Crypto World
Inside the Axiom Insider Trading Allegations


A senior Axiom staffer allegedly accessed sensitive user data, shared private wallet screenshots, and coordinated targeted trading strategies.
ZachXBT has alleged that an employee at Axiom Exchange abused internal access to sensitive user data.
In a series of posts, the prominent crypto investigator identified the employee as Broox Bauer and claimed he used internal tools at Axiom to look up private wallet information and track user activity for trading purposes beginning in early 2025.
Internal Tools Exploited
Axiom was founded in 2024 by Mist and Cal and later participated in Y Combinator’s Winter 2025 batch. ZachXBT said the platform quickly became one of the most profitable companies in the crypto sector, and generated more than $390 million in revenue to date. He stated that he was retained to independently investigate allegations of misconduct at the firm after receiving reports.
According to the investigator, Broox served as a senior business development employee at Axiom based in New York. In recorded clips from a private group call, Broox allegedly said he could track any Axiom user through referral codes, wallet addresses, or user IDs, and claimed he could “find out anything to do with that person.”
In the same recording, Broox allegedly described initially researching 10 to 20 wallets and gradually increasing that number to avoid drawing suspicion. ZachXBT said Broox also set rules for how others could request user lookups and stated he would send a full list of wallets.
The investigator further claimed that in April 2025, Broox shared a screenshot from an internal Axiom dashboard displaying private wallets belonging to a trader identified as “Jerry.” In August 2025, Broox allegedly shared another image showing registration details and connected wallets for a trader named “Monix.” That same month, he reportedly discussed looking up Axiom users who had traded the meme coin AURA.
According to ZachXBT, members of the group created a Google Sheet compiling wallet addresses for multiple key opinion leader (KOL) targets. The sheet allegedly mapped wallet data obtained through Axiom’s internal dashboard by Broox. Multiple KOLs named in the document or shown in leaked screenshots were contacted and independently confirmed that the wallet information attributed to them was accurate, the on-chain sleuth added.
You may also like:
One of the targeted traders was identified as Marcell, described as a KOL known for purchasing large portions of meme coin token supplies from private wallets before promoting them to followers. ZachXBT said such traders were considered prime targets because private wallet addresses are rarely public and address reuse is less common, which increases the value of privileged information.
ZachXBT stated that Broox’s main wallet was identified through private chat messages and that related addresses were mapped. However, he said that due to the high volume of meme coin trades, it was difficult to isolate specific high-confidence examples of insider trading without access to Axiom’s internal logs to review trade timing. Funds from related addresses were said to have flowed primarily to several centralized exchange deposit addresses.
The investigator also alleged that Broox discussed plans during a February 2026 recorded call to help a recently hired Axiom moderator, identified as Gowno (Seb), quickly profit $200,000 by abusing access to internal tools. ZachXBT claimed that Broox shared screenshots of exchange balances in private chats to show that the activity had already generated returns.
ZachXBT added that because Broox is based in New York City, the matter could potentially fall within the jurisdiction of the Southern District of New York.
On-Chain Crime Investigations
From linking “Lick” to wallets tied to over $90 million in suspected thefts and US government seizure-related funds, to uncovering a $5-10 billion “Black U” laundering market on Tron allegedly connected to the Lazarus Group, ZachXBT has built a reputation for tracing major crypto crime networks.
He detailed how stolen assets from hacks on platforms like Bybit were funneled through illicit channels, and separately exposed a Canadian scammer accused of stealing over $2 million via Coinbase support impersonation schemes.
Binance Free $600 (CryptoPotato Exclusive): Use this link to register a new account and receive $600 exclusive welcome offer on Binance (full details).
LIMITED OFFER for CryptoPotato readers at Bybit: Use this link to register and open a $500 FREE position on any coin!
Crypto World
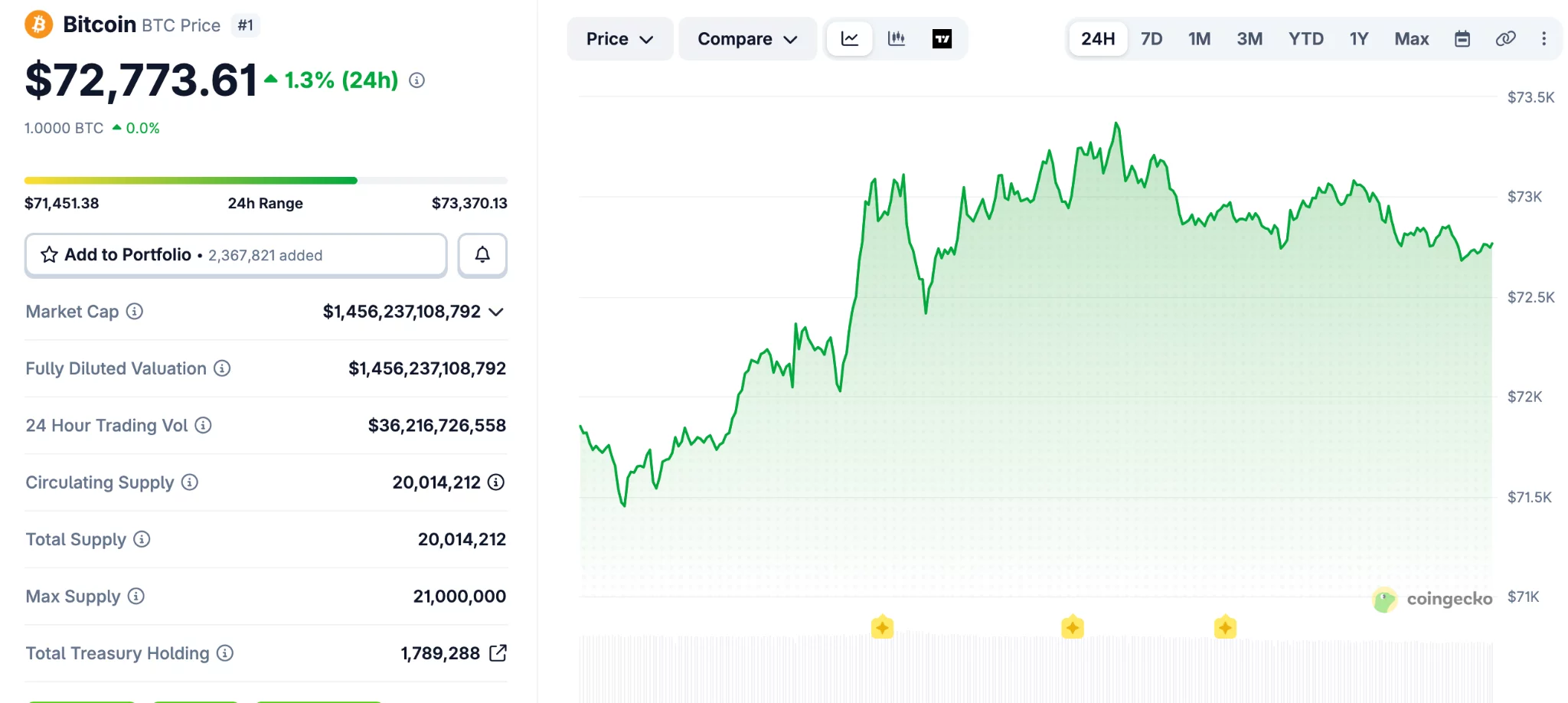
WLFI drops to record low after token-backed loan draws ccrutiny
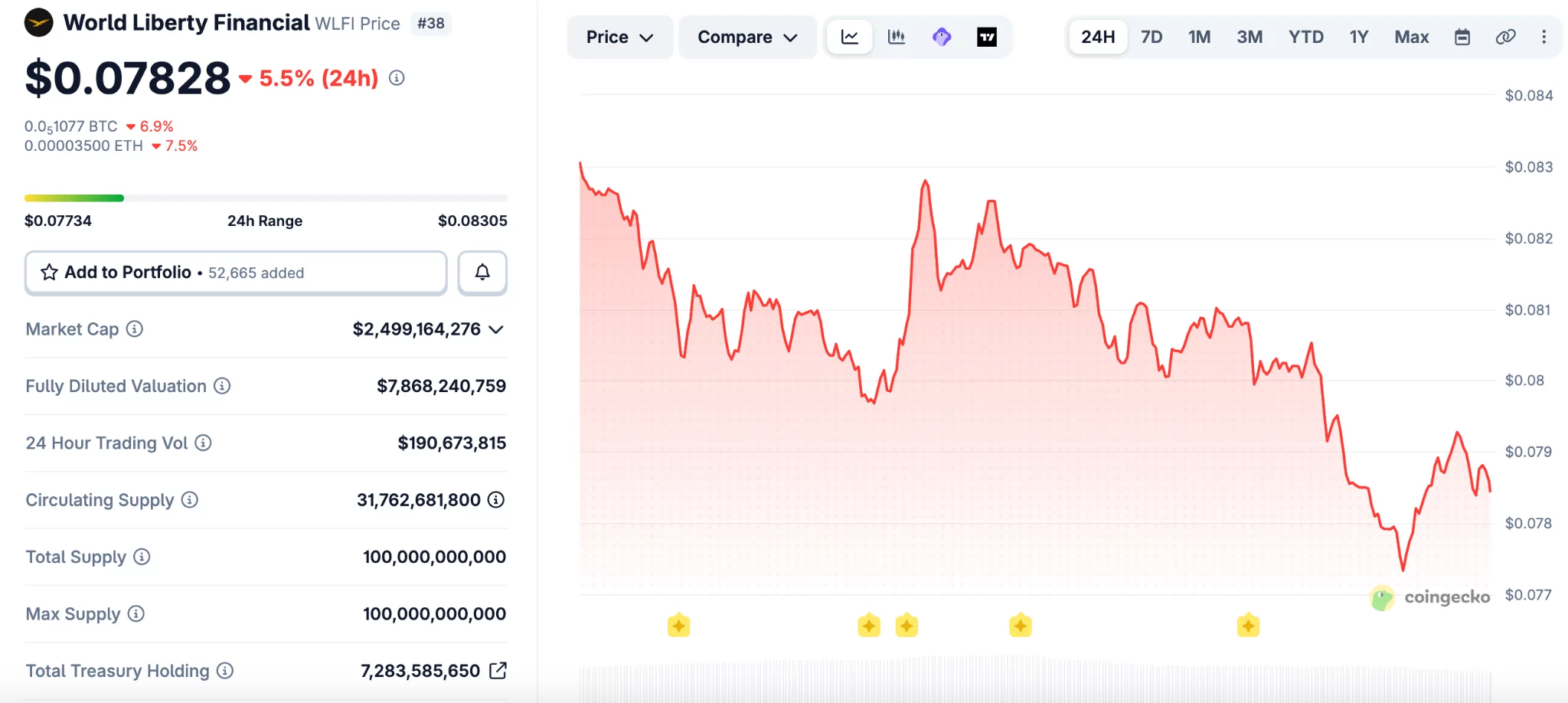
WLFI (WLFI) fell to a new all-time low on Saturday after onchain data showed wallets linked to World Liberty Financial used large token holdings to borrow stablecoins.
Summary
- WLFI fell to a record low after a self-backed loan raised fresh market risk questions.
- Onchain data showed linked wallets used 5 billion WLFI tokens to borrow stablecoins on Dolomite.
- World Liberty said its positions remain safe and framed the lending move as yield strategy.
The move added pressure to the Trump-linked project as traders weighed the risk tied to using its own token as collateral.
WLFI dropped to about $0.077, its lowest level on record, before trading near $0.079. The token is now down 76% from its peak of $0.33 reached in September, based on CoinGecko data.
The decline followed reports that wallets tied to World Liberty Financial deposited about 5 billion WLFI tokens on Dolomite. The same position was then used to borrow $75 million in USD1 and USDC.\
Arkham data showed that more than $40 million of the borrowed funds later moved to Coinbase Prime. That transfer drew more attention to the project’s financing activity and the size of its exposure.
The market reaction was swift because WLFI is not viewed as a deeply liquid asset. A large collateral position tied to price swings can increase pressure if the token falls further.
DeFi users on X said the structure could create risk for lenders if WLFI moves closer to liquidation levels. Some pointed to the token’s high fully diluted valuation and limited trading depth as a weak point.
“WLFI has almost a $10 billion FDV, but it is not an extremely liquid asset,” wrote one user. “So imagine what would happen if 5% of WLFI’s total supply would suddenly need to be sold to liquidate the position.”
Another user compared the setup to borrowing cash against self-created value. The user said,
“It’s the financial equivalent of printing casino chips, borrowing cash against them, and telling everyone else not to panic because the house still believes in the chips.”
Dolomite remains a smaller player in DeFi lending. DefiLlama ranks it 19th among lending platforms by total value locked, which added more focus to the size of the WLFI-linked position.
World Liberty defends the strategy
World Liberty Financial responded on social media and said its positions remain well above liquidation thresholds. The project described itself as an “anchor borrower” and said the strategy supports yield generation.
The team wrote,
“Everyday users are earning outsized stablecoin yields right now — at a time when traditional markets are offering very little.” It added, “That’s the whole point.”
The project also said it plans to introduce a governance proposal for early retail holders. The proposal would replace immediate token access with a phased vesting schedule, subject to a community vote.
Disclosure: This article does not represent investment advice. The content and materials featured on this page are for educational purposes only.
Crypto World
Aethir Contains Bridge Hack While Losses Stay Below $90K


Aethir said it remains fully operational after containing an attack on its ATH bridge contracts.
Summary
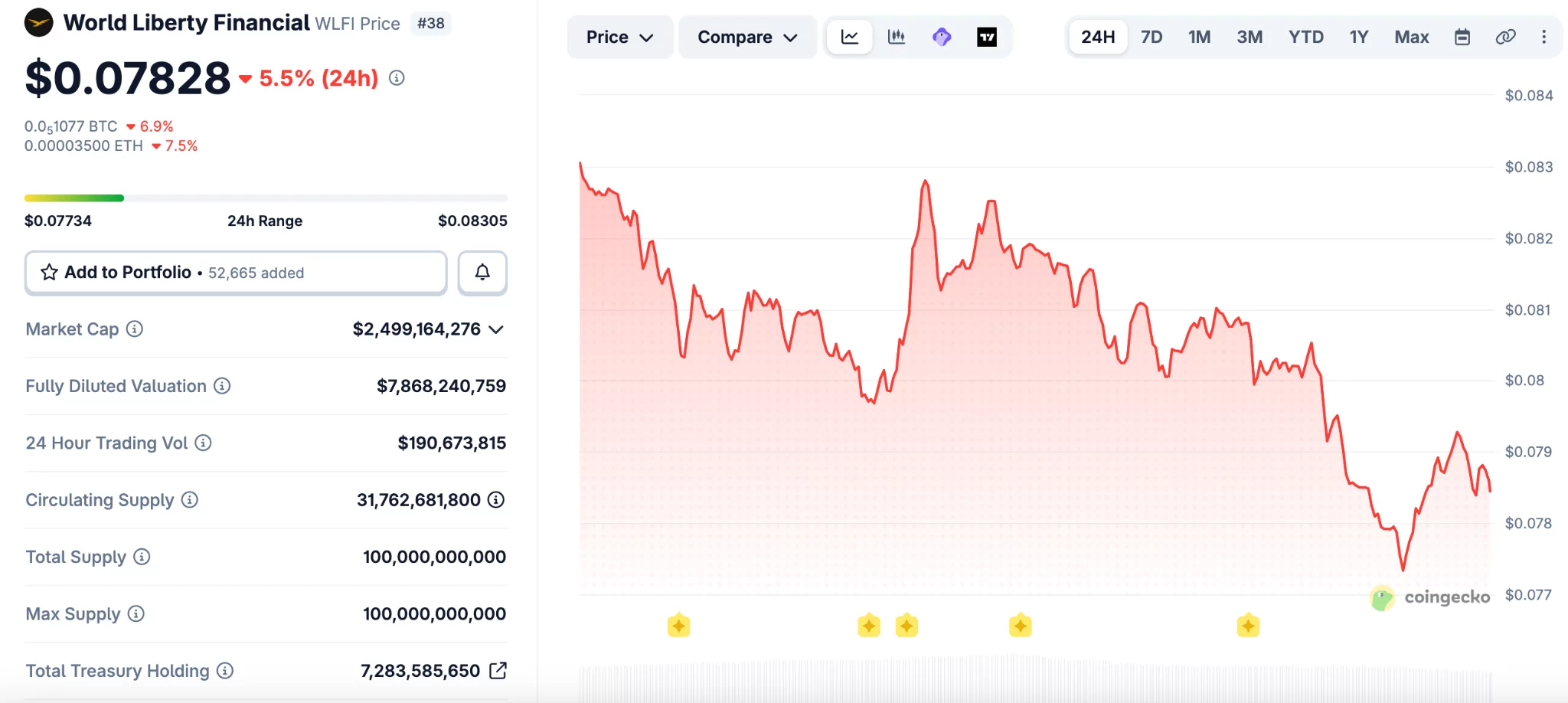
- Aethir said it contained the ATH bridge exploit quickly and kept total user losses below $90,000.
- The company said Ethereum ATH supply stayed intact while affected contracts were disconnected to stop losses.
- PeckShield first estimated higher losses, while Aethir said compensation details will arrive next week soon.
The company said the exploit did not affect the main ATH supply on Ethereum, while user losses stayed below $90,000.
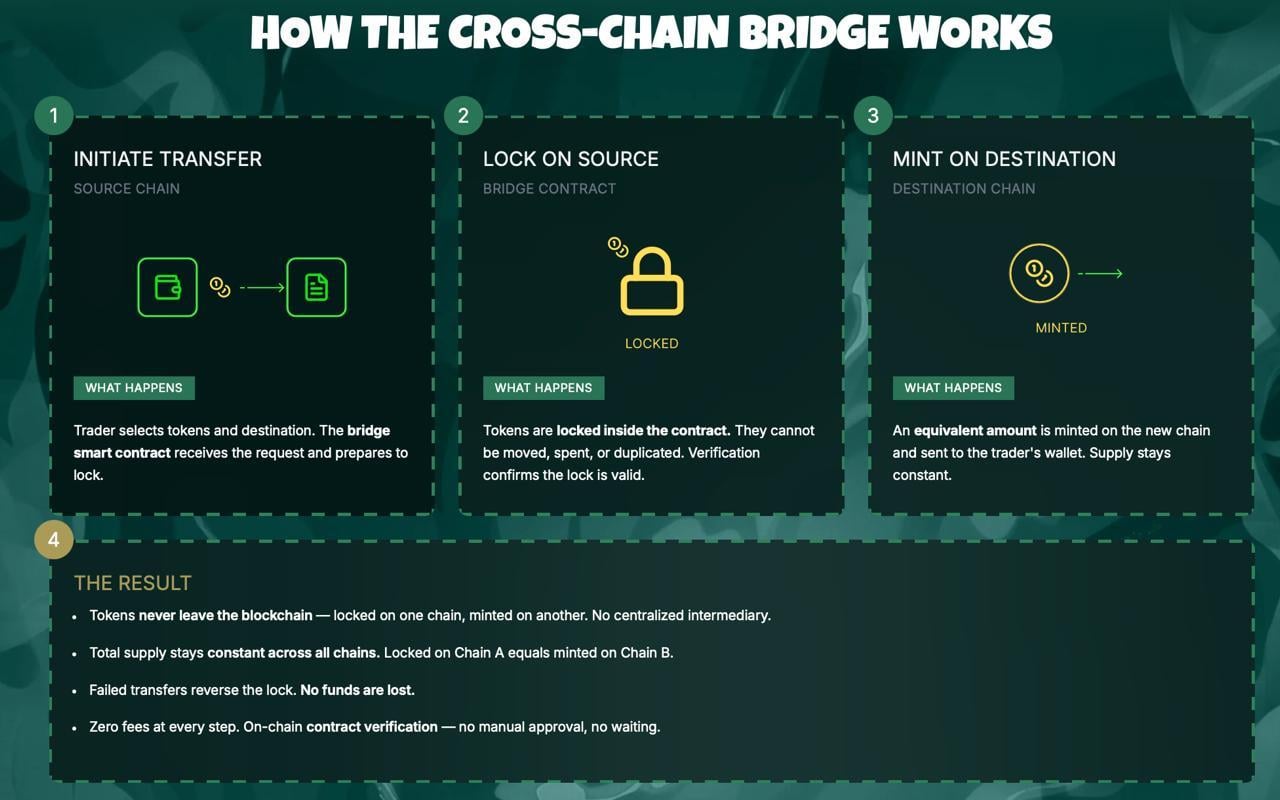
Aethir said it detected a malicious attack targeting ATH bridge contracts that connect Ethereum with other chains. The company said it disconnected all affected contracts soon after finding the issue and stopped further damage.
The team added that the ETH-ARB bridge on Squid was not affected during the incident. It also said the main ATH supply on Ethereum remains intact, which helped prevent wider disruption across the network.
Aethir said it will share a full compensation plan next week. The company also said it is working with authorities and exchange partners to trace the attacker and block related funds.
“A full attacker wallet list will be posted in Discord as we monitor the funds,” Aethir said, in its update.
It added that a detailed memo will explain what happened, which users were affected, and how compensation will work.
Aethir credited several exchanges for acting quickly after the exploit. The company named Binance, Upbit, Bithumb, and HTX among the platforms that blacklisted identified wallets tied to the incident.
The project also thanked ZeroShadow for helping with analysis during the response. Aethir said that early action from partners helped limit the scope of the losses and support the ongoing investigation.
PeckShield had flagged the exploit a day earlier and initially estimated losses at about $400,000. The blockchain security firm also said the attacker moved funds from BNB Chain to Tron through several addresses.
That early estimate differed from Aethir’s latest figure of under $90,000 in user losses. The gap places more attention on fund tracing and the final accounting of the incident.
Crypto attacks continue to pressure the market
The Aethir case comes as crypto security breaches keep hitting the market. PeckShield recently said losses from 20 security incidents reached about $52 million in March, nearly double the February total.
The firm also pointed to a growing pattern where one exploit can spread stress across linked DeFi platforms. Those events can weaken liquidity, create bad debt, and strain lending markets beyond the first target.
PeckShield cited ResolvLabs and Venus Protocol as recent examples of wider fallout after exploits. It also noted targeted attacks on individuals, including a multimillion-dollar theft tied to social engineering on Kraken. The trend has carried into April as other platforms deal with new attacks.
Crypto World
Binance New Listing Calendar Heats Up as Strategy Holds 766,970 BTC and One Presale Fills Fast
Strategy now holds 766,970 BTC worth over $54 billion after buying roughly 45,000 BTC in the past 30 days, proving the largest corporate holder is not slowing down even with BTC above $71,000.
The binance new listing calendar is where the next round of returns gets decided, and the presale filling fastest right now is the one with a confirmed spot on that calendar.
Pepeto is approaching its listing date with more than $8.87 million raised and the cofounder who built the original Pepe coin, and wallets are rushing to lock in the presale entry before stages close.
Strategy bought roughly 45,000 BTC over the past month, pushing its total to 766,970 BTC per CoinDesk. The company launched its STRC offering to fund more purchases, and the position now tops $54 billion.
BTC cleared $72,700 after the ceasefire rally that wiped $600 million in shorts per Bloomberg, and the next confirmed binance new listing is where presale holders turn floor entries into returns that BTC at current prices cannot match.
How BNB, SOL, and the Next Binance New Listing Compare for Returns
Pepeto: What Happens When a Working Exchange Hits the Binance New Listing Calendar
Most tokens land on Binance with a whitepaper and a promise. Pepeto lands with a finished exchange that already runs live trades, and that difference is why the binance new listing for this token is getting more attention than any other presale this cycle.
Zero fee swaps keep positions whole. The bridge moves tokens across chains without charging a cent. The contract scanner catches rug pulls before a dollar goes in. All three tools are live, not coming soon, live.
The presale hit $8.87 million during extreme fear while the rest of the market froze, and the Pepe cofounder who took 420 trillion tokens to $11 billion with nothing behind it is building a real exchange this time. Every contract cleared a SolidProof audit, 186% APY staking grows every position, and analysts model 100x to 300x starting at the $0.0000001863 entry.
The presale fills faster each round because the wallets inside know what listing day does, it replaces this price permanently and the return belongs only to the wallets that got in while the number still existed. The binance new listing date is the clock, and every hour closer is one hour less before the entry is gone.
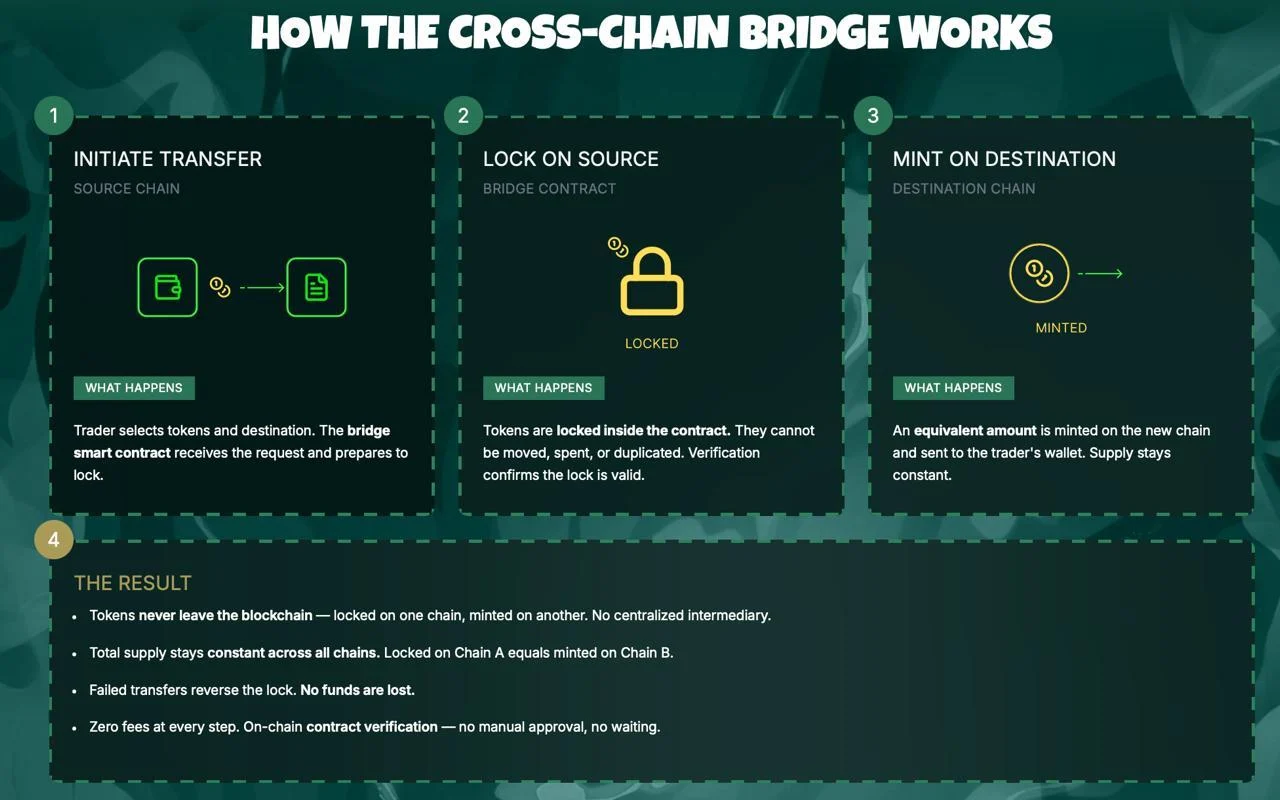
BNB: Exchange Token Holds $605 but Upside Stays Measured
BNB holds near $605 with quarterly token burns and Binance volume keeping demand steady per CoinMarketCap.
New listings on Binance historically lift BNB as traders move capital onto the platform, and the upcoming Pepeto listing adds another event to the calendar.
BNB offers stability, but from $605 the path to $900 is roughly 50%, far from the kind of return a presale floor delivers when the binance new listing opens the gap between entry and market price.
Solana: SOL Sits at $84 With Strong Fundamentals but Limited Ceiling
SOL trades near $84 after commodity classification cleared regulatory clouds per CoinGecko. Nine ETF filings and the Alpenglow upgrade add long term weight, and institutional ownership of SOL products sits at 48.8%, the highest of any crypto fund.
CME Group also plans SUI and AVAX futures for May, showing derivatives markets are expanding beyond BTC and ETH. SOL is strong, but from $84 even a move to $300 delivers 3.5x over months while presale entries hold the spread between presale and listing where the widest returns get built.
Conclusion
Strategy’s 766,970 BTC proves long term confidence in digital assets, but the wallets watching the binance new listing calendar are looking past large caps toward presale entries with real weight. Pepeto has the live exchange, the capital, and the confirmed listing to back it.
The last stage sold out ahead of schedule, and this one fills while these words load. The presale price stops existing the moment the binance new listing date arrives, and the returns belong only to the wallets that got in while the door was still open.
Click To Visit Pepeto Website To Enter The Presale
FAQs
What is the most expected binance new listing in 2026?
Pepeto leads with $8.87 million raised, a live exchange with zero fee trading, and a confirmed listing date. The Pepe cofounder and SolidProof audit give it the strongest profile this cycle.
Can a binance new listing deliver bigger returns than holding BNB or SOL?
BNB at $605 offers 50% to $900 and SOL at $84 targets 3.5x to $300. Presale entries at floor price carry the listing gap where the widest returns in every cycle get built.
Disclaimer: This is a Press Release provided by a third party who is responsible for the content. Please conduct your own research before taking any action based on the content.
Crypto World
Bitcoin nears $73K again as ETH and HYPE push higher
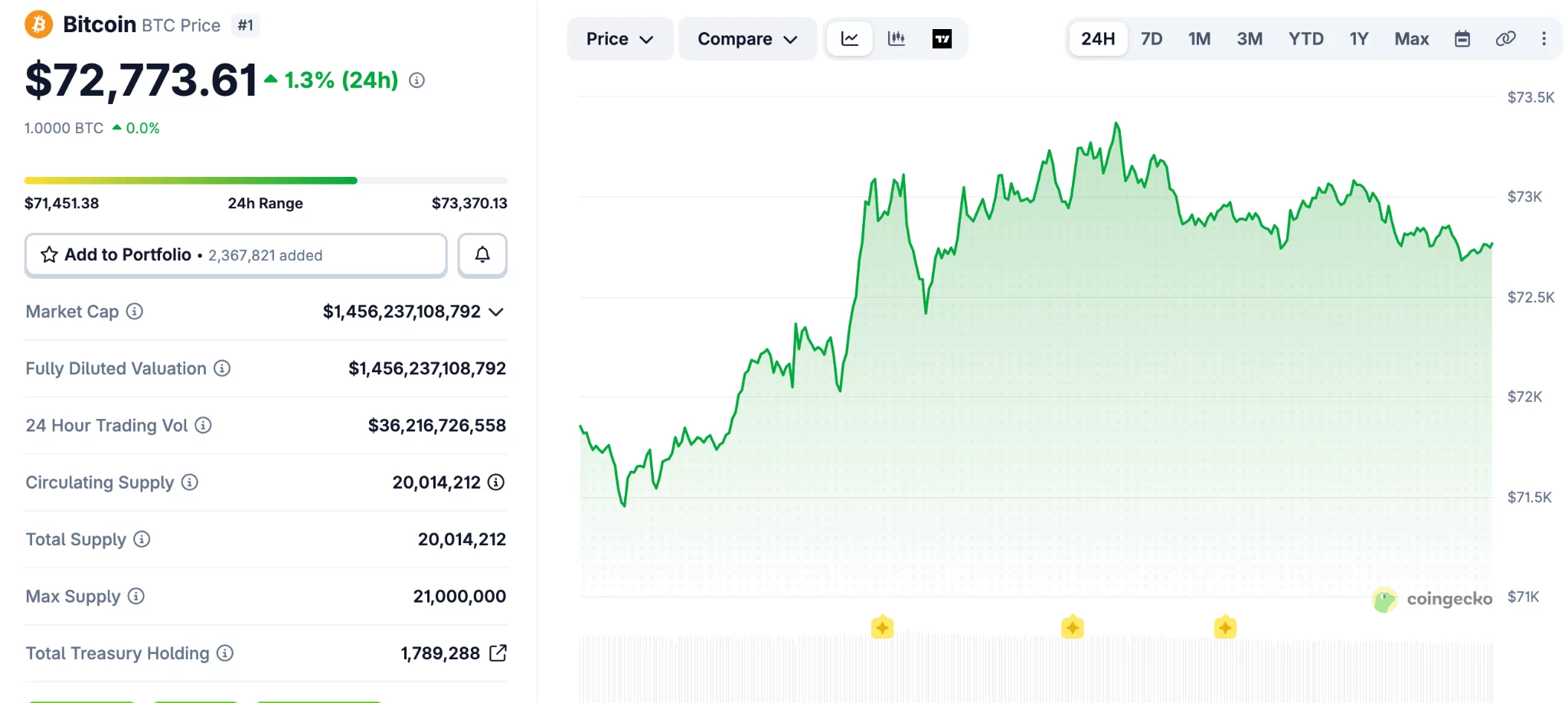
Bitcoin (BTC) extended its upward move over the past 24 hours and reached its highest level in three weeks.
Summary
- Bitcoin climbed above $73,000 as traders weighed cease-fire updates and stronger March CPI data yesterday.
- Ethereum moved back above $2,200, while HYPE and DASH posted gains across the altcoin market.
- RAVE surged 100% in one day and entered the top 100 tokens.
The broader crypto market also moved higher, with Ethereum (ETH), HYPE (HYPE), and RAVE among the tokens posting gains.
Bitcoin traded in a tight range between $66,000 and $67,000 over the weekend. That changed on Monday when the asset moved above $70,000 after reports said the United States and Iran had started talks.
The price later slipped below $68,000 after follow-up reports challenged that claim. Bitcoin then turned higher again on Tuesday after both sides announced a “two-week cease-fire,” which supported market sentiment.
The asset kept climbing even after March CPI data showed stronger inflation. It reached $73,500 earlier today, its highest level since March 18, before easing slightly below $73,000.
Bitcoin’s market value rose to $1.455 trillion, according to CoinGecko data. Its share of the total crypto market also increased over the past week and now stands above 57%.
Ethereum, HYPE, and RAVE lead altcoin gains
Ethereum moved back above the $2,200 mark after a 2.3% daily rise. BNB also traded higher and moved past $600, while HYPE climbed more than 5% and reclaimed $40.
Most large-cap altcoins followed the same direction, though gains remained moderate. A few tokens, including WLFI, XMR, and CC, posted small losses during the session.
RAVE recorded the strongest move among the top gainers. The token jumped 100% in one day and extended its weekly gain to about 700%, which pushed it into the top 100 assets by market value.
DASH also posted a sharp advance and moved above $45 after a 13% gain. SIREN added 10% and returned to the $0.80 level.
The total crypto market value increased by more than $100 billion from last week. It stood at $2.530 trillion at press time, showing broader strength across the sector.
Disclosure: This article does not represent investment advice. The content and materials featured on this page are for educational purposes only.
Crypto World
Iran Bitcoin toll report raises questions over oil ship payments


Reports that Iran may accept crypto for oil tanker tolls in the Strait of Hormuz have sparked debate across the digital asset market.
Summary
- Reports on Iran’s possible crypto tolls for oil tankers have split opinion across Bitcoin and stablecoin circles.
- Analysts said stablecoins face freeze risks, while Bitcoin supporters called BTC harder to block or control.
- Galaxy’s Alex Thorn said tanker payments may use Bitcoin addresses, not Lightning, due to size limits.
The discussion followed a Financial Times report that linked the proposal to Iran’s efforts to reduce exposure to US sanctions.
Market participants have focused on one question: whether Bitcoin would play a real role in such payments. Conflicting claims have since pointed to stablecoins or Chinese yuan as other possible options.
The latest debate started after reports said Iran was considering Bitcoin payments for ships crossing the Strait of Hormuz. The waterway remains one of the world’s busiest energy routes, which has pushed the topic beyond crypto circles and into wider market discussions.
Alex Thorn, head of firmwide research at Galaxy, said later reports did not fully support the original Bitcoin claim. He said some accounts suggested the tolls could instead be settled in stablecoins or Chinese yuan, which left the payment method unclear.
That uncertainty has driven much of the reaction from Bitcoin supporters and market analysts. With no confirmed payment framework in place, traders and industry figures have treated the story as a developing issue rather than a settled policy.
The lack of an official and detailed public plan from Iranian authorities has also kept room for doubt. For now, the crypto market is responding more to reports and commentary than to a final rule.
Bitcoin and stablecoins draw different arguments
Bitcoin supporters argued that BTC would be harder for outside parties to freeze or block. Justin Bechler said, “USDT and USDC include built-in blacklist functions at the smart contract level,” adding that issuers can freeze funds when addresses are flagged.
He also said, “Bitcoin has no issuer, no compliance officer to pressure, and no freeze function.” That argument has pushed some market participants to present Bitcoin as a more resilient option for cross-border settlement under sanctions pressure.
Still, that view has not settled the debate. Stablecoins remain widely used in global crypto payments because they reduce price swings, and that may still matter for any large commercial transaction tied to oil shipping.
The discussion also reflects the difference between theory and practice. A payment method may look strong on paper, but large state-linked payments depend on speed, scale, compliance risk, and operational ease.
Payment size and logistics remain key issues
Thorn estimated that tanker tolls could range from $200,000 to $2 million per ship. That size has raised doubts about whether the Lightning Network would be the main rail, even though some early reporting suggested a payment could be completed within seconds.
He said the more likely setup would involve Iran providing a QR code or a Bitcoin address after approving a ship’s passage. That method would avoid the limits that can affect very large Lightning payments.
Thorn also noted that the largest known Lightning transaction to date was about $1 million. That figure matters because some tanker tolls may sit above that level, which could make direct onchain settlement or pre-arranged transfers more practical.
Crypto World
WLFI Drops to Record Low After Token-Backed Borrowing Raises Risk Concerns
WLFI, the native token of the Donald Trump–backed World Liberty Financial platform, sank to an all-time low on Saturday as crypto users expressed concerns after revelations that the project used a large amount of its own tokens to take out loans.
The token hit a new low of around $0.07714 on Saturday, down 83% from its peak of $0.46 reached last September, according to data from CoinMarketCap. WLFI is currently at $0.07879, down by 4.66% over the past day.
The downturn came after it was revealed that wallets linked to World Liberty Financial deployed substantial WLFI holdings as collateral on Dolomite, a decentralized lending platform co-founded by the project’s chief technology officer, Corey Caplan.
Onchain data from Arkham shows that a wallet linked to World Liberty Financial deposited around 5 billion WLFI tokens on Dolomite. The wallet then used the tokens as collateral to borrow $75 million in USD1 and USDC (USDC) stablecoins, later transferring more than $40 million to Coinbase Prime.
Related: CFTC unveils innovation task force members in crypto clarity push
WLFI-backed loan position sparks concerns
The large collateral position has raised concerns among DeFi analysts, who warn it could create risks for lenders on Dolomite if WLFI’s price falls and approaches liquidation levels.
“WLFI has almost a $10 billion FDV, but it is not an extremely liquid asset,” one user wrote on X. “So imagine what would happen if 5% of WLFI’s total supply would suddenly need to be sold to liquidate the position,” he added.
Another X user argued that the setup resembles creating artificial “chips” and borrowing against them. “It’s the financial equivalent of printing casino chips, borrowing cash against them, and telling everyone else not to panic because the house still believes in the chips,” they claimed.
Dolomite has a relatively small footprint in decentralized finance, ranking 19th among lending platforms by total value locked, according to DefiLlama.
Related: White House warns staff as Iran bets add to growing insider trading concerns
World Liberty defends WLFI lending
World Liberty Financial acknowledged the lending activity on social media, but sought to calm markets, stating that its positions remain well above liquidation thresholds. The project described itself as an “anchor borrower” for WLFI and argued that the strategy helps generate yield.
“Everyday users are earning outsized stablecoin yields right now — at a time when traditional markets are offering very little. That’s the whole point,” the project wrote on X.
On Friday, World Liberty said it will soon introduce a governance proposal to create a phased unlock schedule for WLFI tokens held by early retail buyers, replacing immediate access with a long-term vesting plan subject to community vote.
Magazine: Bitcoin may take 7 years to upgrade to post-quantum — BIP-360 co-author
Crypto World
Court blocks Arizona’s bid to regulate Kalshi’s event contracts

A federal court in Arizona has granted a temporary shield for Kalshi against state-level gambling enforcement, aligning with U.S. regulators in a widening dispute over whether Kalshi’s event-based contracts belong under federal derivatives law or under state betting statutes. Judge Michael Liburdi issued the order at the request of the Commodity Futures Trading Commission (CFTC) and the federal government, effectively blocking Arizona from pursuing civil or criminal actions against Kalshi on contracts listed on CFTC-regulated markets.
The core question of the case is how to classify Kalshi’s “event contracts”—whether they are swaps governed by the Commodity Exchange Act (CEA) or purely gambling under state law. The court indicated that the CFTC is likely to prevail in arguing that the contracts fall within the federal framework, which would give the agency exclusive authority over swaps traded on designated contract markets. The temporary restraining order will hold until April 24, 2026, as the court weighs a longer-term preliminary injunction.
Key takeaways
- The Arizona court temporarily halts state enforcement against Kalshi’s event contracts, pending a ruling on a longer injunction and federal jurisdiction.
- The judge found the CFTC is likely to succeed in classifying Kalshi’s contracts as swaps under the CEA, placing them under federal oversight.
- The decision highlights a broader tension between state gaming laws and federal derivatives regulation as regulators seek uniform treatment for prediction-market products.
- The ruling comes as other states and regulators take related steps—Nevada has extended its ban on Kalshi’s event-based contracts, and Utah has moved to classify such bets as gambling; New Jersey enforcement challenges have also featured in related coverage.
- Kalshi’s status remains unsettled as the legal process continues, with observers watching how the federal/state dynamic will evolve for prediction markets nationwide.
Federal jurisdiction vs. state gambling laws in the Kalshi case
At the heart of the Arizona order is the question of whether Kalshi’s event contracts should be treated as swaps traded on designated contract markets—subject to federal regulation under the CEA—or as gambling offerings governed by state statutes. The CFTC and the Department of Justice argued that the contracts resemble traditional financial instruments because they are contingent on the outcome of real-world events and are cleared on regulated marketplaces. The court agreed that, based on the arguments presented, the CFTC has a strong likelihood of proving the contracts qualify as swaps, thereby placing them under federal jurisdiction.
Arizona authorities had signaled intent to pursue enforcement actions under local gambling rules. The court’s restraining order explicitly blocks such actions while the case proceeds, maintaining a default status quo that preserves Kalshi’s ability to offer its event contracts on federally regulated venues without immediate state-level interference.
Context: a broader patchwork of state actions
The Arizona decision sits inside a wider regional contest over the status of prediction-market products. Kalshi and similar platforms have faced varying treatment across states, with regulators arguing that the products resemble traditional gambling while platform proponents emphasize their roots in financial market design and risk-trading mechanics.
Nevada has already taken a tougher stance, with a judge extending a ban on Kalshi’s offerings in the state, concluding that the contracts closely resemble sports betting and fall under state gaming laws. That ruling underscores the potential for disparate regulatory outcomes as states apply their own legal lenses to prediction markets.
Meanwhile, Utah lawmakers moved to block Kalshi and Polymarket by classifying proposition-style bets on in-game events as gambling, signaling a broader appetite among some state governments to restrict such offerings despite federal regulatory perspectives. In related coverage, a US appeals court previously upheld a decision preventing enforcement against Kalshi in New Jersey, illustrating a fragmented regulatory landscape that Kalshi and its peers must navigate as they scale.
Implications for investors, traders, and the broader ecosystem
For participants in Kalshi’s market, the Arizona ruling reinforces the importance of regulatory clarity when evaluating risk, liquidity, and legal exposure. Federal preemption, if upheld in the longer injunction, could provide a more uniform operating environment for event contracts traded on Kalshi’s platform, potentially stabilizing trading activity across jurisdictions that recognize the federal framework. Conversely, continued state actions—such as Nevada’s ongoing restrictions and Utah’s legislative moves—could constrain Kalshi’s reach and create jurisdictional risk for traders who rely on access to multiple markets.
From a market structure perspective, the decision illustrates how the treatment of prediction markets can pivot on regulatory interpretation. If courts consistently categorize event contracts as swaps, the federal regime could promote standardized disclosure, risk controls, and oversight on trading venues. If states succeed in carving out exceptions or maintaining strict gambling classifications, traders may face a more fragmented landscape with varying access and compliance requirements by venue and state.
Regulators’ stance matters for investors looking at the long-term viability of prediction-market infrastructure. A federal framework that categorizes these products as swaps would align Kalshi with traditional derivatives market design, including clearing, margin, and therefore potential counterparty risk mitigation. However, it would also place these offerings under the same set of rules that govern swaps, which can carry stringent capital and reporting requirements—factors that shape product design, pricing, and user experience.
What’s next
The court will decide whether to extend the injunction beyond April 24, 2026, and how to balance Kalshi’s operations with state enforcement considerations. While the CFTC’s position remains central to the case, the evolving regulatory environment suggests that further developments are likely across multiple states as lawmakers reassess how prediction markets should be treated under gambling or financial-law paradigms.
As Kalshi and other platforms navigate this regulatory mosaic, traders and developers should monitor: potential federal rulings on the classification of event contracts, any new state laws tightening or loosening constraints, and the continued interplay between state enforcement actions and federal oversight that could shape the trajectory of prediction-market products in the United States.
Crypto World
Crypto Market Drops 22% in Q1 2026, But Structural Quality Reaches Record Highs: Report

TLDR:
- Stablecoin market cap hit $320B in Q1 2026, with monthly transfer volumes peaking at $1.8T.
- Systemic leverage compressed to ~3% after October’s deleveraging, reshaping how crypto trades.
- Corporate Bitcoin holdings crossed 1.13M BTC, with treasury strategies turning actively managed.
- Bitcoin ETPs attracted $18.7B in global inflows, with March alone bringing $1.3B net back in.
Digital asset markets fell sharply in the first quarter of 2026, shedding roughly 22% of total market value. Total capitalisation dropped to approximately $2.42 trillion, according to AMINA Bank’s Q1 Crypto Market Monitor.
Yet beneath the price decline, core adoption metrics hit record highs. Stablecoin supply reached $320 billion, corporate Bitcoin reserves crossed 1.13 million BTC, and systemic leverage compressed to around 3%.
Leverage Collapses as Market Structure Resets After October Shock
According to the AMINA Bank report , the October 2025 deleveraging event fundamentally reset how digital assets trade.
Reflexive, momentum-driven rallies gave way to a market built on spot flows and structured hedging. That transition defined Q1 2026.
Total trading volume reached $20.57 trillion for the quarter. Derivatives accounted for $18.63 trillion of that figure. Within derivatives, the composition shifted.
Bitcoin options open interest consistently exceeded perpetual futures, with positions weighted toward downside protection. That shift, highlighted in AMINA Bank’s report, signals that institutional participants are managing risk rather than chasing direction.
The macro backdrop accelerated the repricing. US inflation held at 2.7% while GDP expanded 5.3%. The Federal Reserve kept rates at 3.50% to 3.75%, with markets pricing out cuts for the year.
In late February, geopolitical escalation in the Middle East led to the Strait of Hormuz closure. Oil surpassed $112 per barrel. Risk appetite fell across asset classes.
Through that pressure, Bitcoin held above prior lows. It also showed resilience following Google’s Quantum AI paper, which triggered a fresh wave of quantum computing fears.
When markets absorb bad news without breaking down, AMINA Bank’s report frames that pattern as evidence of seller exhaustion.
Bitcoin Treasury Strategies Go Active as Stablecoins Become Financial Rail Infrastructure
Bitcoin maintained approximately 56% market dominance through the quarter. Corporate accumulation continued, but the behaviour behind it changed. Treasury strategies moved from passive holding to active capital management.
Strategy Inc. added nearly 65,000 BTC during Q1, lifting total holdings to 762,000 BTC. Japan-based Metaplanet scaled its position to over 40,000 BTC.
MARA Holdings sold more than 15,000 BTC to optimise its balance sheet. The divergence illustrates that corporate Bitcoin exposure is no longer uniform. It is becoming a managed allocation decision.
ETF flows reflected a similar dynamic.
The quarter recorded modest net outflows overall, but March reversed that trend with over $1.3 billion in net inflows. Globally, exchange-traded products drew $18.7 billion in inflows for the period, according to AMINA Bank’s data.
Stablecoins emerged as the quarter’s most structurally important development. Monthly transfer volumes peaked at $1.8 trillion. Solana led throughput, processing approximately $650 billion in monthly stablecoin volume.
New purpose-built chains including Plasma, Arc, and Tempo entered development specifically for stablecoin settlement. The GENIUS Act framework also moved into its operational phase, introducing formal rulemaking for payment stablecoins in the US.
DeFi total value locked rose to $92.43 billion. Tokenised real-world assets crossed $20 billion in market capitalisation. AI-driven agents executed over 120 million on-chain transactions during the quarter.
Ethereum, despite a 35% price decline, retained over 56% of total DeFi value locked. Its forthcoming Glamsterdam upgrade targets Layer 1 throughput through enshrined proposer-builder separation and block-level parallel execution.
In public markets, selectivity replaced appetite. BitGo’s post-IPO performance declined 44%. Kraken paused its IPO plans.
Circle, by contrast, posted strong revenue growth as USDC circulation expanded, reinforcing that capital is still flowing to sustainable infrastructure models.
Crypto World
Arizona barred from acting against Kalshi event contracts


A federal judge in Arizona has temporarily stopped state officials from enforcing gambling laws against Kalshi, a prediction market platform regulated by the Commodity Futures Trading Commission.
Summary
- A federal judge paused Arizona action against Kalshi and backed the CFTC’s jurisdiction argument.
- The restraining order blocks Arizona enforcement until April 24 as the case moves forward.
- State and federal officials remain split on whether event contracts are swaps or gambling.
The ruling adds to the legal fight over whether event-based contracts should be treated as financial products under federal law or as gambling under state rules.
The order came from Judge Michael Liburdi of the US District Court for the District of Arizona. The court granted a request from the CFTC and the federal government to pause Arizona’s action while the case moves ahead. The restraining order will stay in place until April 24 as the court considers the next step.
The case centers on Kalshi’s event contracts, which let users trade on the outcome of real-world events. The CFTC argued that these products qualify as swaps under the Commodity Exchange Act and therefore fall under federal oversight rather than state gambling law.
The court said the federal government is likely to succeed on that argument. That finding led the judge to block Arizona from starting or continuing civil or criminal action tied to contracts listed on CFTC-regulated markets. The ruling also paused Arizona’s criminal case against Kalshi.
Additionally, Arizona had moved against Kalshi under state gambling rules and filed criminal charges tied to event-based trading. State prosecutors argued that Kalshi was offering unlawful betting products, including contracts tied to political events and sports outcomes.
After the CFTC stepped in, the federal court halted that effort. The order means Arizona officials cannot continue enforcement tied to Kalshi’s contracts during the current restraining period. Reports also said a scheduled arraignment was called off after the ruling.
Wider fight over prediction markets
The Arizona case is part of a wider dispute over prediction markets in the United States. On April 6, a federal appeals court ruled that New Jersey could not restrict Kalshi’s sports-related event contracts, finding that the CFTC has exclusive jurisdiction over those products.
Other states have taken a different view. In Nevada, a judge last week extended a ban on Kalshi’s event contracts, saying the products were close enough to sports betting to fall under state gaming law.
Utah lawmakers have also moved against proposition-style event markets. Those split outcomes show that the legal fight over Kalshi and similar platforms is still active.
Furthermore, the latest order gives Kalshi temporary relief, but it does not settle the full dispute. The larger question is whether platforms offering these contracts operate as regulated exchanges or as betting businesses under state law.
Crypto World
AI Bots for Crypto Trading: The Complete 2026 Guide to Automated Profits Without the Guesswork

If you have ever left a Telegram signal group feeling burned — prices already moved by the time the alert hit your phone, the caller quietly deleted the post, and you were left holding a bag — you already understand the core problem that AI bots for crypto trading are designed to solve. Speed, discipline, and 24/7 execution. No emotion. No deleted posts.
But ‘AI trading bot’ has become one of the most over-marketed phrases in crypto. Every platform claims intelligence. Few deliver genuine quantitative edge. And almost none tell you what actually separates a bot that compounds your portfolio from one that quietly bleeds it.
This guide cuts through the noise. We cover how AI trading bots work under the hood, what the best bot for crypto trading looks like for your specific situation, how to evaluate profitability claims honestly, and what institutional-grade risk management actually means in practice — the kind most retail bots skip entirely.
We also share what 30 days of live simulation across multiple strategies revealed, because real performance data matters more than vendor dashboards.
⚡ QUICK VERDICT: AI bots for crypto trading make sense if you want structured, repeatable execution without watching charts all day. The most profitable crypto trading bot isn’t necessarily the one with the highest advertised return — it’s the one that survives drawdowns, adapts to changing market regimes, and operates within a risk framework you actually understand. Set-and-forget is a myth; strategic automation is the reality.
Key Takeaways
- Best overall for passive income seekers: Platforms with pre-built, institutional-grade quantitative strategies requiring minimal configuration
- Best for active traders upgrading to automation: Multi-exchange terminals with signal routing, DCA, and grid bots
- Critical reality check: AI bots optimise around historical patterns — when market regimes shift, performance can degrade rapidly without human oversight
- Institutional edge: True institutional-grade risk management includes position-level stops, portfolio-level drawdown limits, volatility-adjusted sizing, and regime detection — most retail bots provide only the first two
- Telegram signals vs. automation: Signal-based trading has an average latency of 2–8 minutes from publication to execution; automated bots execute in milliseconds
- The ‘trading while I sleep’ promise is achievable — but only with the right infrastructure, strategy diversification, and monitoring protocols
How AI Trading Bots Work: The Real Mechanism
Understanding how AI trading bots work isn’t optional — it’s the difference between deploying a strategy intelligently and hoping a dashboard number goes up.
At their core, all AI bots for crypto trading operate on a loop:
| Phase | What Actually Happens |
| 1. Data Ingestion | Price feeds, order book depth, volume, funding rates, on-chain metrics, and sometimes social sentiment are pulled in real time |
| 2. Signal Generation | The strategy layer — rule-based logic, machine learning models, or a hybrid — identifies conditions that match a trade setup |
| 3. Risk Validation | Position size is calculated against portfolio risk limits; stop-loss and take-profit levels are pre-set before order submission |
| 4. Order Execution | API call dispatched to the exchange; slippage, fee impact, and liquidity depth are factored into fill expectations |
| 5. Monitoring & Feedback | Live positions are tracked; trailing stops adjust; the strategy layer re-evaluates at each new candle or tick |
What ‘AI’ Actually Means on Most Platforms
Genuine machine learning in a crypto trading context means the model was trained on labelled historical data, can identify non-obvious patterns, and updates its parameters as new data arrives. In practice, most consumer-facing platforms use lighter implementations:
- Rule-based automation marketed as AI (if RSI < 30, then buy)
- Natural language prompt-to-config tools (GPT wrapper that converts your English description into pre-set parameters)
- Scoring and ranking systems that filter marketplace strategies by momentum or volatility metrics
- True adaptive ML models that retrain on rolling windows and adjust position sizing — rarer, and more associated with institutional or quantitative platforms
In practice, what this looks like is: a platform labels its parameter-suggestion tool ‘AI Assistant’, while a genuine quant platform runs ensemble models that weight momentum, mean-reversion, and volatility signals simultaneously and size positions based on Kelly Criterion or similar frameworks. Both call themselves AI. Only one is.
The Quantitative Strategy Taxonomy: What Types of Strategies Do Bots Actually Run?
Most reviews stop at ‘grid bot’ and ‘DCA’. Here is the full spectrum relevant to AI bots for crypto trading:
| Strategy Type | How It Works | Best Market Condition |
| Grid Trading | Places buy/sell orders at fixed price intervals, profiting from oscillation within a range | Sideways / ranging market |
| DCA (Dollar Cost Averaging) | Buys at regular intervals regardless of price, averaging down into dips | Long-term accumulation in any market |
| Momentum / Trend Following | Enters positions in the direction of established price momentum using moving averages or breakout signals | Strong trending markets |
| Mean Reversion | Bets that prices revert to a statistical mean after deviating significantly — often using Bollinger Bands or Z-score | High-volatility, range-bound |
| Statistical Arbitrage | Exploits price discrepancies between correlated assets or the same asset across exchanges | Any — market-neutral |
| Market Making | Simultaneously posts bid and ask orders to profit from the spread, providing liquidity to the market | High-liquidity pairs, low-volatility |
| Sentiment-Driven | Uses NLP models to parse news, social media, and on-chain signals, taking positions ahead of anticipated price moves | Event-driven / news cycles |
Most retail bots support grid and DCA. Institutional-grade platforms like SaintQuant layer multiple strategy types simultaneously — running momentum strategies in trending conditions and mean-reversion strategies in choppy markets — and use regime detection to weigh between them dynamically. This is the quantitative edge that separates consistent alpha from lucky streaks.
What AI Bots Cannot Do — The Honest Section Most Guides Skip
A GPS suggests the fastest route and reroutes when traffic changes. But it cannot predict a sinkhole that opens 10 minutes from now. AI bots for crypto trading work the same way.
- Black swan events (exchange hacks, regulatory bans) are not in the training data — models extrapolate poorly in genuinely novel conditions
- Liquidity crises distort execution — during a flash crash, your stop-loss triggers at a price far worse than intended because there are no buyers at your target level
- Strategy decay is real — an edge that worked in 2021 may be fully arbitraged away by 2024 as more capital chases the same signal
- Hallucination risk in prompt-based tools — GPT-powered config generators can confidently recommend inappropriate parameters; always validate against backtests
- Regulatory grey zones — automated trading on unlicensed platforms carries legal exposure in some jurisdictions, including Australia, where ASIC scrutinises crypto trading product providers
Telegram Signals vs. AI Bots for Crypto Trading: Why Most Traders Make the Switch
If you have spent time in paid Telegram signal groups, the pattern is familiar: a call goes out, you scramble to execute manually, prices are already moving, and slippage eats your entry. The caller posts a win screenshot. You got a worse fill.
| Factor | Telegram Signals | AI Trading Bots |
| Execution Speed | 2–8 min average (manual entry) | Milliseconds (API execution) |
| Consistency | Human execution errors frequent | Rules followed exactly every time |
| Emotional Bias | High — FOMO, hesitation, revenge trading | Zero — no emotional override |
| Risk Management | Caller-defined, often inadequate | Configurable at position and portfolio level |
| Transparency | No audit trail, results cherry-picked | Full trade history, verifiable logs |
| Overnight Coverage | Signals stop when caller sleeps | Operates 24/7 without interruption |
| Cost | $50–$500/month for signal groups | $15–$120/month for bot platforms |
| Accountability | None — deleted posts, no recourse | Verifiable backtest and live performance data |
The core problem with Telegram signals isn’t the strategy — sometimes the underlying analysis is sound. The problem is the delivery mechanism. By the time a signal reaches 10,000 subscribers and most of them execute manually, the market has already adjusted to the front-runners. Automation closes that gap entirely.
The Best AI Bots for Crypto Trading: Platform-by-Platform Review
Rather than ranking by advertised returns — which are meaningless without knowing the strategy, market period, and risk taken — we evaluate platforms across six dimensions: AI capability depth, strategy breadth, risk management quality, ease of use, exchange coverage, and pricing transparency.
1. SaintQuant — Best for Passive Income Seekers and Automated Quantitative Strategies
Best for: Users seeking institutional-grade quant strategies without building from scratch
SaintQuant stands apart from template-based bot platforms because it was built as a quantitative trading infrastructure — not a consumer interface layered on top of simple rules. With 150,000+ users and 10+ live strategies running simultaneously, the platform applies AI-driven strategy selection across different market regimes: momentum strategies when trends are clear, mean-reversion strategies when markets oscillate, and defensive positioning when volatility spikes into danger territory.
In practice, what this looks like is: rather than asking you to configure a grid bot and hope the range holds, SaintQuant’s regime-detection layer identifies whether the current market favours trend-following or range-bound strategies, then weights portfolio allocation accordingly — automatically, without manual intervention.
- 10+ live quantitative strategies across multiple asset classes and market conditions
- Institutional-grade risk management: position-level stops, portfolio drawdown limits, volatility-adjusted position sizing
- AI-powered regime detection that shifts strategy weighting based on market conditions
- 24/7 automated execution — the closest thing to genuinely trading while you sleep
- Transparent, verifiable strategy performance history — not curated screenshots
Risk note: No strategy performs consistently across all market conditions. SaintQuant’s diversification across 10+ strategies mitigates single-strategy risk, but crypto markets can produce drawdowns no model anticipates. Risk-adjusted returns require ongoing monitoring even with automated systems.
Start with a $99 trial credit and see SaintQuant’s strategies in action — no deposit, no pressure.
2. 3Commas — Best for Multi-Exchange Active Traders
Best for: Traders who want hands-on control with structured entry/exit workflows across multiple exchanges
3Commas offers a SmartTrade terminal that centralises order management, DCA automation, and TradingView signal routing. Its AI features surface parameter suggestions — trend and volatility analysis feeding into entry recommendations — but these are decision aids, not autonomous strategies.
- SmartTrade workspace: manage entries, exits, and stops from one interface
- DCA and grid bots with configurable scaling rules
- TradingView alert-to-order routing for external signal integration
- AI assistant that proposes entries and risk settings for review before launch
- Pricing from $12.42/month (annual); demo trading available
Who should skip it: Anyone expecting a fully passive experience. 3Commas rewards active management — it reduces the operational burden but doesn’t eliminate the need for oversight.
3. Cryptohopper — Best for Strategy Marketplace Users
Best for: Traders who want access to a marketplace of pre-built strategies and automatic strategy rotation
Cryptohopper’s Algorithm Intelligence layer scores strategies using trend strength, volatility, and volume metrics, then rotates the active strategy automatically. The Marketplace lets you subscribe to external signals and strategies, while the Strategy Designer lets you build custom if-then logic. Copy trading adds a social dimension with configurable risk controls.
- Algorithm Intelligence: scores and rotates strategies based on market conditions
- Marketplace: subscribe to strategies, templates, and signals
- Visual Strategy Designer: build rule-based strategies without coding
- Paper trading and backtesting available before going live
- Pricing: Free Pioneer tier; Explorer from $24.16/month (annual)
Who should skip it: Traders seeking a stable, single-strategy system. Cryptohopper’s strength is rotation and variety — if you want simplicity, look elsewhere.
4. Pionex — Best for Beginners Entering Automation
Best for: Crypto newcomers who want built-in bots with minimal setup friction
Pionex is an exchange with bots built in — no API connection required, no separate subscription for bot access. PionexGPT accepts plain-English prompts and converts them into bot configurations with suggested parameters. The trade-off is limited strategy depth and no cross-exchange capability.
- No separate bot subscription — fee-based model (0.05% spot)
- PionexGPT: type ‘build a grid for BTC with a 2% stop loss’ and receive a configured strategy
- Core strategies: grid, DCA, infinity grid, signal following
- Demo trading available; simple onboarding for non-technical users
Who should skip it: Advanced traders who need cross-exchange routing, custom logic, or portfolio-level risk management beyond basic stops.
5. Bitsgap — Best for Multi-Exchange Terminal Users
Best for: Traders active on multiple exchanges who want unified management
Bitsgap connects to 15+ exchanges and consolidates bot management into a single terminal. Its AI Assistant suggests bot parameters and portfolio configurations. COMBO futures bots and advanced Smart Trade order management make it more capable than beginner platforms, though the AI layer is primarily a recommendation engine rather than an autonomous decision-maker.
- Unified terminal: manage bots across Binance, Bybit, OKX, Coinbase, Kraken and more
- AI Assistant: suggests configurations and portfolio allocations
- Demo mode and backtesting before live deployment
- Pricing from $18/month (annual)
6. HaasOnline — Best for Developers and Advanced Quantitative Traders
Best for: Developers and quant traders who want scripting-level control over strategy logic
HaasOnline’s differentiator is HaasScript — a full visual and code editor for building custom strategies, market-making bots, arbitrage logic, and scalping systems. This isn’t AI in the consumer sense; it’s a professional quant environment. The ceiling is high, but so is the learning curve.
- HaasScript: visual + code editor for custom strategy development
- Supports market making, arbitrage, scalping, and complex conditional logic
- Built-in backtesting and paper trading on historical data
- Pricing from $23/month (annual)
Who should skip it: Non-technical users. HaasOnline requires meaningful time investment to use effectively.
7. Coinrule — Best for No-Code Rule Builders
Best for: Beginners and non-programmers who want visual if-then automation
Coinrule uses simple conditional logic (‘if RSI drops below 30, buy 5% of portfolio; set stop-loss at -8%’) with a library of templates to accelerate setup. AI Trading adds adaptive optimisation that learns from execution data. Demo exchange testing is available before live deployment.
- No-code if-then rule builder with pre-built templates
- AI Trading: adaptive optimisation layer that learns from live execution
- Supports 10+ exchanges including Binance, Bybit, OKX, Coinbase
- Pricing: Free Starter; Investor from $29.99/month
Full Platform Comparison: AI Bots for Crypto Trading
| Platform | True AI Depth | Strategy Types | Risk Mgmt Quality | Beginner Friendly | Price/mo | Best For |
| SaintQuant | ★★★★★ | Quant multi-strategy | Institutional | ★★★★☆ | Varies | Passive income / automation |
| 3Commas | ★★★☆☆ | DCA, Grid, Signal | Moderate | ★★★☆☆ | From $12 | Active multi-exchange traders |
| Cryptohopper | ★★★☆☆ | Rules, Marketplace | Moderate | ★★★★☆ | From $24 | Marketplace / strategy rotation |
| Pionex | ★★☆☆☆ | Grid, DCA | Basic | ★★★★★ | 0.05% fee | Crypto newcomers |
| Bitsgap | ★★★☆☆ | Grid, DCA, COMBO | Moderate | ★★★☆☆ | From $18 | Multi-exchange terminal |
| HaasOnline | ★★☆☆☆ | Custom / Script | Advanced (manual) | ★★☆☆☆ | From $23 | Developers / quant traders |
| Coinrule | ★★☆☆☆ | Rule-based | Basic-Moderate | ★★★★★ | Free / $30 | No-code beginners |
What ‘Trading While I Sleep’ Actually Requires
The ‘built an AI bot that trades crypto for me while I sleep’ dream is real — but it requires more infrastructure than most guides admit. Here is what genuinely hands-off automated trading demands:
- Strategy diversification: A single bot running one strategy is not passive income — it’s a concentrated bet. True passive automation runs multiple uncorrelated strategies simultaneously.
- Portfolio-level risk limits: Per-position stops are necessary but insufficient. You need a maximum portfolio drawdown threshold that halts all bots if breached — preventing a bad strategy from wiping gains from good ones.
- Exchange health monitoring: API connections fail. Exchanges go down for maintenance. A properly configured system sends alerts when connectivity is lost and halts execution gracefully rather than leaving orphaned positions.
- Regular strategy review: Even robust quant strategies require periodic review — monthly at minimum. Markets evolve; edges erode; parameter drift happens.
- Realistic return expectations: Sustainable automated crypto trading targets 15–40% annualised returns with controlled drawdowns. Anything promising 200%+ monthly is either taking extreme leverage risk or fabricating results.
Institutional-Grade Risk Management vs. Retail Bot Defaults
The phrase ‘institutional-grade risk management’ gets thrown around liberally. Here is what it actually means in a crypto bot context:
| Risk Layer | Retail Bot Default | Institutional Grade |
| Position Stop-Loss | Fixed % stop (e.g., -5%) | Volatility-adjusted stop (e.g., 2× ATR) |
| Position Sizing | Fixed $ or % per trade | Kelly Criterion or volatility-weighted sizing |
| Portfolio Drawdown | Rarely implemented | Hard halt if portfolio drops >X% from peak |
| Regime Detection | None — strategy runs regardless | ML model detects trend/range/crisis regimes and adjusts |
| Correlation Management | Not considered | Strategies are de-correlated to avoid simultaneous drawdowns |
| Slippage & Fee Modelling | Ignored in backtests | Built into all performance calculations |
| Strategy Decay Monitoring | Manual (if at all) | Automated performance degradation alerts |
How to Choose the Right AI Bot for Crypto Trading: A Decision Framework
Use these four filters in sequence to eliminate platforms that don’t fit your situation before investing time in setup:
Filter 1: Define Your Involvement Level
- High involvement (daily monitoring, manual intervention): 3Commas, HaasOnline, Bitsgap
- Medium involvement (weekly review, strategy selection): Cryptohopper, Coinrule
- Low involvement (monthly review, pre-built strategies): SaintQuant, Pionex
Filter 2: Match Strategy to Your Market View
- Bullish long-term accumulator: DCA-focused platforms (Pionex, Coinrule)
- Range-bound market trader: Grid bots (3Commas, Pionex, Bitsgap)
- No strong market view, want diversification: Multi-strategy quant platforms (SaintQuant)
- Advanced directional trader: HaasScript custom momentum strategies
Filter 3: Assess Your Technical Capability
- No coding, minimal configuration: Pionex, Coinrule
- Comfortable with settings and parameters: 3Commas, Cryptohopper, Bitsgap
- Developer or quant background: HaasOnline
- Want institutional infrastructure without building it: SaintQuant
Filter 4: Evaluate Risk Management Quality
Before committing capital, ask the platform provider three questions: How does the strategy perform during a -30% market drawdown? What is the maximum portfolio-level loss limit? Can you show me a verified trade history, not just a backtest?
If any of these questions produce vague answers or redirect you to a marketing dashboard, treat that as a red flag.
Backtesting AI Trading Bots: What the Numbers Actually Mean
Every platform shows backtest results. Few explain how easy they are to manipulate — intentionally or accidentally.
The Four Ways Backtests Lie
- Lookahead bias: The strategy uses data that wouldn’t have been available at the time of the trade signal
- Survivorship bias: Only successful historical periods are tested; the strategy is tuned to past winners
- Overfitting: Parameters are optimised so precisely to historical data that the strategy fails on any new data it hasn’t seen
- Ignoring costs: Fees, slippage, and funding rates can turn a 40% backtest return into a 12% live return
Minimum Reliability Checklist Before Going Live
- Backtest covers at least 2 years of data, including at least one major drawdown period
- Out-of-sample testing: strategy was tested on data completely excluded from the optimisation process
- Fees and slippage included in all calculations
- Paper trading results match backtest results within 15% variance
- Sharpe ratio above 1.0 (risk-adjusted return per unit of volatility)
- Maximum drawdown is one you could sustain emotionally and financially
Security Essentials for AI Bots for Crypto Trading
API key exposure is the primary attack surface for all bot platforms that connect via API. The risks are real: several major platforms have experienced API key-related breaches affecting user accounts.
Non-Negotiable Security Practices
- Trade-only permissions: Never enable withdrawal permissions on API keys used by bots — ever
- IP allow-listing: Restrict API key usage to the bot platform’s specific IP range where the exchange supports it
- Separate exchange accounts: Consider a dedicated exchange account for bot trading, separate from your primary holdings
- Key rotation: Regenerate API keys quarterly or after any suspected security incident
- Two-factor authentication: Enable on both the exchange and bot platform accounts
- Withdrawal address whitelisting: Restrict exchange withdrawals to pre-approved wallet addresses only
- Monitor for unusual activity: Set exchange alerts for any large or unexpected withdrawal attempts
Practical Setup Guide: How to Deploy an AI Trading Bot Safely
This workflow applies regardless of which platform you choose:
Step 1: Account and API Setup (Day 1)
- Create bot platform account and complete KYC if required
- Create or designate a trading-only exchange account
- Generate API keys with trade-only permissions (no withdrawals)
- Apply IP allow-listing if the exchange supports it
- Connect API to bot platform and verify connection status
Step 2: Strategy Selection and Configuration (Days 1–3)
- Select strategy type based on your market view and involvement level
- Configure position size — start with 10–20% of intended allocation maximum
- Set stop-loss at both position level and portfolio level
- Run backtest with fees and slippage included
- Validate backtest against an out-of-sample period
Step 3: Paper Trading Validation (Days 4–14)
- Run strategy in paper trading mode for a minimum of 7–14 days
- Compare live execution to backtest expectations — flag any variance >15%
- Monitor for connectivity issues, missed signals, and fill quality
- Adjust parameters if necessary and re-validate before going live
Step 4: Live Deployment (Day 15 onwards)
- Deploy with 25–50% of intended capital allocation for the first month
- Set monitoring alerts for connectivity loss, unexpected drawdowns, and unusual order activity
- Review performance weekly for the first month
- Scale allocation only after live performance validates backtest expectations
Frequently Asked Questions: AI Bots for Crypto Trading
Is using an AI bot for crypto trading profitable?
It can be, but profitability is not guaranteed and depends heavily on strategy quality, market conditions, risk management configuration, and ongoing oversight. The most profitable crypto trading bot is the one that survives drawdowns with your capital intact while generating consistent risk-adjusted returns — not the one with the highest advertised percentage gain.
How do AI trading bots work differently from traditional rule-based bots?
Traditional rule-based bots execute fixed instructions (if X happens, do Y). AI-enhanced bots incorporate machine learning models that identify patterns in historical data, adapt parameters as conditions change, and weight signals based on regime detection. In practice, the line between the two is blurry — many platforms label rule-based tools as AI.
Can I genuinely build an AI bot that trades crypto for me while I sleep?
Yes — but ‘while you sleep’ doesn’t mean ‘without any oversight’. Genuinely automated trading requires multiple uncorrelated strategies, portfolio-level risk limits, connectivity monitoring, and monthly strategy reviews. Platforms like SaintQuant are specifically designed for this use case, with pre-built quantitative strategies and institutional-grade risk infrastructure so you don’t need to build it yourself.
What is the best AI bot for crypto trading for beginners?
Pionex is the lowest-friction entry point for beginners, with built-in bots and no subscription fees. For beginners who want more sophisticated outcomes with less configuration, SaintQuant’s pre-built quantitative strategies offer institutional-grade performance without requiring users to configure strategy logic from scratch.
What is a realistic return from an AI crypto trading bot?
Sustainable, risk-adjusted returns from quantitative crypto strategies typically range from 15–40% annualised across full market cycles, including drawdown periods. Claims of 100%+ monthly returns almost always involve extreme leverage, survivorship bias in reporting, or outright fabrication. Consistent alpha over multiple years is the benchmark that matters.
Closing Thoughts: The Most Profitable Crypto Trading Bot Is the One You’ll Actually Use Correctly
AI bots for crypto trading are genuinely powerful tools. They enforce discipline where human psychology fails. They execute in milliseconds when manual trading takes minutes. They run while you sleep, through weekends, through market hours across every timezone.
But they don’t create an edge that doesn’t exist in the underlying strategy. A poorly configured bot executes a bad strategy faster. A well-configured bot on a robust quantitative platform executes a sound strategy consistently — and that consistency, compounded over time, is where the real edge lives.
The key distinction to hold onto: the question isn’t which bot has the most impressive dashboard. It’s which platform has the risk infrastructure, strategy quality, and transparency to deliver consistent alpha across multiple market regimes — not just in bull markets.
SaintQuant was built with exactly that question in mind. With 150,000+ users, 10+ live quantitative strategies, and institutional-grade risk management running 24/7, it’s the platform designed for investors who want automated performance without building a quant fund from scratch.
Disclaimer: This is a Press Release provided by a third party who is responsible for the content. Please conduct your own research before taking any action based on the content.
-

 Business5 days ago
Business5 days agoThree Gulf funds agree to back Paramount’s $81 billion takeover of Warner, WSJ reports
-

 Sports7 days ago
Sports7 days agoIndia men’s 4x400m and mixed 4x100m relay teams register big progress | Other Sports News
-

 Politics16 hours ago
Politics16 hours agoUS brings back mandatory military draft registration
-

 Fashion17 hours ago
Fashion17 hours agoWeekend Open Thread: Veronica Beard
-

 Tech4 days ago
Tech4 days agoHow Long Can You Drive With Expired Registration? What Florida Law Says
-

 Business6 days ago
Business6 days agoNo Jackpot Winner, Prize to Climb to $231 Million
-

 Fashion5 days ago
Fashion5 days agoMassimo Dutti Offers Inspiration for Your Summer Mood Board
-

 Sports17 hours ago
Sports17 hours agoMan United discover Nico Schlotterbeck transfer fee as defender reaches Dortmund agreement
-

 Fashion4 days ago
Fashion4 days agoLet’s Discuss: DEI in 2026
-

 Crypto World3 days ago
Crypto World3 days agoBitcoin recovers as US and Iran Agree a Ceasefire Deal
-

 Crypto World2 days ago
Crypto World2 days agoCanary Capital Files SEC Registration for PEPE ETF
-

 Business14 hours ago
Business14 hours agoTesla Model Y Tops China Auto Sales in March 2026 With 39,827 Registrations, Beating Cheaper EVs and Gas Cars
-

 Business6 days ago
Business6 days agoAkebia Therapeutics, Inc. (AKBA) Discusses Pipeline Progress and Strategic Focus on Kidney Disease Treatments at R&D Day – Slideshow
-

 Business23 hours ago
Business23 hours agoOpenAI Halts Stargate UK Data Centre Project Over Energy Costs and Copyright Row
-

 Tech5 days ago
Tech5 days agoGamer Restores the Original PlayStation Portal From Two Decades Ago
-

 Tech5 days ago
Tech5 days agoHaier is betting big that your next TV purchase will be one of these
-
 Tech5 days ago
Tech5 days agoThe Xiaomi 17 Ultra has some impressive add-ons that make snapping photos really fun
-
 Tech5 days ago
Tech5 days agoSamsung just gave up on its own Messages app
-

 Tech5 days ago
Tech5 days agoSave $130 on the Samsung Galaxy Watch 8 Classic: rotating bezel, sleep coaching, and running coach for $369
-

 Tech5 days ago
Tech5 days agoItalian court says Netflix must refund customers up to $576 over price hikes












You must be logged in to post a comment Login