Crypto World
CRV price slides towards support amid LlamaLend pool exploit

CRV price trades near $0.24 as LlamaLend exploit concerns weigh on short-term sentiment.
Summary
- CRV price is holding above $0.22 support but struggling below $0.25 resistance.
- A $240K LlamaLend pool exploit has added fresh uncertainty around Curve’s ecosystem.
- A daily close below $0.22 could expose the psychological $0.20 level.
Curve DAO (CRV) token is trading at $0.24 at press time, down 3.5% over the past 24 hours. The pullback comes during a recovery attempt, with price still near the upper half of its seven-day range between $0.21 and $0.26.
CRV is up about 5% on the week but remains down 20% over the past month.
Derivatives activity has softened. Volume is down 12% to $127 million, while open interest has slipped 1.73% to $67.8 million, according to CoinGlass data.
As uncertainty persists, the drop in open interest shows that some leveraged positions are being closed rather than opened, indicating caution among traders.
LlamaLend pool exploit adds pressure
Curve Finance’s March 2 statement confirming that it is looking into an attack on the sDOLA LlamaLend markets has dampened sentiment. The issue stemmed from how the pool’s price oracle was configured, which introduced the risk of manipulation.
Blockchain security firm BlockSec had clarified that the vulnerability affected only the sDOLA–crvUSD LlamaLend pool and not Inverse Finance itself. The exploit resulted in an estimated $240,000 profit for the attacker.
Borrowers who used sDOLA as collateral were liquidated, while lenders were unaffected. sDOLA holders even saw gains due to the price distortion.
The attack relied on a flash loan. Funds were borrowed, sDOLA was redeemed and re-staked as a donation, and the pool’s pricing mechanism was temporarily distorted.
That shift pushed several positions below liquidation thresholds, allowing the attacker to liquidate them at a profit.
Curve emphasized that the core protocol contracts were not compromised. Even so, the incident has revived concerns about oracle design and integration risks within DeFi lending markets.
CRV price technical analysis
CRV continues to trade in a bearish structure. The daily chart shows a sequence of lower highs and lower lows. Price sits below the descending 50-day moving average, reinforcing the short- to mid-term downward bias.

Attempts to reclaim the 0.25–0.26 zone have failed so far, leaving overhead supply in place. Bollinger Bands expanded to the downside after a period of contraction, confirming that the latest volatility break favored sellers.
Price is now hugging the lower band, a sign that sell pressure has not fully eased. A close back above the mid-band would be the first sign of stabilization, but that has yet to occur.
The momentum is still skewed toward bears because the relative strength index is less than 50. It recently recovered from around the 30 level, but there hasn’t been any major bullish divergence.
Immediate support sits near 0.22, which marks the lower boundary of the current range and a liquidity cluster. A daily close below that level could open the path toward the psychological 0.20 mark.
On the upside, 0.25 acts as near-term resistance. A sustained move above 0.30 would be required to break the pattern of lower highs and shift the broader structure.
Crypto World
Ansem Says Ethereum Is in a Worse Spot Than 2023 as Thesis Weakens
Crypto analyst Ansem argues that Ethereum (ETH) is in a “worse spot” in 2026 than it was in 2023, pointing to a thesis he says has been eroding for years.
His bearish take drew rebuttals from some members of the community. Meanwhile, on-chain activity and technical indicators elsewhere on the network flash bullish signals.
Ansem Lists Cracks in the ETH Thesis
Ansem argues that Solana (SOL) has dominated retail activity this cycle. Hyperliquid has taken the lead in perpetual futures trading, while rollups have failed to gain traction.
He also noted that Vitalik Buterin “publicly abandoned” the general-use rollup thesis. The ongoing Aave (AAVE) situation around the KelpDAO rsETH exploit, Ansem said, is a mark on Ethereum’s core value proposition of “safety + security of defi & insto interest.
“ETH thesis has been weakening consistently for years,” the analyst wrote. ETH in 2026 is in a worse spot than it was in 2023, amplified by AI doing extremely well & tech stocks being much more favorable investments with real revenues / emerging narratives / increasing momentum, ETH is a $300B asset with a ton of overhang from Tom Lee topblasting + complacent ETH holders sitting idle in defi protocols.”
Follow us on X to get the latest news as it happens
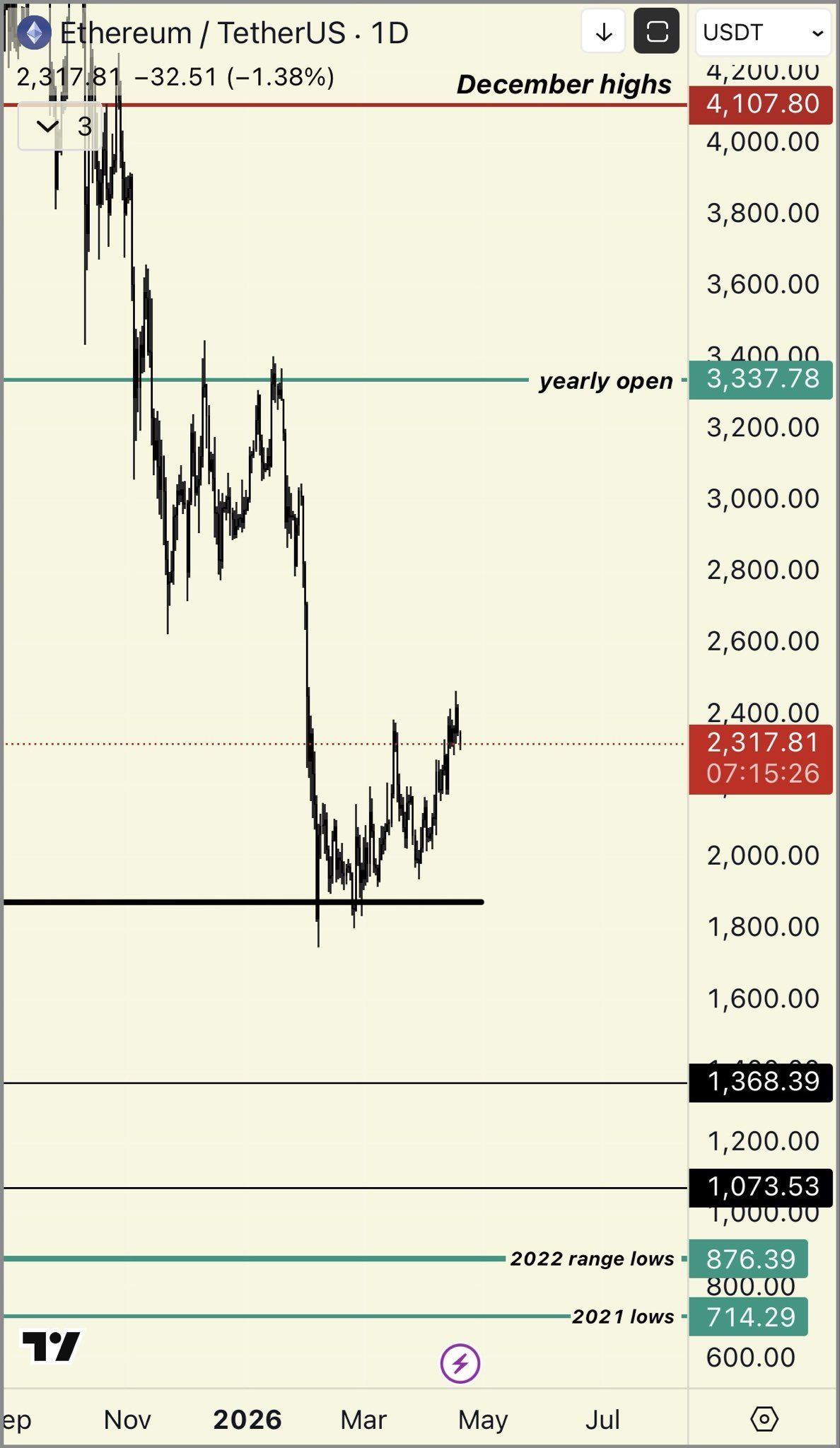
Technically, the analyst noted that ETH remains in a sustained downtrend after failing to break multi-year resistance. He projected that the second-largest cryptocurrency could slip to 2025 lows near $1,300 and to the bear-market lows from 2022.
“Tight invalidation 2377 assuming problems worsen if you want to play it loose assuming other risk assets continues doing well & drags it up probably somewhere around 2700/2800 invalidation fundamentals wise would want to see breakout activity from some new vertical,” the post read.

Community Members Push Back
The take triggered notable pushback. Ryan Berckmans accused Ansem of not understanding fundamentals. Leo Lanza went further, sharply dismissing the analyst’s bearish case on X.
Another user pointed to a 56% drop in the SOL/ETH pair this cycle.
“Soleth is down 56% after being up 12x+ *this cycle* because one guy decided to buy 5% of the eth supply after it had underperformed all cycle. idk why you guys act like i dont also bearpost solana i havent posted anything bullish about sol in over a year,” Ansem replied.
Not everyone shares the bearish view on Ethereum. BeInCrypto recently highlighted that network activity remains strong, while technical indicators like the Rainbow Chart and MACD are also flashing bullish signals.
With macro and geopolitical uncertainty still in play, the question is whether ETH slides further this year or stages a renewed rally.
Subscribe to our YouTube channel to watch leaders and journalists provide expert insights
The post Ansem Says Ethereum Is in a Worse Spot Than 2023 as Thesis Weakens appeared first on BeInCrypto.
Crypto World
Aave’s TVL Falls $8B After $293M Kelp DAO Hack
Total value locked on decentralized lending protocol Aave dropped by nearly $8 billion over the weekend after hackers behind the $293 million Kelp DAO exploit borrowed funds on Aave, leaving roughly $195 million in “bad debt” on the protocol and triggering withdrawals.
Data from DeFiLlama shows that Aave’s TVL fell from about $26.4 billion to $18.6 billion by Sunday, losing the top spot as the largest DeFi protocol.
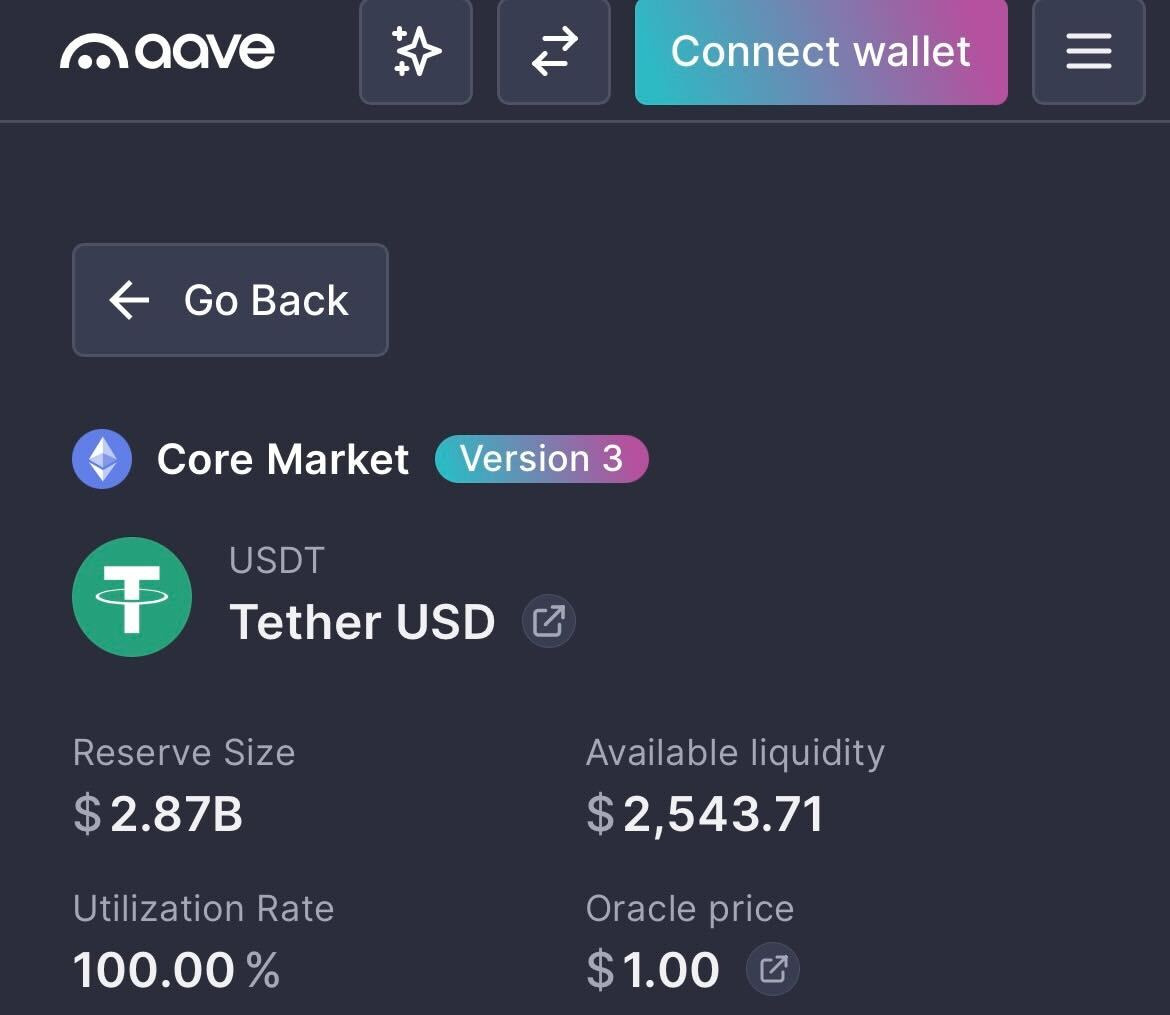
Aave v3’s lending pools for USDt (USDT) and USDC (USDC) are now at 100% utilization, meaning that more than $5.1 billion worth of stablecoins cannot be withdrawn until new liquidity arrives or borrows are repaid.

Aave’s TVL fall shows how rapidly risk from a single security incident can spread throughout the broader, interconnected DeFi lending market, potentially leading to a severe liquidity crisis.
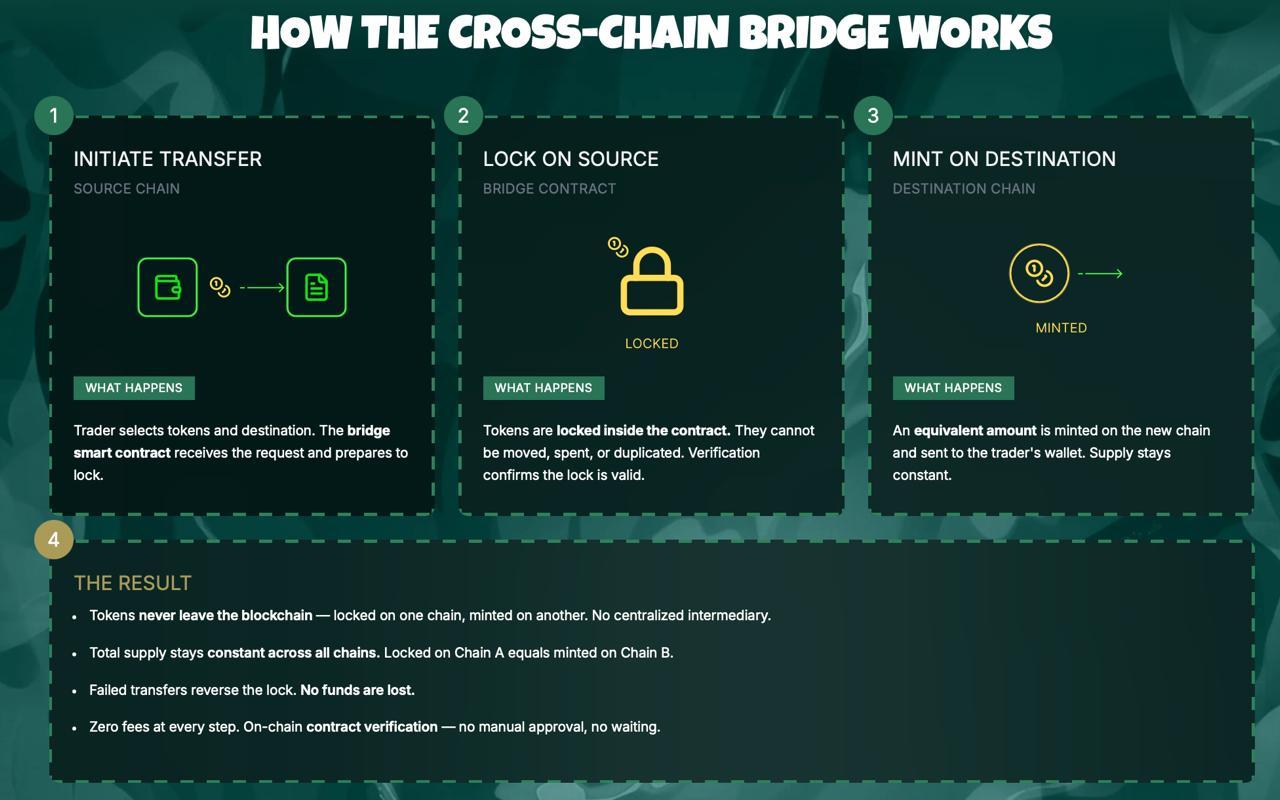
The incident began on Saturday when hackers stole 116,500 Kelp DAO Restaked ETH (rsETH) tokens worth about $293 million from Kelp DAO’s LayerZero-powered bridge and used them as collateral on Aave v3 to borrow wrapped Ether (wETH).
Crypto analytics platform Lookonchain said the move created about $195 million in “bad debt” on Aave, which contributed to the Aave (AAVE) token tanking nearly 20% from $112 on Saturday at 6:00 pm UTC to $89.5 about 25 hours later.
Lookonchain noted that some of the largest crypto whales to withdraw funds from Aave were the MEXC crypto exchange and Abraxas Capital at $431 million and $392 million, respectively.

Several crypto networks and protocols tied to rsETH or the LayerZero bridge have paused use of the bridge until the problem is resolved, including DeFi platform Curve Finance, stablecoin issuer Ethena and BitGo’s Wrapped Bitcoin (WBTC).
Aave has frozen several rsETH, wETH markets
Shortly after the Kelp DAO exploit, Aave said it froze the rsETH markets on both Aave v3 and v4 to prevent any suspicious borrowing and later stated that rsETH on Ethereum mainnet remains fully backed by underlying assets.
WETH reserves also remain frozen on Ethereum, Arbitrum, Base, Mantle and Linea, Aave said.
This incident marks the first significant stress test of Aave’s “Umbrella” security model, which was introduced in June 2025 to provide automated protection against protocol bad debt while enabling users to earn rewards.
Related: Aave DAO backs V4 mainnet plan in near-unanimous vote
Earlier this month, the Bank of Canada found that Aave avoided bad debt in its v3 market by using overcollateralization, automated liquidations and other strategies that shifted risk to borrowers.
In comments to Cointelegraph, Aave defended its liquidation-based model, framing it as a core safety mechanism that protects lenders while limiting downside for borrowers.
It comes as Aave parted ways with its longest-standing DeFi risk service provider, Chaos Labs, on April 6, following disagreements over the direction of Aave v4 and budget constraints.
Magazine: Are DeFi devs liable for the illegal activity of others on their platforms?
Crypto World
Hack at Vercel sends crypto developers scrambling to lock down API keys


A breach at web infrastructure provider Vercel is forcing crypto teams to rotate API keys and do a deep inspection of their underlying code.
In a bulletin, Vercel said the hacker was able to grab behind-the-scenes settings that weren’t locked down, potentially exposing API keys — the digital credentials apps use to connect to other services. Those credentials act like digital passwords, allowing software to connect to databases, crypto wallets, and external services. In the wrong hands, they can be used to impersonate an app, burn through usage limits, or manipulate how it runs.
A post on cybercrime forum BreachForums claimed to be selling Vercel data for $2 million, including access keys and source code, though those claims have not been independently verified. Vercel said it has engaged incident response firms and law enforcement and is continuing to investigate whether any data was exfiltrated.
The company traced the intrusion to Context.ai, a third-party AI tool used by an employee, its CEO said in an X post, where a compromised Google Workspace connection allowed attackers to escalate access into Vercel’s internal environments. Vercel said environment variables marked as “sensitive” are stored in a way that prevents them from being read, and that there is no evidence that they were accessed.
The incident is drawing scrutiny because Vercel underpins frontend infrastructure for many crypto applications and is the primary steward of Next.js, one of the most widely used web development frameworks. Many Web3 teams host wallet interfaces and decentralized app dashboards on Vercel, relying on environment variables to store credentials that connect their frontends to blockchain data providers and backend services.
Solana-based decentralized exchange Orca said its frontend is hosted on Vercel and that it has rotated all deployment credentials as a precaution. The project added that its on-chain protocol and user funds were not affected.
Crypto World
BeInCrypto 100 Institutional Awards Nomination: BitGo for Best Stablecoin Infrastructure Leader


Stablecoins have moved into core financial infrastructure. Monthly on-chain volume now exceeds $2 trillion. Payment networks like Visa, Mastercard, and Stripe have all expanded into the space.
However, the infrastructure behind them is almost invisible. This includes custody, minting, settlement, and compliance systems. That is where BitGo operates.
The company is now nominated for Best Stablecoin Infrastructure Leader at the BeInCrypto Institutional 100 Awards 2026.
Growing Institutional Footprint
The nomination centers on BitGo Mint, launched April 2, 2026. The platform allows institutions to mint, redeem, and manage stablecoins directly within BitGo’s custody environment.
BitGo’s move comes after a series of structural milestones. In December 2025, the Office of the Comptroller of the Currency approved its conversion to a federally chartered national trust bank.
One month later, BitGo listed on the New York Stock Exchange under the ticker BTGO.
That sequence placed BitGo in a unique position where it operates stablecoin infrastructure inside a federally regulated banking framework.
Founded
Assets on Platform
Clients
Ticker
Insurance
Federal Charter
2013
$81.6 billion
5,322
NYSE: BTGO
$250 million
OCC
Assets and client data are based on BitGo’s SEC filings as of December 31, 2025. Insurance and charter details follow the OCC approval in December 2025.
BitGo Mint launched with support for two stablecoins. These include USD1, developed by World Liberty Financial, and SoFiUSD, issued by SoFi Bank. Both run on BitGo’s Stablecoin-as-a-Service infrastructure.
This system handles custody, reserve management, and minting mechanics. It also provides compliance frameworks required for institutional issuance. USD1 is backed by short-term US Treasuries and cash equivalents, with reserves held under qualified custody.
Building a Regulated Stablecoin Backbone
Scale is a central part of the nomination. According to its March 2026 10-K filing, BitGo reports $81.6 billion in assets on platform.
Institutional clients reached 5,322, up 103.5% year over year. The platform also serves 1.2 million users and holds $15.6 billion in staked assets.
The company operates under a national trust bank charter. This allows it to provide custody and related services across all 50 US states without separate licenses. Assets held in custody are insured for up to $250 million.
Analysts have described BitGo as a “military-grade custodian.” The comment reflects its long-standing focus on institutional security infrastructure.
The stablecoin push extends beyond BitGo Mint. In March 2026, the firm partnered with Stable Sea to support B2B stablecoin payments and on-chain treasury services. These products run through its Crypto-as-a-Service stack.
As a result, BitGo now offers a unified system. Custody, wallets, staking, trading, financing, and stablecoin infrastructure operate within a single regulated entity.
This is the core of the nomination. BitGo has combined federal banking oversight with stablecoin issuance and custody in one platform. Most providers still separate these functions across different systems.
The model is already live. Institutions can mint, hold, and distribute stablecoins within a regulated custody workflow.
That changes how stablecoins move between issuers, markets, and counterparties.
The BeInCrypto Institutional 100 Awards aim to identify infrastructure providers shaping the next phase of digital finance. BitGo’s nomination reflects its role in building the backend systems that support institutional stablecoin adoption.
The post BeInCrypto 100 Institutional Awards Nomination: BitGo for Best Stablecoin Infrastructure Leader appeared first on BeInCrypto.
Crypto World
Bitcoin Open Interest Falls $3B as BTC Deleveraging Exposes Fragile Market Structure

TLDR:
- Bitcoin Open Interest fell from $27B to $24B, reflecting broad long position closures across the derivatives market.
- Funding rates stayed slightly positive, confirming shorts are not leading BTC’s current price correction phase.
- One-hour heatmap data showed no major liquidity zones, pointing to capital outflows rather than liquidity hunting moves.
- Analyst Carmelo Alemán noted BTC’s price decline is a consequence of prior structural weakness, not a fresh bearish trigger.
Bitcoin Open Interest has declined sharply, drawing attention to the market’s weak structural foundation. On-chain analyst Carmelo Alemán noted that BTC’s recent price pullback aligns with a notable drop in derivatives exposure.
Open Interest fell from roughly $27 billion to $24 billion. This pattern reflects long position closures and progressive deleveraging rather than aggressive selling. The data confirms that the earlier rally lacked real spot demand and was largely built on leveraged positions.
BTC Price Decline Tied to Derivatives Deleveraging
Bitcoin’s recent correction is directly connected to a derivatives-heavy market structure. Alemán had previously raised concerns that the bullish move lacked structural consistency.
The rally was fueled by futures activity rather than genuine demand in the spot market. Recent market behavior has since confirmed that earlier assessment clearly.
Open Interest dropping from $27 billion to $24 billion captures the full scope of the unwind. Long positions have been closing at a steady pace, pulling down overall derivatives exposure.
This process does not point to aggressive bearish pressure from short sellers. Instead, it reflects a gradual, market-wide effort to reduce leveraged exposure.
Heatmap analysis on the one-hour timeframe adds further context to the price movement. Based on TradingDifferent visual data, no major contiguous liquidity zones were identified in the area.
This rules out liquidity hunting or stop-loss sweeps as the primary driver behind the move. The price action therefore reflects capital outflows rather than directional pressure from either side.
Alemán, a verified contributor on CryptoQuant, noted that this outcome was foreseeable. A move built on derivatives tends to lose consistency once leverage begins coming off.
The price decline is not the root of the problem but a consequence of earlier fragility. The weak structural base was already present before the correction started materializing.
Positive Funding Rates Signal Risk Reduction, Not Bearish Control
Funding rates have remained slightly positive even as Bitcoin’s price continues to pull back. This is an important data point when assessing who is leading the current market move.
Positive funding rates show that long traders are still paying short traders a small periodic fee. Shorts are not the dominant force pushing prices lower at this stage.
Alemán noted that the market is not attacking the downside. Rather, participants are collectively choosing to reduce their derivatives exposure in an orderly way.
There is no evidence of coordinated short-side aggression driving the current phase. The correction aligns more with disciplined deleveraging than with a fresh bearish trend forming.
The one-hour heatmap data also supports this more neutral reading of market structure. Without major liquidity clusters nearby, price tends to drift lower in a measured, methodical manner.
The sharp, reactive moves typical of liquidity-driven markets are largely absent here. This reinforces the view that capital outflows, not targeted selling, are steering the current phase.
Bitcoin Open Interest contraction is clearing the excess leverage that accumulated during the earlier rally. Once this process runs its course, the market may find a more stable structural base.
Alemán’s analysis ties the current correction directly to the previously identified weakness in market structure. The price decline reflects the consequence of that fragility rather than a fresh bearish catalyst.
Crypto World
Aave Faces Crisis: rsETH Exploit Drains $250M as TVL Plunges $7B and AAVE Token Falls 15%

TLDR:
- An rsETH collateral exploit on Aave allowed an attacker to extract approximately $250 million from the protocol
- Aave’s total value locked dropped by roughly $7 billion in a single day following the exploit and mass withdrawals
- Exchange inflows for AAVE surged to over 355,000 tokens, totaling around $32 million across all platforms
- The AAVE token dropped nearly 15% as panic selling intensified amid contributor exits and collateral risk concerns
Aave is facing mounting pressure following a series of internal and external setbacks. The decentralized lending protocol recently suffered an exploit tied to rsETH, a collateral asset accepted within its ecosystem.
The attack allowed a malicious actor to extract approximately $250 million. This event compounded existing challenges, including the departure of key contributors BGD Labs and Chaos Labs.
As a result, the protocol experienced a sharp drop in total value locked and investor confidence.
rsETH Exploit Exposes Collateral Risks on Aave
The exploit did not originate from a flaw within Aave’s core protocol. Instead, the issue was rooted in rsETH, an asset accepted as collateral on the platform.
When a collateral asset deteriorates, it can trigger cascading effects across the lending system. These effects often result in bad debt accumulating within the protocol.
Crypto analyst Darkfost noted on X that cascading risk is inherent to collateral-based lending systems. The decision to accept rsETH ultimately opened the door to this vulnerability.
Once the exploit occurred, panic spread quickly through the community. Users began pulling their funds from the protocol at a rapid pace.
The wave of withdrawals caused the platform’s total value locked to fall by approximately $7 billion. This contraction took place over the course of a single day.
Many participants chose to exit their positions rather than absorb the uncertainty. The reaction was swift and spread broadly across the ecosystem.
The timing also worsened the situation considerably. BGD Labs and Chaos Labs had already left their contributor roles before this event.
Their exits weakened the protocol’s risk management and development capacity. The exploit therefore arrived at a particularly vulnerable moment for the protocol.
AAVE Token Selloff and Exchange Inflows Surge Amid Crisis
The AAVE token fell by approximately 15% on the day the exploit became public. This correction reflected the combined weight of the attack and the loss of community trust.
Investors moved quickly, reducing their exposure to the token as uncertainty grew. The drop was among the sharpest the token had recorded in recent months.
Exchange inflows for the token surged sharply during this period. The monthly average for token inflows into exchanges sits at around 31,000.
During the crisis, more than 236,000 AAVE flowed into exchanges in a short window. That volume represented roughly $21 million at current prices.
According to Darkfost, cumulative inflows across all exchanges exceeded 355,000 AAVE in total. This translates to approximately $32 million worth of the token.
Binance absorbed the largest share of these inflows due to its deep liquidity. The concentration on Binance reflected organized and rapid selling activity.
Together, these numbers point to a broad loss of confidence in the protocol. The platform has lost key contributors and now faces questions about its collateral risk framework.
Exchange inflows and token price declines both show sustained selling pressure. Market participants are watching closely as the situation continues to develop.
Crypto World
Bitcoin Slips Below $74K as US Navy Strikes on Iranian Ship


Bitcoin changed hands near $73,996 during Monday’s Asian trading session, down 2.5% over the past 24 hours. The decline tracked a weekend escalation in the Gulf, where US forces boarded an Iranian vessel Sunday.
Risk assets broadly weakened as Wednesday’s ceasefire deadline loomed, with fresh military friction eroding hopes for de-escalation.
Ship Seizure Raises War Escalation Fears
The US destroyer USS Spruance disabled the engine room of the Iranian-flagged cargo ship Touska after six hours of unheeded stop orders. Tehran’s joint military command labeled the boarding unlawful and pledged a direct response against US naval assets. Sunday’s capture was the first since Washington began enforcing its port blockade one week ago.
Crude futures jumped on the incident, as traders priced in a longer chokehold on Gulf shipping lanes. About one-fifth of the world’s seaborne oil normally transits the strait, which has been mostly idle. Iran’s Supreme National Security Council stated that traffic controls would stay in place until hostilities conclude.
A US team led by Vice President JD Vance is due in Islamabad on Monday for renewed negotiations. Special envoys Steve Witkoff and Jared Kushner will reportedly return for round two after last weekend’s marathon session. Tehran’s state broadcasters cast doubt on whether Monday’s sit-down would proceed, citing fresh grievances with Washington.
The US president also warned of strikes on Iran’s entire power grid and bridge network if terms are refused. Despite Sunday’s slide, Bitcoin remains 4.3% higher over the past seven days, keeping the weekly uptrend intact.
Traders Eye Wednesday Truce Expiry
Daily action swung between $73,886 and $76,165, with the sharpest pressure arriving early Monday in Asia. Total market value held around $1.48 trillion while turnover hovered near $62 billion during the same window.
Market focus shifts to Wednesday’s truce deadline, a pivot point that could sharpen the tone across risk assets. If diplomacy stalls, additional US operations appear likely, potentially extending the pressure on digital assets and equities.
The post Bitcoin Slips Below $74K as US Navy Strikes on Iranian Ship appeared first on BeInCrypto.
Crypto World
Ethereum Faces Liquidity Pressure as Price Swings Between $2,200 and $2,500 Zones

TLDR:
- ETH moved between $2,200 and $2,500 as liquidation zones triggered sharp price reversals
- Heavy leverage clusters near $2,200 and $2,480 continue shaping short-term ETH volatility patterns
- The failed breakout near $2,450 led to renewed downside pressure toward lower liquidity support zones
- Despite price weakness, Ethereum recorded over 200M transactions, showing strong network activity
Ethereum traded within a volatile range as liquidity clusters shaped short-term price action. Recent data showed weakening momentum after a failed breakout, while on-chain activity reached record levels despite a challenging first-quarter performance.
Liquidation Clusters Drive Short-Term Price Movement
Ethereum’s recent structure reflects a liquidity-driven market rather than a sustained directional trend. Price initially climbed from the $2,200 zone toward $2,380 before entering a tight consolidation phase.
A brief breakout near $2,450 followed, but momentum faded quickly, leading to a controlled decline toward the $2,300 range.
A market update shared by Ted Pillows pointed to heavy liquidation clusters influencing price behavior. The tweet noted that Ethereum appeared weak, with long liquidation zones concentrated near $2,200.
It also identified short-side liquidity between $2,450 and $2,480 as a potential final upward move before rejection.
The heatmap data showed bright zones where leveraged positions were concentrated. These levels often attract price movements as the market seeks to trigger liquidations.
Strong resistance formed between $2,480 and $2,520, where the price faced immediate rejection. Meanwhile, support zones between $2,280 and $2,320 acted as a near-term magnet.
As the price moved lower, long positions began to unwind. This shift aligned with the broader pattern of liquidity sweeps between key levels.
The range between $2,300 and $2,450 remained active, with repeated moves targeting both sides of the market.
Strong Network Activity Contrasts Price Weakness
While price action remained under pressure, Ethereum’s network activity expanded sharply. The network recorded over 200 million transactions during the first quarter of 2026.
This marked one of the highest usage periods despite the asset’s 32 percent decline during the same timeframe.
At the same time, ecosystem developments continued to build. Ethereum Name Service integrated with PayPal, enabling users to send funds using simplified name-based addresses. This update aimed to improve accessibility for mainstream users interacting with blockchain systems.
Security and decentralized finance infrastructure have also advanced. Safe introduced a beta version of its wallet designed to act as a pre-execution security layer. In parallel, Silo Finance launched its V3 upgrade, focusing on improved lending safety within decentralized markets.
Looking ahead, price scenarios remain tied to key liquidity levels. A hold above $2,280 could allow a move back toward $2,400 and higher resistance zones. However, a breakdown below this level may lead to a sweep toward $2,200, where deeper liquidity sits.
Market conditions continue to show a balance between technical pressure and underlying network growth. As a result, price action remains sensitive to leveraged positioning, while broader adoption trends develop in the background.
Crypto World
Changpeng Zhao Declines Satoshi Identity Disclosure, Citing Bitcoin Structure

TLDR:
- Changpeng Zhao confirmed he does not know Satoshi Nakamoto’s identity during a recent interview discussion.
- CZ stated he would not reveal Satoshi’s identity even if known, maintaining a consistent long-term stance.
- He explained that anonymity helps Bitcoin avoid central authority and maintain its decentralized structure.
- CZ noted that Satoshi’s absence allows Bitcoin to operate without influence from a single individual.
Changpeng Zhao addressed long-standing curiosity about Bitcoin’s creator during an April 9, 2026, interview. Speaking on the TBPN Channel, he stated he does not know the identity of Satoshi Nakamoto and would not reveal it if known.
CZ Maintains Distance From Satoshi Identity Debate
Changpeng Zhao, founder of Binance, addressed one of crypto’s oldest questions during the interview. He confirmed he does not know Satoshi Nakamoto’s real identity. He also made clear he would not disclose such details even if he had access.
A widely shared post captured his remarks during the interview session. In the clip, CZ reiterated his position calmly and without hesitation.
The statement quickly circulated across crypto communities, drawing attention to his consistent stance on the topic.
He explained that curiosity about Bitcoin’s creator exists across the industry. However, he stressed that uncovering the identity could create unnecessary risks. According to CZ, anonymity has played a key role in Bitcoin’s growth and resilience.
He further noted that Bitcoin operates without reliance on a central figure. This structure, he said, has helped maintain trust in the network. As a result, he sees no reason to pursue the identity question actively.
Anonymity Seen as Core to Bitcoin’s Structure
CZ emphasized that Bitcoin’s decentralized nature remains closely tied to its anonymous origins. He explained that a known founder could attract unwanted attention or influence. That scenario could shift how the network is perceived and governed.
He pointed out that Satoshi Nakamoto’s absence removes any central authority figure. This absence, in turn, allows Bitcoin to function without leadership pressure. It also prevents decisions from being tied to one individual’s influence.
During the discussion, CZ made it clear that he does not intend to investigate further. He described the search for Satoshi’s identity as unnecessary for Bitcoin’s continued operation. Instead, he focused on the system’s design and independence.
He added that Bitcoin’s strength lies in its open and distributed framework. Without a visible founder, the network avoids personality-driven narratives. This structure supports its position as a decentralized financial system.
CZ’s comments align with a broader view held by many in the crypto space. The unknown identity of Satoshi Nakamoto remains one of Bitcoin’s defining characteristics. For CZ, preserving that mystery remains aligned with maintaining the network’s original structure.
Crypto World
Could Pepeto Mirror BTC’s Early Run as Presale Crosses $9.2M Before Binance Listing
BlackRock pulled $505 million into its iShares Bitcoin Trust across two April sessions, the biggest haul since early March. That scale of buying in a slow macro window says real money is already positioning before retail even opens a chart. Against that backdrop, Pepeto is drawing attention on the meme coin exchange layer of the market.
The presale has crossed $9.2 million raised and the token keeps landing on watchlists alongside the latest Bitcoin price news for 2026.
Morgan Stanley launched MSBT this April and delivered the strongest first day for any of its ETFs on record, according to Bitcoin Magazine. Across the same window, BlackRock’s IBIT pulled $505 million in two sessions, per Crypto Briefing.
The combination puts bank distribution firmly behind Bitcoin, and fresh capital is rotating into early entries as the overflow spreads. Money flowing this steady during a quiet macro window reads like slow motion buying by the biggest wallets on the board.
Two Names Worth Watching This April: Pepeto and Bitcoin
Pepeto Could Mirror Bitcoin’s Early Run Ahead of the Binance Listing
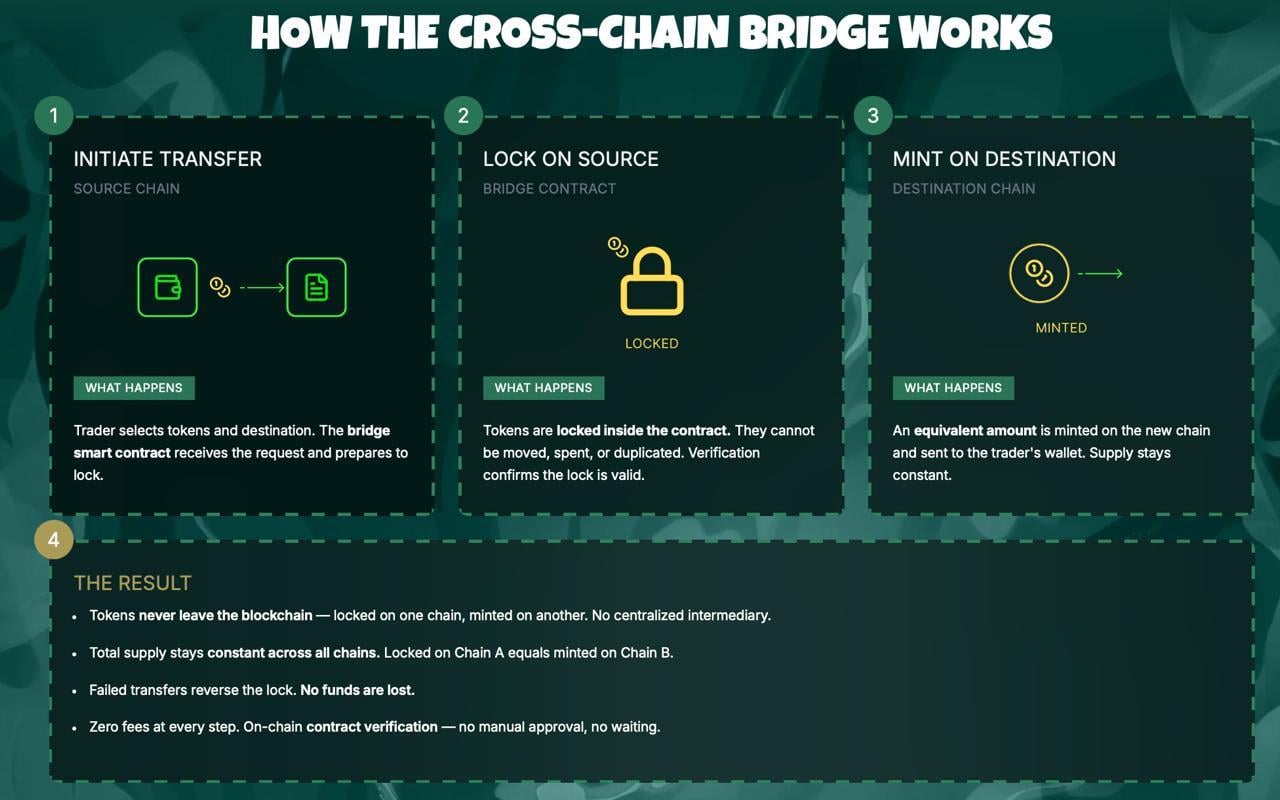
Right now, serious money in crypto is moving toward projects that already ship working products. BlackRock’s IBIT flow this week backs the same pattern, that capital rewards platforms actually building rather than publishing pitch decks. While big exchanges focus on expanding market infrastructure, Pepeto targets the meme coin trading layer with a zero fee exchange and a cross chain bridge live today.
The Pepeto presale has pulled more than $9.2 million and the token sits at $0.000000186 ahead of the Binance listing. A built in risk scorer checks every contract wallets interact with against known attack patterns, helping new buyers avoid the scams that emptied bags during the last meme cycle.
Auditors at SolidProof cleared every piece of the contract stack, a Binance alum drives the engineering side, and the founder who put the original Pepe into the market is at the head of this operation. That team previously drove a token with no working utility up to an $11 billion valuation, and this round a functional exchange is attached before the listing even prints.
Experienced buyers know the biggest returns come from entering before the broader wave shows up. Early buyers in Bitcoin captured that dynamic long before mainstream headlines caught on, and many investors are paying the same attention to Pepeto now. A 150x move matches what Pepe proved once, only this time a live exchange, clean audit, and Binance listing sit in the queue. The people who move during fear own the supply the late crowd pays up for.
BTC Price Prediction: Bitcoin Tests $75.143 With $80K in Range
Bitcoin broke through $75.143 this week according to CoinMarketCap as the Iran tension eased and oil rolled over, and technicals now point at $80,000 as the next zone, per Intellectia analysis. BlackRock IBIT ended Q1 with $54 billion in assets and captured roughly $8.4 billion in net inflows for the quarter.
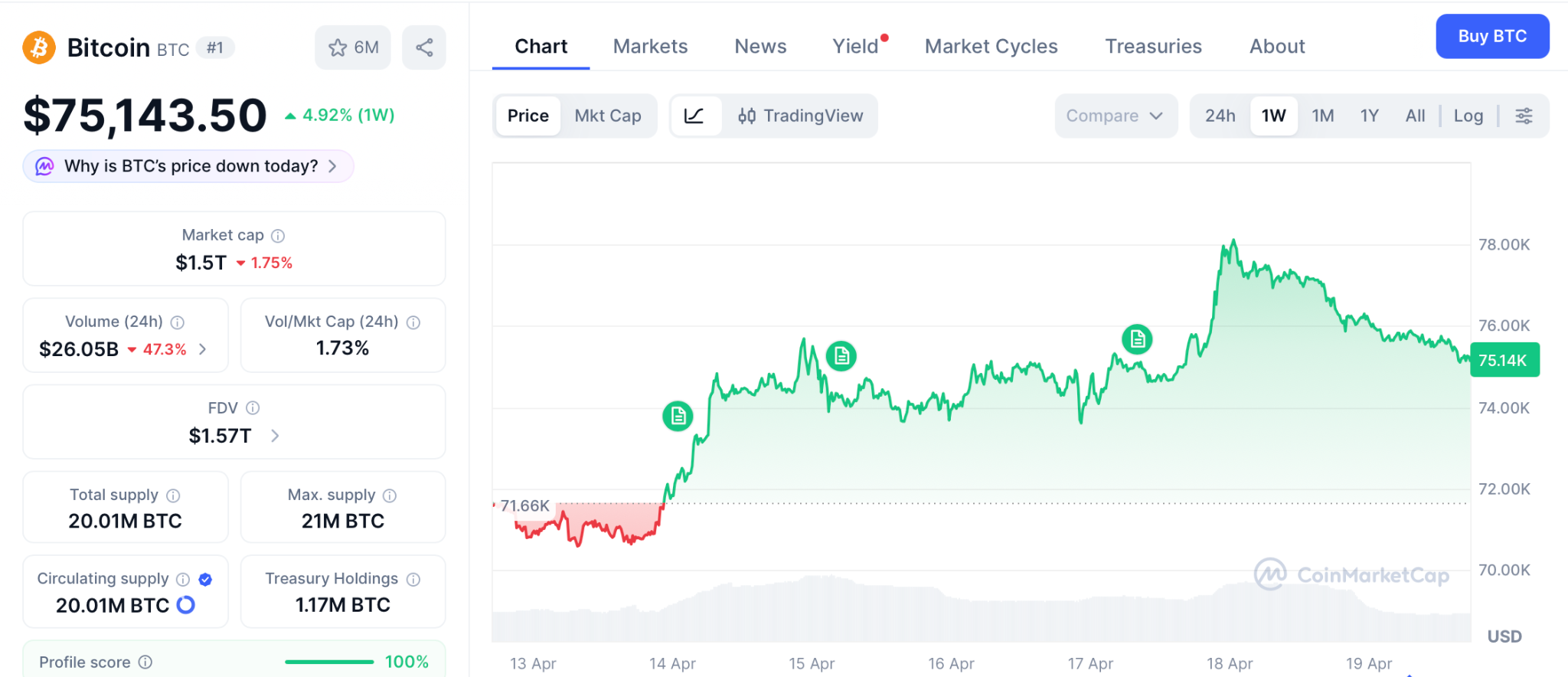
Wallets holding 10,000 to 100,000 BTC have been quietly adding, and ETF holdings now sit near $96 billion across the category. A break above $78,000 opens a path to $80,000 and eventually the $97,000 prior cycle peak.
Failure at $75,143 keeps the range tight between $70,000 and $78,000 while the Fed decision weights. Either way, Bitcoin’s next 2x takes months, which is the same window a 150x presale can close in days.
Conclusion
Retail watches the latest Bitcoin price news hoping for a quick 10% off ETFs, and BlackRock’s $505 million IBIT buy gave them reason to stare. But the setup that produced every early buyer story in crypto looks nothing like a large cap grinding from $75K to $80K.
It looks like an entry today on a token with a working exchange, a clean audit, and the same founder who took Pepe from nothing to $11 billion with zero products.
The same setup minted early SHIB and Pepe millionaires in the last run, and wallets buying Pepeto through the Pepeto official website today walk out of the Binance listing holding the same returns.
Click To Visit Pepeto Website To Enter The Presale
FAQs
Why is institutional activity important for the latest Bitcoin price news?
BlackRock IBIT pulled $505 million this week while Morgan Stanley’s MSBT posted its best ETF debut, keeping structural demand under the Bitcoin price news cycle.
How does the Binance listing affect the Pepeto path from here?
The listing opens Pepeto trading to the biggest exchange audience in the world, and the current entry price at the Pepeto official website closes the moment it prints.
What signals are traders watching for the next Bitcoin move?
Traders track ETF flows, whale wallets, and the $80,000 resistance, which together shape whether BTC breaks out or ranges through the Fed window.
Disclaimer: This is a Press Release provided by a third party who is responsible for the content. Please conduct your own research before taking any action based on the content.
-

 Crypto World6 days ago
Crypto World6 days agoThe SEC Conditionalises DeFi Platforms to Be Avoided for Broker Registration
-

 Fashion2 days ago
Fashion2 days agoWeekend Open Thread: Theodora Dress
-

 NewsBeat6 days ago
NewsBeat6 days agoTrump and Pope Leo: Behind their disagreement over Iran war
-

 Crypto World6 days ago
Crypto World6 days agoSEC Signals Exemption for Crypto Interfaces From Broker Registration
-

 News Videos5 days ago
News Videos5 days agoSecure crypto trading starts with an FIU-registered
-

 Sports3 days ago
Sports3 days agoNWFL Suspends Two Players Over Post-Match Clash in Ado-Ekiti
-
 Crypto World6 days ago
Crypto World6 days agoSEC Proposes Certain Crypto Interfaces Don’t Need to Register as Brokers
-

 Business13 hours ago
Business13 hours agoPowerball Result April 18, 2026: No Jackpot Winner in Powerball Draw: $75 Million Rolls Over
-

 Politics2 days ago
Politics2 days agoPalestine barred from entering Canada for FIFA Congress
-

 Crypto World2 days ago
Crypto World2 days agoRussia Pushes Bill to Criminalize Unregistered Crypto Services
-

 Sports7 days ago
Sports7 days agoNWFL opens Pathway for new Clubs ahead of 2026 Season
-

 Business3 days ago
Business3 days agoCreo Medical agree sale of its manufacturing operation
-

 Entertainment6 days ago
Entertainment6 days agoBrand New Day’ Footage Reveals the Devastating Impact of ‘Now Way Home’
-
 Politics18 hours ago
Politics18 hours agoZack Polanski demands ‘council homes not luxury flats for foreign investors’
-

 Crypto World7 days ago
Crypto World7 days agoTrump whales load up ahead of Mar-a-Lago luncheon.
-
Business7 days ago
Kering slides after Morgan Stanley downgrade, Gucci woes loom
-

 Tech7 days ago
Tech7 days agoApple glasses won’t go brand shopping like Meta did with Ray-Ban and Oakley
-

 Tech7 days ago
Tech7 days agoGoogle adds E2E encryption to Gmail for iOS and Android enterprise users
-

 Entertainment6 days ago
Entertainment6 days agoKarol G’s ‘Ultra Raunchy’ Coachella Set Gave ‘Satanic Vibes’
-
Entertainment7 days ago
How Euphoria Season 3 Premiere Paid Tribute to Eric Dane After Death












You must be logged in to post a comment Login