Crypto World
Counterfeit Ledger Devices Found Draining Crypto Wallets Through Supply Chain Fraud

TLDR:
- Counterfeit Ledger Nano S Plus devices use ESP32 chips to steal seeds and PINs in plain text format.
- A fake Ledger Live app passed Mac App Store review and drained over $9.5 million from 50+ victims.
- The fraud spans five attack vectors including Android, iOS, Windows, macOS, and physical hardware.
- Ledger’s genuine check feature fails when hardware is compromised at the supply chain source level.
Counterfeit Ledger hardware wallets are at the center of a growing threat targeting cryptocurrency users worldwide.
A security researcher has documented a large-scale operation distributing fake Ledger Nano S Plus devices through multiple online marketplaces.
The compromised units appear identical to legitimate products but carry entirely different internal hardware. Seeds, PINs, and wallet data are being sent directly to attacker-controlled servers, draining any wallet initialized on the device.
Fake Hardware Hides Malicious Chips and Firmware
The counterfeit devices replace Ledger’s secure element chip with an ESP32 microcontroller. This substitute chip runs modified firmware labeled “Nano S+ V2 1.”
Unlike the genuine secure element, this hardware stores sensitive data in plain text. That data is then transmitted to remote servers controlled by the attackers behind the operation.
Beyond the hardware, the campaign also distributes a fraudulent version of Ledger Live. This fake app is built with React Native and signed using a debug certificate.
It intercepts transactions and sends sensitive user data to multiple command-and-control servers. Users downloading this version have no visible indication that anything is wrong.
The attack spans five separate vectors: compromised hardware, Android APKs, Windows executables, macOS installers, and iOS apps.
The iOS distribution uses Apple’s TestFlight platform to bypass the standard App Store review process. This approach allows the fraudulent software to reach users without triggering typical security checks. Each channel serves as an independent entry point for the same underlying scam.
Ledger’s built-in genuine check feature is designed to verify device authenticity. However, that verification process can be bypassed when the hardware is tampered with at the source.
This makes the point of purchase a critical security variable. Buying from unauthorized sellers removes the only reliable layer of hardware-level verification.
Separate Mac App Store Fraud Drained Over $9.5 Million
Separately, on-chain investigator ZachXBT documented another fake Ledger Live app that passed through Apple’s Mac App Store review. That operation alone drained more than $9.5 million from over 50 victims.
Among those affected was musician G. Love, who lost 5.92 BTC after entering his recovery phrase into the fraudulent application. The app presented itself as the legitimate Ledger companion software.
These two operations together show a clear pattern in how attackers are targeting hardware wallet users. Rather than exploiting firmware vulnerabilities, they are intercepting users before they reach a genuine device.
The fraud happens at the distribution level, not the protocol level. This shift makes user behavior and purchase source more important than ever.
Security best practices remain unchanged despite the evolving tactics. Hardware wallets should only be purchased directly from the manufacturer’s official website.
No legitimate wallet software will ever request a 24-word recovery phrase on screen. Any application asking for seed phrase input is running a scam, without exception.
The broader message from both incidents is straightforward. The hardware itself remains secure when obtained through proper channels.
The vulnerability now lives in the supply chain and software distribution ecosystem. Staying safe requires equal attention to both where a device is bought and how companion software is sourced.
Crypto World
DTCC Integrates Chainlink for Tokenized Collateral Platform
The Depository Trust & Clearing Corporation (DTCC) will integrate Chainlink infrastructure into its collateral management platform ahead of a planned fourth-quarter 2026 launch as it aims to support near real-time movement, valuation and settlement of tokenized collateral across financial markets and blockchains.
DTCC said its Collateral AppChain platform is designed to serve as shared infrastructure for institutions including custodians, triparty agents and collateral managers. The blockchain oracle provider’s technology will automate processes including margining, collateral optimization and settlement.
Nasdaq said that its research found 52% of firms expect to manage live tokenized collateral by the end of 2026. Yet, 70% of the investment banks, custodians, prime brokers and asset managers survey report settlement matching and delivery issues daily, reflecting the reliance on manual processes that continue to challenge efficiency.
The integration is intended to connect collateral agreements with pricing, valuation and asset movement data across markets, with the goal of enabling 24/7 collateral management workflows and improving capital efficiency, in the fourth quarter of 2026, according to DTCC’s announcement.
Chainlink is a decentralized oracle network that connects blockchains to real-world data, enabling smart contracts to function securely and accurately. DTCC currently custodies $114 trillion in liquid assets from stocks to exchange-traded funds.
Earlier this month, the company announced plans to pilot trading of tokenized securities in July ahead of a targeted October launch. The initiative involves more than 50 firms across traditional finance and digital assets, including BlackRock, Circle, Anchorage Digital and Fireblocks.

Source: Chainlink on X
Related: Veteran investor bets on Ethereum as AI agents drive tokenization demand
Biggest market infrastructure firms expand blockchain and tokenization efforts
DTCC’s rollout comes as some of the world’s biggest exchange and market infrastructure companies expand tokenized securities trading and settlement initiatives.
In March, Intercontinental Exchange, the parent company of the New York Stock Exchange, signed an agreement with tokenization platform Securitize to develop infrastructure for tokenized securities trading and onchain settlement. The initiative includes plans for blockchain-based shares and exchange-traded funds designed to support 24/7 trading and instant settlement.
Days earlier, the US Securities and Exchange Commission approved Nasdaq’s proposal to pilot trading of tokenized stocks and exchange-traded funds alongside traditional securities on the same exchange infrastructure. The program will initially cover select Russell 1000 stocks and major index-tracking ETFs.
Also in March, Nasdaq partnered with crypto exchange Kraken and tokenization company Backed to develop infrastructure for blockchain-based equities trading.
Data from RWA.xyz shows tokenized stocks have grown from roughly $511 million in distributed onchain value a year ago to more than $1.4 billion today, an increase of about 180%.
Magazine: Guide to the top and emerging global crypto hubs: Mid-2026
Crypto World
DTCC taps Chainlink for its tokenized collateral platform ahead of Q4 launch


The Depository Trust & Clearing Corporation (DTCC) will use Chainlink infrastructure for its blockchain-based collateral management platform, extending earlier work between the firms into one of Wall Street’s core risk-management functions.
The firm said its Collateral AppChain will use Chainlink’s Runtime Environment (CRE) and data standard to support pricing, valuation, margining, collateral optimization and settlement. The AppChain is a Besu-based blockchain platform facilitating tokenization of assets and real-time, 24/7 collateral management.
DTCC’s platform is aimed at reducing the delays and fragmentation in today’s collateral systems, where assets are often trapped across institutions and time zones. By tokenizing collateral and automating workflows through smart contracts, the system is designed to enable near real-time collateral movement across both traditional financial markets and blockchain networks.
“By leveraging tokenization and distributed ledger technology (DLT) to modernize collateral mobility, our goal is to enable 24/7, near real-time collateral management across global markets and blockchains,” said Nadine Chakar, DTCC managing director and global head of digital assets.
Chainlink will provide the data and orchestration layer. Its technology will help connect asset prices, valuations and collateral movement, while supporting checks on eligibility, margining and settlement instructions. Chainlink is a decentralized oracle network that feeds blockchains with real-world data such as prices, weather, and APIs since blockchains cannot natively access external information on their own.
The platform runs within DTCC’s AppChain setup. DTCC unveiled the tokenized collateral platform last year, saying collateral mobility could become a key institutional use case for blockchain technology.
The Chainlink tie-up builds on Smart NAV, a 2024 pilot in which DTCC and Chainlink tested bringing mutual fund net asset value data onto blockchains.
JPMorgan, Franklin Templeton and BNY Mellon participated in the pilot, which focused on fund tokenization across multiple chains.
DTCC has also been expanding tokenization work beyond collateral. The company said earlier this month that more than 50 firms had joined a working group for The Depository Trust Company’s tokenization service, with limited production trades planned for July and a launch planned for October.
DTCC’s subsidiaries processed $4.7 quadrillion in securities transactions in 2025. Its depository subsidiary provided custody and asset servicing for securities issues valued at $114 trillion.
Crypto World
DTCC to deploy Chainlink-powered 24/7 collateral management network

DTCC to bring Chainlink oracle technology into its Collateral AppChain marks a notable push toward real-time tokenized collateral across traditional markets and digital assets. The move targets a planned fourth-quarter 2026 rollout, with the goal of automating margining, collateral optimization and settlement by linking collateral agreements to live pricing, valuation and asset movement data across both conventional and crypto rails.
DTCC’s Collateral AppChain is pitched as shared infrastructure for custodians, triparty agents and collateral managers. By integrating Chainlink’s data feeds and decentralized oracle capabilities, the platform would support near-continuous collateral flows and enable 24/7 collateral management workflows, potentially tightening capital efficiency for institutions juggling tokenized securities and traditional assets.
Key takeaways
- DTCC plans a Q4 2026 launch for a tokenized-collateral workflow that utilizes Chainlink oracles to connect collateral terms with pricing and settlement data.
- Nasdaq research indicates 52% of firms expect to manage live tokenized collateral by end-2026, while 70% report daily settlement-matching and delivery issues, underscoring persistent inefficiencies in current processes.
- Industry momentum extends beyond DTCC: Intercontinental Exchange is pursuing tokenized securities infrastructure with Securitize, and Nasdaq is advancing tokenized equities on-chain through pilots with Kraken and Backed.
- Tokenized on-chain value for equities has surged, with RWA.xyz reporting on-chain tokenized stocks growing from about $511 million to $1.4 billion over the past year.
- DTCC’s initiative comes as regulators and market infrastructure players increasingly align on 24/7 settlement and cross-asset tokenization, setting the stage for broader adoption of tokenized collateral in mainstream markets.
DTCC’s Chainlink integration: what changes and why it matters
The Depository Trust & Clearing Corporation’s Collateral AppChain project aims to provide a unified, cross-market backbone for collateral management. By embedding Chainlink’s oracle network, DTCC intends to automate critical data flows that currently rely on manual reconciliation and disparate systems. The envisioned workflow would tie collateral agreements to live valuations, asset movement data and cross-market pricing, enabling near real-time margining, collateral optimization and settlement decisions across asset classes and chains.
DTCC’s announcement frames the integration as a strategic move to remove bottlenecks that slow down collateral life cycles in a world where tokenized assets—ranging from tokenized securities to other on-chain representations—operate across both traditional and distributed-ledger ecosystems. The goal is to support continuous collateral management and reduce the capital tied up in risk management frictions, a topic that has grown more urgent as institutions experiment with tokenized securities and on-chain settlement concepts.
The DTCC move sits within a wider wave of activity among market infrastructures pursuing tokenization and on-chain settlement. Earlier this year, Intercontinental Exchange—the parent company of the New York Stock Exchange—announced a collaboration with tokenization platform Securitize to build out infrastructure for tokenized securities trading and on-chain settlement. The plan envisions blockchain-based shares and exchange-traded funds capable of 24/7 trading and near-instant settlement for select assets. The DTCC–Chainlink collaboration highlights a convergence point for the legacy infrastructure and the burgeoning tokenization ecosystem. For investors and asset managers, a functioning, 24/7 collateral regime could shorten settlement cycles, improve liquidity planning and reduce the capital that must be reserved for collateral buffers. In practice, near real-time margining and automated collateral optimization could meaningfully lower funding costs and help institutions scale tokenized portfolios without default or settlement risk rising unchecked.
Several questions linger as the timeline for Q4 2026 approaches. First, the practical rollout will depend on the ability to harmonize legal frameworks, data standards and security practices across a broad coalition of custodians, banks, asset managers and technology providers. While Chainlink’s oracle feeds promise trusted data, the operational risk of cross-chain settlement, latency considerations and potential interoperability gaps will require careful risk management and auditing. Overall, the convergence of DTCC’s collateral platform with Chainlink’s data integrity, alongside a broader surge of tokenization initiatives from ICE, Nasdaq and other market incumbents, points to a more integrated and dynamic post-trade landscape. For market participants, the era of tokenized collateral that can move, be valued and settle continuously across multiple rails may finally be within reach, subject to the usual governance, risk and regulatory guardrails that accompany any major shift in market infrastructure.
What to watch next: the precise milestones and governance models for the Collateral AppChain rollout, the outcomes of ongoing tokenized securities pilots, and how regulators respond as 24/7 settlement concepts gain traction across asset classes.
Broader momentum in tokenized collateral and securities infrastructure
Implications for investors, users and builders
What remains uncertain and what to watch next
Crypto World
CleanSpark stock slides 9% as quarterly earnings miss estimates on bitcoin holdings loss


CleanSpark (CLSK) stock fell over 9.4% in pre-market trading on Tuesday after the U.S. bitcoin mining company reported a widening net loss of $378.3 million for its second fiscal quarter, hit by a significant non-cash adjustment to its digital asset holdings.
The company reported a net loss of $378.3 million for the quarter ending on March 31, a steep increase from the $138.8 million loss reported the same period last year. The loss of $1.52 per share was more than triple the analyst estimate on EPS of a 41 cents’ loss.
The firm’s bottom-hit was mainly driven by a $224.1 million non-cash bitcoin fair value loss, reflecting market volatility.
Quarterly revenue reached $136.4 million, down 25% from $181.7 million year-over-year, the report revealed, missing estimates of $154.3 million.
Despite the dip, CleanSpark expanded its infrastructure, doubling its megawatts (MW) under contract. CEO Matt Schutz said the company is pivoting to commercializing “AI/HPC-applicable assets,” joining a sector-wide shift toward leasing their computing power as AI data centers.
CFO Gary Vecchiarelly cited the firm’s balance sheet as a “competitive advantage, reporting a bitcoin holdings increase of 14% to $925.2 million in respects to last year. Total cash is $260.3 million, while total assets now sit at $2.9 billion with a long-term debt of $1.8 billion.
The estimated average cost of mining one bitcoin was $88,000 in mid-March, according to a Checkonchain difficulty regression model report. The current price of bitcoin hovers just over $80,000, meaning bitcoin mining companies across the board are operating at a loss
These economics have forced bitcoin miners to pivot toward artificial intelligence and high-performance computing infrastructure. The bitcoin mining industry had taken on roughly $70 billion in such contracts by late March.
Read More: Circle raises $222 million for Arc, beats Q1 earnings estimates but misses on revenue
Crypto World
Top Cardano (ADA) Price Predictions as of Late: 10x Explosion on the Way?
Over the past week, Cardano’s ADA has surged 6%, making it one of the best-performing top-15 cryptocurrencies.
Numerous analysts have recently spotted that the asset has been following a similar pattern witnessed during previous bull cycles, suggesting this could be just the beginning of a major rally.
‘Printing by the Plan’
Earlier this month, ADA came close to reclaiming the $0.30 mark, reaching its highest level since mid-March. It currently trades around $0.27, while its market capitalization remains above $10 billion.
The asset is often among the most talked-about cryptocurrencies and becomes the subject of price predictions. One popular analyst who recently touched upon the matter is JAVON MARKS. The X user claimed that ADA continues to maintain a similar structure to that observed in 2021 and shows “signs of strength.” They set a target of $2.91, meaning that the price could be gearing up for a whopping 10x pump.
Prior to that, Sssebi opined that ADA had been consolidating over the past few months, as it did towards the end of 2024, which was later followed by a price increase above $1.30. That said, the analyst believes a surge above $1 is still in play this year.
For their part, Vuori Trading argued that ADA is still “printing by the plan” and sits in a “strong buy level.” The analyst envisioned a staggering jump to as high as $14, occurring sometime between Q3 2027 and Q1 2028.
Ali Martinez has also given his two cents lately. He emphasized the importance of the $0.25 support zone, noting that it has repeatedly acted as a major inflection point for the token.
For instance, in January 2023, ADA bounced off $0.25, resulting in an 88.27% jump over the following weeks. In September that year, this level again served as firm support, sparking a 243% surge.
More Bullish Signals
ADA’s Relative Strength Index (RSI) also supports the bullish case for further price increases. The ratio of the technical analysis tool has plunged to 22, indicating the asset has entered oversold territory and could be gearing up for a move north.

The RSI measures the speed and magnitude of recent price changes and provides traders with vital information about potential price reversal points. It runs from 0 to 100, and conversely, anything above 70 is interpreted as a warning for an impending pullback.
The post Top Cardano (ADA) Price Predictions as of Late: 10x Explosion on the Way? appeared first on CryptoPotato.
Crypto World
Traders believe inflation could near 5% this year
A customer shops for produce at an H-E-B grocery store on May 11, 2026 in Austin, Texas.
Brandon Bell | Getty Images
Prices in April rose at their fastest pace since May 2023. Traders on prediction market platforms think the peak in inflation isn’t here yet.
While the headline annual inflation rate rose 3.8% last month, traders on Kalshi think it is near certain that price increases will rise above 4% in 2026, and give almost two-in-three odds that it goes above 4.5%.
Traders also see an almost 40% chance that inflation will cross 5% this year. That hasn’t happened since February 2023.
That’s significantly higher than Wall Street projections. Economists polled by FactSet forecast that inflation will peak at an average of 3.8% in the current quarter, and fall to 2.8% by the end of the year.
Households, though, are more in-line with the prediction market forecast. A University of Michigan survey released Friday found that consumers see inflation of 4.5% over the next year. On Polymarket, traders believe there is a 50% chance that U.S. inflation rises above 4.5% in 2026.
Headline inflation jumped last month as energy prices soared due to the U.S.-Iran war and the closure of the Strait of Hormuz. But core inflation, which measures the change in prices excluding food and energy, also rose 0.4% in April and 2.8% year-over-year.
Food, materials, shelter, lodging
“The first order effect from the conflict in the Middle East [has] been a shock to oil prices, which [has] translated very quickly to what consumers are paying at the pump, but the next frontier to watch is rising input prices for food and materials,” said Skyler Weinand, chief investment officer at Regan Capital.
While the U.S.-Iran conflict drove energy prices higher, not all of the inflation story can be explained easily by the war. Notably, shelter prices rose 0.6% in April.
Traveling got more expensive too. Airfares jumped 2.8% in the month — as airlines passed through to consumers rising jet fuel prices — and lodging away from home rose 2.4%. Apparel was up 0.6%, albeit a smaller increase than in March.
But the energy shock is what’s driving headline inflation. So long as the strait, a passageway for 20% of the world’s crude oil before the war, remains closed, consumers are unlikely to see immediate relief. U.S. oil prices again crossed $100 a barrel on Tuesday.
Vessels in the Strait of Hormuz, Musandam, Oman, May 8, 2026.
Stringer | Reuters
In fact, a majority of Kalshi traders don’t think maritime traffic through the strait will return to normal until October.
The longer the strait is closed, the greater the risk to prices. Perhaps as a consequence, Kalshi traders now give a more than 50% chance that the Federal Reserve will raise interest rates by July 2027.
“In the first quarter of disruption, the oil supply shock is largely about higher prices,” wrote Seth Carpenter, chief global economist at Morgan Stanley, in a note on Monday. “A second quarter of disruption with continued price escalation would start to diminish the ‘transitory’ nature of the shock… and central banks would have to pivot from delays to policy stance changes.”
— CNBC’s Liz Napolitano contributed reporting
Disclosure: CNBC and Kalshi have a commercial relationship that includes customer acquisition and a minority investment.
Markets shift and headlines fade, but the core principles of building long-term wealth remain constant. Join us for our third CNBC Pro LIVE, where investors of all backgrounds – from financial professionals to everyday individuals – come together to cut through the noise and gain actionable strategies for smarter, more disciplined investing. No matter where you’re starting from, you’ll leave with clearer thinking, stronger strategies. Enter your email here to get a discount code
Crypto World
SUI drops 4.9%, leading index lower
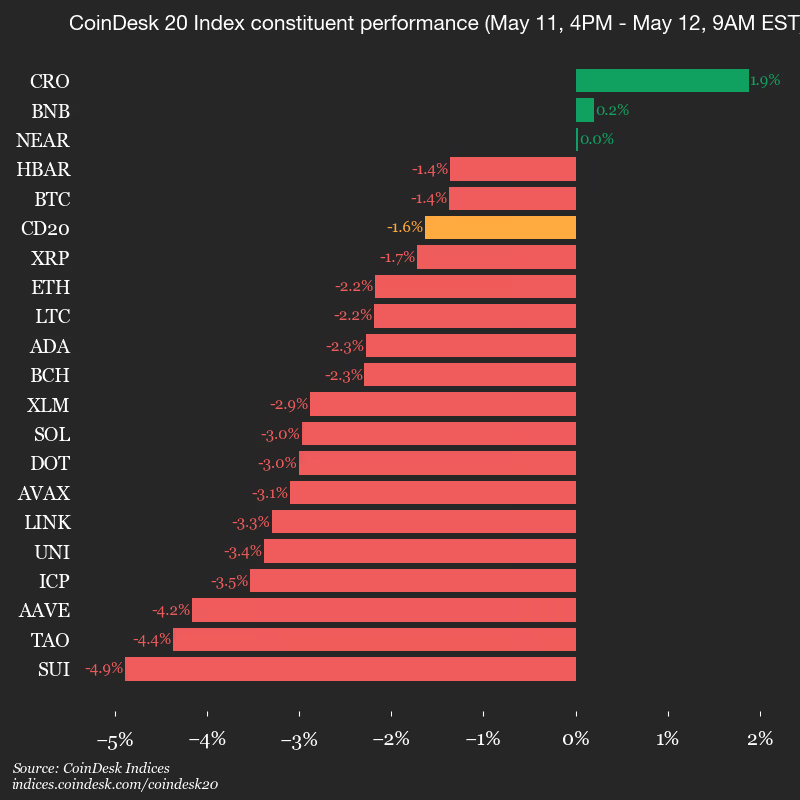
CoinDesk Indices presents its daily market update, highlighting the performance of leaders and laggards in the CoinDesk 20 Index.
The CoinDesk 20 is currently trading at 2196.49, down 1.6% (-36.49) since 4 p.m. ET on Monday.
Three of 20 assets are trading higher.

Leaders: CRO (+1.9%) and BNB (+0.2%).
Laggards: SUI (-4.9%) and TAO (-4.4%).
The CoinDesk 20 is a broad-based index traded on multiple platforms in several regions globally.
Crypto World
Bitcoin Clings To $80K As Altcoins Drag Market Lower


Solana, Cardano and Hyperliquid led the day’s losses as risk appetite cooled across digital assets.
Crypto World
Ronin L2 hard fork completes as gaming chain returns


Ronin L2 migration completed May 12, ending four years as a sidechain after a 10-hour network shutdown.
Summary
- Ronin executed its hard fork at block 55,577,490 on May 12, completing a transition to an OP Stack Ethereum Layer 2 with 10 hours of downtime.
- RON token inflation drops from over 20% to below 1% under a new Proof of Distribution model that rewards active builders over passive stakers.
- Partners including Optimism, Conduit, Boundless, and EigenLayer supported the migration, with EigenDA handling off-chain data availability.
The Ronin L2 hard fork executed at block 55,577,490 on May 12, transitioning the gaming blockchain from an independent EVM sidechain into a full Ethereum Layer 2 built on Optimism’s OP Stack. Sky Mavis co-founder Jihoz announced in the lead-up that the network would enter “hibernation” for approximately 10 hours while the upgrade completed, with no action required from users or players.
Ronin joins Base, Celo, and Fraxtal as purpose-built chains that have chosen to operate under Ethereum’s umbrella through the OP Stack. “Four years ago, we launched Ronin because Axie Infinity needed a faster and more efficient network,” the team said when first announcing the migration. “The time has come to plug back into the mothership.”
What changed in the hard fork
RON token inflation falls from over 20% annually to below 1% under the new Proof of Distribution model, which redirects 90 million RON tokens previously earmarked for passive staking toward the Ronin treasury. Marketplace fees also rise from 0.5% to 1.25%, with sequencer profits from the Layer 2 flowing into the treasury.
EigenDA handles off-chain data availability for the new chain while Ethereum provides settlement and finality. Partners including Optimism, Conduit, Boundless, and EigenLayer supported the migration, with Ronin now composable with Ethereum’s broader DeFi ecosystem.
Any node running older software was cut off once the new chain activated. Ronin confirmed that all games on the network, including Axie Infinity and Pixels, suspended on-chain activity during the downtime and resumed immediately upon completion.
Why the migration happened now
The move addresses the structural concerns that made Ronin vulnerable to the $625 million Lazarus Group bridge exploit in March 2022, the largest DeFi bridge hack in history. Operating as an independent sidechain with only nine validators created a centralised security model that Ethereum Layer 2 settlement directly resolves by inheriting the base chain’s security.
Governance also shifts to token-weighted voting under the new structure, giving RON holders direct input over treasury decisions, buybacks, and DeFi initiatives. Ronin also plans to deploy Uniswap v3 as its canonical DEX post-migration, backed by a $1.5 million liquidity incentive program to bootstrap DeFi activity on the upgraded network.
Crypto World
eToro (ETOR) Stock Declines 4% Despite Strong Q1 Performance and Strategic Expansion
Key Highlights
-
ETOR shares declined 4.81% following release of quarterly results showing revenue expansion.
-
Commodities segment momentum compensated for declining cryptocurrency trading volumes.
-
Strategic Zengo acquisition advances platform’s self-custody digital asset capabilities.
-
Artificial intelligence features and Agent Portfolios enhance platform’s product suite.
-
Platform reached 4.02 million funded accounts while assets under administration expanded.
Shares of eToro (ETOR) experienced downward pressure Tuesday despite the investment platform delivering solid first-quarter financial results and demonstrating product diversification. ETOR closed at $36.88, representing a 4.81% decline, after initially climbing above $41 earlier in the session. Market attention centered on cryptocurrency trading headwinds, artificial intelligence integrations, commodities segment performance, and the strategic Zengo transaction.
Shares Retreat Despite Impressive Quarterly Performance
eToro delivered improved first-quarter profitability as its diversified asset strategy benefited from commodities segment strength. Net contribution expanded 19% on an annual basis to $258 million, versus $217 million in the prior-year period. Management attributed the growth to accelerated commodities trading momentum.
Bottom-line performance strengthened significantly throughout the three-month period, with net income surging 37% year-over-year to $82 million. Adjusted net income posted a 28% increase to $86 million, while adjusted EBITDA jumped 35% to $109 million. Furthermore, adjusted diluted earnings per share came in at $0.91, representing growth from $0.77 in the comparable quarter.
Customer acquisition efforts yielded positive results during the reporting period. Funded accounts grew 12% annually to 4.02 million, driven by increased marketing investments. Assets under administration rose 15% to $17 billion, while the company maintained cash and short-term investments totaling $1.3 billion.
Digital Asset Trading Slows While Commodities Segment Accelerates
Cryptocurrency trading faced headwinds throughout the quarter, notwithstanding eToro’s ongoing digital currency platform development. Management disclosed that April cryptocurrency transactions decreased 32% year-over-year to 2 million. Average invested amounts per cryptocurrency trade fell 22% to $207.
Cryptoasset revenue contracted to $2.15 billion compared with $3.5 billion during the corresponding period last year. However, cryptocurrency-related expenses similarly declined sharply to $2.1 billion. The softer digital asset performance didn’t prevent eToro from delivering enhanced consolidated financial results.
The commodities division emerged as the platform’s primary growth engine. This segment generated approximately 60% of total trading commissions during the three-month period. Additionally, commodities volumes surged nearly fourfold annually following eToro’s introduction of round-the-clock trading for select instruments.
Artificial Intelligence Features, Strategic Acquisition and Platform Development Drive Forward Momentum
eToro maintained its product innovation pace across trading, investment, wealth advisory, and neo-banking services. The platform introduced continuous trading for specific commodities, equities and indices. Management also added Japanese equity access, providing users exposure to securities from 26 global exchanges.
Artificial intelligence capabilities received enhanced focus during the reporting period. eToro unveiled Agent Portfolios and expanded applications within the eToro App Store ecosystem. The platform incorporated xAI’s Grok 4.2 technology into Tori, its artificial intelligence-powered investment advisory tool.
The Zengo transaction continues playing a pivotal role in eToro’s cryptocurrency roadmap. The $70 million acquisition delivered self-custodial wallet capabilities to eToro’s expanding product ecosystem. Management intends to bridge conventional financial services with blockchain infrastructure, prediction markets, and cryptocurrency-native offerings.
-

 Crypto World4 days ago
Crypto World4 days agoHarrisX Poll Found 52% of Registered Voters Support the CLARITY Act
-

 Fashion4 days ago
Fashion4 days agoWeekend Open Thread: Marianne Dress
-

 Crypto World5 days ago
Crypto World5 days agoUpbit adds B3 Korean won pair as Base token gains Korea access
-

 NewsBeat6 days ago
NewsBeat6 days agoNCP car park operator enters administration putting 340 UK sites at risk of closure
-

 Fashion1 day ago
Fashion1 day agoCoffee Break: Travel Steam Iron
-

 Fashion2 days ago
Fashion2 days agoWhat to Know Before Buying a Curling Wand or Curling Iron
-

 Tech3 days ago
Tech3 days agoAuto Enthusiast Carves Functional Two-Stroke Engine from Solid Metal
-

 Politics22 hours ago
Politics22 hours agoWhat to expect when you’re expecting a budget
-
 Politics4 days ago
Politics4 days agoPolitics Home Article | Starmer Enters The Danger Zone
-

 Business3 days ago
Business3 days agoIgnore market noise, India’s long-term story intact, say D-Street bulls Ramesh Damani and Sunil Singhania
-

 Tech2 days ago
Tech2 days agoGM Agrees To Pay $12.75 Million To Settle California Lawsuit Over Misuse Of Customers’ Driving Data
-
 Crypto World6 days ago
Crypto World6 days agoBlackRock CEO Larry Fink Discusses a New Asset Class
-

 Entertainment6 days ago
Entertainment6 days agoSarah Paulson Called Out For Met Gala ‘Hypocrisy’
-

 Entertainment5 days ago
Entertainment5 days agoGeneral Hospital: Ric & Ava Bombshell – Ric’s Massive Secret Exposed!
-
Sports6 days ago
NBA playoff winners and losers: Austin Reaves is not loving Lakers vs. Thunder matchup, but Chet Holmgren is
-
 Entertainment6 days ago
Entertainment6 days agoBold and Beautiful Early Spoilers May 11-15: Steffy Revolted & Liam Overjoyed!
-
 Politics5 days ago
Politics5 days agoSimon Cowell Says He Was ‘Horrible’ To Susan Boyle During BGT Audition
-
 Sports6 days ago
Sports6 days agoUEFA Champions League final schedule, teams, venue, live time and streaming | Football News
-

 Crypto World6 days ago
Crypto World6 days agoRobinhood says Wall Street is building onchain
-

 Tech7 days ago
Tech7 days agoApple and Samsung are dominating smartphone sales so thoroughly that only one other company makes the top 10










You must be logged in to post a comment Login