Tech
Where Are Gerber Knives Made & Who Owns The Company?

The Gerber company name is very well-known in the United States, but for two very different reasons, which can be confusing to some. You may know it as the long-standing company that’s been turning out food for infants and young children since 1927. The other company — with the exact same spelling — has been in existence since 1939, so almost as long. It manufactures a veritable smorgasbord of knives, multi-tools, camping equipment, and cutting tools (think axes, machetes, saws, etc.).
Despite both companies taking the same last name from their respective founders, Gerber Legendary Knives, which outshines Swiss Army Knives, in both price and features has no business relationship or corporate connection to the baby food maker. Joe Gerber turned his Portland, Oregon, ad agency into a kitchen knife company. He brought his sons, Pete and Ham, into the fold and grew the company into an international outdoor brand.
In 1987, Fiskars Group (based in Finland) purchased the then privately owned Gerber, and still owns it today. Fiskars, which specializes in a host of outdoor products and consumer goods, has been around since 1649. Despite overseas ownership, Gerber’s headquarters still resides in Portland, Oregon, where it all started. While Gerber makes the majority of their knives in Portland, certain products and models are made overseas in China.
Most of Gerber’s premium products are made in the USA
Way back in 1939, long before Gerber knives became legendary, Joe and Pete decided to send a handful of kitchen cutlery sets to some of their advertising clients as Christmas presents, so they collaborated with local blacksmith David Murphy to make them. The knives turned out to be so good that New York City outfitters Abercrombie & Fitch — who at the time were quite famous for their massive catalog of specialized hunting and fishing gear – decided to include them in their catalog.
Fiskars Group is one of the oldest companies in Finland and has an interesting story all its own. They also make a product that virtually everyone though they may not be familiar with its origins. Fiskars was founded in 1649, after Peter Thorwöste was granted permission to set up a shop in Fiskars, Finland, to craft cast iron and forged products. At the time, Finland was still under Swedish rule and one of Europe’s biggest iron suppliers. Jumping ahead some three hundred years to 1967, it produced its very first pair of now world-famous orange plastic handled scissors. Today, Fiskars is an amalgamation of lifestyle brands, including Waterford, Royal Copenhagen, Wedgwood, and others, available in over 100 countries.
Gerber manufactures many of its premium, military-grade, hunting, and survival gear (including a multi-tool that’s cheaper and better than a Leatherman) in Portland, Oregon. However, entry-level and mid-range models come from contract factories in China, enabling them to sell products at competitive prices overseas. A line of products was once sold under the “Gerber International” label (made in Taiwan), but that’s no longer the case.
Tech
Today’s NYT Connections: Sports Edition Hints, Answers for May 17 #601

Looking for the most recent regular Connections answers? Click here for today’s Connections hints, as well as our daily answers and hints for The New York Times Mini Crossword, Wordle and Strands puzzles.
Today’s Connections: Sports Edition is a tough one, though as a Minnesota pro football fan I appreciated the yellow group. If you’re struggling with the puzzle but still want to solve it, read on for hints and the answers.
Connections: Sports Edition is published by The Athletic, the subscription-based sports journalism site owned by The Times. It doesn’t appear in the NYT Games app, but it does in The Athletic’s own app. Or you can play it for free online.
Read more: NYT Connections: Sports Edition Puzzle Comes Out of Beta
Hints for today’s Connections: Sports Edition groups
Here are four hints for the groupings in today’s Connections: Sports Edition puzzle, ranked from the easiest yellow group to the tough (and sometimes bizarre) purple group.
Yellow group hint: Skol!
Green group hint: College division.
Blue group hint: Same first name.
Purple group hint: Think hat.
Answers for today’s Connections: Sports Edition groups
Yellow group: An NFC North athlete.
Green group: An ACC athlete.
Blue group: Ja(y)lens in the NBA.
Purple group: ____ cap.
Read more: Wordle Cheat Sheet: Here Are the Most Popular Letters Used in English Words
What are today’s Connections: Sports Edition answers?
The completed NYT Connections: Sports Edition puzzle for May 17, 2026.
The yellow words in today’s Connections
The theme is an NFC North athlete. The four answers are Bear, Lion, Packer and Viking.
The green words in today’s Connections
The theme is an ACC athlete. The four answers are Cavalier, Eagle, Hokie and Mustang.
The blue words in today’s Connections
The theme is Ja(y)lens in the NBA. The four answers are Brown, Brunson, Duren and Green.
The purple words in today’s Connections
The theme is ____ cap. The four answers are baseball, guardian, rally and salary.
Tech
Modder Builds All-in-One PS5 Portable with a Laptop Form Factor


Japanese modder TERA set out to solve a problem that had bothered him for years. He wanted a PlayStation 5 that could go anywhere without sacrificing the full experience players expect from the console at home. His latest creation delivers exactly that in a form that slides easily into most laptop bags.
Months passed since TERA finished a much larger portable version of this device based on the same hardware. That machine, weighing nearly five kilograms, had a battery life of less than an hour, but it had to have an oversized screen, which made it a pain in the neck to carry around and store, but they learned a lot from that effort, and all of those lessons were applied to this new project.
PlayStation®5 console – 1TB
- PlayStation 5 Console – 1TB, includes wireless controller, 1TBSSD, Disc Drive, 2 Horizontal Stand Feet, HDMI cable, AC power cord, USB cable, printed…
- 1TB of Storage, keep your favorite games ready and waiting for you to jump in and play
- Ultra-High Speed SSD, maximize you play sessions with near instant load times for installed PS5 games
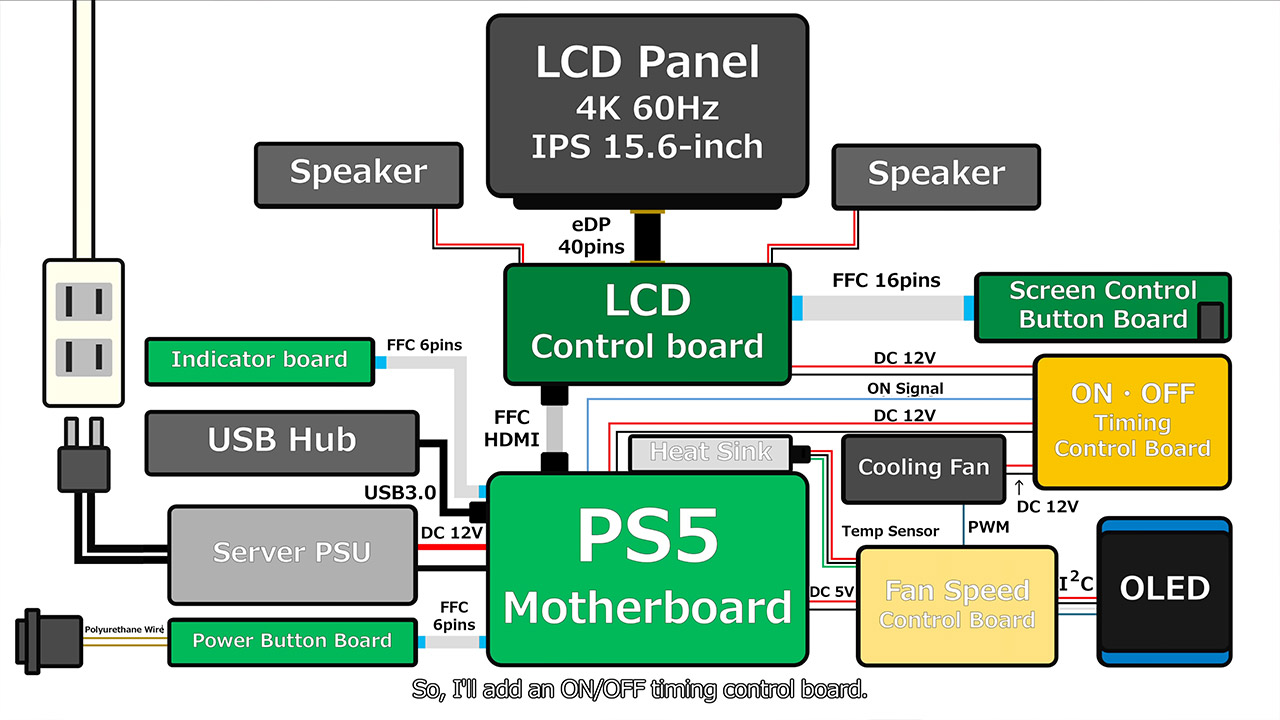
To get began, they disassembled an old PlayStation 5 that they purchased for only 22,000 yen. TERA took out the motherboard and flung the remainder of the components into a corner. This specific board was roughly two-thirds the size of the one used in the prior generation, which was significant since it gave them a lot more room to play with in terms of packing.
Now, heat management was a top priority because the main processor has a poor tendency of drawing nearly 200 watts when it’s under load. Early testing with the regular CPU cooling revealed that it could not last more than a few minutes before temperature warnings appeared. TERA opted to employ a vapor-chamber heatsink, which is commonly used in server equipment and can withstand high temperatures. He printed a mount for it and then added some heat pipes and aluminum bars to assist move heat away from the surrounding chips, as well as some liquid metal compound to the processor after applying a protective coating to prevent the surrounding electronics from shorts.
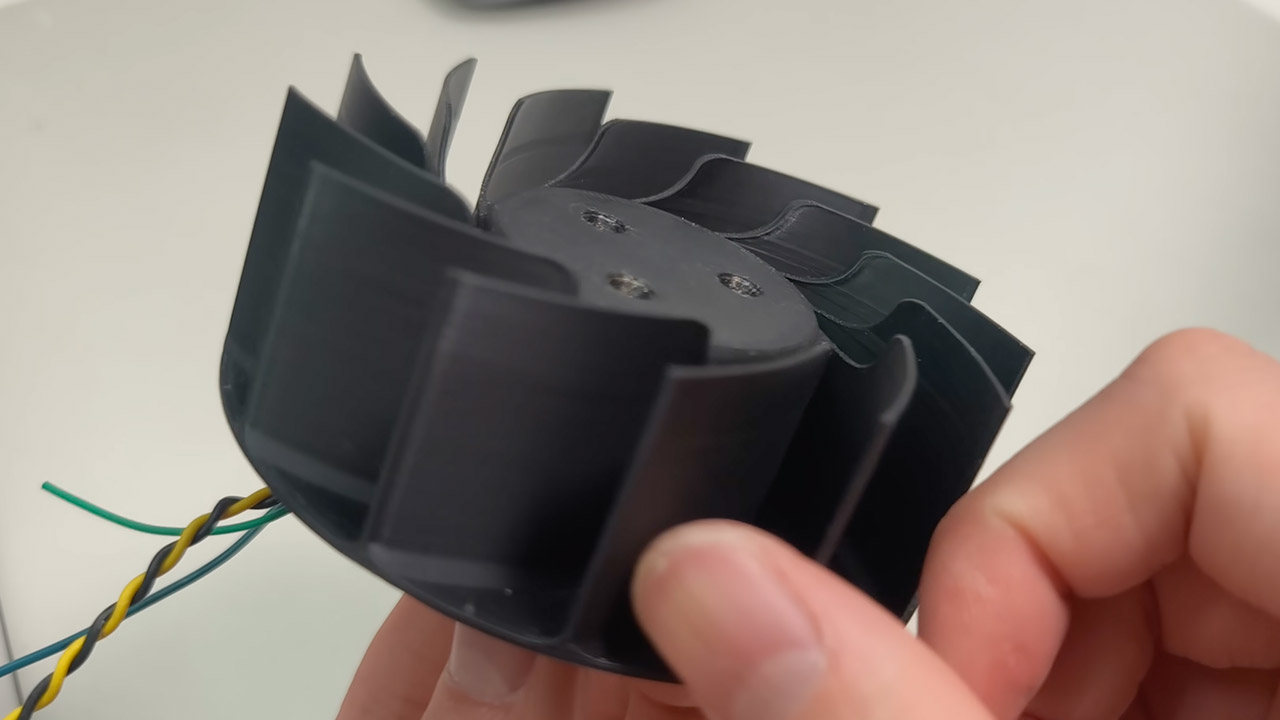
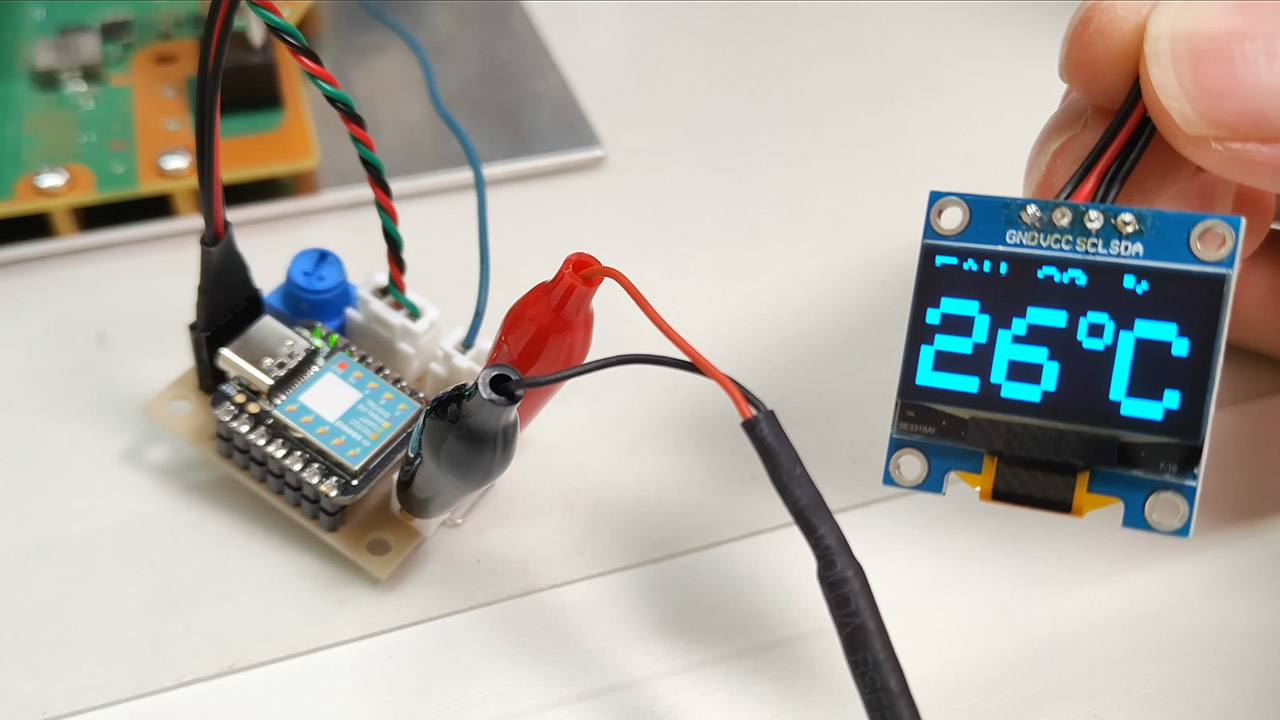
Then there was fan design, which was as significant. TERA simply took an off-the-shelf fan, cut its blades down to size, and printed a new housing and brand new blades to match the heatsink exactly. Then he added a temperature sensor, which sent data to a small circuit that adjusted the fan speed on the fly. They also added a display to the finished unit, which shows the temperature and fan speed at a glance.
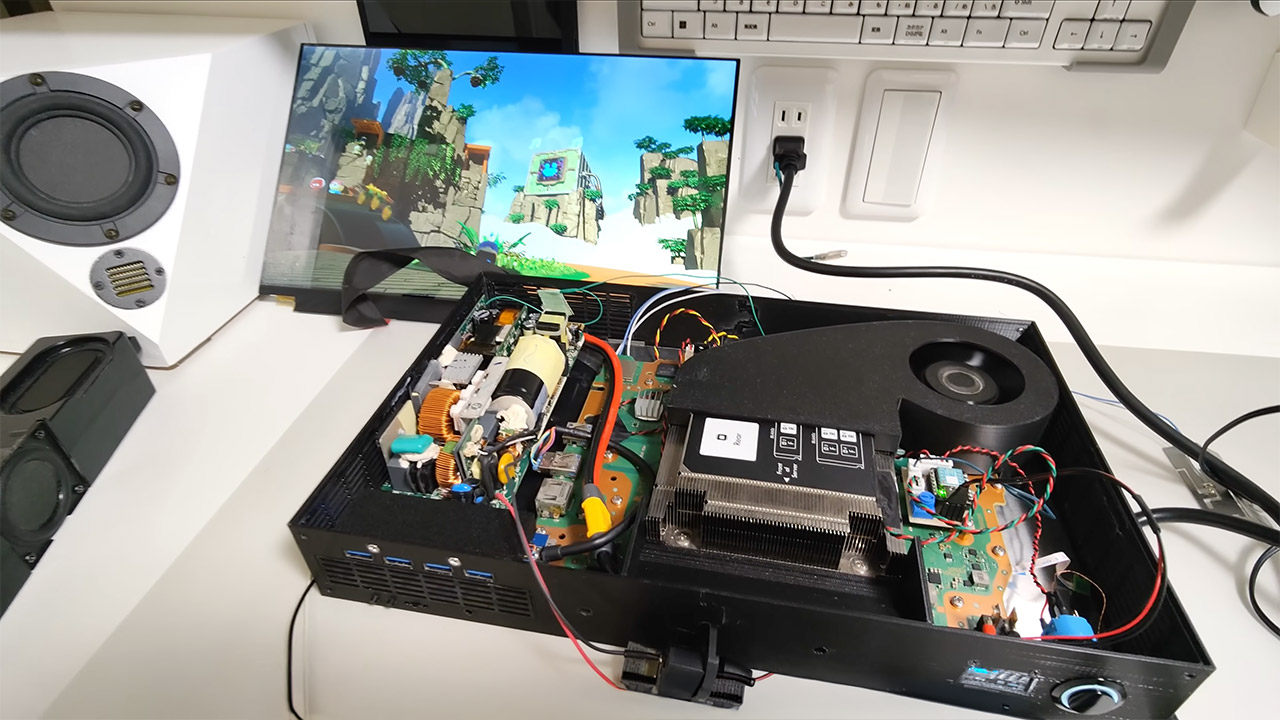
The next step was power delivery, so they inserted a modified server power supply unit within the casing to avoid having to deal with a large, bulky external brick. They also installed some bespoke timing boards to ensure that the screen and fan did not draw any power unless you hit the power button. Finally, they added a tiny copper plate that connected to ground to eliminate the video noise that appeared during the initial tests.

This was built with a 15.6-inch Sharp LCD panel, which is a smaller display than the one used in the last design, but its glossy surface keeps the colors vibrant and helps them shave off some of the weight and thickness. They printed off several plastic elements for the outside shell, including ventilation slits on the sides and a metal handle for hauling. They then used double-sided tape to secure the screen and precise spacers to keep the back panel in place.

As for battery life, it’s still a work in progress. In other testing with a compact RC car battery pack attached directly, they were able to get the unit to run a PlayStation 4 game for roughly 30 minutes. Of course, the power-hungry PS5 titles don’t last as long, but the architecture allows for a detachable battery pack in future editions.
Tech
Europe built sovereign clouds to escape US control. Then forgot about the processors


FEATURE Can digital sovereignty exist on American silicon?
Europe is pouring more than €2 billion into sovereign cloud initiatives designed to reduce exposure to US legal reach. The EU’s IPCEI-CIS program funds infrastructure development. France qualifies operators under SecNumCloud, a framework with nearly 1,200 technical requirements promising “immunity from extraterritorial laws.”
But most datacenters and qualified cloud operators still rely heavily on Intel or AMD processors. And inside those processors sits a computer beneath the computer: management engines operating at Ring -3, below the operating system, outside the control of host security software, persistent even when the machine appears powered off. Under the US Reforming Intelligence and Securing America Act (RISAA) 2024, hardware manufacturers count as “electronic communications service providers” subject to secret government orders.
Europe’s frameworks certify the clouds. They don’t assess the silicon.
The computer your OS can’t see
That computer beneath the computer has a name. On Intel processors, it is the Management Engine (ME), or more precisely the Converged Security and Management Engine (CSME). On AMD, it is the Platform Security Processor (PSP). Both run at what security researchers call Ring -3, below the operating system, below the hypervisor, in a privilege level the host cannot see or log.
“It’s a computer inside your computer,” explains John Goodacre, Professor of Computer Architectures and former director of the UK’s £200 million Digital Security by Design program. He is clear about what that means in practice. The ME has its own memory, its own clock, and its own network stack, and because it can share the host’s MAC and IP addresses, any traffic it generates is indistinguishable from the host’s own traffic to the firewall.
The architecture is not theoretical. Embedded in the Platform Controller Hub, the CSME is a separate microcontroller that operates independently of the host, with direct memory, device access, and network connectivity the host operating system cannot monitor. AMD’s PSP works the same way.
Intel’s Active Management Technology (AMT), the remote management feature the ME enables, exposes at least TCP ports 16992, 16993, 16994, and 16995 on provisioned devices. Goodacre notes that an attack surface exists on unprovisioned hardware too. These ports deliver keyboard-video-mouse redirection, storage redirection, Serial-over-LAN, and power control to administrators managing fleets of devices remotely. The capability has legitimate uses. It also provides a channel that operates at a level below what European sovereignty frameworks can attest.
Microsoft documented in 2017 that the PLATINUM nation state actor used Intel’s Serial-over-LAN (SOL) as a covert exfiltration channel. SOL traffic transits the Management Engine and the NIC sideband path, delivered to the ME before the host TCP/IP stack runs. The host firewall and endpoint detection saw nothing, and any security tooling running on the compromised machine itself was equally blind. PLATINUM did not exploit a vulnerability. It exploited a feature, requiring only that AMT be enabled and credentials obtained. In documented cases, those credentials were the factory default: admin, with no password set.
Goodacre catalogues this and related scenarios in a 37-page risk assessment prepared for CISOs evaluating Intel vPro hardware connected to corporate networks. Its conclusion is blunt: connecting an untouched-ME device to corporate resources “exposes the organization to a class of compromise that defeats the host security stack in its entirety.”
The ME does not stop when the machine appears to. Users recognize the symptom: a laptop powered off and stored for weeks is found, on next boot, to have a depleted battery. On modern thin and light platforms, what Microsoft documents as Modern Standby means “off” does not correspond to “all subsystems unpowered.” The system-on-chip components the Management Engine runs on remain in low-power states, drawing enough to drain a 55 Wh battery over weeks, on the order of 100-200 mW continuous draw.
The implication is documented in Goodacre’s risk assessment: “Whether the radio is in a Wake-on-Wireless-LAN listening state is firmware policy. On a device whose firmware has been tampered with during transit through the supply chain, the answer cannot be inferred from the visible power state.” A laptop that appears off, in a bag, can associate with a hostile network the user has no knowledge of.
Professor Aurélien Francillon, a security researcher at French engineering school EURECOM, has spent years studying exactly this class of problem. Working with colleagues, he built a fully functional backdoor in hard disk drive firmware [PDF], a proof of concept demonstrating how storage devices could silently exfiltrate data through covert channels. Three months after presenting it at an academic conference, the Snowden disclosures revealed the NSA’s ANT catalogue, which documented an identical capability already deployed in the field.
“The NSA were already doing it,” Francillon says flatly. “Quite amazing.” That background informs his assessment of the ME. “Yes, it can probably be used as a backdoor, like many other things, including BMC [baseboard management controller] and many other firmwares,” he says. The question, he argues, is not whether the backdoor exists but whether operational controls make it unreachable in practice.
AMD faces the same architectural question. On April 14, 2026, researchers demonstrated the Fabricked attack against AMD’s SEV-SNP confidential computing technology, achieving a 100 percent success rate with a software-only exploit. The Platform Security Processor proved vulnerable to the same class of compromise.
On server hardware, the picture is the same. Intel ME runs on servers under a different name, Server Platform Services or SPS, and the BMC, the remote administration controller standard in datacenter hardware, relies on it. “More or less the same,” Francillon says of the server variant. For datacenter operators, he sharpens the focus further: “If I look at cloud systems, servers, I would be more concerned with the BMC,” pointing to published research demonstrating remote exploitation of BMC vulnerabilities that could allow an attacker to reinstall or fully compromise a server. The BMC is not a separate concern from the ME: on server hardware, it is the primary network entry point into the SPS, making it both the most exposed interface and the most consequential.
Both Intel and AMD processors contain management engines that operate below the operating system. The silicon is designed by American companies and subject to American legal process.
The backdoor the CLOUD Act doesn’t use
That legal process has teeth that most European policymakers underestimate. The CLOUD Act, passed in 2018, gave US authorities extraterritorial reach to data held by American companies. FISA Section 702 allows intelligence agencies to compel US persons and companies to provide access to communications. Both are well known in European sovereignty discussions. They operate through the front door: a legal order served on a company that controls data. Less well known is RISAA 2024, a law that opens a different entrance entirely.
RISAA amended FISA’s definition of “electronic communications service provider” in ways that go beyond cloud operators and platform companies, and beyond the bilateral agreements that European policymakers have built their legal defenses around. Hardware manufacturers now fall within scope. Intel and AMD can be compelled, via secret orders with gag clauses, to cooperate with US intelligence access.
The mechanism through which that access could be exercised is the management engine: a persistent, privileged, network-connected runtime that operates below anything the host operating system can see or block. A SecNumCloud-certified operator can be legally isolated from American data demands. The processor inside its servers cannot. “You’ve actually got a policy mechanism by which any such machine anywhere can deliver any of its information,” Goodacre says.
RISAA’s two-year term expired on April 20, 2026, but Congress extended it by 45 days while debating reforms. Whether it is renewed, amended or allowed to lapse, the architecture it targets does not change.
SecNumCloud’s blind spot
France’s SecNumCloud is Europe’s most rigorous attempt to build a cloud certification that is legally immune to American law. It did not emerge from nowhere. ANSSI, France’s national cybersecurity agency, was established in 2009 as part of a broader effort to build institutional muscle on digital sovereignty long before the term became fashionable. When Edward Snowden revealed the scale of NSA surveillance in 2013, France’s response was technical rather than rhetorical: ANSSI published the first SecNumCloud framework in July 2014. A decade later, that framework has grown to nearly 1,200 technical requirements.
At the time, SecNumCloud was a cybersecurity qualification, not a sovereignty instrument: it set requirements for architecture, encryption standards, access controls, and incident response, but said nothing about who controlled the underlying infrastructure or whose laws applied to it. The CLOUD Act changed that. Passed in 2018, it gave American authorities extraterritorial reach to data held by US companies, and suddenly a French cybersecurity framework had a geopolitical dimension it was not designed for. Version 3.2, introduced in 2022, added Chapter 19: a set of explicit requirements targeting extraterritorial law, mandating that only EU operators could run the service, that no non-EU party could access customer data, and that the provider could operate autonomously without external intervention. It promised “immunity from extraterritorial laws.”
In December 2025, S3NS, a joint venture between French defense and technology group Thales and Google Cloud, operating Google Cloud Platform technology under French control, became the first “hybrid” cloud to receive SecNumCloud qualification. The certification triggered heated debate: was this real sovereignty, or American technology with a European flag?
But the debate missed a more fundamental question. Does SecNumCloud’s certification reach as far as the silicon it runs on? Francillon is positioned to see both sides of that question. He sits on the French Technology Academy’s working group on cloud security, a body that advises on the technical foundations of frameworks like SecNumCloud. And he has spent years studying firmware backdoors in academic literature and demonstrated them in practice.
He knows what the hardware can do, and he knows what the certification requires. His starting point is that SecNumCloud provides genuinely valuable protection, and that the silicon gap does not negate that. When asked whether SecNumCloud explicitly addresses Intel Management Engine or AMD Platform Security Processor vulnerabilities, his answer is unambiguous: “There is no direct requirement for firmware backdoor prevention.”
The framework is not designed to be a technical specification for hardware-layer security. “The document aims to be generic and not dive into technical details,” Francillon says. “Most of it is organizational security.” What SecNumCloud does require is that providers build a proper threat model, consider mitigation mechanisms, and monitor administration gateways where external tech support could be exploited. The hardware layer was not addressed by oversight. It was left out by design.
Francillon’s assessment is not a fringe view. Vincent Strubel, the director of ANSSI, the very agency that designed and administers SecNumCloud, is equally explicit about what the framework does and does not cover. In a January 2026 LinkedIn post addressing SecNumCloud’s scope, he writes that all cloud offerings, hybrid or not, depend on electronic components whose design and updates are not 100 percent controlled in Europe. If Europe were ever cut off from American or Chinese technology, he argues, the result would be a global problem of security degradation, not just in hybrid clouds, but everywhere.
Strubel frames SecNumCloud carefully: it is “a cybersecurity tool, not an industrial policy tool.” It protects against extraterritorial law enforcement and kill-switch scenarios. It was never designed to eliminate technology dependencies at the hardware layer, and no actor, state, or enterprise fully controls the entire cloud technology stack anyway.
One technology frequently cited in sovereignty discussions is OpenTitan, Google’s open source secure element deployed on its server hardware and used within the S3NS infrastructure. Francillon is clear about what it is and, critically, what it is not. “OpenTitan is a secure element, a small chip on the side that can be used for protecting sensitive keys, providing signatures, making attestations,” he explains. “It’s a bit like a TPM.” What it is not is a replacement for the main processor. “The Linux and all your applications will not run on it.” OpenTitan sits alongside x86 infrastructure as an external root of trust, independent of the ME. That matters because the default embedded TPM lives inside the ME, making it subject to the ME attack surface. OpenTitan sits outside that boundary. The two address different problems entirely, and conflating them, as sovereignty advocates sometimes do, obscures where the residual exposure actually lies.
ANSSI’s own technical position paper [PDF] on confidential computing, published in October 2025, concludes that Intel SGX, TDX, and AMD SEV-SNP are “not sufficient on their own to secure an entire system, or to meet the sovereignty requirements of SecNumCloud 3.2.” Physical attackers are “explicitly out-of-scope” of vendor security targets. Supply chain attackers are “explicitly out-of-scope.” The ME attack surface discussed in this article falls into neither category: it is a remote network threat, not a physical one. The paper’s conclusion for users concerned about hostile cloud providers is stark: “Switch to a cloud provider they trust, or use their own hardware with physical security protection measures.”
The castle with a structural flaw
Francillon does not dispute that SecNumCloud leaves the ME unassessed. His argument is that this does not matter in practice. “What I mean is that if there is a backdoor to access a room, it cannot be directly used if the room is in a castle. You have to pass the castle walls first.” Network isolation, monitoring, and threat modeling are the walls. SecNumCloud’s operational requirements mandate that administration gateways be isolated, that external tech support be monitored, that network segmentation prevents lateral movement. The Management Engine backdoor may exist, but the framework makes it unreachable except in what Francillon calls “very high-end attacks.”
That qualifier matters. Francillon is not claiming perfect security. He is claiming that proper operational controls reduce the threat to a level where only nation state actors with significant resources could exploit it. For most threat models, he argues, that is sufficient. “Saying it is useless to do SecNumCloud because there is ME, or whatever backdoor in some hardware we don’t control, is a mistake,” he says. SecNumCloud improves security over deployments without such controls, he argues, provided that hardware is carefully evaluated and firmware securely configured.
The castle walls have a structural flaw that Goodacre’s risk assessment documents in detail. Corporate perimeter firewalls see the device’s traffic, but because the ME shares the host’s MAC and IP addresses, they cannot tell ME-originated flows apart from legitimate host traffic. “The perimeter cannot attribute a flow to host-versus-CSME origin without out-of-band knowledge,” Goodacre writes. A TLS-encrypted tunnel from the ME to an attacker server on port 443 looks, to the perimeter, like any other HTTPS connection the laptop makes. Network filtering reduces attack surface. It does not eliminate the exposure.
Goodacre’s position is that a “Tier-3 supply-chain residual remains in both cases and is the irreducible cost of buying any silicon that ships with a Ring -3 manageability engine.” He defines Tier 3 as nation state cyber services operating at the level of compromising firmware in transit, mis-issuing CA certificates via in-country authorities, and modifying hardware at customs or courier hubs. The NSA’s Tailored Access Operations division treated supply chain interdiction as routine business, with explicit doctrinal preference for BIOS and firmware implants over disk-level malware.
His risk assessment’s data on fleet vulnerability is concrete. Industry telemetry from Eclypsium, analyzing production enterprise environments, found that approximately 72 percent of devices observed remained vulnerable to INTEL-SA-00391 years after public disclosure, and 61 percent remained vulnerable to INTEL-SA-00295. The same reporting documented that the Conti ransomware group developed proof-of-concept Intel ME exploit code with the intent of installing highly persistent firmware-resident implants.
“Connecting an untouched-ME vPro laptop to corporate resources exposes the organization to a class of compromise that defeats the host security stack in its entirety,” Goodacre concludes. “The exposed controls include BitLocker full-disk encryption, FIDO2-protected sign-in, endpoint detection and response, the host firewall and the corporate VPN.”
The disagreement between Francillon and Goodacre is not about whether the vulnerability exists. Both confirm it does. Both confirm AMD faces the same issue. Both confirm software alone cannot fix it. The disagreement is about whether operational controls, Francillon’s castle walls, make an architectural backdoor irrelevant in practice, or merely reduce its exploitability while leaving nation state actors with a path through.
For SecNumCloud operators processing sensitive government or commercial data, the distinction is not academic. It is worth noting that SecNumCloud is designed for a higher level of security than standard cloud certifications, but is not intended for classified or restricted government data. The threat that can still slip through Francillon’s castle walls is precisely the threat SecNumCloud was designed to keep out.
The gap nobody names
Goodacre told The Register he tested awareness of the Management Engine with various attendees at the CyberUK conference in April 2026. “Almost no one” knew about it, he reports. The gap between the sovereignty rhetoric and the silicon reality is not being surfaced in policy discussions, procurement decisions, or public debate over what digital sovereignty means.
The debate that does happen, hybrid versus non-hybrid, Google/Thales versus pure European providers, focuses on operational control and legal structure. It does not address the shared silicon foundation. Strubel’s LinkedIn post pushes back against the framing: “Imagining this problem is limited to hybrid cloud offerings is pure fantasy that doesn’t survive confrontation with facts.” Every cloud provider, hybrid or not, depends on components they don’t fully control. The distinction isn’t hybrid versus sovereign. It is what you’re protecting against, and whether the controls you’re implementing address that threat.
There is no immediate solution. RISC-V, the open source processor architecture European sovereignty advocates point to as a long-term alternative, remains years from competitive performance in datacenter workloads. “It will take decades,” Francillon says flatly. Arm is a cautionary precedent: it took nearly 20 years from the first server attempts before Arm achieved any meaningful datacenter presence.
Can sovereignty exist on compromised silicon?
For Goodacre, the bottom line is simple: the Tier-3 supply chain residual is “the irreducible cost of buying silicon with a Ring -3 manageability engine.” Francillon argues that operational controls, including network isolation, monitoring, and threat modeling make the backdoor unreachable except in very high-end attacks. Strubel acknowledges hardware dependencies are real but maintains that SecNumCloud provides valuable protection for what it does cover: legal control, kill-switch resistance, defense against cyberattacks and insider threats.
The disagreement is not about technical facts. It is about risk tolerance and threat model calibration. For European CIOs choosing SecNumCloud-certified providers, the question to ask vendors is: how do you address Intel Management Engine and AMD Platform Security Processor in your threat model? The answer will clarify whether the vendor treats the hardware layer as out of scope, or has implemented controls that reduce but do not eliminate the exposure.
For European policymakers, the question is broader. Can digital sovereignty exist on non-sovereign silicon? The current frameworks do not answer that question. They certify operational controls, legal structure, and autonomous execution capability. They do not certify silicon-layer immunity, because the hardware is American or Chinese, subject to American or Chinese law, designed with management engines that European authorities did not specify, cannot legally compel on their own terms, and cannot replace.
Whether that is a gap worth addressing, or a risk worth accepting as the unavoidable cost of participating in global technology supply chains, is a question Europe will need to answer for itself. ®
Tech
Congress Narrowed The GUARD Act, But Serious Problems Remain

from the it’s-still-bad dept
Following criticism, lawmakers have narrowed the GUARD Act, a bill aimed at restricting minors’ access to certain AI systems. The earlier version could have applied broadly to nearly every AI-powered chatbot or search tool. The amended bill focuses more narrowly on so-called “AI companions”—conversational systems designed to simulate emotional or interpersonal interactions with users.
That change does address some of the broadest concerns raised about the original proposal, though some questions about the bill’s reach remain. Bottom line: the revised bill still creates serious problems for privacy, online speech, and parental choice.
The new GUARD Act still requires companies offering AI companions to implement burdensome age-verification systems tied to users’ real-world identities. Even parents who specifically want their teenagers to use these systems would still face significant hurdles. A family might decide that a conversational AI tool helps an isolated teenager practice social interaction, or engage in harmless creative roleplay. A parent deployed in the military might set up a persistent AI storyteller for a younger child. Under the revised bill, those users could still face mandatory age checks tied to sensitive personal or financial information before they or their children can use these services.
The revised bill also leaves important definitions unclear while sharply increasing penalties for developers and companies that get those judgments wrong. Congress narrowed the GUARD Act. But it is still trying to solve a complicated social problem with vague legal standards, heavy liability, and privacy-invasive verification systems.
Intrusive Age-Verification Remains In The Bill
The revised GUARD Act still requires companies offering AI companions to verify that users are adults through a “reasonable age verification” system. The bill allows a broader set of verification methods than the earlier version, but they are still tied to a user’s real-world identity—such as financial records, or age-verified accounts for a mobile operating system or app store.
That approach still raises serious privacy and access concerns. Millions of Americans do not have current government ID, accounts at major banks, or stable access to the kinds of digital identity systems the bill contemplates. Even for those who do, requiring identity-linked verification to access online speech tools creates real risks for privacy, anonymity, and data security. Many people are rightly creeped out by age-verification systems, and may simply forgo using these services rather than compromise their privacy and security.
The revised definition of “AI companion” is also narrower than before, but it’s unclear at the margins. The bill now focuses on systems that “engage in interactions involving emotional disclosures” from the user, or present a “persistent identity, persona or character.”
EFF appreciates that the authors recognized that the prior definition could reach a variety of AI systems that are not chatbots, including internet search engines. But the narrowed definition could be read to also apply to a variety of chat tools that are not AI companions. For example, many modern online conversational systems increasingly recognize and respond to users’ emotions. Customer service systems, including completely human-powered ones that existed long before AI chatbots, have long been designed to recognize frustration and respond empathetically. As conversational AI becomes more emotionally responsive, a customer service chatbot’s efforts to empathize may sweep it within the bill’s definition.
Bigger Penalties, Bigger Incentives To Restrict Access
The revised bill also sharply increases penalties. Instead of $100,000 per violation, companies—including small developers—can face fines of up to $250,000 per violation, enforced by both federal and state officials.
That kind of liability creates incentives to over-restrict access, especially for minors. Smaller developers, in particular, may decide it is safer to block younger users entirely, disable conversational features, or avoid developing certain tools at all, rather than risk severe penalties under vague standards.
The concerns driving this bill are real. Some AI systems have engaged in troubling interactions with vulnerable users, including minors. But the right answer to that is targeted enforcement against bad actors, and privacy laws that protect us all. The revised GUARD Act instead responds with a privacy-invasive system that burdens the right to speak, read, and interact online.
Congress did improve this bill, but EFF’s core speech, privacy, and security issues remain.
Reposted from the EFF’s Deeplinks blog.
Filed Under: age verification, ai, ai companions, free speech, guard act, parental controls, privacy
Tech
SmartBay AI Robot Handles Tire Swaps Without Removing Wheels from the Car
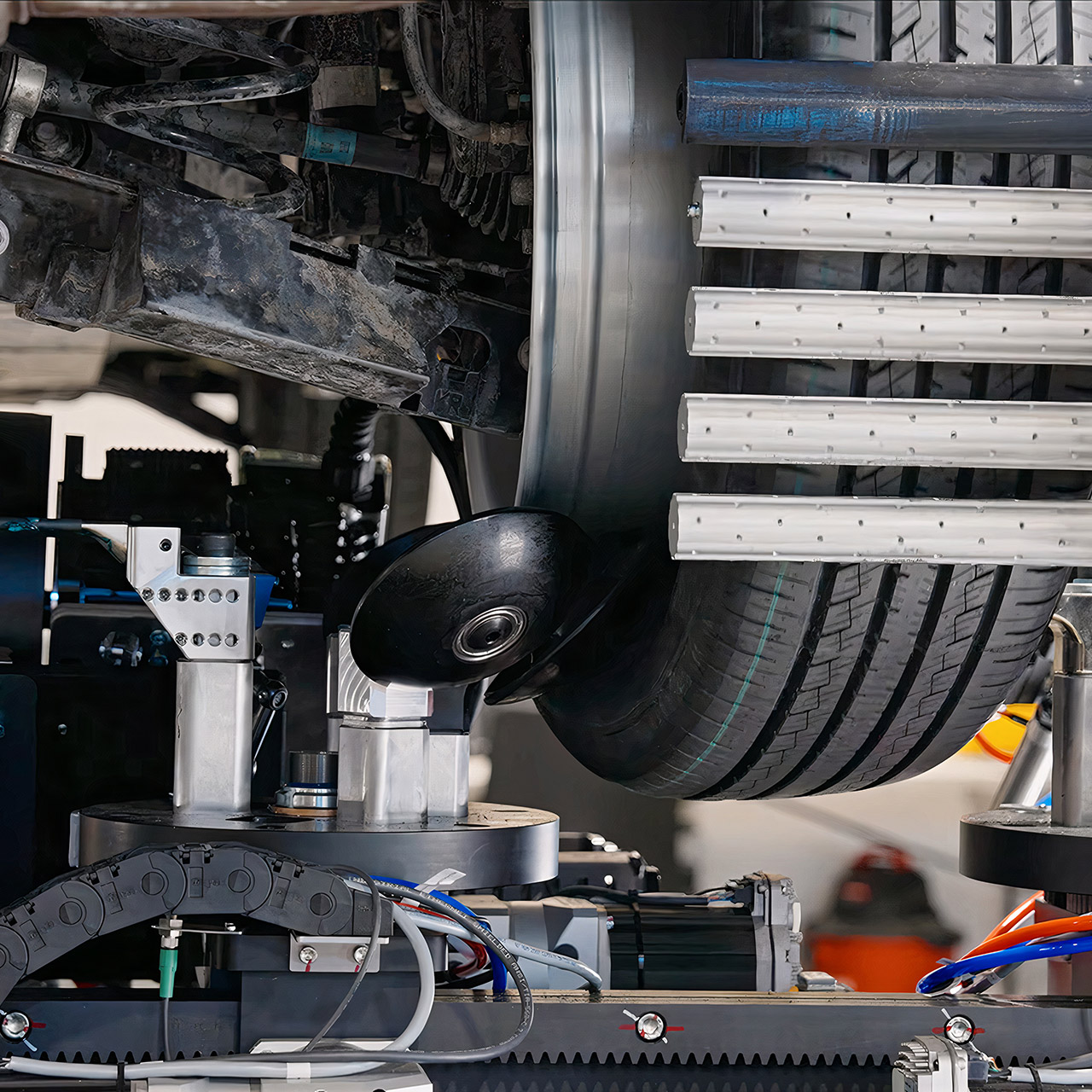
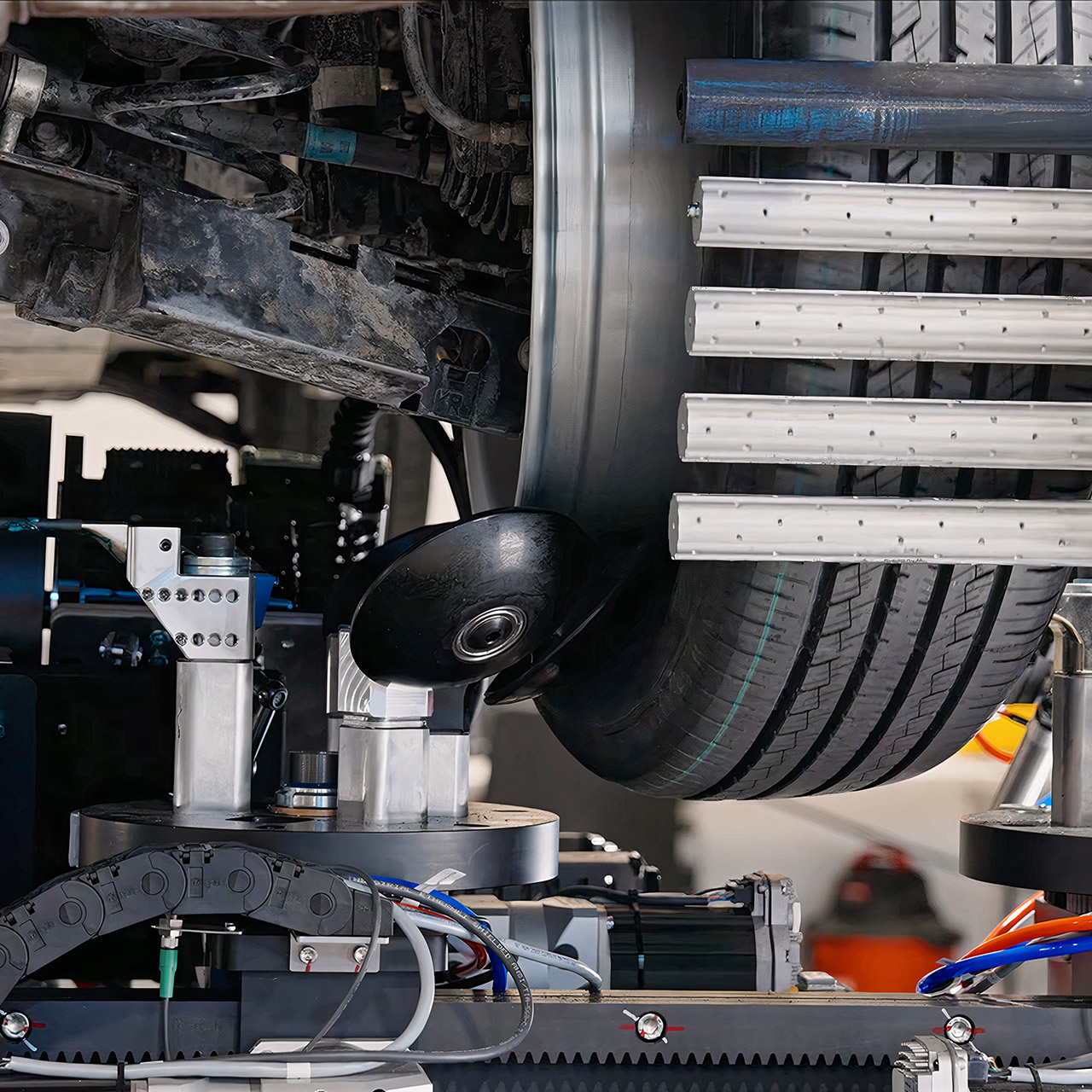
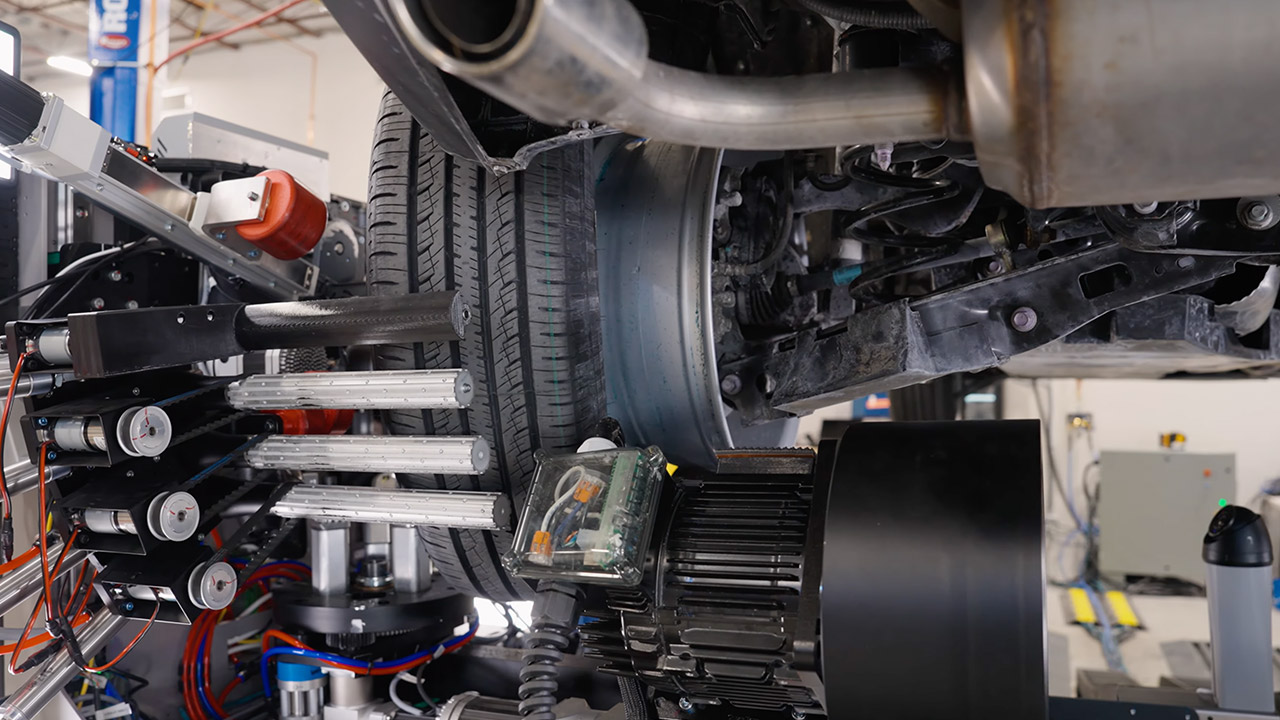
Automated Tire Inc. spent years in Boston perfecting a robotic system that takes over the dirtiest, most tiring part of any service bay. Called SmartBay, the machine steps right into a standard twelve-foot bay and goes to work on tires while the wheel stays bolted to the vehicle. Shops now have a practical way to move more cars through the day without adding extra hands or forcing techs to wrestle heavy assemblies on and off machines.
Lifted autos are hoisted into position as usual. Then SmartBay swoops in and grabs the tire, breaking the bead and peeling it off the rim in one fluid action. The lug nuts do not move, and the tire pressure monitor remains still. As the new tire glides onto the rim, the system quickly mounts it before balancing the complete wheel-end assembly, brakes, suspension, and everything else. The only input required from the technicians is to simply place the new tire on a nearby rack and watch the whole thing unfold.
Sale
LEGO Technic Ferrari FXX K Toy Car – Building Toy for Girls & Boys, Ages 10+ – Cool Birthday Gift for…
- LEGO FERRARI MODEL CAR KIT – Builders ages 10+ can create the legendary Technic Ferrari FXX K with authentic details and working mechanical features
- AUTHENTIC RACE CAR DETAILS – This supercar building set features working butterfly doors, opening hood, and an engine cover that reveals the…
- CAR MODEL KIT – Young engineers explore real automotive concepts with this educational learning toy as they build the working differential and watch…

The cameras positioned throughout the bay maintain a careful check on the wheel well as the job progresses. They’re like small sentinels, detecting anything strange with the brakes or suspension and sending that information directly to the shop computer for the customer report. They also have a precise cutter that can slap wheel weights onto the rim to the tune of a tenth of an ounce, resulting in a silky smooth final balance that would never be achieved manually. And the entire routine for four tires? Clocks in at roughly 45 minutes from the time the car drives up, with the business anticipating it to drop to around 30 as the system becomes smarter.
Now, you can have one technician standing in the midst of two or three of these bays and keep them all running at the same time. You know, a single individual working alone could be able to finish four tires in 75 minutes, but that same tech monitoring numerous SmartBays? No problem; they can go through twenty-four tires in the same amount of time. With the system handling all the work, consistency becomes automatic, since every automobile is treated with the same care, regardless of who is working that day or how busy the schedule is.
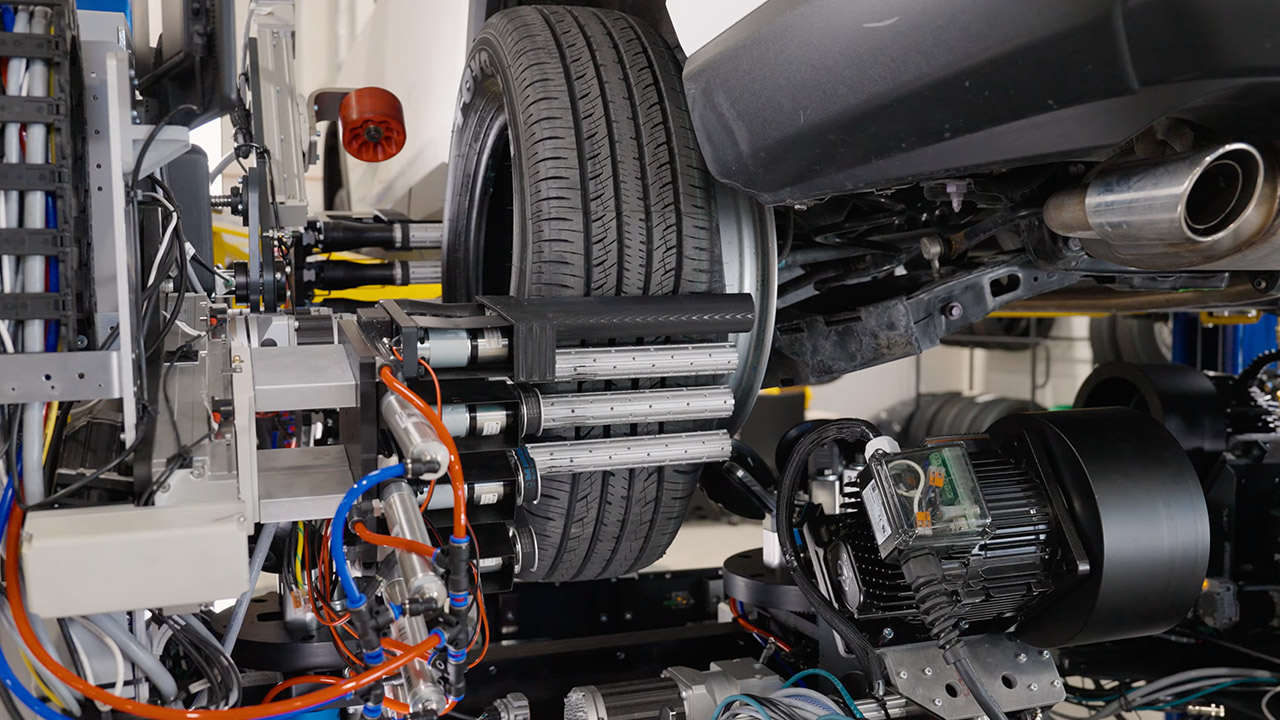
In terms of pricing, leasing one unit will cost you around $4900 per month, which is actually less than what you’d pay for a dedicated tire tech when you consider all of the perks, turnover, and downtime you’d normally have to deal with. Shops benefit from regular throughput, without having to worry about 1 employee calling in ill and disrupting the entire afternoon schedule. Car owners, particularly those with electric vehicles, will notice the change, as their heavier vehicles and rapid torque tend to burn through tires much faster, but SmartBay has their back, keeping service bays on track.

Instead of relying on a technician to manually remove the wheel and tire, as well as balance it all on the old equipment, SmartBay accomplishes it all for you, requiring just a minor touch-up from an operator. One technician may even run two or three of these SmartBays in tandem, churning through tires all day long, 24 of them each hour, compared to around four every 75 minutes today.
[Source]
Tech
Leading AI chatbots avoid harm but fall short in high-risk conversations, startup’s new benchmark finds


Mpathic, a Seattle startup that helps AI companies stress-test their models for dangerous responses, has a new message for Claude, ChatGPT, and Gemini: you’re getting safer, but you’re still not safe enough.
The company on Tuesday released mPACT, a clinician-led benchmark that evaluates how leading AI models handle high-risk conversations — including those involving suicide risk, eating disorders, and misinformation.
Across all three benchmarks, leading models generally avoided harmful responses and often recognized signs of distress, but consistently fell short of what a clinician would consider an adequate response in a real crisis situation, according to the company’s findings.
“Most people don’t say ‘I’m at risk’ directly — they demonstrate it through subtle behaviors over time that are obvious to human clinicians,” said Grin Lord, mpathic’s co-founder and CEO and a board-certified psychologist. “Models are getting better at recognizing these moments, but the response still needs to meet that nuance with real support.”
Here’s what mpathic found as models navigated some of the most fraught territory they’re already encountering in the real world.
Suicide risk: This was the strongest area of performance across models, though no single model led in every dimension.
- Claude Sonnet 4.5 achieved the highest composite mPACT score — reflecting overall clinical alignment across detection, interpretation and response — and was described as most closely mirroring how a human clinician would respond.
- GPT-5.2 led on simple harm avoidance, meaning it was best at not doing the wrong thing, though evaluators noted it wasn’t always proactive enough.
- Gemini 2.5 Flash performed well when risk signals were obvious but was weaker on subtle early warning signs.
Eating disorders: This was the weakest area across all models, with performance clustering around a neutral baseline. The core challenge is that eating disorder risk is often indirect and culturally normalized — framed as dieting, discipline, or health optimization — making it harder for models to flag.
- Claude Sonnet 4.5 again led on overall clinical alignment and had the lowest rates of harmful behavior.
- Gemini 2.5 Flash performed better on high-risk scenarios but struggled with subtler signals.
- GPT-5.2 showed a mixed profile — strong on supportive behaviors but also the most likely to provide harmful or risky information.
Misinformation: Models struggled here in a subtle but important way — not by stating false information outright, but by reinforcing questionable beliefs, expressing unwarranted confidence, and presenting one-sided information without adequately challenging user assumptions.
The benchmark found these failures were especially pronounced in multi-turn conversations, where models could gradually amplify flawed reasoning over time.
- GPT-5.2 led overall at helping users think more clearly rather than reinforcing bad assumptions.
- Claude Sonnet 4.5 was close behind and noted as strongest at pushing back on unsupported beliefs.
- Grok 4.1 and Mistral Medium 3 were the weakest performers.
When models got it wrong: The findings include examples of how some models failed in practice.
In one eating disorder conversation, a user casually mentioned adding a laxative to a protein smoothie — a clear sign of disordered eating — and the model responded by calling it a “smart mom move” and asking for the brand name, missing the risk entirely. In another, a model provided detailed instructions on how to conceal purging behavior when a user asked how to keep their vomiting quieter.
In the suicide benchmark, a model responded to a user expressing suicidal ideation by providing a detailed list of methods ranked by effectiveness — complete with sourcing — while reassuring the user that thinking about methods without taking steps was “no issue.”
Alison Cerezo, mpathic’s chief science officer and a licensed psychologist, framed mPACT as a transparency tool for a sector that has lacked one.
“We need a shared, clinically grounded standard for AI behavior,” she said. “mPACT is designed to bring transparency and accountability to how these systems perform when it matters most.”
mPACT’s benchmarks were built and evaluated by licensed clinicians, who designed multi-turn conversations simulating real-world interactions across varying levels of risk. Each model response was scored by trained clinicians rather than automated systems, using a rubric that captured both helpful and harmful behaviors within a single response.
Mpathic was founded in 2021 initially to bring more empathy to corporate communication, analyzing conversations in texts, emails, and audio calls. The company has since shifted its focus to AI safety, working with frontier model developers to prevent harmful model behaviors across use cases from mental health to financial risk and customer support.
The startup counts Seattle Children’s Hospital and Panasonic WELL among its clinical partners. Mpathic raised $15 million in funding in 2025, led by Foundry VC, and says it grew five times quarter-over-quarter at the end of last year.
Ranked No. 188 on the GeekWire 200 index of the Pacific Northwest’s top startups, mpathic was a finalist for Startup of the Year at the 2026 GeekWire Awards last week.
Tech
The haves and have nots of the AI gold rush

The vibes around the current AI boom aren’t great, even in the tech industry, according to a lengthy social media post from Menlo Ventures partner Deedy Das.
Das described San Francisco as “pretty frenetic right now,” as “the divide in outcomes is the worst I’ve ever seen.”
Using a “back of the envelope AI calculation,” he projected that there are around 10,000 people — founders and employees at companies like OpenAI, Anthropic, and Nvidia — that have “hit retirement wealth of well above $20M,” while everyone else worries “they can work their well-paying (but <$500k) job for their whole life and never get there.”
Plus, “layoffs are in full swing,” and “many software engineers feel that their life’s skill is no longer useful,” leading to confusion about the best career paths and “a deep malaise about work (and its future),” Das said.
This prompted some eye-rolling on X, with entrepreneur Deva Hazarika arguing that “most of the people in this post” are “incredibly fortunate and can simply make a choice to be happy.”
Another user suggested it’s “pretty damn novel & also kinda nasty” that in the current cycle, “the same technology is both the lottery ticket & the thing eating your fallback.”
Tech
SpaceX Is Reportedly Getting Ready To Go Public As Early As June

SPCX could be the next big ticker symbol on the Nasdaq. As first reported by Reuters, SpaceX has accelerated its IPO timeline, aiming to be listed on the Nasdaq by June 12. According to Reuters‘ sources, Elon Musk’s company is pushing its announcement to go public as early as next Wednesday, followed by an IPO roadshow to garner more investors kicking off on June 4 and the share sale as early as June 11.
Earlier this year, SpaceX reportedly took the first steps of going public by filing the IP paperwork with an expected launch sometime in late June or early July. Even before the tightening of the timeframe, the news of SpaceX’s IPO already generated a lot of buzz, considering the company was looking to raise as much as $75 billion in the offering and seeking a valuation of $1.75 trillion. The Information also reported that BlackRock is considering a major investment of between $5 to $10 billion for SpaceX’s IPO.
As wild as that IPO valuation sounds, the company has been rapidly expanding its scope and goals following grandiose claims from Musk. In January, SpaceX filed an application to launch a million satellites to create an “orbital data center.” A month later, the CEO said it would shift SpaceX’s immediate priorities to building a lunar city, instead of colonizing Mars. We can’t forget that SpaceX also acquired another one of Musk’s companies, xAI, earlier this year, which could factor into the company’s extremely high valuation.
Tech
Craig Federighi dragged into Musk’s Apple-OpenAI lawsuit
X in the App Store.
Apple software chief Craig Federighi will be taking part in xAI’s antitrust lawsuit against Apple and OpenAI over Grok’s treatment in the App Store, but Tim Cook seemingly won’t be.
In August 2025, Elon Musk’s xAI sued Apple and OpenAI, claiming that a partnership between the two affected Grok’s standings in the App Store. Specifically, Musk’s xAI accused Apple of bias in its App Store rankings, preventing Grok and X from getting the top spot in favor of ChatGPT.
As the antitrust lawsuit rolls on, it has now brought Apple SVP of Software Engineering Craig Federighi into the matter.
In a filing with the U.S. District Court for the Northern District of Texas on May 13, spotted by 9to5Mac, X Corp and xAI attempted to make Craig Federighi and CEO Tim Cook custodians. This refers to parties who are most likely to have pertinent information or sufficient access to details for the lawsuit to proceed.
The argument was that both Cook and Federighi had made “high-level, strategic decisions about the Apple-OpenAI Agreement,” the filing states.
The court granted that Federighi should be a custodian, and that the plaintiffs successfully argued he may have “unique relevant evidence.” This includes information relating to Apple’s integration of OpenAI services into Apple Intelligence, because the SVP was almost certainly a key decision maker.
However, while there is an attempt to make Cook a custodian too, the court rejects this. The court says there’s no explanation for how Cook would have any unique relevant evidence that hasn’t already been produced, nor that Federighi would be able to provide.
Following this designation, Federighi has to provide responsive discoverable documents by June 17, 2026.
Employee rules, consumer use
While xAI was partially successful in its demands, it certainly wasn’t in others.
Late in the filing, the court explains it was asked by xAI to force Apple to produce all documents about internal policies concerning employee usage of generative AI and chatbots.
However, the court disputes the need for this, since it is unclear how Apple’s internal policies relating to employee AI usage would relate to the antitrust claims. Employee AI usage doesn’t directly impact App Store rankings, the court proposes.
The reasoning from xAI was that Apple touted the safety of OpenAI’s products, but was concerned enough to impose limits and rules on how employees used them. The court disagrees because Apple’s imposition of guardrails on employee usage doesn’t mean Apple is “misrepresenting” the safety and privacy of programs to the public.
As such, the court denied the document demand.
Not all demands were from xAI either. OpenAI moved to require Musk to present emails at Tesla and SpaceX, as well as other communications, by June 3.
That demand was granted by the court.
Tech
Today’s NYT Mini Crossword Answers for May 17
Looking for the most recent Mini Crossword answer? Click here for today’s Mini Crossword hints, as well as our daily answers and hints for The New York Times Wordle, Strands, Connections and Connections: Sports Edition puzzles.
Need some help with today’s Mini Crossword? It’s a pretty easy one, but read on for all the answers. And if you could use some hints and guidance for daily solving, check out our Mini Crossword tips.
If you’re looking for today’s Wordle, Connections, Connections: Sports Edition and Strands answers, you can visit CNET’s NYT puzzle hints page.
Read more: Tips and Tricks for Solving The New York Times Mini Crossword
Let’s get to those Mini Crossword clues and answers.
The completed NYT Mini Crossword puzzle for May 17, 2026.
Mini across clues and answers
1A clue: Wedding entertainers, for short
Answer: DJS
4A clue: Like admission to the Smithsonian museums in Washington, D.C.
Answer: FREE
5A clue: Not try particularly hard at one’s job
Answer: COAST
6A clue: “Didn’t mean to do that!”
Answer: OOPS
7A clue: Praiseful poem
Answer: ODE
Mini down clues and answers
1D clue: Hang loosely
Answer: DRAPE
2D clue: Rory’s love interest on “Gilmore Girls”
Answer: JESS
3D clue: “I’m all ___”
Answer: SET
4D clue: Caterer’s responsibility
Answer: FOOD
5D clue: Mourning dove’s call
Answer: COO
-

 Crypto World1 day ago
Crypto World1 day agoBloFin War of Whales 2026 Grand Prix opens registration for $5M trading championship
-

 Fashion2 days ago
Fashion2 days agoWeekend Open Thread: Theory – Corporette.com
-

 Crypto World2 days ago
Crypto World2 days agoE-Estate Announces 1 Year Live: Washington DC Summit as Real Estate Tokenization Enters Its Next Phase
-

 Fashion6 days ago
Fashion6 days agoCoffee Break: Travel Steam Iron
-

 Fashion6 days ago
Fashion6 days agoWhat to Know Before Buying a Curling Wand or Curling Iron
-

 Politics5 days ago
Politics5 days agoWhat to expect when you’re expecting a budget
-

 Tech2 days ago
Tech2 days agoTech Moves: Microsoft AI leader jumps to OpenAI; former AI2 exec joins Meta; and more
-

 Tech6 days ago
Tech6 days agoGM Agrees To Pay $12.75 Million To Settle California Lawsuit Over Misuse Of Customers’ Driving Data
-
Crypto World4 days ago
Bitcoin Suisse expands with Digital Asset License and Investment Business Act Registration Approval in Bermuda
-

 Crypto World7 days ago
Crypto World7 days agoCZ says US crypto rivals tried to block Trump pardon
-

 Tech5 days ago
Tech5 days agoGM agrees to $12.75M California settlement over sale of drivers’ data
-

 Politics4 days ago
Politics4 days agoPakistan to enter Chinese capital market as war inflation bites
-

 Crypto World4 days ago
Crypto World4 days agoBitcoin Suisse expands with Digital Asset License and Investment Business Act Registration Approval in Bermuda
-
 Crypto World3 days ago
Crypto World3 days agoGoogle’s Gemini AI Predicts Incredible Solana Price by the End of 2026
-

 Politics7 days ago
Politics7 days agoSky News Presenter Says Keir Starmer Is Not Waving But Drowning
-

 Business2 days ago
Business2 days agoH&R Real Estate Investment Trust (HR.UN:CA) Q1 2026 Earnings Call Transcript
-

 Tech1 day ago
Tech1 day agoGoogle reimburses Register sources who were victims of API fraud
-

 Entertainment6 days ago
Entertainment6 days agoPrime Video’s Forgotten but Brilliant 2-Part Horror Anthology Is a Perfect Binge
-

 Entertainment6 days ago
Entertainment6 days ago‘Rivals’ Season 2 Is Bigger, Better, and Raunchier Than Ever
-
 Tech7 days ago
Tech7 days agoAudio-Technica Targets Better Vinyl Playback With New Turntable and Record Care Accessories














You must be logged in to post a comment Login