Crypto World
Fake Police Raid Scam Forces Victim to Send $1M in Bitcoin
Key takeaways
-
Crypto security is expanding beyond digital threats, with criminals increasingly targeting individuals directly through physical coercion rather than trying to exploit blockchain vulnerabilities or hack wallets.
-
The French case illustrates how attackers used a fake police raid and violence to force a Bitcoin transfer worth $1 million, bypassing encryption entirely by compelling the victim to authorize the transaction.
-
Wrench attacks are rising, with criminals using threats or force instead of technical exploits. This highlights how human vulnerability can override even the most secure cryptographic systems.
-
Impersonating authority figures such as police is highly effective because it combines fear, urgency and social conditioning, making victims more likely to comply without questioning the situation.
Digital defenses are no longer the only front line in crypto security. While phishing and exchange hacks have long been major threats, a growing number of thefts now bypass code entirely and target crypto holders directly.
A recent case in France highlights this shift. Attackers posing as police staged a “raid” and physically coerced a couple into transferring nearly $1 million in Bitcoin (BTC). This was not a failure of software, but a high-stakes robbery carried out through physical force.
When the victim, not the wallet, becomes the target
The incident occurred in Le Chesnay-Rocquencourt, a town near Paris, where a couple in their late 50s was allegedly assaulted inside their residence.
Here is the chronology of the incident:
-
Three individuals disguised as police officers gained entry to the home.
-
The couple was threatened at knifepoint.
-
The husband was forced to send Bitcoin to the attackers.
-
Both victims sustained injuries, and the husband was physically restrained and tied up.
-
The assailants fled the scene in a vehicle.
French authorities are currently investigating the matter, with charges including armed robbery and organized criminal conspiracy.
What distinguishes this case is not only the use of violence, but the specific strategy employed.
Rather than attempting to crack encryption, the perpetrators bypassed it entirely by coercing the owner into authorizing the transfer.
Why impersonating police officers is so effective
Posing as law enforcement officials is often effective because it taps into several psychological triggers:
-
Authority: People are socially conditioned to obey police directives.
-
Urgency: The appearance of an official raid creates the impression that immediate compliance is necessary.
-
Fear: Any resistance can seem as though it may lead to criminal consequences.
When criminals present themselves as police, victims often fail to question:
-
The reason for their presence.
-
The legitimacy of their demands.
-
The authenticity of the entire situation.
Under stress, the impulse to obey tends to overpower the instinct to verify or question what is happening.
In crypto, this risk is even greater because a single approved transaction can move significant funds in seconds.
Did you know? The term “wrench attack” became popular in the crypto space after an online comic joked that threatening someone physically is easier than breaking encryption. It reflects a real-world shift in which attackers bypass complex systems by targeting people rather than technology.
From simulated police raid to coerced Bitcoin transfer
Unlike conventional robberies that target cash, jewelry or other tangible items, this assault specifically targeted digital cryptocurrency holdings.
The attackers’ objective was straightforward: force the victim to carry out an immediate crypto transfer.
This form of theft can be difficult to contain for several reasons:
-
Stolen funds can be transferred anywhere in the world within minutes.
-
Blockchain transactions are generally irreversible.
-
Once transferred, funds can be moved quickly, which can make tracing and recovery more difficult.
When the victim retains direct control over their wallet, criminals do not need to steal hardware or break through security. They only need to force the victim to approve and send the transaction personally.
Understanding wrench attacks in the cryptocurrency space
It is often far easier to threaten a person with a wrench than to try to crack their encryption.
Rather than attempting to hack a wallet, perpetrators may use:
-
Threats
-
Physical violence
-
Other forms of coercion
These methods are used to force victims to reveal private keys or authorize the transfer of funds. Such attacks bypass even the strongest technical protections.
No matter how strong the encryption is, human vulnerability can make that security irrelevant.
Did you know? Some high-net-worth crypto holders now use “decoy wallets” with small balances. In a coercive situation, they can reveal these wallets instead of their main holdings, adding an extra layer of psychological and financial protection.
Why these attacks are becoming more frequent
Several underlying factors are driving this increase:
-
Growth in self-custody: A rising number of users now hold their own private keys and manage their assets directly, making them more immediate and accessible targets.
-
Visibility of high-value targets: Many cryptocurrency investors, company founders and executives maintain public profiles that make their wealth and identity relatively easy to identify.
-
Advances in cybersecurity: As digital wallet security improves and remote hacking becomes more difficult, criminals are increasingly turning to the softer target, the human user.
-
Instant global liquidity: Cryptocurrency enables near-instant transfers of value anywhere in the world without banks or intermediaries acting as gatekeepers.
In 2025 alone, documented cases of verified wrench attacks reportedly rose sharply, increasing 75% from 2024. Europe, and France in particular, stood out as a growing hotspot for such incidents. Financial losses reached $40.9 million in 2025, marking a 44% annual increase. While kidnapping remained the primary threat vector, physical assaults surged by 250%.
Why France has experienced a surge
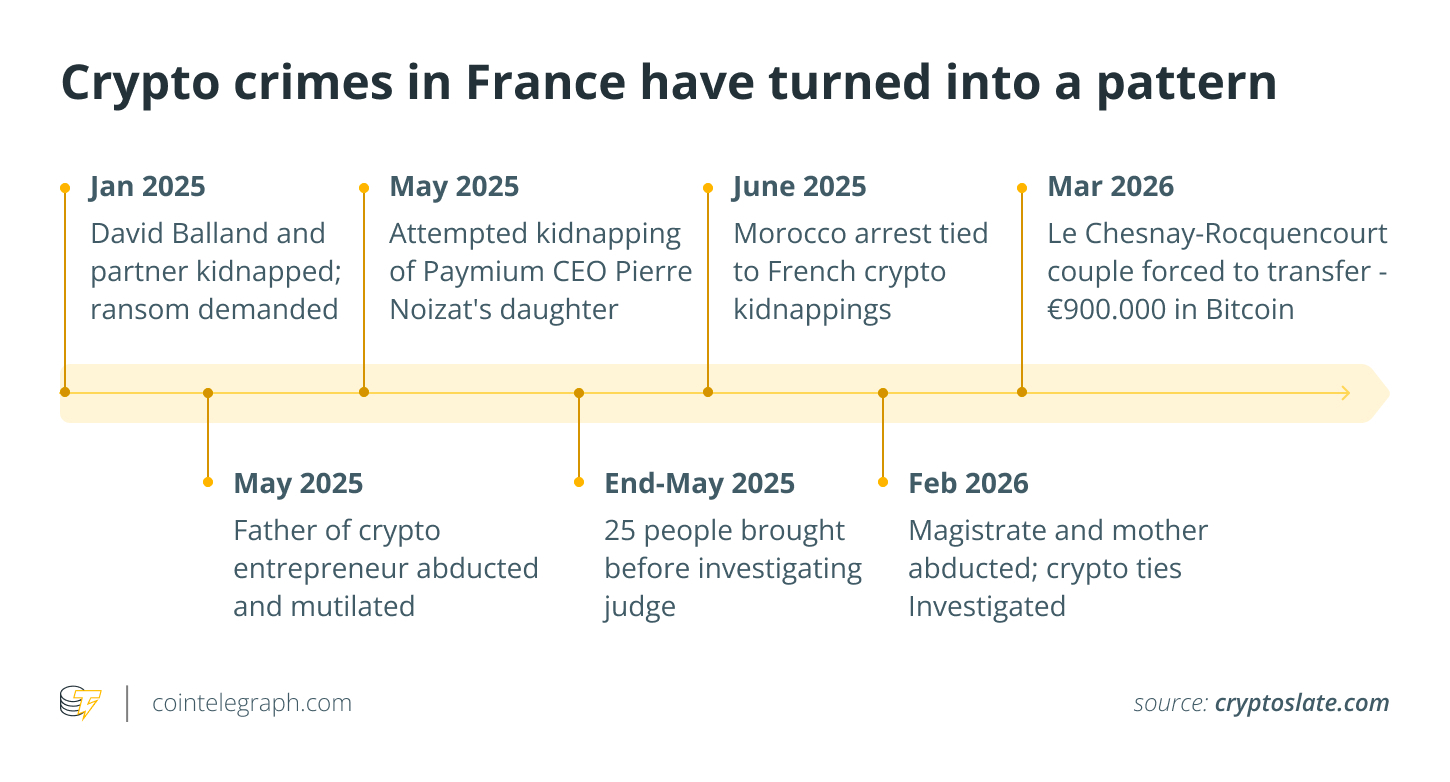
France has recently recorded multiple high-profile violent crimes linked to cryptocurrency:
-
Kidnappings carried out to extort cryptocurrency ransoms.
-
Home invasions specifically targeting high-profile figures in the crypto industry.
-
Coordinated operations by organized criminal groups aimed at stealing digital assets.
These recurring incidents point to a shift in criminal behavior:
-
More deliberate efforts to identify individuals who hold cryptocurrency.
-
Increased surveillance of their physical locations and daily routines.
-
A growing preference for direct physical targeting over purely digital methods.
As cryptocurrency adoption continues to expand, public awareness of who owns it is also growing. Unfortunately, the physical risks associated with that visibility are rising as well.

Why criminals increasingly choose coercion over hacking
Crypto security has become increasingly strong. Hardware wallets, multisignature setups and cold storage solutions make remote hacking far more difficult.
Coercion, however, changes the equation.
Even the strongest technical protections may fail if a victim is coerced into unlocking their hardware device, revealing their credentials or authorizing a transaction.
Coercive attacks bypass cryptographic defenses entirely, target points of human access and exploit natural human reactions.
For perpetrators, this approach is often faster and more reliable than trying to break through technical defenses.
Why Bitcoin remains particularly exposed in duress situations
Bitcoin’s core architecture gives it considerable strength, but it also creates significant vulnerability when the owner is under coercion.
Its key features include:
-
The ability to transfer value immediately
-
The absence of any central entity capable of reversing transactions
-
Permissionless, worldwide accessibility
In a situation where the holder is forced to transfer funds, these traits can result in:
-
Assets being moved almost instantly
-
Virtually no realistic chance of recovery
-
Attackers rapidly moving funds across multiple addresses
The same qualities that give Bitcoin its independence and value also make stolen funds extremely difficult to recover once they are transferred under duress.
Did you know? Private security firms have started offering specialized protection services for crypto investors, including travel risk assessments, home security audits and digital footprint reduction strategies aimed at preventing targeted attacks.
How French authorities are responding
French law enforcement agencies are actively investigating the incident, with specialized organized crime units leading the effort.
Potential criminal charges under review include:
Although authorities are increasing enforcement in response to such incidents, these cases continue to present serious challenges because of:
-
The rapid cross-border movement of stolen assets
-
The pseudonymous and irreversible nature of cryptocurrency transactions
-
The involvement of organized and professional criminal groups
Key security takeaways for cryptocurrency owners
This incident underscores a major shift in the nature of cryptocurrency security threats.
Protecting technical systems alone is no longer enough. Safeguarding wallets, private keys and physical devices must now be paired with strong personal security measures.
Essential protective steps include:
-
Never publicly reveal or discuss the extent of your cryptocurrency holdings.
-
Keep your real-world identity separate from your wallet addresses and ownership.
-
Use multisignature wallets so that no single individual or compromised key can authorize transfers.
-
Distribute signing authority and key control across different geographic locations or trusted parties.
Cointelegraph maintains full editorial independence. Guides are produced without influence from advertisers, partners or commercial relationships. Content published in Guides does not constitute financial, legal or investment advice. Readers should conduct their own research and consult qualified professionals where appropriate.
Crypto World
Coinbase Expands x402 With AI Agent App Store, Pushing Crypto Payments Into AI Infrastructure
Coinbase has launched Agent.market, an AI agent app store built on its x402 payment protocol, embedding permissionless stablecoin rails directly into AI infrastructure across seven service categories. As of April 21, 2026, approximately 69,000 active AI agents on x402 have already processed over 165 million transactions totaling $50 million in volume, figures that frame this as an infrastructure play, not a speculative product launch.
The core question now: whether Agent.market can become the default discovery and payment layer for autonomous AI agents, or whether fragmented developer ecosystems blunt adoption before the rails gain critical mass.
Key Takeaways:
- What x402 is: An open payment protocol named after the unused HTTP 402 status code, enabling instant stablecoin micropayments over HTTP for APIs, apps, and AI agents – no accounts or subscriptions required.
- What Agent.market adds: A permissionless app store spanning seven categories – reasoning, data, media, search, social, infrastructure, and trading – with providers including OpenAI, Bloomberg, CoinGecko, AWS Lambda, and Coinbase RAT.
- What AI agents can now do: Autonomously discover, pay for, and chain together services using Agentic Wallets, without developer-preset API keys or manual billing setup.
- Payment rail: USDC stablecoins on Base, with Coinbase’s Payments MCP enabling LLMs including Anthropic’s Claude and Google’s models to access blockchain wallets via x402.
- Backing: The x402 Foundation, incubated under the Linux Foundation, counts over 20 institutional backers including Cloudflare, Stripe, AWS, Google, Visa, Circle, and the Solana Foundation.
- Watch item: Google’s agentic payments protocol integration with x402 for single-tap USDC retail transactions – a signal that could accelerate volume materially.
Discover: The best crypto to diversify your portfolio with
How Coinbase x402 Agent.market Actually Works – and Why the Architecture Matters
x402 was designed around a structural gap in the existing web: the HTTP 402 status code has existed since the early internet as a placeholder for payment-gated content, but was never implemented at scale.
Coinbase built x402 to fill that gap. When an AI agent hits a payment-required endpoint, x402 handles the USDC micropayment over HTTP instantly, without redirecting to a billing portal or requiring a pre-negotiated API key relationship.
Agent.market operationalizes that mechanic into a browsable catalog. Service providers can list without permission, which directly reduces the setup friction that has historically limited API commerce: x402 creator Erik Reppel stated the protocol “is reshaping customer acquisition activation costs for businesses, as robots can now access services at a very low setup cost without needing API keys.”
That framing matters; it redefines cost-of-acquisition for AI-facing businesses from human onboarding flows to machine-readable price discovery.
The seven-category structure – reasoning, data, media, search, social, infrastructure, and trading – maps directly onto what autonomous agents need to chain multi-step tasks. An agent could pull financial data from CoinGecko, process it through an OpenAI reasoning endpoint, execute a trade via Bankr, and log the transaction through QuickNode infrastructure, with every handoff settled in USDC on Base without human authorization at each step.
If adoption follows the arc of prior API marketplaces, the trading and data verticals will see volume concentration first – they carry the highest per-call value and the most time-sensitive payloads.
The failure mode to watch is latency and settlement finality at scale. x402’s prior 165 million transactions represent an average call value under $0.31 – the architecture is calibrated for micropayments, not bulk settlements. Whether it holds throughput as agent complexity and chain length increase is the open engineering question.
Discover: The best pre-launch token sales
The post Coinbase Expands x402 With AI Agent App Store, Pushing Crypto Payments Into AI Infrastructure appeared first on Cryptonews.
Crypto World
The Real Product of DeFi Is Volatility
Decentralized Finance (DeFi) is often marketed as a parallel financial system built on transparency, efficiency, and permissionless access. Yet beneath these narratives lies a more fundamental driver—volatility. While traditional finance seeks to minimize instability, DeFi, in contrast, is structurally dependent on it. Volatility is not a byproduct of the system; it is, in many ways, the system’s core product.
Volatility as the Engine of Opportunity
At the heart of DeFi protocols such as Uniswap, Aave, and Compound lies a simple premise: market inefficiencies create profit opportunities. These inefficiencies are amplified by price fluctuations.
Without volatility, several foundational DeFi mechanisms would lose their purpose:
- Arbitrage depends on price discrepancies across markets. Stable prices eliminate these gaps, leaving no room for profit extraction.
- Yield farming relies on shifting capital toward higher returns, often driven by rapidly changing incentives and token valuations.
- Liquidation cycles in lending protocols require price movements to trigger collateral thresholds.
In essence, volatility fuels the activity that sustains user engagement and capital flow within the ecosystem.
Liquidity Provision and the Cost of Stability
Liquidity providers (LPs) are often presented as passive participants earning fees. However, their returns are closely tied to market turbulence. In automated market makers (AMMs), price swings generate trading volume, which in turn produces fees.
Yet this comes with a trade-off: impermanent loss. In low-volatility environments, LPs may see reduced trading activity and lower fee generation, while still being exposed to potential downside risks. Ironically, the more stable the market becomes, the less attractive liquidity provision can be.
This dynamic reveals a critical tension: DeFi protocols require stability to build trust, but depend on volatility to remain profitable.
The Feedback Loop of Instability
DeFi does not merely react to volatility—it amplifies it. Mechanisms embedded within protocols often create feedback loops:
- Price drops trigger liquidations, which further push prices downward.
- Yield incentives attract capital rapidly, only for it to exit just as quickly when returns diminish.
- Leveraged positions magnify both gains and losses, increasing systemic sensitivity to price changes.
These cycles are not anomalies; they are intrinsic to how DeFi systems are designed. Platforms like MakerDAO and Curve Finance attempt to introduce stability through collateralization and specialized liquidity pools, yet even they cannot fully escape the gravitational pull of broader market volatility.
Stability as a Narrative, Not a Foundation
Stablecoins and low-volatility pools are often positioned as solutions to DeFi’s chaotic nature. However, even these instruments rely indirectly on volatility elsewhere in the system. For example, maintaining a stable peg frequently depends on arbitrage incentives—again requiring price discrepancies to function effectively.
Thus, stability in DeFi is less a foundational property and more a constructed layer, supported by mechanisms that ultimately trace back to volatility.
Conclusion
The promise of DeFi is frequently framed around democratizing finance and reducing reliance on centralized institutions. While these goals are significant, they can obscure a more pragmatic reality: DeFi thrives on movement, not equilibrium.
Volatility is the fuel that powers arbitrage, sustains yield, and drives liquidations. Without it, the mechanisms that define DeFi would stall. Rather than viewing volatility as a problem to be solved, it may be more accurate to recognize it as the primary product being generated and consumed within the ecosystem.
Understanding this dynamic is essential for participants. Success in DeFi is not about avoiding chaos—it is about navigating it effectively.
REQUEST AN ARTICLE
Crypto World
BitMEX Enables Off-Exchange Trading Via Zodia Custody

BitMEX, a derivatives-focused cryptocurrency exchange, said it has secured a custody partner to enable asset segregation and trading with off-exchange assets.
The company announced Tuesday a partnership with Zodia Custody to allow traders to access derivatives while keeping collateral in segregated custody. The integration is immediately accessible via Interchange, Zodia Custody’s off-venue settlement solution.
BitMEX CEO Stephan Lutz told Cointelegraph the move reflects lessons from past market failures, including the FTX collapse and the $1.4 billion Bybit hack, which exposed risks tied to unsegregated or compromised exchange-held funds.
“Cases like the FTX collapse and the Bybit hack are examples of how custody failures or security threats can put client funds at risk,” Lutz said.
Trading without prefunding the exchange
Under the integration, institutional and professional BitMEX clients can trade derivatives without transferring assets directly onto the exchange. Instead, collateral remains in Zodia’s segregated vault and is mirrored for trading execution.
This structure allows traders to maintain control of assets while accessing BitMEX’s derivatives, including perpetual swaps and futures. It also supports cross-collateral usage of Bitcoin (BTC), Ether (ETH), Tether USDt (USDT) and USDC (USDC).

This setup is designed to improve capital efficiency for traders by removing the need to move assets between custody and exchange accounts. It also reduces operational risk tied to pre-funding workflows, which are common in traditional crypto trading models.
Custody is a core part of traditional finance markets
Zodia Custody, which launched in 2021 and is backed by Standard Chartered, is an institutional digital asset custody provider operating globally. The platform secured a Markets in Crypto-Assets Regulation (MiCA) authorization in Luxembourg in late 2025, enabling regulated services across the European Union.
BitMEX CEO noted that custody has long been a core element of traditional finance, becoming even more critical following collapses like FTX and security incidents like the Bybit hack.
Related: Zonda exchange says 4.5K BTC wallet inaccessible amid withdrawal crisis
“Custody is a core part of traditional finance markets, and recent cases like FTX and Bybit are clear examples of why it’s even more important in crypto,” Lutz said.
“As the industry matures, institutions are trading digital assets like any other asset — and should have access to the same services as they do in traditional markets,” he added.
Additional reporting by Felix Ng.
Magazine: Adam Back says current demand is ‘almost’ enough to send Bitcoin to $1M
Crypto World
Northrop Grumman (NOC) Stock Dips 1.6% Despite Strong Q1 Earnings Performance
Key Highlights
- Q1 earnings per share reached $6.14, surpassing Wall Street’s $6.05 projection by $0.09
- Quarterly revenue totaled $9.88 billion, marking a 4% year-over-year increase and exceeding the $9.76 billion forecast
- The Aeronautics Systems division reported a 17% sales increase, fueled by B-21 bomber and Sentinel program growth
- Operating profit jumped 73% to $989 million while segment margins expanded to 10.8%
- Shares declined approximately 1.6% during premarket hours despite beating estimates, with unchanged annual projections
Northrop Grumman delivered impressive first-quarter 2026 results that exceeded analyst expectations across key metrics, yet the defense contractor’s shares retreated during Tuesday’s early market session.
The company reported earnings per share of $6.14, comfortably above the Street’s $6.05 consensus target. Quarterly sales reached $9.88 billion, reflecting a 4% increase compared to the $9.47 billion recorded in the same period last year, and beating the anticipated $9.76 billion mark.
The Aeronautics Systems division emerged as the standout performer, with revenue soaring 17%. This substantial growth stemmed from a recently secured agreement with the U.S. Air Force that accelerates B-21 bomber manufacturing capacity alongside expedited deployment of the Sentinel intercontinental ballistic missile program’s initial operational capability.
Northrop Grumman Corporation, NOC
Operating profit experienced a remarkable 73% surge to $989 million during the quarter. The company’s operating margin expanded significantly to 10.0% from the prior year’s 6.1%. This dramatic improvement was primarily attributed to the elimination of a $477 million charge related to the B-21 program that had negatively impacted first-quarter 2025 financial performance.
Segment operating profit climbed 89% to $1.07 billion, while segment operating margins improved substantially from 6.0% to 10.8%.
The defense contractor secured $9.8 billion in net new contract awards throughout the quarter. The company’s total backlog now stands at an impressive $95.6 billion — representing more than double its annual revenue.
Organic revenue growth registered at 5% on a year-over-year basis.
Full-Year Projections Remain Unchanged
Northrop maintained its previously issued 2026 full-year guidance without modification. Management continues to anticipate total sales between $43.5 billion and $44.0 billion, with MTM-adjusted earnings per share projected in the $27.40 to $27.90 range.
Current analyst consensus sits at approximately $28 for EPS — positioned above the company’s upper guidance threshold. Notably, when the defense contractor initially provided guidance in January, Wall Street expectations were hovering around $29.
The company reaffirmed its free cash flow target of $3.1 billion to $3.5 billion for the year. Segment operating income guidance remains between $4.85 billion and $5.0 billion.
Chief Executive Kathy Warden characterized the quarterly performance as evidence of the organization’s capability to execute amid “today’s unprecedented global demand environment.”
Market Response
Notwithstanding the earnings beat, NOC shares declined roughly 1.6% during premarket activity to $646.67. Meanwhile, both S&P 500 and Dow Jones Industrial Average futures were trading higher during the same timeframe.
The stock had already appreciated 15% year-to-date prior to Tuesday’s announcement, and approximately 24% over the trailing twelve-month period. Shares currently command a forward price-to-earnings multiple of about 23 times, elevated from roughly 19 times one year earlier.
This premium valuation level may help explain why a solid quarterly earnings performance failed to generate positive momentum for the stock, particularly given the company’s decision to maintain rather than raise its full-year outlook.
Crypto World
Tether Minted 1 Billion USDT: On-chain Trading Grinding Back
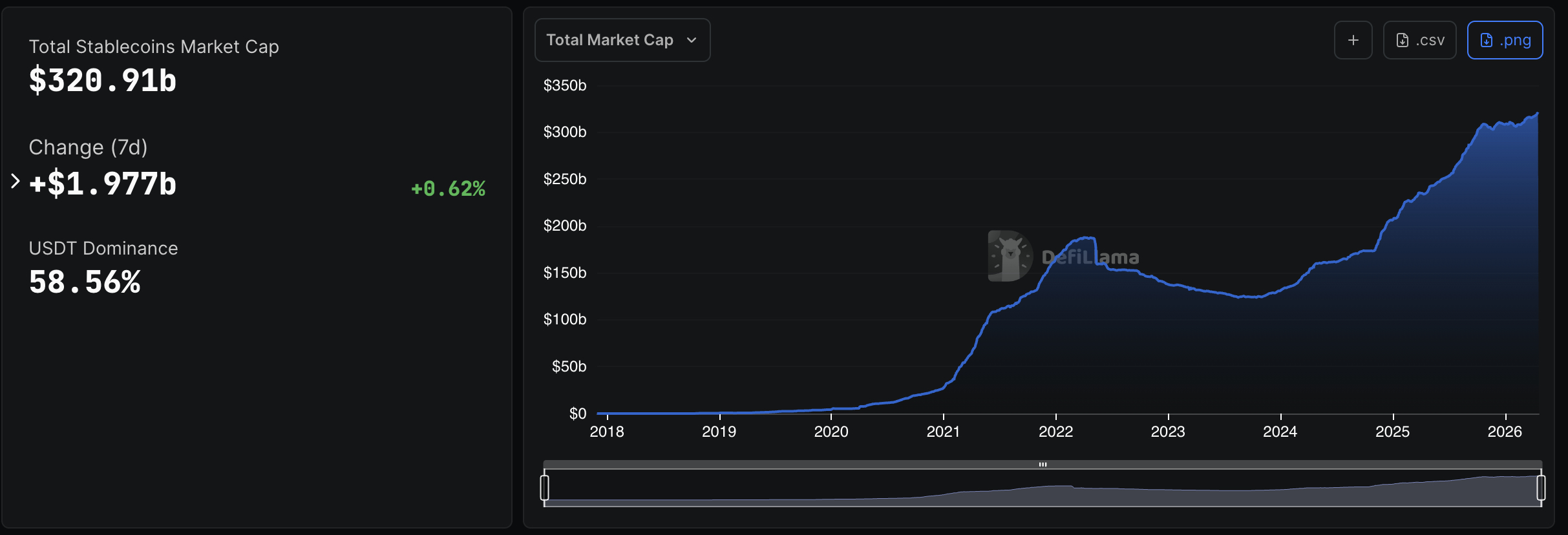
Tether just dropped a 1 billion USDT on Ethereum just as the memecoin scene in the chain is heating up. Arkham Intelligence flagged the event just shortly after Bitcoin pushed past $76,000. Following this, the Total USDT supply now stands at $193 billion, dominating the $320 Billion stablecoins size by 58%.
Institutional capital is moving, and Tether mints of this scale historically precede accelerated exchange inflows. The market is watching where this billion lands.
Discover: The best crypto to diversify your portfolio with
Is Tether 1 Billion USDT Mint a Reliable Liquidity Signal for On-Chain Trading?
Glassnode’s USDT Holder Accumulation Ratio sits at 57.63%, above the 50% threshold that indicates net accumulation by holders. Onchain Lens noted this mint as a precursor to heightened on-chain activity, with tokens expected to flow rapidly toward exchanges and DeFi platforms once deployed.
Transaction volume data reinforces the dominance picture. USDT’s volume of $484.17 billion already surpasses USDC’s $319.2 billion, a $164.97 billion gap that reflects USDT’s stranglehold on crypto payments infrastructure. Tron’s low-fee environment (driving 50%+ USDT network dominance) makes rapid deployment operationally straightforward once Ardoino’s team activates the inventory.
Institutional momentum is building, but the question is whether deployment timing aligns with the current sentiment window.
Discover: The best pre-launch token sales
Maxi Doge Eyes Big Upside as USDT Liquidity Hunts Yield
When $1 billion in fresh stablecoin liquidity enters the ecosystem, it doesn’t sit idle. History shows it finds its way into high-beta plays, and meme tokens with active communities tend to capture disproportionate inflows during liquidity expansion windows.
Maxi Doge ($MAXI) is positioned squarely in that window. Built on Ethereum as an ERC-20 token, the project combines meme-first marketing with structural utility: holder-only trading competitions with leaderboard rewards, a Maxi Fund treasury for liquidity and partnerships, and dynamic staking APY.
The presale has raised $4.7 million at a current price of $0.0002814. Memecoin activity on Ethereum is picking up alongside rising USDT liquidity. It’s the timing that $MAXI’s community is watching closely.
Research Maxi Doge before the next price tier moves.
The post Tether Minted 1 Billion USDT: On-chain Trading Grinding Back appeared first on Cryptonews.
Crypto World
Tokenized Gold Lands on Solana: Is Bitcoin Layer 2 Next For RWA Boost?

Singapore banking giant OCBC just put institutional-grade gold on-chain (Solana), and the RWA market didn’t flinch. But what does it mean for Solana price in April 2026, and could a new Bitcoin layer-2 be next for a RWA boom?
OCBC, one of Southeast Asia’s largest financial institutions, launched its GOLDX token on both Ethereum and Solana in partnership with Lion Global Investors and digital asset exchange DigiFT. The underlying fund, the LionGlobal Singapore Physical Gold Fund, held approximately $525 million in AUM as of April 16.
Institutional investors and hedge funds can subscribe using stablecoins or fiat, with tokens delivered directly to on-chain wallets.
Kenneth Lai, head of global markets at OCBC, called it “a milestone in the corporation’s blockchain-focused approach.”
Meanwhile, Solana’s tokenized gold volume had already surged 290%, processing 25.5 million tokens amid CLARITY Act optimism, a context that makes OCBC’s chain selection look less like a coincidence and more like a calculated bet.
Total tokenized real-world assets on public blockchains now exceed $29 billion, up over 10% in the last 30 days. That growth rate is attracting serious infrastructure attention, and not just on Ethereum and Solana.
Discover: The best pre-launch token sales
Can Solana Price Break Out as RWA Momentum Builds?
SOL looks active on the surface, but the price action tells a different story; this is not a breakout, it is compression with real participation, which usually means supply has not fully cleared yet.
That $78 to $80 zone is doing all the work right now, because as long as it holds, the structure stays intact and buyers are still defending, but it is not strong enough yet to push higher.
The problem is overhead, with $92 to $95 acting like a ceiling every time the price gets close, so until that breaks, this is still a range, not a trend.

If SOL can finally clear that zone with momentum, that is where things open up toward $110 and the next leg starts forming, especially if institutional narratives keep building.
But realistically, this still looks like a grind between $80 and $92 while the market builds a base and waits for a broader alt move.
The risk is if $78 breaks on volume, because that is where the structure weakens, and the price can slip back toward the low $70s, which does not kill the long-term story but definitely delays it.
And the bigger point people miss is that at this size, moves are slower and more measured, you are not getting easy 10x runs here, you are looking at more controlled upside, which is why smaller plays start attracting attention when SOL stalls like this.
Discover: The best crypto to diversify your portfolio with
Bitcoin Hyper Eyes the RWA Infrastructure Gap Bitcoin Itself Can’t Fill
Here’s the structural irony: Bitcoin holds the deepest liquidity, the strongest institutional trust, and the most recognizable security model on the planet, yet it cannot run the smart contracts that make tokenized gold, tokenized equities, or any programmable RWA function.
Solana can. Ethereum can. Bitcoin, natively, cannot. That gap is precisely what Bitcoin Hyper (HYPER) is engineering around.

Bitcoin Hyper positions itself as the first Bitcoin Layer 2 with Solana Virtual Machine (SVM) integration, bringing sub-second smart contract execution to the Bitcoin ecosystem without sacrificing Bitcoin’s base-layer security.
Think Solana-speed programmability, anchored to Bitcoin’s settlement guarantees (a combination that hasn’t existed before).
The project features an extremely low-latency Layer 2 processing architecture, a Decentralized Canonical Bridge for native BTC transfers, and high-speed, low-cost transaction execution, which the team claims outperforms Solana on throughput metrics.
The presale has now raised $32,466,226.06 at a current price of $0.0136789 per $HYPER, with staking available at a high APY for early participants.
The raise trajectory has been consistent, reflecting sustained demand from participants who want BTC-native infrastructure exposure ahead of any RWA catalyst. Presales carry real risk, tokens are pre-launch, and liquidity is unproven.
That caveat stands. But for traders who watched Solana capture the institutional tokenization narrative, the question of which Bitcoin Layer 2 captures the next leg deserves serious research.
Explore Bitcoin Hyper’s presale details here.
The post Tokenized Gold Lands on Solana: Is Bitcoin Layer 2 Next For RWA Boost? appeared first on Cryptonews.
Crypto World
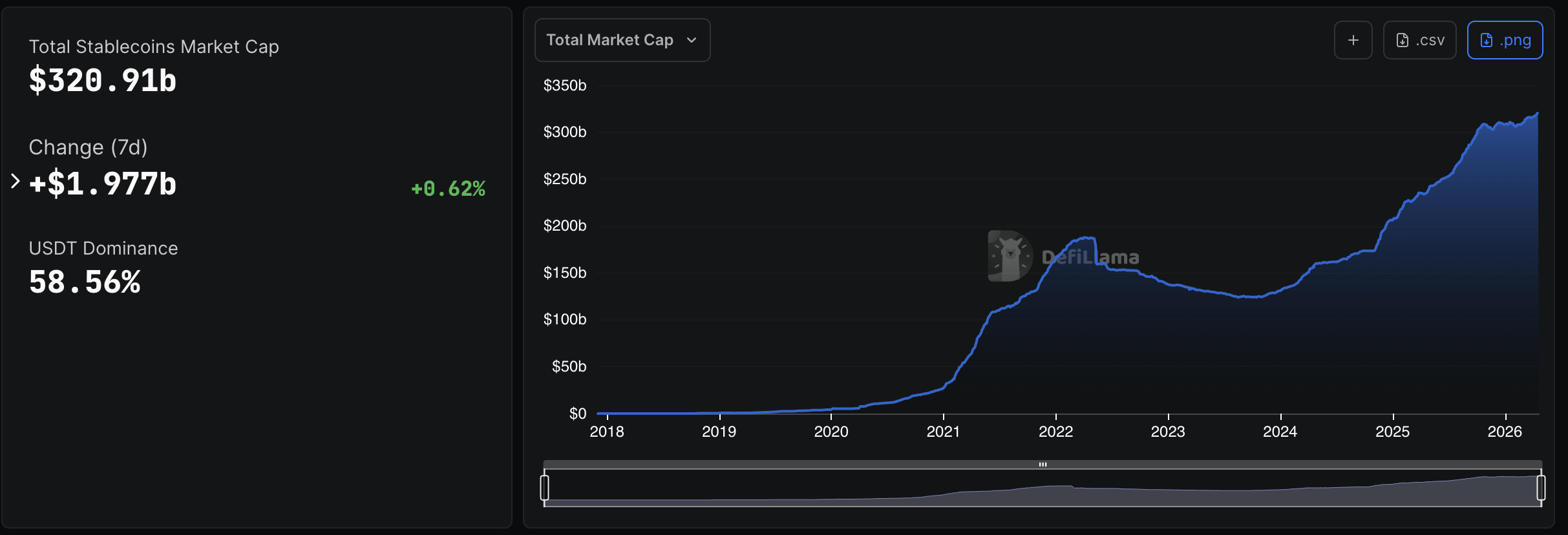
Scammers Hit Strait of Hormuz Ships With Crypto Demands
Fraudsters posing as Iranian authorities have targeted shipping firms with crypto-based demands to secure passage through the Strait of Hormuz, according to maritime risk outfit Marisks.
Marisks said unknown groups contacted shipowners claiming to represent Iran’s security services and demanded payment in Bitcoin or USD Tether in exchange for transit clearance, after requesting verification documents first. Reuters reported on the scam messages, noting they did not originate from Iranian authorities; Tehran has not publicly commented.
The warnings come as the Strait of Hormuz remains largely closed amid regional hostilities. The strait, a critical conduit for global energy shipments, previously handled roughly one-fifth of the world’s oil and LNG before the latest flareups. Earlier this month, Cointelegraph reported that Iran was considering tolls payable in BTC for ships passing through Hormuz, with empty tankers allowed free passage while others could be charged about $1 per barrel of oil.
Key takeaways
- Marisks warns that scams impersonating Iranian security services are soliciting crypto payments (BTC or USDT) for Hormuz transit, accompanied by requests for verification documents.
- The messages are not sourced from official Iranian authorities, according to Marisks and Reuters; Tehran has not publicly commented on the claims.
- The Strait of Hormuz remains largely closed amid Middle East hostilities, underscoring the vulnerability of global energy flows at this chokepoint.
- Sanctions risk looms large: payments tied to Iranian waterways could be treated as material support, with potential violations of US and international sanctions.
- This episode highlights the broader debate about crypto’s role in sanctioned regimes and the regulatory risks for shipping and crypto actors alike.
Crypto tolls, scams and the geopolitics of Hormuz
The messages described by Marisks present a classic manipulation: a supposed security clearance tied to a crypto payment, followed by a claim that transit will be allowed at a pre-arranged time once verification steps are completed. In at least one cited instance, the channel suggested Iranian security services would assess eligibility before determining the crypto payment in BTC or USDt. Marisks noted that a vessel recently targeted by gunfire while attempting to exit the strait may have received such instructions, though this has not been independently verified. Cointelegraph reached out to Marisks for comment but did not receive an immediate reply.
The episode arrives against a backdrop of wider geopolitical tension around Hormuz. Al Jazeera reported the Strait’s continued closures amid the conflict, a development that raises the stakes for insurers, operators and lenders who rely on predictable access to global energy markets. The strategic chokepoint remains a focal point for policy and risk assessment as regional dynamics evolve.
In earlier reporting, Iran was described as weighing crypto-based tolls to monetize navigation through Hormuz—an approach that would tilt the balance between open sea lanes and sanctioned finance. Cointelegraph’s coverage noted debates over BTC and USDt as potential toll instruments, reflecting a broader conversation about crypto’s utility in sanctioned economies and the practical risks for those who accept crypto payments under duress or misrepresentation. See the prior analysis on Iran’s crypto toll discussions for additional context.
Sanctions risk and what it means for operators
Beyond operational risk, industry analysts warn of serious compliance implications. Chainalysis senior intelligence analyst Kaitlin Martin told Cointelegraph that any payments tied to Iranian-controlled waterways could constitute “material support,” potentially violating US and international sanctions targeting entities linked to the Islamic Revolutionary Guard Corps. The warning underscores that crypto payments conditioned on access to strategic corridors can create exposure well beyond the immediate toll itself.
These developments sit at the intersection of geopolitical maneuvering and evolving crypto policy. Iran’s interest in leveraging digital currencies for energy transit has been debated in crypto policy circles, with discussions weighing potential benefits against the entrenched sanctions regime. For readers seeking deeper background, coverage exploring Iran’s BTC and USDt toll dynamics remains a pertinent companion piece.
As authorities surveil illicit use of crypto in restricted corridors, shipowners, operators and their counterparties will be watching for official guidance on sanctions enforcement and any regulatory clarifications related to crypto-enabled tolls. The risk environment around Hormuz—already shaped by conflict, insurance considerations and the reliability of communications—adds another layer of complexity for the global maritime and crypto communities.
Watch for formal statements from regulatory bodies and industry associations as this situation unfolds. The next steps will likely hinge on how sanctions enforcement perspectives evolve and whether crypto-based toll proposals advance or recede amid ongoing geopolitical tensions.
Crypto World
Ripple maps quantum-resistant XRP Ledger by 2028


Ripple has introduced a four-phase roadmap to make the XRP Ledger quantum-resistant by 2028.
Summary
- Ripple plans a four-phase XRP Ledger upgrade to reach quantum-resistant security standards by 2028.
- The roadmap includes 2026 testing, validator benchmarks, custody prototypes, and a final native amendment.
- Ripple linked the plan to rising concern over future quantum attacks on blockchain cryptography.
The plan responds to growing concern that advances in quantum computing could weaken the cryptography used across blockchain networks.
Ayo Akinyele, senior engineering director at RippleX, detailed the roadmap in a company blog post. The plan starts with a “Quantum-Day” contingency that would block classical signatures and direct users to quantum-safe accounts if current cryptography fails unexpectedly.
Ripple said the next two phases will take place during 2026. Those stages will focus on testing quantum-resistant algorithms recommended by the National Institute of Standards and Technology.
The final phase would add a native amendment to the XRP Ledger by 2028. That step is intended to bring quantum-resistant protections directly into the network’s core design.
Ripple said phases two and three will include technical testing and infrastructure work. The company is working with research firm Project Eleven on validator benchmarks and an early custody wallet prototype.
The testing phase aims to measure how quantum-safe algorithms perform under real network conditions. It also gives Ripple time to review how those tools can fit into validator operations and custody systems before a broader rollout.
Ripple’s timeline places much of the development work ahead of the final implementation target. The company said its approach is designed to prepare the ledger before quantum computing becomes a direct threat to blockchain security.
The roadmap also arrives one year before Google’s 2029 post-quantum cryptography target mentioned in the report. That comparison puts Ripple’s deadline earlier than one benchmark often cited in the wider technology sector.
Focus turns to long-term cryptography risk
Ripple linked the plan to the “harvest now, decrypt later” threat. That risk refers to attackers collecting public-key data today and waiting until quantum machines become strong enough to break it later.
The company said this issue matters for long-term holders whose public-key information may remain exposed over time. Recent Google Quantum AI research, cited in the report, found that about 500,000 physical qubits could derive a private key from an exposed public key in nine minutes.
That estimate marked a sharp reduction from earlier assumptions about the resources needed for such an attack. As a result, blockchain developers are giving more attention to how current networks can prepare for future cryptography risks.
XRP Ledger feature may support the transition
Ripple said the XRP Ledger has one built-in feature that could help during the transition. Unlike Ethereum, XRPL supports native key rotation, which allows users to replace vulnerable keys without moving their funds.
That design may make it easier for holders to respond if existing signature methods become unsafe. It also gives the network a direct way to manage account security without forcing full asset transfers during a migration.
The report added that more than 6.9 million Bitcoin sit in wallets with exposed public keys. XRP traded near $1.43 on Monday, up about 7% over the week as the broader crypto market moved higher.
Crypto World
A versatile crypto exchange built for every type of trader


Disclosure: This article does not represent investment advice. The content and materials featured on this page are for educational purposes only.
BYDFi marks rapid global growth with 1M users and multiple industry recognitions.
Summary
- BYDFi serves 1M+ users in 190+ countries, offering spot, futures, bots, and web3 trading.
- The platform added tokenized stocks, forex, and gold trading in USDT, expanding beyond crypto markets.
- BYDFi strengthens trust with proof-of-reserves, an 800 BTC protection fund, and a Ledger wallet partnership.
Overview
Website
https://www.bydfi.com
Founded
2020
Sector
Hybrid crypto exchange (CEX + DEX)
Registered Users
1,000,000+
Countries
190+
Spot Trading Pairs
1,000+
Derivatives Pairs
500+
Maximum Leverage
200x
KYC Requirement
No mandatory KYC
Key Recognition
Official Crypto Exchange Partner of Newcastle United (2025–Present)
What is BYDFi?
Launched in April 2020, BYDFi is a global cryptocurrency trading platform operating under the vision “BUIDL Your Dream Finance.” In just over five years, it has grown to serve more than 1,000,000 registered users across 190+ countries and regions, offering a broad suite of trading tools that spans spot markets, perpetual futures, copy trading, automated bots, and on-chain trading through its proprietary web3 engine, MoonX.
BYDFi has received multiple industry recognitions, including being ranked among the top global crypto exchanges by Forbes in 2023, as well as earning the Trusted Exchange Award 2025 from TrustFinance and being named Best Centralized Exchange (CEX) by BeInCrypto in 2025. The platform is also featured among the top 100 crypto exchanges by Coingecko.
One of BYDFi’s more distinctive moves came in 2025, when it announced a multi-year partnership with Newcastle United, becoming the Premier League club’s Official Crypto Exchange Partner. The partnership is a signal of its ambitions to grow its mainstream brand presence internationally.
Features
BYDFi’s feature set is one of the most comprehensive in the industry. Traders looking for derivatives exposure will find 500+ perpetual contract pairs with leverage up to 200x, which is notably higher than rivals like Binance (125x) and Bybit (100x). The platform supports USDT-margined, USDC-margined, and coin-margined futures, giving traders more flexibility in how they manage collateral.
A standout addition in 2026 is TradFi trading — the ability to trade tokenized stocks (AAPL, TSLA, AMZN, MSFT, and others), forex pairs, and commodities like Gold (XAUUSD), all settled in USDT with zero trading fees. This blurring of the line between crypto and traditional finance is a differentiator that few exchanges can claim.
For newcomers, BYDFi offers a demo account loaded with 50,000 USDT, allowing risk-free practice under real market conditions with full access to derivatives tools and leverage settings. Copy trading and a bot marketplace round out the toolkit, letting beginners mirror professional strategies without needing deep market expertise.
MoonX, BYDFi’s on-chain trading engine, supports Solana, BNB Chain, and Base, and comes with features including token safety indicators, copy trading, portfolio tracking, and a token launch platform called Pump. This gives the platform a genuine CEX+DEX dual-engine architecture, a model that few centralized exchanges have pursued as directly.
Security is addressed through a combination of over 1:1 proof-of-reserves (with periodic public reports), an 800 BTC protection fund added in September 2025, cold storage for the majority of user assets, multi-party transaction approvals, and segregated client accounts. In February 2025, BYDFi also launched a co-branded hardware wallet through a partnership with Ledger.
Pros and Cons
Among BYDFi’s clearest strengths is its no-KYC policy. Users can register with just an email address and immediately access the full range of spot, derivatives, copy trading, bot, and on-chain features. This is a significant advantage for privacy-conscious traders or those in regions where verification processes are slow or complex. Optional KYC unlocks higher withdrawal limits and P2P trading access.
The platform supports multiple languages to assist its global user base. It supports 22 languages and offers 24/7 live customer support, both in-app and on its website.
On the downside, the breadth of BYDFi’s product lineup can feel overwhelming at first glance. New users may need time to navigate between spot, derivatives, TradFi, MoonX, and the various bot strategies before finding their footing. The no-KYC approach, while appealing to some, also raises questions about long-term regulatory positioning as compliance requirements tighten globally.
Conclusion
BYDFi has quietly built one of the more feature-rich trading environments in the crypto space. From 200x leverage and TradFi integration to on-chain meme trading and an 800 BTC protection fund, it has made deliberate product choices that set it apart from generic exchange alternatives. Recognized by both Forbes and Crypto Expo Europe 2026’s Best All-in-One Crypto Trading Platform, it has earned external validation to match its internal ambitions. For traders who want more tools under one roof, without the friction of mandatory identity verification, BYDFi is a platform worth serious consideration.
Disclosure: This content is provided by a third party. Neither crypto.news nor the author of this article endorses any product mentioned on this page. Users should conduct their own research before taking any action related to the company.
Crypto World
Kevin Warsh’s Senate hearing: What to expect

Kevin Warsh, former member of the Federal Reserve Board of Governors.
Courtesy: Hoover Institution
Federal Reserve chair nominee Kevin Warsh travels to Capitol Hill on Tuesday to convince lawmakers he can carry out a presidential push for lower interest rates while remaining free of political constraints in setting policy.
In a much-anticipated hearing before the Senate Banking Committee, the former Fed governor will face questioning over a variety of subjects, from monetary policy to banking regulation to his own complicated personal finances
None likely will be more important than establishing the boundaries between the Fed’s decision-making and politics.
“He has a tricky communication question,” said Bill English, a professor at the Yale School of Management and the Fed’s director of monetary affairs from 2010-15, a period that overlapped with Warsh’s time there.
“I suspect that the way he’ll handle that is by being clear that his views are that rates can likely go lower, maybe a fair amount lower,” English said. “But at the same time, when asked directly about independence, be clear that he values independence. He thinks that independence is important and that a less independent Fed in the medium and long term would be a bad thing for the country.”
Political independence has been a key question surrounding the search for a successor to current Chair Jerome Powell.
Warsh views on independence
In remarks he’s scheduled to deliver to the committee at the hearing’s start, Warsh issued a qualified endorsement of Fed independence.
“So let me be clear: monetary policy independence is essential. Monetary policymakers must act in the nation’s interest, their decisions the product of analytic rigor, meaningful deliberation, and unclouded decision-making,” he said in prepared text.
However, he noted that doesn’t believe independence is endangered when the central bank’s actions are questioned by elected leaders, and said “the Fed must stay in its lane” and not veer into “fiscal and social policies where it has neither authority nor expertise.”

Warsh likely will face a bevy of questions about his political allegiance to President Donald Trump, who made no secret that a willingness to lower interest rates was a litmus test for his nominee. Trump nominated Warsh in late January, following a lengthy search process that included nearly a dozen candidates.
Congressional Democrats, including ranking member Sen. Elizabeth Warren, D-Mass., are expected to push the nominee on the independence question, as well as raise questions over his finances.
If confirmed, Warsh would easily be the wealthiest Fed chair in the central bank’s 113-year history. Disclosures filed ahead of the hearing indicate he would have to divest himself of a significant level of holdings to be in compliance with what have become strict Fed rules on where senior officials are allowed to invest.
Warren met with Warsh on Thursday and left with “deep concerns that if he is confirmed, he will be Donald Trump’s sock puppet.” She also alleged that Warsh had not disclosed “more than $100 million in assets.”
The nomination itself may take a while to get out of committee independent of any concerns about Warsh’s views.
Sen. Thom Tillis, R-N.C., has vowed to hold up the nomination until an investigation is completed from the U.S. Attorney’s Office in Washington, D.C. into renovations at Fed headquarters. A court overturned U.S. Attorney Jeanine Pirro’s subpoena of Powell, but she has vowed to appeal.
White House officials are confident Warsh ultimately will meet the approval of the committee, where Republicans hold a 12-10 advantage.
“My expectation is that after everybody sees him in his hearing and sees how deft on his feet he is, how knowledgeable about the Fed he is, and how good his ideas are about returning the Fed towards a place where it’s nonpartisan, that it’s going to be hard to resist voting ‘yes,’” National Economic Council Director Kevin Hassett said Monday on CNBC.
Forging consensus
Once in office, Warsh will head a Federal Open Market Committee populated with officials who have expressed misgivings about the next steps in monetary policy. While markets expect the committee to be on hold the rest of the year, officials themselves still have penciled in a cut and Warsh has expressed support for lower rates as well.
Warsh will “come in with an idea of what he would like to think about and do, and then the economy will deliver what we actually work on,” San Francisco Fed President Mary Daly said last week. “You work with the economy you have, and you plan for the economy that you’re supposed to achieve.”
As for his approach beyond rate-setting, Warsh last year called for regime change at the Fed and charged that current officials have a “credibility deficit” that he wants to fix.
English, the former Fed official, said his experience with Warsh was one who could work with others, a quality needed at the consensus-driven central bank.
“He was not somebody who was really difficult for the other policymakers or for the staff or for anybody to work with,” English said. “So I’m not sure he’s going to go in and really try to shake things up right away without moving the other policy makers along. To move them along, he’s going to have to be making arguments and making his case in a reasonable way.”
-

 News Videos6 days ago
News Videos6 days agoSecure crypto trading starts with an FIU-registered
-

 Fashion4 days ago
Fashion4 days agoWeekend Open Thread: Theodora Dress
-

 Sports4 days ago
Sports4 days agoNWFL Suspends Two Players Over Post-Match Clash in Ado-Ekiti
-

 Politics4 days ago
Politics4 days agoPalestine barred from entering Canada for FIFA Congress
-

 Business2 days ago
Business2 days agoPowerball Result April 18, 2026: No Jackpot Winner in Powerball Draw: $75 Million Rolls Over
-

 Crypto World4 days ago
Crypto World4 days agoRussia Pushes Bill to Criminalize Unregistered Crypto Services
-
 Politics16 hours ago
Politics16 hours agoGary Stevenson delivers timely reminder to register to vote as deadline TODAY
-

 Tech2 days ago
Tech2 days agoAuto Enthusiast Scores Running Tesla Model 3 for Two Grand and Turns It Into Bare-Bones Go-Kart
-

 Business5 days ago
Business5 days agoCreo Medical agree sale of its manufacturing operation
-
 Politics2 days ago
Politics2 days agoZack Polanski demands ‘council homes not luxury flats for foreign investors’
-

 Tech6 days ago
Tech6 days ago‘Avatar: Aang, The Last Airbender’ Leaked Online. Some Fans Say Paramount Deserves the Fallout
-

 Crypto World4 days ago
Crypto World4 days agoRussia Introduces Bill To Criminalize Unregistered Crypto Services
-

 Tech6 days ago
Tech6 days agoMicrosoft adds Windows protections for malicious Remote Desktop files
-

 Entertainment6 days ago
Entertainment6 days agoDave Portnoy Slams Dianna Russini: ‘Makes Zero Sense’
-

 Crypto World6 days ago
Crypto World6 days agoX Launches New Cashtag Feature for Stocks and Crypto: X
-

 Sports5 days ago
Sports5 days agoBritish climbers complete new route in Swiss Alps
-

 Sports7 days ago
Sports7 days agoYounger Than Sachin Tendulkar: Vaibhav Sooryavanshi Set To Make Historic India Debut
-
 Entertainment7 days ago
Entertainment7 days agoPrince Carter Brings Fans Front Row and Backstage at Boys 4 Life Tour
-
 Crypto World6 days ago
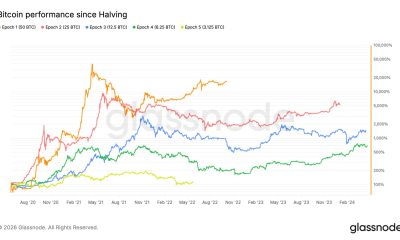
Crypto World6 days agoBitcoin surpasses halfway mark in current halving cycle
-
Entertainment2 days ago
NBA Analyst Charles Barkley Chimes in on Ice Spice McDonald’s Fiasco










You must be logged in to post a comment Login