Crypto World
NSA Accesses Anthropic Model After Pentagon Blacklist

TLDR
- The NSA reportedly used Anthropic’s Mythos Preview despite a Pentagon supply chain risk designation.
- Axios cited sources who confirmed the NSA accessed the model after the restriction.
- The Pentagon labeled Anthropic a supply chain risk in March over safeguard disputes.
- The dispute involved Anthropic’s refusal to loosen controls tied to autonomous weapons and surveillance.
- Anthropic limited Mythos Preview access to about 40 organizations due to offensive cyber capabilities.
The National Security Agency has used Anthropic’s Mythos Preview despite a Pentagon supply chain risk designation. Axios cited multiple sources who confirmed the agency’s access to the model. The report shows internal differences across federal departments over Anthropic technology use.
Anthropic Model Access Expands Inside NSA
Axios reported that two sources confirmed NSA use of Mythos Preview. One source said the department expanded usage beyond limited internal testing.
However, the Pentagon designated Anthropic as a supply chain risk in March. The designation restricted the company’s technology in military contracts after a policy dispute.
The dispute centered on Anthropic’s refusal to loosen safeguards. The company declined to adjust controls linked to autonomous weapons and domestic surveillance systems.
As a result, the Pentagon limited procurement pathways for Anthropic products. Still, Axios reported that the NSA accessed Mythos through existing channels.
The report did not explain the technical route used for access. However, it confirmed that usage occurred after the risk designation.
Axios stated that it remains unclear how the NSA deployed the model. Yet, other authorized organizations have used Mythos to scan systems for vulnerabilities.
Anthropic limited Mythos Preview access to about 40 organizations. The company restricted access because of the model’s offensive cyber capabilities.
Sources told Axios that the NSA relied on the model’s security testing features. They did not describe operational outcomes or contract values.
The report did not state whether the NSA violated formal procurement rules. It also did not clarify if the usage involved classified systems.
White House Engages Anthropic Leadership
The White House has explored options to work with Anthropic despite the ongoing court dispute. Axios reported that discussions took place at senior levels.
Anthropic CEO Dario Amodei met White House Chief of Staff Susie Wiles. He also met Treasury Secretary Scott Bessent to discuss government usage.
Axios reported that Amodei addressed Mythos access and broader security practices. The outlet cited a source familiar with the meeting.
The meeting occurred while the court fight over the Pentagon designation continued. However, officials have not announced any policy change.
The White House did not publicly outline next steps. Still, the talks showed active engagement with Anthropic leadership.
Anthropic has defended its safeguards in previous statements. The company has said it maintains strict controls over high-risk applications.
Pentagon officials have not rescinded the supply chain risk designation. Therefore, formal contract limits remain in place.
Axios reported that agency-level adoption may differ from procurement policy. However, it did not provide internal compliance details.
Crypto World
DeFi Protocols Launch Joint Escape Hatch for Aave ETH Lenders and Loopers


Fluid’s aWETH Redemption Protocol, launched with Lido, Ether.fi, 1inch, 0x and Kyber, has processed $136M out of Aave’s frozen WETH pool in 48 hours.
The same architectural openness that turned a forged cross-chain message at Kelp DAO’s bridge into hundreds of millions of bad debt at Aave has in 48 hours produced its own antidote: A coalition of DeFi protocols has launched an emergency exit route.
Fluid, a DeFi DEX and lending protocol, has joined with other DeFi protocols to build a way for ETH depositors and loopers on Aave to swap their positions out of WETH, either exiting the protocol altogether or switching to a different collateral type, at a time when direct withdrawals are unavailable after the $290 million Kelp DAO exploit.
The aWETH Redemption Protocol has processed 58,510 aWETH, or approximately $136 million, out of Aave’s frozen WETH pool in its first 48 hours, according to the live Dune dashboard Fluid is publishing.
The protocol was built in under 24 hours in response to Aave’s ETH utilization hitting 100% after the April 18 exploit of Kelp DAO’s rsETH bridge adapter.
How it works
The infrastructure allows Aave ETH lenders to swap aWETH into wstETH or weETH collateral in a single transaction, at a discount of roughly 2.21% for a 1,000 aWETH swap, per 1inch co-founder Sergej Kunz. Early exits via secondary markets had been clearing near 23% below par.
Two user scenarios are supported: For lenders, aWETH converts to wstETH and weETH collateral. Users can then withdraw their assets. For borrowers, collateral switches from ETH to wstETH or weETH collateral. Debt remains unchanged and users can exit a previously stuck position or remain on Aave with yield-bearing collateral.
Lenders hand aWETH into Fluid’s Lite ETH Vault in exchange for wstETH or weETH. The vault then uses the incoming aWETH to repay part of its own WETH debt at Aave, extinguishing a liability without requiring WETH to leave Aave’s pool. The netting works because Fluid is the single largest user of the Aave WETH market, carrying approximately $1.5 billion in ETH debt against its looped Lite Vault positions.
Because Fluid already owes the debt being retired, the protocol is not taking on new directional risk. It is exchanging one claim on LST collateral for another, with the exiting lender absorbing a modest haircut and the vault reducing its borrowed exposure in a market where supply is otherwise trapped.
Lido Finance, Ether.fi, 0x Protocol, 1inch, and KyberNetwork are leveraging the protocol. Lido and Ether.fi contribute LST liquidity, 1inch shipped the front-end, and 0x and Kyber are routing orders. Aave’s DAO-recommended withdrawal guidance now directs trapped WETH suppliers toward the Fluid route.
“ETH utilization on Aave hit 100% and lenders had no exit. Fluid built the infrastructure in hours — with significant capacity to support ETH lenders at scale,” Fluid Founder and CTO Samyak Jain said in an announcement.
Kelp DAO exploit context
On April 18, an attacker exploited Kelp DAO’s LayerZero-based rsETH bridge adapter and minted 116,500 rsETH, approximately $293 million, or 18% of circulating supply, without a corresponding amount locked on the Ethereum side. The attacker supplied the unbacked rsETH as collateral on Aave V3 and V4 and borrowed approximately $236 million in WETH before markets were frozen.
Aave’s WETH utilization reached 100% within hours as lenders attempted to withdraw ahead of the bad-debt recognition, breaking the lending invariant that allows passive withdrawals. Variable borrow rates spiked into triple digits and aWETH began trading at a discount on secondary markets.
Aave’s risk team, in its April 20 incident report, modeled bad debt at between $123.7 million and $230.1 million depending on how claims on the under-collateralized rsETH L2 adapter are allocated.
Kelp DAO and LayerZero have continued to dispute responsibility. Kelp’s April 19 statement argued that the 1-of-1 DVN configuration used on the bridge was LayerZero’s documented default in its quickstart guide and was re-confirmed as appropriate by the LayerZero team during Kelp’s L2 expansion. LayerZero has attributed the exploit to the North Korea-linked Lazarus Group’s TraderTraitor subgroup and said it will no longer allow new OFT deployments to ship with 1-of-1 DVN configurations.
The composability dimension
The architectural property that allowed the exploit to cascade across Aave, Compound, Fluid and other venues is what allowed the redemption protocol to be assembled in under a day. aWETH is a standardized receipt token, wstETH and weETH are standardized LSTs, Aave’s “repaywithAtokens” function is public and permissionless, and aggregators can source liquidity from any venue. The Fluid flow combines those primitives without a governance vote, a treasury drawdown, or a new counterparty relationship.
The protocol does not reduce Aave’s modeled bad debt, reverse the attacker’s borrowing, or affect the LayerZero-Kelp dispute. It provides an individual exit for lenders who would otherwise wait for a socialization outcome or accept a steeper market discount.
Fluid said capacity is significant and additional partners are being engaged.
Crypto World
Casibom – 2026 Gncel Casino Giri Linki.871
casibom için güncel giriş linkini bulmayı arıyorsanız, bu sayfayı ziyaret edin. Casibom 158 giriş, casibon veya casibo gibi farklı isimlerle de bilinir. Casibom, güvenli ve hızlı bir şekilde giriş yapmanıza olanak sağlar.
Casibom giriş sayfasına giderek, güncel ve güvenli bir şekilde oyunlarına erişebilirsiniz. Cadibom veya casibom olarak da bilinen bu platform, kullanıcı dostu bir arayüze sahiptir. Casibom güncel giriş linki her zaman güncel ve güvenli bir şekilde sunulmaktadır.
Casibom giriş sayfasına erişmek için, internet bağlantınızın aktif olduğundan ve uygun bir tarayıcı kullanıldığından emin olun. Casibom güncel giriş linki her zaman güvenli ve hızlı bir şekilde kullanılabilir.
Casibom, 2026 yılı için güncel giriş linkini kullanarak, oyunlarınıza hızlı ve güvenli bir şekilde erişebilirsiniz. Casibom giriş sayfasına giderek, güncel ve güvenli bir şekilde oyunlarına erişebilirsiniz.
Casibom’da Oynayın – Güvenli ve Eğlenceli Deneyim
Casibom’da oynayın, çünkü bu güvenli ve eğlenceli bir deneyim sunar. Casibom giriş sayfasından kolayca erişebilirsiniz. 158 giriş numarasını kullanarak hemen oyunları deneyin. Casibo adı altında sunulan çeşitli oyunlar, her tür oyun sevgilileri için mükemmel bir seçenek olur. Casibom güncel giriş linkiyle her zaman güncel kalmak ve en iyi oyunları denemek için bu sayfayı takip edin. Casibom giriş sayfasından hemen giriş yapın ve casibon oyun dünyasına girebilirsiniz. Casıbom, güvenli bir ortamda oyun oynayabileceğiniz ve kazanabileceğiniz bir platformdur.
Casibom’da Oynanabilecek En İyi Oyunlar
Casibom’da oynanabilecek en iyi oyunlar arasında: slot oyunları, live dealer oyunları ve table oyunları bulunur. Slot oyunları arasında popüler olanlar arasında “Mega Moolah” ve “Starlight Princess” bulunur. Live dealer oyunları arasında “Live Roulette” ve “Live Blackjack” sayılabilir. Table oyunları arasında “Baccarat” ve “Poker” yer alır.
Slot Oyunları
Mega Moolah: bu slot oyunu, büyük jackpots ile bilinir. Her kırk sekiz kere oynandığında bir büyük jackpot rastele kazanılır. Oyunun grafikleri ve sesleri harika, oyun deneyimi çok güzeldir.
Starlight Princess: bu oyun, klasik slot oyunlarının en iyi örneklerinden biridir. 25 kuyruklu, 5×3 formatında oynanır ve harika grafiklerle bilinir. Jackpotlar oldukça büyük olabilir.
Live Dealer Oyunları
Live Roulette: canlı cüzzam oyunları, gerçek cüzzamçılarla oynanır. Oyunlar hızlı ve eğlenceli, aynı zamanda güvenli ve adildir. Live roulette, her zaman popülerdir ve her zaman oynanabilir.
Live Blackjack: bu oyun, canlı dealer ile oynanır ve oyunlar hızlı ve adildir. Blackjack, her zaman popüler bir oyun olup, her zaman oynanabilir.
Casibom’da oynanabilecek en iyi oyunları deneyin ve mutluluk bulun!
Casibom’da Güvenli ve Kolay Kayıt Adımları
Casibom’da kaydolmak için basit ve güvenli bir süreç izleyin. İlk adım, https://constitucion40.com/ giriş sayfasına gidin. Burada, kullanıcı adı ve e-posta adresi girerek veya sosyal medya hesaplarıyla hızlı bir şekilde giriş yapabilirsiniz. Kayıt sırasında, gerekli bilgileri doğru ve tam olarak doldurun. Bu, hesabınızın güvenliğini sağlayacaktır.
Kayıt tamamlandığında, hesabınızı doğrulamak için e-posta adresinize gönderilen doğrulama e-postasını kontrol edin. Bu adımdan sonra, Casibom’da tamamen giriş yapabilirsiniz. Güvenliğiniz için, hesabınıza erişim sağladığından emin olun ve şifrenizi düzenleyin.
Crypto World
Bybit Backs Malaysia’s Hata in $8M Series A Funding Round


Bybit has led an $8 million Series A funding round in Hata, a dual-licensed digital asset exchange operating in Malaysia. The round also included participation from global family offices and follows Bybit’s earlier investment in Hata’s $4.2 million seed round.
According to Monday’s announcement, the funding will be used to improve liquidity, expand the user base and develop additional digital asset products.
Hata operates under licenses from the Securities Commission Malaysia and the Labuan Financial Services Authority, allowing it to offer trading and custody services for digital assets in the Southeast Asian country.
Since launching in 2023, the company has reported more than 209,000 registered users and processed 1.04 billion Malaysian ringgits (about $225 million) in transaction volume in 2025.
Ben Zhou, co-founder and CEO, said Malaysia is “strategically important” and has “one of the most digitally engaged populations in Southeast Asia and strong long-term potential for digital asset adoption.”
Bybit is the world’s fifth largest cryptocurrency exchange by trading volume, according to data from CoinMarket.
Beyond the region, the exchange is also deepening its commitment to the Middle East. In March, Bybit appointed Derek Dai as the new country manager for the MENA region to oversee expansion and partnerships despite ongoing regional tensions.
Dai said the Middle East is emerging as a key crypto market, with Bybit planning to expand UAE dirham access and build partnerships with banks and payment providers in the coming months.
Related: Rwanda swats Bybit’s P2P platform offering franc-to-crypto trading
Malaysia builds out digital asset regulatory framework
The investment from Bybit comes as Malaysia has been developing its regulatory framework for digital assets through a series of initiatives and pilot programs.
In June, Malaysia launched its Digital Asset Innovation Hub as a regulatory sandbox, allowing fintech and digital asset firms to test use cases such as programmable payments, ringgit-backed stablecoins and supply chain financing under central bank oversight.
During the same month, a Malaysian telecom company owned by Crown Prince Ismail Ibrahim, son of Sultan Ibrahim Iskandar, launched a ringgit-backed stablecoin called RMJDT on the Zetrix blockchain under the sandbox framework.
In November, Bank Negara Malaysia outlined a three-year roadmap to explore asset tokenization, including pilots for tokenized deposits, stablecoins and cross-border settlement through its Digital Asset Innovation Hub. The central bank’s plan includes an industry working group co-led with the Securities Commission Malaysia to coordinate use cases and address regulatory and legal considerations.
More recently, the central bank said it is piloting three sandbox programs focused on ringgit-backed stablecoins and tokenized bank deposits for cross-border settlement, with participation from institutions including Standard Chartered, CIMB Group and Maybank.
Magazine: Bitcoin will not hit $1M by 2030, says veteran trader Peter Brandt
Crypto World
Last Week Tonight‘s John Oliver Says he Won‘t Placate Prediction Markets

John Oliver, host of HBO’s Last Week Tonight, targeted prediction market platforms on his show’s latest weekly deep dive.
In Sunday’s airing of the HBO show, Oliver discussed some of the trivial event contracts on platforms such as Kalshi and Polymarket, including betting whether members of the Trump administration would use certain words in public addresses, to the companies’ controversial partnering with news organizations.
Specifically, the host questioned Donald Trump Jr.’s relationship with both platforms — an adviser to Kalshi and Polymarket — and how the US Commodity Futures Trading Commission (CFTC) “doesn’t even seem to be trying” to block event contracts on terrorism, assassination and war under Chair Michael Selig.
For much of the show, Oliver discussed how it is “incredibly easy for individuals to manipulate the outcomes,” citing Coinbase CEO Brian Armstrong rattling off a list of crypto-related words in his third-quarter 2025 earnings call to cause many Kalshi and Polymarket users to win their bets.
“I’m going to make you a promise tonight,” said Oliver, echoing Armstrong’s statement. “I will never do anything because someone online placed a bet on it. So you can be confident that if I ever say Bitcoin, Ethereum, blockchain, staking and Web3, it won’t be because I’m trying to move markets — it will be because I’m having a stroke.”

While user activity and trading volume on prediction markets have increased exponentially in recent months — expected to reach $1 trillion by 2030 — the platforms’ controversial bets and legal status in US states have raised eyebrows for some experts. Gaming authorities in several states are suing companies like Kalshi over alleged illegal sports betting, with Coinbase chief legal officer Paul Grewal and others expecting the legal fight to end up before the US Supreme Court.
Related: Senate bill to target sports betting ban on prediction markets: WSJ
Financial giants looking to expand into prediction markets?
In addition to previously announced partnerships with media giants like CNN, CNBC, Fox News and Dow Jones, traditional financial companies including Charles Schwab and Citadel Securities recently signaled plans to consider prediction markets.
Charles Schwab CEO Rick Wurster said on a Thursday investors call that the company would “take a hard look at” prediction markets. In a separate event the same day, Citadel Securities President Jim Esposito said that the company was “absolutely keeping an eye on developments” as part of a potential move into the market.
Magazine: Adam Back says current demand is ‘almost’ enough to send Bitcoin to $1M
Crypto World
Zonder Cruks Online Casino Beoordeling van beschikbare spellen.147 (2)
Wanneer je op zoek bent naar een goksite zonder cruks, kan het lastig zijn om de juiste keuze te maken. Er zijn veel online casinos die zich richten op spelers uit Nederland, maar niet allemaal bieden ze de beste voorwaarden. In deze beoordeling zullen we de beschikbare spellen van Zonder Cruks Online Casino analyseren en beoordelen.
Zonder Cruks Online Casino is een populaire keuze onder gokkers uit Nederland, omdat het casino een brede verscheidenheid aan spellen aanbiedt. Van klassieke gokkasten tot complexere videospelletjes, er is iets voor iedereen. Het casino biedt ook een aantal exclusieve spellen die niet beschikbaar zijn op andere goksites.
Maar hoe zit het met de voorwaarden? Is Zonder Cruks Online Casino een goede keuze voor gokkers zonder cruks? In deze beoordeling zullen we de voorwaarden van het casino analyseren en beoordelen, van het aanbod aan spellen tot de bonusvoorwaarden en de veiligheid van het casino.
We zullen ook de voordelen en nadelen van het casino bespreken, zodat je een goede beslissing kunt nemen over het kiezen van Zonder Cruks Online Casino als jouw goksite zonder cruks. Lees verder om te ontdekken of Zonder Cruks Online Casino de beste keuze is voor jou.
Welke spellen zijn beschikbaar? Zonder Cruks Online Casino biedt een brede verscheidenheid aan spellen, waaronder:
Klassieke gokkasten, zoals Book of Ra en Starburst
Videospelletjes, zoals slots en videopoker
Live casino, met live dealers en live spellen
Progressieve jackpotspellen, zoals Mega Moolah en Hall of Gods
We zullen ook de bonusvoorwaarden van het casino bespreken, waaronder het no deposit bonus en de andere promoties die het casino aanbiedt.
Zonder Cruks Online Casino is een populaire keuze onder gokkers uit Nederland, omdat het casino een brede verscheidenheid aan spellen aanbiedt en een goede reputatie heeft op het gebied van veiligheid en betrouwbaarheid. Lees verder om te ontdekken of Zonder Cruks Online Casino de beste keuze is voor jou.
Welkom bij Zonder Cruks
Welkom bij Zonder Cruks, het online casino dat u een unieke ervaring biedt. Wij zijn gespecialiseerd in het bieden van goksites zonder cruks, zodat u kunt genieten van een veilige en verantwoorde gokervaring.
Onze goksites zonder cruks zijn ontworpen om u een maximale gokervaring te bieden, met een breed scala aan spellen en een veilige en betrouwbare omgeving. Wij bieden ook casino zonder cruks no deposit bonus, zodat u kunt genieten van een extraatje bij het spelen.
Wij zijn ook bekend als de beste online casino zonder cruks, omdat wij ons focussen op de behoeften van onze spelers. Wij bieden een breed scala aan spellen, van klassieke gokkasten tot moderne videospelletjes. Onze spelers kunnen ook genieten van online gokken zonder cruks, omdat wij ons focussen op de veiligheid en betrouwbaarheid van onze diensten.
Wij zijn ook gespecialiseerd in het bieden van casinos zonder cruks, zodat u kunt genieten van een veilige en verantwoorde gokervaring. Wij bieden ook goksite zonder cruks, zodat u kunt genieten van een breed scala aan spellen en een veilige en betrouwbare omgeving.
Wij zijn er om u te helpen bij het vinden van de beste casino zonder cruks, omdat wij ons focussen op de behoeften van onze spelers. Wij bieden een breed scala aan informatie over de beste online casino zonder cruks, zodat u kunt genieten van een veilige en verantwoorde gokervaring.
Wij zijn ook gespecialiseerd in het bieden van gokken zonder cruks, zodat u kunt genieten van een veilige en verantwoorde gokervaring. Wij bieden ook online gokken zonder cruks, zodat u kunt genieten van een breed scala aan spellen en een veilige en betrouwbare omgeving.
Wij zijn er om u te helpen bij het vinden van de beste casino zonder cruks, omdat wij ons focussen op de behoeften van onze spelers. Wij bieden een breed scala aan informatie over de beste online casino zonder cruks, zodat u kunt genieten van een veilige en verantwoorde gokervaring.
Spellen en Features
Als u op zoek bent naar een online casino waar u kunt gokken zonder cruks, dan bent u bij Zonder Cruks Online Casino aan het juiste adres. Dit casino biedt een brede verscheidenheid aan spellen, waaronder klassiekers als blackjack, roulette en poker, evenals moderne spellen zoals video slots en live casino games.
Wanneer u zich aanmeldt bij Zonder Cruks Online Casino, kunt u genieten van een no deposit bonus, waardoor u kunt beginnen met gokken zonder enig financieel risico. Dit is een unieke kans om te ervaren hoe het online gokken zonder cruks werkt.
Naast de brede verscheidenheid aan spellen, biedt Zonder Cruks Online Casino ook een aantal unieke features, waaronder:
Live Casino
Met het live casino kunt u live gokken met een echte dealer, waardoor u een echte casino-ervaring kunt ervaren vanuit uw eigen comfortzone.
Mobile App
De mobile app van Zonder Cruks Online Casino maakt het mogelijk om overal en wanneer u maar wilt te gokken, zonder enig beperking.
Wanneer u kiest voor Zonder Cruks Online Casino, kunt u rekenen op een veilig en betrouwbaar gokken-ervaring, met een goede klantenservice en een brede verscheidenheid aan betalingsmethoden.
Waarom kiezen voor Zonder Cruks Online Casino?
Er zijn vele redenen om voor Zonder Cruks Online Casino te kiezen, waaronder:
– Brede verscheidenheid aan spellen
– No deposit bonus
– Live casino
– Mobile app
– Veilige en betrouwbare gokken-ervaring
Zonder Cruks Online Casino is de perfecte keuze voor iedereen die op zoek is naar een online casino waar hij/zij kan gokken zonder cruks.
Veiligheid en Betrouwbaarheid
Wanneer het om veiligheid en betrouwbaarheid gaat, is het belangrijk om een goksites zonder cruks te kiezen. Een goksites zonder cruks is een online casino dat een goede reputatie heeft en waarbij de veiligheid en betrouwbaarheid van de spelers worden gewaarborgd.
Een goksites zonder cruks biedt meestal een veilige en betrouwbare omgeving voor spelers om te gokken. Dit betekent dat de website is beveiligd met een SSL-certificaat, dat de gegevens van de spelers worden beschermd en dat de website een goede reputatie heeft in de gokwereld.
Een goksites zonder cruks is ook een online casino dat een goede reputatie heeft en waarbij de veiligheid en betrouwbaarheid van de spelers worden gewaarborgd. Dit betekent dat de website een goede reputatie heeft in de gokwereld en dat de spelers kunnen vertrouwen op de veiligheid en betrouwbaarheid van de website.
Het is belangrijk om een goksites zonder cruks te kiezen, omdat dit betekent dat de website een goede reputatie heeft en waarbij de veiligheid en betrouwbaarheid van de spelers worden gewaarborgd. Dit betekent ook dat de website een goede reputatie heeft in de gokwereld en dat de spelers kunnen vertrouwen op de veiligheid en betrouwbaarheid van de website.
Een goksites zonder cruks is een online casino dat een goede reputatie heeft en waarbij de veiligheid en betrouwbaarheid van de spelers worden gewaarborgd. Dit betekent dat de website een goede reputatie heeft in de gokwereld en dat de spelers kunnen vertrouwen op de veiligheid en betrouwbaarheid van de website.
Het is belangrijk om een goksites zonder cruks te kiezen, omdat dit betekent dat de website een goede reputatie heeft en waarbij de veiligheid en betrouwbaarheid van de spelers worden gewaarborgd.
Crypto World
Bitcoin price eyes channel top as 4H MACD turns bearish

Bitcoin price is at $76,466 on April 20, pressing the upper boundary of a 4H ascending channel from the February lows while the MACD simultaneously prints a bearish crossover on the same timeframe, creating a directional tension that will define the nearterm trajectory heading into the FOMC meeting on April 28.
Summary
- Bitcoin price is at $76,466 on April 20, up 0.99% on the 4H session, pressing the upper trendline of a 4H ascending channel that has been intact since the February lows near $59,000.
- The 4H MACD (12,26,9) has printed a bearish crossover with the histogram at -51.11, the MACD line at 148.89 crossing below the signal at 200.00, flagging momentum deceleration precisely at the channel’s upper boundary.
- A confirmed 4H close above the channel upper boundary near $77,500 opens the CME gap at $77,540 as the immediate target; a rejection and close below the SMA 20 at $75,881 exposes the SMA 100 at $72,467 as the next support.
Bitcoin (BTC) price is at $76,466 on April 20, up 0.99% on the 4H session, as price reaches the upper trendline of the ascending channel that has framed the entire recovery from the February lows. The 4H MACD has simultaneously printed a bearish crossover, with the MACD line at 148.89 crossing below the signal at 200.00 and the histogram printing at -51.11. The four SMAs remain in a bullish stack below price: SMA 20 at $75,881, SMA 50 at $74,605, SMA 100 at $72,467, and SMA 200 at $70,552. The 4H volume of 3.1K BTC is modest, confirming neither a high conviction breakout nor a distribution event at this stage.
The ascending channel on the 4H chart connects the February lows near $59,000 with successive higher lows through March and early April, producing a clearly defined upper boundary now aligning near $77,500. The CME futures market closed at $77,540 on Friday before the weekend and reopened Monday at $74,600, creating an upside gap of approximately 3.8% that is acting as a nearterm technical magnet for institutional positioning.
The 4H ascending channel from the February lows is the dominant structural framework for Bitcoin’s current price action. Each prior touch of the upper boundary has been followed by a pullback toward the channel midpoint or the SMA ribbon, and the current test is the most significant since the channel formed. The 4H MACD bearish crossover at this level is the signal that most directly challenges the breakout case. When the MACD line crosses below the signal while price is at a key resistance, the technical convention is that momentum is shifting toward sellers before a breakout can be confirmed on a closing basis.

The histogram reading of -51.11 is modest relative to the 148.89 MACD and 200.00 signal readings, suggesting early-stage deceleration rather than deep bearish momentum. Early-stage crossovers at resistance levels that do not expand into deeply negative histograms have historically resolved with a retest of the resistance rather than a breakdown, provided the ascending channel structure holds on a closing basis below.
Analyst @ChmielDk, a trader with over 15 years of market experience who posted analysis on X, flagged $60,000 as a potential floor under a worst-case geopolitical deterioration scenario, while the CME gap at $77,540 represents the primary nearterm technical target that short covering and institutional buying could accelerate price toward if the sell wall is cleared.
Key Levels: Support, Resistance, and Price Targets
The SMA 20 at $75,881 is the first 4H support on a closing basis. A close below it removes the shortterm dynamic support and brings the SMA 50 at $74,605 into play, which aligns broadly with the ascending channel midpoint. A sustained close below $74,605 breaks the channel midrange and puts the lower boundary near $70,552 into focus, where the SMA 200 also sits.
On the upside, the channel upper boundary near $77,500 is the immediate resistance. A confirmed 4H close above it opens the CME gap at $77,540 as the first target, with $80,000 as the extended psychological objective. Per Coinglass data from April 17, a $450 million sell wall was identified between $75,900 and $76,300, and price is currently sitting directly on top of this cluster. Clearing it on volume is the precondition for a clean push to the channel upper boundary.
Invalidation of the bull case: a 4H close below $74,605 alongside continued expansion of the bearish MACD histogram.
On-Chain and Market Data Context
Bitcoin open interest stands at $57.15 billion per Coinglass, with 24-hour futures volume of $72.75 billion and $136.5 million in futures positions liquidated in the past 24 hours. The modest liquidation figure relative to total open interest indicates the current price has not triggered a cascade in either direction. Bitcoin funding rates on Binance have remained negative for approximately 46 days, meaning short positions have been paying long positions throughout the entire ascending channel advance. Persistently negative funding rates during an uptrend signal accumulated short-side positioning that becomes vulnerable to a squeeze if price clears the overhead sell wall.
Iran reimposed controls on the Strait of Hormuz over the weekend, effectively ending the two-week ceasefire and pushing Brent crude back above $100 per barrel. Bitcoin pulled back from Friday’s high of $78,000 as the macro risk environment reasserted itself at the weekend open. The FOMC meeting on April 28 and 29 is the next scheduled catalyst, with CME FedWatch showing a 98% probability of a rate hold. Until either the geopolitical situation de-escalates or the Fed changes course, Bitcoin’s nearterm ceiling is likely to be defined by the interplay between the ascending channel upper boundary and the accumulated short positioning sitting directly overhead.
If Bitcoin closes a 4H candle above $77,500 with expanding volume, the CME gap at $77,540 is the immediate target and $80,000 the extended objective. A failure to clear $76,300 on the current session and a reversal below $75,881 shifts the focus back to the channel midpoint at the SMA 50 near $74,605.
Crypto World
NVIDIA Mirrors Bitcoin Setup as Trump’s Tariff Refunds Hit

NVIDIA Corporation (NVDA) stock price tests $201.75 resistance after a near 23% rally from its March 30 low at $164.04. NVDA trades at $199.24, down 1.21%, inside a bull flag handle that mirrors Bitcoin’s structure.
A US Supreme Court ruling on tariffs unlocks cost relief for NVIDIA’s import chain. And the next 1.5% of price action decides whether the 23% pole projection activates.
NVIDIA Stock Runs Bitcoin’s Playbook at Matched Volatility
NVIDIA volatility, measured as the 30-day rolling annualized reading, sits at 27.7%. Bitcoin (BTC) prints 27.8% on the same screen. The gap is 10 basis points.
The S&P 500 reads 14.9%, NASDAQ-100 18.4%, Apple 18.4%, and Microsoft 24.6%. NVDA trades roughly 1.5 times its parent index and closely matches a crypto asset. Only MicroStrategy (52.8%), Meta (42.8%), and Tesla (39.9%) print hotter volatility.
The identity does not stop at volatility. Bitcoin bottomed on March 29 at $64,869, per today’s BTC analysis. NVDA bottomed on March 30 at $164.04, one session apart.
Want more insights like this? Sign up for Editor Harsh Notariya’s Daily Newsletter here.
Bitcoin rallied 20.72% to an April 17 peak of $78,380. NVDA rallied 22.95% to $201.75 in the same window. Both assets now trade inside near-identical bull flag pattern handles below resistance.
Bitcoin’s measured move projects $90,841, a 21% extension. NVDA’s measured move projects $248, a 23% extension. The geometry is near-symmetric.
One difference sharpens the read. Bitcoin’s handle shows two rejections at the upper trendline and a long upper wick on April 20. NVDA’s handle shows the opposite footprint, with pullback volume visibly thinner than the seven green candles that built the pole.
Two assets at matched volatility, bottomed together, peaked together, facing the same measured-move math, printing the same pattern. This is not a correlation. The same money is possibly buying both.
The volatility alignment explains the rally size. The next question is whether institutions are actually paying to stay long inside the handle.
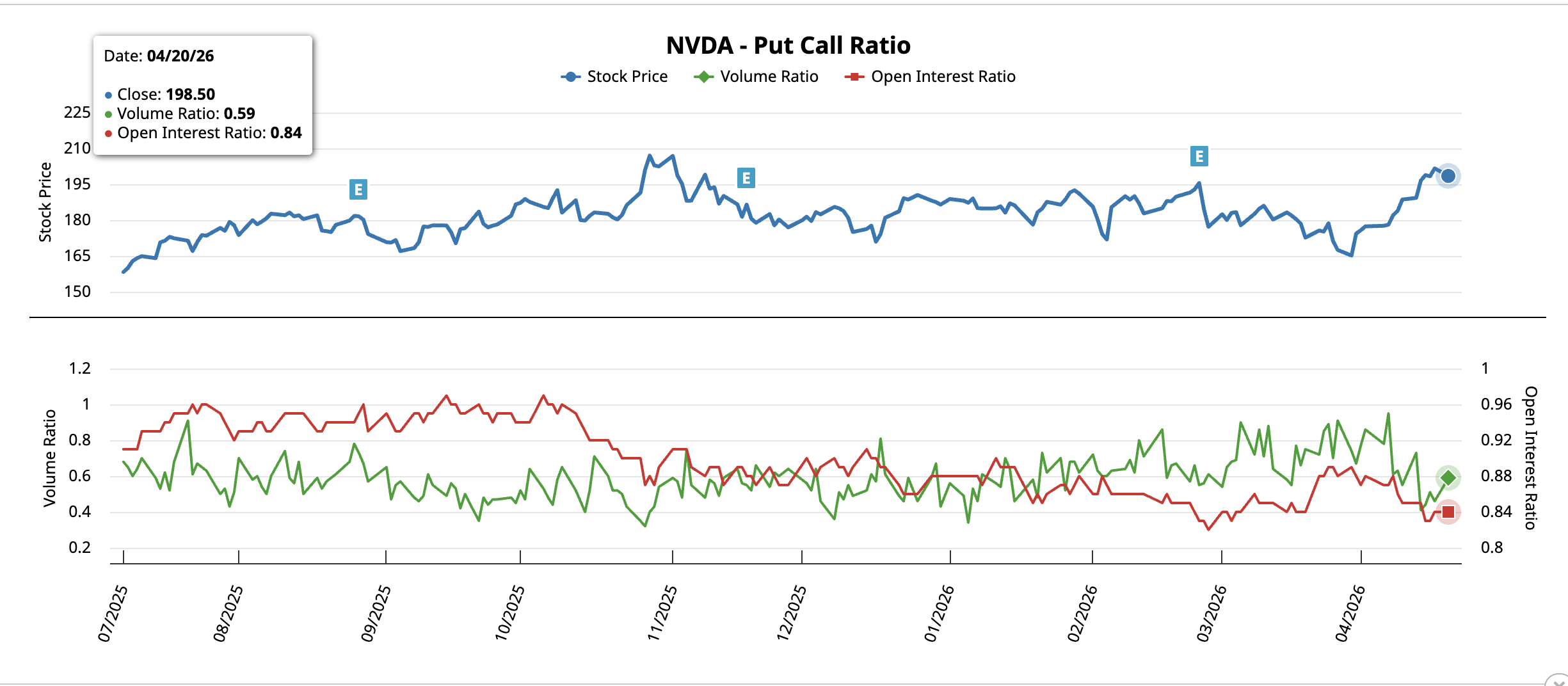
Put-Call Ratio Drops as Tariff Refund Clears Tail Risk
The bull flag needs a demand catalyst inside the handle, and the options tape is already supplying one. NVIDIA’s put-call ratio compares bearish put activity to bullish call activity. The reading has moved lower on both measurement methods since the March 30 pole base.
On March 30, when NVDA bottomed at $164.04, the volume-based ratio read 0.74. The open-interest-based ratio read 0.89. Both sat near the upper end of the post-October 2025 range, reflecting thick downside hedging at the low.
NVDA now trades at $199.24. The volume ratio has fallen to 0.59, and the open interest ratio sits at 0.84. That is a 20% compression in volume and a 6% compression in open interest. Both point in the same direction. Puts (bearish bets) are being closed faster than calls (bullish bets). That is the counterintuitive signal. Hedging usually rises as prices approach resistance. Here it is falling.
Options desks are not buying insurance against the $201.75 rejection.
The catalyst explaining the unwind landed today. The Supreme Court ruled Trump’s reciprocal tariff policy unlawful. The US government has begun refunding up to $166 billion to 330,000 importers across 53 million shipments. Refunds plus interest are scheduled within 60 to 90 days.
NVIDIA’s hardware stack depends on imported components across the global semiconductor supply chain. The tariff rollback reduces forward cost pressure on the AI infrastructure build-out. More importantly, the ruling retires a specific tail risk that had sat on the options curve through 2025. That is the exact risk the puts were pricing, now being dismantled.
Downside protection is cleared with a real catalyst under the tape. The NVIDIA price chart becomes the final decider of how far the bull flag can travel.
NVIDIA Stock Needs $201.75 Close to Activate $250 Target
The NVDA price action has the final call. The pole stalled at $201.75, which is not arbitrary resistance. That zone marks the 0.618 Fibonacci level while plotting the previous swing.
Capital flow confirms the pole was real. Chaikin Money Flow (CMF), a proxy for institutional buying and selling pressure, currently reads 0.21.
CMF traveled from roughly -0.25 at the March low to above zero in mid-April. The indicator then pushed into positive territory as the rally extended. That sequence confirms that real money was rotated in while the pole was being built.
This is why the Bitcoin volatility match is not a statistical coincidence. The same institutional pools are bidding on NVIDIA stock the way they rotate into Bitcoin. Synchronized March bottoms, parallel 21-23% poles, matched 27.7% and 27.8% volatility, and CMF inflows together describe one liquidity regime.
A daily close above $201.75 activates the 23% pole projection, which adds roughly $46 to the breakout trigger. The extension at $253.82 aligns with horizontal resistance at $248.25, suggesting $250 as the average target.

Intermediate checkpoints sit at $211.70 and $227.79. Bull flags in high-volatility regimes can meaningfully widen their handles before resolving. A dip into the $191 zone does not automatically invalidate the pattern. Only a daily close below $185.67 would significantly weaken the structure.
This NVDA price prediction now depends on one level. $201.75 separates the $250 path for NVIDIA stock from a $185.67 retest that would weaken the bull flag.
The post NVIDIA Mirrors Bitcoin Setup as Trump’s Tariff Refunds Hit appeared first on BeInCrypto.
Crypto World
Ripple Charts 2028 Path to Quantum-Resistant XRPL Security

Key Highlights
- Ripple establishes 2028 deadline for complete XRPL quantum-resistant transition
- Four-phase strategic plan addresses evolving quantum computing challenges
- XRPL’s native architecture provides unique advantages for cryptographic migration
- Initiative responds to Google Quantum AI research on blockchain vulnerabilities
- Structured upgrade approach balances security enhancement with network efficiency
Ripple has unveiled a comprehensive strategy to protect the XRP Ledger from quantum computing threats through a phased implementation plan. The initiative aims to achieve complete post-quantum security by 2028 without compromising transaction speed or network efficiency. This strategic response comes amid growing concerns about quantum technology’s potential impact on blockchain cryptography.
Google Research Accelerates Security Timeline
New studies from quantum computing experts reveal significant vulnerabilities in current cryptographic frameworks used throughout the blockchain industry. Ripple has responded by fast-tracking its quantum defense preparations for XRPL. The research underscores particular risks to digital signatures, transaction integrity, and long-term asset security.
Experts have identified a critical “harvest now, decrypt later” vulnerability affecting publicly accessible blockchain information. Malicious actors can capture encrypted data in the present and wait for quantum technology advancement to break encryption. Consequently, Ripple emphasizes proactive measures to protect both current and future ledger operations.
While existing security protocols remain effective against today’s threats, Ripple acknowledges the necessity of forward-looking defense strategies. The company stresses that timely preparation and systematic implementation will keep XRPL secure as quantum technology matures.
Built-In Features Enable Seamless Upgrade
The XRPL platform possesses inherent capabilities that facilitate cryptographic transitions more efficiently than competing blockchain systems. Notably, integrated key rotation functionality enables users to refresh security credentials without transferring assets. Consequently, Ripple can orchestrate smooth migrations while preserving existing account infrastructure.
XRPL’s seed-based key generation system supports deterministic cryptographic management throughout transition periods. This mechanism ensures secure credential creation during security upgrades. Ripple can deploy enhancements while preserving user autonomy and operational stability.
Competing platforms often lack integrated migration capabilities and necessitate complicated asset relocation processes. Ripple’s architectural design provides distinct advantages when implementing post-quantum security measures. These foundational elements create an optimal framework for advanced security deployments.
Staged Implementation Ensures Smooth Transition
Ripple has developed a comprehensive four-stage implementation framework to shepherd XRPL toward quantum resistance. The initial stage prioritizes contingency protocols for addressing potential cryptographic vulnerabilities. This foundation enables secure fund migration during unforeseen security challenges.
Ripple plans extensive testing of quantum-resistant cryptographic methods and performance impact analysis. Increased signature sizes and computational requirements demand thorough evaluation. Therefore, Ripple maintains ongoing experimentation to optimize the security-performance balance.
Subsequent implementation stages will introduce quantum-resistant signatures parallel to existing systems on development networks. This methodology allows thorough performance assessment without risking production environment stability. Ripple targets seamless full deployment by 2028 with minimal operational impact.
Ripple further emphasizes cryptographic flexibility through support for multiple internationally recognized algorithms. This adaptability ensures XRPL can evolve alongside emerging global cryptographic standards. Ripple strategically positions the network for sustained security amid shifting technological landscapes.
Ripple coordinates its strategic vision with worldwide progress in quantum computing and cryptographic science. The implementation roadmap demonstrates both technical readiness and collaborative ecosystem planning. This methodical strategy seeks to fortify XRPL while maintaining transaction velocity and system dependability.
Crypto World
Grayscale Replaces Coinbase with Anchorage for HYPE ETF Custody Services

Key Highlights
- Anchorage Digital Bank named as new custodian for Grayscale HYPE ETF
- Coinbase removed from custody role in amended filing
- Strategic custody diversification by Grayscale for HYPE ETF product
- Anchorage selection reinforces institutional-grade infrastructure
- Custody transition reflects evolving crypto ETF market dynamics
Grayscale Investments has updated its HYPE ETF application, transferring custodial responsibilities to a different service provider. The amended documentation names Anchorage Digital Bank as the new custodian, replacing Coinbase in this critical operational role. This modification represents a tactical repositioning as Grayscale continues developing its HYPE ETF product amid shifting regulatory frameworks.
Anchorage Digital Bank Assumes Custodial Responsibilities
The latest amendment to Grayscale’s HYPE ETF filing establishes Anchorage Digital Bank as the designated custodian. In the original submission, Coinbase performed both prime brokerage and custodial duties for the proposed fund. The revised documentation eliminates Coinbase from these combined functions.
Anchorage holds the distinction of being America’s first federally chartered digital asset bank. Consequently, appointing Anchorage enhances the institutional credibility underlying the HYPE ETF custody arrangement. The financial institution has broadened its offerings to encompass stablecoins, wealth advisory services, and comprehensive token management.
Grayscale previously engaged Anchorage as a backup custodian for its Bitcoin and Ethereum investment vehicles. Conversely, Coinbase continues serving as the main custodian for those established products. This custody transition underscores a wider diversification approach connected to the HYPE ETF launch.
Competitive Landscape and Infrastructure Considerations
Coinbase Custody Trust Company presently safeguards the majority of American spot bitcoin exchange-traded products. In contrast, Fidelity Digital Assets provides custody exclusively for its proprietary bitcoin offering. The HYPE ETF custody modification by Grayscale represents an uncommon shift in this established ecosystem.
The revised submission continues listing The Bank of New York Mellon in its transfer agent capacity. Thus, the foundational operations of the HYPE ETF stay unchanged notwithstanding the custody transition. The product also retains its dependence on CoinDesk benchmark pricing information.
Grayscale submitted its original HYPE ETF application in March alongside comparable submissions from industry competitors. Organizations including 21Shares and Bitwise had earlier pursued similar investment vehicles. As a result, competitive pressures continue influencing the HYPE ETF regulatory approval process.
Hyperliquid Platform Expansion Fuels HYPE ETF Demand
Hyperliquid currently ranks as the dominant onchain perpetual futures decentralized trading platform according to current market metrics. Nevertheless, regulatory barriers continue preventing direct platform participation for American traders. Notwithstanding these constraints, the HYPE ETF seeks to deliver indirect investment exposure to the underlying protocol.
Hyperliquid witnessed substantial expansion throughout 2025, amplifying interest in associated financial instruments. The HYPE ETF exemplifies growing institutional appetite for derivatives-oriented blockchain ecosystems. The fund architecture incorporates optional staking features, subject to regulatory authorization.
Grayscale maintains momentum in expanding its investment product portfolio under enhanced regulatory transparency. The asset manager has introduced additional fund proposals tied to cryptocurrencies including BNB and Zcash. The HYPE ETF constitutes one component of an extensive initiative to broaden digital asset investment options.
Crypto World
BTC bounces above $76,000 as DeFi suffers $14 billion exodus after major hack
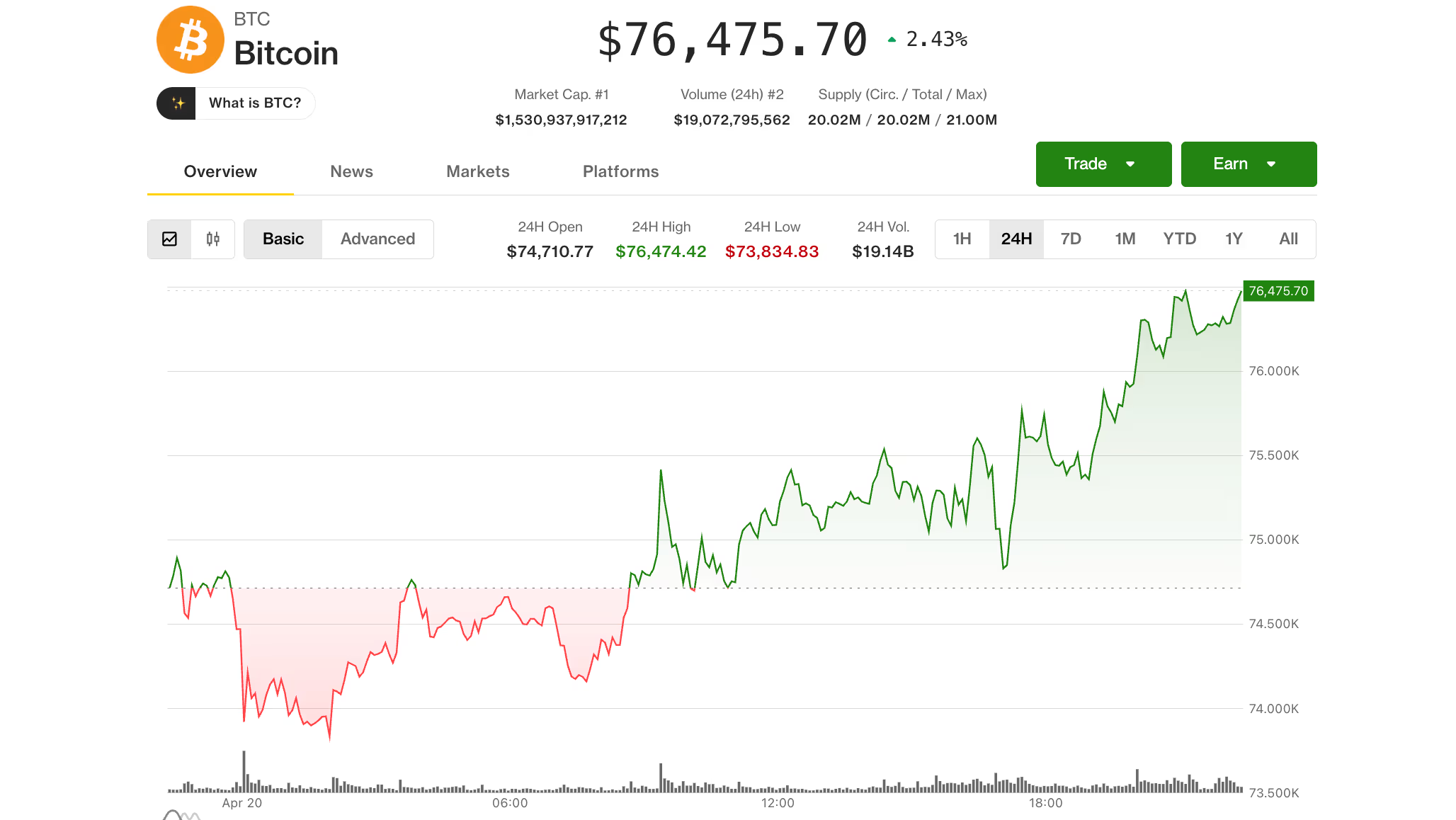
Bitcoin held above $76,000 on Monday, rebounding from overnight lows as the broader crypto market remained steady despite Iran war risks.
The largest cryptocurrency climbed about 2.4% over the past 24 hours, recovering from a dip below $74,000 earlier in the session. Ether (ETH), XRP, Solana (SOL) and other major altcoins also mirrored bitcoin’s move, as the broad-market CoinDesk 20 rose 1.7%.

That resilience comes against a shaky macro backdrop. U.S. President Donald Trump said Sunday that American forces had fired on and seized an Iranian-flagged cargo ship, warning of further escalation while Tehran refuses to strike a deal. A fragile ceasefire is set to expire later this week.
Oil prices jumped 6% to near $90, while the S&P 500 and Nasdaq slipped modestly, down around 0.3%-0.4%.
Crypto equities were mixed. Coinbase (COIN) and bitcoin treasury firm Strategy (MSTR) gained roughly 2%, while Circle (CRCL) and ether treasury Bitmine (BMNR) edged lower by 1%-2%.
“The fact that prices have not fully retraced despite new tensions suggests some genuine demand,” said Jasper De Maere, trader at Wintermute, pointing to recent spot ETF inflows as a supporting factor. Unlike earlier rallies this year, he said, the current move appears less driven by leverage.
That said, the path forward remains tied to geopolitics. A renewed ceasefire could push bitcoin back toward $80,000, while further escalation may keep markets under pressure.
For now, capital continues to concentrate in large-cap assets like bitcoin, De Maere noted, with riskier altcoins lagging, a pattern typical of market environments driven by macro headlines.
DeFi reels from $292 million KelpDAO hack
Elsewhere from the current price action, tensions are still high in the DeFi sector following the biggest crypto exploit of the year.
The $292 million KelpDAO hack cascaded across the market, as a vulnerability allowed the attacker to drain funds that were then used as collateral across lending protocols.
Because those assets were widely integrated into DeFi, the impact quickly spread, with users rushing to withdraw funds amid fears of bad debt and contagion.
Total value locked (TVL) across DeFi protocols fell by $14 billion over the past two days, according to DefiLlama data, even as asset prices remained steady.

DeFi TVL dropped to about $85 billion, its lowest level in a year and roughly 50% below October peaks. Aave, the largest lending protocol that was central in the exploit, saw around $10 billion in deposits withdrawn.
“There’s a tremendous risk-reward imbalance in DeFi,” David Shuttleworth from Anchorage Digital’s protocol team said. “Users will no longer accept the slightly higher (and sometimes lower) than risk-free rate they get by depositing in lending pools,” especially given the latest wave of exploits across protocols.
Read more: ‘DeFi is dead’: crypto community scrambles after this year’s biggest hack exposes contagion risk
-

 NewsBeat7 days ago
NewsBeat7 days agoTrump and Pope Leo: Behind their disagreement over Iran war
-

 Fashion3 days ago
Fashion3 days agoWeekend Open Thread: Theodora Dress
-

 News Videos6 days ago
News Videos6 days agoSecure crypto trading starts with an FIU-registered
-

 Sports4 days ago
Sports4 days agoNWFL Suspends Two Players Over Post-Match Clash in Ado-Ekiti
-
 Crypto World7 days ago
Crypto World7 days agoSEC Proposes Certain Crypto Interfaces Don’t Need to Register as Brokers
-

 Business1 day ago
Business1 day agoPowerball Result April 18, 2026: No Jackpot Winner in Powerball Draw: $75 Million Rolls Over
-

 Crypto World3 days ago
Crypto World3 days agoRussia Pushes Bill to Criminalize Unregistered Crypto Services
-
 Politics3 hours ago
Politics3 hours agoGary Stevenson delivers timely reminder to register to vote as deadline TODAY
-

 Politics3 days ago
Politics3 days agoPalestine barred from entering Canada for FIFA Congress
-

 Business4 days ago
Business4 days agoCreo Medical agree sale of its manufacturing operation
-
 Politics2 days ago
Politics2 days agoZack Polanski demands ‘council homes not luxury flats for foreign investors’
-

 Entertainment7 days ago
Entertainment7 days agoBrand New Day’ Footage Reveals the Devastating Impact of ‘Now Way Home’
-

 Crypto World3 days ago
Crypto World3 days agoRussia Introduces Bill To Criminalize Unregistered Crypto Services
-

 Tech2 days ago
Tech2 days agoAuto Enthusiast Scores Running Tesla Model 3 for Two Grand and Turns It Into Bare-Bones Go-Kart
-

 Tech6 days ago
Tech6 days agoMicrosoft adds Windows protections for malicious Remote Desktop files
-

 Tech5 days ago
Tech5 days ago‘Avatar: Aang, The Last Airbender’ Leaked Online. Some Fans Say Paramount Deserves the Fallout
-

 Entertainment7 days ago
Entertainment7 days agoKarol G’s ‘Ultra Raunchy’ Coachella Set Gave ‘Satanic Vibes’
-
 Tech7 days ago
Tech7 days agoWhat was the first ransomware attack to demand payment in Bitcoin?
-

 Sports6 days ago
Sports6 days agoYounger Than Sachin Tendulkar: Vaibhav Sooryavanshi Set To Make Historic India Debut
-
 Entertainment6 days ago
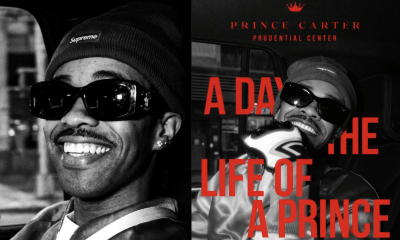
Entertainment6 days agoPrince Carter Brings Fans Front Row and Backstage at Boys 4 Life Tour












You must be logged in to post a comment Login