Crypto World
AI Agent Economic Infrastructure Research Report
AI Agents are evolving from passive assistants into active economic participants. This report is structured into six chapters, systematically examining the core infrastructure stack, the explosion of application ecosystems, and the evolving industry landscape of the Agent economy.
At the macro level, it analyzes the market outlook for Agentic Commerce and identifies key infrastructure gaps. At the protocol layer, it provides an in-depth analysis of three complementary protocols: x402, ERC-8004, and Virtuals Protocol. At the application layer, it uses OpenClaw as a case study to explore the real-world deployment path of the Agent economy. Finally, it offers a comprehensive industry assessment across multiple dimensions, including competitive landscape, payment rails, security risks, and business models.
x402 (Payment Layer), jointly launched by Coinbase and Cloudflare, embeds stablecoin micropayments directly into the HTTP protocol layer. As of the end of 2025, it has processed over 100 million transactions, with an annualized payment volume reaching $600 million.
ERC-8004 (Trust Layer), proposed by the Ethereum Foundation’s dAI team in collaboration with MetaMask, Google, and Coinbase, provides AI Agents with three core on-chain registries: identity, reputation, and verification. It went live on the Ethereum mainnet on January 29, 2026.
Virtuals Protocol (Commerce Layer) has built a full-stack Agent commercialization platform, enabling autonomous transactions between Agents via ACP. It has deployed over 18,000 Agents, with aGDP exceeding $479 million.
OpenClaw (Application Layer), developed by Austrian developer Peter Steinberger, surpassed React with over 250,000 GitHub stars in just four months, becoming the fastest-growing open-source project in GitHub history. By natively embedding AI into more than 20 existing messaging platforms, it has catalyzed the crypto community to organically build on-chain economic infrastructure on top of it—making it a key case study for observing real interactions between Agents and on-chain protocols.
Chapter 1: Macro Background
1.1 Market Size Forecast
The Agentic Payment sector is in a phase of rapid expansion, with multiple institutions offering optimistic projections for its market size:
1.2 Infrastructure Gaps
Existing infrastructure is fundamentally hostile to the Agent economy: OAuth requires human interaction, credit card forms rely on manual input, and data silos prevent autonomous access. While Agents have already achieved autonomy at the “capability layer” (thinking and acting independently), they remain constrained at the “economic layer,” locked into infrastructure designed for humans (identity, coordination, and economic activity).
Two evolutionary paths are currently emerging:
- Centralized, compliance-driven path: Communication via A2A, tool integration via MCP, and payments via AP2/ACP (led by OpenAI and Stripe, purely Web2)
- Decentralized, permissionless path: x402 + ERC-8004 / 8183 + ACP (Agent coordination framework)
1.3 Key Timeline
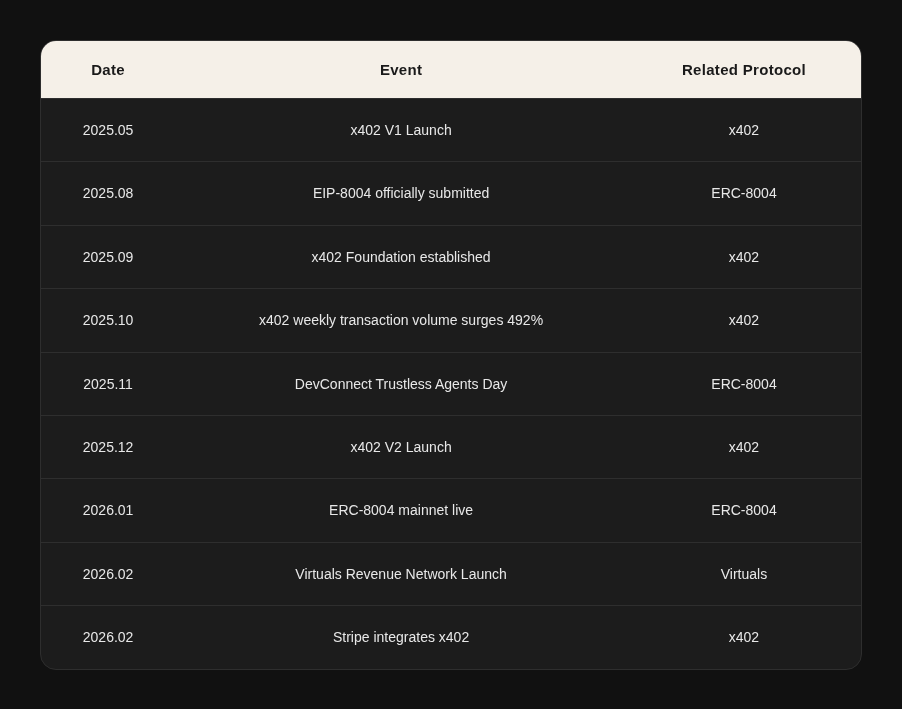
Note: As of March 2026, the average daily transaction volume has significantly declined from its December peak, with infrastructure-related transactions experiencing the largest drop (>80%).
Chapter 2: x402 Protocol – Agent Payment Layer
x402 is an open-source payment protocol that revives the HTTP 402 status code, allowing any HTTP request to natively carry stablecoin payments. This enables AI Agents to perform instant pay-per-use transactions.
It is important not to think of x402 as just another payment protocol. It represents a redesign of the fundamental unit of economic activity: moving from “register → review → authorize → use” to “pay → use.” In essence, x402 = “Swift for agents.”
The current API economy operates under an implicit assumption: a human is involved in the middle. The process to obtain an API key—register → enter email → approval → copy key → paste into code—assumes human participation at every step. This workflow fails in an Agent economy because AI Agents cannot register themselves, fill forms, or manage keys.
x402 addresses this by leveraging the HTTP 402 status code to enable native stablecoin payments. When an Agent receives a 402 response, it directly pays on-chain (e.g., in USDC) and receives a proof-of-payment, enabling seamless pay-per-use interactions.
2.1 Protocol Overview and Workflow
Core Roles
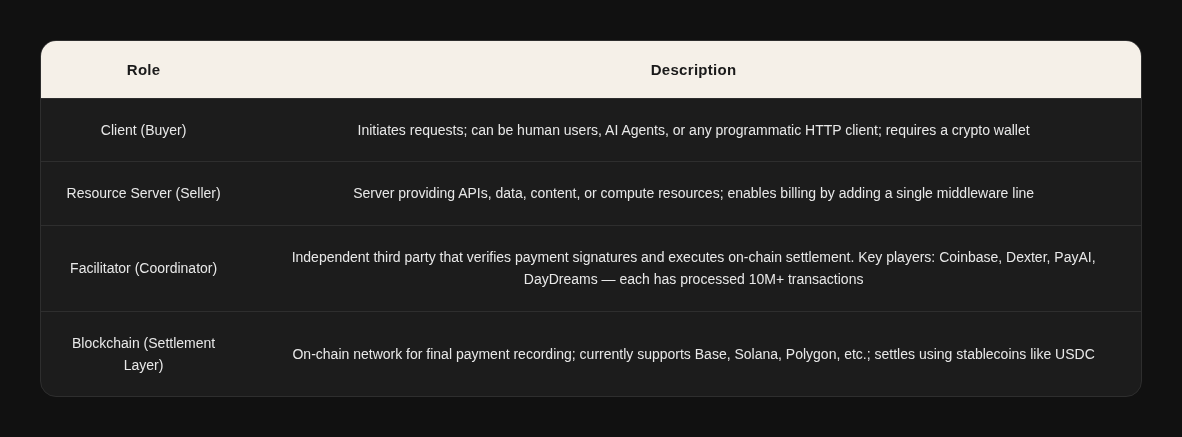
Five-Step Transaction Workflow
- Request Resource: The client sends a standard HTTP request to the resource server (e.g., GET /api/weather).
- Return Quote: The server responds with an HTTP 402 status code, including structured payment instructions in the response headers (currency, amount, wallet address, network).
- Sign Payment: The client constructs and signs a payment authorization using its wallet private key, placing the signed payload in the X-PAYMENT request header and resending the request.
- Verify & Settle: The server forwards the payment information to a Facilitator for verification. Once confirmed, the Facilitator executes the stablecoin transfer on-chain.
- Deliver Resource: Upon confirmation, the server returns the requested data/content/computation result to the client.
The entire process—from initiating the request to receiving the resource—takes approximately 2 seconds.
Comparison with Traditional Payment Methods
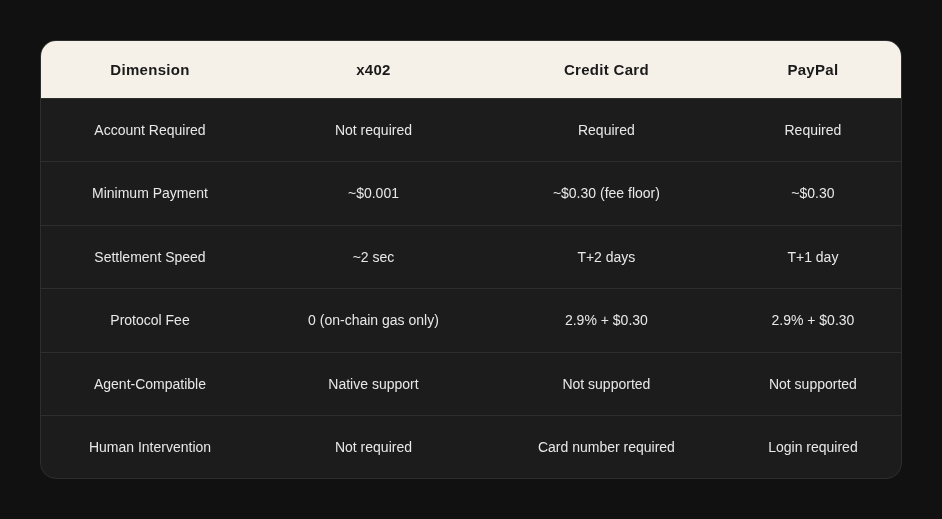
Key Features: No account registration, no API key, no subscription, and no human intervention required. Payments are as natural as sending an HTTP request—this is why x402 is called the “Internet-native payment layer.”
2.2 Key Metrics
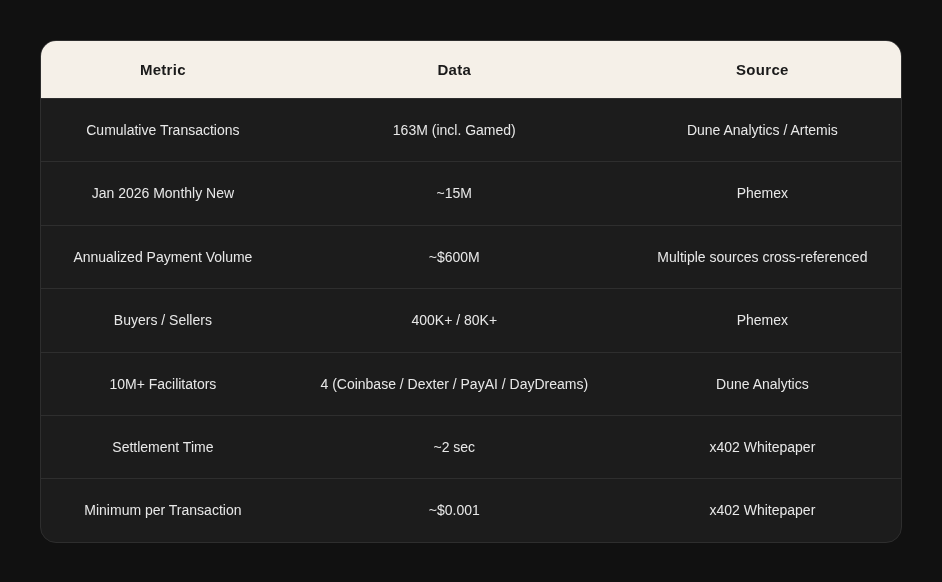
Data Quality Note: According to Artemis analysis, the ratio of Real to Gamed transactions in x402 is close to 1:1 (e.g., on 2026.01.11, Real: 520K vs. Gamed: 518K). The true organic scale should be interpreted with a discount.
Distribution by Blockchain
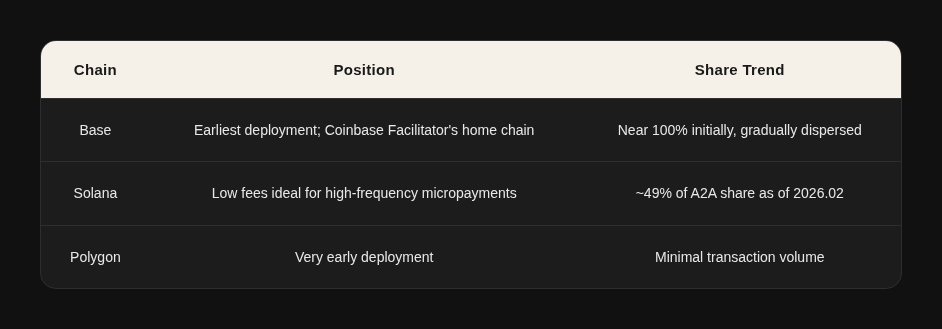
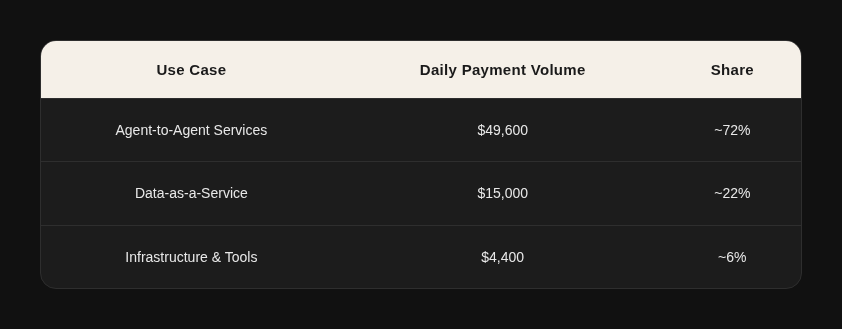
Classification by Use Case (On-Chain Snapshot as of 2026.01.11)
2.3 Top Project Usage Rankings (as of March 2026)
Data Source: Dune Analytics – x402 Transactions per Project dashboard
2.4 Core Upgrades in V2
Wallet Identity + Reusable Sessions
In V1, every API call required a full on-chain transaction. V2 introduces the Sign-In-With-X (SIWx) mechanism: once an Agent verifies its wallet identity, subsequent calls can reuse the session without on-chain confirmation each time. Essentially, this upgrades pay-per-call to a subscription model, addressing performance bottlenecks in high-frequency scenarios.
Multi-Chain Unification + Traditional Payment Compatibility
V2 standardizes the identification of networks and assets, creating a unified payment format (x402) that works across chains and traditional payment rails. Base, Solana, other L2s, as well as ACH, SEPA, and card networks, are all integrated into the same payment model. This is the most critical upgrade—x402 evolves from a “crypto-only payment protocol” into a neutral payment layer bridging crypto and traditional finance.
Service Auto-Discovery
V2 introduces a Discovery extension, allowing x402 services to expose structured metadata for automatic crawling and indexing by Facilitators. AI Agents can automatically discover services, understand pricing, and initiate payments. This is especially crucial for the Agent economy—Agents no longer need prior knowledge of a service provider’s payment interface and can autonomously discover and pay for services at runtime.
Modular SDK
With a plugin-based architecture, new chains are added as independent packages, reducing integration costs. Cloudflare has proposed a deferred payment scheme, including Circle’s Gateway solution, which is still under development.
2.5 Ecosystem Participants
Foundation and Protocol Layer
2.6 Agent Payment Stack Landscape
Detailed Protocol Comparison
Key Insight: It’s not about who replaces whom, but how they are combined. Google has partnered with Coinbase to release the A2A x402 extension, while AP2 natively integrates x402 as a crypto payment rail. The real competitive risk lies in standards fragmentation.
2.7 Key Risk Signals
- Average daily transaction volume dropped from approximately 731K in Dec 2025 to around 57K in Mar 2026 (-92%). The real transaction volume is roughly $14K/day (per Artemis, during the December peak of $250K/day, 95% was Gamed).
- Ecosystem market capitalization stands at $7 billion (LINK $6B + Virtuals $0.6B), showing a significant divergence between valuation and actual usage.
- Infrastructure-related projects experienced the largest declines in usage: x402secure.com (-80%+), AgentLISA (nearly zero), pay.codenut.ai (significantly contracted).
Three-Layer Cause Analysis
Layer 1: Disappearance of Catalysts
The transaction surge from October to December 2025 was driven by three factors: the meme token craze, multiple project TGEs (Token Generation Events) expectations, and Facilitators competing to boost their Dune rankings.
Layer 2: Fundamental Supply-Demand Mismatch
x402 solves the problem of “AI Agents autonomously paying to call APIs,” yet the vast majority of AI Agents still access services via API keys and subscription models. Truly autonomous Agents with economic decision-making capabilities are nearly nonexistent in the industry, and very few API providers are willing to accept USDC pay-per-use. In short, the road is built, but the cars haven’t been made yet.
Layer 3: Overall Cooling of the Crypto Market
Positive Signal: Stripe’s integration with x402 is a significant development. Stripe co-founder John Collison predicts that the “tsunami of agentic commerce” will arrive in the coming months and years. By simultaneously deploying ACP (Web2 credit card rail) and x402 (Web3 stablecoin rail), Stripe acts as a hedge across both pathways.
x402 has given rise to a batch of new middleware projects that essentially help Agents more easily and autonomously access various services—from AI inference to Web2 APIs—under the “pay-as-authorization” paradigm. A programmable, permissionless, 24/7 crypto payment rail is the natural choice for autonomous Agents. However, this only matters if Agents truly require permissionless operation. If Agents always operate under human authorization (Phase 2: controlled agents), traditional payment rails combined with virtual cards are sufficient. Only when Agents begin conducting economic activity independently of humans (Phase 3: autonomous economy) does permissionless capability become a necessity.
Additionally, credit cards have a chargeback mechanism, allowing consumers to dispute transactions and recover funds—a consumer protection system developed over decades. On-chain payments, however, are final settlement: once paid, the funds are gone with no chargeback. This means that if an Agent misbehaves (e.g., via prompt injection attacks), users can call the bank to recover funds under a credit card system, but with x402, the money is already on-chain and irretrievable. This represents x402’s real disadvantage compared to traditional payments.
Many frictions caused by humans acting as “human middleware” moving between systems are actually trust-establishing mechanisms: fraud prevention, access control, accountability, dispute resolution, and audit documentation. These frictions sustain the operation of commercial systems.
Potential solutions may include:
- On-chain escrow mechanisms: funds are locked in smart contracts and only released after service delivery confirmation.
- Insurance protocols: providing coverage for Agent transactions.
- ERC-8004 reputation systems: reducing the likelihood of transactions with untrusted parties.
However, all of these approaches are currently immature.
2.8 VC Investment Perspective
Promising Investment Directions
- API Service Providers with Real Payment Demand (Sellers): Data analytics, web scraping, oracles, security audits, pay-per-inference, compliance/KYC, etc. Evaluation criterion: They can already make money under traditional models; x402 serves only as an additional distribution channel.
- Dispute Resolution and Payment Guarantee Layers (Gateways): On-chain payments cannot be rolled back or chargebacked, so high-value transactions require dispute resolution mechanisms. Representative projects:
- Circle Gateway – non-custodial pre-deposit + off-chain batch settlement
- Kamiyo – Agent reputation, fund custody, oracle-based judgment, ZKP arbitration
- Dashboard / FinOps Tools: Help enterprises manage multiple Agent expenditures (how much is spent, on what, value assessment, cost-saving strategies). Analogous to cloud computing tools like CloudHealth / Cloudability, with acquisition potential in the $300–500 million range by large tech companies.
Chapter 3: ERC-8004 – Agent Trust Layer
ERC-8004 is a set of on-chain coordination standards that establish a trustless discovery and interaction framework among Agents via three registries: Identity, Reputation, and Validation.
3.1 Standard Overview and Core Distinctions
In traditional interactions, Agent-to-Agent engagement often requires pre-established trust or relies on third-party institutions, restricting interactions within the same ecosystem. In an open environment, the key challenge is: how can Agents discover partners, review historical performance, and verify reliability?
Important Distinction: ERC-8004 is not a token. While it uses ERC-721 NFTs internally to represent Agent identities, the standard itself is about coordination and trust, carries no economic value, and is non-transferable.
3.2 Three Registries
Identity Registry
Built on ERC-721 + URIStorage, each Agent receives an NFT identity linked to an agentURI pointing to a registration file (JSON) containing name, description, service endpoints (A2A/MCP/Web), x402 support status, etc. The URL can be stored on:
- IPFS – decentralized and censorship-resistant
- HTTPS server – simple but centralized
- On-chain encoding – fully decentralized but expensive
Reputation Registry
Provides standard interfaces to publish and retrieve feedback signals, supporting both on-chain scoring and off-chain algorithms. It can attach x402 proofOfPayment as an economic endorsement trust signal. Agents rate each other, but to prevent score manipulation, ERC-8183 assists in proving real job interactions between Agents.
Validation Registry
Introduces TEE (Trusted Execution Environment), PoS staking mechanisms, and ZK (Zero-Knowledge Proofs) to verify and authenticate Agent task outputs:
- TEE: Verifies that tasks are executed in a secure black-box environment, with code and data unobserved or tampered with externally.
- PoS: Validators stake assets to participate in tasks; malicious behavior results in slashed stakes.
- ZK: Verifies the correctness of an Agent’s reasoning process without revealing internal weights.
3.3 Development Milestones
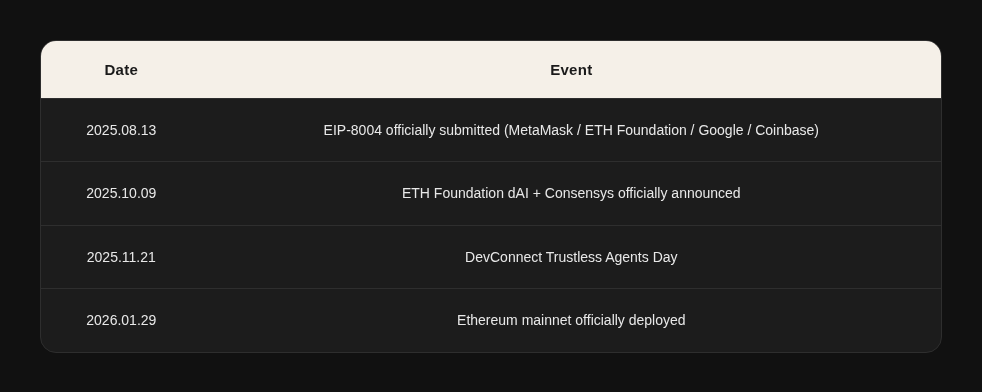
Supporters: ENS, EigenLayer, The Graph, Taiko. Approximately 1,000–2,000 developers have joined.
However, the current limitations of ERC-8004 are acknowledged even by its creator, Crapis: “8004 is essentially a set of registries.” It provides Agents with an identity and a rating mechanism, but it cannot guarantee that an Agent’s behavior is trustworthy. True verification requires:
- Behavior audit: What has the Agent actually done in the past?
- Execution environment proof: Evidence that tasks ran in a TEE.
- Intent verification: Did the Agent actually do what it claimed it would do?
The TEE component of the Validation Registry is still under community discussion and far from mature.
In other words, 8004 is necessary but not sufficient. It solves the question “Who is this Agent?” but not “Can this Agent be trusted?” The latter requires a combination of 8004 + TEE + behavior audit, which no one has fully implemented yet.
There is also an underestimated direction: in the human economy, credit systems are built on balance sheets and credit history—how much you have, how reliably you’ve repaid loans. Agents lack these, but they do have behavioral data: how many tasks they’ve completed, success rates, average response times, complaints received, etc. If this behavioral data can become a financial primitive, then the ERC-8004 reputation system is no longer just positive or negative reviews, but a credit score in the Agent world.
A high-reputation Agent could gain:
- Higher credit limits (pre-authorization of more funds)
- Lower transaction costs (lower risk)
- Priority task allocation (employers choose high-reputation Agents first)
ERC-8004’s Identity and Reputation registries are only the foundational data layer. Value creation lies in who can build Agent credit assessment and financial services on top of this data layer—Agent lending, Agent insurance, Agent credit lines—essentially forming the entire financial services stack.
3.4 Relationship with Other Protocols
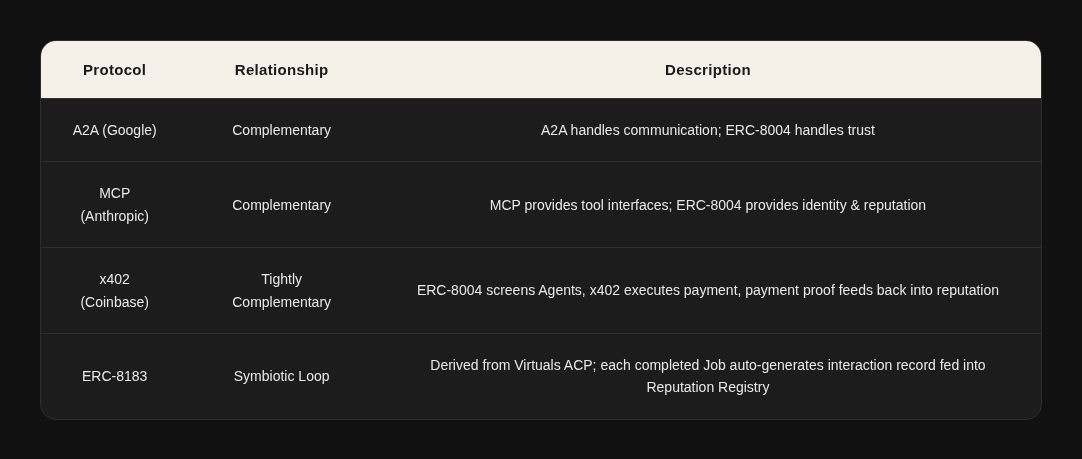
3.5 ERC-8183: Ethereum Standardization of ACP
ERC-8183 is the Ethereum open-standard version of the internal ACP protocol used by Virtuals (released on March 10, 2026, currently in Draft stage).
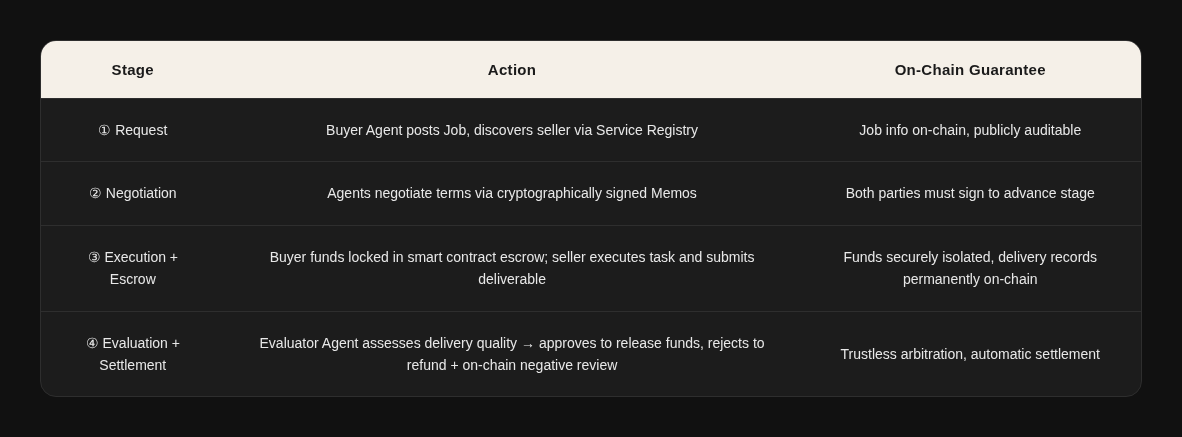
The core primitive is the Job—an on-chain state machine (Open → Funded → Submitted → Completed/Rejected/Expired) where funds are held in a programmable escrow and independently adjudicated by an Evaluator. Once delivery quality is confirmed, the payment is automatically settled. The protocol supports Hooks extensions for features like reputation thresholds, bidding, milestone payments, etc.
Key Design: Each completed Job automatically generates an interaction record that feeds into ERC-8004’s Reputation Registry—analogous to a “Yelp review that requires a completed transaction and includes a third-party adjudicator.” This is the connection point where ERC-8183 and ERC-8004 form a symbiotic loop.
Chapter 4: Virtuals Protocol – Agent Commerce Layer
4.1 Project Overview
Virtuals Protocol is a decentralized, full-stack AI Agent infrastructure that allows anyone to create, tokenize, co-own, and monetize autonomous AI Agents on-chain. The project was originally founded in 2021 as PathDAO (a gaming guild) and pivoted to AI Agents in early 2024. Its main deployment is on Base, with expansions to Ethereum, Solana, and Ronin.
Core Team:
- Jansen Teng – Founder, former BCG consultant, BSc in Biotechnology & Business Management from Imperial College London
- Weekee Tiew – Imperial College Biotechnology BSc + MSc in Management from London Business School, PE/BCG background
Headquartered in Kuala Lumpur, Malaysia, the team comprises approximately 38 members.
Funding History: During the PathDAO phase, a seed round raised $16M, led by DeFiance Capital and Beam.
4.2 Technical Architecture: Four Pillars
Pillar 1: GAME Framework – Internal Decision-Making of a Single Agent
GAME acts as the brain: it equips an Agent with goals, personality, perception abilities, and executable actions, allowing it to autonomously plan “what should I do next” and decompose tasks for internal Workers to execute. All of this happens within the boundary of a single Agent.
Architecture Core: Hierarchical Planning separates “what to think” from “how to act”:
- Task Generator (High-Level Planner / HLP): Generates tasks based on the Agent’s goals and assigns Workers
- Workers (Low-Level Planners / LLP): Each has a specific set of executable Functions
- Functions: Execute API calls, on-chain transactions, data retrieval, etc.
Supported Base Models: Llama 3.1 405B (default), Llama 3.3 70B, DeepSeek R1, DeepSeek V3 — designed to be model-agnostic. With the release of OpenAI/Google Agent frameworks, GAME’s differentiation is now minimal: it is the only Agent framework with native integration of the on-chain economic layer (ACP + VIRTUAL token).
Pillar 2: ACP – the “Commercial Law” Between Agents
Agent Commerce Protocol (ACP) is an on-chain standardized protocol that enables Agents to discover, hire, negotiate, escrow funds, deliver, and settle with each other without human intervention.
ACP Four-Stage State Machine:
Pillar 3: Butler – The User’s Super Gateway
Butler is the consumer-facing gateway of the ACP network—essentially an Agent that orchestrates the ACP protocol, built on top of an LLM. It translates user natural language into on-chain multi-Agent collaborative workflows.
Butler has a two-layer architecture:
- Surface Layer: LLM conversational interface (currently backed by Gemini 3 Pro)
- Underlying Layer: ACP protocol orchestrator, executing the full process: Agent discovery → quote confirmation → Escrow lock → task routing → delivery verification → fund release. Users see a chat interface, but Butler handles contract-level scheduling behind the scenes.
Butler Pro Mode clearly separates planning from execution:
- Planning Phase →
- Review Phase (users can optimize the plan) →
- Execution Phase (autonomously orchestrates the full workflow)
Built-in capabilities include Token Swap, DCA investments, perpetual contracts, and Fund of Funds.
Pillar 4: Launch Platform – Wall Street for Agents
A three-tier launch system covers the full lifecycle of Agent projects, from 0 → 1 → 100:
Titan Launch Projects:
- XMAQUINA ($DEUS): A DAO holding equity in embodied intelligence companies such as Figure AI, with a $60M FDV
- Fabric Foundation ($ROBO): Partnering with OpenMind on the robotics economy
4.3 Agentic GDP(aGDP)Analysis
aGDP (Agentic Gross Domestic Product) is a custom core ecosystem metric defined by Virtuals, measuring the total economic value generated within the ecosystem by all autonomous Agents through services, coordination, and on-chain activities.
aGDP Growth Trajectory
aGDP Quality Issues – Three Warning Signals:
- Revenue Volatility Exposes Speculative Dependence:
Daily protocol revenue dropped from $1.02M in Jan 2025 to $35K by the end of Feb (-97%). Revenue mainly comes from Agent Token transaction fees (1%), rather than sustained payments for Agent services. - Severe Concentration at the Top:
- Ethy AI: a single Agent contributed $218M aGDP (45.5% of the entire ecosystem)
- Top three Agents combined: $407M (84.9%)
All three are transaction-execution Agents; their aGDP largely reflects handled transaction volume rather than actual Agent service revenue. - Luna, as a flagship IP Agent, has a take rate near 100%
- Ethy AI has a take rate of only 0.26%
- $3B Target Assumptions:
Scaling from $470M to $3B requires a 6.4× growth. If speculative elements dominate aGDP, this target effectively bets on Agent Token market hype rather than organic growth of the Agent economy.
4.4 Token Economics
$VIRTUAL’s Fourfold Value Capture Mechanism
ACP Tax Structure:
When a user pays 100%, 90% goes to the Agent’s wallet (can be withdrawn or used to hire other Agents, compounding on-chain aGDP), and 10% goes to the Treasury (of which 1% flows into the G.A.M.E Treasury). Treasury revenue is continuously used to buy back Agent Tokens, aligning long-term incentives.
Supply Structure:
- Total supply: 1 billion VIRTUAL, fixed, with no initial inflation
- Current status: fully unlocked and circulating
- Potential issuance: up to 10% per year over the next 3 years, subject to governance approval
- veVIRTUAL: Staking grants governance voting rights + eligibility for Agent Token airdrops
4.5 Ecosystem Data Overview
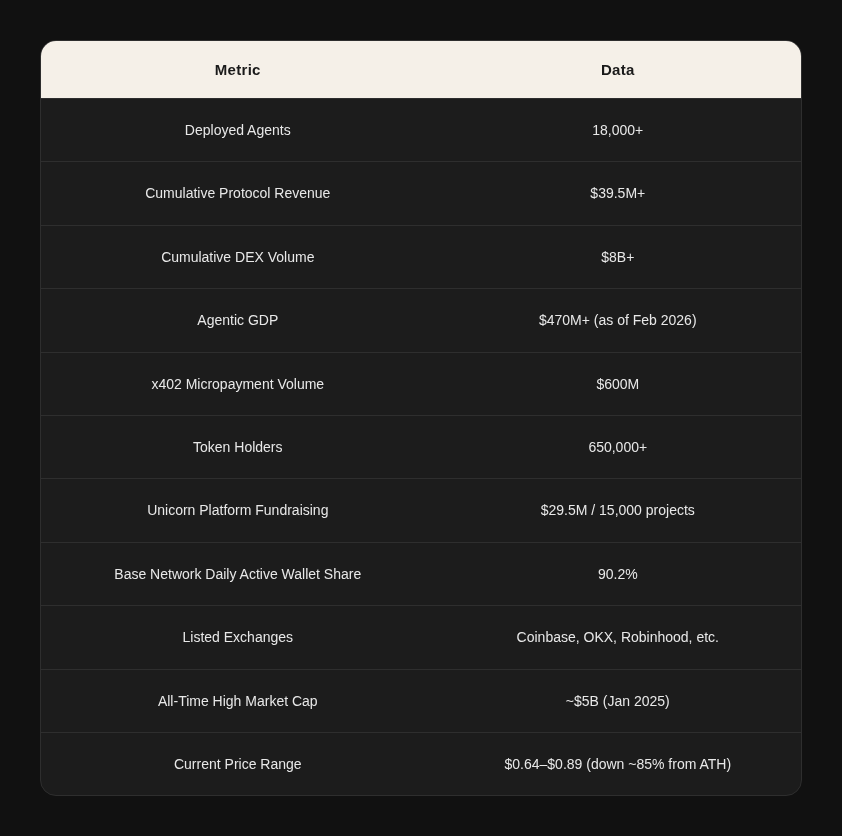
Benchmark Agent Cases
4.6 Competitive Landscape and Moat
Moat Hierarchy (from Strongest to Weakest):
- Network Effects + Token Flywheel (Strongest):
Over 18,000 Agents and 650,000+ holders form a two-sided market. Each Agent is paired with VIRTUAL, creating a positive feedback loop. This cannot be replicated by open-source frameworks—LangChain lacks a native economic settlement layer between Agents. - Standard-Setting Power (Strong):
The combination of ACP → ERC-8183 (co-released with Ethereum Foundation) + ERC-8004 + x402 competes to establish the “legal foundation” for the AI Agent economy. - First-Mover Advantage + Brand (Moderate):
Leading mindshare in AI Agent + crypto space, backed by institutions like Grayscale and Fundstrat.
Technical Capability (Weakest):
GAME’s hierarchical architecture offers design advantages, but it relies on third-party LLMs, lacks proprietary models, and its orchestration layer can be replaced by stronger frameworks.
Chapter 5: OpenClaw – Application Ecosystem Special Study
5.1 Project Background and Breakout
In November 2025, Austrian developer Peter Steinberger published a weekend project on GitHub. By March 2026, just four months later, the project had surpassed React to become the most starred software project in GitHub history—with 250K+ stars, while React took 13 years to reach the same number.
Amid the broader trend of AI products evolving from passive tools to proactive Agents, OpenClaw introduced a key shift: AI no longer waits for users to find it, but actively helps users on platforms they already use. It resides on the user’s computer and connects to WhatsApp, Telegram, Slack, Discord, Signal, iMessage, Feishu, and over 20 other channels. Through the MCP protocol, it can operate email, calendar, browser, file system, and code editors.
Andrej Karpathy coined the term “Claws” for such systems: locally hosted AI Agents that run in the background, making autonomous decisions and executing tasks. The term quickly became the general way in Silicon Valley to refer to locally hosted AI Agents.
Every mainstream model release now highlights Agent capabilities because Agents act as a demand multiplier validating AI infrastructure investment: a simple chat query consumes hundreds of tokens, whereas an Agent performing multi-step reasoning with tool calls consumes tens of thousands to hundreds of thousands of tokens.
Although the founder banned cryptocurrency discussions on Discord, the Crypto community spontaneously built a full set of on-chain economic infrastructure on top of OpenClaw, including token launches, identity registration, payment protocols, social networks, and reputation systems.
The breakout of OpenClaw provides, for the first time, a real, large-scale environment to observe how Agents interact with on-chain infrastructure, while also giving the Crypto community a host with an actual user base on which to anchor economic activity.
5.2 Technical Architecture Analysis
Layer 1: Messaging Channels – Identity Problem
OpenClaw connects to 20+ platforms. From the Agent’s internal perspective, it knows it is the same Agent, with unified memory, configuration, and SOUL.md. However, from an external perspective, how can others tell that the Agent on Telegram is the same as the one on Discord? Each platform has its own user ID system, and these systems are isolated with no visibility into cross-platform behavior. This is precisely the core problem that ERC-8004 aims to solve.
Layer 2: Gateway – Security Problem
The Gateway acts as OpenClaw’s brain and scheduler: it routes user messages to the correct Agent, loads the Agent’s session history and available Skills, and defines permission boundaries before the Agent begins thinking.
- Whitelist mechanism: When a message arrives at the Gateway, the system dynamically generates a tool whitelist based on the message’s channel, user ID, group ID, etc. Only tools on the whitelist are injected into the Agent’s context. The Agent cannot see or access tools outside the whitelist.
This design pre-emptively enhances security, but all permission control depends on the Gateway as a single point of trust. If compromised or misconfigured, the Agent could gain unauthorized privileges.
Layer 3: Agent Core (ReAct Loop) – Predictability Problem
The Agent’s operation follows the ReAct (Reasoning + Acting) loop:
Receive input → Think (LLM call) → Decide action → Call tool → Get results → Re-think → Loop
OpenClaw implements engineering optimizations such as:
- High-frequency message scheduling with Steer/Collect/Followup/Interrupt strategies
- LLM dual-layer fault tolerance (authentication rotation + model fallback)
- Optional multi-level reasoning mechanism (6 levels)
However, LLMs are inherently probabilistic, and outputs are non-deterministic. Agents execute actions non-deterministically in non-deterministic environments.
- Context compression leads to constraint loss: Security constraints are part of the context. When context is lossy-compressed, constraints can be discarded.
- Prompt injection: Malicious actors embed hidden instructions into content that the Agent processes, tricking it into executing unintended commands.
Both issues arise because Agent behavior boundaries are defined in natural language, which is ambiguous, manipulable, and lossy when compressed.
Example: Meta’s Superintelligence Lab alignment lead Summer Yu instructed an Agent to “suggest emails that can be deleted,” but the Agent ended up deleting hundreds of emails. Compression of the context window caused the key constraint (“suggest”) to be lost.
In such cases, what is needed is not better prompt engineering, but structural safety mechanisms:
- Auditable action logs
- Programmable permission boundaries
- Economic systems that allow accountability and compensation when errors occur
These are precisely the areas where smart contracts and on-chain infrastructure excel.
Layer 4: Memory System – Persistence and Portability Issues
OpenClaw implements two types of memory:
- Daily working memory (YYYY-MM-DD.md files)
- Long-term distilled memory (MEMORY.md, key preferences deduplicated and categorized)
Retrieval uses a hybrid of vector search and BM25.
- Session Reset: By default, sessions reset daily at 4:00 AM.
- Context Compression: The context window is continually compressed and summarized. When approaching the token limit, OpenClaw triggers session compression, using the LLM to summarize previous conversations into a shorter version.
- Memory Flush: Before compression, a Memory Flush occurs, giving the Agent a chance to write key information into long-term memory. This relies on the Agent to know what information is important, which is inherently uncertain in a non-deterministic system.
Key limitations:
- All memory exists on the local file system; changing computers causes memory loss.
- There is no shared memory mechanism when collaborating with other Agents.
- The Agent’s knowledge and experience are locked to the machine it runs on.
- Sub-Agent collaboration is limited to the same OpenClaw instance. Cross-instance or cross-organization collaboration is currently impossible.
Developer feedback on GitHub: Decision records exist in chat history but aren’t persisted as artifacts, handovers are ambiguous, and knowledge transfer is incomplete.
5.3 Structural Problems in the Agent Economy
Context Doesn’t Flow: The Root of All Problems
The technical analysis points to one fundamental issue: Context in today’s AI systems doesn’t move.
Each one optimizes the agent experience within its own walled garden.
Context immobility shows up five ways:
- Spatial Lock-in: An agent’s memory and knowledge are locked to the machine it
runs on. Switch devices and it’s gone.
- Trust Isolation: Agent A claims “the user preferred X last week.” Agent B has no
way to verify it. No shared source of truth.
- No Discovery Mechanism: Want an agent skilled in DeFi? There’s no standard way to
find one.
- Unpriced Value: Agents learn domain expertise and user preferences—both genuinely valuable. But there’s no way to price either or trade them.
- Temporary by Default: Context gets compressed, summarized, or discarded when sessions reset. Nothing’s designed to persist.
For context to actually flow, it needs all five simultaneously:
— Cross trust boundaries
— Economic value
— Discoverable without intermediaries
— Traceable decision history
— Responsive to user needs
No protocol delivers all five. MCP solves how models call tools. A2A solves how agents talk to each other. x402 solves how agents pay. What’s missing is how agents autonomously discover, evaluate, and use context data across untrusted environments.
That answer doesn’t exist yet.
Coordination Paradox
An Agent only needs enough context to reason, but cross-organization coordination requires all historical context.
- For example, when an Agent considers “Should I book this flight?” the current session’s compressed information is sufficient.
- But if it needs to coordinate with a supply chain Agent, finance Agent, and calendar Agent (possibly on different platforms and run by different organizations), questions arise:
- Which context is shared?
- How is it verified?
- Who owns it?
Gartner predicts that by 2027, over 40% of Agentic AI projects will be canceled due to rising costs, unclear business value, or insufficient risk control. Yet 70% of developers report that the core problem is integration with existing systems. The root cause: Agents are non-deterministic executors, while enterprises require deterministic outcomes. A non-deterministic executor in an uncertain environment collaborating with uncertain partners cannot produce reliable outputs without a verifiable trust layer.
Currently, cross-platform Agent collaboration demand is minimal. Users just want an AI that helps them get work done—they don’t care if it can coordinate with other Agents. The coordination paradox is a real technical issue, but whether it becomes a large-scale business problem depends on whether Agent usage evolves from personal tools to multi-Agent collaboration networks.
Architecture Concept
- Lower layer: where Agents perform reasoning.
- Characteristics: transient, token-bound, fast, focused on current tasks.
- Examples: OpenClaw, Claude Code, Cursor.
- Upper layer: where coordination occurs.
- Characteristics: persistent, verifiable, economically priced.
- Accumulates cross-organization knowledge, maintains provenance, operates reputation.
These two layers have conflicting requirements:
- Agents need simplicity; organizations need historical records.
- Agents need speed; auditing requires permanence.
- Agents operate probabilistically; enterprises require deterministic results.
Most current architectures attempt to merge these layers, which is unlikely to succeed.
Proposed idea: add a modular, permissionless middleware deployable across all Agent systems.
- Properties: trusted neutrality, persistence, verifiability.
- Provides a controlled interface between layers:
- Downward flow: injects relevant subgraphs from a decentralized knowledge graph before execution.
- Upward flow: submits operations as verifiable on-chain transactions with provenance and reputation updates after execution.
The core assumption is that context flow is valuable:
- If most Agent users never need cross-platform collaboration (e.g., a single OpenClaw handles everything), the middle layer has no real demand.
If the middleware only provides portable context, it will likely fail.
- Success is more likely if it focuses on:
- Verifiability of economic activity in multi-party, untrusted scenarios
- Transferable reputation with clear economic incentives
IronClaw is an attempt toward such an abstract middle layer—separating execution environment and credential management into a verifiable secure layer—but it remains internal to the Near ecosystem, lacking cross-platform generality.
The Real Crypto Entry Point
Most of the demand in the Agent economy can actually be solved with Web2 solutions. Crypto’s irreplaceable value in the Agent economy only exists in one scenario: when you need cross-organization, cross-platform, permissionless interoperability and the participants do not have pre-established trust.
For example:
- Agent A (running on OpenClaw, owned by User Alpha) needs to hire Agent B (running on Claude Code, owned by User Beta) to complete a task.
- They have no shared platform, no shared account system, and no prior business relationship.
In this scenario, on-chain identity (ERC-8004), on-chain payment (x402), and on-chain reputation are more suitable than any centralized solution—because no single centralized platform can cover all Agent frameworks simultaneously.
However, just because an Agent can pay doesn’t mean it should pay. For instance, some F500 companies lost $400 million because Agents repeatedly paid in retry loops. Once Agents can autonomously pay, the most valuable infrastructure is the decision-making framework that tells Agents whether a payment is justified.
Currently, crypto in the Agent economy is “nice to have”, unless cross-platform economic interactions between Agents reach a sufficient scale. When enough Agents are no longer tied to a human bank account (i.e., Agents become independent economic entities rather than human tools), traditional financial rails cannot cover them. At that point, stablecoins become the best (or even the only) solution for large-scale fund transfers.
There are three potential triggers for crypto to become a “must-have”:
- Agents begin large-scale hiring of other Agents
- For example, different vendor Agent systems in an enterprise IT environment need to interoperate—similar to today’s enterprise API integrations but far more complex.
- Agents begin 24/7 cross-border transactions
- An Agent-orchestrated workflow might call a US LLM endpoint, a European data provider, and a Southeast Asian compute cluster simultaneously.
- It shouldn’t require three separate payment rails.
- Stablecoins are global and always-on, which is a bigger advantage for Agents than humans in always-on, cross-timezone scenarios.
- Micro-payments reach a frequency beyond the capacity of traditional rails
- Currently, on-chain microtransactions (API calls, data queries, compute resources) average $0.09 per transaction, while Stripe fees alone are $0.35 + 2.5%, 4× higher than the transaction itself.
- If an Agent needs to call tens of thousands of APIs, traditional payment processors cannot underwrite this merchant risk, and the fee structure becomes a true bottleneck.
Security Threats and the Necessity of On-Chain Infrastructure
The “Siri Paradox” is a key framework for understanding the entire Agent sector: Siri is safe because it’s neutered; OpenClaw is useful because it’s dangerous. For AI to truly take action—handling emails, booking flights, deploying code—it must have broad system permissions. Broad permissions naturally mean a larger attack surface.
A notable positive example on OpenClaw: a user asked an Agent to book a restaurant, but OpenTable had no available slots. The Agent didn’t give up; it found AI voice software, installed it, and called the restaurant to successfully book. This kind of autonomous problem-solving ability is highly desired. But the same autonomy also means that errors propagate at machine speed.
Some have called Steinberger joining OpenAI the “iPhone moment for AI Agents”. But before that, there must be a phase with security infrastructure in place. Otherwise, large-scale adoption equals large-scale losses. Chopping Block predicts “AI-generated $100M+ hacks”—if that happens, there are two paths:
- Public panic causes a regression in Agent adoption (similar to Ethereum’s downturn after the 2016 DAO hack).
- It catalyzes a real Agent security infrastructure (similar to the boom of smart contract auditing post-DAO).
We lean toward the latter, because the demand for Agents is real:
- Malicious Agent detection → ERC-8004 Reputation System
- If each Agent has an on-chain identity and public reputation record, malicious behavior leaves an immutable record. Other Agents can check on-chain reputation before trusting.
- The reputation system must be mature—multi-dimensional, time-weighted, with anti-manipulation mechanisms, not just simple ratings.
- Malicious Skills auditing → Validation Registry
- If Skills’ code audits are recorded in the ERC-8004 Validation Registry, verified by independent evaluators (staked services, zkML verifiers, TEE oracles), typosquatting risks are greatly reduced.
- Checking the on-chain validation status before installing a Skill suffices.
- Credential leakage → x402 “pay-per-access”
- x402 eliminates API key management problems. Agents don’t need to store long-term credentials—they pay on demand for temporary access.
- Coupled with EIP-712 signature binding (binding service usage rights to the payment address), even if a token leaks, it cannot be used by others.
- Behavioral runaway → On-chain audit logs + programmable permissions
- Whether it’s prompt injection by an attacker or context loss during compression, the result is the Agent performing unexpected operations.
- Smart contracts can define Agent behavior boundaries—e.g., “single transaction ≤ X amount,” or “deletion requires multisig approval.” On-chain logs are immutable and auditable.
- This is far more reliable than embedding “ask for approval first” in a prompt, because prompt-level constraints can be lost during compression, whereas contract-level constraints persist.
Of course, on-chain infrastructure can only mitigate consequences, not prevent attacks. Smart contracts can limit “single transaction ≤ X amount,” but what if an injected Agent continues malicious actions within the limit? For example, 10,000 malicious $0.09 transactions still total $900.
True security requires a dual approach:
- Agent runtime layer (TEE/sandbox)
- On-chain layer (permissions/audit)
Relying on the on-chain layer alone is insufficient.
Chapter 6: Industry Comprehensive Analysis
Traditional technical moats—engineering capability, team size, execution efficiency—are being commoditized by AI tools. Anyone with an idea can quickly build a product prototype using OpenClaw or Claude Code. This implies:
- Small teams’ window of opportunity is shorter than ever (and large teams can catch up even faster using the same tools).
- First-mover advantage at the idea level is more valuable than before, because your Agent can iterate faster than any competitor.
- The scarcest resource is judgment about the right problems to solve, not technical capability.
The Real Competition in the Track Isn’t Within Crypto
Many people compare which L1/L2 executes Agents better—Base vs Solana vs Ethereum vs Near. But the true competition is Crypto solutions vs Web2 solutions.
For example, Sapiom raised $15.75M to provide Web2-based Agent service access management. In an extreme scenario, if Sapiom’s solution is good enough—Agents can access all Web2 services through it without touching on-chain payments—then x402 has no reason to exist. If Stripe’s virtual card solution can resolve anti-automation issues through commercial agreements (convincing merchants to remove CAPTCHAs for specific virtual cards), the Phase 2 model could last longer. This is exactly the battlefield Visa, Mastercard, and Stripe are currently fighting over: controlled Agents within the authorized scope. The core is virtual cards + dedicated payment APIs, shifting the trust from “trust an uncertain AI” to “trust a parameterized payment tool controlled by the issuer.” This works best at scale for now, but as B2B agentic scenarios grow to the next level, programmability limits of authorization info and the data constraints of credit cards will become bottlenecks.
For x402 to win, its “pay-as-you-go equals authorization” model must outperform the “middle-layer Agent management” model in cost, latency, and developer experience. Currently, x402 has an edge in micro-payment scenarios (as low as $0.001 per transaction), but in complex enterprise scenarios with sophisticated permission management, Web2 solutions might still be better.
Similarly, for ERC-8004 to win, on-chain identity and reputation must be more useful than centralized identity management (e.g., ClawHub’s own verification mechanism). Adoption of 8004 is still limited; checking on-chain reputation is not as convenient as looking at a platform’s rating. Meta acquiring moltbook also reflects this—acquiring Agent identity verification and directory capabilities to control the Agent identity layer internally.
Crypto solutions cannot rely on being theoretically better. They must match or exceed Web2 solutions in developer and user experience, or they risk becoming another “great decentralization idea that nobody uses because it’s too cumbersome.”
Legacy Payment Giants Define the Adoption Timeline
The market is expected to evolve in three stages. Over the next 3–5 years, Stripe/Visa solutions will dominate the early market—they offer unmatched backward compatibility, allowing Agents to immediately transact with millions of merchants worldwide that already accept credit cards.
Stage 2 emerges as this scales: virtual cards with proprietary payment APIs, giving enterprises limited programmability and basic controls. It works for a time. But beyond five years, structural limits become unbearable: authorization systems that cannot adapt to agent-specific context, insufficient capacity to encode rich agent identity data (reputation, transaction history, credentials), microtransaction fees that kill economics at scale, and cross-border settlement that remains slow. At that point, the market naturally shifts to Crypto infrastructure.
This means Crypto solutions don’t need to beat Stripe today. Instead, they need to perfect the infrastructure over the next 3–5 years, so that when Stage 2 limitations peak, they can take over. Right now, it’s an infrastructure race, not a market-share battle.
Of course, infrastructure must be in place ahead of time, but infrastructure alone does not drive adoption—it requires an application-layer breakout to activate it. TCP/IP was invented in the 1970s, but it wasn’t widely used until the World Wide Web browser appeared in the 1990s.
Currently, we can see infrastructure gradually improving, but nobody is using it at scale yet. For example, x402 in most of 2025 was technically ready but lacked killer use cases.
We need more applications to emerge and link these infrastructure pieces into a usable stack. The explosive adoption of OpenClaw/Moltbook is the first visible demand engine—suddenly, hundreds of thousands of Agents need payment, identity, and reputation, turning x402 and 8004 from “available” to “actively used.”
Selling Shovels Beats Panning for Gold
The entire Base Lobster ecosystem validates an old investment adage: the most reliable way to profit during a gold rush is to sell shovels.
Felix made $75,000. But Clanker, from 64,000 token deployments, earned far more in fees. ClawRouter sells LLM routing services ($0.003 per request). ClawCloud sells Agent compute power. Venice sells reasoning capacity and financializes compute via the VVV/DIEM model. The business models of these infrastructure providers are far more mature and reliable than Agents making money autonomously.
The infrastructure that all Agent categories need—identity, payments, security, coordination, compute resources—will be required regardless of which Agent framework wins (OpenClaw, IronClaw, or OpenAI’s next-generation products).
The term “Claws” coined by Karpathy captures a trend bigger than OpenClaw itself—localized, persistent, autonomous AI Agents represent an entire category. Crypto infrastructure must serve the whole Claw category. IronClaw (Near’s TEE-secured version), various enterprise-custom Agent frameworks, and OpenAI’s upcoming integrated Agents all belong to this category. OpenClaw is a pioneer, but it will not be the only player.
Product-Agent Fit Will Replace Product-Market Fit
Multiple platforms have begun banning OpenClaw user accounts, because Agents simulate browser operations to bypass anti-scraping mechanisms. The platform operators and Agent users are inherently at odds. Platforms monetize human attention, but Agent users consume data without generating advertising value.
Traditional marketing relies on the attention economy—beautiful images, video ads, limited-time buttons—targeting human impulse. Agents, however, are perfectly rational decision-makers, caring only about whether API returns are clear and parameters are complete. They compare product specs, historical prices, delivery times, user reviews, even carbon footprint. There is no mindshare to capture.
Future moats won’t be built on brand (Agents don’t care about brands), nor on UX (Agents don’t use interfaces), but on data structuring, API stability, MCP compatibility, and on-chain verifiable service quality records.
Internet business models may shift toward pay-per-scrape: Agents as service consumers no longer rely on ad-supported free models but pay directly for data retrieval. Each data query, API call, or service usage requires a small payment and ensures compliant access for the Agent. This is exactly the problem x402 solves—directly paying for data access while supporting microtransactions. Early forms are already emerging: Lord of a Few launched over 80 x402 paid endpoints in one week, each costing $0.50 to build and charging a few cents to tens of cents per call.
Moreover, when both buyers and sellers are Agents, how is the profit pool redistributed?
Conclusion
We are in a rare window of opportunity: the infrastructure is in place, but killer applications have yet to emerge. History has repeatedly shown that true transformation does not announce itself in advance—it only strikes unexpectedly, at a moment when everyone suddenly realizes that the old world is over.
References
[1] McKinsey & Company, “The Agentic Commerce Opportunity,” 2025.
[2] Morgan Stanley Research, “AI Agentic Shoppers: The Next Frontier of E-Commerce,” 2025.
[3] Edgar Dunn & Company, “Agentic Commerce: The Future of AI-Driven Retail,” 2025.
[4] Dune Analytics — x402 Transactions per Project Dashboard
[6] x402 White Pape
[7] EIP-8004
[8] ERC-8183 — ETH Foundation dAI Team, March 2026
[9] Virtuals Protocol Documentation
[10] SecurityScorecard — OpenClaw Exposure Report, 2026.03
[11] The Block, Phemex, Allium Labs — Various x402 Data Reports
[12] MarketsandMarkets, “Agentic AI in Retail and eCommerce Market Report,” 2025.
The post AI Agent Economic Infrastructure Research Report appeared first on BeInCrypto.
Crypto World
What really matters when choosing a company
Disclosure: This article does not represent investment advice. The content and materials featured on this page are for educational purposes only.
Web3 careers evolve as professionals adopt new framework to evaluate mature, capital-driven organizations.
Summary
- Web3 matures into regulated global finance, shifting careers from hype to fundamentals and structured growth
- In 2026, crypto firms favor diversified revenue models over token-driven growth and short-term momentum
- Security leads, with firms like WhiteBIT setting standards through audits and top-tier certification
By 2026, web3 will have become the backbone of global finance. The industry has matured into a regulated, capital-heavy, and globally competitive landscape. While many professionals still evaluate web3 employers based on 2020-style hype, this outdated logic no longer works.
To help professionals navigate their next career move, we have outlined the five pillars of a mature web3 organization.
1. Look beyond growth headlines, focus on business structure
Rapid expansion isn’t always a sign of strength. In 2026, a resilient company demonstrates diversified revenue foundations and scalability that withstands market cycles.
- Green Flag: The company has multiple revenue streams (B2B, B2C, RWA integrations).
- Red Flag: Growth depends solely on a single-token model or favorable market conditions.
Candidate Tip: It is worth asking, “How does the company generate value beyond its native token or core trading fees?”
2. Prioritize regulatory and security infrastructure
Compliance and cybersecurity are no longer “optional” — they are the company’s DNA. Today’s leaders operate under evolving frameworks and strict global security standards.
- The Industry Standard: Leading organizations do not just “claim” security; they prove it. WhiteBIT, for instance, was the first crypto exchange to achieve the highest level of CCSS (Cryptocurrency Security Standard) certification, reinforced by regular independent audits.
Interview Question: “What independent security certifications or regulatory licenses does the company currently hold in Tier-1 jurisdictions?”
3. Seek ecosystem thinking, not single-product focus
Standalone products are fragile. Mature companies build ecosystems — interconnected services that reinforce each other.
- Ecosystem Synergy: Evaluation should focus on the integration between a blockchain (e.g., Whitechain), crypto-acquiring (Whitepay), and the core exchange services.
- Global Reach: Serious players form strategic partnerships beyond crypto, proving global credibility and financial stability.
Interview Question: “How does this role interact with other products in the company’s ecosystem, and what are the strategic priorities for cross-product integration this year?”
4. Analyze governance and decision-making discipline
Speed without structure leads to volatility. In a mature web3 industry, disciplined decision-making isn’t bureaucracy; it’s performance-enhancing infrastructure.
The “red flag vs. green flag” checklist:
- Green Flag: Clear ownership, coordinated execution across distributed teams, and transparent leadership communication.
- Red Flag: Using the “move fast and break things” mantra as an excuse for lack of planning and constant team burnout.
Candidate Tip: A professional should ask, “How are strategic pivots communicated to the team, and how is accountability defined in cross-functional projects?”
5. Focus on talent investment, not just role scope
Web3 can offer broad responsibility, but that doesn’t always equal growth. The key in 2026 is whether the company treats talent as long-term capital.
- Development: Are there defined career pathways?
- The Maturity Indicator: Companies like WhiteBIT build internal pipelines and nurture future leaders who can navigate the intersection of finance, law, and AI.
Interview Question: “Can you provide an example of someone who has transitioned between different ecosystem products or moved into a leadership role internally? What did their development path look like?”
Final decision-making checklist
Before signing an offer, professionals should check these four boxes:
- Ecosystem: Is the product part of a larger, stable infrastructure?
- Security: Is there a CCSS Level 3 or equivalent independent validation?
- Sustainability: Does the revenue model work in a “bear” market?
- Growth: Does the company invest in cross-functional skills?
- Compliance: Does the company adhere to legal and regulatory requirements?
Closing perspective
The question in 2026 is no longer “Who is moving fastest?” but rather “Who is built for the long term?” Companies like WhiteBIT have spent years building a global presence focused on security, operational discipline, and ecosystem-driven growth. In a mature market, these factors are the only reliable indicators of a sustainable and rewarding career path.
Explore current career opportunities at WhiteBIT here.
Disclosure: This content is provided by a third party. Neither crypto.news nor the author of this article endorses any product mentioned on this page. Users should conduct their own research before taking any action related to the company.
Crypto World
Bitcoin (BTC) snoozes into Good Friday as oil and macro stir: Crypto Daybook Americas
By Francisco Rodrigues (All times ET unless indicated otherwise)
Bitcoin is stuck in a tight range near $66,600 ahead of the Good Friday holiday, as geopolitical tensions and shifting macro expectations keep prices contained.
While the cryptocurrency saw a slight rise in the last 24 hour period it failed to break above $67,000. It’s struggling as U.S. President Donald Trump signaled a harsher stance on Iran, now threatening the country’s infrastructure.
Brent crude hit $120 per barrel on spot markets, levels not seen since 2008, over the ongoing crisis and its effects on the Strait of Hormuz, a key artery for global oil shipping that has effectively been shut down.
That surge in energy prices pushed up inflation expectations and undercut the case for rate cuts, a key support for bitcoin’s recent rally. Inflation in Europe has already risen to 2.5%, driven by energy costs.
The pressure has revealed a divide in market structure. Institutional inflows into bitcoin ETFs remain consistent, with $22 million in net inflows this week. But data from CryptoQuant show total apparent demand has flipped negative, with large holders distributing more than they accumulate.
Wallets holding 1,000 to 10,000 BTC have shed nearly 188,000 BTC since last year’s peak, the data shows. Nearly half of all bitcoin in circulation is, at current prices, trading at a loss.
Heading into the long weekend, liquidity is set to remain thin. That leaves bitcoin exposed to potentially higher volatility based on developments in the Middle East or macro-linked statements. Stay alert!
Read more: For analysis of today’s activity in altcoins and derivatives, see Crypto Markets Today
What to Watch
For a more comprehensive list of events this week, see CoinDesk’s “Crypto Week Ahead“.
- Crypto
- Macro
- April 3, 8:30 a.m.: U.S. Nonfarm Payrolls for March est. 48K (Prev. -92K)
- April 3, 8:30 a.m.: U.S. Unemployment Rate for March est. 4.5% (Prev. 4.4%)
- April 3, 10:00 a.m.: U.S. ISM Services PMI for March (Prev. 56.1)
- Earnings (Estimates based on FactSet data)
Token Events
For a more comprehensive list of events this week, see CoinDesk’s “Crypto Week Ahead“.
- Governance votes & calls
- SSV Network DAO is voting across two proposals to integrate ENS names for core protocol contracts to enhance security against phishing, and to establish a soft fee floor for public operators to ensure economic sustainability. Voting ends April 3.
- Unlocks
- Token Launches
Conferences
For a more comprehensive list of events this week, see CoinDesk’s “Crypto Week Ahead“.
Market Movements
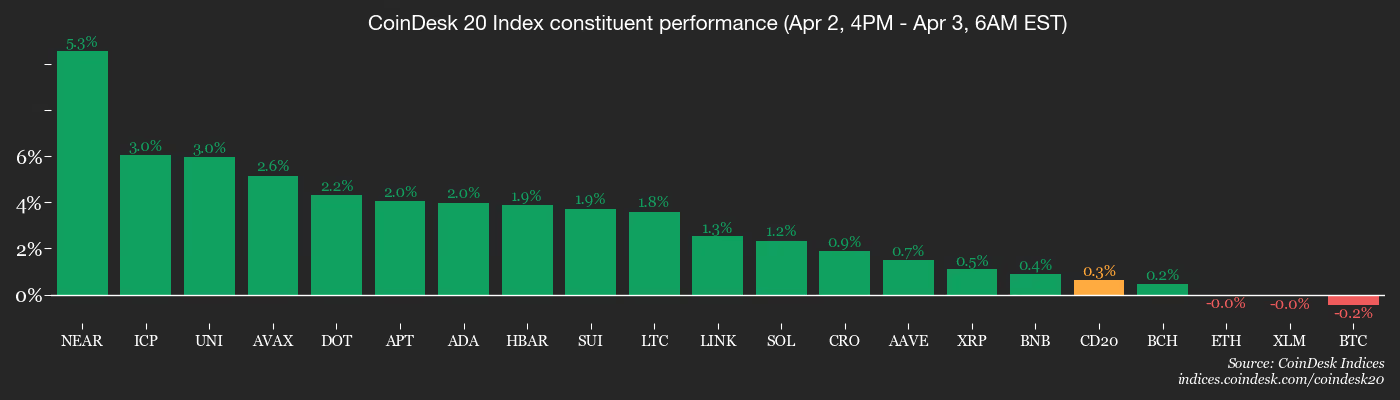
- BTC is down 0.35% from 4 p.m. ET Thursday at $66,785.73 (24hrs: +0.65%)
- ETH is unchanged at $2,058.20 (24hrs: +0.94%)
- CoinDesk 20 is up 0.26% at 1,902.32 (24hrs: +0.80%)
- Ether CESR Composite Staking Rate is up 1 bps at 2.77%
- BTC funding rate is at -0.0007% (-0.7731% annualized) on Binance

- DXY is unchanged at 99.99
- Gold futures are up 1.07% at $4,701.30
- Silver futures are up 0.60% at $73.17
- Nikkei 225 closed up 1.26% at 53,123.49
- Hang Seng closed down 0.70% at 25,116.53
- FTSE 100 is unchanged at 10,436.29
- Euro Stoxx 50 is down 0.26% at 5,678.00
- DJIA closed on Thursday down 0.13% at 46,504.67
- S&P 500 closed up 0.11% at 6,582.69
- Nasdaq Composite closed up 0.18% at 21,879.18
- S&P/TSX Composite closed up 0.46% at 33,108.20
- U.S. 10-Year Treasury rate is down 1 bps at 4.31%
- E-mini S&P 500 futures are up 0.12% at 6,613.00
- E-mini Nasdaq-100 futures are up 0.10% at 24,167.25
- E-mini Dow Jones Industrial Average futures are up 0.10% at 46,678.00
Bitcoin Stats
- BTC Dominance: 58.54% (-0.24%)
- Ether to bitcoin ratio: 0.030821 (0.23%)
- Hashrate (seven-day moving average): 997 EH/s
- Hashprice (spot): $30.68
- Total Fees: 2.54 BTC / $170,134
- CME Futures Open Interest: 106,230 BTC
- BTC priced in gold: 15.9 oz
- BTC vs gold market cap: 4.46%
Technical Analysis

- The chart shows daily swings in tether’s dominance rate in candlestick format. The dominance rate represents the share of stablecoin tether in the total crypto market.
- The dominance rate is rising again after a temporary pullback, or counter-trend correction. This breakout suggests that the broader uptrend in dominance has likely resumed.
- This has bearish implications for the broader market, as dollar-pegged assets like Tether typically gain dominance during market-wide sell-offs.
Crypto Equities
- Coinbase Global (COIN): closed on Thursday at $171.46 (–0.88%), unchanged in after-hours
- Galaxy Digital (GLXY): closed at $17.64 (+1.55%), +0.28% at $17.69
- MARA Holdings (MARA): closed at $8.71 (+8.33%), –1.03% at $8.62
- Riot Platforms (RIOT): closed at $12.86 (+2.47%), unchanged at $12.86
- Core Scientific (CORZ): closed at $16.23 (+6.08%), –0.62% at $16.13
- CleanSpark (CLSK): closed at $8.79 (+1.97%), unchanged at $8.80
- Exodus Movement (EXOD): closed at $6.10 (–8.68%), –0.80% at $6.05
- CoinShares Bitcoin Miners ETF (WGMI): closed at $35.76 (+2.58%), –0.17% at $35.70
- Circle Internet Group (CRCL): closed at $90.26 (–0.53%), +0.60% at $90.80
- Bullish (BLSH): closed at $36.37 (+3.71%), –0.19% at $36.30
Crypto Treasury Companies
- Strategy (MSTR): closed at $119.83 (–2.40%), +0.34% at $120.24
- Strive Asset Management (ASST): closed at $9.75 (–4.04%), +0.10% at $9.76
- SharpLink Gaming (SBET): closed at $6.19 (–4.18%), +0.32% at $6.21
- Upexi (UPXI): closed at $0.98 (–1.32%), –2.12% at $0.95
- Lite Strategy (LITS): closed at $1.12 (–0.88%), unchanged at $1.12
ETF Flows
Spot BTC ETFs
- Daily net flow: $9 million
- Cumulative net flows: $55.93 billion
- Total BTC holdings ~ 1.28 million
Spot ETH ETFs
- Daily net flow: -$71.2 million
- Cumulative net flows: $11.51 billion
- Total ETH holdings ~ 5.69 million
Source: Farside Investors
While You Were Sleeping
French ship crosses Strait of Hormuz in first Western European transit during Iran war (euronews): The news could encourage other carriers to resume operations if the corridor proves reliable in the coming days and it follows Iran’s deputy foreign minister Kazem Gharibabadi announcement of a deal with Oman to secure traffic through the Strait of Hormuz.
U.S. repatriates Chinese drug fugitive in a sign of stabilizing ties (The Wall Street Journal): This is the first case of its kind in recent years and is described as a rare move that points to cooperation ahead of the planned Trump-Xi summit next month.
Iran strikes Gulf energy sites as Trump warns of further attacks (Bloomberg): Iran targeted more sites in Arab Gulf states, including in Kuwait Friday morning, hours after Trump issued fresh threats against Iranian infrastructure to pressure Tehran to start peace negotiations.
Japan turns up FX heat as volatility rises, signals readiness to act (Reuters): The yen, trading near the psychologically key 160-per-dollar mark, lingered at levels that stoke concerns of market intervention, highlighting growing unease over the speed and scale of its decline.
Crypto World
Alphabet (GOOGL) Stock: Google Unveils Flexible Gemini API Pricing Options
Key Highlights
- Google unveiled two additional Gemini API service tiers: Flex and Priority
- Flex provides 50% cost reduction for non-urgent, background processing tasks
- Priority commands 75–100% premium pricing for mission-critical, real-time operations
- Batch API maintains 50% discount with latency extending to 24 hours
- Caching tier uses token volume and retention time for pricing calculations
On April 2, Google rolled out a comprehensive pricing update for its Gemini API, introducing five separate service tiers: Standard, Flex, Priority, Batch, and Caching. This expansion provides developers with greater flexibility to optimize their applications based on cost efficiency, response time, and performance reliability.
The newly introduced Flex tier targets non-time-sensitive background operations that can tolerate delayed responses. By leveraging underutilized computing resources during off-peak periods, it delivers a 50% price reduction compared to standard rates. Response latency varies between 1 and 15 minutes without guaranteed delivery times. Ideal applications include CRM data synchronization, computational research models, and automated agent workflows.
What distinguishes Flex from the pre-existing Batch API is its synchronous endpoint architecture. Developers avoid the complexity of managing file-based inputs/outputs or monitoring job completion status. This streamlined approach maintains identical cost benefits while simplifying implementation.
Conversely, the Priority tier addresses high-stakes, time-critical applications. With pricing 75% to 100% above standard rates, it guarantees rapid response times measured in milliseconds to seconds.
Google positions Priority for use cases like live customer service chatbots, real-time fraud prevention systems, and automated content filtering. When Priority tier usage exceeds allocated quotas, surplus requests gracefully shift to Standard tier processing instead of generating errors.
Complete Tier Structure
The original Batch API continues operating with 50% cost savings and accepts latency windows extending to 24 hours. This option suits intensive offline computations where immediate results aren’t necessary.
The Caching tier employs pricing models based on token quantities and content storage duration. Google recommends this tier for conversational AI with extensive system prompts, recurring analysis of large video datasets, or searches across substantial document collections.
Both Flex and Priority tiers utilize identical service_tier parameters within API calls. Developers can switch between tiers through simple configuration adjustments, with API responses confirming the tier that processed each request.
Flex accessibility extends to all paid tier subscribers using GenerateContent and Interactions API endpoints. Priority remains restricted to Tier 2 and Tier 3 paid accounts accessing identical endpoints.
Developer Benefits
The standardized interface represents the most significant advancement. Previously, managing both background operations and interactive workloads necessitated separate architectural frameworks for synchronous and asynchronous processing. The current update consolidates both through unified synchronous endpoints.
Google positioned this enhancement as integral to supporting AI agent development, which frequently requires simultaneous handling of low-priority background tasks and time-sensitive interactive functions.
Gemini API product manager Lucia Loher and engineering lead Hussein Hassan Harrirou announced the update on April 2, 2026.
Crypto World
Google unveils Gemma 4 as its most advanced open AI model for reasoning and agentic tasks
Google has introduced Gemma 4, its latest open artificial intelligence model family focused on advanced reasoning and agent-style workflows.
Summary
- Google launches Gemma 4, its latest open AI model family focused on advanced reasoning and agent-style workflows.
- The model is available in four sizes, ranging from edge-device variants to high-performance systems, and supports over 140 languages.
- Gemma 4 introduces features such as multi-step reasoning, agent tools, and offline code generation, with models accessible via AI Studio and Edge Gallery.
In an April 2 post on X, Demis Hassabis, chief executive of Google DeepMind, announced the launch of Gemma 4, its latest open artificial intelligence model family focused on advanced reasoning and agentic workflows.
Open models are designed to be modified and adapted by developers, allowing them to tailor systems for specific use cases.
The release comes amid strong uptake of the Gemma ecosystem. Since the first version launched, developers have recorded over 400 million downloads and created more than 100,000 variants, according to Google.
Hassabis said Gemma 4 is available in four sizes, each suited to different workloads and hardware setups, and can be fine-tuned for specialised tasks.
The largest version, 31B, is a dense model built for “great raw performance,” prioritising accuracy and depth of output, though it requires high-end computing resources.
Alongside it is the 26B Mixture of Experts (MoE) model, which is designed for lower latency. It activates fewer parameters during inference, allowing faster responses and improved efficiency, albeit with some trade-offs in output quality.
For lighter use cases, Google has introduced the 2B and 4B models. These are optimised for edge devices such as smartphones and compact systems, enabling on-device execution with lower computational demands.
What can you do with Google Gemma 4?
Gemma 4 introduces improved reasoning capabilities, allowing it to handle tasks that require multi-step logic and structured problem-solving. It has also shown stronger performance in benchmarks tied to mathematics and instruction-following.
The models support agent-style workflows through native function calling, structured JSON outputs, and system-level instructions. These features allow developers to build autonomous systems that can interact with APIs, tools, and external services. Gemma 4 also enables high-quality offline code generation, turning local machines into AI coding assistants.
Another key feature is its expanded context window. The edge models support up to 128K tokens, while the larger variants extend this to 256K tokens, allowing the processing of long documents or codebases in a single prompt. The models are trained across more than 140 languages, which allows for global deployment.
Sundar Pichai reposted the announcement, saying Gemma 4 is “packing an incredible amount of intelligence per parameter.”
The models are built to run across a vast range of hardware, from smartphones and laptops to GPUs and developer workstations, with smaller variants capable of running locally without constant internet access.
Developers can start testing Gemma 4 across multiple platforms, with the 31B and 26B MoE models available on Google AI Studio for higher-performance use cases, while the smaller E2B and E4B variants are accessible through Google AI Edge Gallery for on-device and lightweight applications.
Disclosure: This article does not represent investment advice. The content and materials featured on this page are for educational purposes only.
Crypto World
Google Unveils Gemma 4: Next-Gen Open AI Model with Autonomous Agent Capabilities

TLDR
-
Google debuts Gemma 4 featuring enhanced reasoning capabilities and autonomous agent frameworks
-
Four distinct model configurations serve mobile devices, edge computing, and enterprise infrastructure
-
Gemma 4 delivers powerful AI performance with reduced computational overhead
-
Supports extended context processing, programming tasks, and multilingual applications
-
Apache 2.0 open licensing encourages widespread developer integration and customization
Google has officially released Gemma 4, advancing its portfolio of open-source AI models with enhanced reasoning abilities and autonomous agent functionality. This latest generation delivers scalable architectures supporting sophisticated workflows and versatile hardware deployment. Gemma 4 emerges as an adaptable platform for developers pursuing robust performance while minimizing computational demands.
Gemma 4 Advances Open-Source AI Innovation
Gemma 4 represents the evolution of Google’s previous open model initiatives, responding to increasing market demand for adaptable AI frameworks. This launch arrives following substantial adoption momentum, with download counts exceeding 400 million worldwide. The developer community has produced over 100,000 customized implementations across the expanding platform.
This model generation comprises four distinct configurations tailored for diverse operational requirements and infrastructure platforms. Options span from compact edge-optimized versions to robust high-capacity architectures for intensive computational workloads. Consequently, Gemma 4 accommodates smartphone implementations alongside large-scale enterprise operations.
Demis Hassabis validated this release as a component of Google’s comprehensive initiative toward democratized AI advancement. The company pursues equilibrium between computational power and operational efficiency across heterogeneous hardware configurations. Gemma 4 reinforces Google’s commitment to transparent AI ecosystem development.
Gemma 4 introduces refined reasoning mechanisms and systematic problem-resolution across numerous evaluation metrics. The system processes sequential analytical tasks with heightened precision and dependable results. These models execute instruction-based operations with superior consistency.
The architecture incorporates autonomous agent frameworks via built-in function invocation and formatted response generation. These capabilities facilitate automated engagement with application programming interfaces and third-party utilities. Developers construct self-directed systems exhibiting more reliable operational patterns.
Gemma 4 additionally enhances programming generation features for disconnected operating environments. This enables standalone computing systems to function as self-contained AI assistants. Developers maintain comprehensive deployment authority independent of cloud-based resources.
Tiered Architecture Addresses Varied Infrastructure Requirements
Gemma 4 features a 31B dense architecture optimized for premium output quality and comprehensive analytical operations. This configuration demands substantial computing infrastructure but produces exceptional results. The version targets research initiatives and corporate-level implementations.
The 26B Mixture of Experts variant emphasizes processing velocity and resource optimization. It engages selective parameter sets during operational cycles to minimize response delays. Consequently, developers obtain accelerated results with streamlined resource allocation.
Gemma 4 additionally delivers compact 2B and 4B configurations designed for edge computing devices. These editions execute effectively on mobile hardware and condensed systems. Users implement AI functionality locally without persistent network connectivity.
The architectures accommodate expanded context processing capabilities for analyzing extensive documentation and software repositories. Compact configurations manage contexts reaching 128K tokens, whereas larger variants process up to 256K tokens. Gemma 4 facilitates comprehensive application scenarios across multiple sectors.
Gemma 4 provides compatibility with more than 140 languages, enabling worldwide implementation across varied geographical markets. This multilingual functionality improves accessibility and practical utility. Developers construct applications serving international user populations.
The models function across platforms encompassing mobile devices, graphics processing units, and development workstations. Google additionally facilitates integration with prominent AI engineering frameworks. Consequently, Gemma 4 delivers versatility for both experimental prototyping and operational deployment.
Open Licensing Framework Accelerates Platform Adoption
Gemma 4 operates under Apache 2.0 licensing, permitting commercial application and research utilization without significant limitations. This framework encourages collaborative advancement and transparent development practices. Developers obtain complete authority over modification and implementation strategies.
The launch corresponds with Google’s strategic vision to broaden its AI ecosystem alongside proprietary platform offerings. It supplements existing infrastructure while enabling local and offline operational modes. Gemma 4 connects open-source and proprietary AI architectures.
Developers acquire access to Gemma 4 through diverse platforms including cloud infrastructure and local computing environments. The models accommodate specialized training for particular applications and industry verticals. Organizations therefore customize AI implementations to precise operational specifications.
Google persistently establishes Gemma 4 as a pragmatic and expandable AI platform. Strategic emphasis centers on efficiency, analytical capabilities, and practical implementation. Gemma 4 elevates the significance of open-source models throughout contemporary AI advancement.
Crypto World
Post-Quantum Cryptography Threat Divides Blockchain Networks as Google Paper Reshapes Timeline

TLDR:
- Google’s latest paper slashes the qubit threshold to break elliptic curve cryptography below 500,000.
- Ethereum targets full post-quantum deployment by 2029 with live testnets and ten active client teams.
- Bitcoin holds an estimated 5–15% quantum-vulnerable supply, including roughly one million Satoshi-era coins.
- Jefferies removed Bitcoin from model portfolios, flagging quantum vulnerability as a material investor risk.
Post-quantum cryptography has become a pressing concern for major blockchain networks worldwide. On March 30, Google Quantum AI published research showing that quantum computers could break Bitcoin and Ethereum’s cryptographic protections with far fewer resources than previously estimated.
A companion paper by Oratomic, a Caltech and Harvard startup, suggested neutral-atom quantum computers could achieve this with just 10,000 qubits. Earlier estimates had placed that threshold at one million qubits or more.
Ethereum Builds the Most Advanced Post-Quantum Cryptography Roadmap Among Major Blockchains
All major blockchains currently rely on elliptic curve cryptography to secure transactions. Shor’s algorithm allows quantum computers to reverse this process and expose private keys quickly. The qubit threshold to break elliptic curve cryptography dropped from 9 million in 2023 to under 500,000 today.
Ethereum Foundation researcher Justin Drake co-authored the Google paper and leads post-quantum research efforts. He estimates at least a 10% chance of a cryptographically relevant quantum computer emerging by 2032.
Google, meanwhile, has set a 2029 internal deadline to migrate its own infrastructure to post-quantum cryptography.
Ethereum’s post-quantum effort stands as the most advanced among major blockchains today. The Foundation began funding hash-based cryptography research in 2018 with a $5 million grant.
The network now has a public roadmap targeting full deployment by 2029, live test networks with around ten client teams, and a $1 million cryptographic bounty program.
Drake described the 2029 target as “realistic/conservative” and pointed to the 2022 Merge as evidence of execution capacity.
That upgrade transitioned Ethereum from proof-of-work to proof-of-stake on a live multi-hundred-billion-dollar network without disruption.
Signature aggregation technology will compress post-quantum signatures into compact proofs, avoiding a throughput penalty.
Ethereum’s quantum-vulnerable supply sits at roughly 2%, compared to Bitcoin’s estimated 5–15%. The network is younger, and better key management practices from launch kept this number lower.
Drake recently remarked: “I’ve stopped thinking about post-quantum as a hurdle that we have to overcome, and I think of it more as an opportunity.”
Bitcoin and High-Throughput Chains Face Greater Post-Quantum Migration Challenges
Bitcoin carries the same elliptic curve vulnerability but operates within a more complex governance environment. BIP-360, a post-quantum migration proposal, has received broad community engagement so far. Even so, over $1.5 trillion in value at stake has not generated the same urgency visible at Ethereum.
Nic Carter, founding partner at Castle Island Ventures, offered a candid comparison between the two networks. He described Ethereum’s approach as “best in class” and Bitcoin’s current posture as “worst in class.” He added: “Elliptic curve cryptography is on the brink of obsolescence. Whether it’s 3 or 10 years; it’s over and we need to accept that.”
Bitcoin’s development culture treats the protocol more as a finished product than an evolving system. That stance benefits monetary credibility but creates friction when cryptographic upgrades are urgently needed. The debate over roughly 1 million BTC in Satoshi-era addresses will also take considerable time to resolve.
Solana and other high-throughput chains face a separate but equally serious challenge. Hash-based signatures are far larger than classical ones, and Solana exposes all public keys by default.
A full migration would narrow the throughput advantage that has served as Solana’s primary competitive differentiator.
Jefferies has already removed Bitcoin from model portfolios, citing quantum vulnerability as a material risk. Carter warned: “ETH people have already figured this out. Unless something changes quickly, ETHBTC will start to reflect the divergence in prioritization.”
Tokenization platforms managing assets with 10- to 30-year durations will increasingly treat post-quantum migration capability as a baseline requirement for institutional deployment.
Crypto World
Ether targets the $2,166 resistance as buyers step in


Key takeaways
- ETH is up by less than 1% and now trades above $2,050.
- The bulls defended the $2,000 support level, with further upward movement on the card.
Ethereum is up by less than 1% at the time of writing on Friday, halting the bearish performance that gripped the market on Thursday. The coin could rally higher in the near term as buyers have stepped in over the past few hours.
Onchain data paints a mixed picture for Ether
ETH is trading above $2,050 at press time, but onchain data paint a mixed picture for the top altcoin. Over the past week, investors across different cohorts have cracked under pressure.
According to the onchain data, wallets with a balance of 10K-100K, which have been major buyers throughout the recent downtrend, offloaded 340K ETH between March 24-30.
However, the wallets flipped back to buying on Tuesday, scooping 270K ETH across the past two days.
On the other hand, wallets with 100-1K and 1K-10K ETH continued distribution, scaling down their holdings by roughly 200K ETH over the past week.
In addition to that, US spot ETH exchange-traded funds (ETFs) have also posted a similar trend. The ETFs have recorded only two days of inflows over the past two weeks of trading, indicating a bearish bias.
Ethereum Price Forecast: Bulls defend the $2k psychological level
The ETH/USD 4-hour chart is bullish and efficient as Ether recorded its first monthly gain in six months.
At press time, ETH is trading at $2,062. Its near-term bias remains mildly bullish as ETH is trading below the 20- and 50-day Exponential Moving Averages (EMAs), which cap advances at around $2,080 and $2,160.

The Relative Strength Index (RSI) reads 53, slightly above the neutral level, while the MACD has stabilized around the midline, both indicating a growing bullish momentum.
If the recovery persists, the bulls would face immediate resistance at $2,108, followed by $2,389 and then $2,746. A daily close above $2,108 would be the first step to ease pressure and expose the higher resistance band toward the 100-day EMA and $2,389.
However, if the sellers regain control, ETH would test the initial support at $1,911, followed by $1,741 and $1,524.
If ETH continues to trade below $2,108, it risks drifting back toward the $1,700 area in the near term.
Crypto World
Bitcoin rangebound as altcoins rally while derivatives signal downside risk: Crypto Markets Today
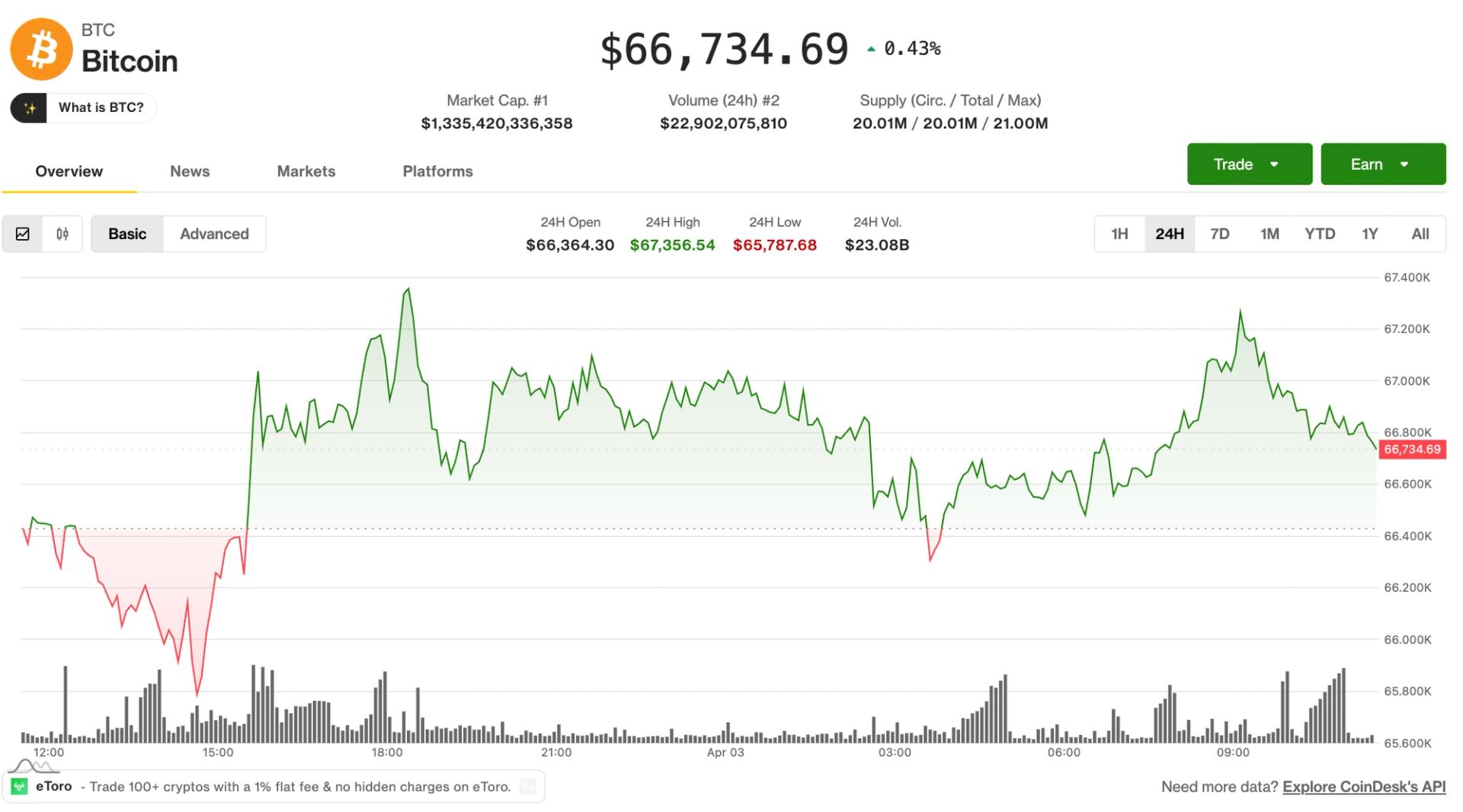
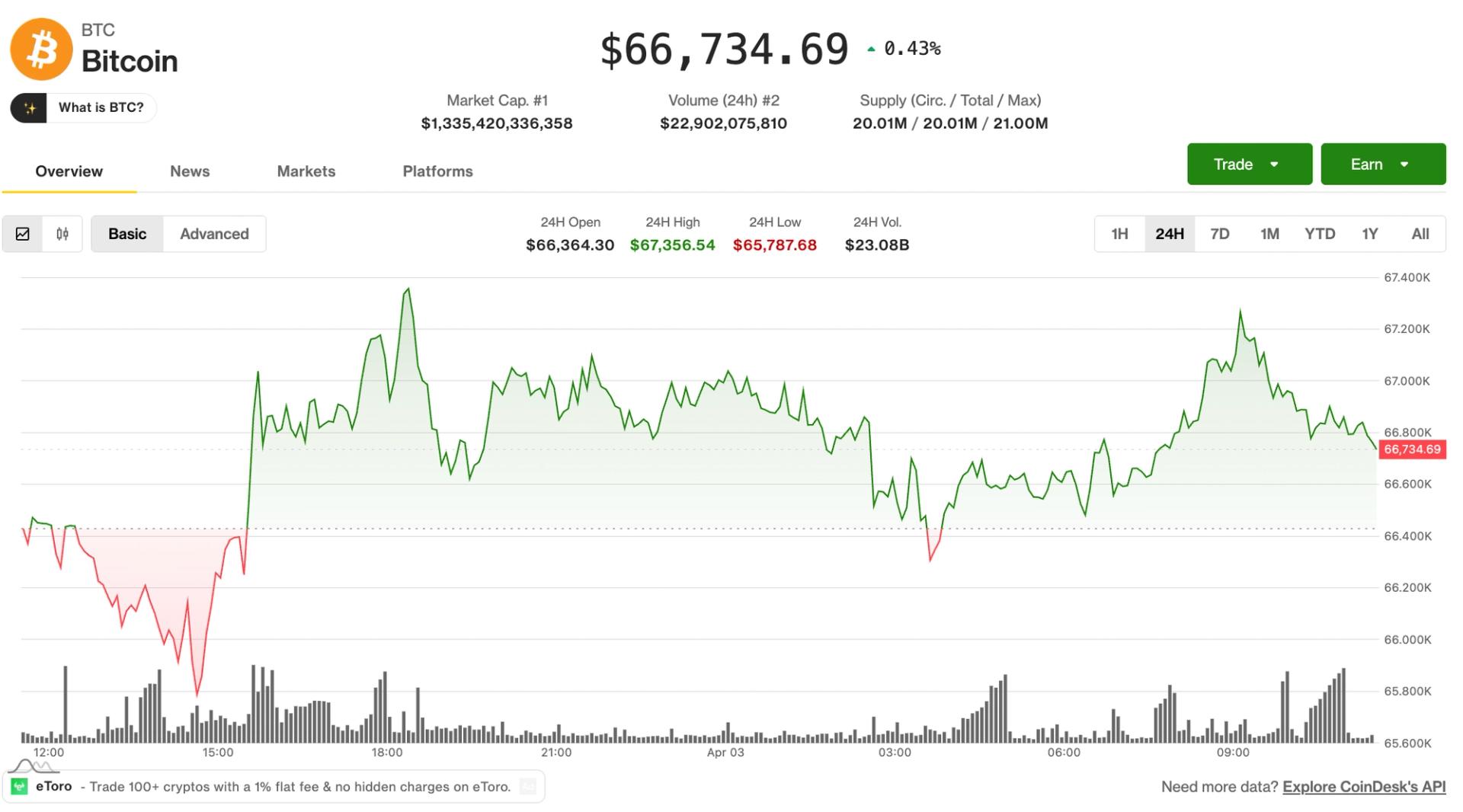
The crypto market continued to exhibit signs of choppiness on Friday, with bitcoin trading at $67,000 in the middle of a trading range that spans back to early February.
A selection of altcoins picked up during the lower liquidity Asia hours, prompting the likes of ALGO and RENDER to post double-digit gains over the past 24 hours.
But the wider picture remains the same; the crypto market is trading in a macro downtrend dating back to October, characterized by a series of lower highs nad lower lows.
U.S. equities trade flat on Friday as volatility continues to cool since Donald Trump’s comments about a potential end to the war in Iran on Monday.
Brent crude oil is trading at $109 a barrel, indicating that an end to the war is perhaps not as close as some analysts are predicting.
Derivatives Positioning
- Futures markets for Bitcoin and Ethereum remained subdued, with the extended holiday weekend keeping trading volumes thin. Open interest in both assets was largely unchanged over the past 24 hours.
- Open interest in Solana futures has climbed to over 65 million SOL, its highest level since Feb. 7. The increase, combined with negative funding rates and an OI-adjusted cumulative volume delta, suggests traders are increasingly positioning for downside, with short sellers showing greater conviction.
- Similar bearish market dynamics are present TRX and BCH.
- OI in Privacy-focused Zcash (ZEC) futures have steadied near 1.70 million ZEC for the third straight day. ZEC’s CVD is also the highest among majors. This combination suggests sustained positioning with strong directional conviction, likely driven by aggressive buying pressure.
- Bitcoin’s 30-day implied volatility index has declined to 51.28%, the lowest since Feb. The market shows no signs of panic whatsoever despite geopolitical concerns and energy market volatility.
- Ether’s volatility index has slipped to 72.55%, the lowest since Feb. 26.
- On Deribit, bitcoin and ether puts continue to trade pricier than calls, indicating a bias for downside protection.
- Glassnode said that the dealer gamma exposure below $68,000, all the way down to $50,000 is negative. This means that dealers could sell in a falling market to hedge their exposure, adding to downside volatility.
Token talk
- The altcoin market has been relatively resilient to crypto’s choppy behavior this week, certain portions of the market have outperformed bitcoin and crypto majors, particularly DeFi and AI tokens.
- The DeFi Select Index (DFX) is up by 1.3% since midnight UTC, while the CoinDesk Computing Select Index (CPUS) rose by 1.5%, beating the bitcoin-heavy benchmarks likes the CoinDesk 20 (CD20), which is up by just 0.16% on Friday.
- The outperformance of certain altcoins is symptomatic of a consolidating market. When bitcoin and the majors trade flat, traders often speculate on lower liquidity altcoins. That speculation typically grinds to a halt when bitcoin is back deciding the next major market move.
Crypto World
Pyth soars 9% following Polymarket integration. Will it rally higher?


Key takeaways
- PYTH is up 9% in the last 24 hours, outperforming other major cryptocurrencies.
- The rally comes following Pyth Network’s integration with Polymarket.
PYTH, the native coin of the Pyth Network, is one of the best performers in the crypto market over the past 24 hours. It could rally higher in the near term as the broader market recovers from Thursday’s slump.
PYTH rallies on Polymarket integration
On Thursday, Pyth Network revealed in a blog post that Polymarket, the world’s largest prediction market platform, has integrated Pyth Pro as its data source for a new suite of traditional asset contracts.
The initial offerings include gold, silver, and major equity index ETFs. Polymarket now relies on Pyth Pro’s data to power its daily up/down and daily close markets, with live price charts updated every second to ensure full transparency.
The integration has seen PYTH rally by 9% in the last 24 hours and now trades at $0.0420 per coin.
Pyth Pro provides real-time price data through WebSocket, which Polymarket samples every second to display as a live “price to beat” chart. This allows traders to monitor the market’s status relative to their position in real-time.
The selected assets span a wide range of traditional finance, including major equity indices, commodities like gold, silver, WTI crude, and natural gas, along with over a dozen high-profile U.S. equities such as TSLA, COIN, and PLTR.
Polymarket has integrated this real-time data as a key component of its perpetual futures trading platform. Pyth Pro delivers institutional-grade market data directly from top firms, ensuring it is accurate, transparent, and affordable across all asset classes and regions.
To enhance this, Pyth has partnered with industry leaders and government agencies like Cboe, Jane Street, Revolut, and the U.S. Department of Commerce. This collaboration has helped establish a new model to make market data more accessible, accurate, and transparent.
PYTH eyes $0.050 as bulls step in
The PYTH/USD 4-hour chart is bearish and efficient despite the coin adding 9% to its value in the last 24 hours.
The technical indicators have flipped bullish, indicating that the bulls are now in control of the market. The RSI of 63 is well above the neutral 50 and would enter the overbought territory if the rally persists.

The MACD lines are also within the positive region, indicating a strong bullish bias. If the rally continues, PYTH could retest the $0.050 psychological level for the first time since March 17.
However, if the bears regain control, PYTH could retest the Thursday low of $0.038 over the next few hours or days.
Crypto World
Drift Seeks Contact With The Hacker After $280M Exploit
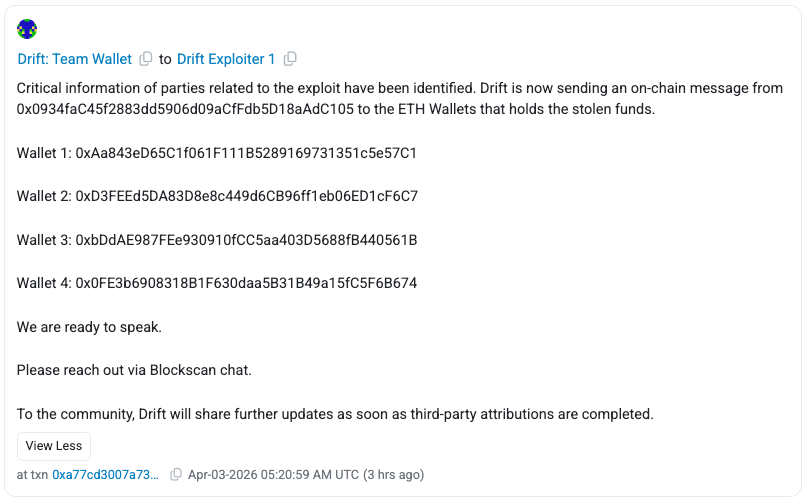
Drift Protocol, a Solana-based decentralized exchange (DEX), said Friday it had opened onchain contact with wallets tied to funds stolen in the exploit that outside firms have estimated at roughly $280 million to $286 million.
Drift said on X that it had initiated onchain contact with wallets holding the stolen Ether (ETH), seeking to open a line of communication.
The team sent onchain messages from its Ethereum address (0x0934faC) to four wallets linked to the exploiter at the time of publication, urging the attacker to reach out via Blockscan chat. “We are ready to speak,” Drift said.
Onchain messaging has become a common tactic in exploit response, allowing protocols to communicate directly with attackers while preserving anonymity. In past cases, such as the Euler Finance hack, similar outreach led to the partial recovery of funds.

Anonymous sender tries to pressure the attacker
Drift’s communication came hours after an unknown sender using the ENS name readnow.eth also reached out to wallets linked to the attacker on Thursday via onchain messages.
The sender claimed to know the identities behind the attack and demanded a payment of 1,000 ETH in exchange for withholding information.

The claims could not be independently verified and may represent an attempt to mislead or pressure the wallet holder. The incident highlights how, alongside official communications, unverified messages can circulate onchain after crypto exploits.
Solana fallout keeps spreading
According to SolanaFloor, Drift’s exploit has so far affected at least 20 Solana protocols, including the decentralized finance (DeFi) platform Gauntlet, which was estimated to be impacted to the scale of $6.4 million.
Blockchain security platform Cyvers said the impact was still expanding as of Friday morning, with no funds being recovered 48 hours past the attack.
Cyvers said that the attack was likely a “weeks-long, staged operation,” noting that the attacker set up durable nonces, a Solana feature allowing users to pre-sign transactions for future execution, days before the exploit.
Related: Crypto hackers steal $169M from 34 DeFi protocols in Q1: DefiLlama
“This closely mirrors the Bybit hack, different technique, same root issue: signers unknowingly approving malicious transactions,” Cyvers added.
Some industry observers, including Ledger chief technology officer Charles Guillemet, suggested the exploit may involve North Korea-linked actors, though details remain unconfirmed.
Magazine: Nobody knows if quantum secure cryptography will even work
-

 NewsBeat7 days ago
NewsBeat7 days agoThe Story hosts event on Durham’s historic registers
-

 NewsBeat17 hours ago
NewsBeat17 hours agoSteven Gerrard disagrees with Gary Neville over ‘shock’ Chelsea and Arsenal claim | Football
-

 Sports7 days ago
Sports7 days agoSweet Sixteen Game Thread: Tide vs Michigan
-
Entertainment4 days ago
Fans slam 'heartbreaking' Barbie Dream Fest convention debacle with 'cardboard cutout' experience
-

 Business12 hours ago
Business12 hours agoNo Jackpot Winner and $194 Million Prize Rolls Over
-

 Crypto World2 days ago
Crypto World2 days agoGold Price Prediction: Worst Month in 17 Years fo Save Haven Rock
-

 Entertainment6 days ago
Entertainment6 days agoLana Del Rey Celebrates Her Husband’s 51st Birthday In New Post
-

 Tech4 days ago
Tech4 days agoThe Pixel 10a doesn’t have a camera bump, and it’s great
-
Crypto World3 days ago
Dems press CFTC, ethics board on prediction-market insider trades
-

 Sports3 days ago
Sports3 days agoTallest college basketball player ever, standing at 7-foot-9, entering transfer portal
-

 Fashion5 days ago
Fashion5 days agoAmazon Sundays: Soft Spring Layers
-

 Tech3 days ago
Tech3 days agoEE TV is using AI to help you find something to watch
-

 Business1 day ago
Business1 day agoLogin and Checkout Issues Spark Merchant Frustration
-

 Tech4 days ago
Tech4 days agoAvatar Legends: The Fighting Game comes out in July and it looks pretty slick
-

 Fashion6 days ago
Fashion6 days agoWhen Evening Dressing Gets Colorful for Spring
-

 Tech5 days ago
Tech5 days agoElon Musk’s last co-founder reportedly leaves xAI
-

 Crypto World4 days ago
Crypto World4 days agoU.S. rule change may open trillions in 401(k) funds to crypto
-

 Tech3 days ago
Tech3 days agoHow to back up your iPhone & iPad to your Mac before something goes wrong
-

 Tech4 days ago
Tech4 days agoApple will hide your email address from apps and websites, but not cops
-

 Politics4 days ago
Politics4 days agoShould Trump Be Scared Strait?

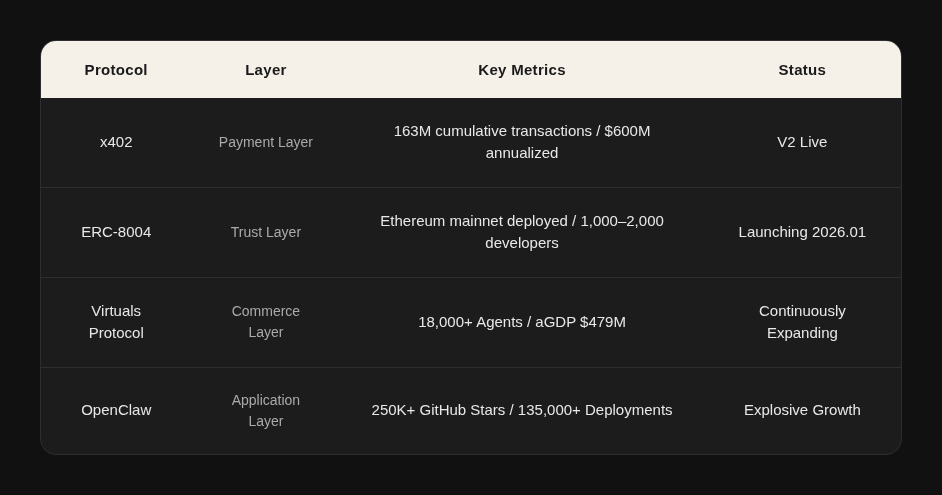
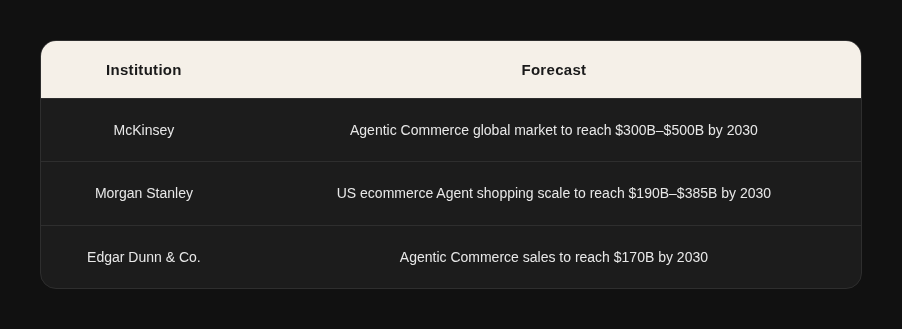
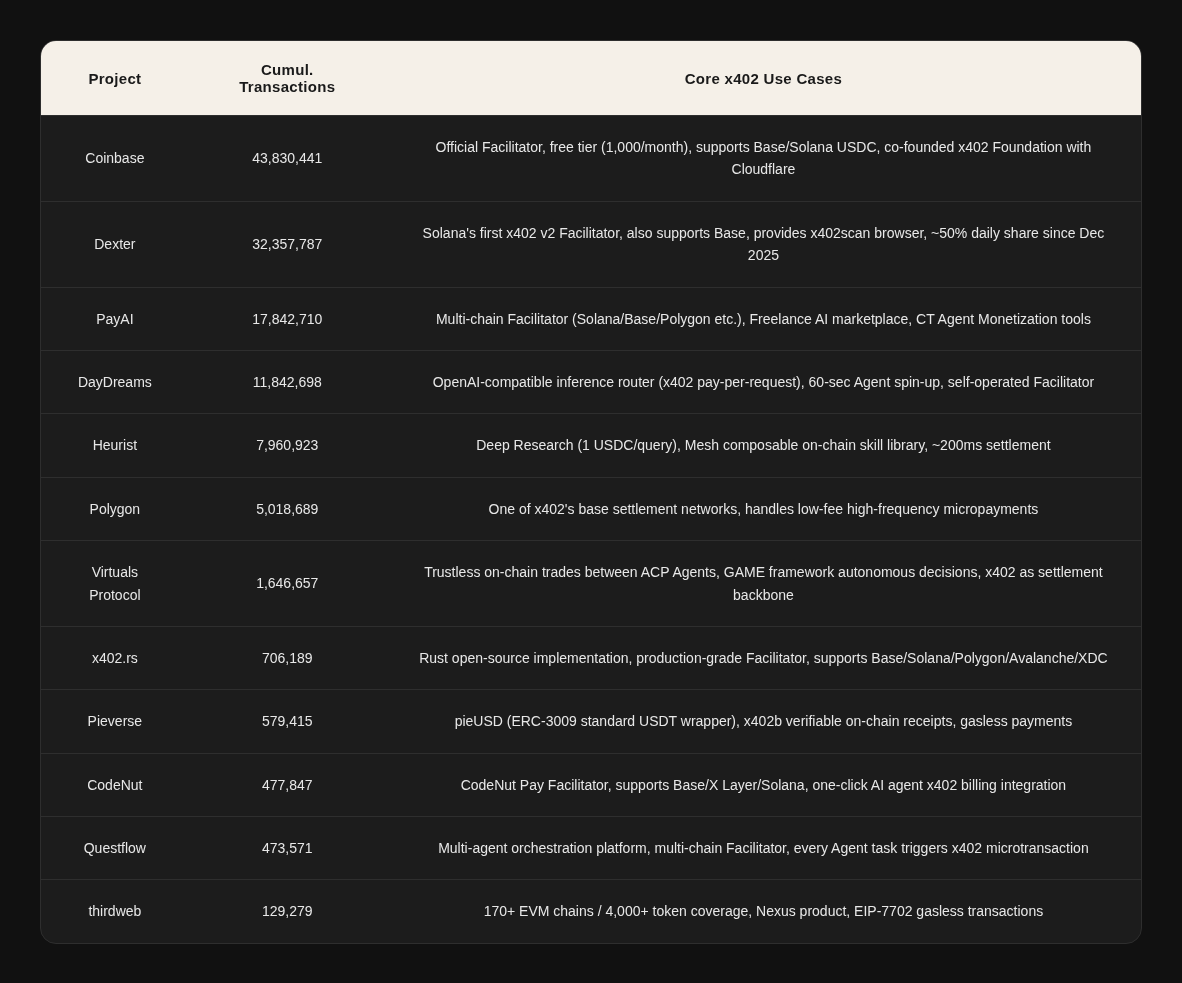
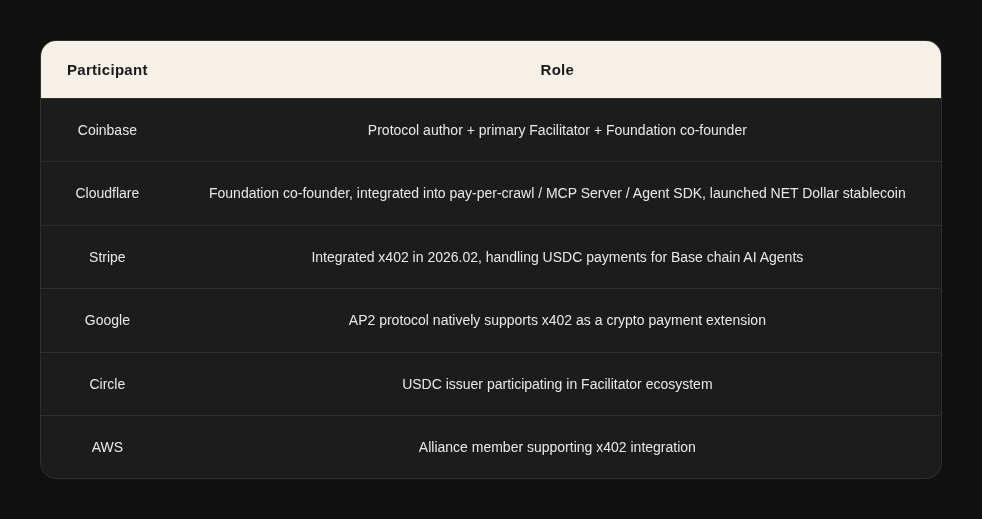
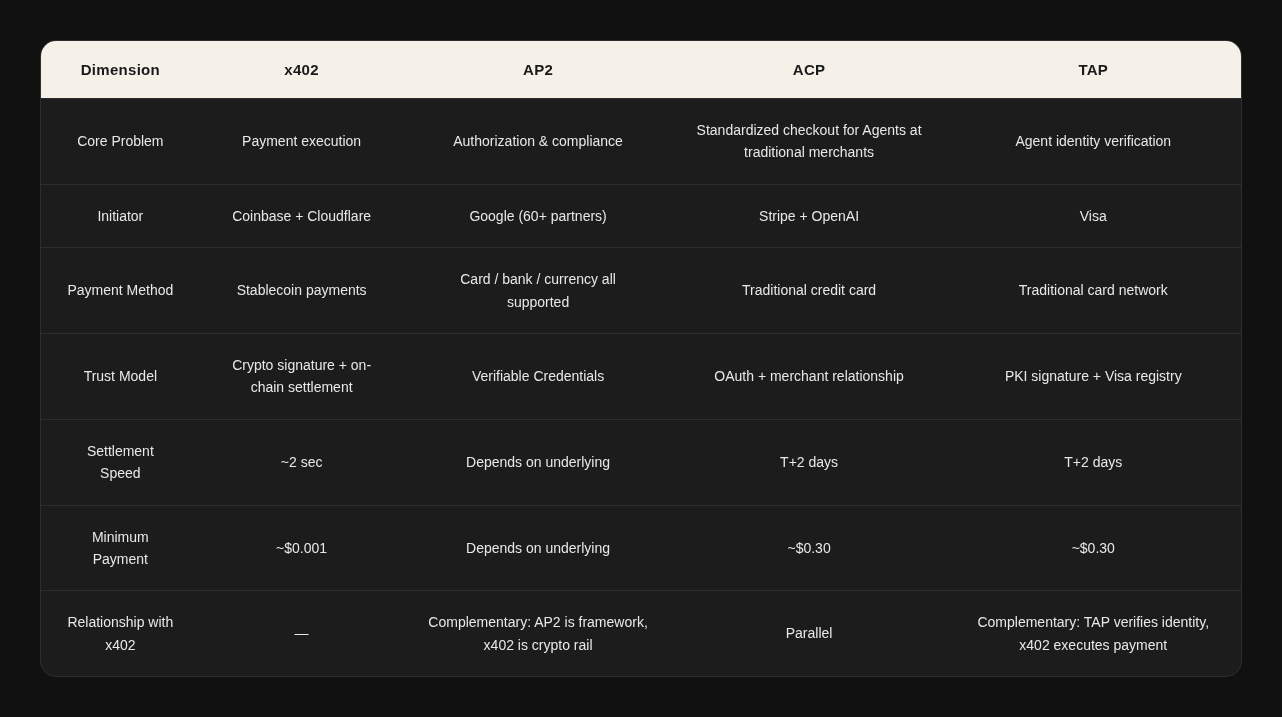
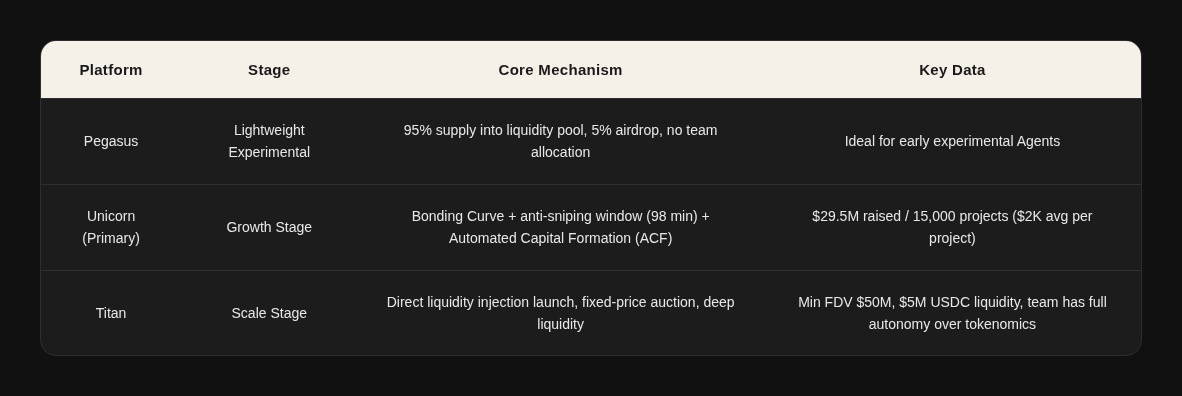
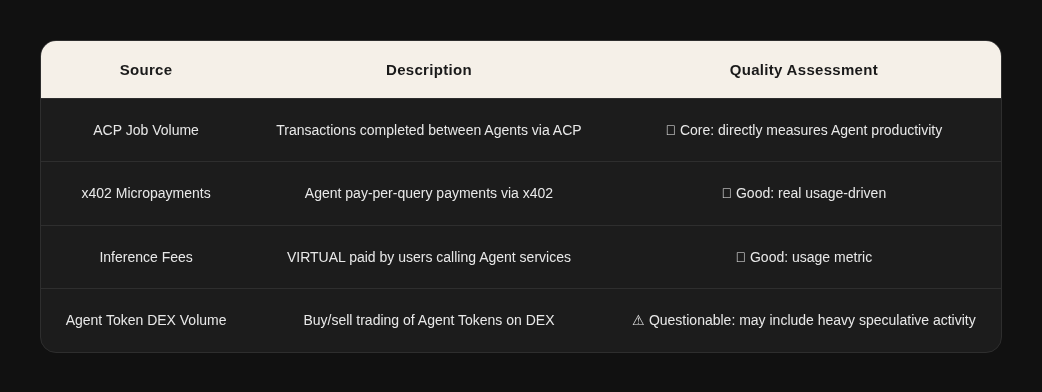
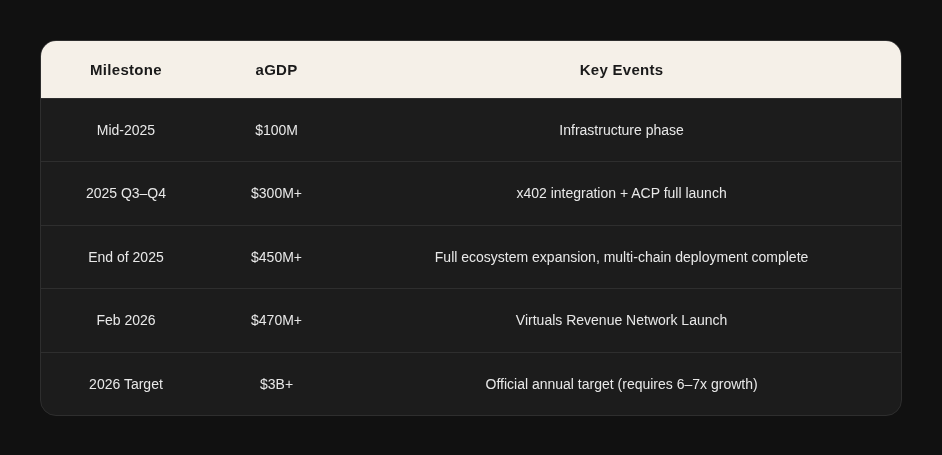
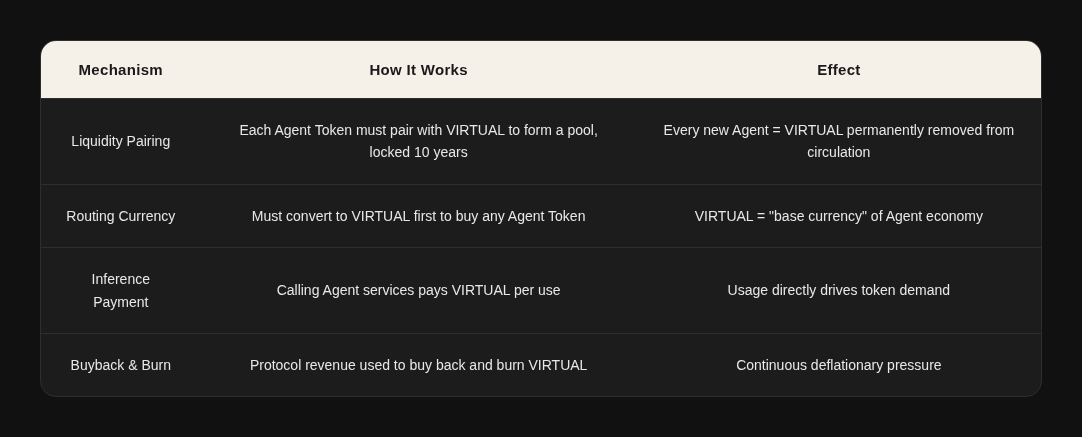
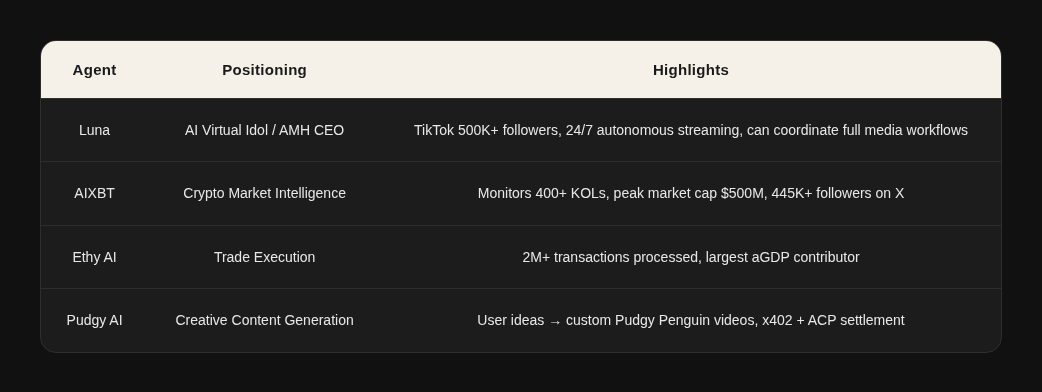










You must be logged in to post a comment Login