Isn’t there some claim events come in threes? After the extremely rare leak of the iOS Coruna exploit chain recently, now we have details from Google on a second significant exploit in the wild, dubbed Darksword.
Like Coruna, Darksword appears to have followed the path of government security contractors, to different government actors, to crypto stealer. It appears to focus on exploits already fixed in modern iOS releases, with most affecting iOS 18 and all patched by iOS 26.3.
Going from almost no public examples of modern iOS exploits to two in as many weeks is wild, so if mobile device security is of interest, be sure to check out the Google write-up.
Another FBI Router Warning
The second too early to be retro – but too important to ignore – repeat security item is a second alert by the FBI cautioning about end-of-life consumer network hardware under active exploitation, with the FBI tracking almost 400,000 device infections so far.
Like the warning two weeks ago, the FBI calls out a handful of consumer routers – but this time they’re devices that may actually still be service in some of our homes (or our less cutting edge friends and family), calling out devices from Netgear, TP-Link, D-Link, and Zyxel:
- Netgear DGN2200v4 and AC1900 R700
- TP-Link Archer C20, TL-WR840N, TL-WR849N, and WR841N
- D-Link DIR-818LW, 850L, and 860L
- Zyxel EMG6726-B10A, VMG1312-B10D, VMG1312-T20B, VMG3925-B10A, VMG3925-B10C, VMG4825-B10A, VMG4927-B50A, VMG8825-T50K
While many of these devices are over ten years old, they still support modern networking – some of them even supporting 802.11ac (also called Wi-Fi 5). Unfortunately, since support has been ended by the manufacturers, publicly disclosed vulnerabilities have not been patched (and now never will be, officially)
Once infected, the routers are enrolled in the AVRecon malware network, which includes the now-typical suite of behavior of remote control, remote VPN access to the internal and external networks, DNS hijacking, and DDoS (distributed denial of service) attacks. This sort of network malware is used by attackers to exploit internal systems like un-patched Windows or IOT devices on the local network, and as a launching point to hide behavior as coming from a certain country or state by using the public Internet connection as a VPN. It’s also often monetized by unscrupulous apps selling cheap VPN service.
The worst type of vulnerability affecting home routers is one which can be triggered remotely from the Internet without user interaction – for instance CVE-2024-12988 which allows arbitrary code execution remotely on Netgear devices, but even vulnerabilities which are only accessible from the local network can be combined with cross-site vulnerabilities or vulnerabilities in other devices to exploit home routers. A malware infection on a Windows system can be leveraged to install additional, permanent malware installs on routers and IOT devices, and malware on a router can be used to redirect the user to install more malware on an internal PC via manipulating the network, or allow direct attack of internal systems via a proxy.
A slight upside is that this batch of vulnerable hardware is often modern enough to run OpenWRT or other replacement firmware. OpenWRT supports thousands of routers and access points – and often forms the basis of the commercial firmware the device was shipped with, before the manufacturer abandoned it. Converting a device to OpenWRT may be intimidating for some, but for anyone with one of the listed devices, the time to try is now! It’s cheaper than buying a new device, and worst case scenario, you’d have to replace that router anyway!
You can use the OpenWRT Table of Hardware to see if there is a version for your device.
Unfortunately, vulnerabilities in home routers don’t offer many lessons: there’s rarely a need to log into them to see if there is a pending update, and almost nothing the typical home user can do except buy a new device when the manufacturer stops supplying security fixes.
Trivy Compromised
The Trivy security scanner suffered a breach themselves, leading to a cascading series of breaches of other tools. Trivy is an automatic vulnerability scanner for finding vulnerabilities is the dependencies of Docker and other container images, package repositories, and language packages in Go, PHP, Python, Node, and many other popular languages. Trivy is often integrated into the CI/CD (continual integration and continual deployment) process of other open and closed source projects and internal company processes.
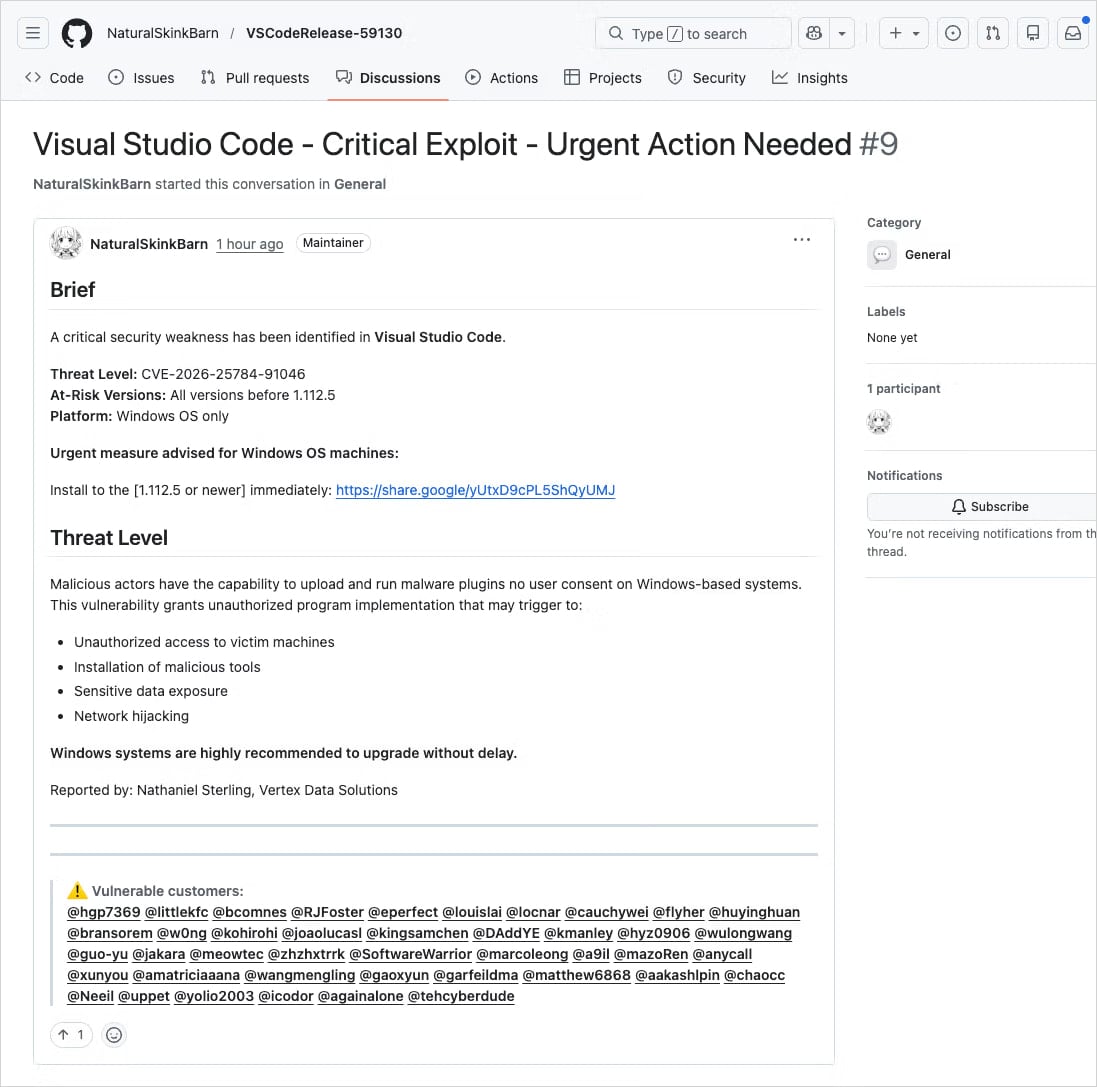
According to the timeline published by Aqua, in late February 2026 a misconfigured GitHub workflow allowed the theft of authentication tokens for the Trivy project. While the attack was detected and the credentials removed, not all credentials were properly removed, which allowed the attackers to complete the attack on March 19, 2026.
Once compromised, all but one release of the Trivy GitHub actions were replaced with trojaned malicious copies, spreading the compromise to any project which used the Trivy GitHub actions, spreading the malware payload to many projects using the Trivy scanner actions.
 GitHub actions are part of GitHub which allows scripts when repository actions like a pull request or merge are performed. Actions can be used to check that a change compiles properly, scan for security issues, generate documentation, or generate release binaries, and typically are allowed to make changes to the repository itself. GitHub workflows can include actions from other repositories via the Action Marketplace. By replacing the Trivy actions, the attackers essentially gained access to every repository using Trivy to scan for vulnerabilities in their own codebases.
GitHub actions are part of GitHub which allows scripts when repository actions like a pull request or merge are performed. Actions can be used to check that a change compiles properly, scan for security issues, generate documentation, or generate release binaries, and typically are allowed to make changes to the repository itself. GitHub workflows can include actions from other repositories via the Action Marketplace. By replacing the Trivy actions, the attackers essentially gained access to every repository using Trivy to scan for vulnerabilities in their own codebases.
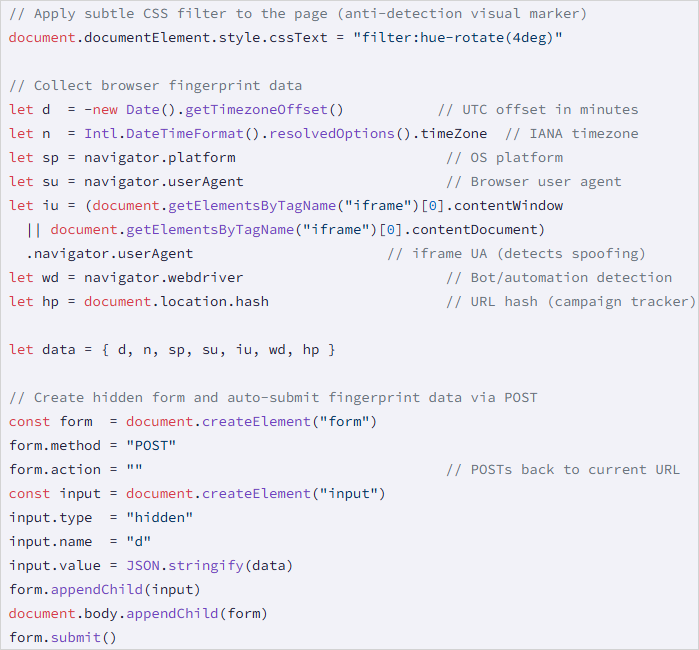
The hijacked Trivy actions collected and exfiltrated access tokens for Docker, Google Cloud, Azure, and AWS, Git credentials, SSH keys, and any other secrets from projects using the Trivy actions. With these keys, the controllers of the original malware are able to attack those projects directly, such as the immensely popular LiteLLM Python interface to AI LLM models from multiple companies.
The compromise of LiteLLM also stole credentials to cloud services, SSH, git, Docker, and Kubernetes on any system that ran the trojaned setup scripts, as well as infecting any connected Kubernetes systems found in the configurations.
There are also reports that the malware actors are also infecting NPM node packages with malware which automatically updates itself from a block-chain based control system and steals NPM authentication tokens to inject itself into any NPM packages the victim may have authored.
Supply-chain attacks happening for years with varying levels of success. But the Trivy attack may be the most successful in spreading compromised packages into multiple package repositories. It’s difficult to avoid supply chain attacks, especially when the vulnerability scanner itself is the source of the problem. GitHub has introduced immutable releases – tagged build versions which can not be updated once released, and the immutable release of Trivy was the only version not compromised by the attackers. As more packages shift to immutable versions it may become harder to insert malware into the supply, but we’re nowhere near a tipping point of projects using immutable releases yet.


































































You must be logged in to post a comment Login