Crypto World
Lazarus Group Uses Fake Meeting Hack


North Korea’s Lazarus Group has launched a new macOS malware campaign called Mach-O Man that uses fake online meeting invitations to trick crypto and fintech executives into executing malicious commands on their own devices, according to blockchain security firm CertiK.
Summary
- Lazarus Group’s new Mach-O Man campaign uses fake meeting invites to lure executives into pasting malicious terminal commands on their Macs.
- The malware auto-deletes after execution, making the breach nearly impossible to detect through standard forensic methods.
- CertiK links the same Lazarus push to over $500 million stolen from DeFi platforms Drift and KelpDAO in the past two weeks.
North Korea’s Lazarus Group is running a new campaign dubbed Mach-O Man that targets executives at crypto, fintech, and other high-value firms by disguising malware delivery as a routine technical fix during a fake business meeting, according to CertiK senior blockchain security researcher Natalie Newson. The campaign was disclosed on April 22 and represents one of the group’s most operationally sophisticated social engineering methods to date.
Lazarus Group Crypto Hack Hides Behind Routine Business Communications
The attack chain begins with an urgent-looking meeting invitation sent over Telegram, impersonating a Zoom, Microsoft Teams, or Google Meet call. The link leads to a convincing but fake website that tells the victim to paste a single command into their Mac terminal to resolve an apparent connection issue, a technique CertiK identifies as ClickFix. Once executed, the command installs a modular malware kit built from native Mach-O binaries tailored for Apple environments, which profiles the host, establishes persistence, and exfiltrates credentials and browser data through a Telegram-based command-and-control channel. Critically, the toolkit auto-deletes after completing its task, making detection and forensic analysis extremely difficult. “These fake verification steps guide victims through keyboard shortcuts that run a harmful command,” CertiK’s Newson told CoinDesk. “The page looks real, the instructions seem normal, and the victim initiates the action themselves, which is why traditional security controls often miss it.”
Why This Attack Is Harder to Catch Than Standard Phishing
Unlike traditional phishing attacks that rely on urgency cues or suspicious sender addresses, the Mach-O Man campaign is designed to look entirely routine at the moment of delivery. Executives in crypto and fintech routinely receive cold outreach from investors, researchers, and business partners, making the fake meeting invitation format a credible lure in a way that generalized phishing often is not. CertiK’s analysis notes that the Mach-O Man framework is tied to Lazarus’ Famous Chollima unit and distributed through compromised Telegram accounts specifically targeting high-value organizations in the digital asset space. Most victims will not realize they have been compromised until well after the malware has erased itself. “They likely don’t know it yet,” Newson said. “If they do, they probably can’t identify which variant affected them.”
The Scale of the Lazarus Threat to Crypto in 2026
CertiK has linked the Mach-O Man campaign to a broader Lazarus offensive that has siphoned more than $500 million from DeFi platforms Drift and KelpDAO in under two weeks, adding to a cumulative theft total estimated at $6.7 billion since 2017. The United Nations has previously estimated that North Korean hackers have stolen several billion dollars in digital assets to fund the country’s weapons programs. “What makes Lazarus especially dangerous right now is their activity level,” Newson said. “This isn’t random hacking. It’s a state-directed financial operation running at a scale and speed typical of institutions.” CertiK is advising crypto professionals to independently verify all meeting requests through a separate channel before clicking any link or downloading any attachment from an unsolicited invitation.
CertiK has shared indicators of compromise tied to the Mach-O Man campaign with the broader security community to support detection and defense efforts across the industry.
Crypto World
Iran Central Bank’s OFAC-Sanctioned Tron Wallets Mapped by Arkham
Blockchain analytics platform Arkham has published what it says is a public, onchain map of crypto wallets attributed to Iran’s central bank, making a pair of US-sanctioned Tron addresses publicly searchable for investigators and the wider public.
The move could increase scrutiny of how Iranian-linked entities use stablecoins and blockchain networks to move funds outside traditional banking rails, as US authorities intensify sanctions enforcement tied to terrorism financing and oil revenues.
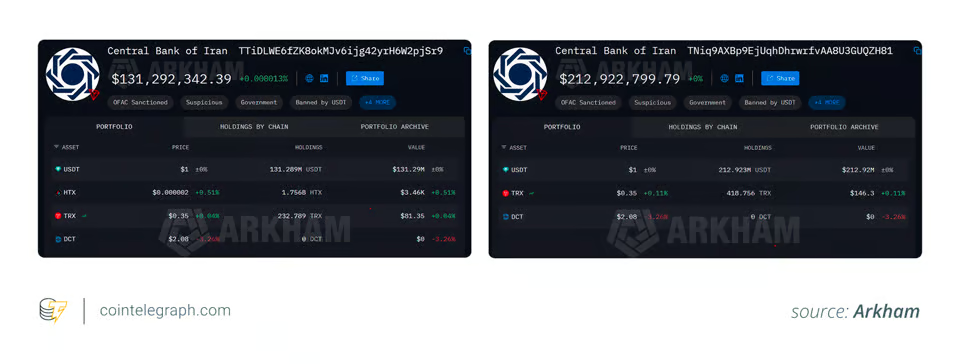
Arkham’s May 11 research post groups the wallets into a Central Bank of Iran entity page and explorer, which the firm says can be used as a starting point to trace connected addresses and flows.
The map is built on two TRC-20 wallets that the US Treasury’s Office of Foreign Assets Control (OFAC) added to its Specially Designated Nationals list on April 24 as property of Bank Markazi Jomhouri Islami Iran, citing links to the Islamic Revolutionary Guard Corps-Qods Force and Hezbollah.

TRC-20 wallets tied to Iran. Source: Arkham
US authorities froze about $344 million in crypto linked to Iran as part of that action, Treasury Secretary Scott Bessent said, describing it as an effort to “systematically degrade Tehran’s ability to generate, move, and repatriate funds.” Tether separately said it had frozen the funds at the request of US authorities over “activity tied to unlawful conduct,” without explicitly naming Iran in its public statement.
Arkham’s wallet mapping reflects a broader push by blockchain analytics firms and stablecoin issuers to expose and disrupt sanctions evasion networks increasingly using crypto infrastructure tied to Tron and Tether.
Related: US Treasury sanctions Iran-linked crypto exchanges in first Iran-related designations
In an April 27 note, Chainalysis described a multi-step stablecoin “pipeline” in which Iranian oil revenues were routed through brokers, intermediary wallets, cross-chain bridges and decentralized finance protocols before cycling back into accounts associated with the Central Bank of Iran and IRGC-linked entities.
Iran’s wider crypto footprint
The Arkham findings come against a broader backdrop of growing Iranian crypto use. A February report on Iran’s digital assets footprint, citing estimates from TRM Labs and Chainalysis, put the country’s overall crypto transaction volume at about $11.4 billion in 2024 and $10 billion in 2025.
In May, Nobitex, Iran’s largest crypto exchange, was reportedly linked to members of a powerful family with ties to Supreme Leader Ali Khamenei, and used as a key conduit between domestic users and offshore liquidity.
In April, Iran reportedly considered charging crypto-denominated tolls to ships transiting the Strait of Hormuz, positioning digital assets as an additional revenue channel outside traditional banking rails.
Separately, Cointelegraph reported Friday that Tether had frozen more than 500 million USDT over a recent 30-day period across Ethereum and Tron, with around 506 million of that on Tron, according to BlockSec’s USDT Freeze Tracker.
A TRON spokesperson told Cointelegraph the network itself cannot monitor or block individual transactions, but pointed to the T3 Financial Crime Unit, a collaboration between TRON, Tether and TRM Labs launched in 2024, as its main channel for tackling abuse, saying it works with law enforcement “to freeze hundreds of millions of funds,” including funds tied to sanctioned entities and terror financing. Tether declined to comment.
Asia Express: North Korea denies crypto hacks, Upbit’s bank tests Ripple
Crypto World
EToro (ETOR) reiterates commitment to crypto despite falling activity in first quarter 2026


EToro (ETOR) doubled down on its commitment to crypto even as digital asset activity weakened in the first quarter and into April.
Revenue from crypto assets dropped 38% from the year-earlier quarter to $2.15 billion, the company said in its first-quarter earnings report released Tuesday. Net trading income from crypto derivatives fell 57% to $33.4 million while overall net income rose 37% to $82.4 million.
The trading platform said the crypto activity decline extended into April, with the total number of crypto trades falling 32% year-over-year and the invested amount per trade dropping 22%. Despite the downturn, CEO Yoni Assia expressed a bullish outlook.
“We do expect later this year to start seeing crypto rising back to, you know, near all-time-highs and that will drive crypto engagement,” Assia told CNBC, adding that the platform’s data suggests that when the markets fall, “retail investors on eToro actually buy the dip.”
The company said it activated its BitLicense to start trading in New York, three years after it was granted, and it completed the $70 million acquisition of crypto wallet provider Zengo, closed April 30.
“The acquisition of Zengo, a leading self-custodial crypto wallet provider, meaningfully advances our strategy of bridging traditional finance with on-chain infrastructure, prediction markets, perpetuals and the broader crypto ecosystem,” Assia said in the report.
Etoro shares fell 0.61% in pre-market trading on Wednesday.
Crypto World
bitcoin tests key resistance zone to form next major breakout
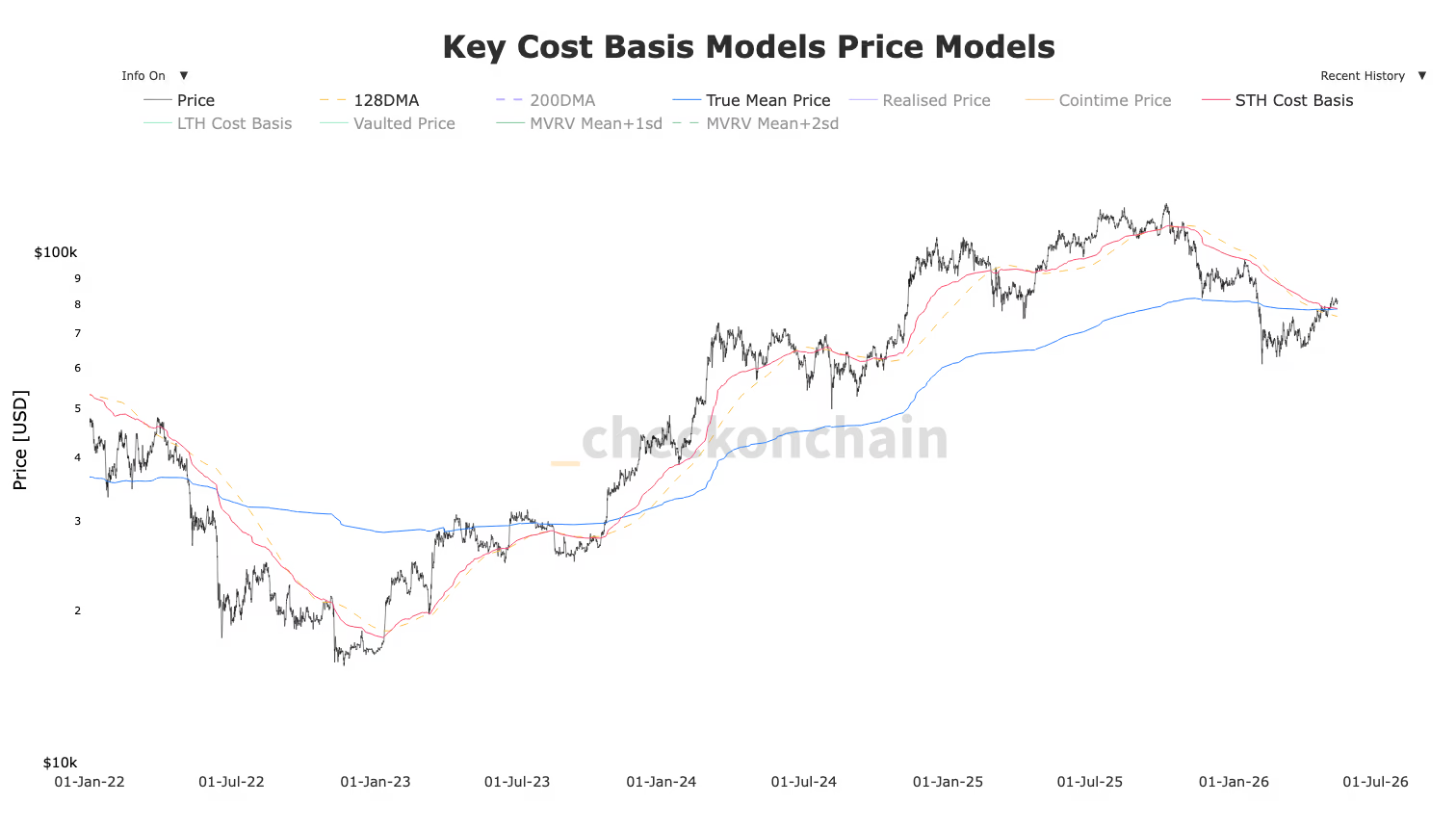
Bitcoin is fighting a key technical battle and is trading just below two closely watched long-term trend indicators: the 200-day Simple Moving Average (200SMA) at $82,455 and the 200-day Exponential Moving Average (200EMA) at $82,027, according to Glassnode data.
The 200SMA calculates the average closing price across the last 200 days, weighting each day equally. The 200EMA uses the same 200-day window but places greater emphasis on more recent prices, making it slightly more responsive to current market conditions.
Together, they form a confluence resistance zone around $82,000–$82,500 that bitcoin must convincingly reclaim to signal a recovery of its long-term uptrend.
Bitcoin first lost the 200DMA in late November 2025, when the price rolled over from $108,000. A brief recovery attempt in January failed to reclaim the level around $97,000 and by early February 2026 bitcoin had fallen to $60,000.
What gives bulls reason for cautious optimism is that bitcoin is holding above several significant cost basis levels, according to CheckonChain. The 128-day Moving Average sits at $75,700, representing the average price paid by buyers over that shorter timeframe and a level BTCX has successfully defended.
The True Market Mean, currently at $78,200, reflects the average price of every bitcoin at the time it last moved onchain, essentially representing the aggregate cost basis of the entire active market.
The Short-Term Holder Cost Basis at $78,400 tracks the average acquisition price of investors who bought within the last 155 days, a group historically prone to panic selling when underwater.
Bitcoin trading above all three suggests the majority of recent buyers remain in profit, reducing sell pressure from forced liquidations or panic selling. The key zone to watch is whether bitcoin can flip the $82,000-$82,500 into support.

Crypto World
Coinbase CEO Brian Armstrong backs CLARITY Act ahead of Thursday markup
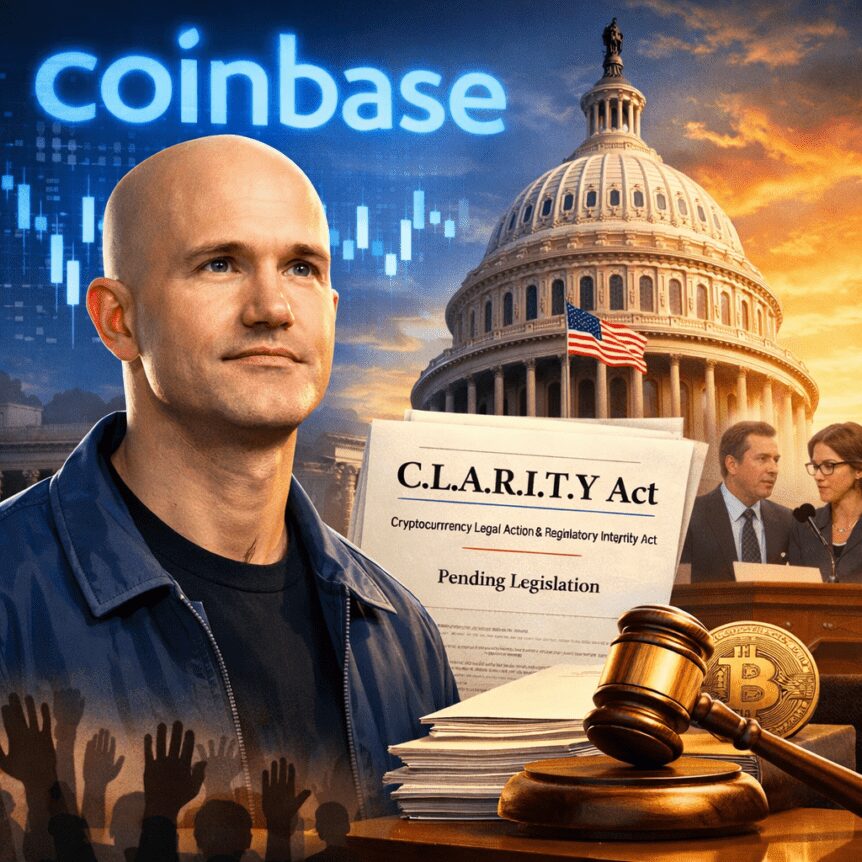
As the White House and Congress continue to shape the U.S. crypto regulatory landscape, Coinbase CEO Brian Armstrong has thrown his weight behind the latest iteration of the Digital Asset Market Clarity Act (CLARITY). He said the bill is now in a stronger, more bipartisan position as the Senate prepares to markup the broader crypto market-structure legislation on Thursday.
Armstrong disclosed his assessment in a post on X, emphasizing that the current draft reflects a rare moment of cross-aisle consensus. “I don’t think it’s ever been in a stronger or more bipartisan position,” he wrote, signaling support from a major industry player even as lawmakers broker delicate compromises on contentious topics like stablecoin yields and DeFi safeguards. He also noted a “healthy compromise” on stablecoin yield, reached through negotiations that included Senators Thom Tillis and Alsobrooks. The brokered agreement appears to have boosted momentum for the legislation, even as some concerns remain about the path forward.
The current CLARITY framework, according to Armstrong, also broadens the bill’s reach in key areas such as decentralized finance (DeFi), tokenized stocks, and the authority granted to the Commodity Futures Trading Commission (CFTC) to regulate crypto markets. Those elements are part of a broader debate about how to delineate compliance regimes for a fast-evolving sector—balancing investor protections with innovation and market access.
The timing of Armstrong’s comments aligns with months of negotiation between the banking industry and crypto participants. The bill stalled earlier in the year after an initial draft faced pushback from industry players led by Coinbase, who argued that certain provisions created uncertainties or barriers for the market. Since then, lawmakers have pursued a revised version aimed at addressing core concerns while preserving Congress’s oversight of a rapidly expanding space. A separate article highlighted how the markup date and the broader political dynamics are shaping expectations for what changes might survive the process.
In the background, polls and surveys illustrate a public-facing climate that is increasingly engaged with crypto policy. A 2025 survey by the National Cryptocurrency Association—spanning about 54,000 U.S. residents—puts ownership of cryptocurrency at roughly 20% of the population. The study also notes that younger investors dominate the user base, with about two-thirds of crypto owners under the age of 45, and a minority (roughly 15%) over 55. Among owners, investing remains the primary use case, cited by about half (52%) as a means to “invest in their financial future.”
Public sentiment toward policy reform sits on a slightly different axis. A HarrisX poll conducted earlier this month found that about 52% of registered U.S. voters supported passing the CLARITY Act into law, while 11% opposed its enactment. Taken together, the signals from industry leadership, lawmakers, and public opinion suggest a moment when a carefully calibrated regulatory bill could gain traction—provided lawmakers can resolve remaining points of disagreement, particularly around DeFi definitions and the treatment of tokenized assets.
Key takeaways
- Coinbase’s Brian Armstrong publicly supports the latest CLARITY draft, calling it the strongest and most bipartisan iteration to date as the Senate moves toward markup.
- The compromise on stablecoin yield—brokered by Senators Tillis and Alsobrooks—appears to have reduced a major hurdle that previously stalled negotiations.
- New provisions in CLARITY reportedly expand coverage for DeFi activities, tokenized stocks, and strengthen the CFTC’s authority to regulate crypto markets.
- Public sentiment is mixed but leaning toward support for policy reform: about 52% of registered voters in HarrisX’s poll, and roughly 20% of Americans own crypto, according to the National Cryptocurrency Association’s 2025 report.
Armstrong’s stance and the politics of market structure reform
Armstrong’s comments underscore a broader trend: industry coalitions are aligning behind a version of CLARITY that they believe can withstand congressional scrutiny while acknowledging concessions. The banker-crypto negotiation dynamic has evolved from a stalemate to a calibrated bargaining room where stakeholders trade guardrails for clarity. The brokered stablecoin yield agreement—though still a live point of contention for some participants—has become a focal point that could determine whether the bill advances through committee stages and into floor debate.
Two elements anchor the current discourse. First, DeFi: the latest CLARITY text purportedly tightens oversight without stifling permissionless innovation, attempting to carve out a regulatory pathway that recognizes the practical realities of decentralized protocols. Second, tokenized stocks: the bill’s language seeks to address how tokenized representations of traditional assets would operate within an asset-ownership and transfer framework that regulators can oversee. Critics have warned about overreach, but proponents argue that clearer delineation reduces legal ambiguity for market participants and issuers alike.
Meanwhile, the CFTC’s expanded remit is a recurring theme: broader authority could help align crypto markets with existing commodity rules, potentially closing gaps that have long drawn regulatory attention. Advocates say it creates a consistent, rules-based environment that could encourage institutional participation, while opponents warn of overreach that could hamper innovation. The evolving language will likely be a proxy for how aggressively U.S. regulators intend to pursue crypto-market structure in the coming years.
Public sentiment, ownership, and investor behavior
The cautionary note from public sentiment matters because policy outcomes are increasingly tethered to political and cultural support beyond technocratic circles. The National Cryptocurrency Association’s 2025 State of Crypto Holders report—drawing on a substantial nationwide sample—paints crypto ownership as a cross-section of the population with a notable skew toward younger demographics. The finding that 20% of Americans own cryptocurrency signals a broad base of potential voters who may weigh policy decisions, even if the sector remains a minority in total terms.
The demographic slice matters for market participants. With 67% of crypto owners under 45, the policy debate intersects with a generation that will shape the sector’s trajectory for years to come. The same survey indicates that investment remains the top motivator for holdings, which has implications for how policy changes could influence market activity, risk appetite, and long-term adoption. On the political front, the HarrisX poll—conducted among registered voters—adds a layer of electoral context: a majority showing support for CLARITY’s passage suggests that policymakers may find it advantageous to push forward with a version deemed acceptable by both industry and broader citizenry, though opposition remains in measurable pockets.
For investors and builders, the practical takeaway is that policy momentum could translate into clearer compliance pathways and potentially reduce regulatory risk for compliant players. Yet the precise contours of DeFi governance, stablecoin oversight, and the treatment of tokenized assets remain live debates. The next weeks will reveal how much of the compromise translates into enforceable rules and which provisions survive the markup process.
What to watch next
As Thursday’s Senate markup approaches, market participants will be parsing whether lawmakers preserve the hard-worn compromises on stablecoins and DeFi while expanding clarity on tokenized equities and CFTC oversight. The outcome will shape the trajectory of U.S. crypto markets, determine whether major platforms can operate with greater regulatory certainty, and influence how innovative projects structure their compliance approaches. With public opinion showing notable support for reform, the key question remains: can Congress finalize a framework that protects investors, preserves competitive dynamics, and avoids hampering innovation in an industry still finding its regulatory footing? Watch for the final language of the markup and any amendments that signal a durable consensus or a fallback to earlier sticking points.
Source-based signals aside, the evolution of CLARITY—tied closely to the broader market-structure debate—will continue to intersect with how institutions engage with digital assets, how DeFi protocols navigate compliance, and how tokenized assets are treated under traditional regulatory paradigms. Investors and developers should monitor committee discussions, potential stakeholder briefings, and any new regulatory guidance that might accompany or follow enactment, as those elements will shape risk, opportunity, and timelines for deployment in the U.S. market.
Note: For context on the policy arc and related reporting, readers may reference contemporaneous coverage detailing the ongoing markup and negotiations surrounding the CLARITY Act and the broader crypto market-structure bill.
Crypto World
Four-Year Highs In US PPI Data Cost Bitcoin the $80,000 Mark

Bitcoin (BTC) fell below $80,000 into Wednesday’s Wall Street open as US inflation data continued to alarm.
Key points:
- Bitcoin price action sees fresh downside pressure thanks to US PPI inflation reaching its highest since 2022.
- Odds of further financial tightening by the Federal Reserve increased in a headwind for crypto.
- BTC price analysis sees the CME futures gap staying as resistance “until further notice.”
BTC price action loses $80,000 in fresh inflation blow
Data from TradingView showed a trip to near $79,500 accompanying the April release of the Producer Price Index (PPI).

BTC/USD one-hour chart. Source: Cointelegraph/TradingView
Like the Consumer Price Index (CPI) print the day prior, PPI delivered a surprise to the upside — a headwind for crypto and risk assets due to the implied future tightening of financial conditions by the Federal Reserve.
“The April increase is the largest advance since rising 1.7 percent in March 2022,” an official news release from the US Bureau of Labor Statistics (BLS) stated.
“On an unadjusted basis, the index for final demand rose 6.0 percent for the 12 months ended in April, the largest 12-month increase since moving up 6.4 percent in December 2022.”

US PPI one-month % change. Source: BLS
The US-Iran war and its associated impact on oil prices thus continued to filter through to the economy, with even more serious upheaval to come.
“All of the data is very clear: consumers are about to face another wave serious pressure on spending power,” trading resource The Kobeissi Letter wrote in a reaction on X.
The results further reduced the odds of the Fed cutting interest rates at its June meeting, with just a 1.4% chance of that outcome, per data from CME Group’s FedWatch Tool.

Fed target rate probabilities for June 17 FOMC meeting (screenshot). Source: CME Group
On Monday, trading resource Mosaic Asset Company summarized the risk that high oil prices, in particular, pose to the risk-asset uptrend.
“The prospect of rising interest rates on the short- and long-end of the yield curve could pose a challenge to stock market valuations,” it wrote in the latest edition of its regular newsletter, The Market Mosaic.
“The easing bias in central banks around the world is shifting to a more hawkish stance.”

CFDs on WTI crude oil one-day chart. Source: Cointelegraph/TradingView
Bitcoin futures gap in control “until further notice”
Bitcoin traders maintained hope for a successful breakout from current resistance for BTC/USD.
Related: Bitcoin price history suggests 77% odds of new all-time high within a year
“Break above that ~$82K region and that gap at $84K will surely be filled. Likely continuing quite a lot higher at that point,” Daan Crypto Trades wrote in his latest X analysis.
Daan Crypto Trades described US stocks as recovering “nicely” from their initial weakness over the CPI data.
“Market mostly awaiting some clarity in regards to the conflict in the middle east,” he added.

BTC/USDT perpetual contract one-day chart. Source: Daan Crypto Trades/X
Trader and analyst Rekt Capital, meanwhile, saw BTC/USD moving within an open “gap” in CME Group’s Bitcoin futures market — a common short-term price magnet.
“Bitcoin finally Weekly Closed below the top of the red area, confirming that price will be consolidating within the CME Gap until further notice,” he told X followers.

CME Bitcoin futures one-week chart. Source: Rekt Capital/X
Crypto World
Tokenized Treasuries hit $15 billion as BTC price stalls, Fed rate-hike concerns build: Crypto Daily

This is an excerpt from CoinDesk newsletter ‘Daybook.’ Sign up here, if you haven’t already.
While bitcoin remains pinned above $80,000, another interest rate-sensitive corner of the crypto market is booming and may suck capital out of other coins.
The total value locked in tokenized Treasuries has surged to $15.35 billion, topping the mid-April peak of around $15.10 billion, according to rwa.xyz data.
This comes as markets price in a higher probability of a Federal Reserve interest-rate hike (yes, an increase in borrowing costs), a stark shift from expectations for rapid rate cuts baked in earlier this year.
“The June cut just got significantly harder to defend, and the allocator positioning we flagged – capital sat in [BlackRock’s] BUIDL and tokenized T-bills rather than spot crypto – is going to look prescient by Friday,” Iggy Ioppe, CIO at Theo, said in an email.
Flows into yield-bearing tokenized Treasuries could rise further if today’s U.S. producer price index (PPI) points to persistent inflationary pressures in the pipeline. Consensus is for the April print to come in at 4.9% year-on-year, up from 4.0% in March.
An elevated reading would add to Fed rate-hike expectations and pose a headwind to risk assets. How bitcoin reacts remains to be seen, especially as it held largely steady above $80,000 after Tuesday’s hotter-than-expected CPI print.
While noting BTC’s resilience, analysts at Marex warned that further gains may be difficult if inflation continues to climb.
“That is the constraint for crypto: it can hold, but it will struggle to trend higher if real [inflation] rates keep grinding up,” analysts at Marex said.
Miners, too, present a potential headwind.
“If large miners are reporting big losses and pivoting toward AI, it usually means they may need to manage balance sheets more actively, which can translate into more spot supply on rallies. That is not a crash trigger, but it can cap upside in a choppy macro tape,” they noted.
In the broader market, smaller coins such as ING, DOT, ATOM and TRUMP added 5% or more, pointing to a rotation of capital into selective tokens. Majors like ether (ETH), solana (SOL), and XRP remain choppy.
Bitcoin and ether volatility indexes continue to point to near-term calm ahead of three major events: the PPI report, the Clartiy Act vote and the meeting between President Donald Trump and his Chinese counterpart, Xi Jingping.
In traditional markets, WTI crude oil futures bounced back above $100, while copper rose to near-record highs, both pointing to more commodity-led inflation ahead. Stay alert!
Read more: For analysis of today’s activity in altcoins and derivatives, see Crypto Markets Today . For a comprehensive list of events this week, see CoinDesk’s “Crypto Week Ahead.”
What’s trending
Today’s signal

Bitcoin appears to be at an inflection point, with the recovery from February lows stalling near the 200-day simple moving average (SMA) at around $82,300 and the upper boundary of a rising channel.
The momentum has stalled just as macro uncertainty around inflation and Federal Reserve policy intensifies.
A bearish resolution would involve BTC failing to break above the 200-day average and slipping below $75,000, which was widely cited as a key level in February-March. That could encourage systematic sellers back to the market, particularly if rising Treasury yields continue to tighten financial conditions and weigh on risk appetite.
On the bullish side, a decisive move above the 200-day average would confirm a bull market, potentially yielding a rally to as high as $92,000.
CORRECTION (May 13, 7:07pm ET): Updates Iggy Ioppe’s title.
Crypto World
What is the Next Resistance Level For Bitcoin Price?

After spending several sessions consolidating above the $72,000 level, Bitcoin briefly reclaimed the $81,000 mark before correcting. The 10% recovery over the past month has pushed Bitcoin back into a critical resistance zone that has capped the latest recovery attempt.
The real test for Bitcoin lies just ahead, with the $83,000 to $85,000 range emerging as the next major barrier.
A failure to maintain this zone would likely shift attention back to lower demand areas around $75,000 and $73,000, with the 100-day moving average near $72,000 acting as a key support level.
Bitcoin price tests key resistance zone
In the first 2 weeks of May, Bitcoin trading activity has also picked up, with 24-hour volume rising 4%.
For context, reviewing the broader Bitcoin price history shows that similar consolidation phases near key resistance levels have often preceded larger directional moves.
A break above the 200-day moving average, currently positioned between $83,000 and $85,000, would likely open the path toward $89,000.
Beyond that, the $94,000 level stands as the next technical checkpoint before any potential move toward the $100,000 psychological barrier.
Bitcoin’s MACD Signal Points to Strengthening Momentum
One of the more closely watched signals right now is the weekly MACD crossover, which flashed bullish on April 13.
Since then, Bitcoin has gained approximately 15%, indicating a shift in momentum after an extended recovery period.
Historical comparisons add context to this setup. Previous MACD crossovers have often preceded strong rallies.
The October 2023 signal came before a 147% move, while the October 2024 crossover was followed by a 75% gain. A similar signal in May 2025 resulted in a 35% rally.
While past performance does not guarantee future results, the consistency of these signals has drawn attention as Bitcoin approaches another major resistance cluster near the 200-day average.
A confirmed breakout above this level would likely bring $89,000 into focus, followed by $94,000.
From there, market participants would start evaluating the probability of a broader move toward $100,000.
Miner Behavior Suggests Limited Sell Pressure
On-chain data provides additional support for the current recovery structure. The Miners’ Position Index (MPI) dropped below -1.0 during the February lows near $60,000, a level historically associated with miner accumulation rather than distribution.
This suggests that miners were not aggressively selling during the market’s weakest phase, which helped reduce downward pressure as Bitcoin established a base.

Although the MPI has since recovered, it remains below zero. This indicates that miner selling is still relatively subdued compared to conditions typically seen near market tops.
Lower distribution from miners can help stabilize prices during upward moves.
That said, traders are monitoring whether the MPI climbs above 0.5. Such a shift could signal increased selling activity as prices rise, potentially slowing the rally’s pace.
Profit-Taking Activity Reflects Strong Demand Absorption
Data from Santiment shows that Bitcoin’s net realized profits recently reached $207.56 million as the price moved above $80,000.
This marks the highest level recorded in the current cycle and reflects increased profit-taking near a major psychological level.

Profit realization during upward price movement is not necessarily bearish. In many cases, it indicates that new demand is strong enough to absorb selling pressure from existing holders.
In this scenario, Bitcoin continued to push higher despite increased selling, suggesting that buyers are actively stepping in at current levels.
A weekly close above $81,000, followed by a successful retest of this level as support, would strengthen the bullish case.
If confirmed, this structure could pave the way for a move toward the $86,000 to $89,000 range, with $100,000 emerging as the next major upside target.
The post What is the Next Resistance Level For Bitcoin Price? appeared first on BeInCrypto.
Crypto World
Ether May Soar to Five-Digit Prices Fueled by Rising Institutional Adoption

Market analysts said Ether (ETH) was ready to continue its uptrend following moves by JPMorgan and BlackRock to launch tokenized funds on the Ethereum network.
Key takeaways:
- Institutional adoption is underway as JPMorgan and BlackRock plan to launch tokenized funds on Ethereum.
- Strong technical structures in multiple time frames suggest ETH price is bottoming out.
ETH traders anticipate the price to “outperform”
Data from TradingView showed ETH/USD trading at $2,320, up 2% over the last 24 hours.
The pair failed to crack through resistance at $2,400 last week, as spot Ether exchange-traded fund (ETF) outflows and rising balance on Binance derailed Ether’s recovery.
As such, bulls must push and hold the ETH/USD pair above $2,400 to continue the uptrend.
In a Wednesday post on X, analyst CryptoJack said ETH is “getting ready for a pump” as it consolidates inside a symmetrical triangle on lower time frames.
“A breakout could lead to a strong move soon.”

ETH/USD chart. Source: X/CryptoJack
Crypto Patel’s chart shows ETH trading inside an ascending triangle that has guided its price action since 2020. ETH is bouncing off the triangle’s lower trendline around $1,800, a zone that previously acted as a launchpad for large upside moves.
The analyst sets the upside target for Ether at $10,000-$15,000, saying:
“$ETH will outperform this cycle.”

ETH/USD two-week chart. Source: X/Crypto Patel
Fellow crypto analyst Celal Kucuker also shared a bullish argument, laying out a long-term roadmap that places ETH on course for a possible move above $24,000.

ETH/USD one-month chart. Source: X/Celal Kucuker
Momentum indicators support the rebound thesis. Ether’s monthly relative strength index (RSI) has cooled toward a historical support area near 42-455, similar to levels that preceded past rallies.
As Cointelegraph reported, buyers will be back in control once the ETH/USD pair breaks above the $2,450-$2,600, confirming a trend shift.
Institutional adoption fuels Ether’s bullishness
As Cointelegraph reported, JPMorgan is set to launch a tokenized money market fund on Ethereum, allowing stablecoin issuers to hold reserves backing their stablecoins while earning interest.
Related: Bitmine slows Ethereum buys, targets December to own 5% of supply
BlackRock, the world’s largest asset manager, has also filed for tokenized versions of its Treasury liquidity funds, where official ownership records will be maintained on Ethereum using ERC-20 token standards.

Source: Cointelegraph
“Institutional adoption just hit another level,” analysts at Ethereum Daily said in a post on X on Wednesday.
“This is the most bullish news for Ethereum,” X user Borovik said in a reaction to the news on Wednesday.
Tokenized funds on Ethereum, bulls argue, will drive onchain activity, increase gas demand and total value locked (TVL). This will, in turn, boost the blockchain’s legitimacy, making ETH the preferred settlement layer for trillions in TradFi capital.
Data from RWA.xyz shows that global tokenized funds already exceed $31 billion, with Ethereum dominating approximately 55% of the space.

Total global RWA value. Source: RWA.xyz
These were not the only bullish news for Ethereum. MN Capital founder Michael van de Poppe said that the approval of the CLARITY Act, which is scheduled for markup on Thursday, would be a “massive trigger for the markets.”
Market analyst Ethprofit.eth said the CLARITY Act “looks extremely bullish for Ethereum,” while Bitcoin Mami said “institutional demand is going insane post CLARITY Act,” pushing ETH price to $10,000.
Polymarket bettors are pricing in a 60% chance that the CLARITY Act will be signed into law in 2026, down 5% over the last 24 hours.

Odds of the CLARITY Act being signed into law in 2026. Source: Polymarket
If the CLARITY Act becomes law, Ether is expected to rally, as seen in July 2025, when the signing of the GENIUS Act into law preceded a 65% ETH price rise to its current all-time high of $4,950 from $3,000.
Crypto World
BeInCrypto Institutional Research: 15 Digital Asset Products Driving Crypto Investment


Best Digital Asset Product is a category within the BeInCrypto Institutional 100, an annual research-driven program recognising institutional digital asset excellence across 26 categories and six pillars.
This category sits under Pillar 3: Access to Digital Assets. The 15 products below are listed alphabetically by issuer and are not ranked. Each entry is anchored on the specific product, not the issuing firm. A shortlist will be named in May 2026, with the winner announced at Proof of Talk in Paris on June 2–3, 2026.
Key Facts
- Long list: 15 products across spot crypto ETFs, tokenized MMFs, tokenized treasuries, private credit and PE funds, tokenized equities, bonds, and regional product stacks
- Initial pool: More than 30 firms screened; 15 advanced to the long list
- Order: Listed alphabetically by issuer, not ranked
- Scoring: 50% quantitative data · 50% Expert Council
- Criteria assessed: AUM, net flows, product structure, regulatory licensure, multi-jurisdiction footprint, on-chain reach, fee structure, distribution channels, institutional holders, innovation signal
- Data sources: SEC EDGAR, ETF flow trackers, SFC, VARA, FCA, FINMA, BaFin, MAS, MiCA-CASP registers, audited reports, ratings agencies, PitchBook, Tracxn, and Crunchbase
| Product / Issuer | HQ & Listing | Reach | Product Structure | Representative Work |
| Apollo Global Management — ACRED | New York · NYSE: APO | $1.026T AUM Six chains live |
Tokenized private credit fund Apollo Diversified Credit Securitize Fund |
ACRED tokenizes Apollo Diversified Credit Fund via Securitize Live on Aptos, Avalanche, Ethereum, Ink, Polygon, and Solana |
| Backed Finance — bCSPX, bIB01, xStocks | Zug, Switzerland FINMA-aligned; Kraken-owned |
$25B+ transaction volume since June 2025 100 tokenized stocks live |
Tokenized equities and bond products xStocks tokenized equity suite |
bCSPX tokenizes S&P 500 ETF exposure; bIB01 tokenizes short-term Treasuries xStocks Alliance includes Bybit, Gate.io, KuCoin, Talos, and 360X |
| BlackRock — IBIT, ETHA, BUIDL | New York · NYSE | $14T+ platform AUM IBIT $66.9B; BUIDL $2.5B–$2.85B |
Spot crypto ETFs Tokenized money market fund |
IBIT became the fastest ETF to cross $80B AUM BUIDL expanded across eight chains |
| Bitwise — BITB, BSOL | San Francisco · NYSE Arca | $11B client assets 40+ investment products |
Spot Bitcoin ETF Solana ETP with staking exposure |
BSOL launched on NYSE Arca in Oct 2025 Built direct SOL exposure with staking rewards target |
| Fidelity — FBTC, FETH | Boston, USA Fidelity Digital Assets OCC conditional charter |
$15T+ platform AUA FBTC $13B–$15B AUM |
Spot Bitcoin and Ethereum ETFs Vertically integrated custody model |
FBTC and FETH combine Fidelity asset management with Fidelity Digital Assets custody Product stack differs from pure ETF issuers through internal custody infrastructure |
| Franklin Templeton — BENJI/FOBXX, EZBC, EZET | San Mateo, CA · NYSE: BEN | $1.74T AUM BENJI deployed across 8+ chains |
Tokenized money market fund Spot Bitcoin and Ethereum ETFs |
FOBXX/BENJI was the first US-registered fund using public blockchain record-keeping Franklin built multi-chain tokenized fund distribution |
| Hamilton Lane — SCOPE, Secondary Fund VI, Direct Equity | Conshohocken, PA · Nasdaq: HLNE | $1T AUM and supervision 780 professionals globally |
Tokenized private credit and private markets funds Securitize-based access structure |
SCOPE went multi-chain on Ethereum and Optimism Secondary Fund VI feeder reduced minimums from $5M to $20K |
| Hashnote / Circle — USYC | New York Bermuda-regulated; Cayman fund structure |
$3B+ AUM Largest tokenized MMF globally by AUM |
Tokenized institutional money market fund Backed by Treasury bills and reverse repos |
USYC overtook BlackRock BUIDL in Jan 2026 Integrated with USDC for 24/7 collateral movement |
| Janus Henderson — JTRSY, JAAA, SPXA | London · NYSE: JHG | $457B AUM 25 offices worldwide |
Tokenized treasury and index funds Rated tokenized fund products |
JTRSY received S&P AA+f / S1+ rating SPXA launched on Base as S&P-licensed tokenized index fund |
| KKR — SKHC / HCSG II | New York · NYSE: KKR | $700B+ AUM Underlying HCSG II fund at $4B |
Tokenized private equity fund Avalanche and Securitize structure |
KKR tokenized Health Care Strategic Growth Fund II as SKHC Product remains available to qualified investors |
| Ondo Finance — OUSG, USDY, Ondo Global Markets | New York Private company; ONDO publicly traded |
$1.81B+ platform TVL 265 tokenized securities and ETFs |
Tokenized treasuries, yield products, tokenized securities Multi-chain market access |
SEC investigation closed without charges in late 2025 Ondo Global Markets reached significant tokenized stocks share |
| OpenEden — TBILL | Singapore BVI feeder fund; BNY-managed |
$260M+ AUM 10x year-on-year growth |
Tokenized US Treasury bills Investment-grade rated product |
First tokenized T-bill product with dual Moody’s and S&P investment-grade ratings BNY appointed investment manager and custodian |
| OSL — Tokenworks, HK Spot ETF Servicing, Taikang MMF | Hong Kong HKEX-listed parent; SFC-licensed VATP |
Sub-custodian and exclusive VATP for Hong Kong spot crypto ETFs Supports BTC, ETH, and SOL ETF servicing |
Tokenization platform and ETF servicing stack Hong Kong institutional product infrastructure |
Distributor and custody partner for Hong Kong’s first tokenized MMF under unit-trust structure Tokenworks serves Tier-1 Hong Kong asset managers |
| Superstate — USTB, USCC, FundOS | New York SEC-registered investment adviser and transfer agent |
USTB $967M AUM USCC $267M AUM |
Tokenized US Treasuries and crypto carry fund White-label tokenization infrastructure |
USTB transitioning to Invesco Advisers as investment manager FundOS powers Coinbase Asset Management’s CUSHY stablecoin yield fund |
| T. Rowe Price — TKNZ | Baltimore, USA · NYSE: TROW | $1.7T–$1.8T platform AUM ETF pending approval |
Active crypto ETF filing 5–15 eligible crypto assets |
TKNZ S-1 filed for active crypto ETF on NYSE Arca Anchorage Digital Bank named as crypto custodian |
About This List
The BeInCrypto Institutional 100 — Best Digital Asset Product (2026 Long List) identifies named institutional products giving investors access to digital assets. The category covers spot ETFs, ETPs, tokenized money market funds, tokenized treasuries, tokenized private credit and equity funds, tokenized securities, and regional product stacks.
Unlike asset manager categories, this list focuses on the product itself. A firm may appear because of one specific ETF, tokenized fund, treasury product, or integrated product suite that meets the long-list threshold.
Methodology
This category is evaluated under Track A of the BeInCrypto Institutional 100 methodology: 50% quantitative data and 50% Expert Council scoring.
Assessment spans AUM and cumulative net flows, product structure, regulatory licensure, jurisdictional footprint, on-chain reach for tokenized products, fee structure, distribution channels, institutional holder concentration, and innovation signal.
Data was verified using SEC EDGAR, ETF flow trackers, SFC, VARA, FCA, FINMA, BaFin, MAS, MiCA-CASP registers, audited reports, Moody’s tokenized product ratings, S&P Global Ratings tokenized fund ratings, KBRA/Kroll, PitchBook, Tracxn, and Crunchbase.
The post BeInCrypto Institutional Research: 15 Digital Asset Products Driving Crypto Investment appeared first on BeInCrypto.
Crypto World
Anthropic, OpenAI tokens plunge as AI firms say pre-IPO share transfers are invalid


The Solana-based tokens marketed as a way to gain exposure to Anthropic and OpenAI before they go public got an unwelcome reality check this week.
The two companies said the transfer of privately held shares to the special purpose vehicles (SPVs) that back the tokens is invalid because any such move requires approval by the corporate board.
The tokens slumped. Anthropic PreStocks (ANTHROPIC), issued by Solana-based platform PreStocks to represent Anthropic shares, dropped 34% in seven days, while OpenAI PreStocks fell 39%, CoinGecko data show.
PreStocks uses SPVs, legal entities set up specifically to hold something on behalf of investors, to hold the shares, and issues tokens on Solana that represent indirect economic exposure to those shares.
“We do not permit special purpose vehicles to acquire Anthropic stock and any transfer of shares to an SPV are void under our transfer restrictions,” Anthropic said in an updated investor warning page.
Any third party claiming to sell its shares through “direct sales, forward contracts, tokenized securities, or other mechanisms” is “likely either engaged in fraud or offering an investment that may have no value due to our transfer restrictions,” the company said.
OpenAI issued a similar warning, saying unauthorized transactions may violate U.S. securities laws and could result in the invalidation of the underlying equity. Both companies named several intermediaries. Anthropic listed Open Door Partners, Hiive and Forge as unauthorized to buy or sell its shares.
While PreStocks tokens claim 1:1 backing through SPVs, neither the platform nor any third-party auditor has published the attestation reports the company promised at launch.
Liquidity is a concern as well. Data from PreStocks shows just over $333,000 in stablecoins and $18,000 in solana (SOL) in Anthropic liquidity as of Wednesday, meaning early buyers sitting on big profits might not be able to fully cash out. This exposes the gap between the implied valuations on the platform and what the underlying SPVs can actually deliver.
The dashboard also shows an implied Anthropic valuation above $1.3 trillion against the platform holding roughly $23 million in total assets, a gap that gave the companies the structural opening to push back.
PreStocks debuted in August 2025 with backing from Republic Capital and is led by CEO Xavier Ekkel. The platform is unavailable to residents of the U.S., Singapore, the European Union, and certain sanctioned jurisdictions, and requires know-your-customer processes for minting and redemptions. Partnerships at launch included Jupiter and Meteora, both decentralized exchanges on Solana.
-

 Crypto World6 days ago
Crypto World6 days agoHarrisX Poll Found 52% of Registered Voters Support the CLARITY Act
-

 Fashion5 days ago
Fashion5 days agoWeekend Open Thread: Marianne Dress
-

 Crypto World7 days ago
Crypto World7 days agoUpbit adds B3 Korean won pair as Base token gains Korea access
-

 NewsBeat7 days ago
NewsBeat7 days agoNCP car park operator enters administration putting 340 UK sites at risk of closure
-

 Fashion2 days ago
Fashion2 days agoCoffee Break: Travel Steam Iron
-

 Tech4 days ago
Tech4 days agoAuto Enthusiast Carves Functional Two-Stroke Engine from Solid Metal
-

 Fashion3 days ago
Fashion3 days agoWhat to Know Before Buying a Curling Wand or Curling Iron
-

 Politics2 days ago
Politics2 days agoWhat to expect when you’re expecting a budget
-

 Business5 days ago
Business5 days agoIgnore market noise, India’s long-term story intact, say D-Street bulls Ramesh Damani and Sunil Singhania
-
 Politics5 days ago
Politics5 days agoPolitics Home Article | Starmer Enters The Danger Zone
-

 Tech3 days ago
Tech3 days agoGM Agrees To Pay $12.75 Million To Settle California Lawsuit Over Misuse Of Customers’ Driving Data
-
 Politics6 days ago
Politics6 days agoSimon Cowell Says He Was ‘Horrible’ To Susan Boyle During BGT Audition
-

 Entertainment7 days ago
Entertainment7 days agoSarah Paulson Called Out For Met Gala ‘Hypocrisy’
-

 Entertainment6 days ago
Entertainment6 days agoGeneral Hospital: Ric & Ava Bombshell – Ric’s Massive Secret Exposed!
-

 Crypto World7 days ago
Crypto World7 days agoRobinhood says Wall Street is building onchain
-
 Sports7 days ago
Sports7 days agoUEFA Champions League final schedule, teams, venue, live time and streaming | Football News
-

 Entertainment6 days ago
Entertainment6 days agoWhy David Letterman Called CBS ‘Lying Weasels’
-
Entertainment7 days ago
Hayden Panettiere reveals she's estranged from mom, addresses brother Jansen's sudden death: 'I was floored'
-

 Sports7 days ago
Sports7 days agoMike Tyson speaks out on status of Floyd Mayweather fight
-

 Entertainment7 days ago
Entertainment7 days agoParamount+’s ‘Landman’ Season 3 Gets Promising New Update From Returning Director









You must be logged in to post a comment Login