Crypto World
Ethereum Foundation Launches Audit Subsidy Program for Builders
The Ethereum Foundation announced a joint initiative with audit providers to subsidize security audit costs for Ethereum builders.
The Ethereum Foundation announced an audit subsidy program on Tuesday designed to reduce the cost of security audits for Ethereum builders. The joint initiative with audit providers aims to make security audits more accessible to projects within the ecosystem while strengthening overall security standards.
Security audits are considered a best practice in the Ethereum ecosystem but remain expensive, creating a barrier for many builders. The subsidy program directly addresses this friction point by making professional security reviews more affordable for developers building on Ethereum.
Sources: Ethereum Foundation
This article was generated automatically by The Defiant’s AI news system from publicly available sources.
Crypto World
Moscow Exchange to Launch SOL, XRP, TRX, and BNB Crypto Indexes on May 13

TLDR:
- Moscow Exchange will launch MOEXSOL, MOEXXRP, MOEXTRX, and MOEXBNB indexes starting May 13, 2026.
- Pricing data will be sourced from Binance, Bybit, OKX, and Bitget based on their trading volume share.
- All crypto indexes will update every 15 seconds during trading sessions, replacing the once-daily calculation.
- The exchange plans to expand crypto benchmarks to ten and eventually enable direct crypto trading by 2027.
The Moscow Exchange is set to expand its cryptocurrency benchmark offerings beginning May 13, with four new crypto indexes covering Solana, Ripple, Tron, and Binance Coin.
These additions come as Russia’s largest securities exchange continues building out its digital asset infrastructure. The move also brings updates to existing Bitcoin and Ether indexes.
As with current crypto instruments on the platform, access remains limited to professional investors only.
New Indexes and How They Will Be Calculated
Starting May 13, the exchange will begin calculating and publishing four new indexes: MOEXSOL for Solana, MOEXXRP for Ripple, MOEXTRX for Tron, and MOEXBNB for Binance Coin.
To determine pricing, the platform will draw from four major crypto exchanges based on their share of total trading volume.
Binance will account for 50% of the data, while Bybit will contribute 20%. OKX and Bitget will each supply 15% of the pricing inputs.
This multi-source approach aims to produce more balanced and representative index values across different trading platforms.
Along with the new listings, the frequency of index calculations will also change. From May 13, all digital currency indexes — including the existing MOEXBTC and MOEXETH — will update every 15 seconds throughout the trading day and during weekend sessions. Currently, these indexes are calculated once per day, with results published by 18:00 Moscow time.
The Moscow Exchange has indicated that these indexes may serve as underlying assets for new financial instruments in the future.
However, all crypto-related tools on the platform remain accessible only to professional investors, in line with current Russian regulations.
Expansion Plans and the Road Ahead
Beyond the four incoming indexes, the Moscow Exchange has set a target of reaching ten cryptocurrency benchmarks in total.
The preliminary list for upcoming additions includes Dogecoin (MOEXDOGE), Cardano (MOEXADA), Hyperliquid (MOEXHYPE), and Chainlink (MOEXLINK).
The exchange’s derivatives market product group head, Maria Silkina, confirmed that the platform intends to offer perpetual futures for Bitcoin and Ether at a later stage.
A futures contract obligates the seller to deliver and the buyer to purchase an asset at a set price within a defined period. In settlement futures, profit or loss is calculated based on the difference between the contract price and the strike price.
Russia’s Bank of Russia opened the door for such instruments in May 2025, permitting financial institutions to offer professional investors derivatives, securities, and digital assets tied to cryptocurrency prices. Actual delivery of digital currencies, however, is not permitted under these arrangements.
By November 2025, the exchange had already launched several instruments, including futures on its Bitcoin and Ether indexes, as well as the iShares Bitcoin Trust (IBIT) and iShares Ethereum Trust (ETHA) ETFs. The Moscow Exchange expects to enable direct cryptocurrency trading by early 2027.
Crypto World
Aave asks court to block $71 million crypto seizure tied to North Korea claims


Leading decentralized lending platform Aave has asked a U.S. federal court to block an attempt by victims of North Korean terrorism to seize about $71 million in crypto frozen after last month’s rsETH-related exploit, escalating a dispute that has already split Arbitrum’s governance.
The filing, submitted Monday in the Southern District of New York, seeks to vacate a restraining notice served on Arbitrum DAO by lawyers representing judgment creditors of the Democratic People’s Republic of Korea. Aave argues the assets belong to users of its protocol, not North Korea, and warns that keeping them frozen risks “irreparable harm” to the platform and the broader DeFi ecosystem.
At the center of the fight is 30,765 ETH that Arbitrum’s Security Council froze after the April exploit, when attackers used improperly valued or unbacked rsETH as collateral on Aave, contributing to a situation that the plaintiffs allege resulted in approximately $230 million in ETH being withdrawn from the Aave Protocol. Some of those funds were later intercepted and immobilized on Arbitrum, with plans to return them to affected users as part of a coordinated recovery effort.
The dispute centers on whether stolen property briefly held by hackers becomes their legal property.
The plaintiffs, three sets of judgment creditors holding $877 million in damages awards against North Korea, argue it does — and that’s because the rsETH attackers are widely believed to be linked to Pyongyang’s Lazarus Group, the recovered ether can be claimed against those decades-old judgments.
Aave’s lawyers call that theory “flatly wrong” and warn it would punish blameless users while rewriting basic property law.
Aave’s motion challenges that theory directly. The filing argues the restrained ETH “belong[s] to completely blameless third parties,” not to North Korea, and that even if a thief briefly held the assets, that does not confer legal ownership.
It also disputes the underlying attribution, calling claims that the exploit was carried out by DPRK actors “conjecture” based on unverified reports.
Aave is asking the court to immediately lift the restraining notice, or at a minimum to suspend it while the case is heard.
Aave says keeping the funds frozen via the restraining notice could deepen losses and destabilize DeFi markets already strained by the exploit. The filing warns this “increases the likelihood of cascading liquidations, sustained liquidity outflows, and irreversible changes to user positions,” a chain reaction the industry has been trying to avoid for two weeks.
The outcome could have consequences far beyond this case. If courts allow seized or recovered crypto to be claimed by outside creditors, it could deter future rescue efforts and complicate how the industry responds to hacks, where speed and coordination are often the only tools to limit damage.
Crypto World
Bitcoin rally targets $89K after MACD crossover, but can bulls hold?

Bitcoin (BTC) traded near $81,025 on May 5 after rising 1.56% in the latest session.
Summary
- Ali Charts says Bitcoin’s weekly MACD crossover has already driven a 15% price increase since April 13.
- Bitcoin whales bought 4,527 BTC worth about $362M as ETF inflows supported renewed institutional demand.
- Santiment data shows Bitcoin on-chain activity hit two-year lows despite BTC reclaiming the $80K level.
The asset also recorded an intraday high near $81,204, while trading volume stayed elevated as buyers returned above the $80,000 zone.
The move followed a sharp market reaction to Middle East headlines and renewed demand through U.S. spot Bitcoin ETFs. Bitcoin’s rebound placed the market back near a key technical area watched by traders after several weeks of recovery.
Analyst watches $83,000 resistance
Well-known crypto analyst Ali Martinez asked, “Is Bitcoin heading to $100,000?” He said Bitcoin has shown structural strength since a bullish MACD crossover appeared on the weekly chart on April 13. Since then, BTC has gained about 15%.
Ali Martinez said similar weekly MACD crossovers preceded earlier multi-month moves. He cited a 147% rally after Oct. 23, 2023, a 75% rally after Oct. 14, 2024, and a 35% rally after May 5, 2025.
On the daily chart, Ali placed the 200-day simple moving average near $83,000. He described that area as the main psychological and structural barrier. A daily close above it could open a path toward $89,000, with $94,000 as the next target.
ETF inflows support Bitcoin demand
Spot Bitcoin ETFs added fresh support to the rally. SoSoValue data showed U.S. spot Bitcoin ETFs drew $532 million in net inflows on May 4, after $630 million on May 1. The two sessions brought about $1.16 billion into the products.

ETF demand also suggests that many buyers are entering Bitcoin through regulated market products rather than direct on-chain transfers. Bitcoin’s market dominance also rose above 60%, showing that capital continued to favor BTC over many altcoins during the move.
Ali Charts also reported that whales bought 4,527 BTC in 24 hours, worth about $362 million. That activity points to large-holder demand even as broader network use remains weak.
Network activity sends mixed signal
Santiment data showed Bitcoin’s on-chain activity dropped to two-year lows while BTC moved back above $80,000. About 531,000 Bitcoin wallets made daily transfers, while roughly 203,000 new wallets were created each day.
That creates a mixed setup for the market. Price has risen while fewer users are active on-chain, meaning the rally may depend more on whales, ETFs and derivatives activity than broad retail participation.
Short liquidations also helped the move. Market data cited by traders showed about $270 million in short positions were cleared as BTC moved higher. Better miner returns also reduced near-term selling pressure, with daily mining revenue per petahash rising to its highest level since late January.
Finally, Macro conditions also shifted after the U.S. launched Project Freedom to guide ships through the Strait of Hormuz. Reuters reported that the operation followed weeks of tension around the shipping route, which remains central to global oil flows.
Disclosure: This article does not represent investment advice. The content and materials featured on this page are for educational purposes only.
Crypto World
Solana’s Volatility Hits a Multi-Year Low and The Institutional Trade Explains Why
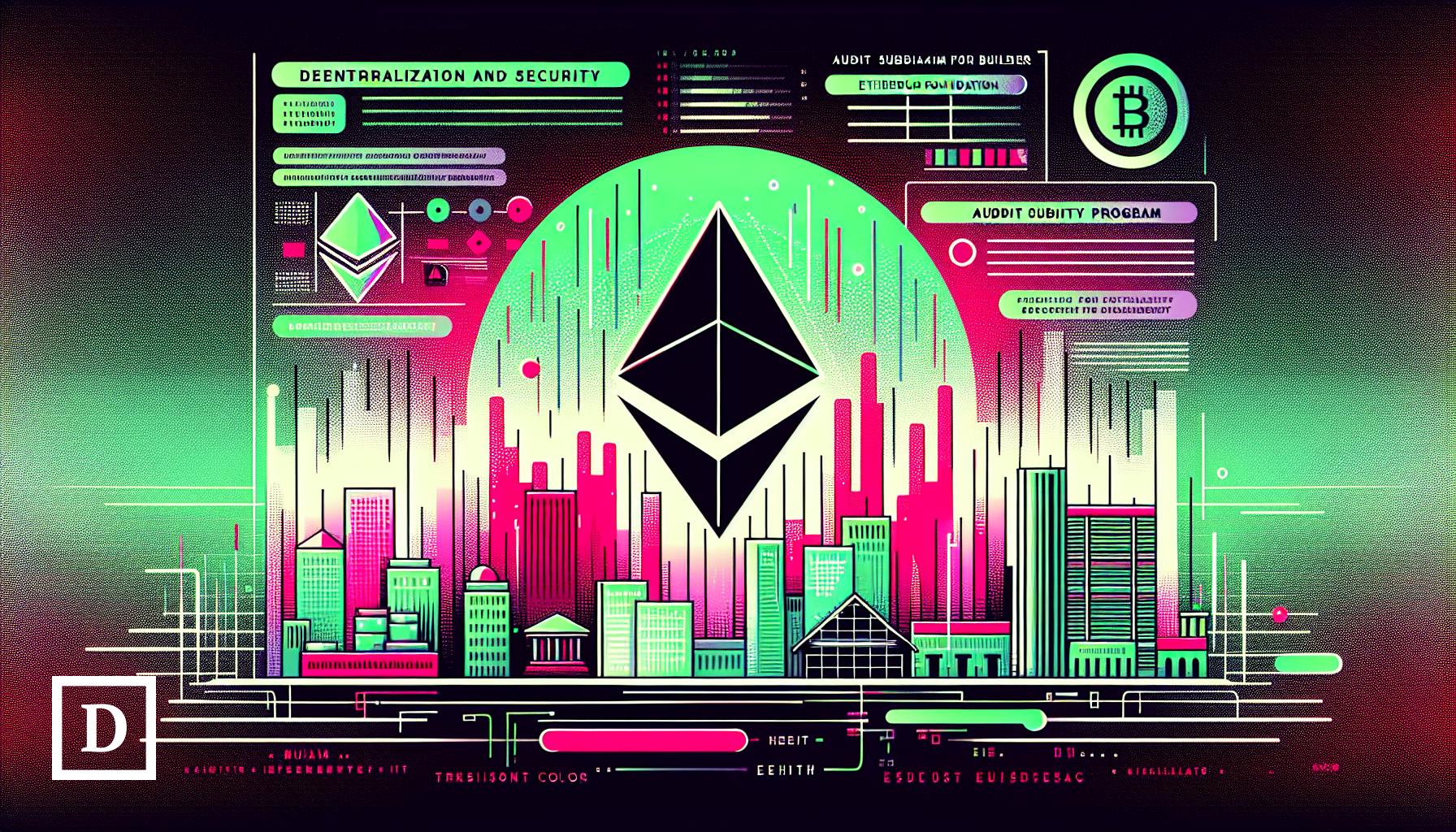
Solana volatility hits a multi-year low, with the 30-day annualized reading dropping to 35.5%. In 2026, it even fell to under 26% for a brief period.
Per BeInCrypto’s exclusive Solana volatility dashboard, this compression marks one of the lowest sustained 30-day prints the indicator has tracked. The cause sits in a structural shift in who owns SOL. The spot ETF, launched in October 2025, has not had a single month of outflows.
Long-term holder supply has expanded sharply over the past two months. The result is a market that has neutralized a textbook breakdown pattern, but capped the upside in the process.
Solana Volatility Crashes to a Multi-Year Low
Per BeInCrypto’s Solana volatility dashboard, the 30-day annualized volatility, a measure of how much SOL’s daily returns deviate from their average over the previous month, sits at 35.5% as of May 4. The 90-day reading is 57.4%. The 200-day is 54.0%.
Want more token insights like this? Sign up for Editor Harsh Notariya’s Daily Crypto Newsletter here.
Compare those numbers to early 2024. The same metrics printed 109% on the 30-day, 92.6% on the 90-day, and 78.8% on the 200-day. Even the early 2026 lows of 58.5%, 50.1%, and 25.8% are now being matched by the active 30-day window.
Two structural facts make the current reading notable. First, the 30-day has dropped below both the 90-day and the 200-day, a configuration that signals the recent trading regime is calmer than the medium-term average.
Second, the SOL price volatility compression has held through a period of macro turbulence, including the April FOMC meeting and the Project Freedom geopolitical risk premium that lifted broader risk assets. Volatility does not compress on its own. Something is absorbing the swings.
The Institutional Trade Explains the Compression
Two strands of ownership data explain the volatility drop.
First, spot Solana ETF flows. The products launched in October 2025 and have not posted a single month of net outflows since. Per SoSoValue data, cumulative inflows have crossed $1.02 billion. Monthly flows have slowed from $419 million in November 2025 to $39.93 million in April 2026, but the cumulative absorption has kept growing every single month.
Second, long-term holder accumulation. Glassnode’s Hodler Net Position Change metric, which tracks accumulation by addresses holding SOL for at least 155 days, expanded from 524,366 SOL on March 8 to 2,588,971 SOL on May 4. That is roughly a five-fold increase in two months.
The combination matters. ETFs absorb supply that does not flow back into the market. Long-term holders accumulate during price weakness rather than during strength. When both forces operate during a flat tape, realized swings compress because the patient cohort is buying every dip and the speculative cohort that drove past volatility no longer dominates flow.
The Solana price chart confirms the same story from a different angle.
Solana Price Levels Show the Trade-Off
Solana has been trading inside a head and shoulders pattern, a bearish reversal setup.
The pattern projects a 19.21% breakdown. But the breakdown has not happened. Sell volume has declined sharply since the mid-February highs, signaling that the seller pressure required to pull SOL through the neckline is structurally absent.

That absence is the institutional bid showing up in price action. Long-term holder accumulation and ETF inflows have possibly absorbed the selling pattern needed to complete its measured move.
The same forces have also capped the upside. SOL has gained roughly 4% over the past 30 days. Bitcoin has gained closer to 20% in the same window. Institutional ownership has stabilized the asset but removed the high-velocity flow that drives speculative breakouts.
The level of math is tight in both directions. Holding $82.86, the 0.382 Fibonacci level, keeps the consolidation intact. A break of $82.86 exposes $77.91. A close below $69.89 confirms the breakdown the pattern projects, but would require a return to higher selling volume, which the current institutional flow data does not support. The full $56.92 target only activates if the institutional thesis breaks.
On the upside, a daily close above $85.93 reopens the path to $90.88. A break above $90.88 neutralizes the head and shoulders structure entirely. Above $97.67, the head’s high, the recovery becomes structural.
The $82.86 to $85.93 range is the line in the sand. A clean break above $85.93 hands the move back to the bulls. A daily close below $82.86 cracks the institutional floor and reopens $77.91. Until volatility expands in either direction, Solana stays caught between two forces that are neither selling nor buying with conviction.
The post Solana’s Volatility Hits a Multi-Year Low and The Institutional Trade Explains Why appeared first on BeInCrypto.
Crypto World
Trump’s Crypto Company Strikes Back: World Liberty Financial Sues Justin Sun for Defamation

Key Takeaways
- World Liberty Financial initiated defamation proceedings in Florida targeting Justin Sun
- Allegations include Sun engaging in short-selling activities and moving WLFI tokens to Binance with intent to manipulate pricing
- Sun had already launched legal action against World Liberty in April over frozen token assets
- The WLFI token experienced a 12% surge following lawsuit disclosure but remains 72% below initial trading levels
- Revenue distribution shows 75% of token sales flowing to the Trump family, generating over $1 billion
The cryptocurrency platform World Liberty Financial, established through a partnership with Donald Trump and his family members, has initiated defamation proceedings against Justin Sun, previously among its most significant financial supporters.
https://twitter.com/coinbureau/status/2051292790693540220?s=20
Court documents were submitted to Florida’s state judicial system on May 4. The complaint accuses Sun of orchestrating a coordinated effort to publicly malign the venture and undermine its credibility.
[[LINK_START_0]]World Liberty[[LINK_END_0]] contends that Sun moved WLFI tokens carrying governance privileges to the Binance cryptocurrency platform. Additionally, the filing asserts he executed short-selling strategies designed to profit from declining token values, coinciding with the public trading debut in September 2025.
Sun has rejected these accusations outright. Through his representatives, he characterized the legal action as “a meritless PR stunt” and expressed confidence in his courtroom defense.
This marks the second round of litigation between these entities. Sun filed his own lawsuit against World Liberty in April through San Francisco’s federal court system. His complaint alleged unauthorized freezing of his token holdings, elimination of his governance participation rights, and threats to permanently destroy the assets.
World Liberty countered that token freezing provisions were explicitly outlined in contractual documentation. The company accused Sun of improper behavior and dismissed his legal challenge as “a desperate attempt to deflect attention.”
The Transformation from Strategic Partner to Courtroom Opponent
Sun’s involvement began as a cornerstone supporter. His financial commitment totaled $45 million across late 2024 and early 2025, earning him an advisory position. He expanded his Trump-related investments by purchasing $100 million worth of Trump’s meme coins in July 2025.
Eric Trump previously praised Sun as “a great friend and an icon in the crypto space.” On September 1, 2025, when WLFI trading commenced, Sun publicly declared his conviction that the project would become “one of the biggest and most important projects in crypto.”
That alliance has now completely deteriorated.
Market Performance and Financial Exposure
Sun’s portfolio includes 4 billion WLFI tokens, presently valued at approximately $264 million. Since trading commenced, the token has plummeted from 31 cents to below 8 cents, representing roughly a 72% depreciation.
The token did experience a temporary 12% price increase after Monday’s lawsuit became public knowledge.
Revenue Distribution Structure
World Liberty’s organizational framework allocates 75% of proceeds from WLFI token transactions to the Trump family. According to Reuters’ financial analysis, the family has already secured more than $1 billion through this arrangement.
In his legal filing, Sun claimed that specific individuals managing World Liberty are exploiting the Trump reputation “to profit through fraud.” World Liberty categorically denies any impropriety.
The Securities and Exchange Commission previously examined Sun regarding allegations that he compensated social media influencers to promote his business interests without proper disclosure. Following the investigation’s closure, Senator Elizabeth Warren raised concerns about potential connections between that outcome and Sun’s financial involvement with Trump’s cryptocurrency enterprises.
Crypto World
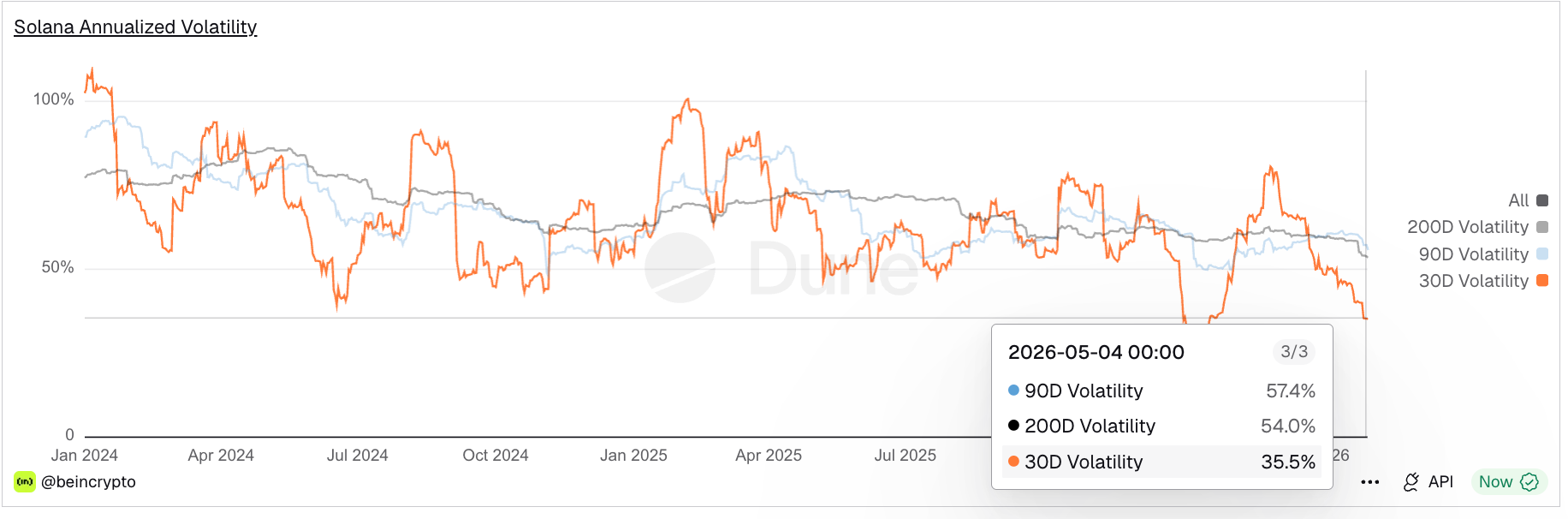
Only 2% of Americans Call the US Economy “Excellent,” Poll Finds
More than 84% of Americans aged 18-24 rate the US economy as bad or terrible, a fresh Generation Lab survey shows, with President Trump and corporate greed sharing most of the blame.
The findings land as Trump’s second term continues to push pro-crypto policy, suggesting economic gloom among Gen Z and younger millennials has not eased despite a friendlier digital asset agenda.
How Americans Feel About Trump’s Economy
Generation Lab surveyed 1,002 Americans aged 18-34 between April 26 and April 29. Among all respondents, 52% rated the economy as bad, and 29% rated it terrible. Just 16% picked good, and only 2% chose excellent.
Follow us on X to get the latest news as it happens

The pattern holds across age brackets. About 84% of 18-24-year-olds rated conditions as bad or terrible. The 25-29 group landed at 81%, while the 30-34s came in at 73%.
Sentiment runs sharper among women, non-binary, and other respondents. Roughly 90% of female respondents chose ‘bad’ or ‘terrible,’ compared with 73% of male respondents.
Meanwhile, among respondents who viewed the economy negatively, responsibility was most often assigned to the President. Overall, 41% attributed poor economic conditions to him.
Within the 18–24 age group, 42% placed the blame on Trump, while 32% cited corporate greed. Among those aged 25–29, opinion was evenly divided, with 33% pointing to Trump and an equal share blaming corporate actors.
The oldest cohort is the harshest. 48% of 30-34-year-olds pin responsibility on Trump, the highest share among any age group surveyed. Just 2% blame former President Biden.
Generation Lab noted that results carry a ±3.1 percentage-point margin of error, with wider margins for subgroup analyses.
Crypto Sentiment Meets Economic Reality
The findings stand out given Trump’s loud support for digital assets since returning to office. His administration backed a Strategic Bitcoin Reserve and signed the GENIUS Act, which regulates stablecoins.
Still, headline pressure remains intense. March inflation rose to 3.3%, while gas prices have surged past $4.45 per gallon since the US-Israel war with Iran began.
Concerns about a potential food shortage and the risk of a recession are also weighing on Americans. Notably, 77% of survey respondents said the United States made the wrong decision in taking military action against Iran.
Subscribe to our YouTube channel to watch leaders and journalists provide expert insights
The post Only 2% of Americans Call the US Economy “Excellent,” Poll Finds appeared first on BeInCrypto.
Crypto World
US Banks Say Stablecoin Proposal Falls Short on Bank Deposits

The banking industry is pushing back against the latest draft of the CLARITY Act, arguing that its language on stablecoin yields does not adequately protect ordinary bank deposits. In a coordinated Monday statement, the American Bankers Association joined several industry groups to say the proposed provisions fall short of the policy goal of prohibiting stablecoin yield in ways that could undermine traditional banking funding models.
The groups—comprising the American Bankers Association, the Bank Policy Institute, the Consumer Bankers Association, the Financial Services Forum and the Independent Community Bankers of America—emphasized that Congress must get the policy right. They warned that any loopholes could enable platforms to offer bank-like interest on crypto balances outside established regulations, thereby threatening the stability of the banking system and the safety of deposits.
Key takeaways
- The CLARITY Act’s current Section 404 is seen by banking coalitions as insufficient to block stablecoin-related yields on crypto platforms, potentially eroding traditional deposit funding streams.
- Lawmakers such as Senators Thom Tillis and Angela Alsobrooks are pursuing policy language intended to prohibit yields on stablecoins, but banks argue the bill as drafted does not adequately close loopholes.
- Banking groups cite studies suggesting that broad stablecoin adoption could trigger substantial outflows from U.S. banks, particularly from smaller, community institutions that lack flexible balance sheets to absorb such shifts without costly wholesale borrowing.
- Economists cited by banks argue that stablecoin yields could depress broad lending if deposits move to crypto platforms, while White House economists say a yield ban would have a relatively modest impact on lending—though the math remains contested.
- The CLARITY Act currently faces a cautious path through Congress, with doubts about whether it can advance before the midterm elections in November 2026, and with ongoing negotiations over exact wording.
The case for stronger language on yields
The banking groups’ joint statement framed the issue around a central question: how to prevent stablecoin rewards from siphoning off core funding from the traditional banking system. They argue that the proposed language, as it stands, would allow crypto platforms to pay interest or yields on crypto holdings in ways that resemble bank deposits but avoid regulation under conventional banking rules. This, they say, would create a significant regulatory blind spot and potential deposit risk for banks that must compete for funding in stricter regulatory environments.
“It is imperative that Congress get this right,” the groups asserted in their Monday communique, stressing that the current iteration would not fully shield banks or customers from the stability risks associated with stablecoins and their yield mechanics. The statement was issued with the backing of major trade associations representing traditional financial institutions, signaling broad concern across the sector.
The draft’s supporters, including Senator Tillis, have argued that the text represents a practical compromise: it prohibits stablecoin rewards on idle balances while allowing other, non-deposit-related customer rewards. Tillis said the current text strikes a balance that could move the CLARITY Act toward passage on a bipartisan basis, even as some in the banking industry push back against continuing ambiguity.
Nevertheless, the bankers pledged to deliver further “detailed suggestions for strengthening the proposed language” to lawmakers in the coming days, underscoring the push for an explicit, robust prohibition that would close perceived regulatory gaps before any final vote.
Economic modeling and policy tensions
Beyond deposit protection, the debate touches on broader economic implications. The banking groups highlighted studies indicating that widespread stablecoin adoption could lead to substantial outflows from U.S. banks, especially among community banks. They argued these outflows could impair banks’ balance-sheet flexibility, potentially forcing higher-cost wholesale funding if institutions cannot shrink their traditional funding bases quickly enough.
In support of a tougher stance, the coalition cited an analysis from a Stanford-trained economist, Andrew Nigrinis, which framed stablecoin yield as a channel that could drive deposits away from banks and, in turn, depress consumer, small-business, and agricultural lending by a material margin. That line of argument underscores a fear among banks that the policy gap is not merely regulatory loophole but a real economic lever with the potential to constrain credit provision.
On the other side of the ledger, White House economists have presented a more subdued projection. In April, officials argued that banning stablecoin yield would yield only a modest net increase in lending—about $2.1 billion—roughly 0.02% of the banking sector’s total lending. The numbers, while small in aggregate, feed a broader debate about how policy choices translate into real-world lending capacity and consumer access to credit.
The divergent views reflect a broader tension around how tightly to regulate stablecoins and related yield mechanisms while preserving incentives for innovation and financial inclusion. The CLARITY Act’s supporters contend that strong, clear rules are essential to safeguard the financial system and to set a predictable framework for developers and investors. Critics say overly aggressive restrictions could hamper the growth of blockchain-based financial services and DeFi infrastructure, potentially pushing activity overseas or into less regulated niches.
Regulatory horizon and industry reactions
The legislative journey of the CLARITY Act remains unsettled. The bill cleared the U.S. House of Representatives in July with a 294-134 vote, but its path through the Senate—and, crucially, whether it can pass before the elections—remains uncertain. The midterm cycle is typically a bottleneck for major regulatory legislation, and the timing raises questions about whether lawmakers will reach a markup or a final vote in the current session.
For now, the banking industry is signaling that while it supports the aim of prohibiting inappropriate yields on stablecoins, it cannot endorse language that leaves room for “customer rewards” or other compensatory mechanisms that could still undermine deposit protection. Some observers note that the debate could become a proxy fight over the balance between innovation and financial stability, especially as more retail users engage with crypto products through mainstream platforms.
Industry advocates argue that a tightly drafted text would offer a clearer path to bipartisan agreement, enabling policymakers to address both consumer protection and system-wide risk. They contend that any compromise should be explicit about what is prohibited and what remains permissible, to prevent misinterpretation by crypto platforms and by banking institutions adapting to a rapidly evolving landscape.
The broader ecosystem—comprising exchanges, wallet providers, DeFi builders and incumbents—will be watching closely. If the Senate advances a version with stronger prohibitions, it could provide a clearer regulatory signal to developers and investors who have been waiting for durable rules. Conversely, a delay or a watered-down provision could keep ambiguity alive, potentially slowing legitimate innovation and prompting continued lobbying from both sides.
What readers should watch next
The immediate watch point is whether the Senate will bring the CLARITY Act to a markup in the coming weeks and whether a bipartisan framework can be achieved before the midterm deadline. Investors and builders in the crypto and DeFi spaces should monitor how lawmakers translate these concerns into concrete text, and how banks’ deposit stability considerations influence the final shape of the law. While the economic projections cited by proponents and opponents differ, the underlying question remains: will the final version deliver a clear, enforceable boundary around stablecoin yields that protects conventional banking models without stifling legitimate innovation?
As this regulatory arc unfolds, market participants should also factor in potential shifts in platform risk, liquidity dynamics in traditional banks, and the incentive structure facing users who interact with stablecoins and yield-generating crypto products. The outcome will likely affect not only policy clarity for developers but also the calculus of institutions considering how to compete or cooperate with crypto-native financial services in a compliant, transparent manner.
Readers should stay tuned for forthcoming legislative text, committee hearings, and potential amendments that could redefine the balance between innovation and stability in this rapidly evolving sector.
Crypto World
Control of Commerzbank ‘not the expected scenario’

Andrea Orcel, chief executive officer of Unicredit, in London, UK, on Thursday, Nov. 23, 2023.
Bloomberg | Bloomberg | Getty Images
UniCredit CEO Andrea Orcel told CNBC Tuesday that he does not foresee a future where the Italian lender fully controls Commerzbank.
Orcel’s comments came as the Italian lender’s tender offer to raise its stake in the German bank kicks off.
“If we get to control, which is not the expected scenario at the moment, what we would do is very clear, and the returns on that would be … very positive for our shareholders, and also for the shareholders of Commerzbank, but it’s up to them,” he told CNBC’s Carolin Roth.
“We’re not really fretting it. We are just focusing on delivering, and we’ve done all we could to engage, and now we are just looking at what shareholders will do.”

Last month, UniCredit announced an offer to build more shares in Commerzbank, structured as a share exchange. The move aims to increase UniCredit’s holding in Commerzbank to more than 30%, a key regulatory threshold.
It already holds a 28% stake in Commerzbank, after steadily increasing its investment in the German lender since taking a minority stake in 2024.
The tender offer for Commerzbank begins on Tuesday.
On Monday, UniCredit shareholders voted to approve the issuance of 470 million new shares which could be exchanged for Commerzbank shares tendered in the offer.
Orcel’s interview with CNBC came after UniCredit published its first-quarter earnings, which were touted as the bank’s 21st quarter of profitable growth and its best quarter on record.
Quarterly net profit grew 16.1% year-on-year to 3.2 billion euros ($3.74 billion), well above the 2.8 billion euros expected by analysts polled by LSEG.
Shares of UniCredit were up by around 3% in early trade on Tuesday.
This is a developing story. Please refresh for updates.
Crypto World
Polygon rolls out private stablecoin payments with hidden transfers


Polygon has introduced a privacy layer for stablecoin transfers, allowing transactions to remain hidden from public view while still meeting compliance checks.
Summary
- Polygon has rolled out private stablecoin transfers using zero-knowledge proofs while keeping KYT compliance checks in place.
- Transactions routed through Hinkal allow users to hide payment details from public view while still generating audit records for regulators.
According to a statement released by Polygon on Sunday, the update adds a wallet feature that routes payments through a shielded pool, where verification is handled using zero-knowledge proofs as part of its integration with Hinkal.
The company said each transaction is screened through Know Your Transaction checks before execution, ensuring that compliance requirements are met even when transaction details are not publicly visible.
Polygon community lead Smokey, writing on X, described the move as a requirement for real adoption, stating that businesses need operational privacy rather than tools designed to avoid regulatory oversight. Polygon, in its own statement, added that confidentiality remains a missing element for institutions that already operate with restricted financial data on traditional payment rails.
Addressing concerns around oversight, Polygon said privacy on its network is designed to limit visibility to the market while preserving access for regulators. Hinkal’s documentation notes that users can generate audit files for authorities, including tax officials, providing a mechanism for post-transaction verification without exposing activity in real time.
The release comes as privacy-focused features continue to gain traction across blockchain networks. Aptos launched its Confidential APT token on April 24, introducing a system that conceals transfer data while maintaining verifiability, with the asset pegged to the value of the native APT token.
Polygon’s move also fits into a wider push to position the network as a payments-focused platform built around stablecoin flows.
In an April report, Polygon Labs said it was seeking up to $100 million in new funding to expand a payments stack that includes Coinme and Sequence, with CEO Marc Boiron stating that the company’s ambition is to operate as a regulated payments entity in the United States.
Polygon has said its Open Money Stack is designed to handle cross-chain and cross-currency transfers in a unified system for fintech firms and enterprises.
Data from DeFiLlama shows Polygon’s stablecoin market capitalization reached $3.6 billion on April 10, placing it among the top chains for stablecoin activity. The network has also handled a large share of non-USD stablecoin transfers, according to ecosystem updates cited by Polygon Labs, highlighting its role in processing local currency payments.
Institutional interest in stablecoin payments has grown following regulatory developments such as the GENIUS Act passed in July last year, which supported stablecoin adoption in financial services. Recent activity from traditional firms has added to that trend, with Western Union announcing a USD-pegged stablecoin on Solana on Sunday.
Earlier integrations have already tested stablecoin use cases on Polygon’s network. In April, Meta Platforms began offering select creators the option to receive payouts in USDC through wallets on Polygon and Solana, with payments processed by Stripe and supported by tools for tax reporting.
Crypto World
Uphold rejects NYAG claims after $5M CredEarn settlement


Uphold has pushed back against the New York Attorney General’s statement on its $5 million CredEarn settlement.
Summary
- Uphold says the NYAG statement misrepresented key facts about its $5M CredEarn settlement.
- The NYAG said more than 6,000 Uphold customers lost over $34M after Cred collapsed.
- Uphold said it froze Cred’s platform access within hours after learning about liquidity issues.
The company shared the update with crypto.news after the regulator said Uphold misled investors by promoting Cred LLC’s crypto yield product.
In its response, Uphold said the Attorney General’s statement misrepresented key facts about the settlement. The company also rejected any claim that it knowingly promoted Cred’s alleged fraud. Uphold said Cred misled the company, its customers and other CredEarn users.
NYAG says Uphold promoted CredEarn
The New York Attorney General said Uphold agreed to pay more than $5 million to harmed investors. The regulator said Uphold promoted CredEarn as a reliable savings product while Cred used customer crypto in risky lending activity.
The settlement document said Uphold advertised CredEarn on its website and mobile app from 2019 to October 2020. It also said more than 6,000 Uphold customers invested about $50 million through the product. Those customers later lost over $34 million after Cred collapsed.
Moreover, Uphold said it did not know about Cred’s liquidity issues until October 2020. It also said it was unaware that Cred’s statements about the financial health of CredEarn were false. The company said it froze Cred’s access to its platform within hours after learning about the issue.
Uphold CEO Simon McLoughlin said, “We are deeply disappointed by the New York Attorney General’s statement.” He also said the U.S. Department of Justice treated Uphold as a victim in its criminal case against Cred executives. Uphold said it settled without admitting liability.
Settlement adds new compliance duties
The settlement requires Uphold to pay $5 million in monetary relief. It also requires any initial distribution tied to Uphold’s $545,189.97 claim in the Cred bankruptcy case to be added to customer payments.
Uphold must also maintain a risk-based review process before recommending third-party products. That process may include checks on financial records, insurance policies, compliance policies, customer checks, security systems and outside verification.
Dispute centers on Uphold’s role
The Attorney General said Uphold promoted CredEarn without proper registration and failed to disclose key risks. The regulator also said no insurance existed to protect retail investors from digital asset investment losses, despite statements about Cred’s insurance coverage.
Uphold gave a different account. It said Cred deceived the company and that it acted to stop further customer exposure once it learned of Cred’s problems. The dispute now centers on whether readers should view Uphold mainly as a promoter of CredEarn or as another party deceived by Cred.
-

 Business6 days ago
Business6 days agoMost Commercial Energy Audits Miss the Real Losses
-

 Fashion6 days ago
Fashion6 days agoKylie Jenner’s KHY Enters a New Era with ‘Born in LA’
-

 NewsBeat2 days ago
NewsBeat2 days agoChannel 5 – All Creatures Great and Small series 7 new post
-

 Tech4 days ago
Tech4 days agoTrump’s 25% EU auto tariff breaches Turnberry Agreement that also covers semiconductors and digital trade
-

 Sports4 days ago
Sports4 days agoPaul Scholes issues Marcus Rashford reality check as agreement emerges over Man United star
-

 Crypto World7 days ago
Crypto World7 days agoCFTC’s AI will review U.S. crypto registration applications, chairman tells CoinDesk
-

 Business6 days ago
Business6 days agoBarclay Brothers Avoid Bankruptcy: HSBC Drops High Court Petitions After IVA Deal
-

 Business6 days ago
Business6 days agoTesla Officially Registers Elon Musk’s Stock: What Investors Need to Know
-

 Crypto World7 days ago
Crypto World7 days agoRobinhood Phishing Scam Exploits Gmail Dot Feature to Bypass Security
-

 Tech7 days ago
Tech7 days agoGet Ready for More Brain-Scanning Consumer Gadgets
-
 Tech6 days ago
Tech6 days agoTexas Instruments made a new flagship graphing calculator: the TI-84 Evo
-

 Business4 days ago
Business4 days agoTwo Powerball Tickets Split $143 Million Jackpot in Indiana and Kansas
-
Crypto World4 days ago
CoreWeave (CRWV) Stock Climbs 8% Despite $45M Insider Share Dump
-

 Business2 days ago
Business2 days agoWinning Numbers Drawn as Jackpot Resets to $20 Million
-

 Crypto World5 days ago
Crypto World5 days agoSecuritize and Computershare Enable Tokenized Equity Issuance for Over 25,000 U.S.-Listed Stocks
-

 Crypto World5 days ago
Crypto World5 days agoGibraltar Proposes Tokenized Funds Regulation to Bolster Compliance
-

 Fashion2 days ago
Fashion2 days agoMary J. Blige Vegas Residency Looks: Crystal-Embellished Fjolla Haxhismajli, Todd Fisher, and More!
-

 Tech5 days ago
Tech5 days agoOfficial SAP npm packages compromised to steal credentials
-
 Tech7 days ago
Tech7 days agoAcer Swift 16 AI (2026) Review: Where Do Your Hands Go?
-

 Sports6 days ago
Sports6 days agoAntrim GAA: Hurlers cancel training as row with board deepens













You must be logged in to post a comment Login