Tech
‘Saros’ Shows Off the PS5’s DualSense Tricks

Spoiler for the very first thing you see in the upcoming game Saros: It’s a bunch of words. The letters type out one by one onto the screen, spelling out some world-building that gives context to kick off the game’s story. I don’t remember what any of it said, because I was so focused on the tactile vibrations coming from the controller in my hands. There is a sharp haptic buzz for every letter, and it immediately feels very clicky-clacky. From the very beginning, Saros makes its intentions clear—this is a story you’ve got to feel.
Since the launch of the PlayStation 5, Sony’s DualSense controllers have enabled haptic feedback that developers can use to make the controller vibrate in just the right way to communicate the feel of what is happening on the screen. Maybe it’s letters typing across the screen, little patters of rainfall, or a big rumble when shooting a gun or whacking something with a melee weapon. Adaptive triggers add resistance to the main triggers, meaning the difference between feathering the trigger and pulling it all the way down is very apparent.
Saros, launching on April 30, is developed by Housemarque, a Finnish studio owned by Sony. It has been here before, when it released the highly regarded PlayStation 5 game Returnal in 2021. That game, as a launch title for the console, aimed to make use of all the new technology Sony was offering with its hardware, especially the haptic and adaptive features in the DualSense controller. Gregory Louden, the creative director at Housemarque who has helmed development on both games, says both titles came with an added bit of pressure to show off what the console could do.
“Back when we started Returnal, we almost felt a responsibility—because we were a launch window title for PlayStation 5—what can you do with this hardware?” Louden tells WIRED. “In a lot of ways, we’re doing it for our players, but also doing it for the medium to try to inspire others.”
As it did with Returnal, Housemarque has developed its newest game to take full advantage of the PlayStation 5’s DualSense controllers. It also uses 3D audio features to make the world feel more lively. Returnal and Saros came out on the same hardware, but Louden says it all gels even more now than ever.
“We’ve really pushed the graphics and pushed the hardware,“ Louden says. “We wanted to do something even better for players and really make the most of the DualSense.”
From the few hours I’ve spent with it, Saros feels quite excellent to play. It is a dark sci-fi roguelike where you mow down dozens of hostile aliens in a barrage of frenetic, tactile gameplay. The battles feel especially palpable because everything onscreen translates to what you feel in the controller. The obvious moves are replicating the feel of shooting a weapon or feeling the reverberations when the enemies’ bullets and explosives crash into your shield. But Housemarque has also deployed haptics in more careful, subtler ways, like during cinematics, where a steady haptic pulse helps make the onscreen characters’ tension and anger more visceral.
Tech
Today’s NYT Mini Crossword Answers for April 26
Looking for the most recent Mini Crossword answer? Click here for today’s Mini Crossword hints, as well as our daily answers and hints for The New York Times Wordle, Strands, Connections and Connections: Sports Edition puzzles.
Need some help with today’s Mini Crossword? Read on for all the answers. And if you could use some hints and guidance for daily solving, check out our Mini Crossword tips.
If you’re looking for today’s Wordle, Connections, Connections: Sports Edition and Strands answers, you can visit CNET’s NYT puzzle hints page.
Read more: Tips and Tricks for Solving The New York Times Mini Crossword
Let’s get to those Mini Crossword clues and answers.
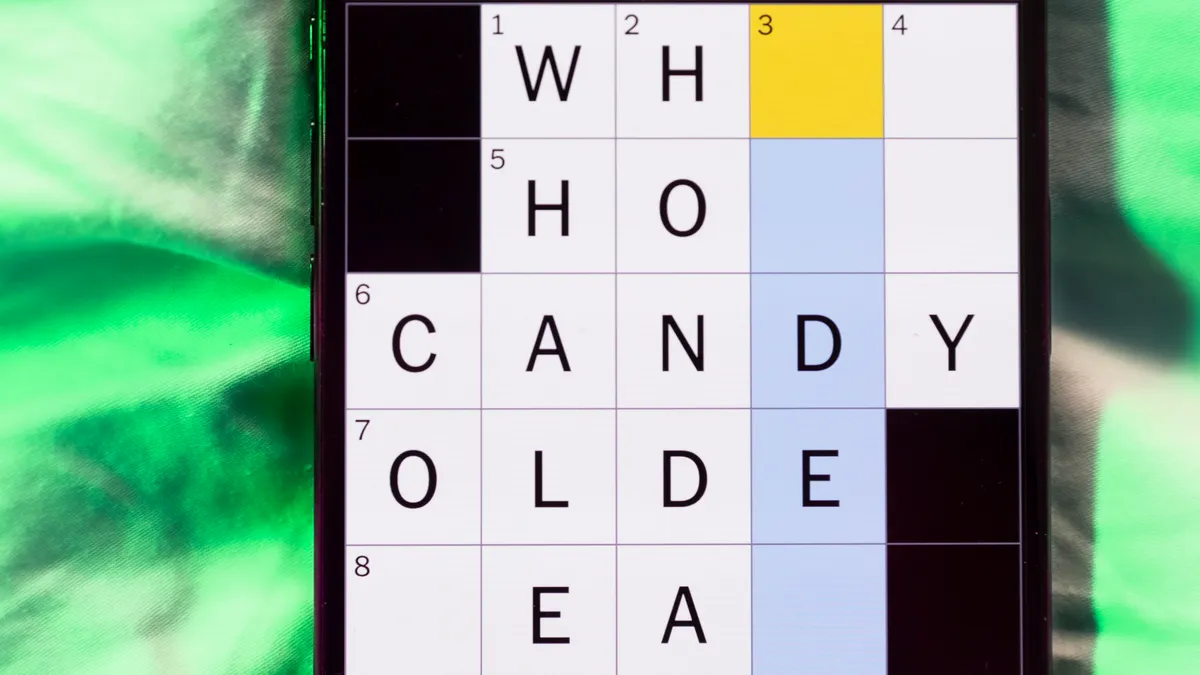
The completed NYT Mini Crossword puzzle for April 26, 2026.
Mini across clues and answers
1A clue: Alternative to electric, for a stove
Answer: CASA
5A clue: Developer’s projects
Answer: APPS
6A clue: Sketch comedy spinoff launched on March 21, 2026
Answer: SNLUK
7A clue: One of 24
Answer: HOUR
8A clue: Gas brand with a green-and-white logo
Answer: HESS
Mini down clues and answers
1D clue: Kayak alternative
Answer: CANOE
2D clue: Great grade
Answer: APLUS
3D clue: N.B.A. team with the 7’4” star Victor Wembanyama
Answer: SPURS
4D clue: “___ not what your country can do for you …”
Answer: ASK
6D clue: Sound made with a finger to the lips
Answer: SHH
Tech
Today’s NYT Connections: Sports Edition Hints, Answers for April 26 #580

Looking for the most recent regular Connections answers? Click here for today’s Connections hints, as well as our daily answers and hints for The New York Times Mini Crossword, Wordle and Strands puzzles.
Today’s Connections: Sports Edition is a tough one. If you’re struggling with today’s puzzle but still want to solve it, read on for hints and the answers.
Connections: Sports Edition is published by The Athletic, the subscription-based sports journalism site owned by The Times. It doesn’t appear in the NYT Games app, but it does in The Athletic’s own app. Or you can play it for free online.
Read more: NYT Connections: Sports Edition Puzzle Comes Out of Beta
Hints for today’s Connections: Sports Edition groups
Here are four hints for the groupings in today’s Connections: Sports Edition puzzle, ranked from the easiest yellow group to the tough (and sometimes bizarre) purple group.
Yellow group hint: Whack!
Green group hint: Hoops team monikers.
Blue group hint: Common last name.
Purple group hint: Not 2 or 3.
Answers for today’s Connections: Sports Edition groups
Yellow group: Hard-hit baseball.
Green group: NBA teams with singular nicknames.
Blue group: ____ Johnson.
Purple group: What “1” might mean.
Read more: Wordle Cheat Sheet: Here Are the Most Popular Letters Used in English Words
The completed NYT Connections: Sports Edition puzzle for April 26, 2026.
What are today’s Connections: Sports Edition answers?
The yellow words in today’s Connections
The theme is hard-hit baseball. The four answers are frozen rope, laser, liner and screamer.
The green words in today’s Connections
The theme is NBA teams with singular nicknames. The four answers are Heat, Jazz, Magic and Thunder.
The blue words in today’s Connections
The theme is ____ Johnson. The four answers are Flau’jae, Gus, Lane and Randy.
The purple words in today’s Connections
The theme is what “1” might mean. The four answers are fastball, pitcher, point guard and top rank.
Tech
The climate tech IPO window could finally be cracking open

Climate tech startups are capital intensive, timelines are long, and the technology is often considered “first of its kind.” What’s more, a key value proposition is addressing pollution — an externality that is, at best, poorly priced by the market. Those aren’t the qualities stock pickers tend to favor.
And yet, public markets appear to be warming to climate tech startups — or at least some of them.
This week, nuclear startup X-energy went public, raising $1 billion in an upsized share offering that appears to have delivered a windfall for its investors, including Amazon. Retail investors apparently can’t get enough, with the stock popping 25% in its first hour of trading. Also this week, geothermal startup Fervo said it filed for an initial public offering. The size of the Fervo IPO has yet to be disclosed, but private investors have valued the company at around $3 billion, according to PitchBook.
The move to go public aligns with what investors told TechCrunch at the end of last year. After years of tepid attitudes toward climate tech companies, they expected public markets to start welcoming energy-related startups. Nearly every investor that weighed in on the question said the startups with the best chances of going public specialize in either nuclear fission or enhanced geothermal. Fervo, specifically, was mentioned several times.
Thank data centers for that. The AI craze has taken a trend of rising demand for electricity and made it sexy and salable. Companies that were already betting on the upswing lucked into a trending narrative that coincided with their technological maturity. Fortune certainly favors the prepared.
The IPOs are also certain to please investors, letting them return capital to their LPs. The recent dearth of IPOs has kept a chunk of climate tech funding locked up, at a time when many funds would like to start cashing out.
But it’s not just about cashing out.
Techcrunch event
San Francisco, CA
|
October 13-15, 2026
Fervo and X-energy have followed the traditional route to public markets, suggesting there is confidence that a broad base of investors wants to participate. If it were just about freeing up investor capital, the startups could have followed the SPAC route. (Several have.) But these two companies took the longer path.
Yet for all that success, a wide swathe of climate tech will probably be left out of the IPO wave.
Companies that aren’t entangled in energy markets will have to find other ways to press on — and without access to the deep pockets the public market provides. The divergence suggests the climate tech world is starting to go K-shaped, a trend which Mark Cupta, managing director at Prelude Ventures, suggested when I spoke to him a little over a week ago.
Companies stuck on the poorer side of the IPO window still have private investors to lean on. But there, too, a K-shaped trajectory is starting to appear.
Venture capital and growth funds raised about $6.5 billion last year, according to Sightline Climate. That’s the same as in 2021, but because there are more funds today, each fund is now smaller. For founders, that could be bad news since funds have less to draw on. On the upside, more competition could drive better fundraising results.
At the same time, the big funds keep getting bigger. Infrastructure dominated climate tech fundraising last year, with 42 funds raising 75% of all dollars in the sector, according to Sightline Climate. That success will spill over into the startup side if it’s a company with a mature technology that is ready to build big.
Sightline said that many new infrastructure funds are specializing in renewables, grid technologies, and energy storage. In other words, the K-shape isn’t going away anytime soon.
When you purchase through links in our articles, we may earn a small commission. This doesn’t affect our editorial independence.
Tech
OpenAI CEO apologizes to Tumbler Ridge community

In a letter to the residents of Tumbler Ridge, Canada, OpenAI CEO Sam Altman said he is “deeply sorry” that his company failed to alert law enforcement about the suspect in a recent mass shooting.
After police identified 18-year-old Jesse Van Rootselaar as a suspected shooter who allegedly killed eight people, the Wall Street Journal reported that OpenAI had flagged and banned Van Rootselaar’s ChatGPT account in June 2025 for after she described scenarios involving gun violence. The company’s staff debated alerting police but ultimately decided against it, eventually reaching out to Canadian authorities after the shooting.
OpenAI has since said that it is improving safety protocols, for example by putting more flexible criteria in place to determine when accounts get referred to authorities, and by establishing direct points of contact with Canadian law enforcement.
In Altman’s letter, which was first published in the local newspaper Tumbler RidgeLines, the CEO said he’d discussed the shooting with Tumbler Ridge Mayor Darryl Krakowka and British Columbia Premier David Eby, and they’d all agreed “a public apology was necessary,” but “time was also needed to respect the community as you grieved.”
“I am deeply sorry that we did not alert law enforcement to the account that was banned in June,” Altman said. “While I know words can never be enough, I believe an apology is necessary to recognize the harm and irreversible loss your community has suffered.”
Altman also said that OpenAI’s focus will “continue to be on working with all levels of government to help ensure nothing happens like this again.”
In a post on X, Eby said Altman’s apology is “necessary, and yet grossly insufficient for the devastation done to the families of Tumbler Ridge.”
Techcrunch event
San Francisco, CA
|
October 13-15, 2026
Canadian officials have said they are considering new regulations on artificial intelligence but have not made any final decisions.
If you are in a crisis or having thoughts of suicide, call or text 988 to reach the 988 Suicide and Crisis Lifeline.
When you purchase through links in our articles, we may earn a small commission. This doesn’t affect our editorial independence.
Tech
The Online Civil War About ‘Michael’ Is a Battle Over Truth

Is truth determined by the size of the audience it reaches?
If so, Michael—a new film about the pop singer Michael Jackson that is on track to have the biggest-ever opening for a music biopic, with projected earnings of $70 million at the US box office, despite critics saying it sanitizes the reality of who Jackson actually was—intends to supplant the King of Pop as the apotheosis of artistic virtue.
The film’s release has sparked a civil war online, between those eager to reclaim the music and myth of Jackson, and those who see any celebration of him as a failure of accountability.
Musically, Jackson was in a class all his own. In the pre-social media days, before AI artists charted on Billboard and he became a recurring meme online, Jackson was the epitome of monoculture: 13 number one singles, countless awards, twice inducted into the Rock & Roll Hall of Fame. He remains, even in death, one of the best-selling music artists of all time. But his legacy was also defined by multiple allegations of sexual abuse, an occasionally eccentric personal life, and Jackson’s on-record admission of sharing his bed with underage boys. “This guy was worse than Jeffrey Epstein,” Dan Reed, the director of Leaving Neverland, the 2019 Emmy-winning HBO documentary about Jackson’s alleged sexual misconduct, recently told the Hollywood Reporter.
Director Antoine Fuqua, who maintains Jackson’s innocence, never intended to fully avoid the allegations that circled Jackson later in life. According to him, the original cut of Michael included a reenactment of the 1993 police raid on Neverland Ranch, where Jackson was strip-searched to verify the physical description of his first accuser, Jordan Chandler. But the scene was ultimately scrapped along with the film’s entire third act—totaling $15 million in reshoots—because of a legal clause in a settlement with Chandler that prohibited the depiction of his experience on screen.
The result is a film that stops abruptly in 1988 and erases the most controversial two decades of Jackson’s life. Instead, the film emphasizes Jackson’s musical legacy—the story arc is structured around career-defining music moments, like the making of the “Thriller” video—over the more contentious aspects of his personal behavior.
Scrubbing the Neverland Ranch scene, but also choosing to completely write around any of Jackson’s alleged misconduct, is not surprising given that the Jackson estate had approval over the use of his music, essentially granting it veto power over the film’s final cut. One argument that keeps surfacing on social media is that critics should judge Michael on its own terms rather than on what they think it should have been. “It seems like people wanted a movie [that] was never going to exist,” noted one X user. “So it was never going to be salacious or introspective”
Jackson’s fans argue the allegations shouldn’t eclipse his musical and artistic legacy, separating the artist from the work, while critics insist that a biopic should present a complete picture of Jackson, regardless of how unflattering that picture may be. As film critic Sean Burns characterized it on X, ending “with the release of Bad is like ending an OJ biopic with him winning the Heisman.” A good Michael Jackson movie, wrote the artist Harmony Holiday, “would be part tragedy, part farce,” calling attention to how the film lacks the real kind of interiority that made Jackson so polarizing.
“Watching it feels more like being frog-marched through a wax museum than watching a movie, each milestone restaged with an off-putting, uncanny-valley resemblance and no interiority,” critic Alison Willmore noted in Vulture.
Tech
California Engineer Identified in Suspected Shooting at White House Correspondents Dinner

A 31-year-old engineer and computer scientist was identified in media reports and President Donald Trump as the suspected shooter at the White House Correspondents Dinner on Saturday night.
Cole Tomas Allen, of Torrance, California, was apprehended following the firing of shots at the Washington Hilton, where Trump was scheduled to deliver remarks to a ballroom full of journalists, cabinet officials, and Hilton staff. Allen’s name surfaced in media reports shortly before Trump posted two photos of a suspect following his apprehension. The person in the photos Trump posted matches photos of Allen.
In dramatic scenes, several shots were heard outside the ballroom, after which Trump and Vice President JD Vance were immediately rushed off the stage by the United States Secret Service. In the immediate aftermath of the shooting incident, it briefly appeared as if the event would proceed—Trump posted “LET THE SHOW GO ON” on Truth Social—but the event was eventually shut down.
According to the Metropolitan Police Department, the suspect “charged” a Secret Service checkpoint at the Hilton hotel, and was intercepted by agents. MPD interim chief Jeffery Carroll said the suspect was carrying a “shotgun, handgun, and multiple knives.”
At a White House press conference following the shooting, Trump said one United States Secret Service agent was shot but saved from serious injury by his bulletproof vest. Trump said the agent, who was not named, is “doing great” and in “great shape.” No other injuries were immediately reported.
The suspect was later transported to a local hospital “to be evaluated,” according to Carroll, who said he appears to be a “lone actor.”
Around the time Trump’s press conference began on Saturday night, he posted a picture on his Truth Social account appearing to show the suspected shooter on the ground, with his hands restrained behind his back, and a foil warming blanket covering the lower half of his body.
A WIRED review of public databases shows a seemingly minimal online presence associated with Allen’s name. According to his LinkedIn profile, he graduated from Caltech in 2017 with a bachelor’s in mechanical engineering from California State University Dominguez Hills in 2025 with a master’s in computer science. A photo that appears to be of Allen appears on the Caltech site identifying him as a member of the school’s Mechanical Engineering 72 class, described by the school as a “two-term engineering design lab” for building robots and autonomous vehicles. His name is also listed in a 2025 Dominguez Hills graduation program. A search in a public facial recognition database returns only two images, both apparently of him as an undergraduate.
According to the shooter’s LinkedIn profile, he has been employed part-time since March 2020 at C2 Education, a private company that helps students prepare for the SAT and ACT exams. In December 2024, C2 Education said in posts on LinkedIn and Facebook that he was the company’s “December Teacher of the Month.”
Since 2018, the suspected shooter self-identified on his LinkedIn profile as a “self-employed” indie game developer. He appears to have released an “atomic fighting game” called Bohrdom on Steam in 2018. He advertised the game using accounts on YouTube and X that appeared to have little to no following. The caption for a trailer of the game describes it as a “non-violent, skill-based, asymmetrical fighting game loosely based on a chemistry model that is itself loosely based on reality.”
Relatives of Allen’s did not immediately respond to requests for comment. C2 Education and the Metropolitan Police Department also did not immediately respond to requests for comment.
Tech
The next Xbox could be waiting on the memory market


Sharma described the decision-making process as an equation, noting that memory costs influence multiple variables. She said Microsoft’s focus is on building a console capable of running great games – including PC titles – while accounting for market conditions that remain in flux.
Read Entire Article
Source link
Tech
Anthropic created a test marketplace for agent-on-agent commerce

In a recent experiment, Anthropic created a classified marketplace where AI agents represented both buyers and sellers, striking real deals for real goods and real money.
The company admitted this test — which it called Project Deal — was only “a pilot experiment with a self-selected participant pool” of 69 Anthropic employees who were given a budget of $100 (paid out via gift cards) to buy stuff from their coworkers.
Nonetheless, Anthropic said it was “struck by how well Project Deal worked,” with 186 deals made, totaling more than $4,000 in value.
The company said it actually ran four separate marketplaces with different models — one that was “real” (where everyone was represented by the company’s most-advanced model, and with deals actually honored after the experiment) and another three for study.
Apparently, when users are represented by more advanced models, they get “objectively better outcomes,” Anthropic said. But users didn’t seem to notice the disparity, raising the possibility of “‘agent quality’ gaps” where “people on the losing end might not realize they’re worse off.”
Also, the initial instructions given to the agents didn’t appear to affect sale likelihood or the negotiated prices.
Tech
Microsoft revamps Windows Insider Program with simpler structure and more user control

Microsoft is rolling out a major overhaul of its Windows Insider Program, aiming to simplify how early Windows features are tested while addressing long-standing user complaints around complexity and control. The update marks one of the biggest structural changes to the program in years, signaling a shift in how Microsoft wants to collaborate with its testing community.
A Simpler Insider Program Built Around Feedback And Control
The revamped program introduces a streamlined structure, reducing multiple Insider channels into two primary ones: Beta and Experimental. This replaces the earlier, more fragmented system that included Dev, Canary, and Release Preview channels, which often confused users about where they belonged.
Microsoft is also making it easier for users to move between channels or exit the program without needing a full system reset, thanks to in-place upgrade options.

Alongside structural changes, the company is rolling out new preview builds and features that focus heavily on usability. Early updates include improvements to Windows Update, such as the ability to pause updates, avoid forced restarts, and gain more control over when updates are installed.
This shift reflects direct feedback from users who have long complained about disruptive updates and lack of control.
Why This Overhaul Matters For Windows As A Platform
The Windows Insider Program is more than just a testing environment. It plays a critical role in shaping the future of Windows by allowing millions of users to test features before they reach the general public.
By simplifying the program, Microsoft is attempting to make feedback more meaningful and participation more accessible. The previous multi-channel system often led to fragmentation, with users unsure about stability levels or feature timelines.
The new approach suggests Microsoft is prioritizing clarity and efficiency over experimentation chaos. It also indicates a broader shift toward improving Windows 11’s overall quality, rather than rushing out features without sufficient refinement.
Why This Should Matter To You As A User
Even if you’re not a Windows Insider, these changes will likely affect your everyday experience. The Insider Program acts as a testing ground for features that eventually roll out to all users. Improvements in update control, system stability, and feature clarity will directly influence future Windows releases.

For enthusiasts and developers, the changes make it easier to participate in testing without dealing with confusing channel choices or risky upgrades. For regular users, it means the features you eventually receive are more likely to be polished and less disruptive.
In simple terms, a better Insider Program leads to a better Windows experience overall.
What Comes Next For Microsoft’s Insider Strategy
The rollout of the revamped program is happening in phases, with users gradually being moved into the new channel structure. Microsoft is expected to continue refining the experience, focusing on transparency, clearer communication, and stronger integration of user feedback into development decisions. There are also indications that future updates will place greater emphasis on performance, reliability, and user control rather than just adding new features.
This overhaul doesn’t introduce a new version of Windows, but it may be just as important. It reflects a recognition from Microsoft that building a better operating system starts with listening more effectively to the people who use it.
Tech
Credential management as a financial risk control


Author: Eirik Salmi, System Analyst at Passwork
When a threat actor walks into your network using a legitimate username and password, which control stops them?
For most financial institutions, the honest answer is: nothing catches it immediately. The attacker looks like an authorised user. They move laterally, escalate privileges, and map critical systems for an average of 186 days before the breach is even identified — and a further 55 days to contain it — according to IBM’s Cost of a Data Breach Report (2025).
By then, the operational damage is done, and the regulatory clock has already started.
On January 17, 2025, the Digital Operational Resilience Act (DORA) entered into application across the EU. Article 9 of the regulation makes credential security a binding financial risk control, with supervisory consequences for institutions that fall short.
The question is no longer whether your authentication posture meets best practice. It is whether it meets the law — and whether you can prove it.
This article traces the specific Article 9 requirements that govern credential management, explains why a compromised password is an operational resilience failure under DORA’s framework, and outlines the practical controls that close the gap.
The threat that DORA was built to counter
Stolen credentials are the single largest initial access vector in 2025, accounting for 22% of all data breaches, per Verizon’s Data Breach Investigations Report. For financial institutions, the sector-specific cost of that exposure averages $5.56 million per incident, according to IBM’s Cost of a Data Breach Report — down from $6.08 million in 2024, yet still the second-highest of any industry globally.
The supply side of credential theft has been fully industrialised. Initial Access Brokers sell verified corporate network access for an average of $2,700, with 71% of listings including privileged credentials — pre-packaged access that requires no technical skill to exploit, according to Rapid7 research.
Infostealers such as Lumma, RisePro, StealC, Vidar, and RedLine automate credential harvesting at scale. IBM X-Force data shows their delivery via phishing increased 84% year-on-year in 2024, with 2025 data pointing to an even steeper trajectory.
DORA’s Article 9 exists precisely to interrupt this chain. The regulation reflects a documented, ongoing threat to the operational continuity of European financial markets.
DORA Article 9 requires strong authentication, least-privilege access, and documented controls.
Passwork delivers all three — self-hosted, ISO 27001 certified, with full audit logs your compliance team can export on demand.
What DORA Article 9 actually requires
Article 9 of DORA — titled “Protection and Prevention” — sits within the ICT risk management framework mandated by Article 6. It sets out specific technical and procedural obligations that financial entities must implement.
Two provisions are directly relevant to credential management.
-
Article 9(4)(c) requires financial entities to “implement policies that limit the physical or logical access to information assets and ICT assets to what is required for legitimate and approved functions and activities only.” This is the least-privilege principle, stated as a legal obligation.
-
Article 9(4)(d) goes further, requiring entities to “implement policies and protocols for strong authentication mechanisms, based on relevant standards and dedicated control systems, and protection measures of cryptographic keys whereby data is encrypted based on results of approved data classification and ICT risk assessment processes.”
Unpacking that language in operational terms: MFA is mandatory. The reference to “relevant standards” points directly to FIDO2/WebAuthn — the most widely deployed authentication standard currently resistant to Adversary-in-the-Middle (AiTM) phishing kits, which can bypass SMS and TOTP-based MFA in real time. Cryptographic key management is a regulatory requirement.
Privileged access management (PAM) tools are not named explicitly in the regulation — but the controls they deliver map directly onto Article 9’s requirements. Session recording, just-in-time (JIT) access provisioning, and privileged credential vaulting are precisely the “dedicated control systems” the regulation describes.
Institutions that have not deployed these controls face a compliance gap that supervisors can act on.
The European Banking Authority (EBA) and ESMA’s Regulatory Technical Standards under DORA provide additional specificity on ICT risk management requirements, reinforcing the Article 9 baseline with sector-specific implementation guidance.
Credential compromise as an operational resilience failure
DORA’s stated purpose is to ensure financial entities can withstand, respond to, and recover from ICT disruptions. A credential compromise looks entirely different through that lens than it does through a security incident lens.
With an average dwell time of 186 days, a compromised credential does not produce a discrete security event. It produces a sustained, invisible threat to operational continuity — an attacker moving laterally, escalating privileges, and mapping critical systems while appearing as a legitimate user. It is a direct threat to the operational continuity DORA is designed to protect.
The breach of France’s national bank registry in January 2026 made the mechanics concrete. A threat actor obtained the credentials of a single civil servant with access to Ficoba — the interministerial database holding records on every bank account opened in France.
Using only that one account, the attacker accessed and extracted data on 1.2 million bank accounts, including IBANs, account holder names and addresses, and tax identification numbers.
The affected system was taken offline, operations at the registry were disrupted, and the incident was reported to France’s data protection authority, CNIL. The attack required no technical sophistication.
Under DORA, an incident of that scale at a financial entity would trigger mandatory reporting obligations under Article 19 — an initial notification within 4 hours of classification (and no later than 24 hours after detection), an intermediate report within 72 hours, and a final report within one month.
The third-party dimension: Vendor credentials are your credentials
DORA’s Chapter V places explicit obligations on financial entities regarding ICT third-party risk. The compliance perimeter does not stop at the institution’s own systems.
The Santander breach in May 2024 is the European reference point. Attackers used credentials stolen from employees of Snowflake to access a database containing customer and employee data across Spain, Chile, and Uruguay.
The credentials had been harvested months earlier by infostealer malware infecting contractor workstations. None of the compromised Snowflake accounts had multi-factor authentication enabled.
The entry point was not inside Santander. It was a vendor’s weak authentication posture — and it exposed data belonging to one of Europe’s largest banks without a single exploit being written.
Under DORA, a financial institution whose critical ICT provider suffers a credential-based breach faces direct regulatory exposure. Institutions must contractually require equivalent authentication standards from their vendors and audit compliance against those requirements.
A vendor’s password policy gap is not the vendor’s problem alone — it is the financial entity’s regulatory liability.
Building a DORA-compliant credential management
Meeting Article 9’s requirements demands a structured programme across four areas.
-
Deploy phishing-resistant MFA first. FIDO2/WebAuthn-based authentication — hardware security keys, passkeys, platform authenticators. SMS and TOTP-based one-time passwords are not adequate against current attack techniques. Enforce phishing-resistant MFA for all users, with particular rigour on privileged accounts and remote access paths.
-
Enforce least-privilege access. JIT provisioning — granting elevated access only for the duration of a specific task — eliminates the standing privileges that make credential theft so damaging. Deactivate accounts immediately on offboarding. Dormant accounts are among the most common and most avoidable attack vectors.
-
Vault all credentials. Service account passwords, API keys, and privileged credentials must be stored in an encrypted, access-controlled credential vault. Manual credential management at scale is operationally unworkable and produces no audit trail. A business password manager Passwork — deployed on-premise within the institution’s own infrastructure — provides the encrypted vaulting, granular access controls, and complete activity history that Article 9 demands.
-
Monitor continuously. Anomalous login behaviour — unusual geolocations, off-hours access, lateral movement patterns — must trigger automated alerts. Reducing that 186-day average dwell time is the single most effective lever for cutting both financial exposure and DORA incident reporting obligations.
All four controls depend on the same foundation: how credentials are stored, shared, accessed, and monitored. Without structure at that layer, even well-designed policies fail at execution.
How Passwork supports DORA compliance in practice
Passwork is a corporate password manager certified to ISO/IEC 27001 and available as a self-hosted deployment — meaning your credential data never leaves your own infrastructure.
For financial entities navigating DORA’s Chapter V supply chain obligations, that distinction matters: a third-party SaaS credential store introduces exactly the kind of ICT dependency the regulation requires you to govern.
For institutions working through the four controls above, Passwork addresses the credential management dimension of each.
-
MFA enforcement across the credential layer. Passwork supports biometric, passkey, and security key MFA natively, with SAML SSO and LDAP integration for enterprise environments.
-
Role-based access control and least privilege. Permissions are assigned at vault and folder level, inherited from AD or LDAP groups, and updated automatically on directory changes. Offboarding revokes access to shared credentials in a single operation — logged and timestamped, producing the evidence an investigator will request under Article 9(4)(c).
-
Privileged account inventory and secure sharing. Passwork provides a structured, searchable repository of all organisational credentials, including shared administrative accounts. Encrypted vault sharing replaces informal channels that leave no audit trail and cannot be revoked.
-
Audit logs for compliance documentation. Every credential access, permission change, password reset, and sharing event is recorded in a tamper-evident log, exportable for compliance reporting and integrable with SIEM systems. A structured activity history is a substantively stronger response to a regulator than a policy document alone.
DORA compliance is as much an evidence problem as a technical one. The institutions that navigate enforcement most effectively are those that can produce documentation on demand.
Act before the audit
DORA has converted credential management from a security best practice into a binding financial risk control. Articles 9(4)(c) and 9(4)(d) are explicit: least-privilege access, strong authentication, and cryptographic key protection are legal obligations for every financial entity operating in the EU.
Operational resilience begins with identity — and identity begins with controlling who holds the keys.
Audit your credential controls against Article 9, document the findings, and have the evidence ready before a regulator asks. Under DORA, the absence of documentation is itself a finding.
Passwork is designed for exactly this situation: a self-hosted password manager that keeps credential data inside your own infrastructure, enforces MFA across every access point, and generates the tamper-evident audit logs that turn a compliance conversation from a liability into a demonstration. ISO/IEC 27001 certified, with LDAP and SAML SSO integration for enterprise environments.
Start your free Passwork trial — full functionality, no limitations.
Sponsored and written by Passwork.
-

 Business7 days ago
Business7 days agoPowerball Result April 18, 2026: No Jackpot Winner in Powerball Draw: $75 Million Rolls Over
-

 Fashion1 day ago
Fashion1 day agoWeekend Open Thread – Corporette.com
-
 Politics7 days ago
Politics7 days agoZack Polanski demands ‘council homes not luxury flats for foreign investors’
-
Entertainment6 days ago
NBA Analyst Charles Barkley Chimes in on Ice Spice McDonald’s Fiasco
-
 Politics5 days ago
Politics5 days agoGary Stevenson delivers timely reminder to register to vote as deadline TODAY
-

 Crypto World5 days ago
Crypto World5 days agoBank of Hawai’i (BOH) Q1 2026: Net Income Drops to $57.4M as Net Interest Margin Expands
-

 Crypto World10 hours ago
Crypto World10 hours agoHyperliquid $HYPE Rally Builds Momentum as AI Sector Enters Prove-It Phase
-

 Politics3 days ago
Politics3 days agoMaking troops accountable for war crimes threatens US alliance, ex-SAS colonel warns
-

 Politics3 days ago
Politics3 days agoDisabled people challenge government SEND proposals over segregation concerns
-

 Business4 days ago
Business4 days agoRolls-Royce Voted UK’s Most Iconic Trade Mark as IPO Register Hits 150
-

 Politics3 days ago
Politics3 days agoZack Polanski responds to home secretary’s taser threat
-

 Politics3 days ago
Politics3 days agoStarmer handler McSweeney to be dragged from shadows by Foreign Affairs Committee
-
Politics3 days ago
Wings Over Scotland | How To Get Away With Crimes
-
Crypto World5 days ago
Five Value Stocks with Recovery Potential in 2026: PayPal (PYPL), Nike (NKE), and More
-

 Politics3 days ago
Politics3 days ago‘Iran is still a nuclear threat’
-

 Crypto World4 days ago
Crypto World4 days agoNew York sues Coinbase, Gemini over prediction market offerings
-

 Sports3 days ago
Sports3 days agoTim Bradley names the current best in the world: “Better than Inoue and Usyk”
-

 Politics7 days ago
Politics7 days agoReform investigating candidate who ‘hates’ the NHS
-

 Business4 days ago
Business4 days agoThe Job Benefits Most Men Don’t Know to Negotiate
-
 Crypto World2 days ago
Crypto World2 days agoMichael Saylor says BTC winter is over. Market analyst disagrees, says bitcoin was in a pullback










You must be logged in to post a comment Login