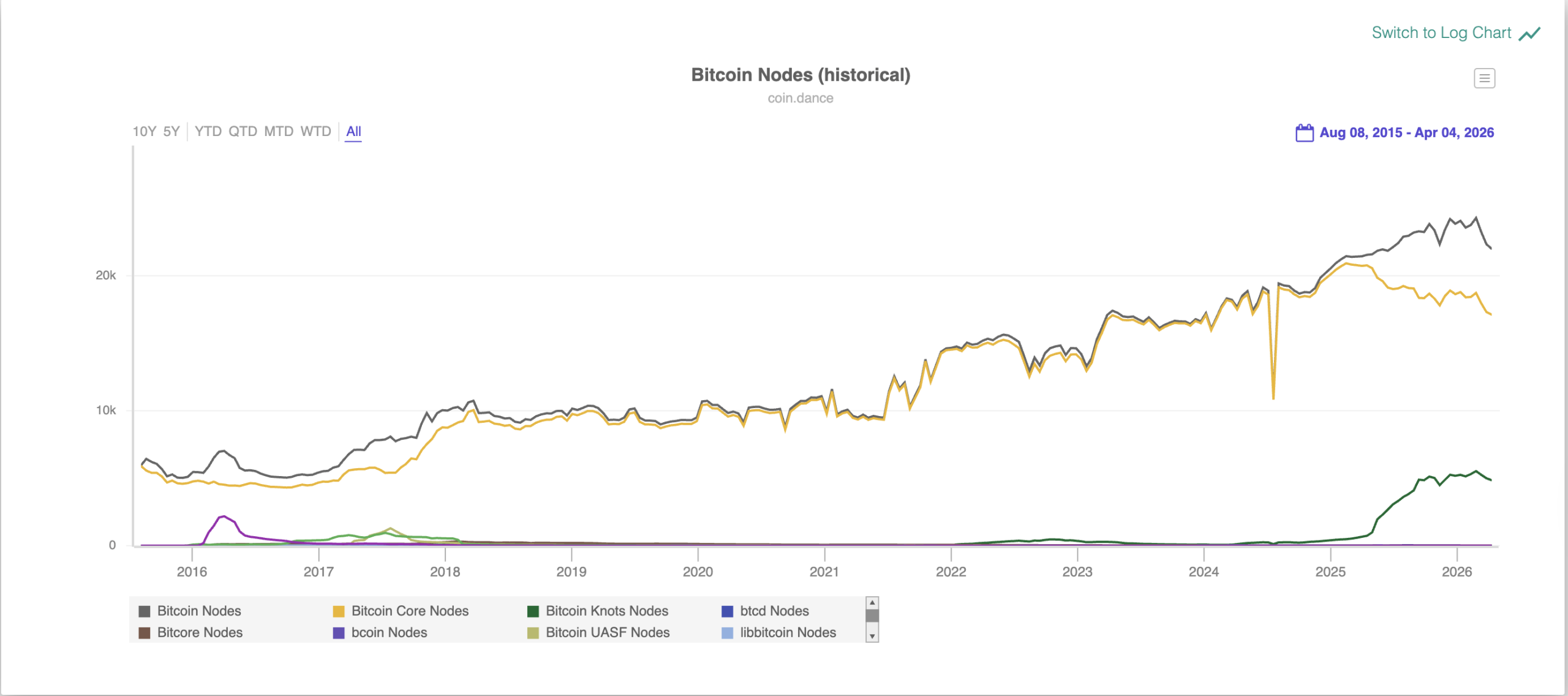
The Bitcoin (BTC) network needs a “conservative” Bitcoin client node software implementation to preserve its monetary properties and strengthen network decentralization, according to Jimmy Song, co-founder of ProductionReady, a non-profit organization funding open source Bitcoin node software development and education.
The organization has a “bias” against significant code changes, unless there is “overwhelming” community support for the change, Song told Cointelegraph.
“The general principle is: if you’re not sure a change makes the money better, don’t make it,” he said.

ProductionReady expects to restore the 83-byte OP_Return data limit for arbitrary, non-monetary information in Bitcoin transactions, he said, adding that keeping node storage costs down by limiting arbitrary data is essential to network decentralization. He said:
“The more self-sovereign Bitcoin users are, the more decentralized and resilient the network becomes. That means keeping the cost of running a node low enough for ordinary people to do it.
“When storage and bandwidth requirements grow, fewer people verify for themselves, and the network centralizes by default. A conservative client takes that tradeoff seriously,” Song continued.
Maximizing nodes and making them accessible to the average user hardens the Bitcoin network, reducing the chances of cheating by submitting false transactions or a few actors colluding to centralize the network.

Related: 72% of subsea cables would need to fail to impact Bitcoin, study shows
Bitcoin Core 30 removes the OP_Return data limit, sparking major pushback
Node storage and onchain spam became hot-button topics in 2025 after Bitcoin Core developers unilaterally changed the 83-Byte data limit in Bitcoin Core version 30, the latest major upgrade to the reference implementation for Bitcoin node software.
The limit was changed to 100,000 bytes despite significant pushback from the Bitcoin community. For context, the proposal to change the limit received about 4 times as many downvotes as it did upvotes, according to the proposal’s GitHub pull request page.
Bitcoin Core 30 went live in October 2025, triggering a historic surge in the number of Bitcoin nodes running Bitcoin Knots, an alternative implementation of the node client software.

There are 4,746 Bitcoin Knots nodes, representing over 21.7% of nodes on the network, according to Coin Dance.
Only about 1% of the network was running the Knots software in 2024 before the decision to remove the OP_Return function was announced.
Magazine: Bitcoin may face hard fork over any attempt to freeze Satoshi’s coins
Crypto World
XRP Price Prediction: Can XRP Price Ever Reach The $100 Dream ? While Pepeto Delivers the True 150x Entry
The xrp price prediction crowd has chased the $100 target for years. Goldman Sachs just revealed a $153.8 million position spread across four XRP ETFs, making it the largest institutional holder by a factor of six, according to 24/7 Wall St. The CLARITY Act faces its make-or-break Senate markup in late April, and if it passes, Standard Chartered projects $4 to $8 billion in fresh ETF inflows that could push XRP toward $3.50 to $6, according to Yahoo Finance.
Yet XRP sits at $1.30, and reaching $100 still demands a $5.7 trillion market cap, larger than the entire crypto market combined. While XRP holders wait for a target that math alone cannot justify, one presale built by the team behind a $7 billion token is offering 150x at a price most investors have never seen this low. This piece breaks down the xrp price prediction reality and where the return math actually lives.
Goldman Sachs Loads XRP ETFs as CLARITY Act Approaches Binary Vote
24/7 Wall St reported that Goldman Sachs holds $153.8 million across Bitwise, Franklin Templeton, Grayscale, and 21Shares XRP ETFs, while CoinMarketCap confirmed $11.4 billion in XRP left Binance on April 2, tightening exchange supply to multi-month lows. The partnership validates XRP’s institutional case, but a validated use case and a profitable entry from $1.30 remain entirely different calculations.
The XRP Price Prediction Ceiling vs the Pepeto Floor: Where Returns Actually Live
Pepeto: The Presale That Converts XRP’s Validation Into Actual Holder Wealth
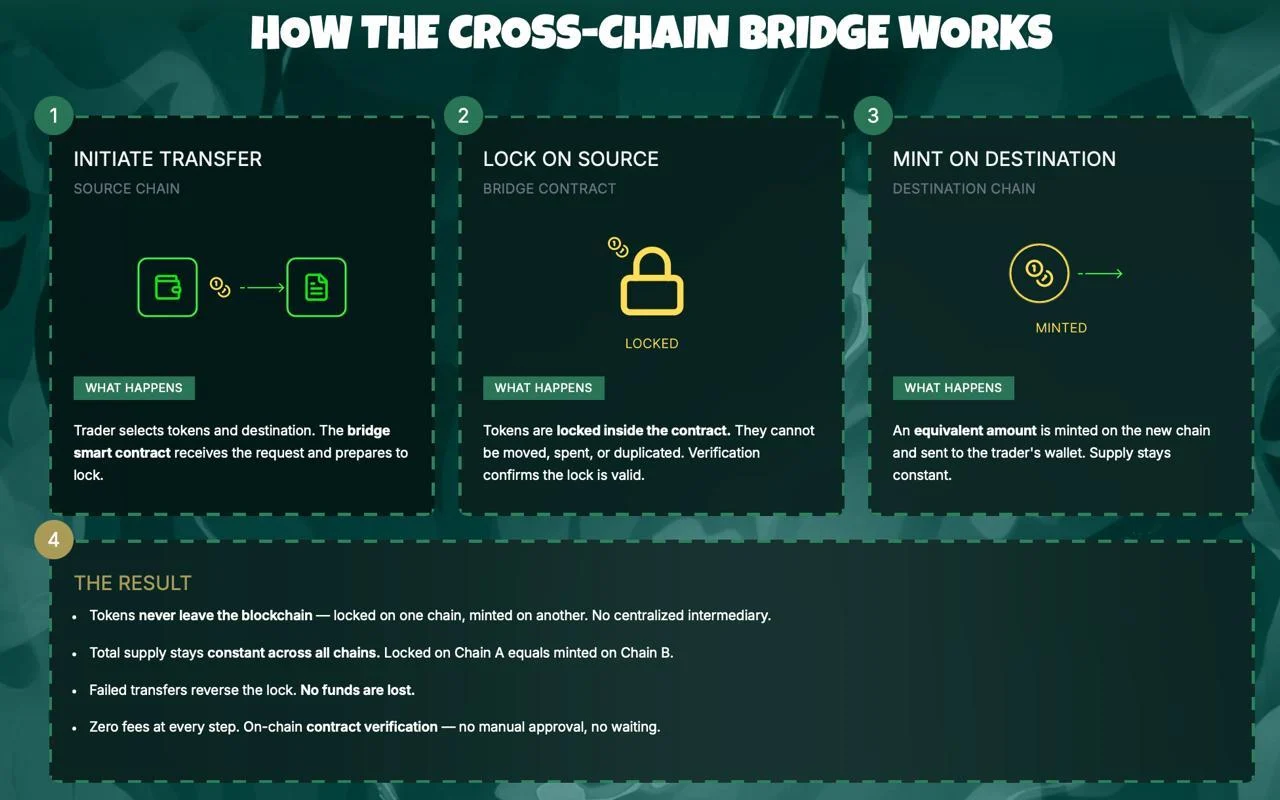
Finding a presale that combined meme token pricing with functional exchange infrastructure used to be nearly impossible. Most projects offered dashboards, chatbots, or lending tools that thousands of competitors already shipped. Pepeto changed the equation by delivering a full exchange ecosystem with zero-fee trading, a cross-chain bridge spanning Ethereum, BNB Chain, and Solana, and 188% APY staking that compounds daily.
These tools are not placeholder features on a roadmap. The exchange processes volume across three blockchains simultaneously, and every component runs on smart contracts verified through a SolidProof audit. That foundation keeps Pepeto in structural demand regardless of whether the market trends up or down, because utility drives volume in every condition.
At $0.0000001862, a $1,000 entry secures billions of tokens. The original Pepe shares the same 420 trillion total supply and peaked at an $11 billion market cap with zero products behind it. Reaching that valuation turns a $1,000 position into approximately $150,000, a 150x return that analysts treat as conservative because Pepeto has the audited exchange, the cross-chain bridge, and the working infrastructure Pepe never built. The cofounder who took Pepe from zero to $7 billion architects this project, and a former Binance executive shapes the listing strategy.
With the Binance listing approaching, these projections mirror BNB’s trajectory from $0.15 at ICO to over $700 once real trading activity powered the token. Staking at 188% APY grows every position daily before listing day. The wealth that changed lives in every prior cycle was captured by wallets that entered infrastructure presales while others hesitated, and Pepeto’s confirmed Binance listing will permanently eliminate this entry along with the 150x math attached to it.
XRP Price Prediction: Why $100 Demands More Capital Than Crypto Has Ever Seen
XRP trades at $1.30 according to CoinMarketCap with an $80 billion market cap. Hitting $100 would require a valuation above $5.7 trillion, exceeding the entire crypto market’s current $2.38 trillion capitalization by more than two times. The bullish xrp price prediction from ChatGPT targets $3.50 to $6 if the CLARITY Act passes in late April, delivering 160% to 340% from current levels, according to 24/7 Wall St.
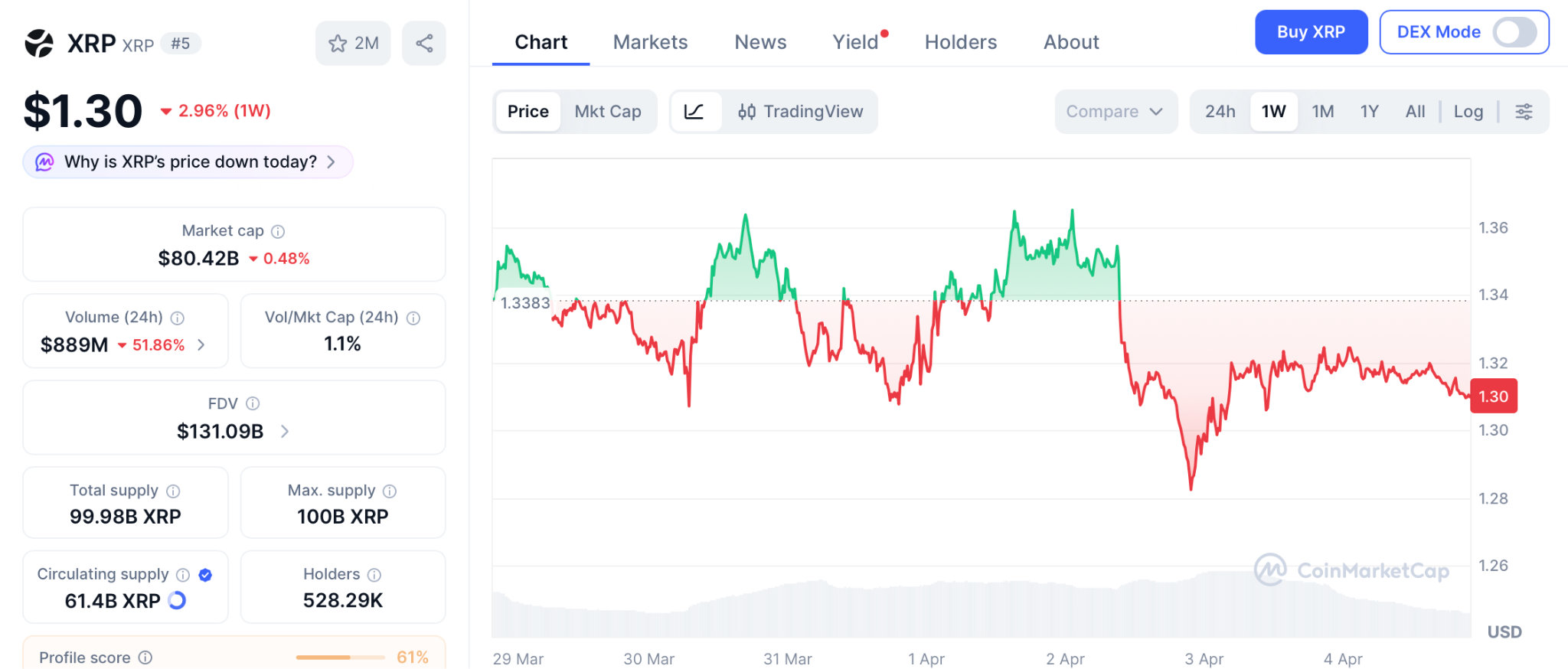
Even reaching $10 demands a $570 billion valuation that rivals Ethereum at its historic peak. The xrp price prediction is constructive long term, but the math confirms the largest percentage returns already happened for holders who entered under $0.20. From $1.30, the upside is measured in percentages while Pepeto measures it in multiples.
Conclusion
Goldman Sachs loaded $153.8 million into XRP ETFs and the token barely moved. That is the ceiling of an $80 billion asset. Pepeto sits at $0.0000001862 with a SolidProof audited exchange, 188% APY staking, and a Binance listing approaching.
A $1,000 entry targets $150,000 at a fraction of what Pepe achieved with nothing. XRP needs $5.7 trillion for $100. Pepeto needs a sliver of what Pepe reached for 150x. The gap is not close. Visit the Pepeto official website and secure the entry that the xrp price prediction will never offer you at this stage.
Click To Visit Pepeto Website To Enter The Presale
FAQs
Is $100 a realistic target for the xrp price prediction?
Reaching $100 requires a $5.7 trillion market cap. Most analysts see $3.50 to $6 as realistic if the CLARITY Act passes.
Why does Pepeto offer stronger return math than XRP from here?
At $0.0000001862 with 420 trillion supply, matching Pepe’s ATH delivers 150x, a multiple XRP at $80 billion cannot produce.
What impact does Goldman Sachs buying XRP ETFs have on price?
Goldman holds $153.8M in XRP ETFs, confirming institutional interest, but XRP remains rangebound until the CLARITY Act advances.
Disclaimer: This is a Press Release provided by a third party who is responsible for the content. Please conduct your own research before taking any action based on the content.
Crypto World
Bitcoin Shorts Face $2.5B Liquidation Risk at $72K Threshold

Bitcoin has struggled to reclaim its recent highs near $75,000, but a move up to $72,000 could trigger a substantial squeeze in the futures market, potentially flushing billions in short bets. With macro headwinds from geopolitics and a fragile risk appetite shaping investor flow, analysts say the next price move could reveal how much of the current downside positioning is leaning on leverage rather than a fundamental shift in demand.
According to data provider Coinglass, a climb to $72,000 from around $67,100 could unleash roughly $2.5 billion in liquidations of Bitcoin short positions. That magnitude underscores how quickly a price rally can reverse a crowded bearish setup, even as bears maintain their leverage-heavy stance amid ongoing macro uncertainty.
Key takeaways
- Liquidation risk at $72,000: Coinglass estimates approximately $2.5 billion in Bitcoin futures short liquidations if price advances to $72,000 from current levels.
- Bear pressure from miners and equities: Miner dispositions, notably MARA selling 15,133 BTC in late March to de-leverage and pivot to AI compute, add to downside momentum alongside a weaker S&P 500.
- Funding signals a bear tilt in leverage: Negative funding rates in BTC perpetual futures point to tepid demand for bullish leverage and potential vulnerability to squeeze-driven moves.
- ETF inflows could re-accelerate a rally: Inflows into U.S. listed BTC ETFs have shown bursts of interest, with around $1.5 billion net inflows over two weeks during a prior period, suggesting catalysts exist for renewed upside if demand returns.
- Geopolitics and macro data as swing factors: Oil’s rally in the wake of the Iran conflict and broader recession concerns shape liquidity and risk appetite, making a break above key levels a noteworthy signal for traders and investors alike.
Macro drivers, miner behavior, and the price framework
The immediate backdrop is fragile: oil prices have surged as geopolitical tensions intensify, elevating logistic costs and pressuring consumer demand. At the same time, equities have shown signs of strain; after peaking near the end of January, the broad market faced a notable drawdown through March, stoking concerns about a potential downturn in growth signals and central-bank policy space.
Bitcoin’s price action has been tethered to these macro currents even as mining dynamics remain a focal point for downside pressure. MARA Holdings, a publicly traded Bitcoin miner, disclosed on March 26 that it liquidated a sizable portion of its Bitcoin holdings—selling 15,133 BTC to reduce debt exposure and reallocate capital toward AI computing. The move underscores how mining profitability and balance-sheet management can feed into broader market sentiment during risk-off periods.
Against this backdrop, the S&P 500’s wobble and the resilience (or lack thereof) of alternative risk assets influence whether BTC can extend a rally. The market’s nerves around economic resilience and central-bank policy endure, with traders pricing in a high probability that the Federal Reserve will hold rates steady in the near term, while maintaining a cautious stance on future tightening or easing. The latest odds from market-implied rate expectations reflect a complex calculus where inflation persistence and growth concerns coexist with policy fatigue.
Liquidity conditions in the futures market add another layer. Bitcoin perpetual futures have shown negative funding rates, a sign that the current demand for long leverage is limited relative to the supply of capital seeking hedges or short exposure. In practical terms, negative funding rates can complicate the path for bulls, especially if liquidity dries up or volatility spikes higher on headlines.
Reflation catalysts: ETF inflows and potential upside triggers
One potential pathway for renewed upside is the return of institutional demand via exchange-traded products. Earlier episodes showed notable inflows into U.S.-listed Bitcoin ETFs, with data tracking net flows hitting material levels over a two-week window. If ETF demand resumes, it could provide an additional incentive for price discovery and help clear the overhead supply that has weighed on BTC around the $70,000–$75,000 zone.
The market has also watched for the resilience of external demand factors that once propelled rapid gains. A strong ETF inflow narrative paired with favorable macro signals could catalyze a broader move, potentially helping Bitcoin reclaim the $72,000 level and set the stage for a deeper test of the prior highs.
Investor attention remains anchored to the balance between macro risks and the crypto market’s own internal dynamics. The market has historically shown that even in the absence of a perfect macro backdrop, a combination of short squeezes, inflows, and stabilizing macro data can kindle a meaningful move higher. The next phase may hinge on whether ETF demand re-accelerates or if macro pressures reassert themselves.
What to watch next
Looking ahead, traders will be watching for any shift in the Iran-related geopolitics, changes in oil pricing, and any new ETF inflows that could re-energize demand. If BTC can clear the $72,000 hurdle with sustained activity, the ensuing price action could attract fresh risk-taking, particularly from funds that have been sidetracked by volatility and funding-rate dynamics. Conversely, persistent macro weakness or renewed risk-off sentiment could prolong the current range or push prices lower, especially if miners continue to adjust balance sheets to manage debt pressures.
For investors and traders, the key takeaway is that the next few weeks may reveal whether current downside risk has been priced in or if a tactical squeeze can unlock a broader rally. Given Bitcoin’s current position around 47% below its all-time high, a decisive move above $72,000 would carry outsized implications for market sentiment, liquidity cycles, and the setup for a possible spring or early-summer bull run.
Readers should stay alert to ETF flow updates, changes in leveraged positioning, and any headline-driven shifts in risk appetite, as these factors tend to precede more substantial moves in the Bitcoin market.
Crypto World
Limited time left to buy BlockDAG at $0.000022 while Pippin dumps and Dogecoin stalls

Disclosure: This article does not represent investment advice. The content and materials featured on this page are for educational purposes only.
BlockDAG stands out among the top crypto gainers with a limited $0.000022 entry price, as the Pippin crypto price drops and the Dogecoin price prediction remains uncertain.
Sentiment across crypto sits at extreme fear right now, with the Fear & Greed Index barely scraping double digits and altcoins absorbing the worst of it. Pippin is a clear example: whale exits hammered the price over 10% in 24 hours, volume dried up, and key support near $0.0427 is now holding by a thread. Dogecoin is in a similar holding pattern, stuck inside a descending triangle after a near-30% slide since February.

Neither coin is broken, but neither is giving traders much reason to feel confident right now. That’s actually the context that makes BlockDAG (BDAG) worth slowing down on. Priority access at $0.000022 closes April 8. CoinMarketCap already shows $0.40. That’s a 39,900% difference. Global listings on BitMart, Coinstore, and P2B open the same day, bringing real exchange exposure. Analysts called $0.30 to $0.40 months ago. That range already happened. Now $0.70 is the number people are watching.
Pippin Plummets 10% Amid Whale Sell-Off
Pippin (PIPPIN), a Solana-based memecoin, has dropped over 10% in the past 24 hours, driven by a whale sell-off and growing bearish sentiment among traders. On March 29, PIPPIN fell 10.52% to $0.0512, while trading volume slid 18% to $40.20 million, reflecting reduced market interest. Analytics from Nansen showed whales cut holdings by 25%, even as the top 100 wallets slightly increased theirs.
Major players, including Solana co-founder Raj Gokal, reportedly rotated into PUNCH, signaling weakening momentum. The Pippin crypto price currently trades near key support at $0.0427, consolidating between $0.047 and $0.0599. If support holds, recovery is possible, but a break could trigger sharper declines.
Overall, short-term bearish pressure continues, and the Pippin crypto price remains volatile, with bulls struggling. Traders are eyeing $0.0467 and $0.0605 for key activity, shaping the Pippin crypto price outlook.
Dogecoin Faces Critical Support as Market Awaits Next Move
The DOGE price is at a critical juncture as the chart compresses within a descending triangle, with highs dropping while support near $0.0886 holds. Since mid-February, DOGE has fallen almost 30%, from $0.1280 to $0.0905, putting pressure on this key level. Analysts note that if support holds, a bounce toward $0.1050 is possible, but a break could drive prices down to $0.0820.

Historical cycles suggest DOGE has repeated accumulation and breakout phases, with prior gains of 190% and 480%. This has traders watching closely. Short-term momentum is mixed, making the Dogecoin price prediction uncertain. Current conditions suggest that Dogecoin price prediction hinges on reclaiming higher ranges, and the next decisive move could shape the broader trend. Overall, the Dogecoin price prediction remains volatile but watchful.
BlockDAG Unveils 85x Price Jump Chance
BlockDAG has emerged as one of the top crypto gainers this year thanks to an exceptional rise in price and a limited-time priority access offer. The current priority access at $0.000022 remains available but only until April 8 which can guarantee at least 85x price jumps as compared to BDAG lowest price on the open market, while today’s CoinMarketCap price reached $0.4, representing a 39,900% increase from Stage 1 and 700% above the listing price.
This massive gap between the entry price and the current market price highlights an opportunity few investors ever encounter. The three-month head start before community deposits open in June allows early participants to secure positions far below market levels.

Global trading opens on April 8, with listings across BitMart, Coinstore, and P2B, exposing BlockDAG to millions of traders worldwide. The combination of limited priority access and broad exchange exposure has accelerated interest and amplified the sense of urgency.
Market analysts had projected the $0.3–$0.4 range, which has already been achieved, and now attention has shifted to $1 prediction for the near future. For those holding priority access at $0.000022, the ROI potential is nearly unimaginable, reaching hundreds of thousands of percent if prices move as predicted.
Network fundamentals support the growth story. Developer engagement continues to rise, mining hardware distribution strengthens the system between April and June, and futures markets add depth to liquidity. The combination of strong infrastructure, early gains, and priority access highlights an opportunity to enter the market at $0.4 or higher, allowing participants to benefit from early positioning.
Final Thoughts
Pippin’s support at $0.0427 is doing a lot of work right now, and whether it holds or breaks will define the Pippin crypto price outlook for the next few weeks. Dogecoin is in a similar wait-and-see spot. The Dogecoin price prediction stays clouded until bulls actually reclaim ground, not just defend it.
BlockDAG is where the math gets interesting. Buying at $0.000022 when CoinMarketCap shows $0.40 is a gap most people stumble across after it closes. April 8 is when global listings go live, and that $0.000022 entry goes with it. Among top crypto gainers this year, few offer a closing window this specific. Specific tends to matter.
For more information, visit the official website, presale, Telegram, and Discord.
Disclosure: This content is provided by a third party. Neither crypto.news nor the author of this article endorses any product mentioned on this page. Users should conduct their own research before taking any action related to the company.
-

 NewsBeat2 days ago
NewsBeat2 days agoSteven Gerrard disagrees with Gary Neville over ‘shock’ Chelsea and Arsenal claim | Football
-

 Business2 days ago
Business2 days agoNo Jackpot Winner and $194 Million Prize Rolls Over
-

 Fashion1 day ago
Fashion1 day agoWeekend Open Thread: Spanx – Corporette.com
-
Entertainment5 days ago
Fans slam 'heartbreaking' Barbie Dream Fest convention debacle with 'cardboard cutout' experience
-

 Crypto World3 days ago
Crypto World3 days agoGold Price Prediction: Worst Month in 17 Years fo Save Haven Rock
-

 Tech6 days ago
Tech6 days agoThe Pixel 10a doesn’t have a camera bump, and it’s great
-
Crypto World4 days ago
Dems press CFTC, ethics board on prediction-market insider trades
-

 Entertainment7 days ago
Entertainment7 days agoLana Del Rey Celebrates Her Husband’s 51st Birthday In New Post
-

 Tech6 days ago
Tech6 days agoAvatar Legends: The Fighting Game comes out in July and it looks pretty slick
-

 Business3 days ago
Business3 days agoLogin and Checkout Issues Spark Merchant Frustration
-

 Sports4 days ago
Sports4 days agoTallest college basketball player ever, standing at 7-foot-9, entering transfer portal
-

 Tech5 days ago
Tech5 days agoEE TV is using AI to help you find something to watch
-

 Tech5 days ago
Tech5 days agoApple will hide your email address from apps and websites, but not cops
-

 Fashion7 days ago
Fashion7 days agoAmazon Sundays: Soft Spring Layers
-

 Politics5 days ago
Politics5 days agoShould Trump Be Scared Strait?
-

 Tech6 days ago
Tech6 days agoElon Musk’s last co-founder reportedly leaves xAI
-

 Fashion5 days ago
Fashion5 days agoThe Best Spring Trends of 2026
-

 Tech4 days ago
Tech4 days agoHow to back up your iPhone & iPad to your Mac before something goes wrong
-

 Crypto World5 days ago
Crypto World5 days agoU.S. rule change may open trillions in 401(k) funds to crypto
-

 Tech5 days ago
Tech5 days agoFlipsnack and the shift toward motion-first business content with living visuals















You must be logged in to post a comment Login